Captive Portals: A Comprehensive Guide to Implementation, Customisation, and Security
This guide provides IT managers, network architects, and CTOs with a definitive technical reference for deploying, customising, and securing captive wifi portals across enterprise venues including hotels, retail chains, stadiums, and public-sector facilities. It covers authentication architectures, GDPR and PCI DSS compliance obligations, threat mitigation strategies, and the advanced analytics capabilities available through Purple's enterprise WiFi intelligence platform. Organisations that implement captive portals correctly transform a basic connectivity utility into a measurable business intelligence and revenue-generation asset.
🎧 Listen to this Guide
View Transcript
Executive Summary
A captive Wi-Fi portal is the controlled gateway through which every guest device must pass before accessing your network. For the CTO evaluating this investment, the business case is straightforward: a well-deployed captive portal simultaneously satisfies your legal obligations under GDPR and sector-specific regulations, eliminates anonymous network access, and converts every Wi-Fi login into a structured first-party data event that feeds your CRM, marketing automation, and operational analytics stack.
The UK captive portal market grew from £0.88 billion to £1.01 billion between 2023 and 2024, reflecting a 15.3% compound annual growth rate driven by hospitality and retail adoption. Brussels South Charleroi Airport reported an 842% return on investment following deployment of Purple's platform, while enterprise customers consistently report a 90% reduction in on-site IT engineer visits through centralised cloud management.
This guide covers the technical architecture of captive portals, the three primary authentication models and their trade-offs, security hardening against the most common attack vectors, GDPR and PCI DSS compliance requirements, and the advanced customisation and analytics capabilities that differentiate an enterprise-grade deployment from a commodity login page.
Technical Deep-Dive
How a Captive WiFi Portal Works
At its core, a captive portal is a network access control mechanism that intercepts unauthenticated traffic and redirects it to a web-based authentication page. The mechanism operates as follows. When a device associates with a guest SSID, the access point assigns an IP address via DHCP and places the device in a restricted firewall state. DNS resolution functions normally — this is by design, as the portal redirect depends on it — but all outbound HTTP and HTTPS traffic is intercepted by the gateway and met with an HTTP 302 redirect to the portal URL.
Modern operating systems include built-in Captive Network Assistant (CNA) detection. iOS probes captive.apple.com, Android probes connectivitycheck.gstatic.com, and Windows uses Network Location Awareness to query www.msftconnecttest.com. When these probes return unexpected responses, the OS automatically launches a lightweight browser window presenting the portal. This is why users experience an almost immediate pop-up rather than a browser timeout.
The four-stage authentication flow is as follows:
- Association and DHCP: Device connects to the SSID and receives an IP address. The gateway marks the session as unauthenticated.
- Interception and Redirect: The gateway intercepts the first HTTP request and issues a 302 redirect to the portal URL. For HTTPS requests, the gateway must either present a valid TLS certificate for the intercepted domain (which triggers browser warnings) or rely on the CNA mechanism to avoid HTTPS interception entirely.
- Authentication Action: The user completes the required action on the portal page — accepting an AUP, submitting credentials, or entering a voucher code.
- Session Authorisation: The portal controller notifies the gateway that the device's MAC address (or session token) is now authorised. The firewall rule is updated and full internet access is granted for the configured session duration.
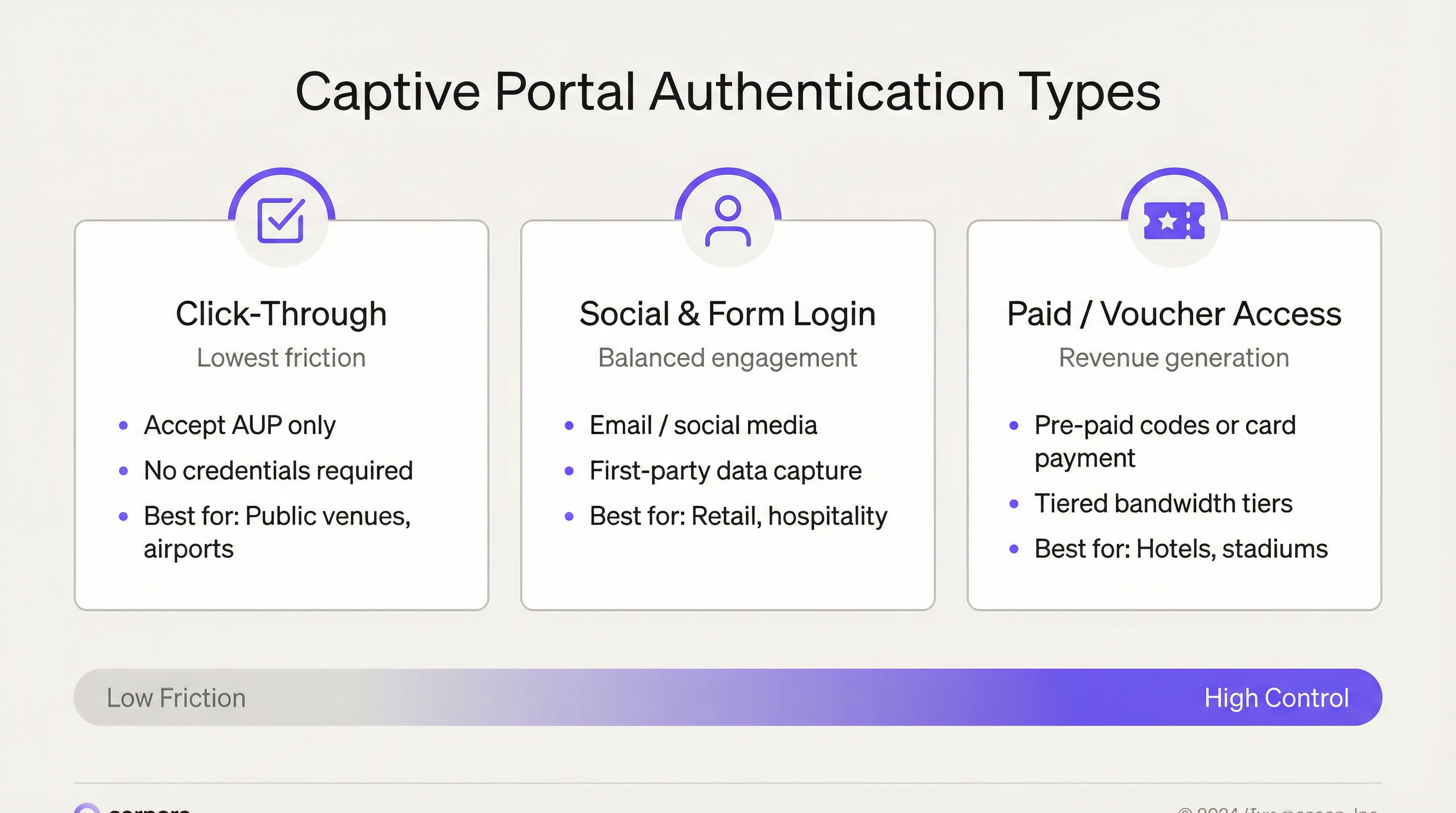
