Identity-Based Networking: What It Is and Why It Matters
This guide provides a comprehensive technical reference on Identity-Based Networking (IBN) — what it is, how it works, and why it is a critical investment for any organisation managing large, diverse user populations across hotels, retail chains, stadiums, and public-sector venues. It covers the core IEEE 802.1X architecture, Purple's cloud-native implementation, real-world deployment scenarios, and a clear ROI framework to support procurement decisions.
🎧 Listen to this Guide
View Transcript
Executive Summary
Identity-Based Networking (IBN) represents a fundamental shift in how network access is managed, moving from a static, port-based model to a dynamic, user-centric one. In a traditional network, access rights are tied to physical ports or MAC addresses, creating a rigid and insecure environment. IBN ties network access privileges to a user's verified identity. This means that regardless of how or where a user connects — via Wi-Fi, Ethernet, or VPN — their access to network resources is determined by who they are, not what device they are using or where they are plugging in.
For organisations managing large, diverse user bases in environments like hotels, retail chains, and stadiums, this is a game-changer. It enables a Zero Trust security posture by default, where every user and device must be authenticated and authorised before gaining access. This dramatically simplifies network segmentation, enhances security by containing threats, and streamlines compliance with regulations like PCI DSS and GDPR.
For a CTO, IBN delivers significant ROI by reducing the administrative overhead of managing complex VLANs and access control lists (ACLs), mitigating the risk of security breaches, and providing deep visibility into network usage patterns that can inform business strategy. Purple's implementation of IBN leverages existing infrastructure and integrates seamlessly with cloud identity providers to deliver a scalable, resilient, and intelligent access layer fit for the modern enterprise.
Technical Deep-Dive
From Ports to People: The Core Architectural Shift
Traditional networking, a relic of a time when devices were static and users were tethered to desks, operates on a principle of implicit trust within a network perimeter. An authenticated device is trusted, and its physical connection point (a switch port) dictates its network access. This model is fraught with challenges in the modern era of BYOD (Bring Your Own Device), IoT, and mobile workforces.
Identity-Based Networking (IBN), often implemented using the IEEE 802.1X standard, fundamentally inverts this model. It decouples the user from the physical port and makes identity the new perimeter. The core components of an IBN architecture are:
Supplicant: The client device (e.g., laptop, smartphone) requesting network access. It runs software that communicates with the authenticator. Modern operating systems — Windows, macOS, iOS, and Android — include a native 802.1X supplicant, so no additional software installation is required for end users.
Authenticator: The network access device, such as a Wireless Access Point (WAP) or an Ethernet switch. It acts as a gatekeeper, blocking or allowing traffic from the supplicant. The authenticator holds the port in an unauthorised state until it receives explicit instruction from the authentication server.
Authentication Server (AS): Typically a RADIUS (Remote Authentication Dial-In User Service) server. This server is the intelligence layer of the operation. It receives the supplicant's credentials from the authenticator, validates them against an identity store (e.g., Azure Active Directory, Google Workspace, a local database), and sends back an authorisation decision that includes a specific network policy.
