Captive Portal Login: Troubleshooting Common Issues and Optimising User Experience
This authoritative technical reference guide equips IT managers, network architects, and CTOs with a comprehensive framework for diagnosing and resolving captive portal login failures, selecting the optimal authentication strategy for their venue type, and measuring portal performance against business KPIs. Drawing on real-world deployment scenarios across hospitality, retail, and public-sector environments, it covers the full lifecycle from architecture and compliance to step-by-step troubleshooting for platforms including Purple AI, UniFi, Meraki, and MikroTik. For any organisation operating guest or public WiFi, a poorly performing captive portal is a direct revenue and reputation risk — this guide provides the decision frameworks and operational playbooks to eliminate that risk.
🎧 Listen to this Guide
View Transcript

Executive Summary
The captive portal login remains the primary access-control mechanism for guest and public WiFi across hospitality, retail, events, and public-sector deployments. Yet it is also one of the most frequently misconfigured components in enterprise network stacks — responsible for abandoned connections, compliance exposure, and lost first-party data. This guide addresses the four root-cause failure categories that account for the majority of captive portal incidents: DNS and firewall misconfiguration, RADIUS authorisation failures, Captive Network Assistant (CNA) compatibility issues, and session persistence breakdowns. It provides platform-specific remediation steps for Purple AI, Cisco Meraki, Ubiquiti UniFi, and MikroTik RouterOS, alongside a structured authentication method selection framework aligned to venue type and data objectives. Compliance considerations under GDPR, UK GDPR, and PCI DSS v4.0 are integrated throughout. Network teams that implement the recommendations in this guide can expect authentication success rates above 92%, a measurable reduction in helpdesk escalations, and a defensible compliance posture for personal data collected at the point of WiFi login.
Technical Deep-Dive
How Captive Portal Login Works: The Architecture
A captive portal login operates through a deliberate interception of a device's initial connectivity probe. When any modern operating system connects to a new WiFi network, it immediately dispatches an HTTP request to a known endpoint to verify internet reachability. Apple devices query captive.apple.com; Android devices query connectivitycheck.gstatic.com; Windows queries www.msftconnecttest.com; Firefox queries detectportal.firefox.com. The captive portal gateway — typically implemented at the access controller layer — intercepts this probe and returns an HTTP 302 redirect to the splash page URL rather than the expected response.
The operating system detects this redirect, recognises the network as "captive", and launches a sandboxed mini-browser — Apple's Captive Network Assistant (CNA), Android's Provisioning Wizard, or Windows' Network Sign-In browser — to display the authentication interface. Once the user completes the required action (form submission, social login, click-through), the portal server communicates with the network controller via an API callback or RADIUS authorisation to remove the device's MAC address from the blocked list, granting full network access.
