Gone are the days when business Wi-Fi was just about getting online. Today, it is a strategic tool, delivering secure, identity-based access and invaluable data insights. It is about moving away from a single, insecure password to a system where every user and device connects based on their identity. This transforms your Wi-Fi from a simple utility into a powerhouse for security, marketing, and operational efficiency, making your network both safer and smarter.
What Are Modern Business WiFi Solutions
Consider your traditional office Wi-Fi. It is likely akin to having a single master key for the entire building. One password is shared with staff, guests, and all company devices. If that single password falls into the wrong hands, your entire network is exposed.
Modern business Wi-Fi solutions discard that outdated blueprint. Instead of a master key, imagine providing everyone with a personalised smart access card. Each person and device receives their own unique, verifiable credential, ensuring they only access the areas they're authorised to enter.
This transition from a one-size-fits-all password to identity-based access is the essence of modern Wi-Fi. It is no longer just about providing an internet connection. It is about controlling who connects, what they can do, and how securely they do it. Best of all, it integrates directly into your company’s core identity systems, making access control a seamless, automated process.
From Cost Centre to Strategic Asset
For years, Wi-Fi was just another line item on the IT budget—a necessary expense that needed to function but did not offer much in return. That perspective is completely outdated. The right Wi-Fi solution is now a powerful asset that delivers tangible value to multiple departments. If you need a refresher on the basics, you can learn more about what WiFi is and how it works .
Here’s how different teams benefit:
- For IT Teams: Security receives a massive upgrade through zero-trust principles. Forget struggling with complex RADIUS servers or dealing with endless password-related helpdesk tickets. When an employee leaves, their access is revoked automatically. It is as simple as that.
- For Marketing Departments: Imagine capturing rich, first-party data on visitor behaviour. You can monitor footfall, track dwell times, and measure visit frequency. This is invaluable for creating personalised marketing campaigns and truly understanding the customer journey.
- For Operations Leaders: Gain actionable insights into how your physical spaces are actually utilised. A retail manager can optimise store layouts based on real customer traffic, while a hotel operator can anticipate peak demand to enhance guest services.
A modern Wi-Fi network does more than connect you to the internet; it connects you to your customers and secures your operations. It is the invisible infrastructure that drives visible business outcomes, from enhanced security to increased customer loyalty.
By consolidating management under a single platform and integrating with the systems you already use, these solutions offer a comprehensive picture of network activity. This allows you to enforce consistent security policies, analyse user behaviour, and ultimately, transform a simple internet connection into a source of powerful business intelligence. Your network ceases to be a passive utility and starts actively contributing to your growth and security.
Looking Under the Hood at Next-Gen WiFi Tech
To truly understand what modern business WiFi solutions can achieve, we need to look under the hood at the underlying technologies. These are not just minor tweaks; they represent a complete rethink of how devices connect, authenticate their identity, and remain secure. It is the difference between a cumbersome, manual process and a seamless, automated experience.
Think of Passpoint and its broader counterpart, OpenRoaming, as a global passport for your smartphone or laptop. Once configured, your device can automatically and securely connect to thousands of participating WiFi networks worldwide. No more searching for network names, typing in passwords, or connecting to unsecured public hotspots. Your device is recognised and trusted instantly.
This is a massive shift, and the industry is taking notice. Research from the Wireless Broadband Alliance indicates that a staggering 81% of Wi-Fi industry executives are planning OpenRoaming rollouts in 2025/2026. That is an increase of nearly 19% from 2024, signalling a clear move towards password-free, automated access, especially in venues like hotels and retail stores.
To appreciate how far we have come, let us compare the traditional approach with the new standard.
The Traditional Approach: Captive Portals
We have all experienced it. You connect to the WiFi at a hotel or coffee shop, and that familiar login page appears. That is a Captive Portal. You have to find the network, select it, enter your details, and check a box stating you agree to the terms. Every single time.
It is the digital equivalent of filling out the same form every time you enter a building. It is repetitive, cumbersome, and frankly, it conditions people to connect to almost any network that requests their details—a significant security risk.