Authentication Models: A Technical Comparison
The choice of authentication model is the most consequential decision in a captive portal deployment. It determines your data quality, your compliance posture, and your user experience metrics.
| Authentication Model | Technical Mechanism | Data Captured | Compliance Complexity | Best Fit |
|---|---|---|---|---|
| Click-Through (AUP-only) | Single checkbox; MAC-based session authorisation | Device MAC, timestamp, session duration | Low — no personal data collected | Public sector, transport hubs, libraries |
| Email / Form Registration | Form submission; server-side validation; session token issued | Email, name, demographics, opt-in status | Medium — GDPR consent flow required | Hospitality, retail, corporate campuses |
| Social Login (OAuth 2.0) | OAuth 2.0 authorisation flow via Facebook, Google, LinkedIn | Social profile data (subject to platform restrictions) | Medium-High — third-party data processing agreements | Hospitality, events, retail |
| Voucher / Paid Access | Pre-generated codes or payment gateway integration | Email (for receipt), payment reference | Medium — PCI DSS scope if card payment on-network | Hotels, stadiums, conference centres |
| PMS / Room Number Auth | Integration with Property Management System API | Guest identity from PMS record | Low — data already held under hotel booking | Hotels, resorts |
The social login model warrants particular attention. OAuth 2.0 flows via Facebook and Google provide a frictionless user experience and richer demographic data, but platform API changes have progressively restricted the data fields accessible to third-party applications. Network architects should not architect data pipelines that depend on social profile fields that may be deprecated. Email capture with explicit consent remains the most durable first-party data strategy.
Network Architecture and Segmentation
Proper network segmentation is the single most important security control in a captive portal deployment. The guest network must be architecturally isolated from the corporate LAN, any PCI-scoped cardholder data environment, and any operational technology networks. The recommended architecture is as follows:
- Dedicated Guest SSID mapped to a dedicated VLAN (e.g., VLAN 100) with no Layer 2 adjacency to corporate VLANs.
- Inter-client isolation enforced at the access point level, preventing guest devices from communicating with each other.
- DMZ routing for all guest traffic, with stateful firewall inspection before internet egress.
- Captive portal controller (hardware, virtual, or cloud-managed) sitting in the DMZ, handling redirect logic, session management, and policy enforcement.
- Separate DNS resolvers for the guest VLAN, with DNSSEC validation enabled.
For multi-site enterprise deployments, cloud-managed platforms such as Purple centralise this architecture across hundreds of venues. A policy change — updating the AUP text, adding a new social login provider, or modifying bandwidth tiers — is pushed once and propagates globally within minutes, eliminating the per-site configuration overhead that makes controller-based deployments operationally expensive at scale.
Implementation Guide
Phase 1: Requirements and Compliance Scoping
Before any technical configuration begins, define your compliance obligations. For EU and UK operations, GDPR Article 6 requires a lawful basis for processing personal data. For captive portal deployments, this is typically consent (Article 6(1)(a)) or legitimate interests (Article 6(1)(f)). Consent is the cleaner basis for marketing data; legitimate interests may apply to security logging. Document your legal basis for each data category in your Record of Processing Activities (ROPA) under Article 30.
If your venue processes card payments on any network that shares infrastructure with your guest Wi-Fi — even via shared uplink switches — you must assess your PCI DSS scope. The safest approach is complete network isolation: guest Wi-Fi on a separate physical or logically isolated network with no path to the cardholder data environment.
