Age Verification on Guest WiFi: Compliance for Gaming, Alcohol, and Adult Venues
This authoritative technical reference guide explores the implementation of age verification on guest WiFi networks for high-risk venues like casinos, bars, and stadiums. It details compliance strategies, architectural deployment models, and the balance between regulatory requirements and user onboarding friction.

Executive Summary
For IT leaders and network architects managing Hospitality and entertainment venues, providing public internet access is no longer a simple matter of broadcasting an SSID. Venues that serve alcohol, offer gaming, or restrict entry by age face stringent regulatory scrutiny. Providing unfiltered, unverified Guest WiFi access in these environments can lead to licensing violations, substantial fines, and reputational damage.
This guide outlines the technical strategies for implementing compliant age verification at the captive portal layer. It moves beyond basic Terms of Service (ToS) checkboxes to explore robust authentication workflows, including declared age gates, third-party identity API integrations, and ID document verification. By leveraging platforms like Purple, which supports custom sign-up fields and age gates, venues can enforce compliance without needlessly degrading the guest onboarding experience or running afoul of data privacy frameworks like GDPR.
Technical Deep-Dive: Verification Architectures
Implementing an age check on guest WiFi requires intercepting the user's initial connection attempt and forcing an authentication flow before granting full network access. This is fundamentally a captive portal operation, often relying on RADIUS (Remote Authentication Dial-In User Service) for policy enforcement.
The Walled Garden Challenge
The most critical technical hurdle in advanced age verification is the "Walled Garden." When a user connects to the SSID, their device is in a pre-authenticated state. They cannot access the broader internet. However, if your age verification method relies on an external API (such as an identity verification service or an OAuth provider), the wireless controller or access point must be explicitly configured to permit traffic to those specific IP addresses or domains before the user is authenticated.
Failure to accurately configure the Walled Garden results in the captive portal splash page loading, but the verification script timing out, effectively bricking the onboarding process.
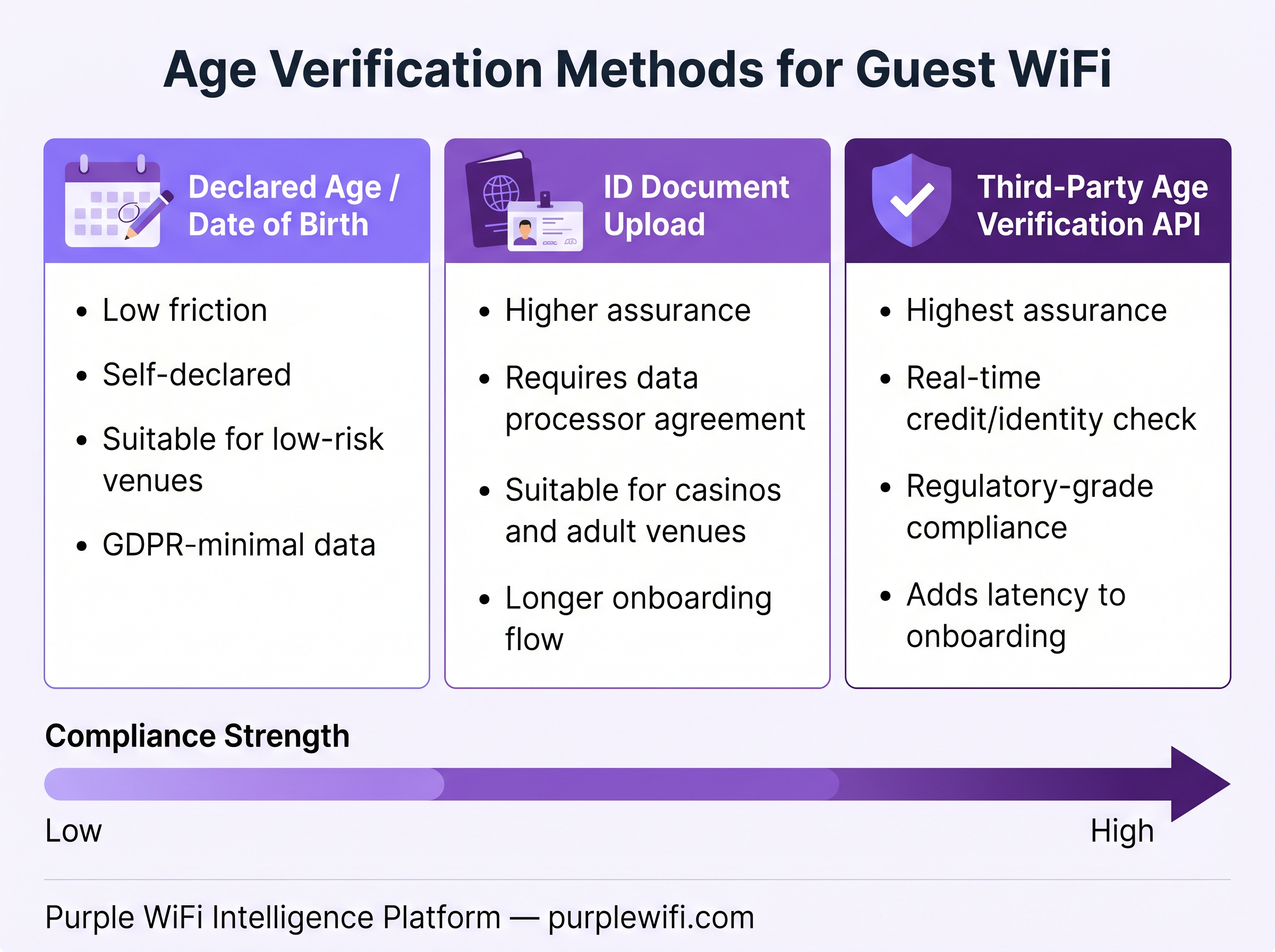
Verification Tiers
Venue operators must select a verification tier commensurate with their regulatory risk profile.