The New Standard: Passwordless Authentication
Passwordless authentication is the modern, seamless alternative. It is more akin to a quick, secure keycard swipe that grants you immediate access, relying on stronger, certificate-based methods to verify a device’s identity automatically.
This is the key to how modern WiFi delivers both enterprise-grade security and incredible convenience. Once a user or device is authenticated, they remain authenticated during future visits, creating a completely frictionless journey.
A Place for Everything: Identity Pre-Shared Keys
But what about all those other devices that do not support advanced security certificates, such as office printers, smart thermostats, or IoT sensors? This is where Identity Pre-Shared Keys (iPSK) come into play. Instead of a single password shared across all these miscellaneous devices, an iPSK system assigns a unique, individual key to each one.
Think of it as providing every piece of equipment with its own personal keycard. If a device is ever compromised, you simply revoke its key. There is no need to disrupt anything else on the network. This provides you with incredibly granular control and addresses a common security vulnerability.
The table below outlines the key differences between these traditional and modern approaches, highlighting why the shift to modern authentication is crucial for businesses.
Comparison of WiFi Authentication Methods
As the comparison demonstrates, transitioning away from Captive Portals towards passwordless methods is not just about enhancing user convenience—it is a critical step in building a more secure and professional network environment.
Naturally, these technologies do not exist in isolation. They are often built on foundational standards like WiFi 6, which delivers superior speeds and can handle more devices simultaneously. To learn more, check out our guide on the benefits of WiFi 6 (802.11ax) .
The diagram below helps visualise how all these components fit together.
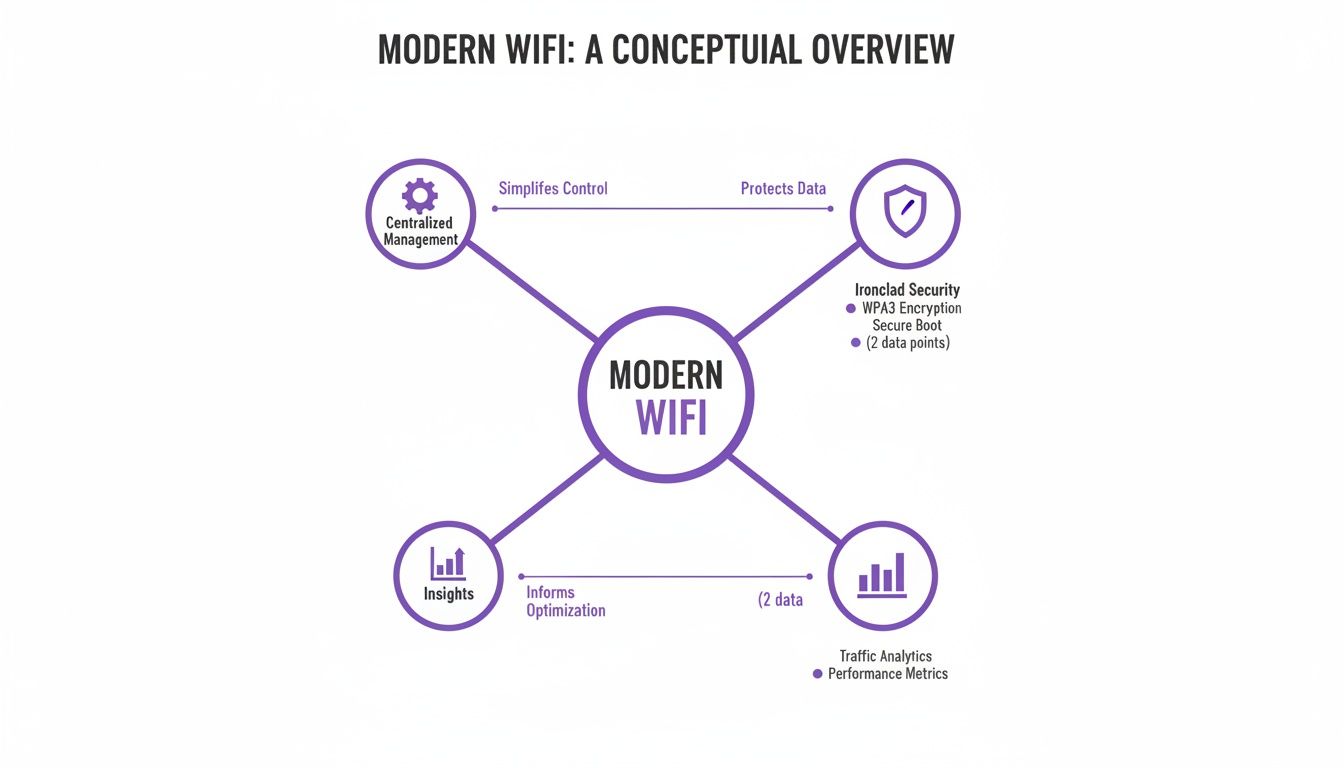
What this illustrates is that a modern WiFi solution is not just a single component. It is a combination of centralised management, robust security, and the capability to generate actionable business insights from network data. Each element supports the others, creating a system that is significantly more powerful than the sum of its parts. By integrating technologies like Passpoint and iPSK, businesses can finally build a network that is both highly secure and effortlessly simple to use.
