What is RADIUS Authentication and How Does It Work?
This guide provides a definitive technical reference on RADIUS authentication for IT leaders managing enterprise and guest WiFi deployments. It demystifies the AAA protocol, explains how 802.1X and EAP methods work together, and details how Purple's cloud-based platform simplifies deployment for hotels, retail chains, stadiums, and public-sector organisations. Readers will leave with a clear implementation roadmap, real-world case studies, and the decision frameworks needed to migrate from insecure pre-shared keys to a robust, identity-driven network access control architecture.
🎧 Listen to this Guide
View Transcript

Executive Summary
For IT leaders at multi-site venues — hotels, retail chains, stadiums, and conference centres — providing secure and reliable WiFi access to thousands of daily users is a mission-critical service that carries significant operational and regulatory risk. The legacy approach of using a single pre-shared key (PSK) for guest and staff networks is no longer a defensible security posture. It exposes organisations to compliance violations under PCI DSS and GDPR, operational disruption, and reputational damage from potential breaches.
The modern, industry-standard solution is to centralise network access control through the RADIUS (Remote Authentication Dial-In User Service) protocol. RADIUS provides a robust framework for the three pillars of network security — Authentication, Authorisation, and Accounting (AAA) — enforcing identity-based access for every user and device. By integrating with an existing identity directory such as Azure AD, Google Workspace, or Okta, RADIUS ensures that only authorised individuals can connect, and that their access is precisely scoped to their role.
This guide provides a practical, actionable overview of RADIUS, the underlying IEEE 802.1X standard, and how Purple's WiFi intelligence platform abstracts away the complexity of deployment. It is written for network architects and IT managers who need to make implementation decisions this quarter, not next year.
Technical Deep-Dive
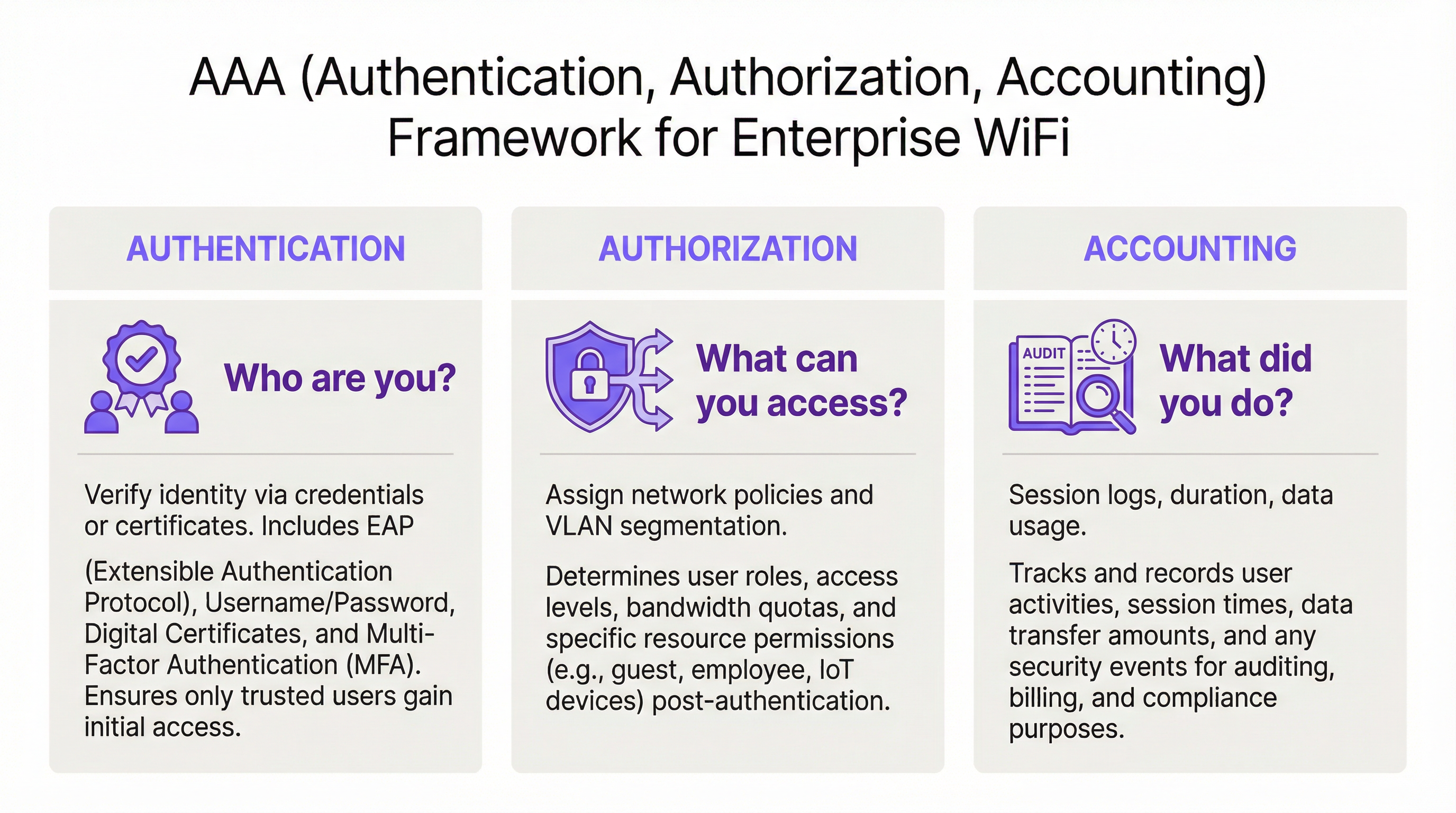
The AAA Framework: Authentication, Authorisation, and Accounting
