Aruba ClearPass vs Cisco ISE: NAC Platform Comparison
This technical reference guide provides a detailed, vendor-neutral comparison of Aruba ClearPass and Cisco ISE. It equips network architects and IT managers with actionable insights into architecture, deployment complexity, licensing, and integration ecosystems to drive informed NAC platform decisions.
🎧 Listen to this Guide
View Transcript

Executive Summary
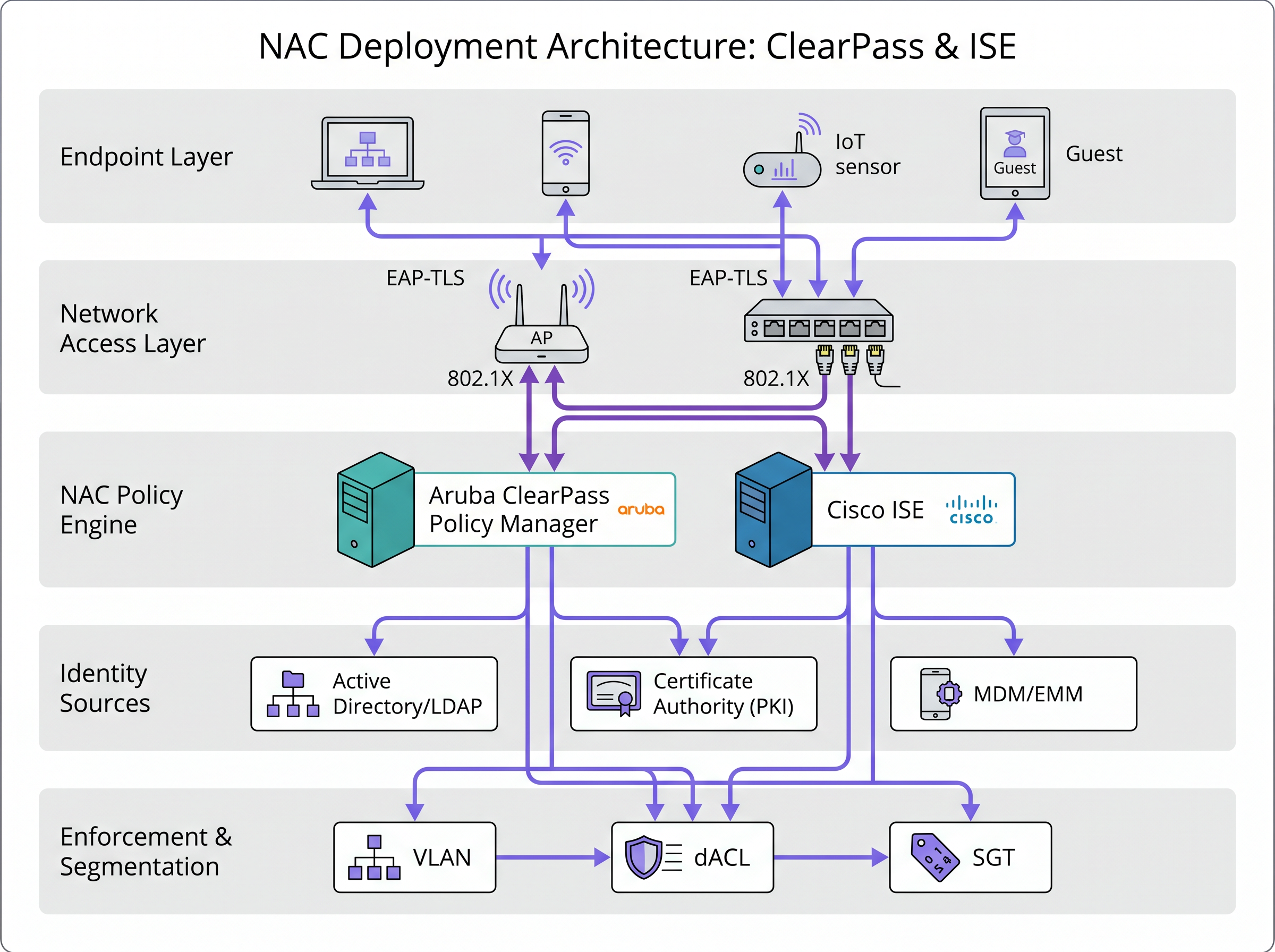
For enterprise network architects and CTOs evaluating Network Access Control (NAC) platforms, the choice often narrows down to two dominant forces: Aruba ClearPass and Cisco Identity Services Engine (ISE). Both platforms provide robust authentication, authorization, and accounting (AAA) capabilities, ensuring that every endpoint—from corporate laptops to headless IoT sensors—is securely profiled and segmented before gaining network access. However, their architectural philosophies differ significantly. Cisco ISE is deeply embedded within the Cisco ecosystem, leveraging proprietary protocols like pxGrid and TrustSec to deliver unparalleled micro-segmentation in homogeneous environments. Conversely, Aruba ClearPass is designed from the ground up as a vendor-agnostic policy engine, utilizing open standards like RADIUS and REST APIs to seamlessly integrate across multi-vendor networks. This guide provides a pragmatic, deep-dive comparison of both platforms, exploring their features, deployment complexities, and licensing models to help you align your NAC strategy with your organization's operational realities and compliance requirements.
