Cloud-Managed WiFi vs Controller-Based WiFi: Which Should You Choose?
This guide provides a vendor-neutral technical comparison of cloud-managed WiFi and controller-based (on-premise) WiFi architectures, helping IT managers, network architects, and CTOs make an informed deployment decision. It covers the architectural trade-offs across scalability, data sovereignty, cost model, and offline resilience, with real-world case studies from hospitality, retail, and public-sector environments. It also explains how Purple's WiFi intelligence platform integrates with either architecture to deliver guest experience management, first-party data capture, and GDPR-compliant analytics.
🎧 Listen to this Guide
View Transcript

Executive Summary
The decision between cloud-managed WiFi and controller-based WiFi is one of the most consequential architectural choices a network team will make this decade. Both models deliver enterprise-grade wireless connectivity, but they differ fundamentally in where intelligence resides, how they scale, what they cost over time, and how they handle compliance obligations.
Cloud-managed WiFi moves the controller function to a vendor-hosted cloud platform, enabling zero-touch provisioning, automatic firmware updates, and single-pane-of-glass management across unlimited sites. Controller-based WiFi keeps that intelligence on-premises, providing maximum data sovereignty, offline resilience, and granular control — at the cost of higher CapEx and greater operational overhead.
For most multi-site operators — hotel chains, retail estates, stadium operators, and local authorities — cloud-managed WiFi now represents the operationally superior choice. For large single-campus deployments with strict data residency requirements, on-premises controllers remain compelling. In either case, Purple's WiFi management platform operates as an infrastructure-agnostic overlay, adding guest experience management, GDPR-compliant data capture, and actionable analytics on top of whichever architecture you choose.
Technical Deep-Dive
What Is Cloud-Managed WiFi?
Cloud-managed WiFi is a wireless LAN architecture in which the controller function — authentication, policy enforcement, radio frequency management, firmware distribution, and monitoring — is hosted in a vendor-operated cloud platform rather than on dedicated on-premises hardware. Access points at local sites connect to the cloud management platform over encrypted HTTPS or CAPWAP tunnels, receiving their configuration and sending telemetry data upstream. The data plane — the actual forwarding of user traffic — typically remains local at the access point, ensuring that a WAN outage does not interrupt active user sessions.
Leading cloud-managed WiFi platforms include Cisco Meraki, Aruba Central (HPE), Juniper Mist, Extreme Networks CloudIQ, and Ruckus One. Each platform provides a web-based management console, a RESTful API for integration with third-party systems, and varying degrees of AI-driven RF optimisation and anomaly detection.
What Is Controller-Based WiFi?
Controller-based WiFi is the traditional enterprise wireless architecture in which a physical or virtual wireless LAN controller (WLC) is deployed on-premises to manage all access points within a site or campus. The controller handles IEEE 802.1X authentication via RADIUS, enforces QoS and security policies, manages fast roaming between access points (IEEE 802.11r), and provides centralised monitoring and troubleshooting. In a split-tunnel or local-switching configuration, user traffic is forwarded locally at the access point; in a centralised-switching configuration, all traffic is tunnelled back to the controller.