RADIUS operates on the client-server model and is built around the AAA framework, a foundational concept in network security. Understanding each component is essential for a successful deployment.
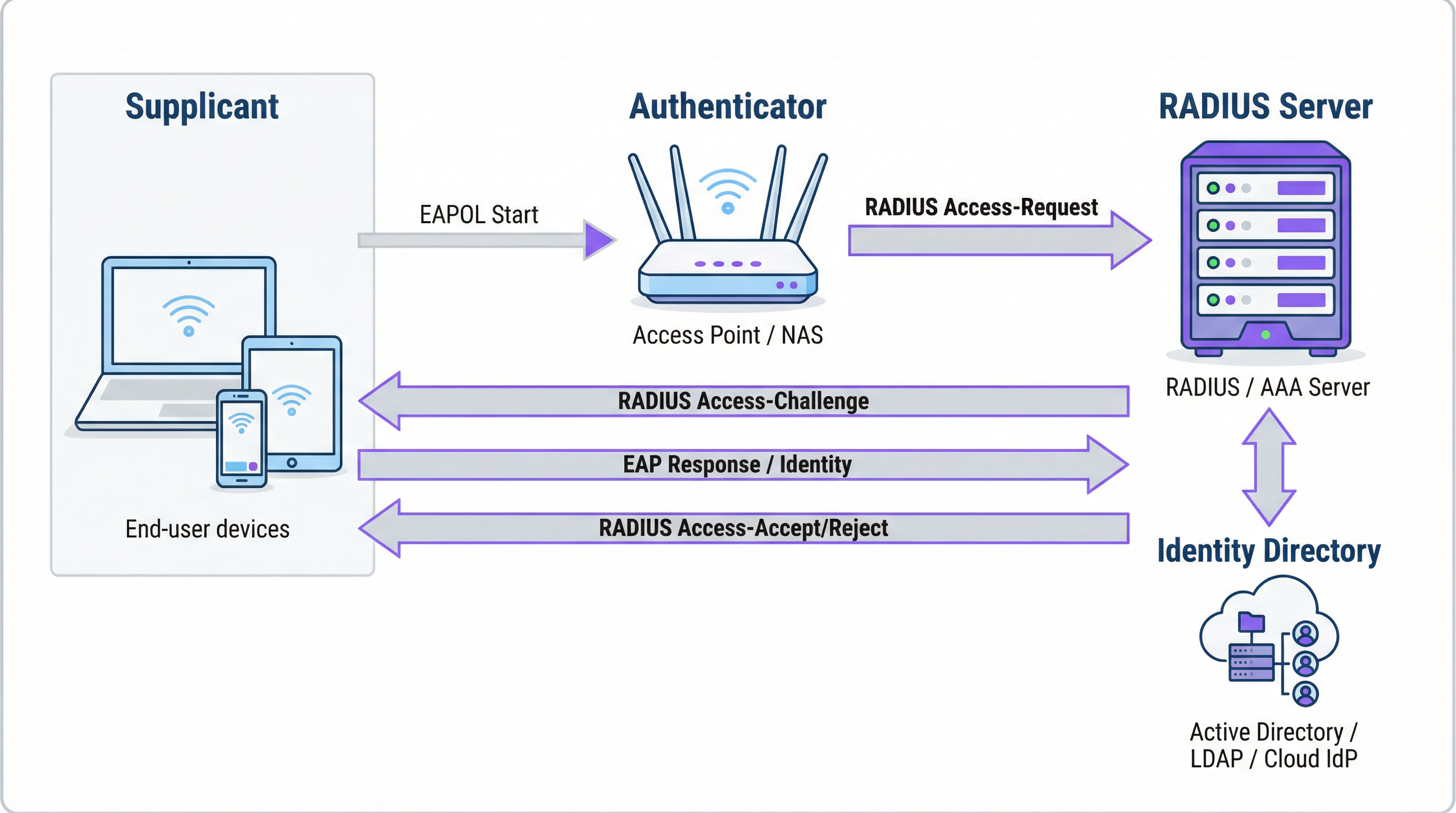
Authentication is the process of verifying a user's identity. When a user attempts to connect to a WiFi network secured with WPA2/WPA3-Enterprise, their device — the Supplicant — sends credentials to the Wireless Access Point — the Authenticator. The Authenticator does not make the access decision itself; it forwards the request to the RADIUS server. The RADIUS server validates these credentials against a configured identity source: Microsoft Active Directory, a cloud IdP such as Okta, or a local user database. Validation can use a username and password combination or, for significantly stronger security, a digital certificate via an EAP method such as EAP-TLS.
Authorisation determines what an authenticated user is permitted to do. Based on policies defined by the network administrator, the RADIUS server returns specific attributes to the Authenticator. These attributes dictate the VLAN assignment (separating guest traffic from corporate traffic), bandwidth limits, and time-of-day access restrictions. This granular, dynamic policy enforcement is one of RADIUS's core advantages over static PSK-based systems.
Accounting tracks user activity throughout the session. The RADIUS server logs connection timestamps, session duration, data transferred, and device MAC addresses. This audit trail is invaluable for troubleshooting, capacity planning, and compliance reporting. Under PCI DSS 4.0, logging and monitoring all access to network resources is a mandatory control.
How RADIUS and 802.1X Work Together
The IEEE 802.1X standard defines port-based network access control. In a WiFi context, 802.1X enables an access point to block all traffic from a device — except authentication messages — until the RADIUS server has confirmed authorisation. The communication between the Supplicant and the Authenticator uses the Extensible Authentication Protocol (EAP), carried over the LAN as EAPOL (EAP over LAN). The Authenticator then relays this to the RADIUS server using the RADIUS protocol.
The choice of EAP method is a critical security decision:
| EAP Method | Authentication Type | Security Level | Recommended Use Case |
|---|---|---|---|
| EAP-TLS | Certificate-based | Highest | Corporate managed devices — gold standard |
| PEAP-MSCHAPv2 | Credential-based | Medium | Windows-heavy environments transitioning to certificates |
| EAP-TTLS/PAP | Credential-based | Medium | Mixed-OS environments with legacy device support |
For corporate devices, EAP-TLS is the target state. It uses mutual certificate authentication — both the client and the server present certificates — completely eliminating passwords and the associated risks of credential theft and phishing.
RADIUS Ports and Transport
By default, RADIUS uses UDP port 1812 for authentication and authorisation, and UDP port 1813 for accounting. Some legacy deployments use ports 1645 and 1646. Since RFC 6613, RADIUS can also operate over TCP with TLS (RadSec), which is increasingly used in cloud deployments for enhanced transport security.
Implementation Guide
Transitioning from PSK to RADIUS: A Five-Step Roadmap
Step 1: Select Your RADIUS Infrastructure. Choose between an on-premises server (Microsoft NPS for Windows environments, FreeRADIUS for open-source deployments) or a cloud-based RADIUS service. For multi-site organisations, a cloud RADIUS platform such as Purple's is almost always the correct choice. It provides built-in high availability, geographic redundancy, and eliminates the operational burden of server management.
Step 2: Integrate Your Identity Source. Connect the RADIUS server to your organisation's authoritative identity directory. Modern cloud RADIUS platforms support direct integration with Azure AD, Google Workspace, and Okta via SAML or LDAP. For guest users, the identity source is typically a CRM, a property management system (PMS), or a purpose-built guest WiFi platform.
Step 3: Configure Network Hardware. On your wireless LAN controller or access points, create a new SSID configured for WPA2-Enterprise or WPA3-Enterprise. Point the SSID at your RADIUS server's IP address and configure the shared secret — a password that encrypts communication between the access point and the RADIUS server. This value must match exactly on both sides; a mismatch is one of the most common causes of initial deployment failures.