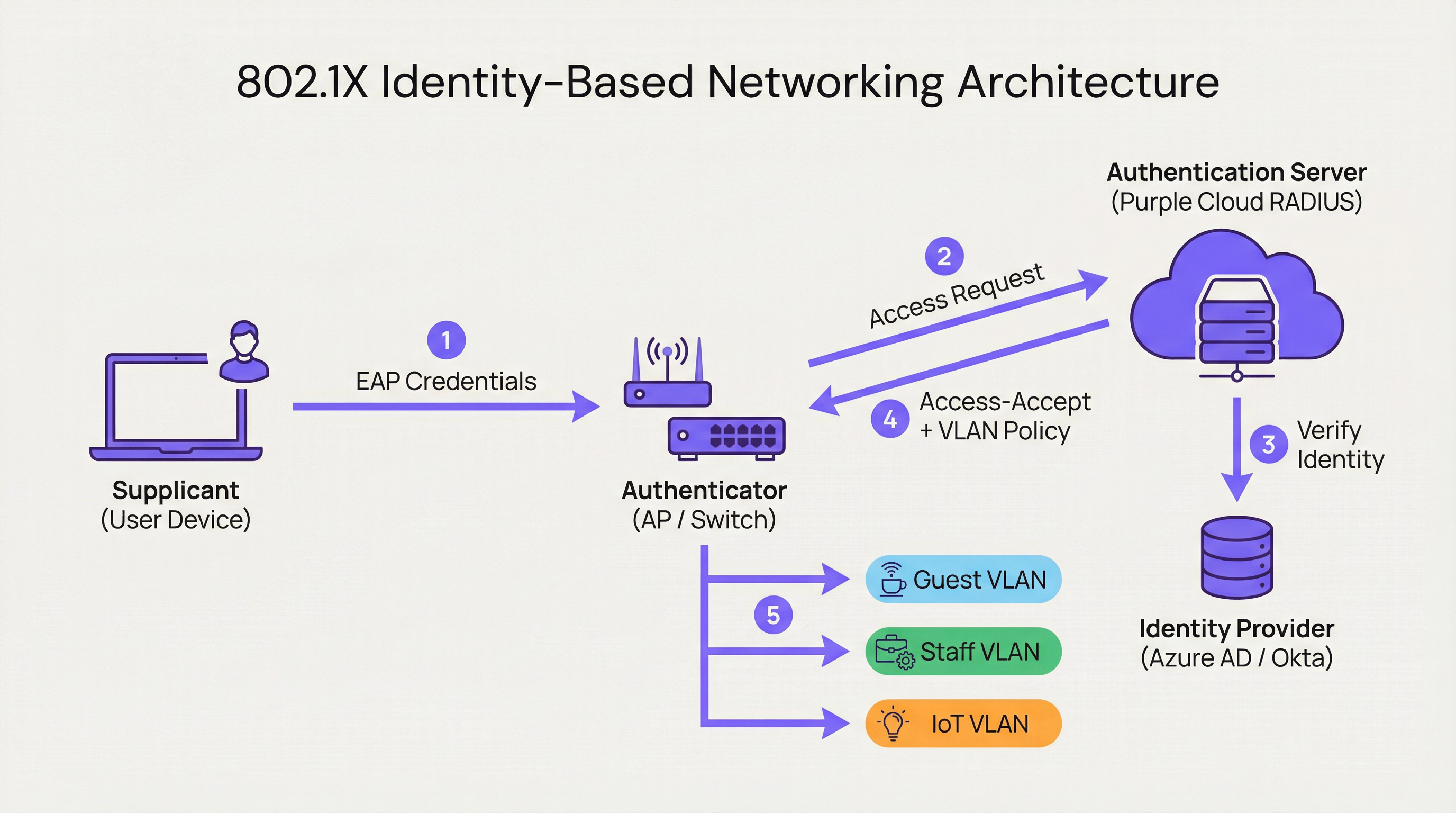
When a user connects, the authenticator places the port into an unauthorised state, blocking all traffic except for 802.1X authentication packets. The supplicant provides its credentials, which the authenticator forwards to the Authentication Server. The AS checks the identity and, based on pre-defined policies, instructs the authenticator on what to do. This instruction is not simply a binary allow or deny; it can include dynamic VLAN assignment, Quality of Service (QoS) profiles, session timeouts, and specific firewall rules. A corporate user might be placed on the CORP_VLAN with access to internal servers, while a guest is placed on the GUEST_VLAN with internet-only access — from the same SSID or physical port.
How Purple Implements IBN
Purple's platform acts as a cloud-native Authentication Server and policy engine, designed for the complexities of large public venues. Our approach focuses on abstracting away the complexity of RADIUS and 802.1X configuration.
Cloud-Native RADIUS: We eliminate the need for on-premises authentication servers, providing a globally distributed, highly available service that scales on demand. There are no servers to rack, no firmware to patch, and no single point of failure.
Identity Provider (IdP) Integration: We connect seamlessly with leading IdPs including Azure AD, Okta, and Google Workspace. This allows organisations to use their existing single source of truth for identity, ensuring that when an employee's account is disabled, their network access is revoked instantly.