Tier 1: Declared Age (Low Friction, Low Assurance) The simplest method involves asking the user to self-declare their age or date of birth on the splash page. This data is captured via custom fields in the captive portal and stored in the user profile, such as within the WiFi Analytics dashboard. While easy to deploy, it relies entirely on user honesty and is easily bypassed. It is suitable primarily for low-risk environments where the goal is basic policy acknowledgement rather than strict enforcement.
Tier 2: Third-Party API Verification (Medium Friction, High Assurance) This approach integrates the captive portal with an external identity provider. The user inputs basic details (name, address, phone number), and the portal makes a real-time API call to verify this data against credit reference agencies or mobile network operators. If the API returns a positive age verification, the RADIUS server receives an Access-Accept message. This method offers robust compliance but requires careful Walled Garden configuration and may incur per-transaction costs.
Tier 3: Document Upload & Biometrics (High Friction, Highest Assurance) Reserved for the highest-risk venues, such as casinos or adult-only resorts, this method requires the user to upload a photo of a government-issued ID and often a live selfie. The captive portal passes these assets to a specialized verification service which uses Optical Character Recognition (OCR) and facial matching to confirm identity and age. This introduces significant onboarding latency and complex data privacy considerations.
Implementation Guide: Best Practices
Deploying age verification requires a careful balance between security and user experience.
- Assess Regulatory Requirements: Do not over-engineer the solution. If local licensing only requires a "21+ to enter" sign at the door, a Tier 3 ID upload for WiFi access is likely disproportionate and will severely impact adoption rates.
- Optimize the Walled Garden: Maintain an up-to-date list of required domains for your chosen verification API. Ensure your network hardware supports domain-based Walled Garden entries, as IP addresses for cloud services change frequently.
- Implement MAC Randomization Strategies: Modern mobile operating systems randomize MAC addresses to prevent tracking. If your system relies on remembering a device's MAC address to bypass the age gate on subsequent visits, users will face constant re-verification. Tie verification status to a more persistent identifier, such as a user account or loyalty app integration, where possible.
- Enforce Data Minimization: When using API or ID upload methods, configure the integration to only return and store a boolean value (
is_over_18 = true). Never store copies of identity documents or full credit profiles on your local RADIUS servers or captive portal databases. This is a fundamental principle of GDPR compliance.

Troubleshooting & Risk Mitigation
Even with a perfect architecture, operational issues will arise. Network engineers must be prepared to troubleshoot the onboarding flow.
- Captive Portal Not Triggering: This is often caused by incorrect DNS interception or overly permissive Walled Garden rules that allow devices to reach connectivity check URLs (like
captive.apple.com) without interception. - Verification API Timeouts: Verify the Walled Garden configuration. Use packet captures on the wireless controller to confirm that DNS requests for the API endpoint are resolving and that HTTPS traffic is permitted.
- High Drop-off Rates: If analytics show users abandoning the process at the age gate, the friction is too high. Consider simplifying the form, improving the UI, or re-evaluating if a lower tier of verification is legally acceptable.
By carefully selecting the appropriate verification tier and meticulously configuring the network infrastructure, IT teams can ensure their venues remain compliant while still providing a valuable guest service.
Podcast Briefing
Listen to our 10-minute technical briefing on implementing age verification on guest WiFi:
Key Terms & Definitions
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
This is the primary interface where age verification workflows are presented to the user.
Walled Garden
A restricted environment that controls the user's access to web content and services, typically allowing access only to specific approved domains before full authentication.
Crucial for allowing pre-authenticated devices to reach third-party identity verification APIs.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The backend system that ultimately grants or denies network access based on the result of the age verification process.