Step 4: Define Authorisation Policies. Create rules on the RADIUS server mapping user groups to network policies. A typical policy set for a hotel might include: Staff on VLAN 10 with full internal access; Contractors on VLAN 30 with limited access and a 50 Mbps bandwidth cap; Guests on VLAN 20 with internet-only access and an 8-hour session limit.
Step 5: Onboard Users and Devices. For corporate staff, deploy WiFi profiles with 802.1X settings via your MDM platform. For guests, deploy a Captive Portal. Purple's platform automates the guest onboarding flow — supporting social media logins, registration forms, and voucher codes — and creates temporary RADIUS user accounts that expire automatically.

Best Practices
Adopt WPA3-Enterprise. Where hardware supports it, WPA3-Enterprise provides significant security improvements over WPA2-Enterprise, including Protected Management Frames (PMF) and stronger encryption via the 192-bit security mode. Conduct a hardware audit to identify access points that require firmware updates or replacement.
Implement EAP-TLS for Corporate Devices. Certificate-based authentication eliminates the password as a vulnerability. Integrate your RADIUS server with your PKI or use a cloud-based certificate management solution. Automate certificate deployment via MDM to minimise IT overhead.
Enforce VLAN Segmentation. Dynamic VLAN assignment via RADIUS is non-negotiable for PCI DSS compliance and Zero Trust architecture. Ensure your network switches and firewalls enforce inter-VLAN routing policies that prevent guest traffic from reaching corporate resources.
Deploy Redundant RADIUS Infrastructure. Configure at least a primary and secondary RADIUS server on your access points. Cloud RADIUS platforms typically provide this automatically. Test failover regularly.
Troubleshooting and Risk Mitigation
| Failure Mode | Root Cause | Resolution |
|---|---|---|
| All users rejected | Shared secret mismatch between AP and RADIUS server | Verify shared secret on both AP and RADIUS server configuration |
| Certificate errors on client devices | RADIUS server certificate not trusted by client | Install root CA certificate on all client devices via MDM |
| Intermittent authentication failures | RADIUS server overloaded or unreachable | Implement secondary RADIUS server; review server capacity |
| Guest portal not redirecting | Walled garden misconfiguration | Ensure portal URL and social login provider domains are in the walled garden |
| Users cannot reconnect after session expiry | Accounting session not properly terminated | Review RADIUS accounting configuration; check for stale sessions |
ROI and Business Impact
The business case for RADIUS deployment is compelling across multiple dimensions. Security risk reduction is the most immediate benefit: replacing a shared PSK with identity-based access eliminates the most common vector for WiFi-based network intrusions, potentially avoiding breach costs that average £3.4 million for UK businesses. Compliance assurance under PCI DSS, GDPR, and sector-specific regulations is achieved through the combination of identity-based access control and comprehensive accounting logs. Operational efficiency gains are significant in large deployments — centralised policy management means that onboarding a new user or revoking access for a departing employee is a single action in the identity directory, not a manual reconfiguration across dozens of access points. Finally, the accounting data generated by RADIUS provides actionable intelligence for capacity planning, enabling infrastructure investment decisions to be grounded in actual usage data rather than estimates.
Key Terms & Definitions
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol, standardised in RFC 2865, that provides centralised Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service. It operates on a client-server model, where the Network Access Server (NAS) is the client and the RADIUS server is the decision-making authority.
This is the core engine of enterprise WiFi security. When an IT manager talks about 'moving to 802.1X', they are almost always talking about deploying a RADIUS server.
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It defines the encapsulation of the Extensible Authentication Protocol (EAP) over IEEE 802 networks, enabling an authenticator (e.g., a WiFi access point) to enforce authentication before granting network access.
This is the standard that makes RADIUS work for WiFi. When configuring an SSID for 'WPA2-Enterprise', you are enabling 802.1X on that SSID.
AAA (Authentication, Authorization, Accounting)
A security framework for intelligently controlling access to computer resources, enforcing policies, and auditing usage. Authentication verifies identity, Authorization determines permitted actions, and Accounting records activity.
RADIUS servers are often called 'AAA servers'. Understanding this framework is the conceptual foundation for all network access control design.
Supplicant
In the 802.1X framework, the Supplicant is the client device — a laptop, smartphone, or IoT device — that is requesting access to the network. The supplicant software on the device handles the EAP authentication exchange.