Major controller-based platforms include Cisco Catalyst Wireless (formerly AireOS), Aruba Mobility Controllers, Juniper Mist with on-premises virtual controllers, and Ruckus SmartZone. These platforms are mature, feature-rich, and widely deployed across enterprise, healthcare, and public-sector environments.
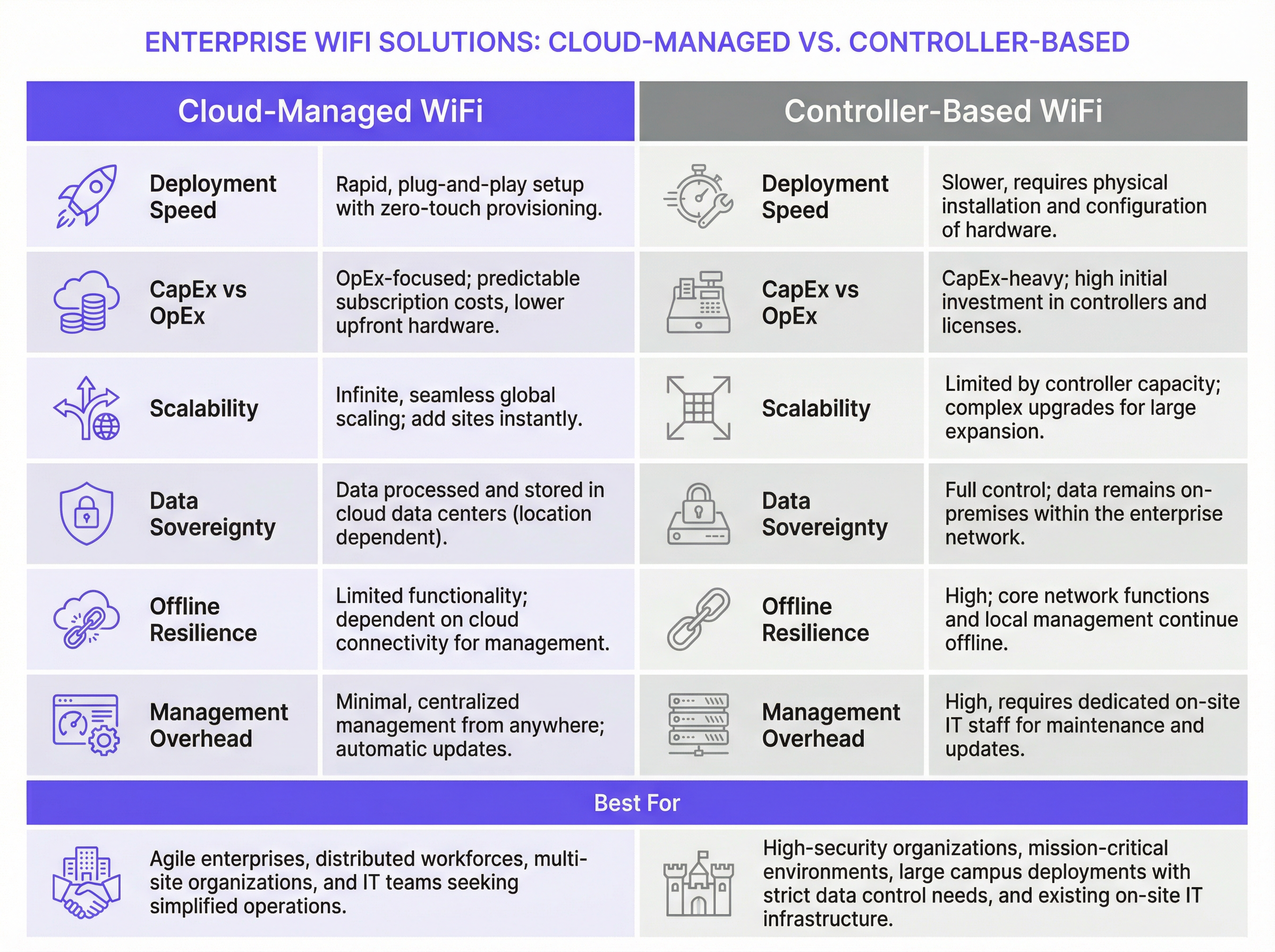
Architectural Trade-Offs: A Structured Comparison
| Dimension | Cloud-Managed WiFi | Controller-Based WiFi |
|---|---|---|
| Deployment Speed | Rapid; zero-touch provisioning via pre-staged AP configuration | Slower; requires on-site controller installation and AP registration |
| Cost Model | OpEx-dominant; per-AP subscription licensing | CapEx-dominant; hardware purchase plus annual support contracts |
| Scalability | Effectively unlimited; add sites without hardware changes | Limited by controller capacity; requires hardware upgrades to scale |
| Offline Resilience | Local traffic forwarding continues; management access lost | Full management and data plane functionality maintained locally |
| Data Sovereignty | Management data processed in cloud (region-dependent) | All data remains within the enterprise network boundary |
| Firmware Management | Automatic, vendor-managed updates | Manual or scheduled; requires IT team oversight |
| Advanced Features | Improving rapidly; AI-driven RF optimisation available | Mature; advanced QoS, location services, and policy granularity |
| Multi-Site Management | Single pane of glass across all sites natively | Requires additional NOC tooling or per-site management |
| IT Overhead | Low; minimal on-site expertise required | High; requires skilled wireless engineers for maintenance |
Security Architecture Considerations
Both architectures support enterprise-grade security standards. WPA3-Enterprise with IEEE 802.1X authentication is available on all modern cloud-managed and controller-based platforms. RADIUS integration for centralised authentication is standard in both models. VLAN segmentation to isolate guest, staff, and IoT traffic is supported across all major vendors.
The key security distinction lies in the management plane. In a controller-based deployment, all management traffic remains within your network perimeter, which is a significant advantage for organisations subject to PCI DSS (which requires strict controls on cardholder data environments) or ISO 27001 certification requirements. In a cloud-managed deployment, management traffic traverses the public internet — albeit encrypted — and your security posture depends in part on the cloud vendor's own security controls and certifications.
For guest WiFi specifically, GDPR compliance requires that any personal data collected via a captive portal — including email addresses, social login tokens, or device identifiers — is captured with explicit, informed consent, stored securely, and subject to data subject rights including access and erasure. This obligation applies regardless of whether your underlying network is cloud-managed or controller-based. Purple's consent management framework addresses this requirement directly, providing timestamped consent records, automated data retention policies, and a self-service portal for data subject requests.