This architecture has three critical dependencies that, when any one fails, produce a broken login experience: the DNS/firewall layer must correctly redirect probe traffic; the splash page must render correctly within the CNA sandbox; and the authorisation callback must successfully reach the network controller.
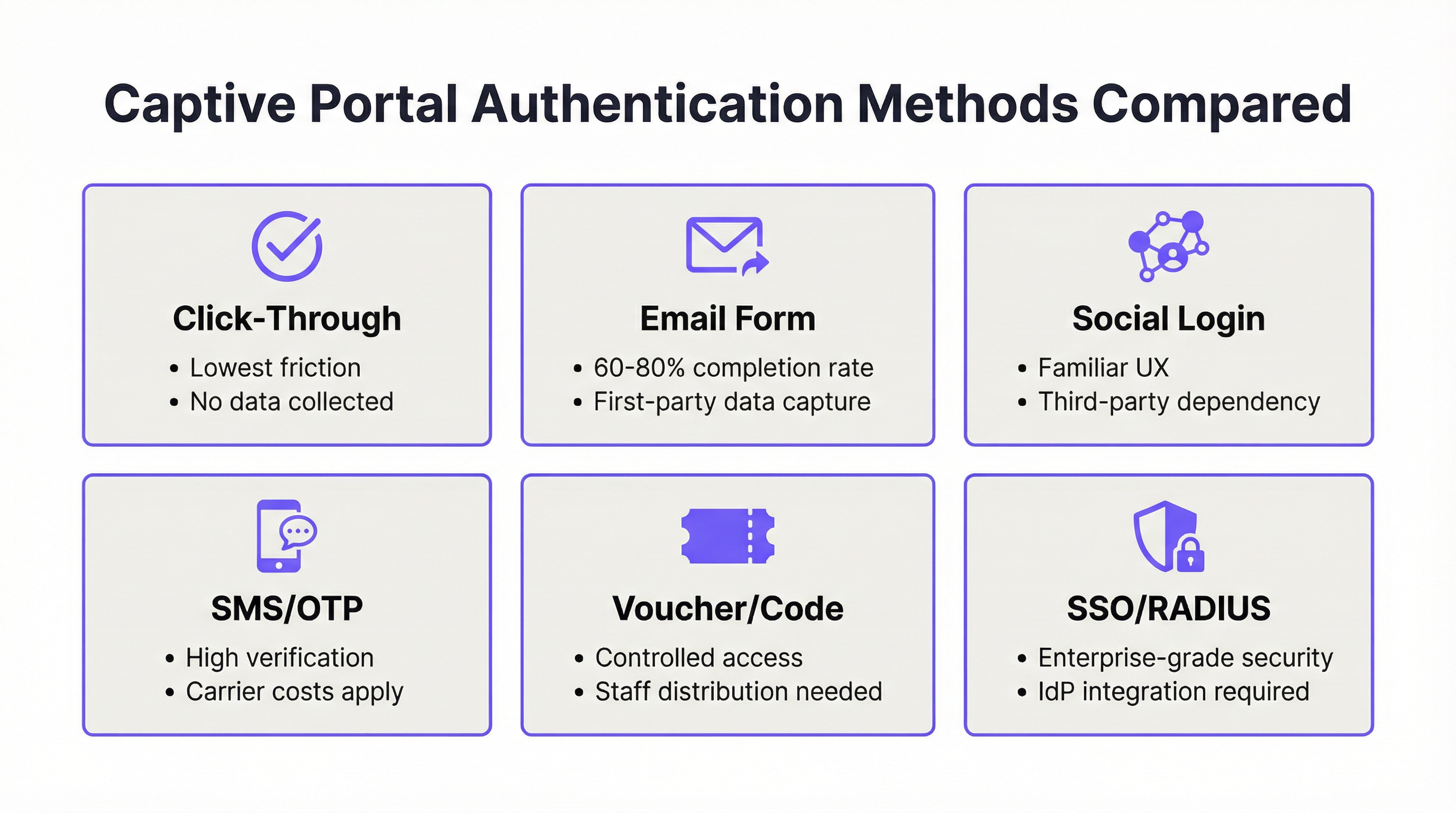
Authentication Methods: Technical Comparison
The choice of authentication method is simultaneously a technical and strategic decision. The following table provides a structured comparison across the dimensions most relevant to enterprise deployment decisions.
| Method | Completion Rate | Data Yield | GDPR Complexity | Infrastructure Dependency | Best Venue Type |
|---|---|---|---|---|---|
| Click-Through | 95%+ | None | Minimal (ToS only) | None | Quick-service retail, transport |
| Email Form | 60–80% | High (first-party) | Moderate | None | Hospitality, retail, events |
| Social Login | 55–70% | Moderate (third-party) | High | Third-party API | Hospitality, entertainment |
| SMS OTP | 50–65% | High (verified) | Moderate | SMS gateway | Public WiFi, transport hubs |
| Voucher/Code | 85%+ (distributed) | Low | Low | Distribution system | Hotels, conference centres |
| SSO/RADIUS | 90%+ (enrolled users) | Full identity | Low (internal) | IdP / RADIUS server | Corporate, education |
Social Login Considerations: Deploying Facebook or Google social login requires a Data Processing Agreement (DPA) with the respective platform under GDPR Article 28. The platform acts as a data processor, and your organisation remains the data controller. Any change to the social platform's API terms — as Facebook has made repeatedly since 2018 — can break your authentication flow without notice. For enterprise deployments, social login should be treated as a supplementary option, not a primary authentication path.
RADIUS and IEEE 802.1X: For corporate and education environments, RADIUS-based authentication aligned to IEEE 802.1X provides the strongest security posture. The 802.1X framework enables per-user, per-session encryption keys and integrates with certificate-based authentication (EAP-TLS), eliminating shared pre-shared keys entirely. WPA3-Enterprise, which mandates 802.1X, further strengthens this with 192-bit minimum cryptographic strength for sensitive environments. Purple's platform supports RADIUS integration natively, enabling a unified portal experience even in 802.1X-secured environments.
Security Architecture and Compliance
A captive portal that collects personal data is, by definition, a data processing system subject to applicable privacy regulation. For UK and EU deployments, this means GDPR and UK GDPR compliance is mandatory from the moment you collect a name, email address, or phone number. The minimum compliance requirements are: a lawful basis under Article 6 (legitimate interest or consent, depending on how data is used); a privacy notice displayed at the point of collection; a documented data retention policy; and a mechanism for data subject access requests.
For deployments in environments where payment card data transits the network — hotel lobbies, retail environments, conference centres — PCI DSS v4.0 Requirement 1.3 mandates network segmentation between the cardholder data environment and the guest WiFi network. A VLAN-segregated architecture, with the captive portal operating on a dedicated guest VLAN with no routing access to POS systems, is the standard implementation.