Dynamic Policy Engine: Our intuitive management console allows IT managers to create granular access policies based on user attributes such as group membership, role, and department. A policy might state: "All users in the 'Retail-Staff' group connecting to the 'Staff-WiFi' SSID between 9 AM and 5 PM are assigned to the 'POS_VLAN' with a bandwidth limit of 10 Mbps."
Dynamic VLAN Assignment: This is a cornerstone of our IBN implementation. Instead of manually configuring VLANs on every switch port, the network dynamically assigns a user to the correct VLAN based on their identity. This is a massive operational efficiency gain and a significant security enhancement.

Implementation Guide
Deploying IBN with Purple is a structured process designed to minimise disruption and maximise security from day one.
Step 1: Network Infrastructure Audit
Before deployment, verify that your network hardware — switches and access points — supports IEEE 802.1X. Most enterprise-grade equipment manufactured in the last decade does. This includes vendors such as Cisco, Meraki, Aruba, and Ruckus. Ensure all firmware is current, as older firmware versions can have known 802.1X vulnerabilities.
Step 2: Define User Roles and Access Policies
This is the most critical phase. Work with stakeholders from HR, operations, and management to classify all network users into distinct roles. Common examples include Corporate Staff (full access to internal resources), Guest Users (internet-only access via a captive portal), Contractors (time-limited access to specific applications), and IoT Devices (highly restricted access to a dedicated VLAN, communicating only with their specific management server). For each role, define the required access level explicitly.
Step 3: Configure Purple as the Authentication Server
In your network controller — such as Meraki Dashboard or Aruba Central — configure a new RADIUS profile pointing to the Purple authentication endpoints with a shared secret. This establishes the trust relationship between your network hardware and the Purple cloud. Purple's onboarding documentation provides step-by-step configuration guides for all major hardware vendors.
Step 4: Phased Rollout and Testing
Do not attempt a flash-cut migration. Start with a pilot group of users or a specific area of your venue, such as a single floor or a non-critical retail store. Create a new, dedicated SSID for the IBN trial. Onboard pilot users and test all defined roles. Validate that users are being assigned to the correct VLANs and that access permissions are correctly enforced. Critically, test failure modes: what happens if the RADIUS server is unreachable? Configure hardware for a fail-closed posture.
Step 5: Full Deployment and Legacy Decommissioning
Once the pilot is successful, expand the rollout across the entire organisation. Develop a clear communication plan to guide users through the one-time process of connecting to the new secure network. Once all users are migrated, decommission the old, insecure SSIDs and port configurations.
Best Practices
Leverage WPA3-Enterprise: Where supported, use WPA3-Enterprise in conjunction with 802.1X. It offers significant security enhancements over WPA2, including protection for management frames (802.11w) and stronger encryption algorithms.
Certificate-Based Authentication: For corporate devices, move beyond username and password credentials (EAP-PEAP) and implement certificate-based authentication (EAP-TLS). This is the gold standard for 802.1X security, as it mitigates phishing risks and simplifies the user experience by eliminating password prompts.
Centralise Identity: Maintain a single, authoritative source of truth for user identity. This prevents identity sprawl and ensures that when an employee leaves the organisation, their network access is revoked instantly at the source.
Regular Policy Review: User roles and access requirements change. Conduct quarterly reviews of your IBN policies to ensure they still align with business needs and security principles. Prune unused roles and tighten permissive rules.
| Best Practice | Standard / Reference | Priority |
|---|---|---|
| WPA3-Enterprise | IEEE 802.11ax, Wi-Fi Alliance | High |
| Certificate Authentication (EAP-TLS) | RFC 5216 | High |
| Dynamic VLAN Segmentation | IEEE 802.1Q | Critical |
| Centralised Identity (IdP) | NIST SP 800-63 | Critical |
| Fail-Closed RADIUS Policy | CIS Benchmark | High |
| Quarterly Policy Review | ISO 27001 | Medium |
Troubleshooting & Risk Mitigation
Failure Mode: RADIUS Server Unreachable
If the authenticator cannot reach the Purple cloud, the default hardware behaviour may be to fail-open (allow all access) or fail-closed (deny all access). Configure your hardware for a fail-closed posture for maximum security. Purple's geo-distributed infrastructure makes extended outages highly unlikely, but defence-in-depth is essential. Consider configuring a local RADIUS fallback for critical infrastructure.
