The Future of Seamless Connectivity: Passpoint and OpenRoaming Explained
This technical reference guide provides actionable insights for IT leaders on transitioning from traditional captive portals to Passpoint and OpenRoaming. It details the underlying IEEE 802.11u and WPA3 standards, secure authentication flows, and real-world deployment strategies to improve seamless connectivity, enhance security, and drive measurable ROI in enterprise venues.
🎧 Listen to this Guide
View Transcript

Executive Summary
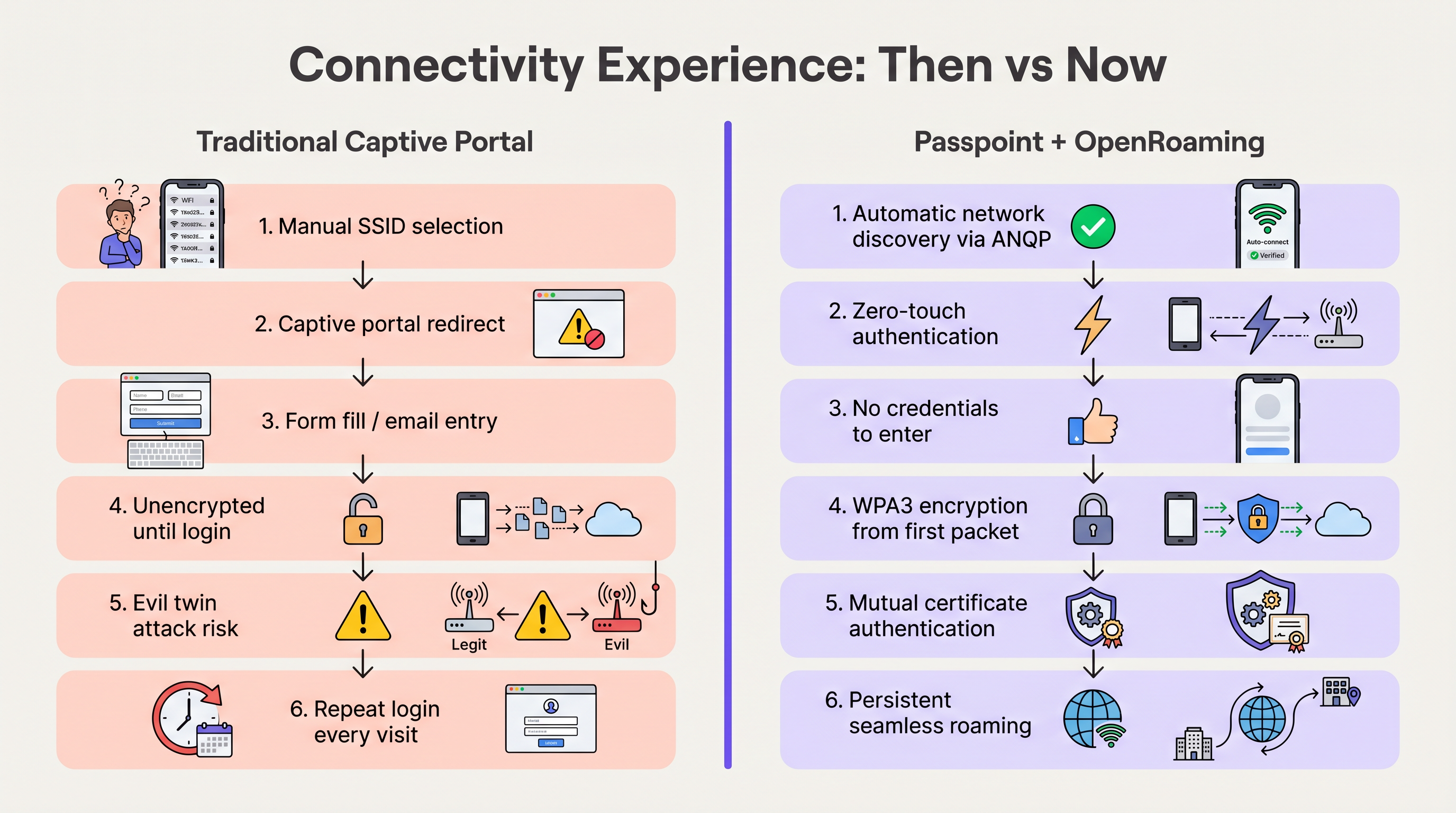
For the past decade, guest WiFi has relied on captive portals—a friction-heavy model that frustrates users, degrades brand experience, and introduces significant security vulnerabilities. As venues across Hospitality, Retail, and public sectors demand higher attach rates to fuel WiFi Analytics and location-based services, the industry is shifting toward seamless, cellular-like connectivity.