Implementation Guide
Step 1: Pre-Deployment Architecture Review
Before configuring any captive portal platform, validate the following network prerequisites. The gateway or access controller must support external portal redirection — verify this against your hardware vendor's documentation. Your DNS infrastructure must be capable of intercepting pre-authentication queries and resolving only the splash page domain until authentication completes. Your firewall must permit outbound HTTPS traffic from the controller to the portal provider's servers, and inbound HTTPS from the portal provider to the controller's management interface on the appropriate port (typically 8443 for UniFi, 443 for cloud-managed platforms).
Step 2: Walled Garden Configuration
The walled garden defines the set of domains and IP ranges accessible to unauthenticated devices. An incomplete walled garden is the single most common cause of intermittent portal failures. The minimum walled garden for a production deployment must include the following entries.
| Category | Domains / Ranges | Purpose |
|---|---|---|
| OS Probe Endpoints | captive.apple.com, connectivitycheck.gstatic.com, www.msftconnecttest.com, detectportal.firefox.com |
Enables OS captive portal detection |
| Portal Provider | Your portal's domain and CDN ranges | Loads the splash page |
| Social Login (if used) | *.facebook.com, *.google.com, *.linkedin.com |
Enables OAuth flows |
| Payment (if used) | *.stripe.com, js.stripe.com |
Loads payment forms |
| Analytics (if used) | Your analytics provider's domains | Enables tracking scripts |
Step 3: Splash Page Optimisation
The splash page must be designed for the CNA environment, not a full browser. This means: total page weight under 500 KB; no reliance on external JavaScript CDNs unless whitelisted; valid HTTPS with a certificate from a trusted CA; responsive design tested at 320px width (iPhone SE) through 1024px; and a form with no more than three fields (name, email, and consent checkbox) for maximum completion rates.
Step 4: Session and Policy Configuration
Configure session parameters to match your venue's usage pattern. The following reference values are based on Purple's deployment data across thousands of venues.
| Venue Type | Session Duration | Idle Timeout | Bandwidth Policy |
|---|---|---|---|
| Hotel | 24 hours | 60 minutes | 10 Mbps per device |
| Coffee Shop / Café | 4–8 hours | 30 minutes | 5 Mbps per device |
| Conference Centre | Event duration | 120 minutes | 20 Mbps per device |
| Stadium / Arena | Event duration | 45 minutes | 5 Mbps per device |
| Retail | 2–4 hours | 20 minutes | 3 Mbps per device |
| Public Sector / Library | 2 hours | 30 minutes | 5 Mbps per device |
Step 5: Platform-Specific Configuration — Purple AI
Purple AI's captive portal is configured through the Purple dashboard. Navigate to WiFi > Splash Pages to create or edit your portal. Select your authentication method under Login Options — Purple supports click-through, email form, social login (Facebook, Google, LinkedIn, X), SMS OTP, voucher, and SSO via Microsoft Entra ID, Google Workspace, and Okta. Under Compliance, enable GDPR-compliant consent capture and configure your privacy policy URL. Under Session Settings, apply the values from the table above. Publish the splash page and associate it with your SSID in the Networks section. Purple's platform automatically handles the walled garden configuration for its own domains; you will need to manually add any third-party domains your splash page references.
Step 6: Testing Protocol
After deployment, execute the following test matrix before going live. Connect a test device to the guest SSID and verify: the portal appears within 3 seconds; the splash page renders correctly and is fully functional; authentication completes successfully; internet access is granted immediately after authentication; and the device does not require re-authentication within the configured session duration. Repeat this test on iOS (latest), iOS (previous major version), Android (latest), Android (previous major version), Windows 11, and macOS. Document the results and remediate any failures before opening the network to guests.
Best Practices
Performance Monitoring: Treat authentication success rate as a primary network KPI, targeting 92% or above. Purple's analytics dashboard surfaces this metric in real time. A drop below 85% warrants immediate investigation — common causes include certificate expiry, OS updates that alter probe behaviour, and firewall rule changes.
Certificate Management: SSL certificates for splash page domains must be renewed before expiry. Implement automated renewal via Let's Encrypt or your certificate management platform, and set calendar alerts 30 days before expiry. An expired certificate will cause iOS and Android to display security warnings that effectively prevent users from connecting.
GDPR Consent Records: Every consent captured at the captive portal must be logged with a timestamp, the version of the privacy notice displayed, and the specific consents granted. Purple's platform maintains this audit trail automatically. For manual implementations, ensure your database schema captures this data and that records are retained for the duration required by your data retention policy.
