Splash Page Design Best Practices for Guest WiFi
This guide provides IT managers, network architects, and venue operations directors with a definitive technical reference for designing and deploying high-performance guest WiFi splash pages. It covers the four core pillars of effective captive portal design — brand identity, user experience, data capture, and legal compliance — and translates them into actionable deployment guidance. By following these best practices, organisations can expect measurable improvements in guest connection rates, marketing database growth, and demonstrable ROI from their guest WiFi infrastructure.
🎧 Listen to this Guide
View Transcript
Executive Summary
The guest WiFi splash page — or captive portal — is the single most consequential touchpoint in any venue's wireless deployment. It is the first interaction a guest has with your network, and it determines whether they connect at all. Yet it remains one of the most consistently under-engineered components of enterprise WiFi infrastructure. A poorly designed splash page does not merely frustrate users; it actively destroys the commercial value of a network investment that may run into hundreds of thousands of pounds.
This guide is structured for senior IT and operations professionals who need to make implementation decisions now. It covers the technical architecture of captive portal authentication, the UX principles that drive conversion, the legal and compliance obligations under GDPR and related frameworks, and the branding requirements that transform a login screen into a revenue-generating asset. Real-world deployment scenarios from hospitality, retail, and events sectors are included to ground every recommendation in operational reality. The core argument is straightforward: your splash page is not a security tick box. It is a strategic business tool, and it should be designed accordingly.
Technical Deep-Dive
How Captive Portal Authentication Works
A captive portal operates at the network access layer, intercepting all HTTP and HTTPS traffic from an unauthenticated client device and redirecting it to the splash page URL. The underlying mechanism relies on DNS hijacking and HTTP 302 redirects. When a device associates with the guest SSID, the access point or wireless controller assigns it a restricted IP address and routes all outbound traffic to the portal server. Until the user completes the authentication flow on the splash page, the device is held in a quarantine VLAN, with access restricted to the portal's IP address and any pre-authorised walled-garden domains (such as social login providers).
Upon successful authentication — whether via email submission, social login, SMS OTP, or voucher code — the controller or RADIUS server updates the client's authorisation state, moves it to the appropriate access VLAN, and grants internet connectivity. This entire flow must be transparent and fast. Any latency in the portal redirect or authentication response will be perceived by the user as the WiFi being broken.
From a standards perspective, the captive portal architecture is vendor-neutral and operates independently of the underlying wireless security protocol. However, the SSID itself should be configured with WPA3-Personal or WPA3-Enterprise where device compatibility allows, in accordance with the IEEE 802.11ax (Wi-Fi 6) specification. The captive portal layer handles identity and access management, while the underlying wireless protocol handles transmission security. These are distinct functions and must be architected separately.
Authentication Methods: A Comparative Analysis
The choice of authentication method is the most consequential design decision for any splash page deployment. Each method carries different implications for user friction, data richness, compliance overhead, and security posture.
| Authentication Method | Friction Level | Data Quality | GDPR Complexity | Best-Fit Venue Type |
|---|---|---|---|---|
| Click-through (T&Cs only) | Very Low | Minimal | Low | Airports, public transport, libraries |
| Email submission | Low | High (email, visit frequency) | Medium | Hotels, retail, restaurants |
| Social login (Facebook/Google) | Low-Medium | Very High (demographics) | High | Bars, entertainment venues, retail |
| SMS / OTP | Medium | High (verified mobile number) | Medium | Premium hospitality, healthcare |
| Voucher / PIN code | Low | None (anonymous) | Very Low | Conference centres, co-working spaces |
| RADIUS / Active Directory | Very Low (SSO) | Enterprise-grade | Low (internal users) | Corporate campus, education |
For most commercial deployments, email submission represents the optimal balance. It captures a durable, marketable identifier with minimal friction and is straightforward to manage under GDPR's lawful basis requirements. Social login is compelling for data richness but requires a more complex consent framework and introduces a dependency on third-party OAuth providers — a risk worth evaluating carefully in enterprise contexts.
Walled Garden Configuration
A walled garden is the set of domains and IP addresses that an unauthenticated client is permitted to access before completing the splash page flow. This is a critical configuration element. At minimum, the walled garden must include the portal server itself, any CDN endpoints serving portal assets, and the OAuth endpoints for any social login providers in use. Failure to correctly configure the walled garden is the most common cause of social login failures and is a frequent source of support tickets in new deployments.