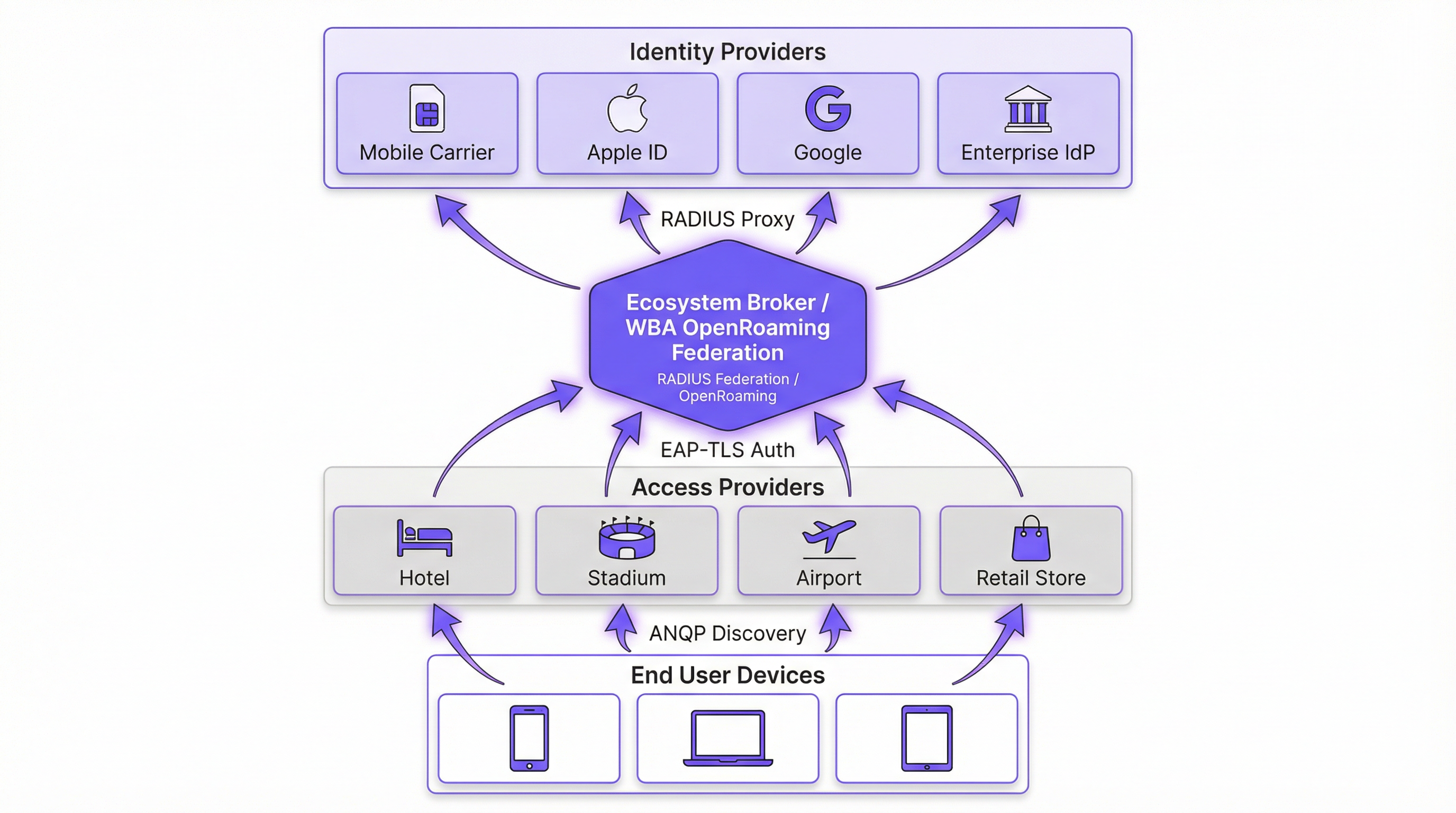
Passpoint (Hotspot 2.0) and OpenRoaming represent the definitive future of enterprise wireless access. Built on the IEEE 802.11u standard and managed by the Wireless Broadband Alliance (WBA), this ecosystem enables zero-touch, secure (WPA3) authentication. By federating identity providers (like Apple, Google, and mobile carriers) with access networks, venues can automatically onboard guests without manual SSID selection or splash pages. This guide provides a practical, vendor-neutral roadmap for IT managers and network architects to evaluate, design, and deploy Passpoint and OpenRoaming, transforming guest WiFi from a cost centre into a secure, data-rich asset.