Network Segmentation: Guest WiFi must be on a separate VLAN with no layer-3 routing access to internal networks or POS systems. This is a PCI DSS requirement and a fundamental security control. Verify segmentation with a penetration test at least annually.
Firmware and Platform Updates: Keep your access controller firmware and portal platform current. Many CNA compatibility issues are resolved in firmware updates — Cisco Meraki, Ubiquiti, and Aruba all release regular updates that address OS-specific portal detection changes. Subscribe to vendor security advisories and apply updates within your change management window.
Troubleshooting & Risk Mitigation
Diagnostic Framework: The Four-Layer Check
When a captive portal login failure is reported, work through the following four-layer diagnostic sequence before escalating or making configuration changes.
Layer 1 — DNS and Redirect: Verify that the gateway is intercepting probe traffic and returning the correct redirect. Use a test device and a packet capture tool to confirm the 302 redirect is being issued. If no redirect is seen, the issue is at the gateway configuration level.
Layer 2 — Splash Page Delivery: Verify that the splash page loads correctly in the CNA. If the page loads in a full browser but not the CNA, the issue is likely a JavaScript dependency or a missing walled garden entry. Use browser developer tools to identify blocked resources.
Layer 3 — Authentication Processing: Verify that the authentication request reaches the portal server and returns a success response. Check portal provider logs for failed authentication attempts. If authentication fails silently, the issue is typically a form validation error or a missing required field.
Layer 4 — Authorisation Callback: Verify that the portal server can reach the network controller to authorise the device's MAC address. Check firewall logs for blocked connections between the portal server IP ranges and the controller management interface. If the callback is failing, whitelist the portal provider's IP ranges and verify controller accessibility.
Common Failure Modes and Remediation
| Symptom | Most Likely Cause | Remediation |
|---|---|---|
| Portal doesn't appear on connection | Missing OS probe domains in walled garden; AP not restarted after config change | Add probe domains to walled garden; restart APs |
| Portal appears but page doesn't load | JavaScript dependency blocked; CDN not in walled garden | Audit page dependencies; add CDN domains to walled garden |
| Authentication succeeds, no internet | RADIUS callback blocked; controller unreachable | Whitelist portal provider IPs; verify controller accessibility |
| Portal works on iOS, fails on Android | Android probe domain blocked; HTTPS certificate issue | Add connectivitycheck.gstatic.com to walled garden; verify certificate |
| Guests must re-login repeatedly | Session duration too short; MAC persistence not configured | Increase session duration; verify MAC tracking in controller |
| Slow portal load (>5 seconds) | Page too heavy; DNS resolution slow; congested uplink | Optimise page weight; use reliable DNS (8.8.8.8); check uplink capacity |
| Social login fails | OAuth domain not in walled garden; third-party API change | Add social platform domains to walled garden; check API status |
| Payment form doesn't load | Stripe domains not in walled garden | Add *.stripe.com and js.stripe.com to walled garden |
Frequently Asked Questions
Q: Why does my portal work perfectly in testing but fail intermittently in production? Intermittent failures in production are almost always caused by one of three conditions: high concurrent connection load overwhelming the gateway's redirect capacity; DNS resolution timeouts under load; or a race condition between the AP's configuration cache and a recent change. Increase your gateway's connection tracking table size, use a dedicated DNS resolver (not the ISP default), and always restart APs after configuration changes.
Q: Can I use a custom domain for my Purple splash page? Yes. Purple supports custom domains for splash pages. Configure a CNAME record pointing your chosen subdomain to Purple's portal infrastructure, and ensure your SSL certificate covers the custom domain. A branded domain significantly improves user trust and reduces abandonment.
Q: How do I handle the transition from HTTP to HTTPS for my splash page? All production splash pages should be served over HTTPS. If you are migrating from an HTTP portal, update your gateway redirect configuration to point to the HTTPS URL, obtain a valid certificate from a trusted CA, and test on all major OS and browser combinations before switching over.
Q: What is the impact of iOS 17 and later on captive portal behaviour? Apple tightened CNA restrictions in iOS 17, blocking third-party cookies and restricting JavaScript execution from certain origins. If you are seeing failures specifically on iOS 17+ devices, audit your splash page for third-party cookie dependencies and JavaScript from non-whitelisted origins. Simplify your splash page to the minimum required functionality.
Q: Does Purple AI support multi-site management for retail chains? Yes. Purple's enterprise platform supports centralised management of captive portal configurations across unlimited locations, with per-site customisation of splash pages, authentication methods, and session policies. Changes can be pushed to all sites simultaneously or staged by region.
Q: How do I ensure GDPR compliance when using social login? When using social login, you must: disclose in your privacy notice that data is obtained from the social platform; establish a DPA with the social platform provider; ensure you have a lawful basis for processing the data received; and provide a mechanism for users to request deletion of their data. Purple's compliance tooling assists with consent capture and audit trails, but the legal framework must be established by your organisation's data protection officer.