HTTPS and Certificate Management
All splash pages must be served over HTTPS. Modern mobile operating systems, including iOS 14+ and Android 11+, will display security warnings or block connections to HTTP captive portals. Your portal server must present a valid TLS certificate from a trusted Certificate Authority. Self-signed certificates are not acceptable in production deployments. Certificate expiry is a common operational failure mode; automated renewal via Let's Encrypt or your platform provider's managed certificate service should be standard practice.
Implementation Guide
Phase 1: Requirements Definition
Before opening a design tool, the project team must align on four parameters: the authentication method (informed by the comparative analysis above), the data fields to capture (apply the principle of data minimisation — collect only what you will actively use), the marketing consent model (opt-in vs. opt-out, with opt-in strongly recommended for GDPR compliance), and the brand assets to be incorporated (logo files in SVG format, hex colour codes, approved typefaces).
Phase 2: Splash Page Design
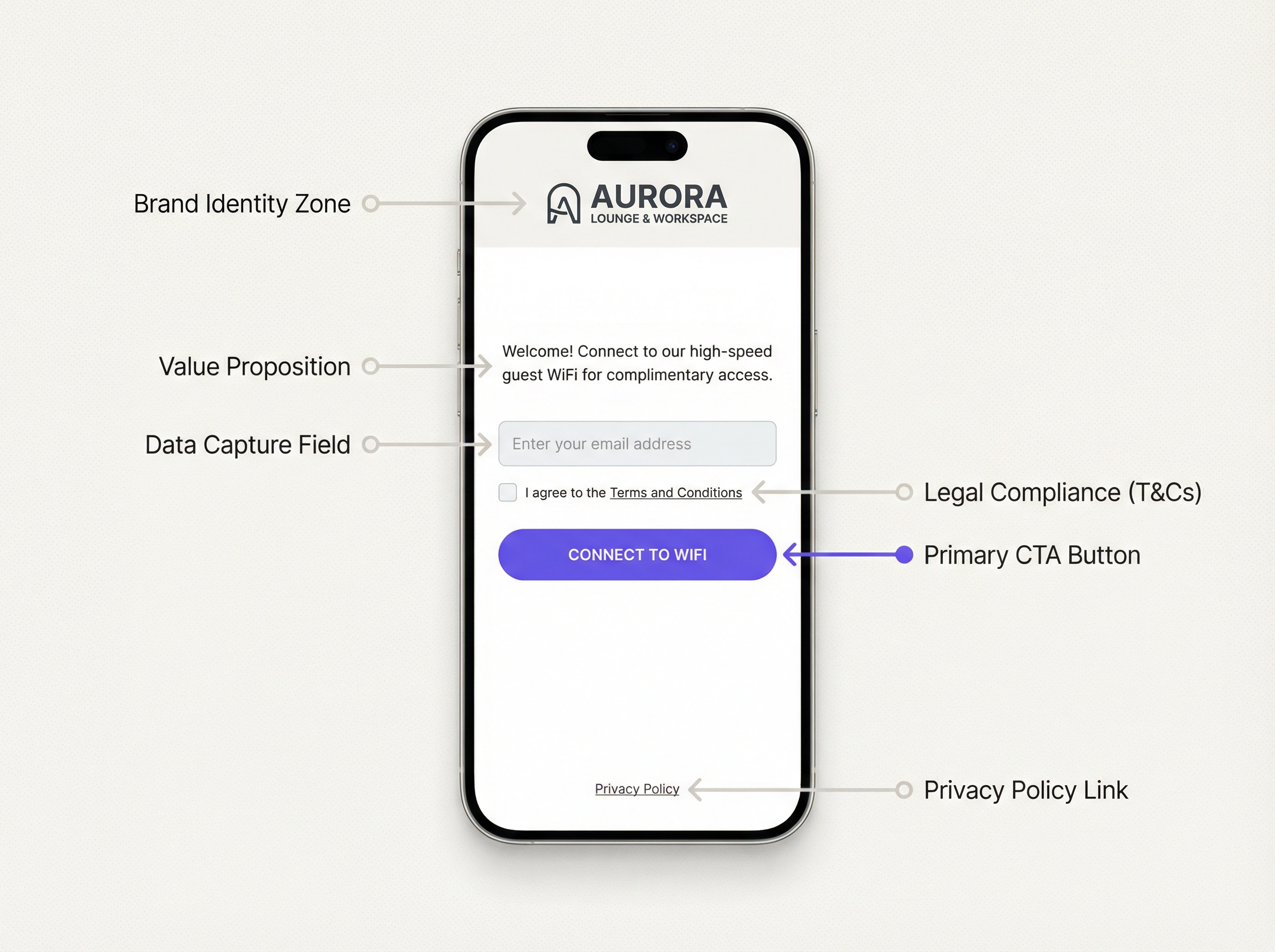
Effective WiFi splash page design follows a clear visual hierarchy. The brand identity zone occupies the top of the page and must load first. A concise value proposition — no more than one sentence — immediately follows. The authentication form is the central element and must be the most visually prominent interactive component. Legal compliance elements (T&Cs tick box, privacy policy link) sit below the form. The call-to-action button is the final element and must be large, high-contrast, and unambiguous.
