Dynamic VLAN Assignment with RADIUS: Segmenting Users by Role
This guide provides a comprehensive technical overview of implementing dynamic VLAN assignment using RADIUS attributes. It details how enterprise venues can automate network segmentation for staff, guests, and IoT devices to enhance security and reduce manual configuration overhead.
🎧 Listen to this Guide
View Transcript
Executive Summary

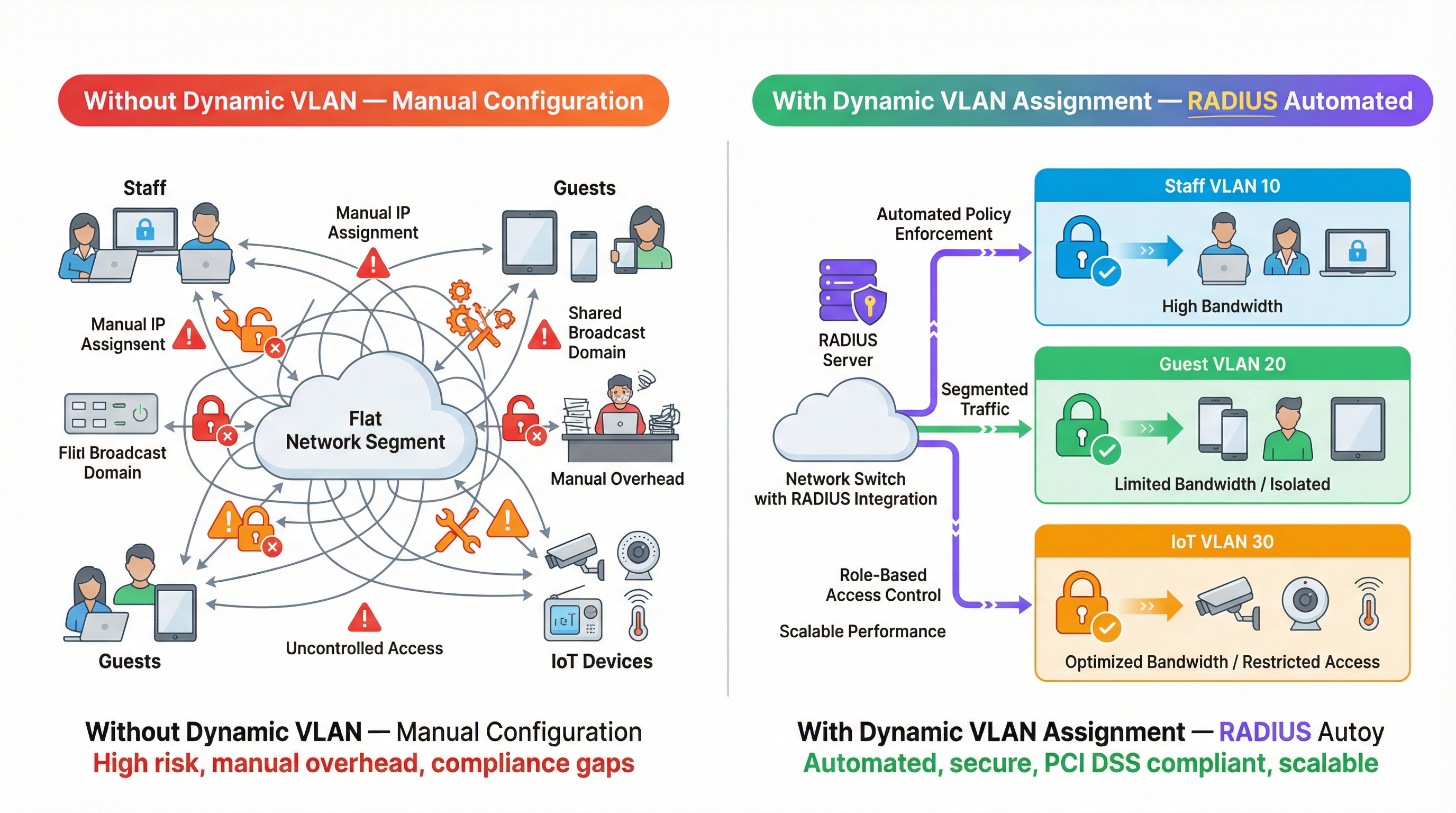
For multi-venue operators, managing network segmentation manually is a significant operational bottleneck. As the number of connected devices scales across hospitality, retail, and public sector environments, relying on static VLAN configurations per port or broadcasting dozens of SSIDs becomes unsustainable. This guide explores how to leverage dynamic VLAN assignment with RADIUS to automatically segment users and devices by role at the point of authentication. By passing specific RADIUS attributes (such as Tunnel-Pvt-Group-ID), network architects can dynamically assign users to the correct VLAN, enforcing strict security policies, ensuring compliance with standards like PCI DSS, and drastically reducing manual IT overhead.