Failure Mode: Misconfigured Policies
A poorly written policy can grant excessive privileges or deny legitimate access. Use a staging environment or a pilot group to test every policy change before rolling it out to production. Purple's policy simulator allows you to test a user's expected access level before committing a change.
Risk: Onboarding Complexity
The initial connection process for users can be complex, especially with certificate deployment. Provide clear, step-by-step guides with screenshots and offer helpdesk support during the transition period. Consider deploying an onboarding tool like Purple's Network Access Manager to automate the device configuration process.
Risk: Legacy Devices Without 802.1X Support
Not all devices — particularly older IoT hardware, printers, and medical equipment — support 802.1X. Use MAC Authentication Bypass (MAB) for these devices, pre-registering their MAC addresses and assigning them to highly restricted, isolated VLANs with strict firewall rules.
ROI & Business Impact
The business case for IBN is built on three pillars: cost reduction, risk mitigation, and business enablement.
Cost Reduction: The primary saving is operational. Automating VLAN and ACL management drastically reduces the man-hours required for network administration. Dynamic VLAN assignment can reduce network provisioning time by over 85%, according to independent network operations benchmarks. This frees IT staff to focus on strategic initiatives rather than routine maintenance.
Risk Mitigation: The cost of a data breach is substantial — IBM's Cost of a Data Breach Report consistently places the global average above USD 4 million. By implementing a Zero Trust model and micro-segmentation, IBN significantly reduces the attack surface. If a user's device is compromised, the breach is contained within their specific, limited network segment. This is critical for PCI DSS compliance in retail and GDPR compliance in public-sector organisations.
Business Enablement: IBN provides rich data on who is using the network, where they are, and what they are doing. This intelligence is invaluable for venue operations. A hotel can understand guest movement patterns, a retailer can analyse footfall in different departments, and a stadium can optimise staffing based on real-time crowd density. This transforms the network from a cost centre into a strategic business asset.
| ROI Dimension | Metric | Typical Outcome |
|---|---|---|
| Operational Efficiency | IT admin hours saved per week | 40-60% reduction |
| Security Posture | Attack surface reduction | Significant via micro-segmentation |
| Compliance | Audit preparation time | Reduced via automated logging |
| Business Intelligence | Guest data capture rate | Increased via captive portal integration |
| Staff Productivity | Network provisioning time | 85%+ reduction |
Key Terms & Definitions
Identity-Based Networking (IBN)
An approach to network administration where access to network resources is granted based on the authenticated identity of a user or device, rather than its physical connection point or IP address.
IT teams use IBN to create more secure and flexible networks that can handle BYOD, IoT, and mobile users safely. It is the foundational technology for a Zero Trust network architecture.
IEEE 802.1X
An IEEE standard for Port-Based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, using the EAP framework to carry authentication credentials.
This is the primary technical standard that underpins most IBN deployments. Network hardware must support 802.1X to be compatible with an identity-driven access model.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service.
The RADIUS server is the brain of an IBN system. It makes the decisions about who gets access and what level of access they receive. Purple provides this as a cloud-native service, eliminating the need for on-premises RADIUS infrastructure.
Dynamic VLAN Assignment
The ability of a network to assign a user to a specific Virtual LAN (VLAN) based on their authenticated identity, regardless of the physical port or SSID they connect to.
This is a key operational benefit of IBN. It automates the process of network segmentation, saving significant administrative time and reducing the risk of misconfiguration that leads to security incidents.
Supplicant
The software on a client device (such as a laptop or smartphone) that provides credentials to the network authenticator as part of the 802.1X authentication process.
Modern operating systems (Windows, macOS, iOS, Android) have a built-in 802.1X supplicant, so end users do not need to install any special software to connect to an IBN-secured network.
EAP (Extensible Authentication Protocol)
An authentication framework that provides a common way for supplicants and authentication servers to negotiate an authentication method. Common EAP types include EAP-TLS (certificate-based) and EAP-PEAP (password-based).
