WiFi-Datenerfassung: Ein umfassender Leitfaden zu Datenschutz, Compliance und Best Practices
This guide provides IT leaders with a comprehensive technical reference for implementing WiFi data capture solutions. It focuses on navigating the complex landscape of privacy, legal compliance (GDPR, CCPA), and data ethics, offering actionable best practices for venue operators in hospitality, retail, and large public spaces.
🎧 Listen to this Guide
View Transcript

Executive Summary
Für moderne Unternehmen ist das Verständnis des physischen Raums ebenso entscheidend wie das des digitalen. Die WiFi-Datenerfassung hat sich als leistungsstarkes Instrument für Standortbetreiber etabliert, um tiefe, umsetzbare Einblicke in Besucherverhalten, Kundenfrequenz und Raumnutzung zu gewinnen. Durch die Analyse von Probe-Requests, die passiv von WiFi-fähigen Geräten gesendet werden, können Unternehmen transformative Erkenntnisse gewinnen, um Layouts zu optimieren, das Kundenerlebnis zu verbessern und die betriebliche Effizienz zu steigern. Diese Fähigkeit geht jedoch mit erheblichen rechtlichen und ethischen Verpflichtungen einher. Aufsichtsbehörden weltweit stufen unter Rahmenwerken wie der GDPR und dem CCPA Gerätekennungen wie MAC-Adressen als personenbezogene Daten ein. Folglich unterliegen deren Erfassung und Verarbeitung strengen Regeln hinsichtlich Einwilligung, Anonymisierung und Data Governance. Dieser Leitfaden dient als praktische, maßgebliche Referenz für CTOs, IT-Manager und Netzwerkarchitekten. Er geht über akademische Theorie hinaus und bietet herstellerneutrale, einsatzbereite Strategien für die Implementierung eines WiFi-Analyseprogramms, das nicht nur leistungsstark, sondern auch sicher, konform und respektvoll gegenüber der Privatsphäre der Nutzer ist. Wir beleuchten die technische Architektur, skizzieren robuste Implementierungsmethoden und liefern klare, umsetzbare Best Practices, um Risiken zu minimieren und den ROI zu maximieren.
Technischer Deep-Dive
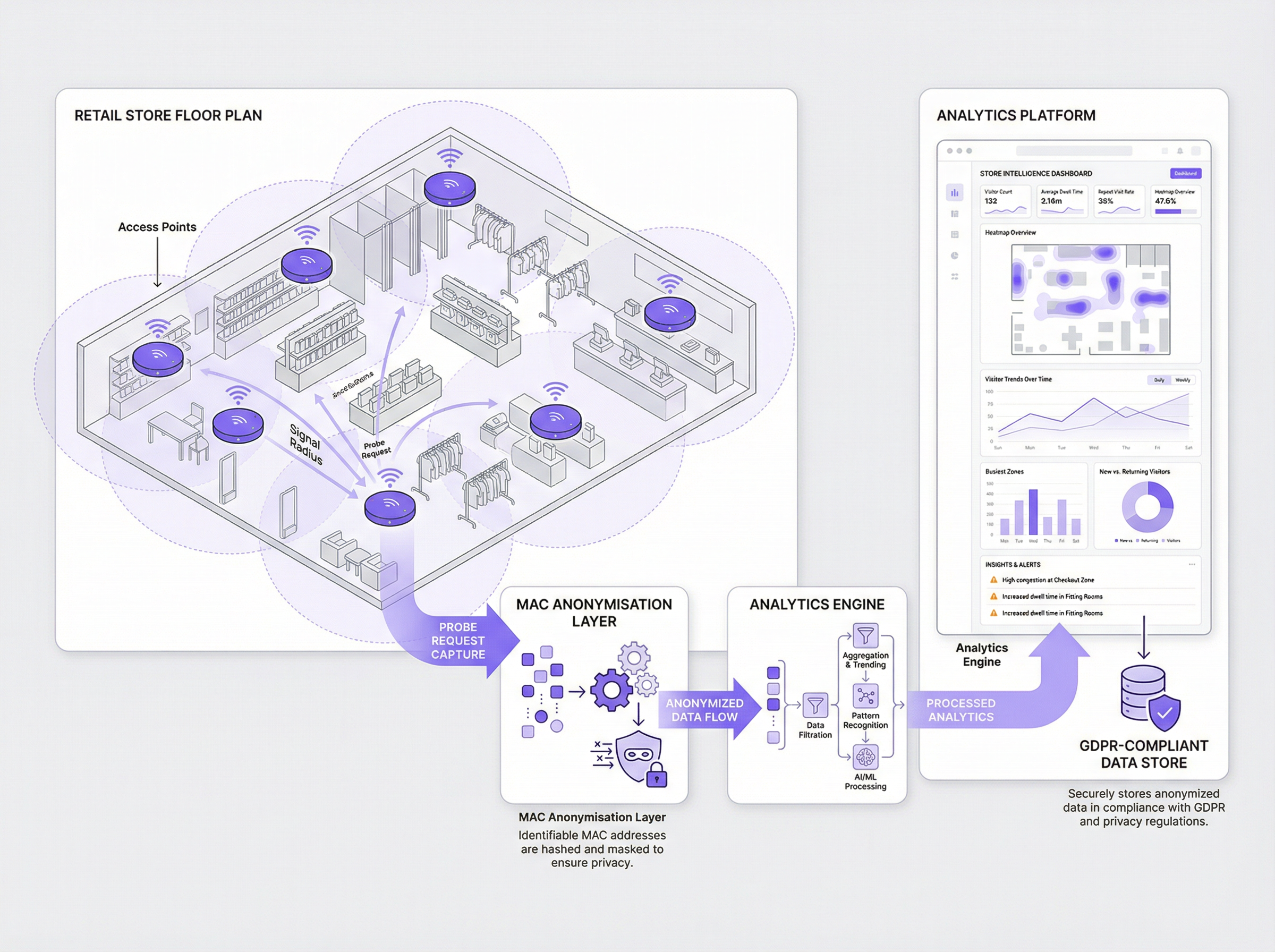