Technical Deep-Dive
The Passpoint and OpenRoaming Architecture
To understand the shift, we must distinguish between the underlying technology and the federation that scales it.
Passpoint (Hotspot 2.0) is a Wi-Fi Alliance certification based on the IEEE 802.11u standard. It defines the mechanism for devices to discover and authenticate to networks automatically. The core protocol is the Access Network Query Protocol (ANQP), which allows a client device to interrogate an Access Point (AP) before associating. The device checks the AP's advertised Roaming Consortium Organizationally Unique Identifiers (OUIs) against its locally provisioned profiles. If a match is found, the device initiates an Extensible Authentication Protocol (EAP) connection (typically EAP-TLS or EAP-TTLS).
OpenRoaming is the global federation built on top of Passpoint. While Passpoint handles the local device-to-AP interaction, OpenRoaming provides the RADIUS proxy infrastructure that connects millions of APs to thousands of Identity Providers (IdPs). This eliminates the need for venues to negotiate individual roaming agreements or manage complex Public Key Infrastructure (PKI) for external guests.
Security Paradigm Shift
Traditional open networks with captive portals transmit data unencrypted until the user completes the login process. This exposes users to "evil twin" attacks, where malicious actors spoof the venue's SSID to harvest credentials.
Passpoint fundamentally alters this risk profile. Because authentication occurs via 802.1X, the connection is secured with WPA2-Enterprise or WPA3-Enterprise encryption from the very first packet. Furthermore, the mutual authentication inherent in EAP-TLS means the device verifies the network's certificate before sending any credentials, effectively neutralizing evil twin vulnerabilities. As detailed in our guide on Device Posture Assessment for Network Access Control, establishing device trust is paramount, and Passpoint enforces this at the edge.
Implementation Guide
Deploying OpenRoaming requires coordination between your Wireless LAN Controller (WLC), your RADIUS infrastructure, and the WBA federation. The following vendor-neutral steps outline a standard enterprise deployment.
Phase 1: Infrastructure Readiness Assessment
Before configuration, verify that your existing hardware supports the required standards. Most enterprise APs (e.g., Cisco, Aruba, Ruckus) released in the last five years support 802.11u and Passpoint natively. Ensure your WLC firmware is updated to support WPA3 and Protected Management Frames (PMF), which are mandatory for Passpoint Release 3.
Phase 2: RADIUS and Federation Integration
The critical integration point is connecting your local network to the OpenRoaming federation. This is achieved by establishing a secure RADIUS proxy connection.
- Select a Cloud RADIUS Provider: Choose a provider that is a certified OpenRoaming Ecosystem Broker (e.g., IronWiFi, Cisco Spaces).
- Establish RadSec Tunnels: Configure your WLC to forward authentication requests to the cloud RADIUS server using RadSec (RADIUS over TLS). This secures the authentication traffic across the internet. For detailed configuration, refer to RadSec : Sécurisation du trafic d'authentification RADIUS avec TLS.
- Configure Realm Routing: Set up routing rules on the RADIUS server to forward requests matching OpenRoaming domains (e.g.,
apple.openroaming.net) to the WBA federation.
Phase 3: WLAN Configuration
Configure the specific SSID on your WLC to broadcast the necessary ANQP elements.
- Enable 802.11u: Turn on Hotspot 2.0/Passpoint features for the target WLAN.
- Define Roaming Consortium OUIs: Add the specific OUIs provided by the WBA (e.g.,
5A-03-BAfor OpenRoaming-Settlement-Free) to the AP's beacon. - Configure Security: Set the Layer 2 security to WPA2/WPA3-Enterprise with 802.1X authentication.
Phase 4: User Onboarding Strategy
While federated users (e.g., those with Apple or Google profiles) will connect automatically, you must plan for users who do not have pre-existing profiles. Implement an Online Sign-Up (OSU) server or integrate profile provisioning into your venue's mobile app. This allows users to download a Passpoint profile during their first visit, ensuring seamless connectivity for all subsequent visits.
Best Practices
- Maintain a Hybrid Approach During Transition: Do not immediately disable your legacy captive portal. Run the Passpoint-enabled SSID concurrently with your open Guest WiFi network to accommodate legacy devices and users without profiles. Monitor the attach rates to determine when the open network can be safely sunset.
- Prioritize RadSec: Never transmit RADIUS traffic over the internet unencrypted. Always use RadSec to secure the communication between your WLC and the cloud RADIUS provider.