Phase 2: Network Design and Infrastructure
Deploy your guest SSID on a dedicated VLAN. Trunk this VLAN to your uplink switches and verify the trunk configuration before proceeding — a misconfigured trunk is the most common cause of guests inadvertently appearing on the corporate network. Configure DHCP for the guest VLAN with a short lease time (1–4 hours) to reclaim IP addresses efficiently in high-turnover environments.
Select your captive portal deployment model: controller-based (on-premises hardware or virtual appliance) or cloud-managed (SaaS platform). For organisations with more than five sites, cloud-managed is strongly recommended for operational efficiency. Purple's platform supports over 400 hardware integrations including Cisco Meraki, Aruba, Ruckus, and Ubiquiti, enabling deployment without replacing existing access point infrastructure.
Phase 3: Portal Configuration and Branding
With Purple's platform, splash page customisation is achieved through a drag-and-drop editor supporting full HTML/CSS override for organisations requiring pixel-perfect brand alignment. Key configuration elements include:
- Brand assets: Logo, colour palette, background imagery, and font selection.
- Language localisation: Purple supports automatic device language detection across 25+ languages, presenting the portal in the user's device language without manual selection.
- Authentication flow: Configure your chosen authentication method(s). Multiple methods can be offered simultaneously — for example, email registration and click-through — with the click-through option available as a fallback for users unwilling to register.
- Consent management: Configure separate, independently optional checkboxes for AUP acceptance (required for access) and marketing opt-in (optional). Ensure the marketing checkbox is unchecked by default. Link to your privacy policy from the portal page.
- Post-authentication redirect: Configure a meaningful redirect URL — your loyalty programme, a promotional landing page, or your venue app download page.
- Session parameters: Set session duration appropriate to your venue type. Hotels typically use 24-hour sessions; high-turnover retail may use 4–8 hours; events may use event-duration sessions.
Phase 4: Security Hardening
Apply the following security controls before go-live:
- Deploy the portal exclusively over HTTPS with a valid TLS certificate from a trusted CA. Renew certificates automatically using Let's Encrypt or your CA's ACME protocol support. Set a calendar reminder 30 days before expiry as a manual backstop.
- Enable 802.11w Management Frame Protection on the guest SSID. This is mandatory under WPA3 and mitigates deauthentication attacks used in evil twin scenarios.
- Configure wireless intrusion detection to alert on rogue SSIDs matching your guest SSID name.
- Enable per-user rate limiting at the access point level to prevent bandwidth monopolisation and mitigate denial-of-service from individual devices.
- Configure session timeout and idle timeout policies. An idle timeout of 30–60 minutes reclaims gateway sessions from devices that have left the venue.
Phase 5: Testing and Go-Live
Test the complete authentication flow on the following device/OS combinations before go-live: iOS Safari (latest), Android Chrome (latest), Windows 11 Edge, macOS Safari, and Android Firefox. Verify that the CNA pop-up triggers correctly on iOS and Android. Test certificate validity — navigate directly to the portal URL in a browser and confirm no certificate warnings. Test the post-authentication redirect. Test bandwidth tier enforcement if applicable. Document test results.
Best Practices
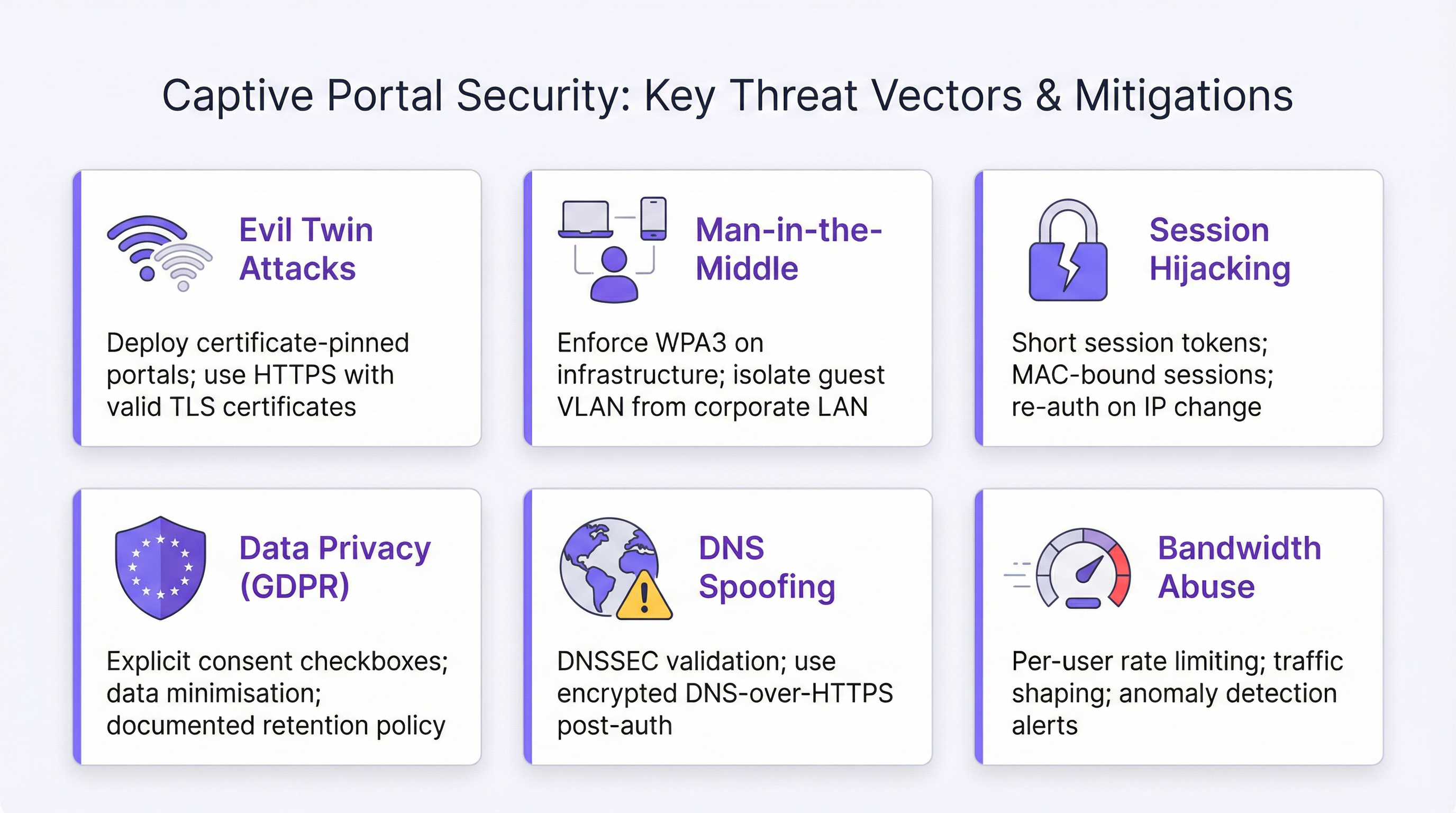
Security Best Practices
The most significant security risks associated with captive Wi-Fi portals are evil twin attacks, man-in-the-middle interception, session hijacking, and DNS spoofing. Each has a defined mitigation strategy.
Evil twin attacks are mitigated through HTTPS enforcement with valid TLS certificates, 802.11w Management Frame Protection, and wireless IDS monitoring. A user connecting to a rogue AP will receive a certificate warning if the attacker cannot obtain a valid certificate for your portal domain — which they cannot, assuming your domain is properly controlled.