Technical Deep-Dive
Dynamic VLAN assignment relies on the IEEE 802.1X standard for port-based network access control, combined with a RADIUS (Remote Authentication Dial-In User Service) server for centralised authentication, authorisation, and accounting (AAA). When a client device attempts to connect to the network, the authenticator (typically a Wireless Access Point or a network switch) acts as an intermediary, forwarding the client's credentials to the RADIUS server via the Extensible Authentication Protocol (EAP).
If the credentials are valid, the RADIUS server responds with an Access-Accept message. The critical mechanism for dynamic VLAN assignment is the inclusion of specific IETF standard RADIUS attributes within this Access-Accept packet. The three essential attributes are:
- Tunnel-Type (Attribute 64): Must be set to
VLAN(value 13). - Tunnel-Medium-Type (Attribute 65): Must be set to
IEEE-802(value 6). - Tunnel-Private-Group-ID (Attribute 81): This contains the actual VLAN ID string (e.g., "10", "20", "Guest_VLAN").
When the authenticator receives these attributes, it dynamically tags the user's traffic with the specified VLAN ID, placing them into the appropriate network segment regardless of the physical port or SSID they connected to.
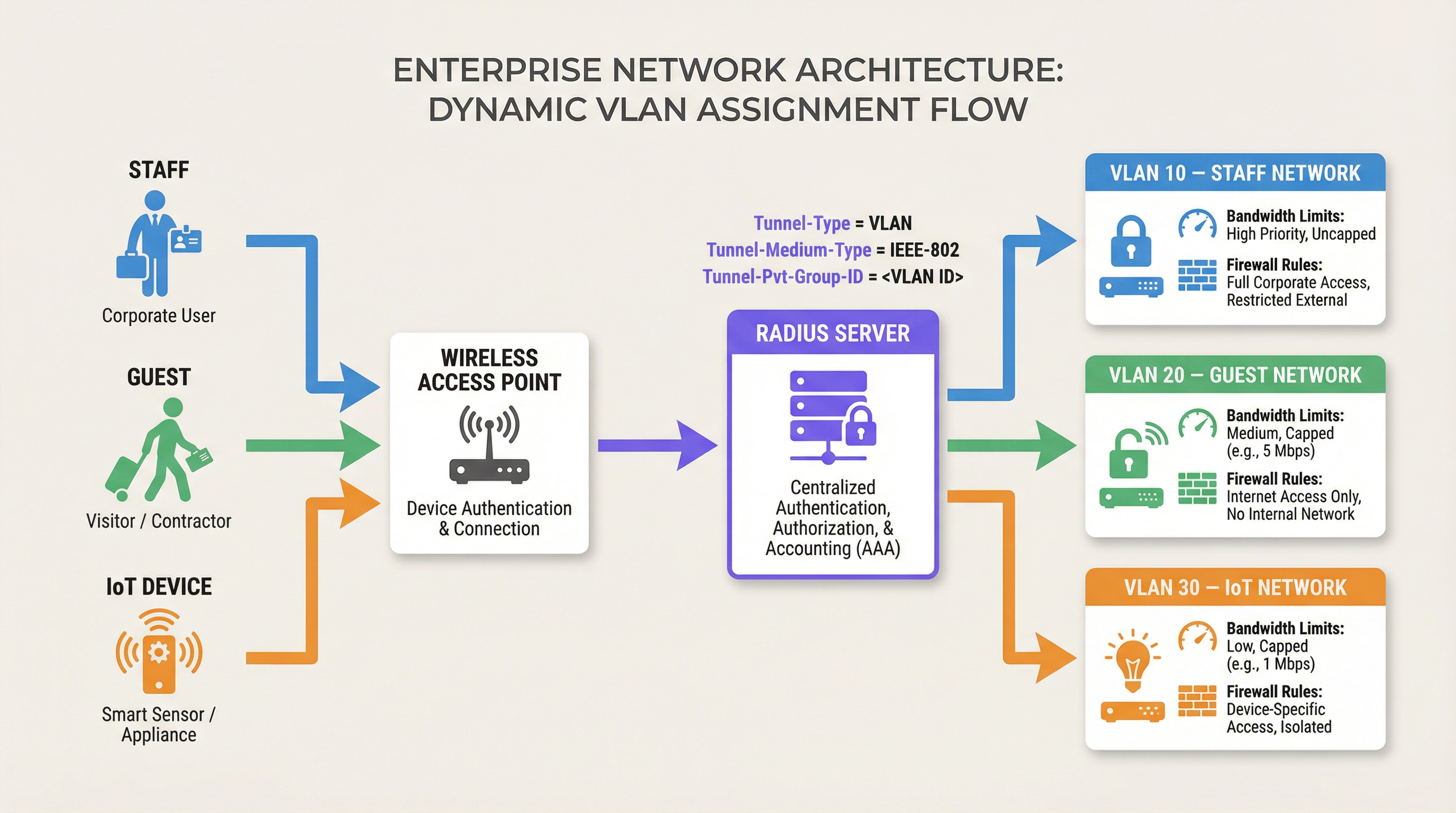
This architecture enables role-based network access control. A single SSID can securely serve multiple distinct user groups, dropping them into isolated network segments with their own firewall rules, bandwidth limits, and routing policies. For instance, Purple's Guest WiFi solutions often integrate with RADIUS to ensure guests are placed on an isolated VLAN, protecting internal resources.
Implementation Guide
Deploying dynamic VLAN assignment requires configuration on both the RADIUS server and the network infrastructure (Access Points or Switches). While the exact syntax varies between vendors (e.g., Cisco ISE, Aruba ClearPass, FreeRADIUS), the core principles remain consistent.