Q: What monitoring should I have in place for a production captive portal? At minimum: real-time authentication success rate alerting (threshold: below 85%); certificate expiry monitoring (alert at 30 days); portal uptime monitoring (5-minute check intervals); and a weekly review of authentication failure logs. Purple's analytics dashboard provides all of these metrics natively.
ROI & Business Impact
The business case for a well-configured captive portal extends well beyond network access control. For hospitality operators, each authenticated guest WiFi login represents a first-party data point — name, email, visit timestamp, device type — that feeds directly into CRM systems, loyalty programmes, and marketing automation. Purple's deployment data across its customer base demonstrates an average of 842% ROI from guest WiFi programmes when the captive portal is integrated with CRM and marketing platforms.
For retail operators, the footfall intelligence derived from WiFi analytics — dwell time, repeat visit frequency, zone occupancy — provides the same category of insight as a physical people-counting system, at a fraction of the cost, with the added benefit of individual-level data linkage when guests are authenticated. A 200-store retail chain with an average of 500 daily WiFi logins per store is generating 100,000 first-party data points per day — a dataset that, properly activated, can drive measurable improvements in promotional targeting, staffing, and store layout.
For venue operators — stadiums, conference centres, airports — the captive portal is a direct revenue channel through sponsorship of the splash page, targeted advertising to authenticated users, and premium WiFi tier upsells. Brussels South Charleroi Airport, a Purple customer, achieved 9.2 million customer visits tracked through guest WiFi during the first 24 months of deployment, enabling data-driven decisions on retail placement and passenger flow management.
The cost of a poorly performing captive portal is equally quantifiable. If 22% of users abandon the login process — the industry average for poorly designed portals — and your venue processes 1,000 WiFi connection attempts per day, you are losing 220 data points daily, or approximately 80,000 per year. At a conservative CRM value of £2 per verified email address, that represents £160,000 in lost data asset value annually, before accounting for the marketing revenue those contacts would have generated.
The investment required to close that gap — optimised splash page design, correct walled garden configuration, appropriate session settings, and a monitoring framework — is measured in hours of engineering time, not capital expenditure. The ROI case is unambiguous.
Key Terms & Definitions
Captive Portal
A network access control mechanism that intercepts all HTTP/HTTPS traffic from unauthenticated devices and redirects it to a designated authentication page (the splash page). The device remains in a 'captive' state — with access restricted to the splash page and any whitelisted domains — until authentication is completed and the network controller authorises the device's MAC address.
IT teams encounter captive portals as the primary guest WiFi access control mechanism in hospitality, retail, events, and public-sector environments. The term is often used interchangeably with 'splash page' or 'guest portal', though strictly the captive portal refers to the entire system (gateway + splash page + authentication backend), not just the login page.
Captive Network Assistant (CNA)
A sandboxed mini-browser built into iOS, macOS, and other Apple operating systems that automatically opens when the OS detects a captive portal redirect. The CNA has significantly more restrictive behaviour than a full browser: it blocks third-party cookies, restricts JavaScript execution from certain origins, and does not persist sessions across launches. Android has an equivalent mechanism called the Provisioning Wizard.
The CNA is the source of the majority of device-specific captive portal failures. Engineers who test only in a full browser will miss CNA-specific issues. All splash page testing must include CNA testing on the latest and previous major iOS and Android versions.
Walled Garden
The set of domains, IP ranges, and URLs that unauthenticated devices are permitted to access before completing the captive portal login. The walled garden is configured at the network gateway or access controller and must include, at minimum, the OS probe endpoints, the portal provider's domains, and any third-party services referenced by the splash page.
An incomplete walled garden is the most common cause of intermittent captive portal failures. IT teams should audit the walled garden whenever a new third-party service is added to the splash page, and after any OS update that may have changed probe endpoint behaviour.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised authentication, authorisation, and accounting (AAA) for network access. In captive portal deployments, RADIUS is used to verify user credentials against a central directory (Active Directory, LDAP, or a cloud IdP) and to communicate authorisation decisions back to the network access server. RADIUS operates on UDP ports 1812 (authentication) and 1813 (accounting).
RADIUS is the standard authentication backend for enterprise and education WiFi deployments. IT teams encounter RADIUS configuration issues most frequently when the shared secret between the portal server and the RADIUS client does not match, or when the RADIUS server's IP is not reachable from the access controller. Purple supports RADIUS integration natively.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices attempting to connect to a LAN or WLAN. 802.1X uses the Extensible Authentication Protocol (EAP) to exchange authentication credentials between the supplicant (device), the authenticator (access point), and the authentication server (RADIUS). It is the foundation of WPA2-Enterprise and WPA3-Enterprise security.