Man-in-the-middle interception is addressed through strict VLAN segmentation, inter-client isolation, and routing all guest traffic through a stateful firewall. Post-authentication, encourage users to connect to sites over HTTPS — a note on the post-auth landing page is sufficient.
Session hijacking is mitigated by using session tokens rather than MAC addresses as the sole authorisation identifier, setting appropriate session durations, and implementing re-authentication triggers on IP address changes. Note that MAC address randomisation — enabled by default on iOS 14+, Android 10+, and Windows 10+ — means MAC-based session persistence is no longer reliable. Session tokens tied to authenticated identity are the correct approach.
DNS spoofing is addressed through DNSSEC validation on your guest DNS resolvers and, post-authentication, encouraging or enforcing DNS-over-HTTPS for guest traffic.
GDPR Compliance Checklist
The following controls are required for GDPR-compliant captive portal operation in UK and EU jurisdictions:
- Consent checkboxes unchecked by default.
- Separate, independently optional checkboxes for AUP acceptance and marketing opt-in.
- Clear, plain-language description of what data is collected and why.
- Link to privacy policy on the portal page.
- Documented data retention and deletion policy.
- Data Processing Agreements with all third-party processors (CRM platforms, analytics tools).
- Record of Processing Activities (ROPA) entry covering the captive portal data collection.
- Process for responding to Subject Access Requests within 30 days.
- Process for data deletion on request.
Operational Best Practices
The most common operational failure in enterprise captive portal deployments is the "set and forget" pattern: the portal is deployed, it works, and it receives no further attention until something breaks. Implement a quarterly operational review covering: TLS certificate expiry dates, social login API key validity, privacy policy link integrity, AUP text currency (particularly following regulatory changes), and authentication flow testing across all supported OS/browser combinations.
Troubleshooting & Risk Mitigation
Common Failure Modes
| Failure Mode | Symptoms | Root Cause | Resolution |
|---|---|---|---|
| Portal not appearing on iOS | Device connects but no CNA pop-up | Apple probe blocked by firewall | Allow outbound HTTP to captive.apple.com; ensure DNS resolves correctly |
| Certificate warning on portal | Browser shows "Not Secure" warning | Expired or self-signed TLS certificate | Renew certificate; configure auto-renewal |
| Redirect loop | User stuck in infinite redirect | Misconfigured post-auth redirect URL or firewall rule not updated | Verify firewall session authorisation; check redirect URL configuration |
| Social login failure | OAuth flow returns error | API key expired or platform permission change | Regenerate API keys; review platform developer console for permission changes |
| Guests on corporate network | Guest devices appearing in corporate VLAN | VLAN trunk misconfiguration | Verify VLAN trunk on uplink switch; confirm SSID-to-VLAN mapping |
| MAC randomisation breaks sessions | Users re-prompted for login on reconnect | MAC-based session persistence fails with randomised MACs | Switch to token-based session management; increase session duration |
| Bandwidth tier not enforced | Premium users receive same throughput as free users | QoS policy not applied at AP level | Configure per-user rate limiting at access point, not only at gateway |
Risk Register
For enterprise risk management purposes, the key risks associated with captive portal deployments and their mitigations are as follows. GDPR non-compliance (likelihood: medium, impact: high) is mitigated through documented consent flows, ROPA entries, and quarterly compliance reviews. TLS certificate expiry (likelihood: medium, impact: high — portal becomes inaccessible) is mitigated through automated certificate renewal and calendar-based monitoring. Evil twin attack (likelihood: low, impact: high) is mitigated through 802.11w, WIDS monitoring, and HTTPS enforcement. Data breach via guest network (likelihood: low, impact: very high) is mitigated through strict VLAN segmentation and firewall policy.