Step 1: RADIUS Server Configuration
Configure your RADIUS server to return the required attributes based on user groups or device profiles. For example, you might create policies that state:
- If User Group = "Staff", return Tunnel-Private-Group-ID = "10".
- If User Group = "Contractors", return Tunnel-Private-Group-ID = "20".
- If Device Type = "IoT Sensor" (via MAC Authentication Bypass), return Tunnel-Private-Group-ID = "30".
Step 2: Authenticator Configuration (Access Points/Switches)
Configure your network devices to query the RADIUS server and process the returned attributes. This typically involves:
- Defining the RADIUS server IP address and shared secret.
- Enabling 802.1X authentication on the relevant SSIDs or switch ports.
- Enabling dynamic VLAN assignment (sometimes called "AAA Override" or "RADIUS VLAN assignment").
Vendor-Specific Considerations
- Cisco: On WLCs, ensure "AAA Override" is enabled on the WLAN configuration. For switches, configure
authentication port-control autoanddot1x pae authenticator. - Aruba: In ArubaOS, ensure the AAA profile has "RADIUS Server" configured and that the server group is set to process server rules for VLAN derivation.
- Ubiquiti UniFi: In the UniFi Network application, enable "RADIUS MAC Authentication" or "WPA2/WPA3 Enterprise" and ensure "Enable RADIUS assigned VLAN" is checked in the network settings.
Best Practices
To ensure a robust and scalable deployment, adhere to the following industry-standard recommendations:
- Standardise VLAN IDs Globally: Inconsistent VLAN naming across sites is a major pitfall. If VLAN 10 is "Staff" at site A but "Guest" at site B, dynamic assignment will cause chaos. Establish a global VLAN numbering scheme before implementing dynamic assignment.