Technical Deep-Dive
Architecture and Ecosystem Integration
The fundamental divergence between ClearPass and ISE lies in their approach to ecosystem integration. Cisco ISE thrives in a Cisco-centric environment. It utilizes Security Group Tags (SGTs) within the Cisco TrustSec framework to enforce granular, scalable access control across Catalyst switches, Meraki access points, and Firepower firewalls without relying solely on traditional IP-based Access Control Lists (ACLs). The pxGrid (Platform Exchange Grid) protocol further enhances this by enabling ISE to share rich contextual data with third-party security solutions, creating a cohesive, automated threat response ecosystem.
Aruba ClearPass, in contrast, embraces a heterogeneous network philosophy. It acts as a universal translator, applying consistent policies across Aruba, Cisco, Juniper, and Palo Alto hardware using standard RADIUS and TACACS+ protocols. Its robust REST API and broad integration ecosystem allow it to ingest context from Mobile Device Management (MDM) platforms, firewalls, and endpoint security agents effortlessly. For venues with mixed hardware deployments, ClearPass often presents a lower barrier to entry for unified policy enforcement.
Policy Engine and Management Interface
Policy creation in ClearPass is highly visual and service-oriented. Administrators define a 'Service' (e.g., 'Corporate 802.1X') and sequentially stack authentication methods, authorization sources, and enforcement profiles. This top-down, modular approach is intuitive and simplifies troubleshooting.
Cisco ISE utilizes a rule-based matrix, akin to configuring a sophisticated firewall. Policies are constructed using complex, multi-condition rules that evaluate identity, posture, and context simultaneously. While this offers immense flexibility and power for intricate enterprise scenarios, it demands a steeper learning curve and meticulous configuration management to avoid unintended consequences.