802.1X is relevant to captive portal deployments in enterprise environments where the guest WiFi must coexist with a corporate 802.1X-secured network. IT teams must ensure that the guest SSID is not inadvertently configured to require 802.1X, which would prevent the captive portal from functioning correctly.
MAC Address Authorisation
The mechanism by which a captive portal grants network access after successful authentication. When a user completes the login process, the portal server sends the device's MAC address to the network controller, which removes it from the blocked list and allows full internet access. Session persistence is maintained by tracking the MAC address — the controller does not redirect a previously authorised MAC address until the session expires.
MAC address authorisation is the reason captive portals can be bypassed by MAC spoofing. For environments requiring strong identity assurance, MAC-based authorisation should be supplemented with certificate-based authentication (802.1X/EAP-TLS) or SMS OTP verification.
Splash Page
The web page displayed to unauthenticated users when they connect to a captive portal network. The splash page hosts the authentication interface — login form, social login buttons, click-through agreement, or voucher entry — and is the primary touchpoint for brand presentation and data collection. The splash page is served from the portal provider's infrastructure (or a self-hosted server) and is the only page accessible to unauthenticated devices before the walled garden is opened.
IT teams are responsible for ensuring the splash page renders correctly in the CNA environment, loads within acceptable time limits, and complies with GDPR requirements for data collection. Marketing teams are responsible for the brand design and messaging. The two teams must collaborate on splash page design to avoid compliance gaps and technical failures.
GDPR Article 6 Lawful Basis
Under the General Data Protection Regulation (GDPR) and UK GDPR, any processing of personal data must have a documented lawful basis. For captive portal deployments, the two most commonly applicable bases are: Article 6(1)(a) — consent, where the user explicitly agrees to data processing; and Article 6(1)(f) — legitimate interests, where the organisation has a legitimate business reason for processing that is not overridden by the individual's rights. The chosen basis determines the design of the consent capture mechanism and the data subject rights obligations.
IT teams deploying captive portals that collect personal data must ensure the lawful basis is documented before deployment. Failure to establish a lawful basis is a GDPR violation that can result in regulatory fines of up to €20 million or 4% of global annual turnover. Purple's compliance tooling supports both consent and legitimate interest frameworks.
PCI DSS Network Segmentation
A requirement under PCI DSS v4.0 (Requirement 1.3) that the cardholder data environment (CDE) must be isolated from other network segments, including guest WiFi. In practice, this means the guest WiFi network must be on a separate VLAN with no layer-3 routing access to POS systems, payment terminals, or any system that stores, processes, or transmits cardholder data. The segmentation must be verified through penetration testing at least annually.
IT teams in retail, hospitality, and events environments must ensure that the captive portal guest network is correctly segmented from the payment infrastructure. A misconfigured VLAN that allows guest devices to reach POS systems is a critical PCI DSS violation and a significant security risk.
SSO (Single Sign-On)
An authentication mechanism that allows users to authenticate once with a central identity provider (IdP) and gain access to multiple services without re-entering credentials. In captive portal deployments, SSO enables employees or students to log in to the guest WiFi using their existing corporate or institutional credentials (e.g., Microsoft Entra ID, Okta, Google Workspace), eliminating the need for separate WiFi passwords or vouchers.
SSO integration is the preferred authentication method for corporate campus and education deployments. Purple supports SSO via SAML 2.0 and OAuth 2.0, enabling integration with all major enterprise IdPs. IT teams should verify that the IdP's OAuth endpoints are included in the walled garden to prevent SSO flow failures.
Case Studies
A 350-room luxury hotel group is deploying Purple AI across 12 properties. Guests are reporting that the captive portal login works on their laptops but fails on iOS devices. The IT team has confirmed the portal renders correctly in Safari on a desktop Mac. What is the most likely cause, and how should the team diagnose and resolve it?
The symptom — portal works in a full browser but fails on iOS devices — is a classic Captive Network Assistant (CNA) compatibility issue. The CNA on iOS is a sandboxed mini-browser with significantly more restrictive behaviour than Safari. The diagnostic process should proceed as follows.
Step 1: Connect an iOS test device to the guest SSID and observe the CNA behaviour. Note whether the page fails to load entirely, loads partially, or loads but fails during authentication.
Step 2: If the page loads partially, open Safari on the iOS device and navigate to the splash page URL directly. Use Safari's developer tools (enabled via Settings > Safari > Advanced > Web Inspector) to identify any blocked resources or JavaScript errors.
Step 3: Check the walled garden configuration in Purple's dashboard. Verify that all domains referenced by the splash page — including any CDN domains for fonts, scripts, or images — are included. A common culprit is Google Fonts (fonts.googleapis.com, fonts.gstatic.com) or a social login SDK.