Building a Zero-Trust Network with Secure WiFi
Modern business WiFi solutions serve as the perfect foundation for a robust zero-trust security strategy. The core principle is simple yet incredibly effective: never trust, always verify. It is a complete departure from the traditional "castle-and-moat" mindset, where being inside the network perimeter meant you were trusted by default.
Consider a zero-trust network less like a medieval fortress and more like a high-security corporate facility. Your identity is not merely verified at the main entrance; it is re-verified at every single door you attempt to open—whether it leads to the server room, the finance department, or the staff cafeteria. Every access request requires fresh authentication, ensuring you only access areas you are explicitly authorised for.
This is precisely how it functions with your WiFi. Every single time a device attempts to connect or access a resource, the network effectively asks, "Who are you, and do you have the necessary permissions?" This continuous cycle of verification drastically reduces your attack surface and contains potential threats before they can propagate.

Integrating with Your Corporate Identity
The true value is realised when you link network access directly to an employee's corporate identity. Today’s WiFi solutions integrate seamlessly with the identity providers you already rely on, such as Microsoft Entra ID (formerly Azure AD), Google Workspace, or Okta.
This integration means an employee’s network login is identical to the one they use for all other corporate applications. When they connect to the WiFi, the system verifies their status in your central directory in real-time. Are they an active employee? Which department do they belong to? What is their role?
Based on these verified details, the network automatically assigns the appropriate level of access. For IT teams, this is a complete game-changer.
Automating Access Control and Offboarding
One of the most persistent security challenges for any organisation is the "lingering access" of former employees. With legacy systems, revoking access was often a manual, multi-step process that left dangerous security gaps wide open.
A zero-trust WiFi model closes this loophole entirely. The moment an employee leaves the company and their account is deactivated in your central directory, their WiFi access is revoked instantly and automatically. There is no time lag, and no manual intervention is required from an IT administrator.
This automatic revocation ensures that network permissions are always perfectly synchronised with an employee’s current status, eliminating a critical vulnerability that attackers frequently exploit. The moment an individual is no longer part of the organisation, their digital access simply ceases to function.
This automated approach delivers significant operational benefits.
- No More RADIUS Servers: You can finally eliminate the need to manage complex, often fragile on-premise RADIUS servers. Authentication is handled in the cloud, massively simplifying your IT infrastructure.
- Fewer Helpdesk Tickets: Because access is tied to the corporate login employees already use, you eliminate an entire category of "I forgot the WiFi password" helpdesk tickets.
- Reduced Vulnerabilities: By strictly enforcing the principle of least privilege—where users can only access the absolute minimum resources required to perform their roles—you dramatically limit the potential damage a single compromised account can cause.
Ultimately, building a zero-trust framework with your business WiFi is not just about adding another layer of security. It is about fundamentally rethinking how access is granted and managed, creating a network that is inherently more intelligent, responsive, and secure by design. With a focus on robust data protection, you can confidently build a secure network foundation. You can find more details in our overview of data and security practices .