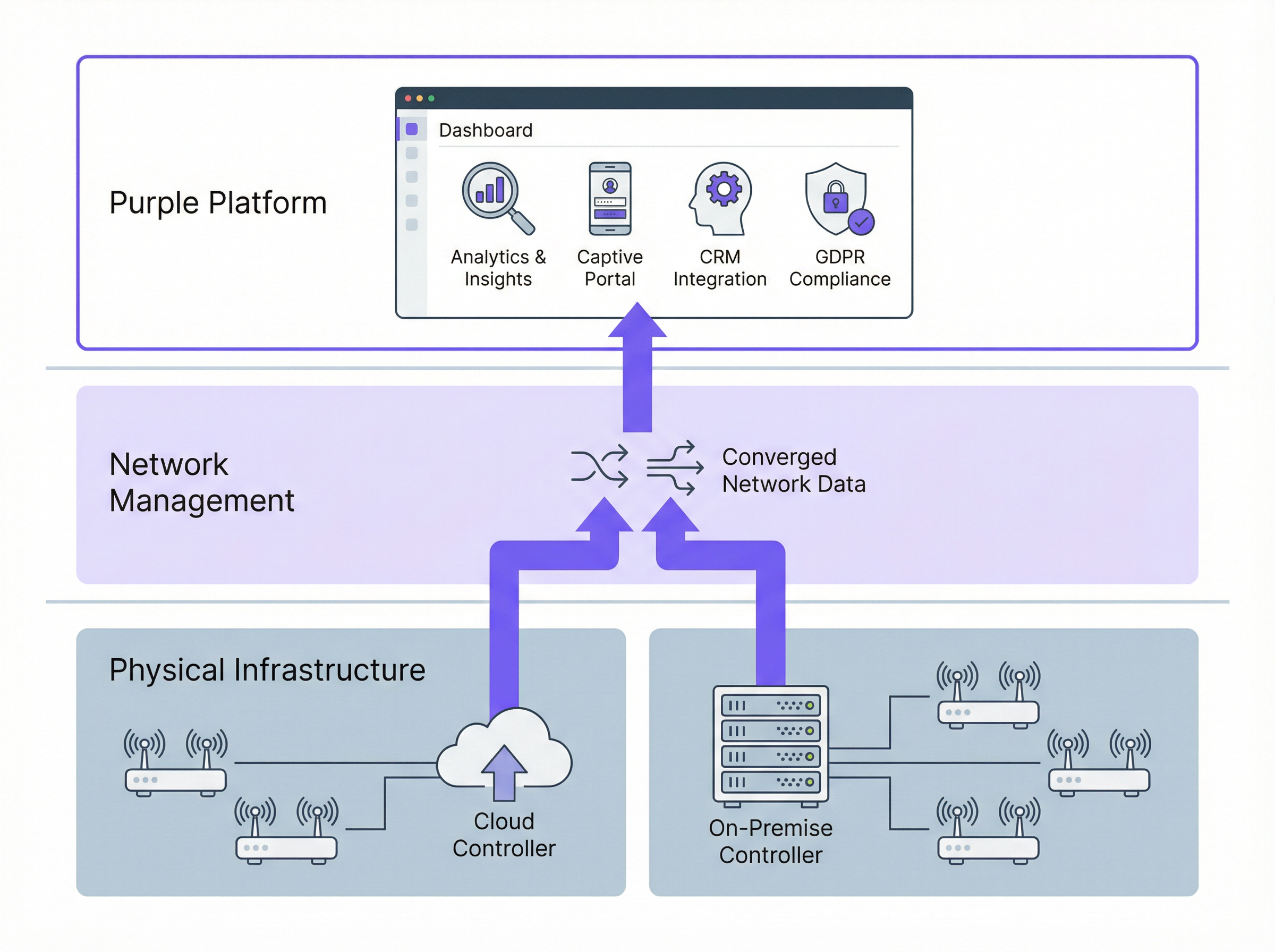
How Purple Integrates with Both Architectures
Purple operates as a WiFi intelligence overlay — it does not replace your network vendor, but augments it with a guest experience and analytics layer. Purple connects to your network infrastructure via standard APIs and RADIUS integration, regardless of whether your access points are managed by a cloud platform or an on-premises controller.
For guest WiFi, Purple provides a customisable captive portal that handles user authentication (social login, email, SMS verification, or the Purple App), GDPR-compliant consent capture, and seamless handoff to the network. For staff WiFi, Purple's identity-based networking capabilities enable automatic access provisioning and revocation tied to your HR or identity management system — ensuring that a departing employee's network access is terminated without manual intervention.
Purple's analytics platform then processes connection data to generate footfall metrics, dwell time analysis, new versus returning visitor ratios, and demographic insights. These analytics are available via Purple's dashboard, via API integration with your business intelligence tools, or via direct CRM connectors to platforms including Salesforce, HubSpot, and Microsoft Dynamics.
