Event-Driven Marketing Automation Triggered by WiFi Presence
This architectural reference guide provides senior IT and operations leaders with a blueprint for designing event-driven marketing automation triggered by WiFi presence. It covers infrastructure requirements, latency management, deduplication strategies, and privacy compliance frameworks necessary for enterprise-scale deployments.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Four-Layer Architecture
- Layer 1: The Network Layer
- Layer 2: The Presence Engine
- Layer 3: The Automation Layer
- Layer 4: The Delivery Layer
- Implementation Guide: Latency and Deduplication
- Managing End-to-End Latency
- The Deduplication Challenge
- Privacy and Compliance Frameworks
- GDPR and PECR Compliance
- Security and Segmentation
- ROI & Business Impact
Executive Summary

For modern venues—from retail chains and hospitality groups to large-scale stadiums—the existing wireless network infrastructure represents an underutilised asset for real-time customer engagement. Event-driven marketing automation triggered by WiFi presence transforms passive network connectivity into an active engagement channel. This guide provides a definitive architectural blueprint for implementing presence-based automation, focusing on the technical mechanics of converting raw network events into contextually relevant, compliant marketing actions. By bridging the gap between network infrastructure and marketing technology, IT leaders can deliver measurable business impact while maintaining stringent privacy and security standards.
Listen to the executive briefing podcast:
Technical Deep-Dive: The Four-Layer Architecture
Architecting a robust WiFi presence automation system requires a decoupled, four-layer approach. This separation of concerns ensures that changes to marketing logic do not require network reconfiguration, and network upgrades do not break automated campaigns.
Layer 1: The Network Layer
The foundation of presence detection relies on the physical infrastructure—access points, wireless LAN controllers, and the RADIUS server. The critical architectural decision at this layer is determining which network events will trigger downstream automation. While legacy systems often relied on passive probe requests, modern implementations must prioritise authenticated session events. Since the introduction of default MAC address randomisation in modern mobile operating systems, probe-based tracking has become technically unreliable and legally precarious. Instead, leveraging association events tied to a Guest WiFi captive portal login provides a persistent, consent-linked identifier that survives MAC randomisation.