Turning Your WiFi into a Business Growth Engine
Beyond robust security, modern business WiFi solutions can completely transform how you view your network. It ceases to be merely a necessary expense and becomes a powerful engine for growth. Every time a guest or customer connects, the generated data becomes a treasure trove of first-party business intelligence, offering clear insights into how people navigate and interact with your physical spaces.
This is not about analysing abstract data points; it is about understanding real-world behaviour. Think of it as a web analytics platform, but for your physical premises. Instead of tracking clicks and page views, you are measuring footfall, identifying high-traffic zones, and observing how long visitors spend in different areas.
This shift in perspective transforms your WiFi from a passive utility into an active business tool. It informs crucial decisions, helps you create superior customer experiences, and ultimately delivers a tangible return on your investment.

Unlocking Actionable Customer Insights
The true value emerges when you start applying this data to solve specific business challenges. The insights gathered can optimise everything from marketing spend to operational staffing, directly impacting your bottom line.
Here are a few practical examples of how this works in reality:
- Retail Analytics: A shopping mall or retail centre can analyse foot traffic patterns to determine which entrances are most popular and which stores attract the largest crowds. This data can justify premium rents for high-traffic locations and help store managers optimise product placement based on where customers spend the most time.
- Hospitality Engagement: A hotel can easily track guest visit frequency. When a loyal customer who stays several times a year reconnects to the WiFi, the system can automatically send them a personalised "welcome back" email with a voucher for a complimentary beverage, building loyalty and encouraging positive reviews.
- Venue Management: An arena or conference centre can monitor real-time crowd density during an event. This enables operations teams to proactively manage queues at food and beverage counters or redirect foot traffic to less congested areas, significantly improving the visitor experience.
By turning anonymous foot traffic into identifiable behavioural patterns, your WiFi network provides the first-party data needed to make smarter, evidence-based decisions about your physical environment and customer engagement strategies.
Integrating WiFi Data with Your Marketing Stack
This data becomes exponentially more powerful when it does not exist in a silo. Modern WiFi platforms are designed to integrate directly with your existing business systems, particularly your Customer Relationship Management (CRM) platform.
This integration allows you to enrich customer profiles with real-world behavioural data. For instance, when a customer logs into your guest WiFi, their visit information can be automatically appended to their profile in your CRM.
Powering Personalised Marketing Journeys
Once this integration is established, you can build highly effective, automated marketing campaigns based on physical presence. This is where your business WiFi solution truly proves its worth as a revenue generator.
Consider these scenarios:
- Re-engagement Campaigns: If a regular customer has not visited your restaurant in over 60 days, the system can automatically send them a "we miss you" offer with a discount on their next meal.
- Loyalty Programme Growth: You can utilise the WiFi login page to promote your loyalty programme. The system can even identify frequent visitors who are not yet members and present them with a targeted sign-up incentive the next time they connect.
- Post-Visit Feedback: Shortly after a guest departs from your hotel, an automated email can be sent requesting a review while their experience is still fresh, helping to boost your online ratings.
By linking digital marketing efforts to physical presence, you close the loop between online engagement and offline behaviour. Your WiFi transitions from being a mere cost centre to an indispensable tool for driving customer loyalty and increasing revenue.
How Different Industries Use Business WiFi Solutions
The true potential of a modern business WiFi solution lies not just in the technology itself, but in its application. The requirements of a hotel chain are vastly different from those of a hospital, and different again from a bustling retail park. Understanding these industry-specific use cases is key to unlocking its true value and addressing real-world business challenges.
This flexibility is especially important in the UK, which has made significant strides in its digital backbone. By 2025, an impressive 63% of small and mid-sized businesses will have access to full-fibre broadband. With gigabit coverage now reaching 86% of all premises, the foundation is set for businesses of all types to deliver a standout WiFi experience. You can read more about the UK's business broadband transformation and what it means for the future.
Let us examine how different sectors are deploying these solutions.
Hospitality: Crafting a Seamless Guest Journey
For hotels, resorts, and restaurants, the guest experience is paramount. Nothing diminishes a visitor’s impression faster than a cumbersome, frustrating WiFi login process. The objective is not just connectivity; it is an invisible connection that simply works, every single time.
