SMS vs Email Verification for Guest WiFi: Which to Choose
A comprehensive, data-driven technical comparison of SMS and Email verification methods for guest WiFi captive portals, covering conversion rates, architecture, per-verification costs, compliance requirements, and venue-specific deployment recommendations. Essential reading for IT managers, network architects, and venue operations directors designing or optimising guest WiFi sign-up flows.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Performance
- SMS Verification Architecture
- Email Verification Architecture
- Implementation Guide: Venue-Specific Deployment Recommendations
- High-Density, Transient Venues (Stadiums, Transport Hubs, Retail Concourses)
- Low-Footfall, High-Dwell Venues (Hotels, Conference Centres, Corporate Campuses)
- Dual-Method Deployment (Best Practice for All Venues)
- Best Practices and Compliance
- Troubleshooting and Risk Mitigation
- ROI and Business Impact

Executive Summary
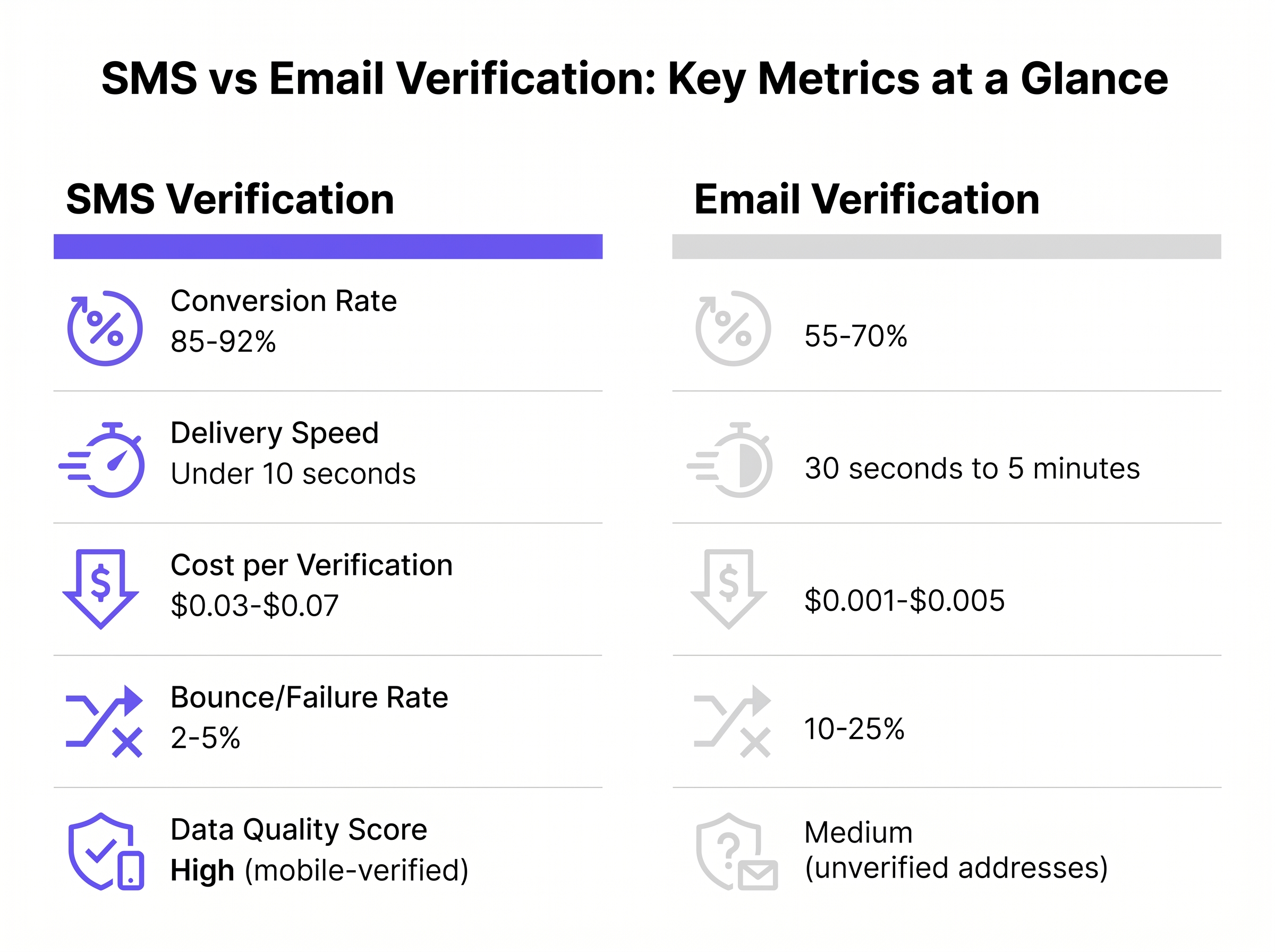
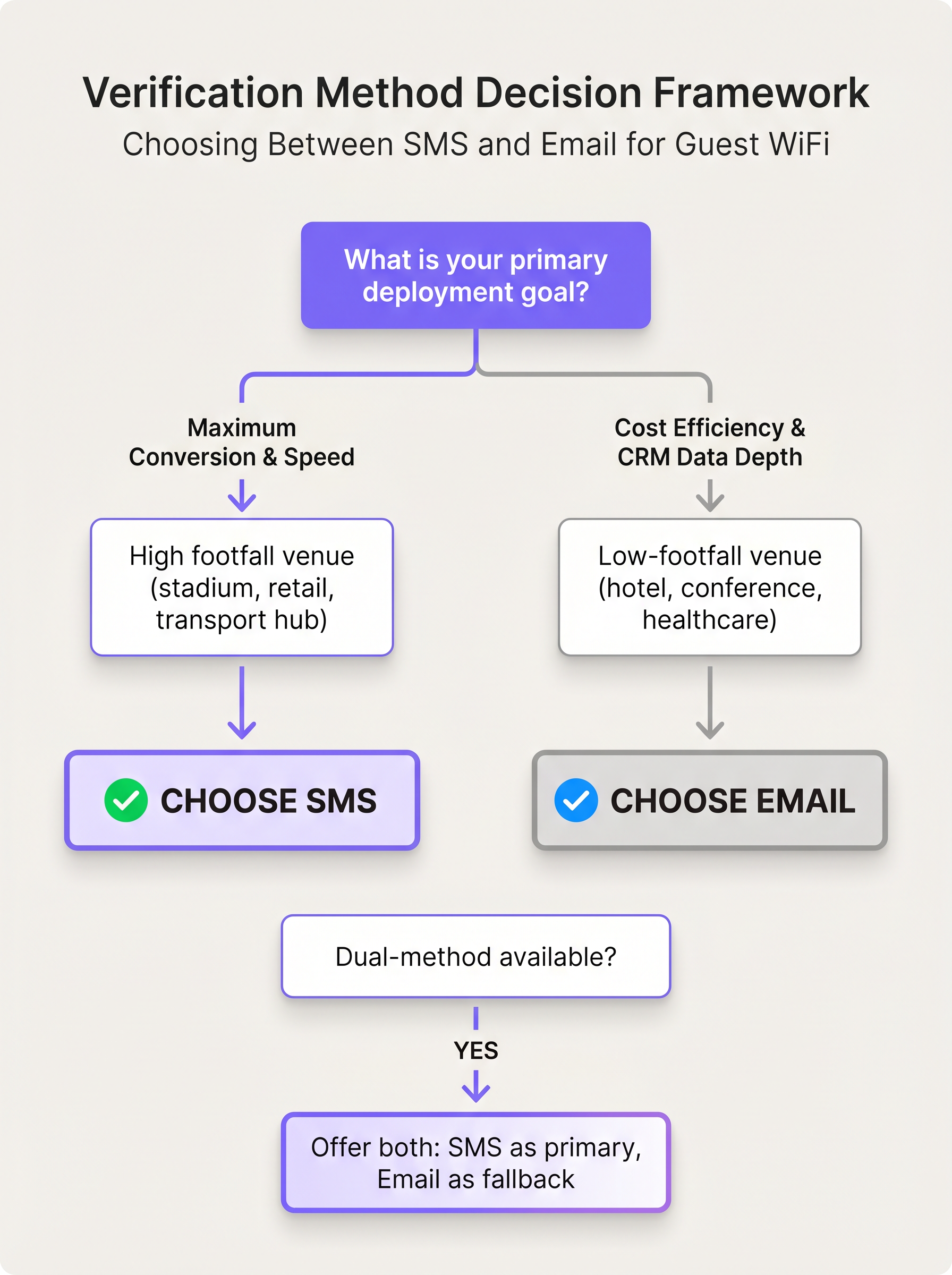
For IT managers, network architects, and venue operations directors, selecting the right authentication method for Guest WiFi is a critical balance of user experience, data quality, and operational cost. This guide provides a data-driven comparison of SMS and Email verification methods for captive portals. While SMS delivers superior conversion rates (85–92%) and speed in high-footfall environments, it carries a distinct per-message cost. Conversely, email verification offers significant cost efficiencies and deeper CRM integration potential, making it ideal for venues prioritising long-term engagement over rapid throughput. By understanding the technical trade-offs, compliance requirements, and real-world deployment scenarios across Retail , Hospitality , and public venues, technical leaders can architect a sign-up flow that maximises ROI while mitigating friction.