Die Grundlage der WiFi-Analyse liegt in der Erfassung von 802.11-Management-Frames, insbesondere von Probe-Requests. Jedes WiFi-fähige Gerät (Smartphone, Laptop, Tablet) sendet diese Anfragen regelmäßig aus, um drahtlose Netzwerke in der Nähe zu entdecken. Jeder Frame enthält mehrere wichtige Informationen, aber die für die Analyse entscheidendste ist die Media Access Control (MAC)-Adresse des Geräts – eine eindeutige Hardwarekennung. Durch den Einsatz von Sensoren oder die Konfiguration bestehender Access Points zum Abhören dieser Frames kann ein System die Anwesenheit, den Standort und die Bewegung von Geräten innerhalb eines physischen Raums erfassen.
Methoden der Datenerfassung:
- Passive Erfassung: Diese Methode nutzt Sensoren, die passiv auf Probe-Requests lauschen, ohne dass sich Nutzer mit dem Netzwerk verbinden müssen. Sie bietet einen umfassenden Überblick über alle Geräte in einem Bereich und liefert umfangreiche Daten zur Gesamtfrequenz und zu Bewegungsmustern. Da es jedoch keine direkte Interaktion mit dem Nutzer gibt, ist die Einholung einer ausdrücklichen Einwilligung schwierig, was eine robuste, sofortige Anonymisierung unerlässlich macht.
- Aktive Erfassung (Captive Portal): Diese Methode erfordert, dass sich ein Nutzer aktiv mit dem Gäste-WiFi-Netzwerk des Standorts verbindet. Der Verbindungsprozess wird über ein Captive Portal gesteuert, das eine Login- oder Splash-Page anzeigt. Dies ist der Branchenstandard, um die ausdrückliche, informierte Einwilligung des Nutzers einzuholen, bevor Daten verarbeitet werden. Obwohl hierbei nur Daten von verbundenen Nutzern erfasst werden, bietet dies eine wesentlich stärkere Rechtsgrundlage für die Datenverarbeitung und ermöglicht tiefere, identitätsbezogene Analysen, sofern sich der Nutzer authentifiziert.
Die Notwendigkeit der Anonymisierung: Unter der GDPR gilt eine MAC-Adresse als personenbezogenes Datum. Daher darf sie nicht in ihrem Rohformat gespeichert werden. Die Best Practice besteht darin, unmittelbar bei der Erfassung einen kryptografischen Einweg-Hash (z. B. SHA-256) in Kombination mit einem rotierenden Salt anzuwenden. Dieser als Pseudonymisierung bekannte Prozess wandelt die MAC-Adresse in eine irreversible, eindeutige Kennung um, die nicht auf das ursprüngliche Gerät zurückgeführt werden kann. Diese anonymisierte ID kann dann für Analysen, wie die Berechnung von Wiederholungsbesuchen, verwendet werden, ohne personenbezogene Daten zu speichern.