This is where technologies like OpenRoaming and Passpoint truly excel. A guest authenticates their device once, and on every subsequent visit—or even at another venue within the same network—they are reconnected automatically and securely. No more cumbersome Captive Portals or forgotten passwords.
This creates a premium, hassle-free experience that genuinely fosters loyalty. It also relieves staff from the burden of troubleshooting WiFi issues, allowing them to focus on what they do best: delivering exceptional service.
Retail: Unlocking In-Store Analytics and Personalisation
In the highly competitive retail sector, understanding your customer is critical. Modern WiFi analytics can transform a shopping mall or high street store into a treasure trove of first-party data. By analysing footfall patterns, retailers can gain a deep understanding of shopper behaviour.
- Dwell Time Analysis: Identify which displays or departments capture customers' attention the longest, helping to optimise product placement.
- Pathing Data: Visualise the most popular routes shoppers take through a store to inform layout modifications and strategic placement of key promotions.
- Visit Frequency: Identify loyal, repeat customers and use their WiFi connection as a trigger to deliver personalised offers or loyalty rewards directly to their devices.
This type of data finally bridges the gap between online marketing campaigns and actual in-store activity, demonstrating the real-world impact of your initiatives.
Healthcare: Ensuring Secure and Segmented Access
Hospitals and clinics handle highly sensitive patient data, making network security not just a feature, but an absolute necessity. A robust business WiFi solution is vital for maintaining compliance and protecting patient confidentiality. The key is network segmentation: creating separate, firewalled networks for different user groups.
In a healthcare environment, network segmentation is not merely a best practice; it is a critical safety measure. It ensures that a patient streaming video in the waiting room is on a network completely isolated from the one transmitting critical medical data or being used by doctors to access patient records.
This approach delivers distinct, secure environments for all stakeholders:
- Staff Access: Secure, certificate-based authentication for doctors and nurses, providing them with reliable access to internal systems on their mobile devices.
- Patient and Guest Access: An easy-to-use, isolated network for patients and visitors that keeps their traffic completely segregated from clinical operations.
- Medical Device Network: A dedicated, highly secure network for essential IoT devices such as infusion pumps and heart monitors, ensuring they remain protected and fully operational.
Multi-Tenant Housing: Simplifying Private Networks
For residential buildings, student accommodations, or serviced offices, the primary challenge is delivering a home-like WiFi experience at an enterprise scale. Every resident requires their own private, secure network where their devices can communicate with each other—but remain invisible to their neighbours.
Modern solutions resolve this challenge by creating a personal area network (PAN) for each apartment or unit. This allows a tenant to cast a show from their smartphone to their smart TV just as they would at home, all while being managed from a single, centralised platform. It simplifies operations for property managers while providing residents with the privacy and performance they expect.
Your Checklist for Choosing and Deploying a WiFi Solution
Transitioning to a modern WiFi infrastructure is a significant undertaking, not merely a quick hardware replacement. A successful deployment relies on meticulous planning, from assessing your current setup to measuring the final outcomes. This checklist provides a clear, step-by-step guide to help you select and deploy the right business WiFi solution for your organisation.
Consider it akin to designing a new public transport system. You would not simply lay down tracks at random. First, you would map out where people are, their destinations, and the busiest transit hubs. Similarly, an effective WiFi deployment begins with a comprehensive understanding of your physical space and your users' actual requirements.
Phase 1: Auditing Your Current Network
Before you can build for the future, you need a clear picture of your current state. This initial phase is focused on discovery, regardless of whether your existing hardware is from vendors like Meraki , Aruba , or UniFi .
- Conduct a Site Survey: Map out your physical premises. The objective is to identify potential dead zones, locate areas of signal interference (such as thick concrete walls or heavy machinery), and pinpoint high-density zones where large numbers of users will congregate.
- Inventory Existing Hardware: Compile a list of all your current access points, switches, and routers. Note their age, capabilities (e.g., WiFi 5 vs. WiFi 6), and any known performance issues.
- Analyse Current Usage: Examine your existing network data. How many devices are connecting? What types of devices are they—laptops, smartphones, IoT gadgets? When are your peak usage times? This baseline data is absolutely critical for capacity planning.