Listen to the Purple Technical Briefing on this topic:
Technical Deep-Dive: Architecture and Performance
The underlying architecture of your chosen verification method directly impacts network performance, user conversion, and backend data quality. Understanding these mechanics is essential before committing to a deployment strategy.
SMS Verification Architecture
SMS verification relies on an out-of-band authentication flow. When a user enters their mobile number into the captive portal splash screen, the system triggers an API call to an SMS gateway provider (such as Twilio, AWS SNS, or Vonage), which dispatches a One-Time Password (OTP) to the device via the cellular network. The critical advantage is that modern iOS and Android operating systems natively intercept incoming OTPs and offer to autofill them directly into the browser field, eliminating the need for the user to switch applications.
| Metric | SMS Verification |
|---|---|
| Delivery Speed | Under 10 seconds |
| Conversion Rate | 85–92% |
| Cost per Verification | $0.03–$0.07 |
| Bounce / Failure Rate | 2–5% |
| Data Quality | High (mobile-verified) |
The primary technical constraint with WiFi SMS verification is the reliance on cellular coverage. In environments with poor indoor cellular reception — subterranean Retail spaces, heavily shielded hospital wards, or basement conference suites — SMS delivery will fail, stranding the user at the captive portal. Furthermore, international deployments require robust phone number validation logic on the portal to ensure correct country codes are applied before the API call is dispatched, as a malformed number will result in a silent failure.
Email Verification Architecture
Email verification typically employs either a magic link or a numeric OTP delivered via SMTP to the user's provided address. The user must navigate away from the captive portal splash screen, open their email client, retrieve the code or click the link, and return to the portal to complete authentication. This multi-step, multi-application workflow is the primary source of friction.
| Metric | Email Verification |
|---|---|
| Delivery Speed | 30 seconds to 5 minutes |
| Conversion Rate | 55–70% |
| Cost per Verification | $0.001–$0.005 |
| Bounce / Failure Rate | 10–25% |
| Data Quality | Medium (unverified addresses common) |
A critical architectural dependency for email verification is the Walled Garden (implemented via pre-authentication ACLs on the network controller). This configuration grants the client device limited internet access — specifically to reach common email providers such as Gmail, Outlook, and Apple Mail — before full network access is granted. Misconfiguration of these Walled Garden rules is the single most common cause of email verification failure in production deployments.
Implementation Guide: Venue-Specific Deployment Recommendations
Deploying the optimal verification method requires aligning the technology with the specific operational realities of the venue. The following guidance is vendor-neutral and applicable across major network controller platforms.
High-Density, Transient Venues (Stadiums, Transport Hubs, Retail Concourses)
In environments like a stadium concourse or an airport terminal, throughput is the critical metric. Users require immediate access, and the average connection duration is short. Every second spent on the captive portal is a second of potential abandonment.
Recommendation: Deploy SMS verification as the primary method, with Email as a mandatory fallback.
The sub-10-second completion time minimises dwell time on the captive portal, reducing the load on the DHCP server and RADIUS infrastructure. The higher per-verification cost is justified by the successful onboarding of a significantly larger percentage of users — a direct input into WiFi Analytics and real-time crowd flow monitoring. For more on designing networks for these environments, refer to the guide on High-Density WiFi Design: Stadium and Arena Best Practices .