IT teams choose an EAP type based on their desired balance of security and usability. EAP-TLS is the most secure option and is recommended for corporate devices; EAP-PEAP is simpler to deploy but relies on password security.
MAC Authentication Bypass (MAB)
A technique that allows devices without 802.1X supplicant support to be authenticated on an IBN network by pre-registering their hardware MAC address with the authentication server.
MAB is a pragmatic solution for IoT devices, printers, and legacy hardware that cannot participate in 802.1X. It is less secure than full 802.1X authentication and should be combined with strict VLAN isolation and firewall rules.
Zero Trust
A security model based on the principle of 'never trust, always verify.' It requires that all users, whether inside or outside the organisation's network, be authenticated, authorised, and continuously validated before being granted access to applications and data.
IBN is a foundational technology for implementing a Zero Trust architecture. It ensures that the principle of 'always verify' is applied right at the network edge, before any traffic is allowed to flow.
WPA3-Enterprise
The latest generation of the Wi-Fi Protected Access security protocol for enterprise networks. It mandates the use of 802.1X authentication and offers stronger encryption (192-bit security mode) and protection for management frames.
IT teams should target WPA3-Enterprise for all new deployments and hardware refreshes. It provides a significant security uplift over WPA2-Enterprise, particularly in high-density public environments.
Case Studies
A 500-room luxury hotel needs to provide secure, differentiated Wi-Fi access for guests, conference attendees, staff, and back-of-house IoT devices (minibars, smart locks). They currently use a single, shared WPA2-Personal password for everyone, which is a major security and compliance risk.
Role Definition: Define four distinct roles: Guest, Conference, Staff, and IoT.
Policy Creation in Purple:
- Guest: Authenticate via captive portal with room number and surname. Assign to Guest_VLAN with a 20 Mbps bandwidth cap and client isolation enabled to prevent peer-to-peer attacks.
- Conference: Authenticate via a shared, time-limited credential provided by the event organiser. Assign to Conference_VLAN with a 50 Mbps cap, allowing communication between devices within the same conference group.
- Staff: Authenticate via Azure AD credentials. Assign to Staff_VLAN with access to the Property Management System (PMS) and internal servers only.
- IoT: Authenticate using MAC Authentication Bypass (MAB) with a pre-registered list of device MAC addresses. Assign to IoT_VLAN, which has no internet access and can only communicate with the IoT management platform.
Network Configuration: Configure hotel APs to use Purple's cloud RADIUS. Create a single SSID, Hotel_WiFi, using WPA2/WPA3-Enterprise.
Rollout: Pilot the new SSID in a single wing of the hotel before full deployment. Validate each role before expanding.
A retail chain with 150 stores wants to replace its aging guest Wi-Fi and provide secure network access for corporate staff, store associates using handheld scanners, and third-party vendors (merchandisers). They need to achieve and maintain PCI DSS compliance.
Role Definition: Define four roles: Corporate, Store_Associate, Vendor, and Guest.
Policy Creation in Purple:
- Corporate: Authenticate via Okta credentials. Assign to CORP_VLAN with full network access.
- Store_Associate: Authenticate handheld scanners via EAP-TLS (device certificates issued by the company CA). Assign to POS_VLAN, which is fully segmented from all other network traffic and only has access to the payment processing gateway and inventory server. This is the critical control for PCI DSS compliance.
- Vendor: Authenticate via a self-service portal where they register for time-limited access (e.g., 8 hours). Assign to Vendor_VLAN with internet-only access.
- Guest: Authenticate via a social login (Facebook, Google) or email on a branded captive portal. Assign to Guest_VLAN with client isolation.
Network Configuration: Deploy Meraki APs in all stores, managed centrally via Meraki Dashboard. Configure the Retail_Secure SSID to point to Purple for authentication. Centralise all policy management in Purple.
Measurement: Use Purple's analytics to track guest engagement, dwell times, and repeat visits, providing valuable data to the marketing team and demonstrating the commercial value of the Wi-Fi investment.
Scenario Analysis
Q1. A large conference centre is hosting a high-profile tech event with 5,000 attendees, 200 event staff, and a dedicated live-streaming production crew requiring guaranteed bandwidth. How would you design the IBN policy to serve all three groups from a single network infrastructure?