When troubleshooting authentication failures, the supplicant configuration (e.g., the WiFi profile on a laptop) is often the source of the problem.
Authenticator
In the 802.1X framework, the Authenticator is the network device — typically a wireless access point or an Ethernet switch — that enforces access control. It relays EAP messages between the Supplicant and the Authentication Server but does not make the authentication decision itself.
The access point is a relay, not a decision-maker. This is a critical distinction: the AP's job is to forward the request to RADIUS and then act on the response.
EAP (Extensible Authentication Protocol)
An authentication framework defined in RFC 3748 that supports multiple authentication methods. EAP itself does not define a specific authentication mechanism; instead, it provides a standard format for negotiating and carrying various EAP methods (e.g., EAP-TLS, PEAP, EAP-TTLS).
When configuring 802.1X, you must choose an EAP method. The choice between EAP-TLS (certificates) and PEAP (passwords) is one of the most consequential security decisions in a WiFi deployment.
EAP-TLS (EAP Transport Layer Security)
A certificate-based EAP method that provides mutual authentication between the client and the RADIUS server using X.509 digital certificates. It is widely regarded as the most secure EAP method, as it eliminates passwords entirely.
EAP-TLS is the gold standard for corporate device authentication. Deploying it requires a Public Key Infrastructure (PKI) to issue and manage client certificates, which is why cloud-based certificate management solutions are increasingly popular.
Captive Portal
A web page that intercepts a user's connection to a public WiFi network, requiring them to complete an action — such as accepting terms of service, entering credentials, or authenticating via a social media account — before internet access is granted.
Captive portals work in conjunction with RADIUS for guest WiFi. The portal is the user-facing interface; RADIUS is the back-end authentication engine that validates the user's session and enforces access policies.
VLAN (Virtual Local Area Network)
A logical network segment created within a physical network infrastructure. VLANs allow network administrators to segregate traffic from different user groups — such as guests, staff, and IoT devices — even when they share the same physical hardware.
Dynamic VLAN assignment via RADIUS is the mechanism that enables network segmentation in enterprise WiFi. It is a fundamental requirement for PCI DSS compliance and Zero Trust architecture.
Shared Secret
A password configured on both the RADIUS client (the access point) and the RADIUS server to authenticate their communication and encrypt RADIUS attribute values. It must be identical on both sides.
A shared secret mismatch is one of the most common causes of RADIUS authentication failures during initial deployment. Always copy-paste rather than manually type this value.
Case Studies
A 500-room hotel needs to provide secure WiFi for guests, conference attendees, and staff. Guests should have a frictionless onboarding experience, while staff require secure access to internal property management and point-of-sale systems. The hotel uses Oracle OPERA as its Property Management System (PMS).
Deploy Purple's cloud RADIUS platform integrated with the hotel's Oracle OPERA PMS. Provision three separate SSIDs: 'Hotel-Guest', 'Conference-WiFi', and 'Staff-Internal'. The 'Staff-Internal' SSID is configured for WPA3-Enterprise with EAP-TLS. Digital certificates are deployed to all hotel-owned devices via an MDM platform (e.g., Jamf or Microsoft Intune), enabling passwordless, seamless authentication for staff. The 'Hotel-Guest' SSID uses a branded captive portal integrated with OPERA. At check-in, OPERA automatically creates a temporary RADIUS user account with credentials valid for the duration of the guest's stay. The guest receives a QR code or a welcome email with a direct connection link. The 'Conference-WiFi' SSID uses a voucher-based system within Purple's platform, allowing event coordinators to generate unique, time-limited access codes for their attendees. All three SSIDs use dynamic VLAN assignment to enforce strict traffic segmentation.
A retail chain with 200 stores across the UK wants to replace its insecure, shared-password guest WiFi network. The marketing team requires opt-in demographic data from store visitors to support targeted campaigns. The IT team uses Azure Active Directory for all corporate identity management.
Deploy Purple's cloud RADIUS and guest WiFi platform across all 200 stores using a centralised, templated configuration. For guest access, configure a branded captive portal on a dedicated guest SSID. The portal offers authentication via social media accounts (Facebook, Google) or a simple registration form, capturing opt-in marketing consent in compliance with GDPR. Purple's platform aggregates this data into a centralised analytics dashboard, providing the marketing team with visitor demographics, dwell times, and repeat visit rates. For corporate staff, integrate the RADIUS server with the existing Azure AD tenant. Staff connect to a separate 'Staff' SSID using their Azure AD credentials via PEAP, with a phased migration plan to EAP-TLS with certificates for the highest-risk roles. All guest traffic is isolated on a dedicated VLAN with no access to the store's internal network or EPOS systems, meeting PCI DSS network segmentation requirements.