Implementation Guide
Step 1: Define Your Requirements Profile
Before evaluating vendors, document your requirements across five dimensions: site count and distribution (single campus versus multi-site estate); compliance obligations (GDPR, PCI DSS, data residency requirements); IT team capacity (can you support on-premises hardware at each site?); commercial objectives (do you need guest data capture and analytics?); and budget model (CapEx versus OpEx preference).
Step 2: Select Your Architecture Model
Apply the following decision logic. If you operate more than five geographically distributed sites, cloud-managed WiFi is almost certainly the right choice for your access layer — the operational savings from centralised management and zero-touch provisioning will outweigh the subscription costs within twelve to eighteen months. If you operate a single large campus with strict data sovereignty requirements, evaluate on-premises controllers, including virtual controller options that reduce hardware CapEx. If you have a mix of site types, consider a deliberate hybrid model with clearly defined criteria for each deployment type.
Step 3: Evaluate Network Vendors
Issue a structured RFP covering: AP hardware specifications (Wi-Fi 6E support, antenna design, PoE requirements); management platform capabilities (API completeness, monitoring, alerting); security certifications (SOC 2 Type II for cloud platforms, ISO 27001); SLA commitments (uptime guarantees, support response times); and integration ecosystem (RADIUS, VLAN, third-party platform APIs).
Step 4: Deploy Purple as Your Intelligence Layer
Once your network infrastructure is selected, deploy Purple to add guest experience management and analytics. Purple's deployment process involves: configuring a dedicated guest SSID on your network infrastructure; pointing the SSID's splash page or RADIUS authentication to Purple's cloud platform; customising the captive portal with your brand identity and consent flows; and connecting Purple to your CRM and marketing automation platforms via the integrations marketplace.
Step 5: Validate Compliance and Security
Before go-live, conduct a compliance review covering: GDPR consent flow validation (ensure consent is explicit, granular, and recorded); network segmentation verification (confirm guest traffic cannot reach internal systems); PCI DSS scope assessment (if payment card data is processed anywhere on the network); and penetration testing of the guest WiFi environment.
Best Practices
Segment aggressively. Always deploy separate SSIDs for guest, staff, and IoT devices, each mapped to a dedicated VLAN with appropriate firewall policies. Guest traffic should be isolated from internal systems by default, with internet-only access unless a specific business requirement justifies otherwise.
Enforce WPA3 where hardware supports it. Wi-Fi 6 and Wi-Fi 6E access points universally support WPA3. For guest networks, WPA3-Personal with Simultaneous Authentication of Equals (SAE) provides significantly stronger protection against offline dictionary attacks than WPA2-PSK. For staff networks, WPA3-Enterprise with 802.1X provides per-user authentication and forward secrecy.
Plan for OpenRoaming. The Wi-Fi Alliance's OpenRoaming standard, built on Passpoint (IEEE 802.11u), allows users to connect automatically to any OpenRoaming-enabled network using credentials from their home identity provider — their mobile network, their employer, or a platform like the Purple App. Deploying OpenRoaming eliminates captive portal friction for returning users while maintaining authenticated, secure access. Purple supports OpenRoaming natively.
Automate firmware management. Unpatched firmware is one of the most common attack vectors in enterprise WiFi deployments. Cloud-managed platforms handle this automatically; for on-premises deployments, establish a quarterly firmware review cycle and use your controller's scheduled update functionality to push updates during maintenance windows.
Monitor continuously. Deploy WIDS (Wireless Intrusion Detection System) capabilities, available on all major enterprise platforms, to detect rogue access points, deauthentication attacks, and evil twin attacks. Integrate WIDS alerts with your SIEM platform for centralised security monitoring.
Troubleshooting and Risk Mitigation
Risk: Cloud management platform outage. Mitigation: Verify that your chosen platform supports local AP survivability — the ability for access points to continue operating with their last-known configuration if cloud connectivity is lost. All major cloud platforms (Meraki, Aruba Central, Juniper Mist) support this capability. Test it explicitly during your acceptance testing phase.
Risk: GDPR non-compliance in guest data capture. Mitigation: Use a platform like Purple that provides a pre-built, legally reviewed consent management framework. Avoid building custom captive portals without legal review — the specific language, granularity, and recording requirements for GDPR consent are precise and frequently misimplemented.
Risk: Controller hardware failure in on-premises deployments. Mitigation: Deploy controllers in high-availability pairs with automatic failover. For virtual controllers, ensure the underlying hypervisor infrastructure has appropriate redundancy. Document your recovery time objective (RTO) and test failover procedures annually.
Risk: Insufficient WAN bandwidth for cloud management. Mitigation: Cloud management traffic is typically modest — one to two megabits per second per hundred access points — but spikes during firmware updates. Schedule firmware updates during off-peak hours and use QoS policies to prioritise management traffic over guest data if WAN bandwidth is constrained.
Risk: Vendor lock-in. Mitigation: Evaluate the openness of your chosen platform's API and its support for vendor-neutral standards (RADIUS, 802.1X, VLAN tagging). Purple's infrastructure-agnostic architecture means you can change your underlying network vendor without losing your guest data, analytics history, or CRM integrations.