ROI & Business Impact

Measuring Return on Investment
The ROI of a captive Wi-Fi portal deployment is measured across three dimensions: direct revenue generation, operational cost reduction, and marketing and data value.
Direct revenue generation applies primarily to venues offering tiered access — hotels, stadiums, and conference centres that sell premium bandwidth packages. A 200-room hotel charging £5 per day for premium Wi-Fi to 30% of guests generates approximately £110,000 in annual incremental revenue from a deployment that costs a fraction of that figure.
Operational cost reduction is driven by centralised management. Purple's enterprise customers report a 90% reduction in on-site IT engineer visits following migration from controller-based to cloud-managed deployments. For a retail chain with 200 locations, eliminating even two engineer visits per site per year at £150 per visit represents £60,000 in annual savings.
Marketing and data value is the most strategically significant dimension. A captive portal that captures email addresses with marketing consent builds a first-party data asset that is increasingly valuable as third-party cookie deprecation removes alternative data sources. Purple's platform integrates with over 400 CRM and marketing automation connectors, enabling captured data to flow directly into Salesforce, HubSpot, Mailchimp, and equivalent platforms. The analytics layer — footfall heatmaps, dwell time analysis, repeat visitor identification, and peak hour reporting — provides operational intelligence that informs staffing, store layout, and promotional timing decisions.
Key Performance Indicators
| KPI | Definition | Target Benchmark |
|---|---|---|
| Portal Adoption Rate | % of connected devices that complete authentication | >60% for hospitality; >40% for retail |
| Data Capture Rate | % of authenticated sessions that provide email address | >50% for form-based portals |
| Marketing Opt-In Rate | % of authenticated sessions that consent to marketing | 20–35% is typical for hospitality |
| Session Duration | Average time a device remains connected post-auth | Venue-dependent; track trends over time |
| Repeat Visitor Rate | % of authenticated sessions from previously seen identities | Indicates loyalty; target >30% for retail |
| Portal Uptime | % of time the portal is available and functioning | >99.9% SLA target |
| TLS Certificate Days Remaining | Days until certificate expiry | Alert threshold: <30 days |
Case Study: Brussels South Charleroi Airport
Brussels South Charleroi Airport deployed Purple's captive portal platform to manage guest Wi-Fi across its terminal. The deployment achieved a 25% fan connection rate per event, captured 9.2 million customer visits during the first 24 months, and delivered an 842% return on investment. The portal's survey integration enabled real-time passenger satisfaction data collection, replacing expensive manual survey processes and providing actionable operational intelligence to venue management.
Case Study: Major UK Retail Chain
A major UK retail chain operating across 150+ locations deployed Purple's platform to unify guest Wi-Fi management and analytics. Prior to deployment, the chain had no visibility into in-store dwell time, footfall patterns, or the relationship between Wi-Fi usage and purchasing behaviour. Following deployment, the analytics layer identified that stores with above-average dwell times in the café area had 23% higher average transaction values. This insight drove a store layout redesign programme that delivered measurable revenue uplift within two quarters. The centralised management capability reduced IT operational overhead by eliminating per-site configuration management, with the 90% reduction in engineer visits translating to significant annual cost savings across the estate.
Key Terms & Definitions
Captive WiFi Portal
A network access control mechanism that intercepts unauthenticated HTTP/HTTPS traffic from newly connected devices and redirects it to a web-based landing page. The user must complete a defined action — accepting terms, submitting credentials, or making a payment — before the network gateway grants full internet access. The portal creates a 'walled garden' that controls the initial network access event.
IT teams encounter this term when specifying guest Wi-Fi requirements, evaluating network access control solutions, or auditing existing deployments. It is the foundational concept for all guest connectivity management in hospitality, retail, events, and public-sector environments.
Captive Network Assistant (CNA)
A built-in OS mechanism that detects the presence of a captive portal and automatically launches a lightweight browser window to display the portal page. iOS probes captive.apple.com, Android probes connectivitycheck.gstatic.com, and Windows uses Network Location Awareness. When these probes return unexpected responses, the CNA triggers automatically.
Network architects must ensure their firewall and DNS configuration does not inadvertently block CNA probes, as this prevents the portal from appearing automatically on user devices — the most common cause of 'portal not showing' support tickets.
VLAN (Virtual Local Area Network)
A logical network segmentation technique that isolates traffic at Layer 2 of the OSI model. In captive portal deployments, the guest SSID is mapped to a dedicated VLAN that is architecturally isolated from corporate VLANs, preventing guest traffic from reaching internal systems.
VLAN configuration is the foundational security control in any captive portal deployment. Misconfigured VLAN trunking — where the guest VLAN is not properly isolated from corporate VLANs — is the most common and most serious security failure mode in enterprise guest Wi-Fi deployments.
OAuth 2.0
An open authorisation framework (RFC 6749) that enables third-party applications to obtain limited access to user accounts on platforms such as Facebook, Google, and LinkedIn. In captive portal deployments, OAuth 2.0 is used to implement social login — the user authorises the portal to access their social profile, providing identity verification without requiring a separate account.