Phase 2: Defining Your Access Policies
Once you have assessed your current infrastructure, it is time to establish the operational guidelines. One of the most significant advantages of modern business WiFi solutions is the ability to create specific access policies for different user groups, ensuring security while delivering an excellent user experience.
You will need to define clear policies for three primary groups:
- Staff Access: Will employees connect using their corporate login credentials via SSO? This is the zero-trust gold standard, linking network access directly to their verified identity.
- Guest Access: How will visitors connect to the internet? A seamless, password-free option like OpenRoaming or a simple email login is ideal. It provides a positive first impression and allows you to capture data for your marketing initiatives.
- Device Access (IoT): How will you securely connect devices that lack a user interface, such as printers, sensors, or smart TVs? An Identity Pre-Shared Key (iPSK) approach is perfect for managing these "headless" devices without compromising security.
Your access policies form the foundation of your network's security and usability. By segmenting users and devices into distinct groups from the outset, you ensure everyone receives the access they require without inadvertently exposing sensitive corporate information.
Phase 3: Evaluating and Measuring Success
With your requirements finalised, you can begin evaluating vendors and, crucially, determine how you will measure success. Key Performance Indicators (KPIs) provide concrete data to demonstrate the return on your investment. Use the table below to track performance metrics before and after implementing your new system.
Key Performance Indicators for Evaluating Business WiFi
Use these KPIs to measure the success and effectiveness of your business WiFi solution across technical performance, user experience, and business impact.
By following this structured approach—auditing your setup, defining your policies, and measuring the outcomes—you can confidently select and implement a business WiFi solution that not only meets your technical requirements but also delivers tangible, measurable value from day one.
Your Questions Answered: Business Wi-Fi Solutions
Transitioning to modern connectivity naturally raises a few practical questions. Here are clear, straightforward answers to the most common queries we receive about deploying advanced business Wi-Fi solutions.
How Difficult Is It to Transition to Passwordless?
Transitioning from a traditional password system to a modern, passwordless solution is significantly more straightforward than you might expect, particularly with today's cloud platforms. You can dismiss the notion of a complete hardware rip-and-replace.
Instead, solutions like Purple are designed to function as an authentication layer that sits directly on top of your existing network. It integrates seamlessly with hardware from major providers such as Meraki , Aruba , and UniFi . The primary task involves configuring the platform to communicate with your access points and connecting it to your identity provider, such as Entra ID. Because it is a cloud-based solution, you can bypass the complexities of setting up on-premise RADIUS servers, which dramatically simplifies the entire process.
What is the Actual Difference Between Guest and Staff Wi-Fi?
The fundamental difference boils down to trust and access privileges, viewed through the lens of zero-trust security. Guest Wi-Fi is completely isolated from your internal corporate network. A visitor connects using a public method, such as OpenRoaming or a simple email verification, and is only granted access to the internet.
Staff Wi-Fi, conversely, is entirely identity-driven. An employee connects using their verified corporate credentials, often via certificate-based SSO. This process confirms their identity and role, granting them secure, encrypted access exclusively to the internal resources they are authorised to use.
In summary: guests receive a secure, firewalled connection to the internet. Staff receive verified, role-based access to the tools required for their roles, with permissions that can be revoked instantly if their status changes in the corporate directory.
Can We Actually Measure the ROI of a New Wi-Fi Solution?
Absolutely. One of the most significant advantages of a modern business Wi-Fi solution is the ability to directly link connectivity data to business outcomes, which is how you measure its return on investment (ROI). This transforms Wi-Fi from a simple utility expense into a measurable business asset.
For example, a retail centre can track increases in footfall and dwell times, then correlate that data with sales figures. A hotel can monitor how many guests who enjoyed a seamless Wi-Fi experience return for another stay. By integrating Wi-Fi analytics into your CRM, you can directly attribute loyalty programme sign-ups or successful marketing campaigns back to the Wi-Fi onboarding experience.
Ready to transform your network from a cost centre into a strategic asset? Purple delivers secure, passwordless access for guests and staff, integrates with your existing hardware, and provides the analytics required to prove your ROI. Discover the Purple platform today.