💡 Hint:Consider the distinct requirements of each group: attendees need basic internet access, staff need access to event management systems, and the production crew needs guaranteed, high-priority bandwidth with no contention.
Show Recommended Approach
Define three distinct roles. Attendees authenticate via a simple captive portal (email address or event registration code). Place them on a Public_VLAN with a strict per-client bandwidth limit (e.g., 5 Mbps) and client isolation enabled to prevent peer-to-peer attacks and ensure fair bandwidth distribution. Event Staff authenticate using pre-shared credentials managed by the event organiser. Place them on a Staff_VLAN with a higher bandwidth limit (e.g., 25 Mbps) and access to event management systems. Production Crew is the most critical group. Authenticate their equipment using EAP-TLS certificates for maximum security. Place them on a dedicated Production_VLAN with the highest QoS priority (DSCP EF marking) and no bandwidth restrictions. This VLAN must be completely isolated from all other traffic to guarantee performance for the live stream. Use Purple's policy engine to set session timeouts for attendee credentials that align with the event schedule.
Q2. Your CFO is questioning the investment in an IBN solution, arguing that the existing WPA2-Personal passwords 'work fine.' How do you construct a compelling business case focused on ROI?
💡 Hint:Translate the technical benefits — security, automation, compliance — into financial terms: cost savings, risk reduction, and revenue enablement.
Show Recommended Approach
The business case has three parts. First, Operational Savings: calculate the weekly hours your IT team spends on manual network changes (MAC whitelisting, VLAN updates, ACL changes, password resets). Show how automating this with IBN frees up that time for strategic projects. Even recovering five hours per week at a fully-loaded cost of £50/hour represents £13,000 per year in recovered productivity. Second, Risk Reduction: reference industry data on the average cost of a data breach. Frame IBN as an insurance policy that significantly lowers the probability of such an event by implementing micro-segmentation and Zero Trust principles. Third, Compliance Costs: if subject to PCI DSS or GDPR, highlight the cost of failing an audit or the scale of potential regulatory fines (up to 4% of global annual turnover under GDPR). Position IBN as a key enabler for compliance, directly reducing that financial risk.
Q3. You are deploying IBN in a hospital. A critical piece of medical equipment — an MRI scanner — does not support 802.1X. How do you securely connect it to the network while maintaining your Zero Trust posture?
💡 Hint:The device cannot authenticate itself using standard 802.1X. How can the network authenticate it on its behalf, and what compensating controls are needed?
Show Recommended Approach
This is a classic use case for MAC Authentication Bypass (MAB). Register the MRI scanner's MAC address in the Purple platform and associate it with a Medical_Device access profile. When the switch detects that MAC address, it queries Purple, which instructs the switch to place the device into a highly restricted Medical_VLAN. This VLAN must have a strict firewall policy (implemented at the network layer) that only permits the MRI machine to communicate with its dedicated imaging server on specific ports, and blocks all other traffic. This provides a secure, albeit less ideal, alternative to 802.1X for legacy or non-supplicant devices. Document this as a known exception in your security risk register, and schedule a hardware refresh to a 802.1X-capable model at the next available opportunity. The compensating control of strict VLAN isolation and firewall rules is the key to maintaining your Zero Trust posture.
Key Takeaways
- ✓Identity-Based Networking (IBN) ties network access to verified user identity, not physical ports or MAC addresses.
- ✓It is a core component of a modern Zero Trust security strategy, operating on the principle of 'never trust, always verify.'
- ✓Key enabling technologies are IEEE 802.1X, RADIUS, EAP, and dynamic VLAN assignment.
- ✓IBN dramatically simplifies network administration by automating VLAN and access rule management.
- ✓It delivers measurable ROI through reduced operational costs, mitigated breach risk, and enhanced regulatory compliance (PCI DSS, GDPR).
- ✓Purple provides a cloud-native RADIUS platform that integrates with existing IdPs (Azure AD, Okta) to implement IBN at scale without on-premises infrastructure.
- ✓Deployment should follow a phased approach: audit infrastructure, define roles, configure Purple, pilot test, then roll out fully.