IT teams evaluating social login authentication must understand that OAuth 2.0 introduces a dependency on third-party API availability and is subject to platform policy changes that may restrict the data fields accessible to the portal application. Social platform API changes have historically reduced the demographic data available via social login without advance notice.
IEEE 802.11w (Management Frame Protection)
An IEEE 802.11 amendment that provides cryptographic protection for management frames — the control messages that govern Wi-Fi association, disassociation, and authentication. Without 802.11w, management frames can be spoofed by attackers to force device disconnection (deauthentication attacks), a technique used in evil twin attacks. 802.11w is mandatory under WPA3.
Network architects deploying captive portals in high-risk environments (airports, financial institutions, healthcare) should enable 802.11w on guest SSIDs where supported by the access point hardware. It significantly raises the bar for evil twin attacks by preventing the deauthentication frames that force devices to reconnect to a rogue AP.
GDPR Article 30 (Record of Processing Activities)
A GDPR requirement for organisations processing personal data to maintain a documented record of all data processing activities, including the categories of data processed, the purposes of processing, data retention periods, and details of any third-party processors. Captive portal deployments that collect personal data (email addresses, social profile data) must have a corresponding ROPA entry.
IT managers are frequently responsible for ensuring that new data collection systems — including captive portals — are documented in the organisation's ROPA before go-live. Failure to maintain an accurate ROPA is a GDPR compliance gap that can result in ICO enforcement action, particularly following a data breach.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards established by the PCI Security Standards Council to protect cardholder data. For captive portal deployments in retail environments, PCI DSS requires complete network isolation between the guest Wi-Fi network and any system that stores, processes, or transmits cardholder data (the Cardholder Data Environment, or CDE).
Retail IT teams must assess PCI DSS scope when deploying guest Wi-Fi. If the guest Wi-Fi network shares any infrastructure — switches, uplinks, or firewalls — with the PCI-scoped network, the guest network may be brought into PCI scope, significantly increasing compliance obligations and audit costs.
MAC Address Randomisation
A privacy feature enabled by default on iOS 14+, Android 10+, and Windows 10+ that generates a random MAC address for each Wi-Fi network a device connects to, rather than using the device's hardware MAC address. This prevents cross-network tracking of devices by their MAC address.
MAC address randomisation directly impacts captive portal session management and analytics. Any system that uses MAC addresses as stable device identifiers for repeat visitor detection, session persistence, or security policy enforcement will produce incorrect results on modern devices. The correct approach is to use authenticated identity (email, social profile ID) as the stable identifier.
Walled Garden
A network configuration in which unauthenticated devices have access only to a restricted set of IP addresses and URLs — typically the captive portal itself and any resources required for the portal to function (CDN assets, OAuth endpoints) — while all other internet traffic is blocked until authentication is complete.
IT teams configuring captive portals must carefully define the walled garden whitelist. Common omissions include: the portal's CDN asset URLs (causing the portal page to render without styling), Apple's CNA probe URL (causing the portal not to appear on iOS), and OAuth provider endpoints (causing social login to fail). A well-documented walled garden configuration is essential for reliable portal operation.
DSCP (Differentiated Services Code Point)
A field in the IP packet header used to classify and manage network traffic for Quality of Service (QoS) purposes. In captive portal deployments with tiered bandwidth, DSCP marking is used to classify traffic from premium-tier users so that QoS policies at the access point and gateway can enforce differentiated throughput limits.
IT teams implementing paid bandwidth tiers must configure DSCP marking and corresponding QoS policies at the access point level, not only at the gateway. Gateway-only QoS policies may not differentiate traffic correctly when multiple users share the same access point, resulting in premium users receiving the same throughput as free-tier users.
Case Studies
A 350-room international hotel needs to deploy a captive wifi portal that authenticates guests using their room number and surname, captures email addresses for the loyalty programme, complies with GDPR, and provides tiered bandwidth (free standard / paid premium at £8/day). The hotel uses Opera PMS and Cisco Meraki access points. What is the recommended deployment architecture and configuration?
The recommended deployment uses Purple's enterprise platform integrated with Cisco Meraki via the Meraki API. Step 1: Configure a dedicated guest SSID on Meraki mapped to VLAN 200, with client isolation enabled and a separate DHCP scope (e.g., 10.200.0.0/22 providing up to 1,022 addresses for a 350-room hotel with multiple devices per guest). Step 2: Configure Purple as the captive portal controller, pointing the Meraki splash page URL to Purple's hosted portal endpoint. Step 3: Enable the Opera PMS integration in Purple's connector library. Configure the authentication flow to present a room number and surname form as the primary authentication method, with email address capture as a mandatory second step post-PMS validation. Step 4: Configure the GDPR consent flow: AUP acceptance checkbox (required, unchecked by default) and marketing opt-in checkbox (optional, unchecked by default) with a link to the hotel's privacy policy. Step 5: Configure two bandwidth tiers in Purple — Standard (5 Mbps down / 2 Mbps up) and Premium (25 Mbps down / 10 Mbps up). Integrate with a payment gateway (Stripe is supported) for the Premium tier purchase flow. Configure Meraki QoS policies using DSCP marking to enforce tier differentiation at the AP level. Step 6: Set session duration to 24 hours with a 60-minute idle timeout. Step 7: Configure post-authentication redirect to the hotel's loyalty programme enrolment page. Step 8: Enable Purple's analytics dashboard and configure a CRM connector to push captured email addresses and opt-in status to the hotel's CRM platform. Test on iOS Safari, Android Chrome, and Windows Edge before go-live.