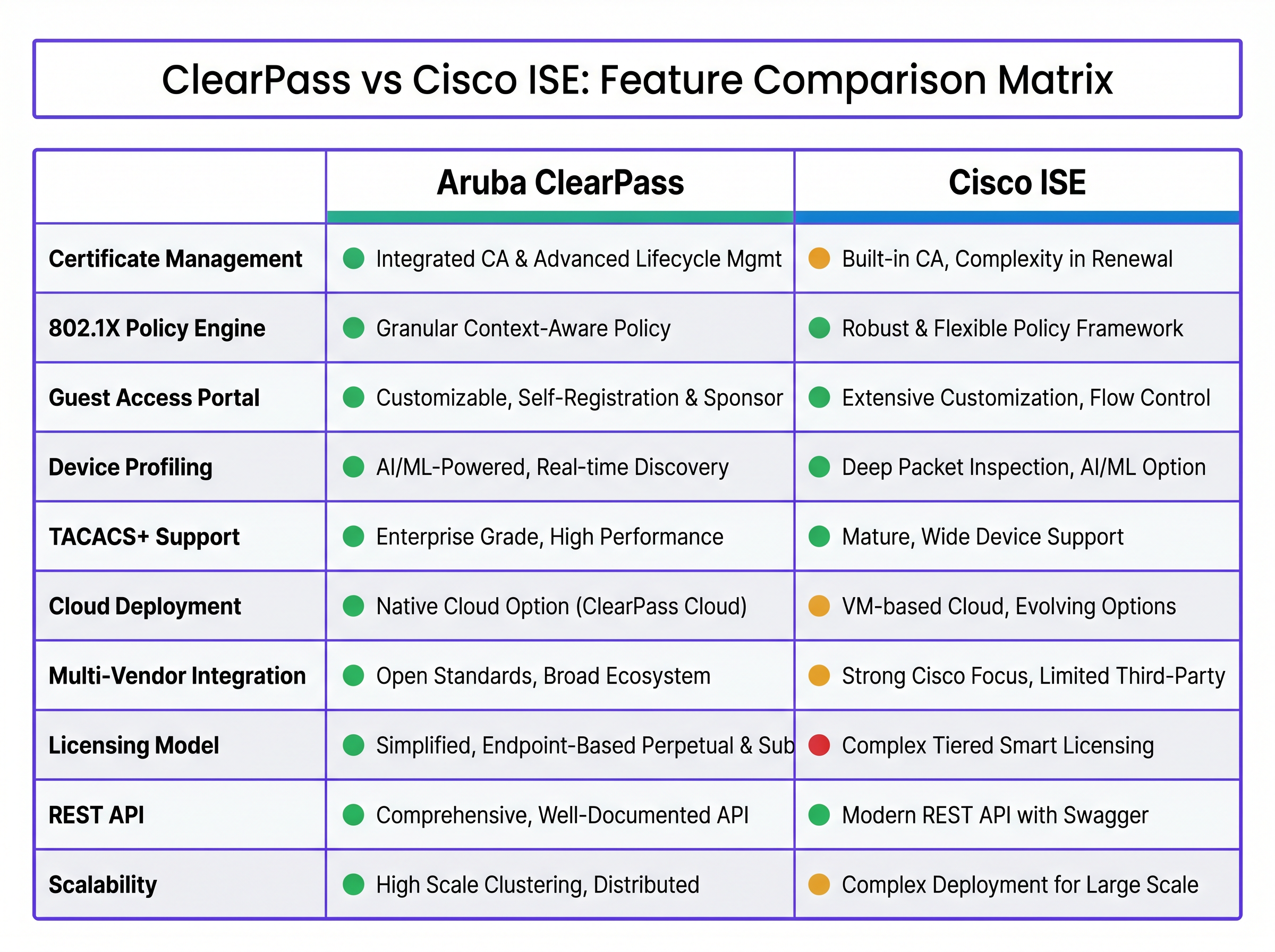
Device Profiling and Visibility
Accurate device profiling is critical for modern NAC, especially with the proliferation of IoT devices. Both platforms excel here, utilizing DHCP, HTTP, MAC OUI, and SNMP data. ISE holds an advantage in Cisco environments through Device Sensor, which feeds deep packet inspection data directly from Cisco switches to the ISE node. ClearPass counters this with ClearPass Device Insight, an AI-powered, cloud-based solution that leverages machine learning to identify obscure or spoofed devices that evade standard profiling signatures.
Implementation Guide
Deploying a NAC platform is a high-stakes operation. A misconfiguration can lock legitimate users out of the network, crippling business operations.
- Start with Visibility (Monitor Mode): Never deploy enforcement on day one. Configure the NAC to profile devices and log authentication requests without blocking traffic. This provides a clear picture of what is actually on your network and helps identify devices that will fail 802.1X authentication.
- Enforce Wireless First: Wireless networks are generally easier to secure because devices are accustomed to authenticating (e.g., WPA3-Enterprise). Begin with corporate laptops managed by Active Directory or an MDM, as these can easily receive the necessary certificates.
- Tackle the Wired Network: Wired 802.1X is notoriously difficult due to legacy printers, unmanaged IoT devices, and 'dumb' switches. Use MAC Authentication Bypass (MAB) for devices that cannot support 802.1X, but strictly limit their network access using dynamic VLAN assignment or dACLs.