Low-Footfall, High-Dwell Venues (Hotels, Conference Centres, Corporate Campuses)
In a Hospitality setting, the guest relationship is persistent — often spanning several days — and the WiFi sign-up is frequently tied to a loyalty programme or property management system (PMS).
Recommendation: Deploy Email verification, integrated directly with the PMS or CRM via API.
The cost savings over thousands of extended guest stays are substantial. More critically, an email address is the primary unique identifier for most hotel loyalty programmes, making it the most commercially valuable data point to capture at the point of onboarding. The slower delivery speed is acceptable in this context, as guests are typically settled in their room or at a table, not rushing through a concourse.
Dual-Method Deployment (Best Practice for All Venues)
The optimal architecture for any venue is to offer both methods simultaneously, presenting SMS as the primary option and Email as the fallback. This approach maximises accessibility across user demographics and mitigates the failure modes of each individual method.
Best Practices and Compliance
Regardless of the method chosen, adherence to data privacy regulations and security standards is non-negotiable.
GDPR and CCPA Compliance: The acceptance of network Terms and Conditions must be logically and visually separated from the opt-in for marketing communications. Forcing marketing consent as a condition of WiFi access violates GDPR Article 7 principles on freely given consent. Both the phone number and email address collected constitute personal data under GDPR and must be handled accordingly, including documented lawful bases for processing and clear data retention policies.
Walled Garden Maintenance: If utilising email verification, Walled Garden IP and domain lists must be continuously reviewed. Major email providers regularly update their CDN infrastructure, and a stale Walled Garden configuration will silently break email delivery for a subset of users.
Addressing MAC Randomization: Modern mobile operating systems employ MAC address randomization to protect user privacy. Both SMS and Email verification directly mitigate the impact of this on WiFi Analytics by tying the session to a verified, persistent identity — a phone number or email address — rather than a rotating hardware address. For venue operators relying on footfall analytics, this is a compelling operational argument for requiring verification rather than offering open access.
Telecom Regulations: SMS verification is subject to carrier-level regulations in many jurisdictions. In the United States, the TCPA governs commercial SMS messaging, and in the UK, the ICO's PECR applies. Ensure that the OTP message template is clearly identified as a transactional (not marketing) message to remain compliant.
Troubleshooting and Risk Mitigation
Failure Mode 1 — SMS Delivery Failure The most common cause is poor indoor cellular coverage or an incorrectly formatted international dialing code. Mitigation requires implementing a dual-method fallback: if the SMS fails to arrive within 30 seconds, the portal should automatically surface the email verification option. The UI must include a prominent, pre-populated country code selector to reduce formatting errors.
Failure Mode 2 — Email Walled Garden Blocking If the captive portal's pre-authentication ACLs do not include the correct IP ranges and domains for the user's email provider, the verification email cannot be retrieved. Mitigation requires regular auditing and testing of Walled Garden configurations, using wildcard domain entries where the network controller supports them to account for CDN changes by email providers.
Failure Mode 3 — Captive Portal Detection Conflict When a user on iOS or Android switches from the captive portal mini-browser to their email app to retrieve an OTP, the OS may interpret the WiFi connection as broken and drop it. This is particularly common with Apple's Captive Network Assistant. The mitigation is to implement a "magic link" approach rather than a numeric OTP for email verification, as the link can be opened directly in the full browser, bypassing the mini-browser session entirely.
ROI and Business Impact
The financial case for each method must be evaluated in the context of the venue's commercial objectives and the WiFi Analytics value generated from the collected data.
Direct Cost Comparison: Email verification costs are negligible — typically fractions of a cent per send. SMS verification carries a hard, per-message cost of $0.03–$0.07. For a venue processing 100,000 authentications per month, SMS could cost up to $7,000 monthly, whereas email would cost under $50. However, the 85–92% SMS conversion rate versus the 55–70% email rate means SMS onboards approximately 30% more users from the same footfall — a significant uplift for analytics and marketing data collection.
Value Creation from Verified Data: The cost of SMS verification must be weighed against the downstream value of the data. Verified mobile numbers enable targeted, location-based SMS marketing campaigns. If a campaign sent to 10,000 verified numbers generates a 3% redemption rate on a $10 offer, the $300–$700 verification cost is recovered with a significant margin. The Heatmap Analysis for Venue Traffic: A Practical Guide demonstrates how verified identity data, combined with WiFi Analytics , can generate actionable insights that directly inform merchandising and staffing decisions.