Layer 2: The Presence Engine
Raw network events are inherently noisy and require processing before they can trigger business logic. The Presence Engine, powered by Purple's Event Stream, ingests association events and performs critical filtering. This includes probe detection filtering to eliminate 'drive-by' signals, dwell time calculation to ensure the device has remained in the venue for a minimum threshold, and sophisticated deduplication. In high-density environments like Retail or Hospitality , a single guest visit may generate dozens of association and roaming events. The Presence Engine collapses these into a single, clean 'presence' signal.
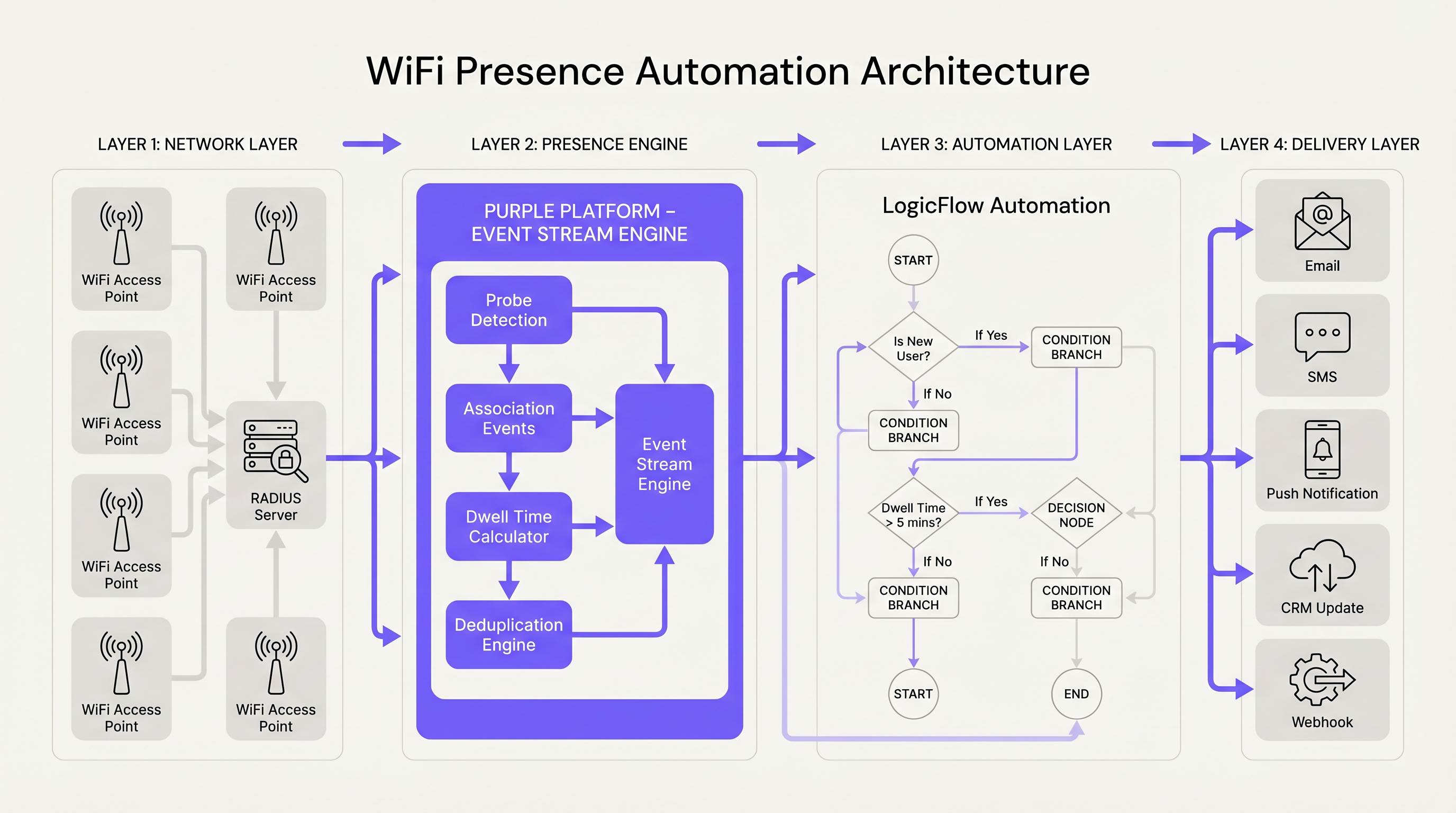
Layer 3: The Automation Layer
Once a clean presence signal is established, it passes to the Automation Layer. In the Purple ecosystem, this is handled by LogicFlow. This layer evaluates the presence event against predefined business rules, such as user segmentation, visit frequency, and campaign suppression windows. For example, a rule might dictate that a 'Welcome Back' campaign only fires if the user has not visited in the last 30 days and has been present on the network for at least five minutes.
Layer 4: The Delivery Layer
The final layer is responsible for executing the action. This could be dispatching an SMS, sending an email, triggering a push notification via a venue application, or firing a webhook to update an external CRM. The Delivery Layer must strictly adhere to the consent preferences captured during the initial authentication phase, ensuring compliance with privacy regulations.
Implementation Guide: Latency and Deduplication
Successful deployment hinges on managing two critical technical constraints: end-to-end latency and event deduplication.
Managing End-to-End Latency
Latency in presence automation is defined as the time elapsed between a device associating with the network and the guest receiving the triggered communication. Acceptable latency varies significantly by venue type. In a Transport hub, a trigger must fire within seconds, whereas a hotel deployment can tolerate higher latency.