- Implement Guest Access: For hospitality and retail environments, guest access is a primary concern. ClearPass Guest offers a highly customizable portal with self-registration and sponsor approval, integrating smoothly with platforms like Guest WiFi for advanced analytics. ISE also provides robust guest capabilities but may require more effort to achieve a highly branded experience.
Best Practices
- Maintain Directory Hygiene: A NAC is only as effective as the identity store it queries. Ensure your Active Directory or LDAP is clean, accurate, and up-to-date.
- Leverage Certificates: Avoid password-based authentication (PEAP-MSCHAPv2) wherever possible. Deploy EAP-TLS using certificates issued by a trusted Certificate Authority (CA) for superior security and seamless user experience.
- Plan for High Availability: NAC is a critical infrastructure component. Deploy redundant nodes in a distributed architecture to ensure continuous network access during maintenance or failures.
Troubleshooting & Risk Mitigation
Common failure modes often revolve around certificate expiration, incorrect policy ordering, or misconfigured switch ports.
- Certificate Expiration: Implement automated certificate renewal processes (e.g., SCEP/EST) to prevent sudden, widespread authentication failures.
- Policy Ordering: In both ClearPass and ISE, policies are evaluated top-down. Ensure more specific rules are placed above general catch-all rules to prevent unintended access.
- Rogue APs: Ensure your wireless intrusion prevention system (WIPS) is actively monitoring for impersonation attacks. Refer to our guide on Rogue AP Detection: Protecting Venue WiFi from Impersonation Attacks for detailed strategies.
ROI & Business Impact
The financial impact of a NAC deployment extends beyond the initial software and hardware costs.
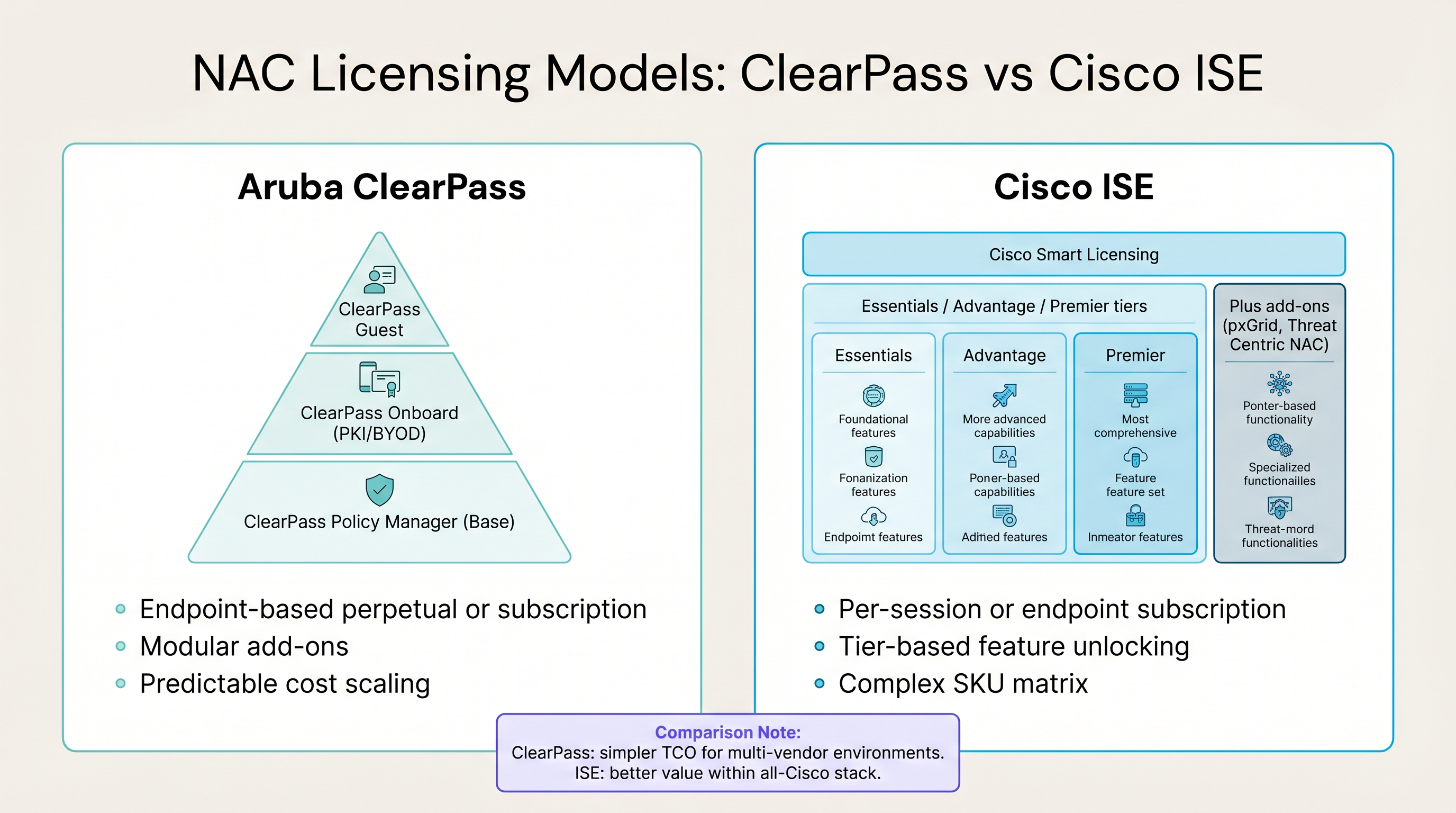
- Aruba ClearPass: Offers a predictable, endpoint-based licensing model (perpetual or subscription) with modular add-ons for Guest and Onboard. This simplicity often translates to a lower Total Cost of Ownership (TCO) in multi-vendor environments.
- Cisco ISE: Utilizes a complex Smart Licensing model with Essentials, Advantage, and Premier tiers. While potentially more expensive, it delivers exceptional ROI if you are fully leveraging the advanced capabilities of a unified Cisco security architecture.
Ultimately, a successful NAC deployment mitigates the risk of costly data breaches, ensures compliance with standards like PCI DSS and GDPR, and reduces the operational overhead of manual network provisioning.
