ISO 27001 Guest WiFi: A Compliance Primer
This authoritative technical reference maps guest WiFi deployments directly to ISO 27001:2022 controls, detailing network segregation, logging, and risk treatment requirements. It provides actionable guidance for IT managers and network architects on generating audit-ready evidence and leveraging vendor SOC 2 attestations to satisfy ISMS supplier assurance mandates.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Mapping ISO 27001 Controls to WiFi Architecture
- Network Segregation and Security (Controls A.8.20 & A.8.22)
- Supplier Assurance and Cloud Platforms (Control A.8.21)
- Logging, Filtering, and Information Transfer (Controls A.8.15, A.8.23, A.5.14)
- Implementation Guide: Building the Audit Evidence Pack
- Step 1: Formalise the Risk Assessment
- Step 2: Export Configurations as Evidence
- Step 3: Establish the Supplier Review Cadence
- Best Practices for Enterprise Venues
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Audio Briefing

Executive Summary
For enterprise venues—whether a 500-room hotel, a multi-site retail chain, or a 50,000-seat stadium—guest WiFi is rarely treated with the same governance rigour as the corporate LAN. However, under ISO 27001:2022, a public-facing wireless network is a live information asset that intersects your network boundary, supplier relationships, and legal obligations. This primer translates the theoretical requirements of an Information Security Management System (ISMS) into practical engineering and compliance outcomes for Guest WiFi deployments.
By treating the guest network not as a commodity service but as an audited segment, IT leaders can mitigate lateral movement risks, ensure regulatory compliance, and produce definitive evidence for lead auditors. This guide details the specific Annex A controls applicable to wireless deployments, outlines the required risk assessment methodology, and explains how to build a defensible audit evidence pack—saving hundreds of hours during certification cycles.
Technical Deep-Dive: Mapping ISO 27001 Controls to WiFi Architecture
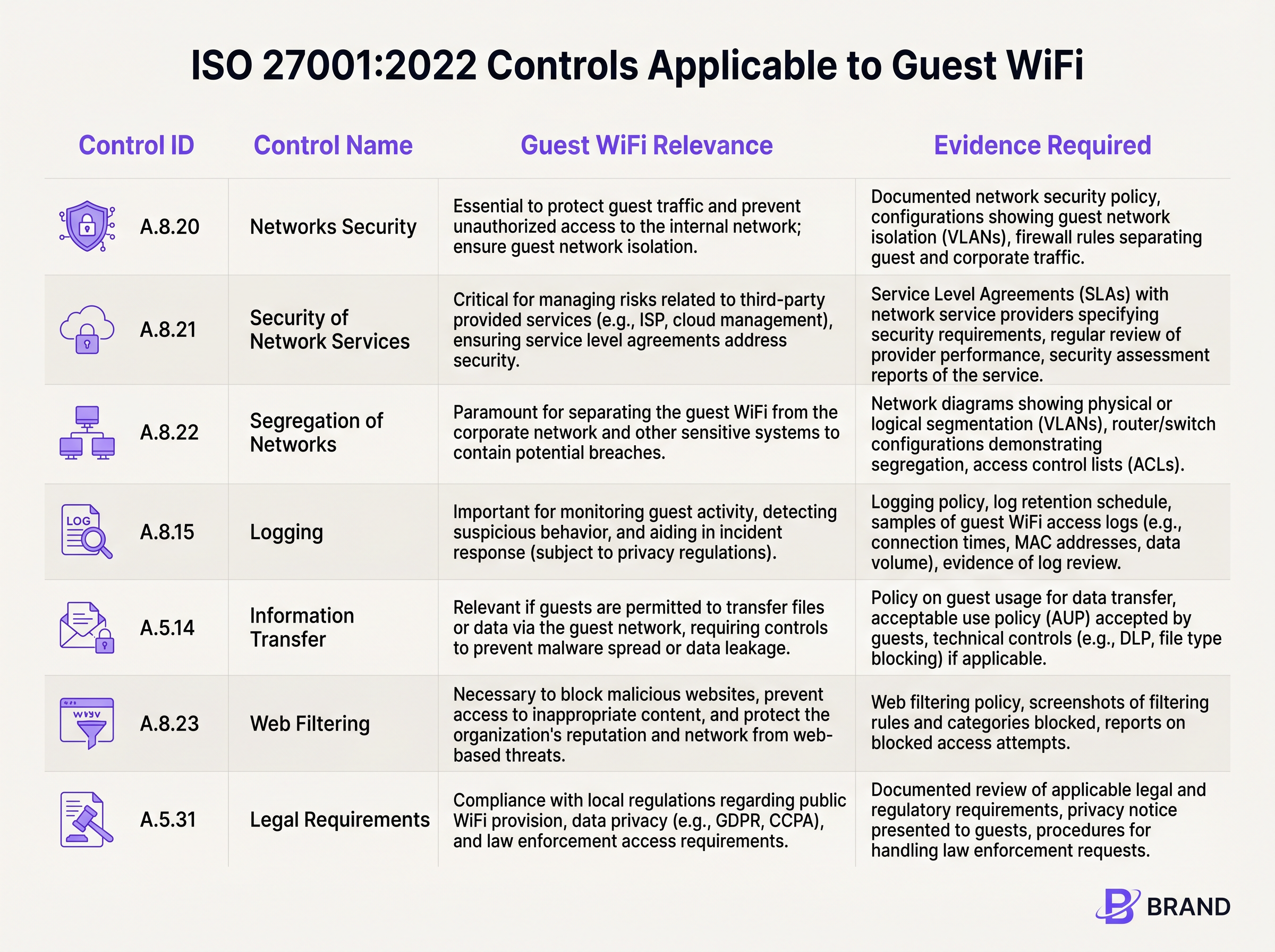
ISO 27001:2022 restructured its Annex A controls into four themes. For guest wireless networks, the critical requirements reside primarily within the Technological and Organisational domains. Understanding how these controls translate into network configurations is the foundation of compliance.