Auswirkungen der MAC-Adressen-Randomisierung: Moderne mobile Betriebssysteme (iOS 14+ und Android 10+) haben die Randomisierung von MAC-Adressen implementiert, um den Datenschutz der Nutzer zu verbessern. Diese Geräte senden für jedes neue WiFi-Netzwerk, das sie abfragen, eine andere, zufällig generierte MAC-Adresse. Obwohl dies eine datenschutzfreundliche Funktion ist, stellt sie herkömmliche Analyseplattformen vor eine erhebliche Herausforderung, da ein einzelnes Gerät als mehrere eindeutige Besucher erscheinen kann. Ausgereifte Analyse-Engines wie die von Purple setzen fortschrittliche Algorithmen ein, um diese randomisierten Adressen intelligent zu identifizieren und abzugleichen, wodurch die Genauigkeit der Besuchermetriken sichergestellt wird. Dies ist eine entscheidende technische Fähigkeit für jede moderne WiFi-Analyse-Implementierung.
Implementierungsleitfaden
Die Bereitstellung einer konformen Lösung zur WiFi-Datenerfassung erfordert einen strukturierten, mehrstufigen Ansatz, der auf dem Prinzip 'Privacy by Design' basiert.
Schritt 1: Bewertung der Infrastruktur Beginnen Sie mit einem Audit Ihrer bestehenden WiFi-Infrastruktur. Moderne Enterprise-Access-Points von Anbietern wie Cisco, Meraki, Aruba und Ruckus verfügen oft über integrierte Funktionen, um Management-Frames an einen Analyseserver zu streamen. Prüfen Sie, ob Ihre Hardware dies unterstützt oder ob dedizierte Sensoren erforderlich sind. Stellen Sie eine ausreichende Abdeckung in allen Bereichen sicher, in denen Sie Daten erfassen möchten.
Schritt 2: Definition Ihrer Datenrichtlinie & Einwilligungsmechanismen Dies ist der wichtigste Schritt für die Compliance. Arbeiten Sie mit Ihren Rechts- und Compliance-Teams zusammen, um Folgendes zu definieren:
- Welche Daten Sie erfassen werden: Seien Sie spezifisch (z. B. "
Key Terms & Definitions
MAC Address (Media Access Control)
A unique, 48-bit hardware number that identifies each device on a network. Under GDPR, it is considered Personal Identifiable Information (PII).
This is the core piece of data captured by WiFi analytics. IT teams must ensure it is never stored in its raw format and is anonymized immediately upon capture.
Probe Request
An 802.11 management frame sent by a WiFi-enabled device to discover nearby wireless networks.
These are the signals that WiFi analytics systems listen for. Understanding the volume and signal strength of probe requests allows the system to determine footfall and location.
Captive Portal
A web page that a user must view and interact with before being granted access to a public WiFi network.
This is the primary and most effective mechanism for an IT team to obtain explicit, informed consent from users before collecting and processing their data for analytics purposes.
Pseudonymization (Hashing)
The process of replacing a data identifier (like a MAC address) with a pseudonym (a cryptographic hash). It is a reversible process if the key is known, but one-way hashing makes it irreversible.
This is the critical technical process for making WiFi data compliant. A raw MAC address is PII; a hashed MAC address is an anonymized data point that can be used for analysis.
MAC Address Randomization
A privacy feature in modern mobile operating systems (iOS, Android) where the device uses a fake, temporary MAC address when searching for networks.
IT teams must be aware that this feature can severely skew analytics data. A modern analytics platform is required to correctly interpret these randomized addresses and avoid overcounting visitors.
GDPR (General Data Protection Regulation)
A comprehensive data protection law in the European Union that governs the processing of personal data.
This is the key regulation governing WiFi data capture in Europe. Any organisation with a European presence or that serves European citizens must ensure their analytics deployment is fully GDPR-compliant.
Data Controller
The entity that determines the purposes and means of processing personal data.
When a venue deploys WiFi analytics, the venue owner (e.g., the retail chain, the hotel) is the Data Controller and is legally responsible for ensuring compliance.
Dwell Time
A metric that measures the average amount of time visitors spend in a specific, defined area.
This is one of the most valuable business insights from WiFi analytics. It helps operations directors understand engagement, identify bottlenecks, and measure the success of marketing displays or layout changes.
Case Studies
A 50-store retail chain wants to understand customer behaviour in their flagship stores to inform a nationwide redesign. They need to measure dwell times in different departments, identify popular paths, and understand repeat visitor frequency, all while ensuring strict GDPR compliance.