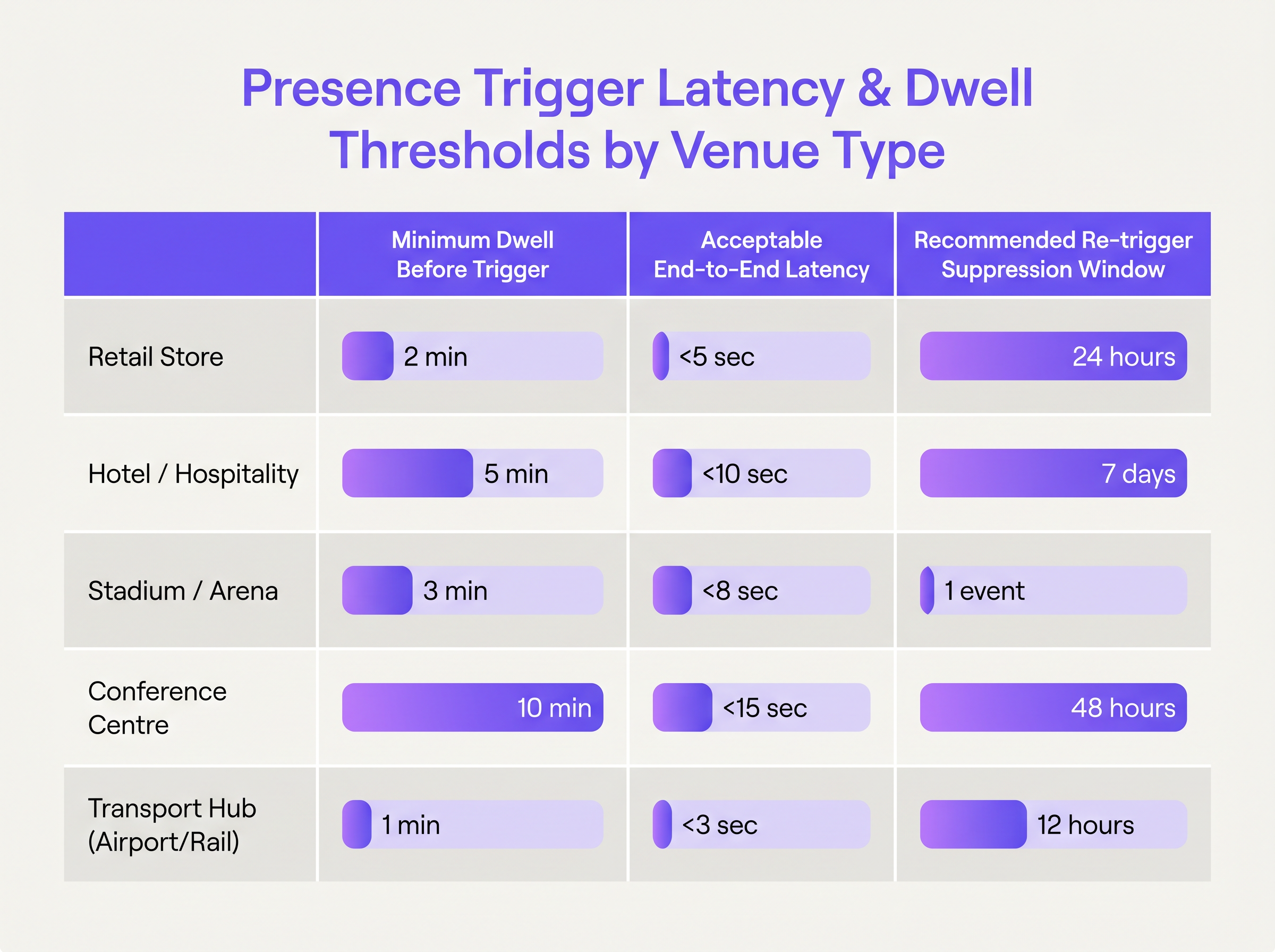
To achieve sub-ten-second latency, architects must optimise the network-to-platform event transmission (typically via syslog or API push from the controller) and select appropriate delivery channels. SMS and push notifications are suitable for real-time triggers, whereas email should be reserved for asynchronous communications due to inherent delivery delays.