Strategic Alignment: Ultimately, the choice must align with the broader digital strategy. If the goal is rapid onboarding and real-time Wayfinding or crowd management, SMS is the architecturally superior choice. If the goal is long-term CRM database growth and email marketing, Email verification is the correct deployment decision.
Key Terms & Definitions
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before broader network access is granted. Typically implemented via DNS redirection on the network controller.
The primary interface for Guest WiFi authentication and the point at which the SMS vs Email verification decision is implemented and experienced by the end user.
Walled Garden
A restricted network environment that controls the user's access to internet resources, allowing access to a specific, pre-approved set of IP addresses or domains prior to full network authentication.
Critical for Email verification deployments. Without a correctly configured Walled Garden permitting access to email provider infrastructure, users cannot retrieve the OTP sent to their inbox.
Out-of-Band Authentication
An authentication mechanism that uses a secondary, independent communication channel to verify a user's identity. The verification signal travels via a different network path than the primary access request.
SMS verification is an out-of-band method: the access request is made over WiFi, but the OTP is delivered via the cellular network. This independence provides a meaningful security benefit.
MAC Randomization
A privacy feature in modern mobile operating systems (iOS 14+, Android 10+) that uses a randomized, per-network MAC address when connecting to WiFi networks, rather than the device's permanent hardware MAC address.
Severely impacts device-based analytics and repeat visitor tracking. Requiring SMS or Email verification resolves this by tying the session to a persistent, verified identity.
One-Time Password (OTP)
A password that is valid for only one login session or transaction, generated algorithmically and typically time-limited to a short window (30–300 seconds).
The standard verification token used in both SMS and Email verification flows to confirm the user has access to the provided contact detail.
DHCP Pool Exhaustion
A network state in which the DHCP server has assigned all available IP addresses within its configured scope, preventing new client devices from obtaining an address and connecting to the network.
A significant operational risk in high-density venues. Slow verification methods (e.g., email) that cause clients to hold IP addresses in a pre-authenticated state for extended periods can contribute to pool exhaustion during peak periods.
Pre-Authentication ACL
Access Control Lists applied to a client device's network session before that device has successfully completed the captive portal authentication process.
The technical mechanism used on network controllers (e.g., Cisco, Aruba, Ruckus) to enforce Walled Garden policies, permitting limited access to specific resources before full authentication.
Synthetic Identity
A fabricated or disposable identity, typically constructed using temporary or randomly generated contact details, used to gain access to services without providing genuine personal information.
Email verification is susceptible to synthetic identities via temporary email services (e.g., Mailinator, Guerrilla Mail). SMS verification significantly mitigates this risk, as it requires a physical SIM card.
Case Studies
A 50,000-seat stadium is upgrading its Guest WiFi network ahead of a major international tournament. The marketing team wants to collect verified contact data from every connected fan, but the network operations team is concerned about DHCP pool exhaustion during peak half-time periods if users dwell too long on the captive portal splash screen. Which verification method should they deploy, and how should they configure the fallback?
The stadium should deploy SMS verification as the primary authentication method, configured with a 30-second OTP expiry and an automatic fallback to Email verification if the SMS is not confirmed within that window. The captive portal should present a pre-populated country code selector defaulting to the host nation's dialing code, with an easy mechanism to change it. The Walled Garden must be configured to allow access to major email providers as a fallback. The DHCP lease time should be reviewed and reduced to the minimum viable duration for the expected session length to mitigate pool exhaustion risk.
A national retail chain with 500 locations wants to implement Guest WiFi to track dwell times and repeat visit rates across different stores, feeding data into their existing email marketing platform. They have a limited IT budget and a small central IT team responsible for maintaining all 500 deployments. Which verification method and integration architecture should they adopt?
The retail chain should implement Email verification as the primary method. The captive portal must be configured with a robust, centrally managed Walled Garden template that allows access to major email providers (Gmail, Outlook, Yahoo, Apple Mail) before authentication is complete. The portal should integrate via a webhook or REST API directly with their existing email marketing platform (e.g., Mailchimp, Klaviyo, Salesforce Marketing Cloud) to automatically sync verified addresses and trigger a welcome journey. A centralised network management platform should be used to push Walled Garden configuration updates to all 500 locations simultaneously, reducing the maintenance burden on the central IT team.