Key Terms & Definitions
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for secure enterprise network access, preventing unauthorized devices from communicating on the network.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The primary protocol used by both ClearPass and ISE to communicate with network switches and access points.
TACACS+ (Terminal Access Controller Access-Control System Plus)
A Cisco-developed protocol that provides access control for routers, network access servers, and other networked computing devices via one or more centralized servers.
Used primarily for device administration (authenticating IT staff logging into switches and routers), separating authentication from authorization.
MAC Authentication Bypass (MAB)
A method of authenticating devices that do not support 802.1X (like printers or legacy IoT devices) by using their MAC address as the identity credential.
A necessary workaround for headless devices, though inherently less secure than 802.1X as MAC addresses can be spoofed.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An EAP method that relies on client and server certificates for mutual authentication.
Considered the gold standard for wireless and wired security, providing robust protection against credential theft.
TrustSec
A Cisco security architecture that uses Security Group Tags (SGTs) to enforce access control policies based on endpoint identity and context, rather than IP addresses.
A key differentiator for Cisco ISE in homogeneous Cisco environments, enabling scalable micro-segmentation.
pxGrid (Platform Exchange Grid)
A Cisco protocol that enables security platforms to share context and automate threat responses across the network infrastructure.
Allows ISE to act as a central intelligence hub, sharing user and device context with firewalls and endpoint security tools.
Device Profiling
The process of identifying the type, operating system, and capabilities of a device connecting to the network using various data sources (DHCP, HTTP, SNMP).
Essential for applying appropriate security policies to IoT and unmanaged devices that cannot authenticate via 802.1X.
Case Studies
A large university campus with a mix of Aruba wireless controllers and legacy Juniper access switches needs to implement role-based access control for students, faculty, and IoT devices (projectors, smart locks). They currently use Active Directory for identity.