The Deduplication Challenge
Deduplication must occur at both the device level and the campaign level. Device-level deduplication involves defining a 'session window'—typically 15 to 30 minutes. If a device disassociates and reassociates within this window, it is treated as a continuation of the existing session rather than a new visit. Campaign-level deduplication requires configuring suppression windows to prevent message fatigue. A common pitfall is failing to implement cross-device deduplication, where a user connects with both a smartphone and a laptop, resulting in duplicate campaign triggers. This is mitigated by linking MAC addresses to a single authenticated user profile (e.g., an email address) within the WiFi Analytics platform.
Privacy and Compliance Frameworks
Implementing presence-based automation requires strict adherence to privacy and security frameworks. A technically flawless system that violates compliance standards introduces unacceptable risk to the enterprise.
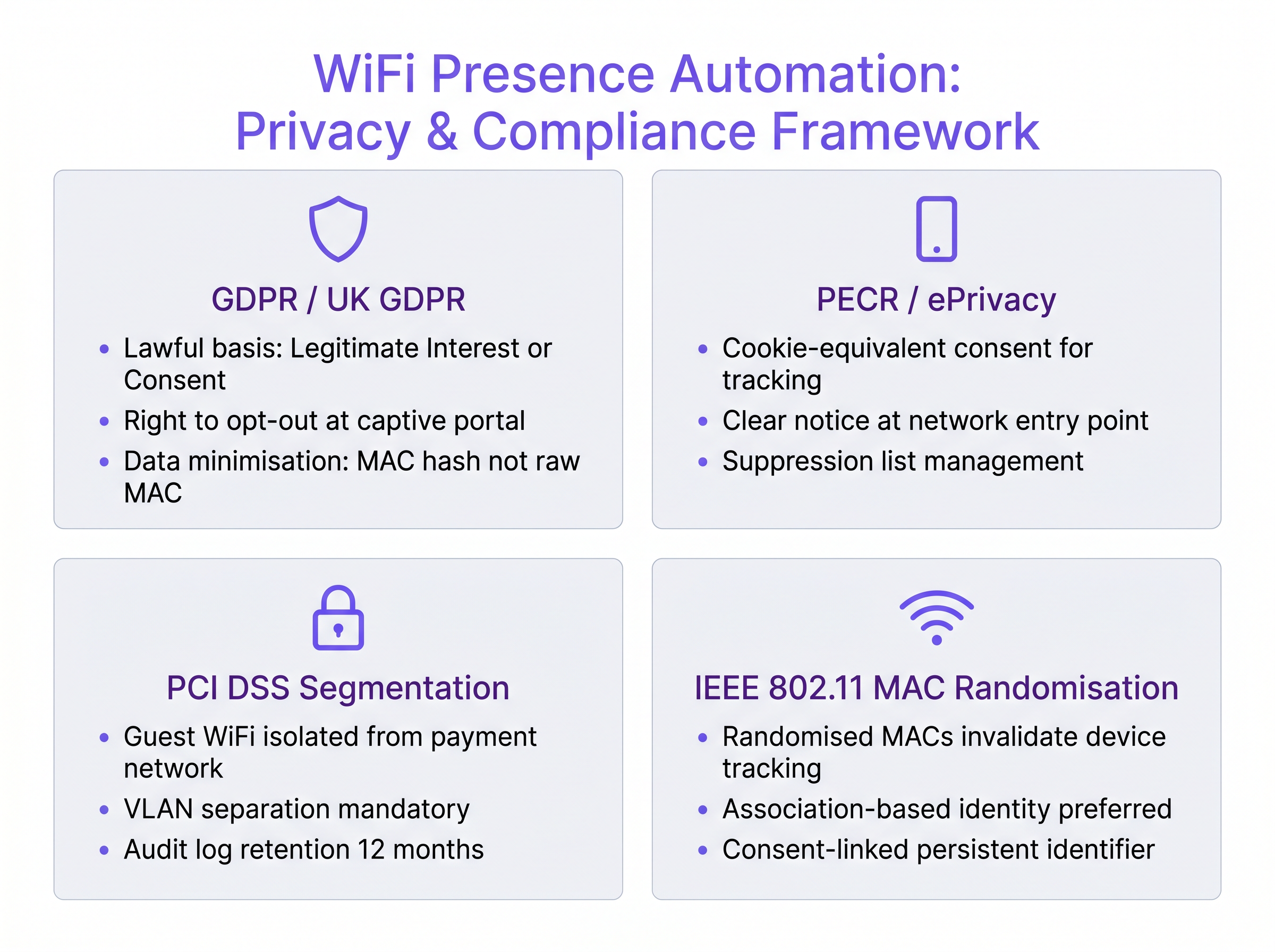
GDPR and PECR Compliance
Under the General Data Protection Regulation (GDPR), processing location data requires a lawful basis. While 'Legitimate Interest' is sometimes used, explicit 'Consent' captured at the captive portal is the most defensible approach for marketing automation. Furthermore, the Privacy and Electronic Communications Regulations (PECR) mandate specific, informed consent for electronic marketing communications (SMS, email). Pre-ticked boxes are invalid; active opt-in is required.