Page weight is a critical performance variable. The total uncompressed size of all splash page assets — HTML, CSS, JavaScript, images — should not exceed 200KB. Background images, if used, must be compressed and served in modern formats (WebP preferred). A page that takes more than three seconds to load on a 4G connection will see a measurable increase in abandonment rates. Test performance using tools such as Google PageSpeed Insights and target a Largest Contentful Paint (LCP) of under 2.5 seconds.
Responsive design is non-negotiable. The majority of guest WiFi connections originate from smartphones. The splash page must render correctly at viewport widths from 320px to 1440px. Use CSS media queries and a mobile-first design approach. Avoid fixed-width layouts.
Phase 3: Platform Configuration
Deploy the splash page through your guest WiFi management platform. A production-grade platform such as Purple provides a template-based editor that allows marketing teams to manage brand updates without engineering intervention. Configure the SSID to redirect to the portal URL, set the session timeout and bandwidth policies, and define the walled garden domains. Conduct end-to-end testing across at least three device types (iOS, Android, Windows laptop) before going live.
Phase 4: Analytics and Optimisation
Post-deployment, instrument the splash page with conversion tracking. The key metrics are: Impression Rate (devices that detected the SSID), Portal View Rate (devices that loaded the splash page), Completion Rate (devices that successfully authenticated), and Drop-off Rate (the delta between views and completions). A healthy completion rate for an email-capture flow is above 65%. Rates below 50% indicate a UX or performance problem that warrants investigation.
Best Practices
The following recommendations represent the distilled guidance from enterprise deployments across hospitality, retail, and public-sector environments.
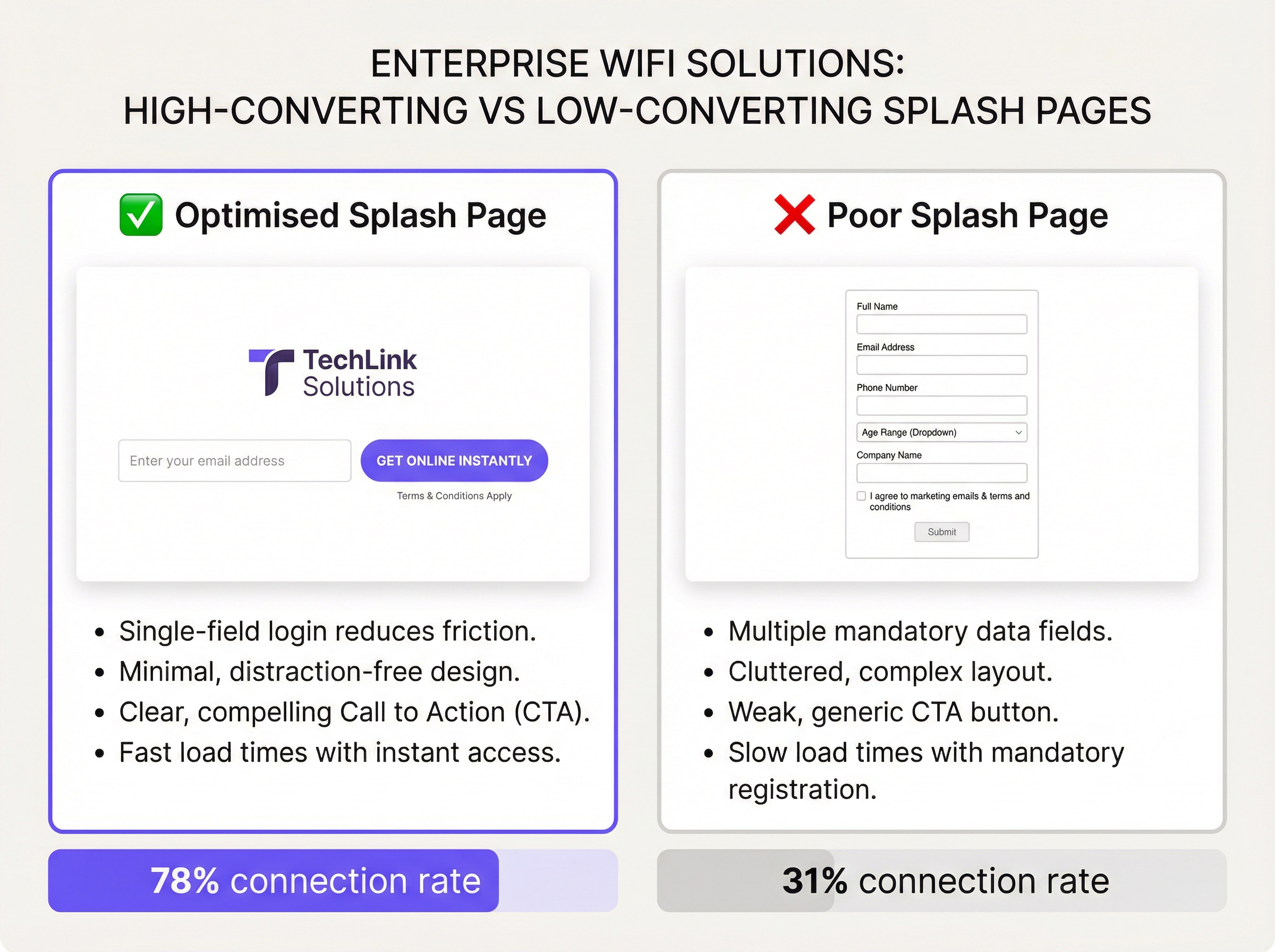