- Leverage App Integration: For hospitality and retail venues, embed the Passpoint profile provisioning within your brand's loyalty app. This guarantees the user is authenticated securely while directly tying network presence to their customer profile.
- Monitor Certificate Expirations: Passpoint relies heavily on PKI. Implement automated monitoring and alerting for all RADIUS and web server certificates to prevent sudden authentication failures.
Troubleshooting & Risk Mitigation
When deploying Passpoint, IT teams typically encounter specific failure modes. Understanding these risks is crucial for a smooth rollout.
- ANQP Timeout Issues: If APs are overloaded or the controller is sluggish, ANQP responses may time out, preventing devices from discovering the network. Mitigation: Ensure APs are adequately provisioned and monitor control plane CPU utilization. For high-density environments, consider optimizing beacon intervals.
- Certificate Trust Failures: If the client device does not trust the Root CA that signed the RADIUS server's certificate, the EAP-TLS handshake will fail silently. Mitigation: Always use certificates issued by widely recognized public Certificate Authorities (e.g., DigiCert, Let's Encrypt) for public-facing RADIUS servers. Avoid self-signed certificates for guest access.
- RadSec Connectivity Drops: Firewalls or intermediate routing issues can sever the TCP connection required for RadSec. Mitigation: Implement robust monitoring on the RadSec tunnel status and configure secondary RADIUS servers for failover.
ROI & Business Impact
The transition to Passpoint and OpenRoaming is not merely an IT upgrade; it is a strategic business enabler. By removing the friction of captive portals, venues see immediate improvements in key metrics.
- Increased Attach Rates: Venues typically observe a 40-60% increase in the number of devices connecting to the network. This directly expands the sample size for WiFi Analytics and Sensors, providing more accurate footfall and dwell time data.
- Enhanced Customer Engagement: In retail and hospitality, seamless connectivity allows venues to trigger location-based notifications via their apps the moment a guest walks through the door, driving immediate engagement.
- Reduced Support Overhead: Eliminating captive portals drastically reduces helpdesk tickets related to login failures, browser redirects, and forgotten passwords, freeing up IT resources.
- Data Monetization: By integrating with Wayfinding and loyalty platforms, venues can correlate physical presence with purchasing behaviour, providing actionable insights that justify the network investment.
Listen to our comprehensive briefing on this topic:
Key Terms & Definitions
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance certification based on the IEEE 802.11u standard that enables devices to automatically discover and securely connect to Wi-Fi networks without user intervention.
IT teams deploy Passpoint to replace legacy captive portals, providing a cellular-like roaming experience for enterprise and guest WiFi.
OpenRoaming
A global roaming federation managed by the Wireless Broadband Alliance (WBA) that connects Identity Providers (IdPs) with Access Networks using Passpoint technology.
Venues join OpenRoaming to allow guests to authenticate using existing credentials (e.g., Apple ID, Google, Carrier SIM) without managing local accounts.
ANQP (Access Network Query Protocol)
A Layer 2 protocol defined in 802.11u that allows a client device to request information from an Access Point (such as supported roaming partners) before associating with the network.
ANQP is the mechanism that allows a smartphone to 'know' if it can connect to a Passpoint network silently in the background.
RadSec (RADIUS over TLS)
A protocol that secures RADIUS authentication traffic by wrapping it in a TLS tunnel, typically using TCP port 2083.
Essential for OpenRoaming deployments to ensure that authentication requests sent from the venue to the cloud RADIUS provider cannot be intercepted.
OUI (Organizationally Unique Identifier)
A 24-bit number that uniquely identifies a vendor, manufacturer, or organization, used in Passpoint to identify supported roaming consortiums.
Network admins configure specific OUIs on their WLCs to broadcast which identity providers or federations (like OpenRoaming) are supported at the venue.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A highly secure authentication framework that requires mutual certificate-based authentication between the client and the server.
The gold standard for Passpoint authentication, ensuring that both the user's device and the venue's network verify each other's identities before connecting.
OSU (Online Sign-Up)
A standardized mechanism in Passpoint Release 2 and later that allows a device to securely obtain network credentials and a profile from a provisioning server.
Used to onboard new guests who do not already have a Passpoint profile installed on their device.
Evil Twin Attack
A wireless attack where a malicious actor sets up a rogue Access Point broadcasting the same SSID as a legitimate network to intercept user traffic and credentials.
Passpoint eliminates this risk by requiring the network to present a valid certificate (mutual authentication) before the device will connect.
Case Studies
A global hotel chain with 200 properties wants to improve guest connectivity and increase the adoption of its loyalty app. Guests currently complain about having to log in to the captive portal every day of their stay, and attach rates are low.