- Implement Fallback Mechanisms: RADIUS unavailability is a critical failure mode. Configure a "critical VLAN" or "fallback VLAN" on your access points. If the RADIUS server is unreachable, the AP should drop the device into a restricted VLAN that perhaps only allows internet access, maintaining connectivity without compromising internal security.
- Use MAC Authentication Bypass (MAB) for Headless Devices: IoT devices like Sensors or smart thermostats often cannot perform 802.1X authentication. Use MAB to authenticate these devices based on their MAC address, assigning them to a locked-down IoT VLAN.
- Leverage Analytics: Use platforms like Purple's WiFi Analytics to monitor authentication trends, identify anomalies, and optimise network performance based on role-based usage patterns.
Troubleshooting & Risk Mitigation
When implementing dynamic VLAN assignment, be prepared to troubleshoot common issues:
- Client Placed in Default VLAN: This usually occurs if the RADIUS server fails to send the correct attributes, or if the authenticator is not configured to process them (e.g., "AAA Override" is disabled). Use packet captures to verify the contents of the
Access-Acceptmessage. - Authentication Timeouts: If devices fail to authenticate, check network connectivity between the authenticator and the RADIUS server. Verify the shared secret and ensure the RADIUS server has the authenticator configured as a valid client.
- DHCP Issues: After a device is dynamically assigned to a VLAN, it must obtain an IP address for that subnet. Ensure the DHCP server is correctly configured for all dynamic VLANs and that IP helper addresses are in place if necessary.
ROI & Business Impact
Implementing dynamic VLAN assignment delivers significant return on investment by reducing manual configuration overhead and mitigating security risks.
- Operational Efficiency: Eliminates the need to manually configure static VLANs per port or broadcast multiple SSIDs for different user groups, saving IT teams hours of administrative work.
- Enhanced Security: Enforces strict role-based access control, ensuring that compromised devices or unauthorised users are isolated from critical business systems. This is essential for compliance with standards like PCI DSS in Retail environments.
- Improved User Experience: Provides a seamless authentication experience for staff and guests, as they can connect to a single SSID and automatically receive the appropriate network access privileges.
Listen to our technical briefing podcast for more insights:
For more information on securing your network, see our guide on 802.1X Authentication: Securing Network Access on Modern Devices.
Key Terms & Definitions
Dynamic VLAN Assignment
The process of automatically assigning a device to a specific Virtual Local Area Network (VLAN) based on its identity or role during authentication, rather than its physical connection point.
Essential for scalable network segmentation in enterprise environments, eliminating the need for manual port configuration.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The core engine that evaluates credentials and dictates network policy, including VLAN assignment.
802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The framework that allows devices to securely transmit credentials to the network infrastructure before gaining access.
Tunnel-Private-Group-ID
RADIUS Attribute 81, used to specify the VLAN ID or VLAN name that the authenticator should assign to the user's session.
The specific data field in the RADIUS response that dictates the network segment.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X (like printers or IoT sensors) by using their MAC address as their identity.
Crucial for integrating headless devices into a dynamically segmented network architecture.
Authenticator
The network device (such as a wireless access point or switch) that facilitates the authentication process between the client and the RADIUS server.
The device responsible for enforcing the VLAN assignment policy returned by the RADIUS server.
Access-Accept
The RADIUS message sent to the authenticator indicating that the user's credentials are valid and access should be granted.
This packet carries the crucial VLAN assignment attributes.
AAA Override
A configuration setting on many authenticators (like Cisco WLCs) that allows the RADIUS server to override the default VLAN or policy configured on the device.
Must be enabled for dynamic VLAN assignment to function correctly.
Case Studies
A 500-room luxury hotel needs to segment its network for guests, staff, and IoT devices (smart thermostats and door locks). They currently broadcast 5 different SSIDs, causing significant co-channel interference and confusing guests. How can dynamic VLAN assignment solve this?