ROI and Business Impact
The business case for cloud-managed WiFi with Purple as the intelligence layer is well-established across multiple verticals. McDonald's, a Purple customer, achieved a 90% reduction in on-site IT engineer visits by deploying cloud-managed guest WiFi with centralised management — a direct operational cost saving that funded the platform investment within the first year. Brussels South Charleroi Airport achieved an ROI of 10,630% from Purple's guest WiFi analytics, driven by improved passenger experience, increased dwell time in retail areas, and data-driven commercial decisions.
For a typical 40-property hotel estate, the financial model looks approximately as follows. Controller-based deployment: £80,000 to £120,000 in controller hardware CapEx, plus £15,000 to £25,000 per year in support contracts, plus engineering time for maintenance. Cloud-managed deployment: £0 controller hardware, plus £8,000 to £15,000 per year in platform subscriptions, plus significantly reduced engineering overhead. The cloud-managed model typically reaches break-even within 18 to 24 months and delivers lower total cost of ownership over a five-year horizon.
The commercial value of Purple's analytics layer adds a further dimension to the ROI calculation. First-party guest data captured via Purple's captive portal — email addresses, visit frequency, demographic data — has direct commercial value for marketing campaigns, loyalty programme enrolment, and personalised communications. Organisations that integrate Purple with their CRM platform typically report a 25 to 40% increase in marketing-qualified contacts within the first twelve months of deployment.
Listen to the Purple Technical Briefing podcast for a 10-minute audio walkthrough of this guide, covering architecture trade-offs, implementation recommendations, and rapid-fire Q&A.
Key Terms & Definitions
Cloud-Managed WiFi
A wireless LAN architecture in which the controller function — including authentication, policy enforcement, radio frequency management, and firmware distribution — is hosted in a vendor-operated cloud platform. Access points connect to the cloud platform for configuration and monitoring, while local traffic forwarding typically remains at the access point.
IT teams encounter this term when evaluating modern WiFi platforms from vendors such as Cisco Meraki, Aruba Central, and Juniper Mist. It is the dominant deployment model for new enterprise WiFi deployments as of 2024.
On-Premise WiFi Controller (WLC)
A physical or virtual appliance deployed within the enterprise network that centrally manages all access points, handling authentication, QoS, roaming, and security policy enforcement. All management traffic remains within the enterprise network perimeter.
IT teams encounter this in legacy enterprise environments and in organisations with strict data sovereignty or compliance requirements. Major platforms include Cisco Catalyst 9800, Aruba Mobility Controller, and Ruckus SmartZone.
Zero-Touch Provisioning (ZTP)
A deployment capability that allows network devices — access points, switches, or routers — to be shipped directly to a site and automatically configured upon first connection to the network, without requiring on-site engineer intervention. The device contacts a cloud management platform, downloads its pre-staged configuration, and becomes operational.
ZTP is a primary operational advantage of cloud-managed WiFi for multi-site deployments. It eliminates the need to pre-configure devices in a staging environment or dispatch engineers to remote sites for initial setup.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices connecting to a LAN or WLAN. It requires a supplicant (the connecting device), an authenticator (the access point or switch), and an authentication server (typically a RADIUS server) to complete an authentication exchange before network access is granted.
IT teams implement 802.1X for staff WiFi networks to enforce per-user authentication, typically using EAP-TLS (certificate-based) or PEAP-MSCHAPv2 (username/password) as the inner authentication method. It is required for WPA3-Enterprise deployments.
WPA3-Enterprise
The current generation of WiFi security protocol for enterprise networks, defined by the Wi-Fi Alliance. WPA3-Enterprise uses IEEE 802.1X for authentication and supports 192-bit cryptographic strength (CNSA suite) for high-security environments. It provides forward secrecy, meaning that the compromise of a long-term key does not expose past session traffic.
IT teams should be deploying WPA3-Enterprise on all new staff WiFi SSIDs where hardware supports it. All Wi-Fi 6 and Wi-Fi 6E certified access points are required to support WPA3.
Captive Portal
A web page presented to users when they connect to a WiFi network, requiring them to complete an action — accepting terms of service, entering credentials, or providing personal information — before being granted internet access. Captive portals are implemented using DNS and HTTP redirection at the network level.
IT teams deploy captive portals for guest WiFi to enforce acceptable use policies, capture user data for marketing or analytics purposes, and comply with legal requirements for identifying users on public networks. Purple provides a fully customisable, GDPR-compliant captive portal as a core product feature.
GDPR (General Data Protection Regulation)
The European Union's primary data protection regulation, effective from May 2018, which governs the collection, processing, and storage of personal data relating to EU residents. Under GDPR, organisations must have a lawful basis for processing personal data, provide transparent privacy notices, and respect data subject rights including access, rectification, and erasure.