The hotel deploys Passpoint across all properties. Instead of a captive portal, they integrate Passpoint profile provisioning into their loyalty app. When a guest downloads the app and logs in, a Passpoint profile is silently installed on their device. The APs are configured to broadcast the hotel's specific Roaming Consortium OUI. The WLC uses RadSec to forward authentication requests to a cloud RADIUS provider. When the guest arrives at any property globally, their device detects the OUI, authenticates via EAP-TLS using the profile, and connects instantly with WPA3 encryption.
A large conference centre needs to provide secure WiFi for 10,000 attendees. Managing temporary credentials for a 3-day event via a captive portal is operationally heavy and insecure.
The venue implements OpenRoaming. They configure their WLC to broadcast the WBA OpenRoaming OUIs and establish a RadSec connection to an OpenRoaming Ecosystem Broker. Attendees arriving at the venue who already have an OpenRoaming profile (e.g., via their mobile carrier or a previous venue) connect automatically. For attendees without a profile, the venue provides QR codes around the concourse that direct users to an Online Sign-Up (OSU) server to download a temporary event profile.
Scenario Analysis
Q1. You are the IT Director for a retail chain. Marketing wants to track repeat customer visits accurately using WiFi analytics, but the current open guest network with a captive portal has a 15% attach rate. Customers complain the login takes too long. How do you redesign the network access strategy to meet Marketing's goals while improving the customer experience?
💡 Hint:Consider how you can tie network authentication to an asset the customer already values, removing the friction of the captive portal entirely.
Show Recommended Approach
Implement Passpoint and integrate the profile provisioning into the retailer's existing mobile loyalty app. When customers download or update the app, the Passpoint profile is silently installed. Upon entering any store, their device authenticates automatically via EAP-TLS. This removes the captive portal friction, dramatically increases the attach rate (providing Marketing with accurate repeat visit data), and secures the connection with WPA3.
Q2. During a pilot deployment of OpenRoaming at a stadium, the network team notices that while authentication requests are reaching the local WLC, they are failing to reach the cloud RADIUS provider. The firewall team confirms that standard RADIUS ports (UDP 1812/1813) are open outbound. What is the most likely cause of the failure?
💡 Hint:OpenRoaming Ecosystem Brokers mandate secure communication for authentication traffic over the internet.
Show Recommended Approach
The WLC is likely attempting to send standard, unencrypted RADIUS traffic, but OpenRoaming deployments require RadSec (RADIUS over TLS) for communication with the cloud broker. The firewall team needs to ensure that TCP port 2083 (the standard port for RadSec) is open outbound, and the WLC must be configured to establish the TLS tunnel using the correct certificates.
Q3. A hospital wants to deploy Passpoint to provide seamless roaming for doctors moving between the main campus and satellite clinics. However, the Information Security Officer (ISO) is concerned about 'evil twin' attacks where a malicious actor might spoof the hospital's SSID at a nearby coffee shop to steal credentials. How does Passpoint address this specific concern?
💡 Hint:Focus on the specific EAP methods used in Passpoint and how the client device verifies the network before transmitting data.
Show Recommended Approach
Passpoint mitigates the evil twin risk through mutual authentication, typically using EAP-TLS or EAP-TTLS. Before the doctor's device sends any authentication credentials, the AP (via the RADIUS server) must present a valid digital certificate. The device verifies this certificate against its trusted Root CAs. If a malicious actor spoofs the SSID, they will not possess the valid private key/certificate for the hospital's RADIUS server, and the device will silently abort the connection before any credentials are exchanged.
Key Takeaways
- ✓Passpoint (802.11u) eliminates captive portals by enabling devices to discover and connect to networks automatically and securely.
- ✓OpenRoaming scales Passpoint by creating a global federation, allowing users to authenticate using existing trusted identities (Apple, Google, Carriers).
- ✓Security is drastically improved through WPA3 encryption from the first packet and mutual certificate authentication, neutralizing 'evil twin' attacks.
- ✓Deploying Passpoint requires WPA3-capable access points, a cloud RADIUS provider, and RadSec (RADIUS over TLS) for secure external communication.
- ✓Integrating Passpoint profile provisioning into venue loyalty apps drives higher network attach rates and richer location-based analytics.
- ✓Venues should run a hybrid model during transition, broadcasting both the legacy captive portal SSID and the Passpoint SSID until adoption reaches critical mass.
- ✓OpenRoaming simplifies GDPR compliance by relying on anonymised persistent tokens rather than collecting personal data via splash pages.