Network Segregation and Security (Controls A.8.20 & A.8.22)
The foundational requirement for any guest network is strict isolation. Control A.8.22 (Segregation of Networks) mandates that groups of information services be segregated. In practical terms, this requires deploying dedicated VLANs for guest traffic that are logically (and where necessary, physically) separated from corporate subnets, point-of-sale (POS) systems, and building management IoT devices.
Coupled with Control A.8.20 (Networks Security), this isolation must be enforced via robust firewall rulesets and Access Control Lists (ACLs). An auditor will expect to see configurations that explicitly deny routing from the guest VLAN to any internal RFC 1918 IP space. If a penetration tester on the guest SSID can reach the management interface of a Sensors gateway or a corporate file share, it constitutes a major nonconformity.
Supplier Assurance and Cloud Platforms (Control A.8.21)
Modern guest WiFi relies heavily on managed service providers and cloud-hosted captive portals. Control A.8.21 (Security of Network Services) dictates that these supplier relationships must be governed by security requirements. This is where vendor attestations become critical. Instead of conducting a bespoke audit of a cloud WiFi platform, organisations should rely on the vendor's SOC 2 Type II report. Platforms like Purple carry SOC 2 alignment, providing independent assurance over their security, availability, and privacy controls. This documentation feeds directly into your ISMS supplier assurance file.
Logging, Filtering, and Information Transfer (Controls A.8.15, A.8.23, A.5.14)
Visibility and control over guest traffic are mandated by several overlapping controls. Control A.8.15 (Logging) requires the retention of connection events and authentication logs. However, this must be balanced against data minimisation principles. The captive portal serves as the primary mechanism for Control A.5.14 (Information Transfer), where guests must accept an Acceptable Use Policy (AUP) before access is granted.
Furthermore, Control A.8.23 (Web Filtering) necessitates the deployment of DNS-based filtering or cloud proxies to block malicious domains and command-and-control infrastructure, protecting both the network's reputation and the devices connected to it.