Security and Segmentation
From a network security perspective, the guest WiFi infrastructure must be strictly segmented from corporate and payment networks. In environments processing cardholder data, PCI DSS compliance mandates VLAN separation and firewall isolation. The presence automation platform should only interact with the isolated guest network segment. For further reading on securing network access, review our guide on Aruba ClearPass vs Cisco ISE: NAC Platform Comparison .
ROI & Business Impact
The business value of event-driven marketing automation is measured in conversion rate uplift and operational efficiency. By shifting from batch-and-blast marketing to real-time, contextually relevant engagement, venues typically observe a 3x to 5x increase in engagement rates. For example, a stadium triggering an SMS merchandise offer 15 minutes after a fan connects to the network capitalises on high-intent dwell time. Furthermore, integrating these presence events into broader enterprise workflows—such as Connecting WiFi Events to 1,500+ Apps with Zapier and Purple —allows IT teams to automate operational tasks, such as alerting staff when a VIP guest arrives on premises. Similar to the network efficiency gains discussed in The Core SD WAN Benefits for Modern Businesses , automating marketing workflows reduces manual overhead and ensures consistent execution at scale.
Key Terms & Definitions
MAC Randomisation
A privacy feature in modern operating systems where a device broadcasts a randomly generated MAC address instead of its true hardware address when scanning for networks.
Crucial for IT teams to understand because it invalidates legacy presence analytics systems that rely on passive probe tracking.
Probe Request
A frame sent by a client device to discover available 802.11 networks within its proximity.
Useful for footfall counting, but insufficient for marketing automation due to lack of identity and consent.
Association Event
The moment a wireless client successfully connects and authenticates to an Access Point.
The primary, reliable trigger point for event-driven marketing automation.
Dwell Time
The continuous duration a device remains associated with the network during a single visit.
Used as a condition in automation logic to differentiate between a transient passerby and an engaged customer.
Suppression Window
A defined period during which a specific automated campaign will not fire again for the same user, regardless of trigger conditions being met.
Essential for preventing message fatigue and maintaining a positive user experience.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The critical juncture for capturing user identity and securing legal consent for marketing automation.
LogicFlow
A visual workflow automation engine that evaluates presence events against business rules to trigger downstream actions.
Allows marketing teams to manage campaign logic without requiring network engineers to alter infrastructure configurations.
VLAN Segmentation
The practice of partitioning a physical network into multiple distinct broadcast domains.
A mandatory security requirement to isolate guest WiFi traffic from corporate or payment processing systems.
Case Studies
A 400-room resort hotel wants to trigger a 'Welcome to the Spa' SMS offer when a guest connects to the WiFi network near the spa facilities. They are currently using probe requests for detection, but the marketing team reports that the campaign is firing inconsistently, and some guests are receiving the message multiple times a day.