Minimise form fields. Every additional field reduces completion rates. Numerous A/B tests across large-scale deployments consistently show that moving from a two-field form (name + email) to a single-field form (email only) increases completion rates by 15-25 percentage points. Unless a specific business case justifies additional data collection, a single email field is the correct default.
Make the value proposition explicit. Users will not complete a form without understanding what they receive in return. A headline such as "Connect to free, high-speed WiFi" or "Get online in seconds" directly above the form field significantly improves conversion. Vague or absent value propositions are a leading cause of high drop-off rates.
Comply with GDPR by design. The splash page must present a clear, unbundled consent mechanism for marketing communications, separate from the T&Cs acceptance required for network access. Pre-ticked marketing consent tick boxes are non-compliant under GDPR Article 7. The privacy policy must be accessible via a clearly labelled link and must accurately describe how WiFi-derived data is processed, stored, and shared.
Implement session management correctly. Define appropriate session timeout and re-authentication intervals. A 24-hour session for hotel guests is standard. A 2-hour session for a coffee shop is appropriate. Forcing re-authentication every 30 minutes in a venue where guests stay for hours is a significant UX failure and a common complaint in hospitality environments.
Test across operating systems. iOS Captive Network Assistant (CNA) and Android's captive portal detection mechanism behave differently. iOS opens a mini-browser window (the CNA) to display the portal, which has limitations including no JavaScript support in older versions and restricted cookie handling. Ensure your portal degrades gracefully in the CNA environment. Test on current and N-1 versions of both iOS and Android.
Isolate guest traffic. The guest VLAN must be firewalled from all internal corporate networks, management interfaces, and POS systems. This is a fundamental network security requirement and is mandated under PCI DSS Requirement 1.3 for any venue that processes card payments. Failure to segment guest traffic is a critical security vulnerability.