Scenario Analysis
Q1. A hospital IT director needs to implement Guest WiFi across five campuses for patients and visitors. The buildings have notoriously poor indoor cellular reception due to reinforced concrete construction and medical equipment shielding. The hospital's marketing team wants to grow their patient communications email list. Which verification strategy should they adopt, and what are the key configuration requirements?
💡 Hint:Consider the physical limitations of the environment and the architectural dependencies of each verification method, as well as the stated business objective.
Show Recommended Approach
The hospital must prioritise Email verification. Because SMS relies on cellular networks to deliver the OTP, poor indoor reception will result in high failure rates and frustrated patients and visitors. Email verification utilises the WiFi network itself (via Walled Garden access) to deliver the OTP, bypassing the cellular reception issue entirely. Key configuration requirements include: (1) a correctly configured Walled Garden permitting access to major email providers, (2) GDPR-compliant separation of network ToS acceptance from marketing opt-in, and (3) API integration with the hospital's CRM to sync verified addresses. The marketing objective of growing the email list is also directly served by this approach.
Q2. You are configuring the Walled Garden for a new Email verification deployment at a conference centre. You have whitelisted the IP ranges for Gmail and Outlook, but users are reporting that after switching to their email app to retrieve the OTP, the captive portal page fails to load when they switch back. What is the most likely cause, and how do you resolve it?
💡 Hint:Think about what happens to a mobile device's WiFi connection state when it switches between applications during the pre-authentication phase, and consider the role of the OS captive portal detection mechanism.
Show Recommended Approach
The most likely cause is the OS-level Captive Network Assistant (CNA) behaviour on iOS or Android. When the user switches away from the CNA mini-browser to their email app, the OS may interpret the WiFi connection as broken or the captive portal as unresponsive, and either drop the WiFi connection or close the CNA session. The resolution is to switch from a numeric OTP to a magic link approach for email verification. A magic link can be opened directly in the device's full browser (not the CNA mini-browser), bypassing the session state issue. Additionally, ensure the Walled Garden is configured to allow the captive portal's own domain to be accessible, so the link resolves correctly when clicked.
Q3. A marketing manager at a retail chain insists on using SMS verification because they heard it has a higher conversion rate. However, their primary campaign objective is to grow a database for a monthly email newsletter. How do you advise them, and what alternative architecture would you propose?
💡 Hint:Align the verification method with the specific type of data required to fulfil the business objective, and consider whether the higher conversion rate of SMS actually serves the stated goal.
Show Recommended Approach
Advise against SMS as the sole method for this specific objective. While SMS has a higher conversion rate, it only directly captures a mobile number. If the business objective is to send a monthly email newsletter, an email address is the required data point. Using SMS as the only method would either require a secondary step to capture the email address (increasing friction and reducing the effective conversion rate), or leave the business without the data it needs. The recommended architecture is Email verification as the primary method, which directly captures the required data point in a single step. If the marketing manager is concerned about conversion rates, a dual-method approach (SMS primary, Email fallback) can be offered, but the Email capture must be a mandatory field in the SMS flow as well.
Key Takeaways
- ✓SMS verification delivers conversion rates of 85-92% and completes in under 10 seconds, making it the optimal choice for high-density, transient venues such as stadiums, transport hubs, and retail concourses.
- ✓Email verification costs a fraction of a cent per send versus $0.03-$0.07 for SMS, making it significantly more cost-effective at scale for venues with high monthly authentication volumes.
- ✓Email verification requires a correctly configured Walled Garden (pre-authentication ACLs) to allow users to access their inbox before full network access is granted — misconfiguration is the leading cause of email verification failure.
- ✓SMS verification is susceptible to failure in environments with poor indoor cellular coverage; always implement Email as a mandatory fallback in any SMS-primary deployment.
- ✓Both methods directly address the analytics disruption caused by MAC address randomization by tying each session to a verified, persistent user identity.
- ✓GDPR and CCPA compliance requires that marketing consent opt-ins are logically and visually separated from the network Terms and Conditions acceptance — this applies equally to both verification methods.
- ✓The optimal architecture for most venues is a dual-method deployment: SMS as the primary option for speed and conversion, Email as the fallback for accessibility and cost control.