GDPR is directly relevant to guest WiFi deployments because the collection of email addresses, device identifiers, or behavioural data via a captive portal constitutes processing of personal data. Organisations must ensure their captive portal consent flows meet GDPR requirements for valid consent under Article 7.
OpenRoaming
A Wi-Fi Alliance standard built on Passpoint (IEEE 802.11u) that enables automatic, seamless WiFi authentication across networks operated by different providers, using credentials from a user's home identity provider (mobile carrier, employer, or platform account). Users connect without a captive portal, and the network authenticates them via a federated identity exchange.
IT teams deploying guest WiFi in venues with high repeat visitor rates — airports, hotel chains, retail estates — should evaluate OpenRoaming to reduce authentication friction for returning users. Purple supports OpenRoaming natively, enabling users who have previously authenticated via the Purple App to connect automatically at any Purple-enabled venue.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards developed by the major card networks (Visa, Mastercard, Amex, Discover) that applies to any organisation that stores, processes, or transmits payment card data. PCI DSS includes specific requirements for network segmentation, access control, encryption, and monitoring that directly affect WiFi architecture design.
IT teams at hospitality, retail, and events venues must ensure that their WiFi architecture does not bring guest or staff networks into PCI DSS scope unnecessarily. The standard approach is to isolate payment card processing systems on a dedicated, firewalled network segment that is physically and logically separated from guest WiFi traffic.
WiFi Management Platform
A software platform that provides centralised visibility, configuration management, analytics, and policy enforcement for a wireless LAN deployment. This term encompasses both the network management layer (controller or cloud platform) and the application layer (guest experience, analytics, and compliance platforms such as Purple).
IT teams use this term when evaluating the full stack of software required to operate an enterprise WiFi deployment. It is important to distinguish between the network management layer (which controls how APs operate) and the intelligence layer (which extracts business value from the network).
Case Studies
A 45-property mid-market hotel chain is replacing end-of-life WiFi infrastructure across its estate. Properties range from 80 to 220 rooms. The IT team consists of three engineers based at head office, with no dedicated on-site IT staff at individual properties. The chain wants to capture guest email addresses for its loyalty programme and needs GDPR-compliant data handling. Budget is constrained, with a preference for OpEx over CapEx. Which WiFi architecture should they choose, and how should Purple be deployed?
This scenario is a strong fit for cloud-managed WiFi with Purple as the guest experience layer. The recommended deployment approach is as follows.
Infrastructure selection: Deploy a cloud-managed platform such as Cisco Meraki MR or Aruba Instant On across all 45 properties. Use zero-touch provisioning: pre-stage AP configurations in the cloud management portal, then ship APs directly to each property for installation by local staff or a third-party field services provider. No on-site controller hardware is required.
SSID architecture: Configure three SSIDs per property: (1) a guest SSID mapped to an internet-only VLAN, with Purple's captive portal as the splash page; (2) a staff SSID using WPA3-Enterprise with 802.1X authentication against the chain's Active Directory via a cloud RADIUS service such as Cisco ISE or JumpCloud; (3) an IoT SSID for in-room devices, isolated on a dedicated VLAN with restricted inter-device communication.
Purple deployment: Configure Purple's captive portal on the guest SSID. Implement a two-step consent flow: step one collects the guest's email address and loyalty programme opt-in; step two presents the WiFi terms of service and GDPR privacy notice with explicit consent checkboxes. Connect Purple to the chain's CRM (e.g., Salesforce) via Purple's native connector to sync guest profiles automatically.
Compliance validation: Enable Purple's data retention policies to automatically anonymise guest records after 24 months in line with the chain's data retention schedule. Configure Purple's consent audit log to satisfy GDPR Article 7(1) requirements for demonstrating valid consent.
Ongoing management: All 45 properties are managed from a single cloud dashboard. Firmware updates are pushed automatically during the 02:00–04:00 maintenance window. The three-person IT team receives automated alerts for AP offline events and can remotely diagnose and resolve most issues without travel.
A Premier League football stadium with a capacity of 62,000 seats is upgrading its WiFi infrastructure ahead of a major international tournament. The stadium hosts 25 home matches per year plus concerts and corporate events. Peak concurrent users are estimated at 18,000 during sold-out events. The stadium's IT team has five engineers on-site. Data sovereignty is a concern as the stadium processes payment card data in its hospitality suites. The stadium wants to offer free guest WiFi to all fans and capture connection data for sponsorship reporting. What architecture is recommended?
This scenario warrants a hybrid architecture with on-premise controllers for the primary network and Purple as the analytics and guest experience layer.
Infrastructure selection: Deploy a centralised on-premise wireless LAN controller cluster (e.g., Cisco Catalyst 9800 or Aruba Mobility Controller) in the stadium's data centre. Deploy Wi-Fi 6E access points (802.11ax, 6 GHz band) across the bowl, concourses, hospitality suites, and back-of-house areas — approximately 800 to 1,200 APs depending on the stadium's geometry. Use a high-density AP deployment design with directional antennas to serve seated fans without co-channel interference.