Troubleshooting & Risk Mitigation
Common Failure Modes
The table below catalogues the most frequently encountered issues in captive portal deployments and their root causes.
| Symptom | Root Cause | Resolution |
|---|---|---|
| Portal page does not appear | DNS hijacking not configured; client using DoH/DoT | Ensure controller intercepts DNS; block DNS-over-HTTPS at firewall |
| Social login fails | OAuth provider not in walled garden | Add all OAuth endpoints and CDN domains to walled garden |
| HTTPS warning on portal | Expired or self-signed TLS certificate | Deploy valid certificate; implement automated renewal |
| iOS CNA shows blank page | JavaScript dependency in portal; CNA JS restrictions | Audit portal for CNA compatibility; use server-side rendering |
| High drop-off rate | Too many form fields; slow page load; unclear CTA | Reduce fields; optimise assets; A/B test CTA copy |
| Users cannot reconnect after session expiry | Session token not cleared; MAC address not re-evaluated | Review session management configuration in controller |
| GDPR audit finding | Pre-ticked consent boxes; missing privacy policy link | Remediate consent UX; add compliant privacy policy link |
Risk Mitigation: The Compliance Audit Checklist
Before any guest WiFi deployment goes live, the following compliance items must be verified: the privacy policy is current and accurately reflects data processing activities; marketing consent is opt-in and unbundled from T&Cs; data retention periods are defined and enforced; a process exists for handling Subject Access Requests (SARs) for WiFi-derived data; and guest traffic is fully isolated from internal networks and PCI-scoped systems.
ROI & Business Impact
The commercial case for investing in a well-designed splash page is straightforward. Guest WiFi data — primarily email addresses and visit frequency data — is among the most valuable first-party data an organisation can collect. With third-party cookies deprecated across major browsers and mobile advertising identifiers increasingly restricted, the email address captured at the WiFi login point is a durable, consent-based, owned marketing asset.
Consider the economics of a 200-location retail chain. If each location serves 300 unique guest WiFi users per day and the current completion rate is 35%, the chain captures approximately 21,000 email addresses per day. By optimising the splash page to achieve a 70% completion rate — a realistic target with the practices described in this guide — that figure doubles to 42,000 per day. Over a year, this represents an additional 7.6 million opted-in contacts entering the marketing database. At a conservative email marketing revenue attribution of £0.10 per contact per year, this optimisation is worth £760,000 in incremental annual revenue — from a design change that costs a fraction of that to implement.
Beyond direct marketing value, the splash page is the entry point to a broader guest intelligence platform. Dwell time analytics, repeat visit frequency, peak footfall mapping, and customer journey analysis all originate from the authentication event. This data informs operational decisions — staffing levels, store layout, promotional timing — that have measurable impact on operational efficiency and revenue per square foot.
The ROI calculation for splash page optimisation is therefore not a marketing exercise. It is a data infrastructure investment with compounding returns.
Key Terms & Definitions
Captive Portal
A network access control mechanism that intercepts all HTTP/HTTPS traffic from an unauthenticated client and redirects it to an authentication web page before granting internet access. Operates at the access layer via DNS hijacking and HTTP 302 redirects.
IT teams encounter this term when configuring wireless controllers, access points, and network management platforms. It is the technical term for what marketing teams call a 'splash page' or 'WiFi login page'. Understanding the distinction between the portal mechanism and the page design is essential for effective troubleshooting.
Splash Page
The web page presented to a guest WiFi user via the captive portal mechanism. It is the user-facing interface for authentication and is the primary point of brand expression, data capture, and legal consent in a guest WiFi deployment.
The term is used interchangeably with 'captive portal' in commercial contexts, though strictly speaking the splash page is the front-end design layer and the captive portal is the underlying network mechanism. IT managers should be precise about this distinction when briefing design agencies or platform vendors.
Walled Garden
A defined set of IP addresses, domains, and URLs that an unauthenticated client device is permitted to access before completing the splash page authentication flow. Configured at the wireless controller or firewall level.