The hotel should consolidate to two SSIDs: 'Hotel_Guest' (Open/Captive Portal) and 'Hotel_Secure' (802.1X). For 'Hotel_Secure', staff authenticate using their corporate credentials. The RADIUS server verifies the credentials against Active Directory and returns Tunnel-Private-Group-ID = '10' (Staff VLAN). For IoT devices, which cannot use 802.1X, the network uses MAC Authentication Bypass (MAB). The RADIUS server recognizes the MAC addresses of the thermostats and locks, returning Tunnel-Private-Group-ID = '30' (IoT VLAN). Guests connect to 'Hotel_Guest' and are placed in VLAN 20 via standard captive portal workflows, potentially integrated with Purple's Hospitality solutions.
A large retail chain is deploying point-of-sale (POS) terminals across 50 locations. To comply with PCI DSS, these terminals must be strictly isolated from the corporate and guest networks. How can dynamic VLAN assignment ensure compliance even if a terminal is moved to a different port?
The IT team configures the network switches to require 802.1X authentication on all edge ports. The POS terminals are configured with certificates for EAP-TLS authentication. When a terminal connects to any port, it authenticates with the RADIUS server. The RADIUS server verifies the certificate and returns Tunnel-Private-Group-ID = '40' (PCI VLAN). The switch dynamically assigns the port to VLAN 40, applying strict ACLs that only allow communication with the payment processing gateways.
Scenario Analysis
Q1. You are deploying dynamic VLAN assignment across a university campus. The RADIUS server is successfully sending the Access-Accept message with Tunnel-Private-Group-ID set to '50' for faculty members. However, faculty devices are still being placed in the default VLAN (VLAN 1) configured on the SSID. What is the most likely cause?
💡 Hint:Check the configuration on the wireless access point or controller.
Show Recommended Approach
The most likely cause is that the authenticator (the Wireless LAN Controller or Access Point) does not have 'AAA Override' (or the equivalent setting, such as 'Enable RADIUS assigned VLAN') enabled for that specific SSID. Even if the RADIUS server sends the correct attributes, the authenticator will ignore them and use the default configuration unless explicitly instructed to process dynamic assignments.
Q2. A hospital needs to connect hundreds of new smart infusion pumps to the network. These devices do not support 802.1X supplicants. How can the IT team ensure these devices are automatically placed into a secure, isolated clinical IoT VLAN?
💡 Hint:Consider how devices without 802.1X capabilities can be identified by the network.
Show Recommended Approach
The IT team should implement MAC Authentication Bypass (MAB). The MAC addresses of all infusion pumps must be added to the RADIUS server's database. When a pump connects to the network, the switch or AP will use its MAC address as the identity for authentication. The RADIUS server will recognize the MAC address and return an Access-Accept message containing the Tunnel-Private-Group-ID for the clinical IoT VLAN.
Q3. Your enterprise network relies heavily on dynamic VLAN assignment. During a scheduled maintenance window, the primary and secondary RADIUS servers become temporarily unreachable. What configuration must be in place to ensure business-critical devices maintain some level of connectivity?
💡 Hint:Look for features related to authentication failure or fallback scenarios on the switch or AP.
Show Recommended Approach
The network infrastructure must be configured with a 'Critical VLAN' or 'Fallback VLAN'. When the authenticator detects that the RADIUS servers are dead (unreachable), it automatically places connecting devices into this pre-defined Critical VLAN. This VLAN should have strict ACLs applied, perhaps only allowing internet access or access to essential remediation services, ensuring basic connectivity without exposing the internal network.
Key Takeaways
- ✓Dynamic VLAN assignment automates network segmentation based on user role or device identity.
- ✓It relies on 802.1X authentication and specific RADIUS attributes (Tunnel-Type, Tunnel-Medium-Type, Tunnel-Pvt-Group-ID).
- ✓This approach eliminates the need for manual port configuration and reduces SSID bloat.
- ✓MAC Authentication Bypass (MAB) is essential for segmenting headless IoT devices.
- ✓Global standardisation of VLAN IDs is critical for successful multi-site deployments.
- ✓Always configure fallback mechanisms (Critical VLAN) to handle RADIUS server outages.