Step 4: If the splash page uses social login (Facebook, Google), verify that the OAuth domains are in the walled garden: accounts.google.com, graph.facebook.com, and their associated CDN domains.
Step 5: Audit the splash page for third-party cookie dependencies. iOS 17+ blocks third-party cookies in the CNA. If the authentication flow relies on a third-party session cookie, it will fail silently on iOS 17+.
Resolution: Add all missing domains to the walled garden in Purple's dashboard. Simplify the splash page to remove any third-party cookie dependencies. Test on iOS 17 (latest), iOS 16 (previous major), and iOS 15 (two versions back) before deploying to production. For the hotel group's 12 properties, push the updated walled garden configuration centrally through Purple's multi-site management interface, then restart APs at each property during a low-traffic window.
A national retail chain with 85 stores is experiencing a compliance audit finding: their captive portal collects customer email addresses but has no documented lawful basis for processing, no privacy notice at the point of collection, and no data retention policy. The CTO has been given 30 days to remediate. What is the remediation plan?
This is a GDPR compliance remediation scenario with a hard deadline. The remediation plan must address three distinct requirements: lawful basis documentation, privacy notice implementation, and data retention policy.
Week 1 — Legal and Policy Framework: Engage the organisation's Data Protection Officer (DPO) or external legal counsel to determine the appropriate lawful basis under GDPR Article 6. For marketing use of guest WiFi data, legitimate interest (Article 6(1)(f)) is typically the strongest basis, supported by a Legitimate Interest Assessment (LIA). If the data will be used for direct marketing, explicit consent (Article 6(1)(a)) may be required. Document the chosen basis and the LIA.
Week 2 — Splash Page Remediation: Update the captive portal splash page in Purple's dashboard to include: a link to the organisation's privacy notice (which must be updated to describe WiFi data collection); a clear statement of how the data will be used; and, if consent is the chosen basis, an explicit opt-in checkbox that is unchecked by default. Purple's compliance tooling supports GDPR-compliant consent capture natively — enable the consent capture module and configure the privacy policy URL.
Week 3 — Data Retention and Subject Rights: Define a data retention period (typically 12–24 months for marketing data) and configure Purple's data retention settings accordingly. Implement a data subject access request (DSAR) process — Purple provides a self-service data deletion mechanism accessible via the guest portal. Document the process in the organisation's data protection register.
Week 4 — Audit and Evidence: Conduct a full audit of the updated configuration across all 85 stores using Purple's multi-site management console. Export consent records to demonstrate that post-remediation logins are capturing compliant consent. Prepare a remediation report for the auditor, including the LIA, updated privacy notice, configuration screenshots, and sample consent records.
Scenario Analysis
Q1. Your organisation operates a 600-seat conference centre that hosts 3–5 events per week, ranging from half-day seminars to 3-day international conferences. The current captive portal uses a single click-through authentication method and a 4-hour session duration. The events team has requested that the WiFi system begin capturing delegate contact details for post-event marketing. The IT team has 6 weeks to implement the change. What authentication method should you deploy, what session configuration changes are required, and what compliance steps must be completed before go-live?
💡 Hint:Consider the operational model of a conference centre: delegates arrive at registration, receive credentials, and expect seamless connectivity throughout a multi-day event. The authentication method must balance data collection objectives with the operational reality of managing hundreds of simultaneous connections at event start.
Show Recommended Approach
The recommended authentication method is a voucher or code system combined with an email form capture at the point of voucher redemption. This approach allows the events team to distribute unique codes at registration (printed on delegate badges or sent via email confirmation), ensuring controlled access while capturing verified contact details. The session duration should be set to the maximum event duration — 72 hours for a 3-day conference — with an idle timeout of 120 minutes to accommodate breaks and overnight periods without requiring re-authentication. For compliance, the following steps must be completed before go-live: (1) determine the lawful basis for processing delegate contact data (consent is recommended for conference environments, as delegates have a clear expectation of data use); (2) update the splash page to include a GDPR-compliant privacy notice and an explicit consent checkbox; (3) configure Purple's consent capture module to log consent records with timestamps; (4) establish a data retention policy (12 months is standard for event marketing data); and (5) brief the events team on the data subject rights process. The 6-week timeline is achievable: weeks 1–2 for legal and policy framework; weeks 3–4 for platform configuration and testing; weeks 5–6 for staff training and a pilot event.
Q2. A 50-store fashion retail chain is reporting that their captive portal authentication success rate has dropped from 94% to 71% over the past two weeks, with failures concentrated on Android devices. No configuration changes have been made to the portal or network infrastructure during this period. What is your diagnostic approach, and what are the three most likely causes?