Encountered during initial deployment configuration and whenever the splash page design changes. An incorrectly configured walled garden is the most common cause of social login failures and broken portal page rendering. Must be reviewed and updated whenever new authentication methods or third-party scripts are added to the splash page.
GDPR (General Data Protection Regulation)
EU Regulation 2016/679, applicable in the UK as the UK GDPR post-Brexit. Governs the collection, processing, storage, and transfer of personal data. Requires a lawful basis for processing, explicit and unbundled consent for marketing communications, and the right for individuals to access, rectify, and erase their data.
Directly applicable to any splash page that collects personal data (email addresses, names, device identifiers). IT and marketing teams must ensure the splash page's consent mechanism, privacy policy, and data retention practices are compliant. Non-compliance carries fines of up to 4% of global annual turnover under Article 83.
WPA3 (Wi-Fi Protected Access 3)
The current generation wireless security protocol defined by the Wi-Fi Alliance, superseding WPA2. Introduces Simultaneous Authentication of Equals (SAE) for stronger password-based authentication, enhanced protection against offline dictionary attacks, and mandatory use of Protected Management Frames (PMF).
Relevant when specifying SSID security configuration for guest networks. WPA3-Personal is recommended for guest SSIDs where device compatibility allows. Note that WPA3 governs transmission security and is distinct from the captive portal authentication layer, which operates at the application layer.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorisation, and Accounting (AAA) management for users connecting to a network. Defined in RFC 2865. Used in enterprise WiFi deployments to validate credentials against a central directory (e.g., Active Directory, LDAP) and enforce access policies.
Encountered in enterprise and education deployments where guest WiFi must integrate with existing identity infrastructure. For pure guest WiFi with email capture, RADIUS is typically not required. It becomes relevant when deploying 802.1X-authenticated SSIDs for staff or when integrating with a centralised policy management platform.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards defined by the PCI Security Standards Council, mandating controls for any organisation that stores, processes, or transmits cardholder data. Requirement 1.3 mandates network segmentation to isolate cardholder data environments from all other networks, including guest WiFi.
Directly applicable to hotels, retailers, and any venue that processes card payments on the same physical network infrastructure as the guest WiFi. IT teams must ensure the guest VLAN is fully isolated from POS systems, payment terminals, and any system in scope for PCI DSS. Failure to segment is a critical finding in PCI audits.
Progressive Profiling
A data collection strategy in which additional user attributes are requested incrementally across multiple sessions, rather than all at once during the initial authentication. Each subsequent interaction presents a short, optional prompt to enrich the user's profile.
Highly relevant for retail and hospitality deployments where richer demographic data is commercially valuable but front-loading a long form would suppress connection rates. Implemented at the platform level, with conditional logic that detects returning devices and presents appropriate prompts. Must be clearly disclosed in the privacy policy.
Conversion Rate (WiFi Context)
The percentage of devices that load the splash page and successfully complete the authentication flow, expressed as: (Authenticated Sessions / Portal Page Views) x 100. A key performance indicator for splash page effectiveness.
The primary metric for evaluating splash page performance. IT and marketing teams should establish a baseline conversion rate at deployment and track it continuously. A rate below 50% for an email-capture flow indicates a significant UX or performance issue. Rates above 70% are achievable with optimised single-field designs and clear value propositions.
Case Studies
A 350-room business hotel in central London is deploying a new guest WiFi infrastructure across its property. The hotel's marketing team wants to capture guest email addresses for post-stay communications, while the IT team is concerned about GDPR compliance and network security. The hotel also hosts corporate events and needs to support conference delegates who expect seamless, fast connectivity. How should the splash page be designed and configured to meet all of these requirements?
The deployment should use a tiered SSID architecture: a primary guest SSID with an email-capture splash page for hotel residents and general guests, and a separate event SSID with voucher-code authentication for conference delegates. This separation allows the marketing team to collect opted-in email addresses from hotel guests without forcing conference delegates — who may be attending a third-party event — through a data-capture flow that could create GDPR complications for the event organiser.
For the primary guest splash page, the design should feature the hotel's logo and brand colours prominently, a single email input field, a clearly labelled opt-in checkbox for marketing communications (unchecked by default), a mandatory T&Cs acceptance checkbox, and a high-contrast 'Connect' CTA button. The page should load in under 2 seconds and be fully responsive. The session timeout should be set to 24 hours, with automatic re-authentication suppressed for returning devices within a 30-day window to reduce friction for repeat guests.