Network segmentation: Create separate VLANs for: fan guest WiFi (internet-only, Purple captive portal); hospitality suite WiFi (internet plus access to point-of-sale systems, PCI DSS scoped); staff and operations WiFi (access to stadium management systems); and broadcast and media WiFi (dedicated high-bandwidth SSID for press and broadcast teams).
PCI DSS compliance: The hospitality suite network must be isolated from the guest network and subject to PCI DSS controls including network segmentation, access logging, and quarterly vulnerability scanning. The on-premise controller architecture supports this by keeping all PCI-scoped traffic within the stadium's network perimeter.
Purple deployment: Deploy Purple's captive portal on the fan guest WiFi SSID. For a stadium environment, minimise friction: use a single-click social login or the Purple App for authentication. Configure Purple's analytics to capture per-event connection counts, peak concurrent users, and return visitor rates — the key metrics for sponsorship reporting. Integrate Purple with the stadium's sponsorship management platform via API to automate report generation.
Capacity planning: For 18,000 peak concurrent users, target a minimum of one AP per 30 to 40 concurrent users in high-density seating areas, with a throughput budget of 2 to 5 Mbps per user for typical fan usage patterns (social media, messaging, live score apps).
A national retail chain with 280 stores wants to deploy guest WiFi to capture customer data for its marketing team, while also improving store operations through WiFi-based footfall analytics. The chain's IT team manages infrastructure centrally. Stores range from small convenience formats (500 sq ft) to large superstore formats (50,000 sq ft). Some stores are in areas with limited or unreliable internet connectivity. How should the architecture be designed to handle the connectivity variability?
Architecture: Cloud-managed WiFi with local AP survivability enabled, plus Purple for guest experience and analytics.
Connectivity resilience: For stores in areas with unreliable internet connectivity, configure APs with local survivability mode — this ensures that guest WiFi continues to operate with the last-known configuration even if the cloud management connection is lost. For the most connectivity-constrained stores, consider deploying a 4G/LTE failover router as a secondary WAN link, with automatic failover triggered when the primary connection drops below a defined threshold.
Tiered AP deployment: For small convenience formats, deploy two to three APs per store. For large superstore formats, deploy 15 to 25 APs with a high-density design in checkout and food service areas. Use the cloud management platform's template-based configuration to push consistent SSID, VLAN, and security policies across all 280 stores from a single configuration template.
Purple analytics for operations: Beyond guest data capture, configure Purple's footfall analytics to measure customer dwell time in key departments, identify peak traffic periods, and compare performance across the estate. This data feeds directly into the retail operations team's workforce planning and merchandising decisions.
Data architecture: Connect Purple to the chain's CDP (Customer Data Platform) via API to merge WiFi-derived behavioural data with transactional data from the POS system, creating unified customer profiles that the marketing team can use for personalised campaigns.
Scenario Analysis
Q1. A regional NHS trust operates 12 hospitals and 45 GP surgeries across a county. The trust's IT team of eight engineers manages all infrastructure centrally. The trust is subject to NHS Data Security and Protection Toolkit requirements and processes patient data on its clinical networks. It wants to offer free guest WiFi to patients and visitors in waiting areas, and is evaluating whether to deploy cloud-managed or controller-based WiFi. What architecture would you recommend, and what are the key compliance considerations?
💡 Hint:Consider the NHS DSP Toolkit requirements around data residency and the separation between clinical and guest networks. Also consider the IT team's capacity to manage 57 sites.
Show Recommended Approach
The recommended architecture is cloud-managed WiFi for the guest network, with strict network segmentation to ensure the guest network is completely isolated from clinical systems. The 57-site scale and the small central IT team make cloud-managed WiFi the operationally superior choice — the alternative of deploying on-premise controllers at each site would require significantly more engineering resource than the team can sustain. The guest WiFi SSID should be on a dedicated VLAN with internet-only access, enforced by firewall rules that block all traffic to clinical network segments. This segmentation ensures that the guest network does not fall within the scope of NHS DSP Toolkit clinical data requirements. For data residency, select a cloud-managed platform that processes and stores data within the UK (or EEA at minimum), and verify this in the vendor's data processing agreement. Deploy Purple on the guest SSID for GDPR-compliant patient data capture, with consent flows that clearly distinguish between WiFi access (which requires minimal data) and optional marketing communications (which require explicit opt-in). The key compliance consideration is demonstrating to NHS Digital that clinical data cannot be accessed from the guest network — this requires documented network segmentation evidence, not just a policy statement.
Q2. A conference centre operator runs a single 15,000 sq metre venue that hosts 200 events per year, ranging from small boardroom meetings (20 delegates) to large exhibitions (5,000 attendees). The venue's IT team has two engineers. The operator wants to offer exhibitor-grade WiFi (dedicated bandwidth per stand) as a paid service, alongside free delegate WiFi. The venue currently has an ageing on-premise controller that is out of support. What architecture should replace it?