Given the multi-vendor environment, Aruba ClearPass is the recommended solution. The deployment would begin in monitor mode to profile the diverse range of IoT devices. Faculty and student laptops would be onboarded using ClearPass Onboard to provision EAP-TLS certificates, ensuring secure, password-less authentication. The legacy Juniper switches would be configured to use RADIUS for 802.1X authentication, with MAC Authentication Bypass (MAB) configured for the IoT devices. ClearPass policies would dynamically assign VLANs based on the user's AD group (Student vs. Faculty) or the device profile (IoT).
A global retail chain is standardizing its entire network infrastructure on Cisco Meraki (APs, switches, and MX security appliances). They need to enforce strict micro-segmentation to isolate point-of-sale (POS) terminals from the guest WiFi network and corporate devices to maintain PCI DSS compliance.
Cisco ISE is the optimal choice for this homogeneous Cisco environment. The deployment would leverage Cisco TrustSec to assign Security Group Tags (SGTs) to different endpoints. POS terminals would receive a specific SGT upon authentication (via MAB or 802.1X). ISE would then push Security Group Access Control Lists (SGACLs) to the Meraki switches and MX appliances, explicitly denying traffic between the POS SGT and the Guest or Corporate SGTs, regardless of the underlying IP addressing or VLAN structure.
Scenario Analysis
Q1. A hospital network requires strict isolation between medical devices (infusion pumps, patient monitors) and the guest WiFi network. The infrastructure consists of Aruba wireless access points and Cisco Catalyst switches. Which NAC platform is best suited for this environment and why?
💡 Hint:Consider the multi-vendor nature of the network infrastructure.
Show Recommended Approach
Aruba ClearPass is the recommended platform. While Cisco ISE is powerful, its advanced segmentation features (TrustSec/SGTs) require end-to-end Cisco hardware to function optimally. ClearPass can effectively manage policies across both Aruba APs and Cisco switches using standard RADIUS attributes to dynamically assign VLANs or dACLs, ensuring the medical devices are securely isolated from guest traffic.
Q2. Your organization is migrating from a password-based PEAP-MSCHAPv2 wireless network to a certificate-based EAP-TLS deployment to improve security. You have a large BYOD (Bring Your Own Device) population. What is a critical feature you need from your NAC platform to support this transition?
💡 Hint:Think about how certificates will be delivered to unmanaged personal devices.
Show Recommended Approach
You need a robust onboarding and certificate provisioning portal. In the Aruba ecosystem, this is ClearPass Onboard; in Cisco, it's the ISE BYOD portal. This feature allows users to self-provision their personal devices by connecting to an open provisioning network, authenticating with their corporate credentials, and automatically downloading and installing the required EAP-TLS certificate and network profile, minimizing helpdesk overhead.
Q3. During a phased NAC rollout, you configure a switch port for 802.1X enforcement. A user connects a legacy printer that does not support 802.1X. What mechanism should the NAC platform use to authenticate this device, and what is the primary security risk associated with it?
💡 Hint:How do you identify a device that cannot provide a username or certificate?
Show Recommended Approach
The NAC platform should use MAC Authentication Bypass (MAB). The switch sends the printer's MAC address to the NAC server as the username and password. The primary security risk is MAC spoofing; an attacker can easily discover the printer's MAC address, clone it to their laptop, and gain unauthorized access to the network segment assigned to the printer. Therefore, MAB must be combined with strict profiling and network segmentation (e.g., placing printers in a highly restricted VLAN).
Key Takeaways
- ✓ClearPass excels in multi-vendor environments using open standards (RADIUS, REST APIs).
- ✓Cisco ISE provides unmatched micro-segmentation (TrustSec) in homogeneous Cisco networks.
- ✓Never deploy a NAC in enforcement mode on day one; always start with monitor mode to gain visibility.
- ✓Prioritize certificate-based authentication (EAP-TLS) over password-based methods for enhanced security.
- ✓ClearPass offers a simpler, predictable licensing model, while ISE uses a complex, tiered Smart Licensing approach.
- ✓Both platforms provide robust device profiling, but ClearPass Device Insight offers advanced AI-powered identification for obscure IoT devices.