For the event SSID, the hotel's IT team should pre-generate a batch of single-use or time-limited voucher codes that the events coordinator distributes to delegates. This provides controlled access without data capture obligations. The event VLAN should be firewalled from the hotel's PMS (Property Management System) and POS infrastructure in compliance with PCI DSS Requirement 1.3.
All guest traffic must traverse a dedicated guest VLAN, isolated from the hotel's operational network. The splash page must be served over HTTPS with a valid certificate. The privacy policy linked from the splash page must explicitly reference WiFi data collection, retention periods (recommend 24 months), and the right to unsubscribe from marketing communications.
A national retail chain with 180 stores wants to use its guest WiFi network to build a first-party marketing database and gain footfall analytics. The current splash page — provided by the ISP — is unbranded, asks for name, email, date of birth, and postcode, and has a connection rate of 28%. The marketing director has set a target of 65% connection rate and 500,000 new email opt-ins within 12 months. What changes should be made to the splash page, and what supporting infrastructure is required?
The immediate priority is to replace the ISP-provided portal with a branded, platform-managed solution. The form must be reduced to a single email field. Removing name, date of birth, and postcode will be the single most impactful change. These fields add friction without providing data that is immediately actionable in a retail context; email address alone is sufficient to trigger a welcome journey, attribute future purchases, and measure visit frequency.
The new splash page design should incorporate the retailer's brand identity — logo, primary brand colour, approved typeface — and include a value proposition headline such as 'Free WiFi. Connect in seconds.' The T&Cs and privacy policy links must be present and compliant. The marketing opt-in checkbox should be unchecked by default with clear copy such as 'Yes, I'd like to receive exclusive offers by email.'
To achieve the 500,000 opt-in target, the chain should also implement a progressive profiling strategy: on a user's second or third visit, the splash page can present an optional prompt to complete their profile (e.g., add a name or confirm their postcode for localised offers). This approach collects richer data without compromising the initial connection rate.
The supporting infrastructure requires a centralised guest WiFi management platform with multi-site management capabilities, a CRM integration to push captured emails and consent flags directly into the marketing automation platform, and a real-time analytics dashboard to monitor per-store connection rates and identify underperforming locations. A/B testing capability at the platform level is highly desirable to allow ongoing optimisation of CTA copy and page layout.
Projected outcome: based on comparable deployments, moving from a five-field form to a single-field form with a branded design typically increases completion rates from 28% to 65-75%. At 180 stores averaging 250 unique daily visitors, a 65% completion rate generates approximately 29,000 new email opt-ins per day, reaching the 500,000 target in approximately 17 days of operation — well within the 12-month window.
Scenario Analysis
Q1. You are the IT Manager for a 500-seat stadium that hosts 40 events per year, ranging from football matches (general public) to corporate hospitality events (premium guests). The commercial team wants to use guest WiFi to build a marketing database, while the security team insists on minimal data exposure. The stadium's existing network uses a flat guest VLAN with no segmentation. How do you design the splash page strategy and supporting network architecture to satisfy both teams?
💡 Hint:Consider whether a single splash page design can serve both use cases, and think carefully about what network segmentation changes are required before any splash page optimisation is meaningful.
Show Recommended Approach
The correct approach is a dual-SSID architecture: a public SSID for general admission guests with an email-capture splash page, and a separate corporate SSID for hospitality guests with a voucher-code or pre-shared key authentication. This satisfies the commercial team's data capture requirement for the general public cohort while giving the security team a controlled, low-data-exposure path for corporate guests. Before any splash page work begins, the flat guest VLAN must be segmented: general guest traffic, corporate guest traffic, and operational/POS traffic must each occupy separate VLANs with appropriate firewall rules between them. This is a prerequisite, not an optional enhancement. The email-capture splash page should use a single field (email), an unchecked marketing opt-in checkbox, and a clear T&Cs link. The privacy policy must reference the stadium operator as data controller and describe the marketing use of captured data. Post-event, the captured emails should be exported to the CRM platform within 24 hours to enable timely follow-up communications.