MAC Randomization
A privacy feature in modern operating systems that periodically changes the device's MAC address to prevent tracking across different networks.
Complicates the ability to 'remember' a user's age verification status across multiple visits based solely on their device hardware address.
Data Minimization
A principle in privacy law (like GDPR) stating that data controllers should limit the collection of personal information to what is directly relevant and necessary to accomplish a specified purpose.
Dictates that venues should not store ID documents or detailed personal profiles if a simple 'verified' token is sufficient.
OAuth
An open standard for access delegation, commonly used as a way for Internet users to grant websites or applications access to their information on other websites but without giving them the passwords.
Often used in social login flows, which can sometimes provide age data if the user's profile includes a verified date of birth.
VLAN Assignment
The process of dynamically placing a user's device onto a specific Virtual Local Area Network based on their authentication status or profile.
Used to segregate users who fail age verification onto a restricted network segment with aggressive content filtering.
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or inappropriate content.
A necessary secondary control layer; even if a user passes an age gate, the network should still block illegal or highly inappropriate content to protect the venue's liability.
Case Studies
A large regional casino is upgrading its network infrastructure. The compliance team mandates that all guest WiFi users must be verified as 21 or older due to online gambling regulations. They want to implement an ID document upload flow. How should the network architect design the Walled Garden and data flow to ensure compliance without violating privacy laws?
The architect must configure the wireless controller's Walled Garden to permit HTTPS traffic to the specific domains of the chosen identity verification API (e.g., api.verifyservice.com). The captive portal must be designed to securely capture the ID image and transmit it directly to the API, without storing it locally. The API response must be configured to return only a boolean token indicating 'age verified' or 'age not verified'. The RADIUS server should then authorize the session based on this token, logging only the transaction ID and the boolean result, ensuring no PII is retained on the venue's infrastructure.
A family-friendly restaurant chain that serves alcohol wants to offer free WiFi but needs to ensure they are not liable for minors accessing restricted content. They want a low-friction solution. What is the recommended deployment?
The recommended approach is a Tier 1 Declared Age gate combined with robust DNS-based content filtering. The captive portal should require users to enter their Date of Birth. If the calculated age is under the legal limit, the RADIUS server assigns the user to a highly restrictive VLAN or applies a specific filtering policy that blocks adult content and gambling sites. If over the limit, a standard filtering policy is applied.
Scenario Analysis
Q1. A stadium IT director notices a 40% drop-off rate at the captive portal since implementing a new age verification flow that requires users to scan their driver's license. The legal team only requires users to acknowledge they are over 18 to access the network. What is the most appropriate technical recommendation?
💡 Hint:Consider the balance between compliance requirements and onboarding friction.
Show Recommended Approach
The current implementation is over-engineered for the legal requirement, causing unnecessary friction. The recommendation is to downgrade the verification method to a Tier 1 'Declared Age' gate (e.g., a simple checkbox or Date of Birth field). This meets the legal team's requirement for acknowledgement while significantly reducing the barrier to entry, which should improve connection rates.
Q2. During testing of a new third-party API age verification integration, the captive portal loads correctly on a mobile device, but when the user submits their details, the page spins indefinitely and eventually times out. What is the most likely configuration error?
💡 Hint:Think about the state of the user's network access before they are fully authenticated.
Show Recommended Approach
The most likely issue is an incomplete or incorrect Walled Garden configuration on the wireless controller. The device is in a pre-authenticated state and is attempting to reach the third-party API to verify the details. If the API's domain or IP addresses are not explicitly allowed in the Walled Garden, the traffic is blocked by the controller, causing the script to time out.
Q3. A venue wants to implement a system where users only have to verify their age once, and the network will 'remember' them for all future visits. They plan to use the device MAC address as the unique identifier in their database. Why is this approach fundamentally flawed in modern deployments?
💡 Hint:Consider privacy features implemented by modern mobile operating systems (iOS and Android).
Show Recommended Approach
This approach will fail because modern mobile operating systems employ MAC randomization. By default, devices present a different, randomized MAC address to different networks, and often change this address periodically even on the same network. The venue's database will not recognize the returning device, forcing the user to re-verify their age on subsequent visits.
Key Takeaways
- ✓Providing unfiltered guest WiFi in age-restricted venues exposes operators to significant regulatory and licensing risks.
- ✓Age verification methods range from low-friction self-declaration to high-assurance ID document uploads.
- ✓The Walled Garden must be meticulously configured to allow pre-authentication traffic to third-party verification APIs.
- ✓Data minimization is critical; systems should store verification tokens (booleans), not sensitive PII or ID images.
- ✓MAC randomization prevents reliable device-based tracking, necessitating account-based verification for persistent access.
- ✓Venues must balance strict compliance enforcement with the need for a smooth guest onboarding experience.