A national retail chain with 180 stores wants to deploy a unified captive wifi portal programme. Requirements: email capture with marketing consent, footfall analytics by store, GDPR compliance, integration with Salesforce Marketing Cloud, and no replacement of existing Aruba access points. The IT team has three engineers for the entire estate. How should this be structured?
This is a cloud-managed deployment scenario where on-premises infrastructure is non-negotiable. Step 1: Audit existing Aruba infrastructure for firmware versions and confirm compatibility with Purple's Aruba integration (Purple supports Aruba Instant and Aruba Central deployments). Step 2: Configure a standardised guest SSID template in Purple — one configuration that will be pushed to all 180 stores. Define VLAN assignment, DHCP parameters, and firewall policy in the template. Step 3: Design the portal template: brand assets, email registration form with separate AUP and marketing opt-in checkboxes, and a post-auth redirect to the chain's loyalty app download page. Configure the portal in 25+ languages to support stores in international markets if applicable. Step 4: Configure the Salesforce Marketing Cloud connector in Purple. Map captured fields (email, first name, opt-in status, store ID, visit timestamp) to the corresponding Salesforce objects. Ensure a Data Processing Agreement is in place with Salesforce. Step 5: Enable Purple's footfall analytics. Configure store-level dashboards showing daily unique visitors, peak hours, dwell time, and repeat visitor rate. Set up automated weekly reports delivered to store managers and a consolidated estate-level report for the IT and marketing leadership teams. Step 6: Roll out in waves — pilot with 10 stores, validate data flows and Salesforce integration, then deploy remaining 170 stores. With cloud management, each store deployment requires only VLAN configuration on the local switch and SSID assignment on existing APs — typically 30–45 minutes per site for a trained engineer. Step 7: Document all data flows in the ROPA. Establish a quarterly operational review process.
A 60,000-capacity stadium is deploying captive wifi for matchday use. Expected peak concurrent users: 18,000. Requirements: fast authentication (under 10 seconds), event-duration sessions, sponsor branding on the portal, data capture for the club's CRM, and integration with the club's ticketing system for fan verification. What are the key technical considerations and recommended architecture?
High-density stadium deployments require specific architectural decisions that differ from hospitality or retail scenarios. Step 1: Capacity planning. With 18,000 concurrent users, the DHCP scope must accommodate at least 25,000 addresses (allowing for churn). Use a /17 or /16 subnet for the guest VLAN. Configure DHCP lease times of 4 hours (event duration) rather than the default 24 hours to prevent address exhaustion across multiple events. Step 2: Authentication performance. Click-through with email capture is the recommended model for stadium deployments — social login OAuth flows introduce latency and depend on external API availability, which is a risk in high-concurrency scenarios. Configure the portal to be served from a CDN-backed endpoint to minimise latency under load. Step 3: Ticketing system integration. Configure a custom authentication field for ticket barcode or booking reference, validated against the ticketing system API. This provides fan identity verification and links Wi-Fi sessions to ticketing records, enabling post-event CRM segmentation by stand, ticket tier, and attendance frequency. Step 4: Sponsor branding. Purple's platform supports interstitial video and branded splash pages. Configure a sponsor-branded portal with the club's primary and secondary sponsors' assets. Rotate sponsor branding by event type if required. Step 5: Session management. Set session duration to match event duration (typically 3–4 hours) with no idle timeout — fans moving around the stadium should not be re-prompted. Step 6: Analytics. Configure Purple's real-time dashboard for the venue operations team, showing live concurrent connections by zone, authentication rate, and bandwidth utilisation.
Scenario Analysis
Q1. A conference centre hosts 50 events per year, ranging from 200-person seminars to 3,000-person trade shows. The venue's IT team has proposed a single captive portal configuration for all events, using click-through authentication with a generic venue-branded splash page. The sales team wants event-specific sponsor branding and delegate data capture for each event organiser. How would you resolve this conflict, and what is the recommended architecture?
💡 Hint:Consider whether a single portal configuration can serve both the IT team's operational simplicity requirement and the sales team's per-event customisation requirement. Evaluate whether Purple's platform supports per-event portal configurations managed from a central account.
Show Recommended Approach
The conflict is resolvable without choosing between operational simplicity and commercial flexibility. The recommended architecture uses Purple's multi-portal capability, where a single platform account manages multiple portal configurations — one per event or event type — all deployed to the same physical access point infrastructure. The IT team maintains a single platform to manage, while the sales team (or event organisers, via delegated access) can configure event-specific branding, authentication flows, and data capture fields for each event. The recommended authentication model for conference events is email registration with marketing opt-in, not click-through — event organisers have a legitimate commercial interest in capturing delegate contact data, and click-through provides no value for post-event follow-up. Configure a base portal template with the venue's brand framework, then allow per-event customisation of sponsor logos, colour accents, and post-auth redirect URLs. Set session duration to event duration (typically 8-10 hours for a full-day event). Configure data export per event so each organiser receives only their delegates' data, not a combined dataset from all events — this is both a GDPR requirement (data minimisation) and a commercial necessity. The GDPR consent flow must be configured so that the marketing opt-in clearly identifies the event organiser as the data controller, not the venue — or alternatively, the venue acts as data processor under a Data Processing Agreement with each event organiser.