- Migrate from probe-based detection to authenticated association events. Probe requests use randomised MAC addresses, causing the system to treat a single device as multiple new visitors. 2. Implement Location-Based Triggers using specific Access Point (AP) MAC addresses located in the spa zone, rather than the general venue SSID. 3. Configure a Dwell Time Threshold of 3 minutes to filter out guests merely walking past the spa to the elevators. 4. Set a Campaign Suppression Window of 7 days to ensure a guest only receives the offer once per typical stay, preventing message fatigue.
A large retail chain wants to integrate their WiFi presence events with their central CRM (Salesforce) to update customer profiles in real-time when they enter a store. The IT team is concerned about API rate limits being exceeded during peak weekend trading hours.
- Do not use direct, synchronous API calls from the WiFi controller to the CRM for every association event. 2. Route all association events through the Purple Event Stream Engine to perform device-level deduplication, collapsing multiple micro-disconnects into a single 'Visit Started' event. 3. Configure a webhook in LogicFlow to send only the processed 'Visit Started' event to an enterprise integration middleware (e.g., Zapier or a custom AWS Lambda function). 4. Implement a queuing mechanism in the middleware to batch CRM updates or apply rate-limiting logic before pushing the data to Salesforce.
Scenario Analysis
Q1. A stadium IT director wants to send a push notification via the venue's mobile app the moment a fan connects to the WiFi at the entrance gates. They are currently seeing a 45-second delay between connection and notification delivery. Where should they investigate first to reduce latency?
💡 Hint:Consider the components of the latency budget: Network-to-platform, Platform processing, and Delivery channel.
Show Recommended Approach
They should investigate the network-to-platform event transmission. In a high-density environment like a stadium, if the wireless controller is batching syslog events or API updates rather than streaming them in real-time, it introduces significant artificial latency before the automation platform even receives the trigger signal. Secondary investigation should verify the push notification gateway's processing queue.
Q2. A retail marketing team requests that the IT department configure the network to track all devices walking past their storefront windows to trigger a 'Come Inside' SMS campaign. How should the IT architect respond?
💡 Hint:Consider the technical reality of modern mobile devices and the legal requirements for electronic marketing.
Show Recommended Approach
The IT architect must reject the request on both technical and compliance grounds. Technically, tracking devices outside the store relies on passive probe requests, which use randomised MAC addresses, making reliable identification impossible. Legally, under PECR and GDPR, sending an SMS requires explicit, prior opt-in consent, which cannot be obtained from a device merely walking past. The architect should propose an alternative: triggering campaigns only for users who have previously authenticated via the captive portal and explicitly opted into SMS marketing.
Q3. During testing of a new presence automation deployment in a hospital waiting room, the system is correctly identifying devices, but the 'Welcome to the Clinic' email is firing every time a patient's device roams between two adjacent access points. What configuration is missing?
💡 Hint:Consider how the system differentiates between a network roaming event and a new visit.
Show Recommended Approach
The system is missing device-level deduplication (specifically, a session window configuration). The Event Stream Engine needs to be configured to recognise that a disassociation followed immediately by a reassociation to a different AP within the same venue constitutes a roaming event within an ongoing session, not a new visit. The session window should be set to at least 15-30 minutes to collapse these micro-events.
Key Takeaways
- ✓Base automation triggers on authenticated association events, not passive probe requests, to overcome MAC randomisation.
- ✓Implement a decoupled four-layer architecture separating network infrastructure from marketing logic.
- ✓Configure strict dwell time thresholds to filter out transient connections and drive-by traffic.
- ✓Apply two-tier deduplication: session windows to handle network roaming, and suppression windows to prevent message fatigue.
- ✓Ensure end-to-end latency aligns with the venue's use case (e.g., <10 seconds for transport hubs).
- ✓Capture explicit consent at the captive portal to ensure GDPR and PECR compliance for electronic marketing.
- ✓Maintain strict VLAN segmentation between guest WiFi and payment networks to satisfy PCI DSS requirements.