Q2. A regional library authority is deploying free public WiFi across 22 branches. The authority's legal team has flagged that collecting email addresses from library users may conflict with the authority's obligations under the Public Sector Equality Duty and data minimisation principles. The IT team is under pressure to deploy quickly. What authentication method should be used, and what are the key splash page design requirements for this public-sector context?
💡 Hint:Consider the principle of data minimisation under UK GDPR and the specific obligations of a public-sector body. Is email capture necessary to achieve the authority's objectives?
Show Recommended Approach
For a public library context, a click-through authentication — requiring only T&Cs acceptance with no data capture — is the most appropriate and legally defensible approach. The authority's primary obligation is to provide equitable access to information; data collection is not a core objective and introduces compliance risk without commensurate benefit. The splash page should be simple and accessible: the authority's branding, a brief welcome message, a T&Cs acceptance checkbox, and a 'Connect' button. The T&Cs must include an acceptable use policy that prohibits illegal activity, in compliance with the authority's obligations under the Computer Misuse Act 1990. If the authority wishes to collect usage analytics, this should be done at the network level (aggregate throughput, peak usage times) rather than at the individual user level. If email capture is later deemed necessary for a specific programme (e.g., a digital skills initiative), it must be implemented as a separate, clearly optional flow with a documented lawful basis under UK GDPR Article 6(1)(e) (public task) or Article 6(1)(a) (consent).
Q3. Your organisation's guest WiFi splash page has a completion rate of 42% against a target of 65%. Analytics show that 85% of users load the splash page, but 43% abandon before clicking 'Connect'. The page currently asks for first name, last name, email address, and date of birth, and includes a 400KB background image. The marketing team does not want to remove the date of birth field as it is used for age verification for an alcohol-related promotion. How do you diagnose and resolve the drop-off issue?
💡 Hint:Separate the performance problem from the UX problem. Address them in sequence. Consider whether the age verification requirement can be met by a different mechanism that does not require a form field.
Show Recommended Approach
The diagnosis identifies two distinct problems: a performance problem (the 400KB background image is likely causing slow load times, contributing to early abandonment) and a UX problem (four form fields is significantly above the optimal one-field design). Address the performance problem first: compress the background image to under 50KB using WebP format, or replace it with a CSS gradient that loads instantly. This alone may recover 5-10 percentage points of completion rate. For the UX problem, negotiate with the marketing team to remove first name, last name, and date of birth from the standard flow. The age verification requirement for the alcohol promotion can be met more effectively by a separate age-gate mechanism (a simple 'I confirm I am 18 or over' checkbox) rather than a date-of-birth field, which is disproportionate data collection for this purpose and creates a GDPR data minimisation issue. Implement progressive profiling to request additional data on subsequent visits if richer profiling is genuinely required. After these changes, re-measure the completion rate over a 30-day period. If it remains below 65%, conduct user testing to identify any remaining friction points in the authentication flow.
Key Takeaways
- ✓A guest WiFi splash page is a strategic business asset, not a technical formality — its design directly determines the ROI of your entire guest WiFi investment through connection rates and first-party data capture.
- ✓Apply the One-Field Rule as your default: a single email field consistently outperforms multi-field forms, often doubling completion rates from below 35% to above 70% in comparable deployments.
- ✓Legal compliance is non-negotiable and must be designed in from the start — GDPR requires unbundled, opt-in marketing consent, an accurate privacy policy, and a documented lawful basis for all data processing activities.
- ✓Network segmentation is a prerequisite, not an optional enhancement — guest traffic must be isolated from corporate and POS systems in compliance with PCI DSS Requirement 1.3 before any splash page optimisation work begins.
- ✓Page performance is as important as visual design — a splash page that takes more than three seconds to load will see measurable abandonment; target a total asset weight under 200KB and an LCP under 2.5 seconds.
- ✓Choose your authentication method based on venue type and business objective — email capture is optimal for most commercial venues, while click-through is appropriate for public-sector and high-throughput environments where data collection is not a primary objective.
- ✓Instrument your splash page with conversion analytics from day one — without baseline data on impression rate, portal view rate, and completion rate, you cannot measure the impact of optimisation changes or identify underperforming locations in a multi-site deployment.