- Infrastructure: Deploy a Purple-compatible WiFi analytics solution using their existing Meraki MR access points. Configure the Meraki dashboard to stream analytics data to the Purple cloud.
- Consent: Implement a branded captive portal for the guest WiFi network. The portal will feature a single, clear opt-in checkbox: "I agree to allow Purple to analyse my anonymized visit data to help improve the store layout and experience. This data is fully anonymized and will not be used for marketing." A link to the full privacy policy is provided.
- Anonymization: Configure the system to use Purple's patented Cryptographic Anonymization, which hashes the MAC address at the moment of capture. This ensures no PII is ever stored.
- Analysis: Use the Purple dashboard to create zones for each department (e.g., Menswear, Womenswear, Checkout). Track anonymized visitor flow between these zones and measure average dwell times. Use the repeat visitor metric to understand customer loyalty.
- Action: After 90 days, the data reveals that the Menswear department has high traffic but low dwell time. The chain redesigns the department layout to be more open and improves product displays. They then measure the impact of these changes over the next 90 days.
A large conference centre with multiple exhibition halls hosts a variety of third-party events. They want to offer event organisers data on attendee flow and booth popularity, but they are concerned about the privacy implications of tracking attendees across different, unrelated events.
- Data Segregation: The key is to treat each event as a separate entity. The WiFi analytics platform must be configured to use a different rotating salt for its hashing algorithm for each event. This means an anonymized ID from Event A will not be the same as the anonymized ID for the same device at Event B.
- Organiser Portals: Provide each event organiser with a separate, sandboxed view of the analytics data for their event only. They should not have access to historical data from other events or raw data of any kind.
- Consent per Event: The captive portal for each event must be unique and clearly state which organiser is the data controller for that event. Attendees must provide consent for each event they attend.
- Reporting: The platform can then generate reports on footfall, hall traffic, and booth dwell times for each specific event. This data can be sold to organisers as a premium service.
- Data Purge: Implement a strict data retention policy to purge all data associated with an event 30 days after the event concludes.
Scenario Analysis
Q1. A stadium is deploying a new WiFi analytics system to manage crowd flow on match days. Their legal team is concerned about storing location data. What is the most important technical control to implement regarding location?
💡 Hint:Think about the principle of data minimisation.
Show Recommended Approach
The most important control is to not store raw or fine-grained location data (e.g., X-Y coordinates). Instead, the stadium should be divided into large, pre-defined zones (e.g., "North Stand, Level 1", "West Entrance Gate"). The system should only record which zone a device is in, not its precise location within that zone. This minimises the sensitivity of the location data while still providing the necessary operational insights for crowd management.
Q2. A shopping mall uses a third-party to manage its guest WiFi. The third-party offers a 'free' analytics package. What is the number one question the mall's CTO should ask the third-party vendor?
💡 Hint:Who is the Data Controller and what are their responsibilities?
Show Recommended Approach
The CTO must ask: "Where and how is the MAC address anonymized?" They need to get a specific, technical answer. If the vendor cannot confirm that the MAC address is hashed with a salt, on-premise, before it is sent to their cloud, it is a major compliance red flag. The mall, as the Data Controller, is ultimately liable for any data breach or non-compliance, even if it is caused by their vendor.
Q3. A user logs into your guest WiFi and consents to analytics. They later submit a 'Right to be Forgotten' request under GDPR. You have stored their data as a hashed, anonymized ID. What is your technical obligation?
💡 Hint:How does pseudonymization relate to a user's rights?
Show Recommended Approach
Even though the data is pseudonymized, it is still linked to a specific individual, and the user's rights still apply. The analytics platform must have a mechanism to process these requests. When the user made the request, they would have provided an identifier (e.g., the email they used to log in). The platform needs a secure, audited process to look up the anonymized IDs associated with that user account and permanently delete them from the analytics database. Simply saying 'the data is anonymous' is not a compliant response.
Key Takeaways
- ✓WiFi data capture offers powerful insights but carries significant privacy obligations.
- ✓A MAC address is personal data under GDPR; it must be anonymized at the point of capture.
- ✓Explicit user consent via a captive portal is the best practice for compliance.
- ✓Modern analytics platforms are essential to handle challenges like MAC address randomization.
- ✓Adopt a 'Privacy by Design' approach, building compliance into your architecture from day one.
- ✓Transparency with users is not just a legal requirement; it is crucial for building trust.
- ✓Regularly audit your system and policies to ensure ongoing compliance and risk mitigation.