Implementation Guide: Building the Audit Evidence Pack
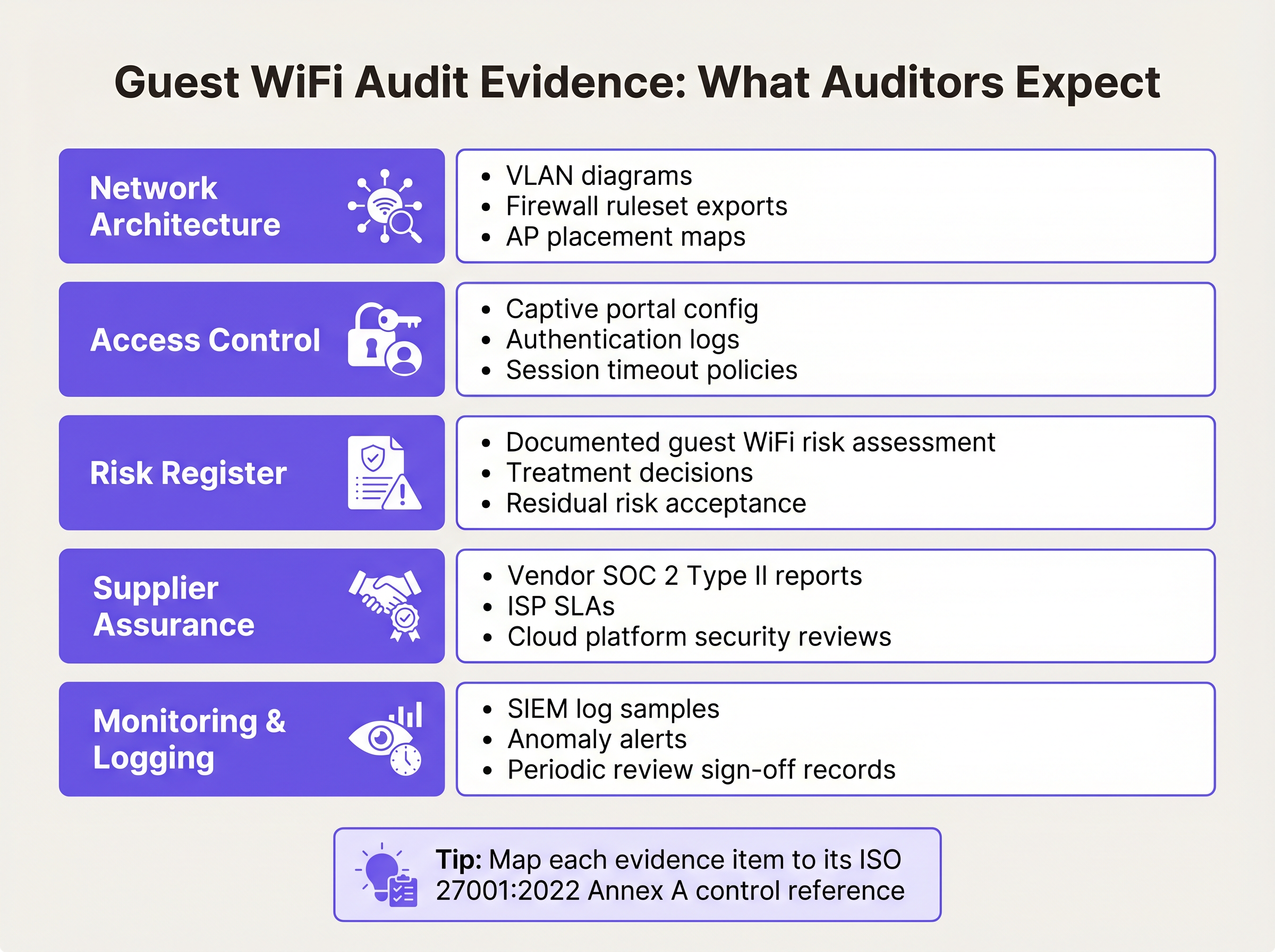
Implementing the technology is only half the battle; proving it to an auditor is the other. The following steps outline how to translate technical configurations into a defensible ISO 27001 evidence pack.
Step 1: Formalise the Risk Assessment
The ISMS must include a formal risk assessment specifically for the guest WiFi asset. This should document threats such as unauthorised lateral movement, malware propagation, and bandwidth exhaustion. For each threat, document the likelihood, impact, and the chosen risk treatment (e.g., mitigate via VLAN isolation and client isolation). The Statement of Applicability (SoA) must reference this assessment as the justification for selecting controls like A.8.22 and A.8.23.