Q2. Your organisation's security audit has flagged that the existing captive portal deployment uses a self-signed TLS certificate, has no inter-client isolation configured, and the guest VLAN is on the same /16 subnet as the corporate network (different VLANs, but same IP range with no firewall between them). Prioritise the remediation actions and explain your reasoning.
💡 Hint:Assess each finding by its potential impact and exploitability. Consider which finding represents an active risk to corporate data versus which represents a user experience or compliance issue.
Show Recommended Approach
Prioritise remediation in the following order. Priority 1 (Immediate): The absence of a firewall between the guest VLAN and the corporate network is a critical vulnerability. Even with VLAN separation, if there is no stateful firewall enforcing policy between the VLANs, a guest device that obtains or guesses a corporate IP address can potentially reach corporate systems. This is an active data breach risk. Remediation: implement a stateful firewall rule set that explicitly denies all traffic from the guest VLAN to the corporate VLAN, with logging enabled. This must be done before any other remediation. Priority 2 (Within 48 hours): Enable inter-client isolation on the guest SSID. Without it, guest devices can communicate directly with each other at Layer 2, enabling ARP poisoning, traffic interception between guests, and lateral movement within the guest network. Priority 3 (Within one week): Replace the self-signed TLS certificate with a certificate from a trusted CA. A self-signed certificate triggers browser warnings that train users to ignore certificate errors — a conditioning that makes them vulnerable to future MITM attacks. Use Let's Encrypt for automated, free certificate issuance and renewal. The self-signed certificate is a compliance and user experience issue rather than an active data breach risk, which is why it is Priority 3 rather than Priority 1 — but it must be remediated within the same change window if possible.
Q3. A 500-store UK retail chain is preparing for a GDPR audit. The DPO has identified that the captive portal has been collecting email addresses and marketing opt-ins for three years, but the consent flow has a pre-checked marketing opt-in checkbox. The DPO estimates that approximately 2.3 million email records in the CRM may have been collected under invalid consent. What are the immediate actions required, and how should the organisation remediate the historical data issue?
💡 Hint:Consider both the forward-looking remediation (fixing the consent flow) and the backward-looking remediation (handling the 2.3 million potentially invalid consent records). Reference GDPR Article 7 on conditions for consent and the ICO's guidance on consent.
Show Recommended Approach
Immediate actions: First, fix the portal consent flow today. Remove the pre-checked marketing opt-in checkbox and replace it with an unchecked checkbox. This stops the ongoing collection of invalid consent and is the highest-priority action. Second, document the change with a timestamp and retain evidence for the audit. Third, notify the DPO and legal counsel — this is a reportable compliance gap that should be disclosed proactively to the ICO rather than discovered during audit. For the historical 2.3 million records: GDPR Article 7(1) requires that the controller be able to demonstrate that consent was given. A pre-checked checkbox does not constitute valid consent under GDPR Recital 32, which explicitly states that silence, pre-ticked boxes or inactivity should not constitute consent. The organisation has three options for the historical records. Option 1 (Recommended): Send a re-consent campaign to the 2.3 million contacts, clearly explaining that their marketing consent is being re-confirmed, providing an easy opt-out, and stating that contacts who do not actively re-confirm will be removed from marketing lists within 30 days. This is the cleanest remediation and demonstrates good faith to the ICO. Option 2: Suppress all 2.3 million records from marketing use immediately, retaining them only for the purposes for which valid consent exists. Option 3: Delete all records collected under invalid consent. The re-consent campaign (Option 1) is recommended as it preserves commercial value while demonstrating active remediation. Document the entire remediation process for the audit.
Key Takeaways
- ✓A captive wifi portal is simultaneously a network access control mechanism, a GDPR compliance instrument, a first-party data collection tool, and — when deployed on a platform like Purple — a business intelligence gateway that delivers measurable ROI through footfall analytics, CRM integration, and operational insights.
- ✓Network segmentation is the foundational security control: the guest VLAN must be completely isolated from the corporate LAN and any PCI-scoped environment, with a stateful firewall enforcing the boundary. This must be verified before any portal configuration begins.
- ✓Authentication model selection drives everything downstream — click-through for public-sector access provision, form/social login for hospitality and retail data capture, paid/voucher for revenue generation. Changing the model post-deployment requires reconfiguring consent flows and data pipelines.
- ✓GDPR compliance requires separate, independently optional, unchecked-by-default checkboxes for AUP acceptance and marketing opt-in. Bundling these or pre-checking the marketing box is a violation that has attracted ICO enforcement action.
- ✓MAC address randomisation — enabled by default on iOS 14+, Android 10+, and Windows 10+ — makes MAC-based session management and repeat visitor analytics unreliable. Use authenticated identity (email, social profile ID) as the stable identifier for cross-session analytics.
- ✓The 'set and forget' portal is the most common enterprise failure mode. Implement a quarterly operational review covering TLS certificate expiry, social login API key validity, privacy policy link integrity, and end-to-end authentication flow testing on iOS and Android.
- ✓Cloud-managed platforms become operationally mandatory above five sites. For estates of 20+ venues, the per-site configuration overhead of controller-based deployments typically exceeds the annual platform subscription cost of cloud-managed alternatives within the first year.