💡 Hint:Consider the variable density requirements (20 to 5,000 users), the paid WiFi service model, and the small IT team. Also consider how Purple can support the commercial model.
Show Recommended Approach
Replace the ageing on-premise controller with a cloud-managed WiFi platform, deploying Wi-Fi 6E access points throughout the venue. The cloud-managed model suits the small IT team and eliminates the hardware maintenance burden of an on-premise controller. For the paid exhibitor WiFi service, configure dedicated SSIDs per exhibition stand using dynamic VLAN assignment, with bandwidth shaping policies enforced at the access point level — all major cloud-managed platforms support this capability. For the free delegate WiFi, deploy Purple's captive portal to capture delegate data (email, organisation, job title) with GDPR-compliant consent, creating a valuable database for the venue's marketing and event follow-up activities. Purple's analytics will also provide the venue operator with per-event attendance data, dwell time metrics, and return visitor rates — useful for commercial reporting to event organisers. The variable density requirement (20 to 5,000 users) is handled by the cloud management platform's dynamic RF management, which automatically adjusts transmit power and channel allocation based on active user density. Ensure the AP deployment design includes sufficient density for peak exhibition capacity, and validate throughput during a high-density test before the first major event.
Q3. A luxury hotel group is deploying a new WiFi estate across 8 five-star properties in Europe. Each property has 150 to 300 rooms, multiple F&B outlets, spa facilities, and conference rooms. The group's CTO wants to use WiFi data to personalise the guest experience — recognising returning guests, understanding their movement patterns within the property, and triggering personalised offers via the hotel app. The group's legal team has flagged GDPR concerns about tracking guest movements. How should the architecture be designed to achieve the commercial objective while remaining GDPR-compliant?
💡 Hint:Consider the distinction between network-level data (which device is connected to which AP) and personal data (which guest is connected). GDPR compliance depends on the consent basis and the data minimisation principle.
Show Recommended Approach
Deploy cloud-managed WiFi across all 8 properties with Purple as the guest intelligence layer. The GDPR compliance framework requires careful design of the consent and data architecture. At the point of WiFi authentication via Purple's captive portal, present guests with a layered consent notice: the first layer covers basic WiFi access (minimal data, legitimate interest basis); the second layer, presented as an optional enhancement, covers personalised services including movement analytics and targeted offers (explicit consent basis, clearly described). Guests who consent to personalised services have their device's WiFi probe data associated with their guest profile, enabling movement pattern analysis. Guests who do not consent receive standard WiFi access without tracking. This approach satisfies GDPR's requirement for granular, informed consent and the data minimisation principle (only collecting movement data from guests who have explicitly consented). Purple's consent management framework records consent timestamps and scope for each guest, providing the audit trail required under GDPR Article 7. The hotel app integration allows consenting guests to receive personalised offers triggered by their location within the property — for example, a spa offer when they are near the spa entrance. The legal team should review the privacy notice language to ensure the description of movement analytics is sufficiently clear and specific to constitute valid informed consent.
Key Takeaways
- ✓Cloud-managed WiFi is operationally superior for multi-site deployments (5+ sites) due to zero-touch provisioning, automatic firmware updates, and single-pane-of-glass management — typically delivering lower total cost of ownership than on-premise controllers within 18 to 24 months.
- ✓Controller-based WiFi remains the right choice for large single-campus deployments with strict data sovereignty requirements, PCI DSS scope concerns, or the need for advanced features such as granular QoS and real-time RF optimisation.
- ✓Purple operates as an infrastructure-agnostic WiFi intelligence overlay — it integrates with both cloud-managed and controller-based architectures, adding GDPR-compliant guest data capture, footfall analytics, and CRM integration without requiring changes to the underlying network infrastructure.
- ✓GDPR compliance for guest WiFi is non-negotiable and applies regardless of network architecture: consent must be explicit, granular, and recorded before any personal data is processed. Purple's consent management framework addresses this requirement out of the box.
- ✓Security best practice for any enterprise WiFi deployment requires WPA3-Enterprise on staff networks, strict VLAN segmentation between guest, staff, and IoT traffic, and a documented firmware management process — automated in cloud-managed deployments, scheduled quarterly in on-premise deployments.
- ✓The commercial ROI of guest WiFi analytics is well-evidenced: Purple customers including McDonald's (90% reduction in IT engineer site visits) and Brussels South Charleroi Airport (10,630% ROI) demonstrate that WiFi intelligence delivers measurable business value beyond connectivity.
- ✓Avoid the hybrid trap: if you must operate both cloud-managed and controller-based infrastructure, define explicit criteria for each deployment type and ensure your monitoring and security operations tools can span both environments — unmanaged architectural complexity erodes the cost savings you were trying to achieve.