Step 2: Export Configurations as Evidence
Auditors require point-in-time evidence of configurations. Generate a comprehensive network diagram clearly labelling the guest VLAN and its boundaries. Export the firewall ruleset demonstrating the explicit deny rules for internal routing. If you are using a cloud platform, export the captive portal configuration showing the mandatory AUP acceptance checkpoint. For guidance on balancing user experience with these security checkpoints, review our guide on Guest WiFi Session Timeouts: Balancing UX and Security .
Step 3: Establish the Supplier Review Cadence
Supplier assurance is not a one-time activity. Establish a calendar for annual reviews of your ISP and cloud portal providers. Request their updated SOC 2 Type II reports and document a formal management review of these reports. If the vendor's audit highlights any exceptions, document how those exceptions impact your own risk posture.
Best Practices for Enterprise Venues
Deploying compliant guest WiFi across complex environments like Hospitality or Transport hubs requires adherence to vendor-neutral best practices that satisfy both security and operational demands.
- Enforce Client Isolation: At the access point level, enable client isolation (sometimes called AP isolation or guest mode). This prevents devices connected to the same SSID from communicating directly with each other, mitigating peer-to-peer attacks and malware propagation.
- Implement Robust Session Management: Configure forced session timeouts that require re-authentication. For a retail environment, a 12-hour timeout may be appropriate; for an airport, a 4-hour timeout ensures abandoned sessions are terminated. This limits the window of opportunity for hijacked MAC addresses.
- Align with Data Privacy Regulations: Ensure your captive portal data collection aligns with local privacy laws (e.g., GDPR). Only collect data necessary for the service or for which you have explicit, documented consent. This directly supports Control A.5.31 (Legal Requirements).
Troubleshooting & Risk Mitigation
Even with a robust architecture, compliance drift can occur. The most common failure mode is 'scope creep'—where the guest network is either entirely excluded from the ISMS scope (leading to audit failures) or over-scoped (applying unnecessary internal controls to guest devices).
Another frequent issue is the degradation of network segmentation. Firmware updates or emergency network changes can inadvertently alter VLAN routing. To mitigate this, implement automated configuration monitoring or schedule quarterly manual reviews of the firewall ruleset governing the guest segment. If you are managing multiple distributed sites, consider the compliance advantages of modern wide-area networking; our overview of The Core SD WAN Benefits for Modern Businesses explores how centralised policy enforcement reduces audit complexity.
ROI & Business Impact
Investing in ISO 27001 compliance for guest WiFi delivers measurable business value beyond merely passing an audit. A secure, compliant wireless infrastructure protects the venue's brand reputation by preventing the network from being used as a staging ground for cybercrime.
Furthermore, by leveraging a SOC 2-aligned platform that integrates WiFi Analytics , venues can safely extract commercial value from footfall data while maintaining strict adherence to data privacy and security controls. The reduction in audit preparation time—often saving dozens of engineering hours annually by relying on exportable platform evidence—provides a direct operational ROI.
Audio Briefing
For a detailed walkthrough of these concepts, listen to our 10-minute technical briefing podcast:
Key Terms & Definitions
VLAN Segregation
The logical separation of a physical network into distinct broadcast domains, preventing traffic from one segment from reaching another without passing through a routed firewall.
Critical for satisfying ISO 27001 Control A.8.22, ensuring guest devices cannot access corporate or operational technology systems.
Client Isolation
A wireless network setting that prevents devices connected to the same Access Point or SSID from communicating directly with one another.
Used to mitigate peer-to-peer attacks and malware spread on public networks, supporting Control A.8.20.
SOC 2 Type II
An independent audit report that evaluates a service organisation's controls related to security, availability, and privacy over a specified period (usually 6-12 months).
The primary evidence used by IT teams to satisfy Control A.8.21 (Security of Network Services) for cloud-hosted WiFi platforms.
Statement of Applicability (SoA)
A mandatory ISO 27001 document that lists all Annex A controls, stating whether each is applied or excluded, along with the justification.
The SoA must explicitly reference the guest WiFi risk assessment to justify the inclusion of network segregation and filtering controls.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
Serves as the technical enforcement point for Acceptable Use Policies and privacy consent, generating the logs required for Control A.8.15.