💡 Hint:A sudden drop in success rate on a specific OS platform, with no configuration changes, points to an external change — either an OS update that altered probe behaviour, or a change to a third-party service the splash page depends on.
Show Recommended Approach
The diagnostic approach follows the Four-Layer framework, but given the OS-specific nature of the failure, begin at Layer 2 (splash page delivery in the CNA). The three most likely causes are: (1) A recent Android OS update has altered the probe endpoint or the Provisioning Wizard's behaviour — check the Android security bulletin for the relevant period and verify that connectivitycheck.gstatic.com is accessible in the walled garden; (2) A third-party service used by the splash page — most likely a social login SDK or analytics script — has changed its domain or CDN configuration, and the new domain is not in the walled garden; (3) The SSL certificate for the splash page domain has expired or is being served from a different certificate chain that Android's trust store does not recognise. To diagnose: connect an Android test device to the guest SSID and capture the CNA behaviour; use Android's developer options to inspect network traffic; check the portal provider's error logs for the period in question. For Purple deployments, the analytics dashboard will show the authentication failure rate by device type and OS version, which will confirm whether the failure is concentrated on a specific Android version — pointing to an OS update as the cause.
Q3. A regional airport authority is planning to deploy guest WiFi across its terminal, with a requirement to collect passenger contact details for emergency communications and optional marketing. The deployment must comply with UK GDPR, and the IT security team has mandated that the guest network must be fully segregated from the airport's operational technology (OT) network, which includes baggage handling systems and gate management. The airport processes approximately 8,000 passenger WiFi connections per day. What architecture and authentication strategy would you recommend, and what are the key compliance and security controls required?
💡 Hint:Airport environments have dual compliance requirements: data protection (UK GDPR for passenger data) and operational security (OT network segregation). The authentication method must handle high concurrent connection volumes at peak times (flight arrivals) without degrading performance.
Show Recommended Approach
The recommended architecture uses a two-SSID model: a guest SSID for passenger WiFi, and a staff SSID secured with WPA3-Enterprise and 802.1X for airport employees. The guest SSID operates on a dedicated VLAN with no layer-3 routing to the OT network or any internal airport systems. Firewall rules must explicitly deny all traffic from the guest VLAN to OT network ranges, with the segmentation verified through quarterly penetration testing. For authentication, deploy an email form with a two-purpose consent model: mandatory consent for emergency communications (lawful basis: vital interests under GDPR Article 6(1)(d), or legitimate interests); and optional consent for marketing communications (lawful basis: consent under Article 6(1)(a)). The form should present these as two separate checkboxes, with the emergency communications checkbox pre-checked and non-removable (with clear explanation), and the marketing checkbox unchecked by default. Session duration should be set to 8 hours (covering a typical airport dwell time) with a 60-minute idle timeout. For peak load management — 8,000 daily connections with significant concurrency during flight arrivals — the gateway must be sized for at least 500 simultaneous authentication requests. Purple's platform is horizontally scalable and handles this load natively. Key compliance controls: UK GDPR privacy notice at point of collection; consent audit trail in Purple's compliance module; data retention policy (12 months for emergency contact data, 24 months for marketing data); and a DSAR process accessible via the splash page.
Key Takeaways
- ✓The four root causes of captive portal login failures are DNS and firewall misconfiguration, RADIUS authorisation callback failures, Captive Network Assistant (CNA) compatibility issues, and session persistence misconfiguration — diagnose in this sequence before making any changes.
- ✓An incomplete walled garden is the single most common cause of intermittent portal failures: always include OS probe endpoints (Apple, Google, Microsoft, Firefox), portal provider domains, and all third-party service domains referenced by the splash page.
- ✓Keep splash pages under 500KB and test specifically in the CNA environment on iOS and Android — a page that renders perfectly in a desktop browser may fail entirely in the CNA due to JavaScript restrictions and third-party cookie blocking.
- ✓Authentication method selection is a strategic decision: use the Data-Friction Matrix to identify the method that maximises data value while minimising user friction — for most hospitality and retail environments, a well-designed email form (name + email only) sits in the optimal quadrant.
- ✓GDPR compliance is non-negotiable for any captive portal that collects personal data: document your lawful basis under Article 6, display a privacy notice at the point of collection, capture and log consent records, and establish a data retention policy before deployment — not after.
- ✓Monitor authentication success rate as a primary KPI with an alert threshold at 85%: a drop below this level indicates a change in the environment — certificate expiry, OS update, or firewall modification — that requires immediate investigation.
- ✓Purple AI's enterprise platform delivers measurable ROI: 842% average return on investment when guest WiFi data is integrated with CRM and marketing automation, with built-in GDPR compliance tooling, multi-site management, and support for all major authentication methods including SSO via Microsoft Entra ID, Google Workspace, and Okta.