Acceptable Use Policy (AUP)
A set of rules applied by the owner of a network that restrict the ways in which the network may be used.
Required evidence for Control A.5.14, demonstrating that guests have been informed of their obligations before transferring data.
WPA3-Personal (SAE)
The modern wireless security protocol that uses Simultaneous Authentication of Equals to provide forward secrecy, protecting session traffic even if the shared password is known.
The recommended security standard for shared-passphrase guest networks to ensure baseline encryption of the wireless medium.
Risk Treatment
The process of selecting and implementing measures to modify risk, typically categorised as mitigate, accept, transfer, or avoid.
IT managers must document how they treat the risks associated with guest WiFi (e.g., mitigating lateral movement via firewalls) within the ISMS.
Case Studies
A 400-room hotel group needs to deploy guest WiFi across three properties. The IT Director wants to keep the guest network out of the ISO 27001 ISMS scope to save time. Is this permissible, and what are the architectural requirements if it is included?
Excluding the guest network from the ISMS scope is highly risky if the physical infrastructure (switches, APs, internet circuits) is shared with the corporate network, or if guest authentication captures personal data (bringing it under A.5.31 Legal Requirements). The correct approach is to include it in scope but apply proportionate controls. Architecturally, the hotel must implement strict VLAN segregation (Control A.8.22), apply client isolation at the AP level, and route guest traffic directly to the internet via a firewall that explicitly denies access to the hotel's property management system (PMS) and corporate subnets.
During an internal audit of a retail chain's WiFi, the auditor notes that the cloud-based captive portal provider has not been assessed for security in over two years. How should the network architect remediate this nonconformity against Control A.8.21?
The architect must immediately request the latest SOC 2 Type II report from the captive portal provider. Upon receipt, the architect should formally review the report, noting the auditor's opinion and any exceptions listed in the Trust Services Criteria. This review must be documented, signed off by management, and filed in the ISMS supplier assurance repository. A recurring calendar event should be established to request this report annually.
Scenario Analysis
Q1. You are preparing for an ISO 27001 surveillance audit. The auditor asks for evidence that the guest WiFi network is secure from internal threats. What three specific artifacts should you provide?
💡 Hint:Think about architecture, policy enforcement, and supplier management.
Show Recommended Approach
- A network diagram and firewall ruleset proving VLAN segregation (Control A.8.22). 2) Captive portal logs showing guests accepting the Acceptable Use Policy (Control A.5.14). 3) The latest SOC 2 Type II report from your cloud WiFi platform provider (Control A.8.21).
Q2. A stadium operations director wants to disable the captive portal to 'speed up entry' and just use an open network with no terms of service. As the Information Security Manager, how do you respond using ISO 27001 principles?
💡 Hint:Consider the legal and logging implications of an unmanaged open network.
Show Recommended Approach
You must advise against this, as it violates Control A.5.14 (Information Transfer) by removing the Acceptable Use Policy checkpoint, and compromises Control A.8.15 (Logging) by removing the ability to tie sessions to an authentication event. Furthermore, it increases the venue's legal exposure under Control A.5.31 if the network is used for illicit purposes without a documented terms of service.
Q3. Your guest WiFi risk assessment identifies 'Access to malicious websites' as a high risk. You decide to implement DNS filtering. How do you document this in the ISMS?
💡 Hint:Link the threat to the specific Annex A control and the SoA.
Show Recommended Approach
Update the Risk Register to show the threat is treated by implementing DNS filtering. In the Statement of Applicability (SoA), mark Control A.8.23 (Web Filtering) as 'Applicable', citing the risk assessment as the justification, and reference the DNS filtering configuration as the implementation evidence.
Key Takeaways
- ✓Guest WiFi is a live information asset that must be included in your ISMS scope and risk assessment.
- ✓Control A.8.22 demands strict VLAN segregation and firewall rules to isolate guest traffic from corporate networks.
- ✓Control A.8.21 requires you to govern third-party WiFi platforms; rely on their SOC 2 Type II reports for audit evidence.
- ✓The captive portal is essential for fulfilling legal (A.5.31) and information transfer (A.5.14) controls by enforcing AUP acceptance.
- ✓Audit preparation involves exporting configurations (firewall rules, AP settings) to prove point-in-time compliance.