Scenario Analysis
Q1. You are the IT architect for a large conference centre. A major technology company is renting your venue for a three-day conference with 5,000 attendees. The client has a hard requirement that attendees can connect to a secure, high-performance WiFi network without manually entering a password each day. The client uses Okta as their identity provider. How would you design the authentication solution?
💡 Hint:Consider how to provide a seamless, passwordless experience for a large number of users from a single external organisation. Think about certificate-based authentication and how to integrate with a third-party identity provider for a time-limited event.
Show Recommended Approach
The optimal solution is to provision a dedicated SSID for the conference configured for WPA3-Enterprise with EAP-TLS. Integrate your cloud RADIUS platform with the client's Okta tenant via SAML federation for the duration of the event. Before the conference opens, attendees are directed to a one-time onboarding portal where they authenticate with their Okta credentials. Upon successful authentication, a unique digital certificate is generated and installed on their device. For the remainder of the conference, their device automatically and securely connects to the SSID without any further user interaction. The certificates are issued with a validity period matching the conference duration and are automatically revoked at close. This delivers a seamless, passwordless experience while maintaining strong security, and it leverages the client's existing identity infrastructure rather than creating a separate credential system.
Q2. A private hospital needs to provide WiFi for patients and visitors, but must ensure this traffic is completely isolated from the network used for clinical systems, electronic health records, and medical devices, to comply with HIPAA and NHS DSP Toolkit requirements. What RADIUS feature is most critical to achieving this isolation, and how would you configure it?
💡 Hint:Focus on the Authorization pillar of the AAA framework. The key is not just authenticating users, but controlling what they can reach after authentication. Consider how RADIUS communicates network policy to the access point.
Show Recommended Approach
The most critical feature is dynamic VLAN assignment via RADIUS authorization policies. You would create a dedicated 'Patient-Guest' VLAN (e.g., VLAN 50) on the network infrastructure, configured with firewall rules that permit only internet access and explicitly deny all traffic to the clinical network VLANs. On the RADIUS server, create an authorization policy that assigns any user authenticating to the patient WiFi SSID to VLAN 50, regardless of their credentials. The RADIUS server communicates this assignment to the access point via the Tunnel-Type, Tunnel-Medium-Type, and Tunnel-Private-Group-ID attributes in the Access-Accept message. The access point then places the user's traffic into VLAN 50 at the point of connection. This ensures that even if a patient's device is compromised, it has no network path to clinical systems — a fundamental requirement for HIPAA compliance and clinical network security.
Q3. Your organisation has deployed 802.1X with RADIUS across its corporate estate. An employee reports that they cannot connect to the corporate WiFi from their new laptop, but they can connect successfully from their smartphone and from their previous laptop. The IT helpdesk has confirmed the employee's account is active in Azure AD. What is your diagnostic approach, and what are the three most likely root causes?
💡 Hint:The issue is device-specific, not user-specific — the user can authenticate from other devices. This narrows the problem to the device configuration, the device's certificate, or the device's supplicant settings. Start with the RADIUS server logs.
Show Recommended Approach
The diagnostic approach is to first examine the RADIUS server's authentication logs for Access-Reject messages corresponding to the MAC address of the new laptop. The rejection reason code will identify the root cause. The three most likely causes are: (1) Missing or invalid client certificate — if the deployment uses EAP-TLS, the new laptop may not yet have had a certificate provisioned via MDM. Check whether the device is enrolled in the MDM platform and whether the certificate deployment policy has been applied. (2) Incorrect WiFi profile — the new laptop may have the wrong 802.1X supplicant settings, such as the wrong EAP method, an incorrect RADIUS server certificate trust configuration, or the wrong username format. Verify the WiFi profile matches the standard corporate template. (3) Device not yet registered in the identity directory — some RADIUS policies perform a device compliance check against Azure AD. If the new laptop has not yet completed Azure AD join and device registration, it may fail this check even though the user's account is active.
Key Takeaways
- ✓RADIUS is the industry-standard protocol for centralised network access control, implementing the AAA (Authentication, Authorization, Accounting) framework to manage who can access your WiFi, what they can do, and to log all activity.
- ✓It replaces insecure pre-shared keys (PSKs) with robust, identity-based authentication, ensuring every user and device has a unique, verifiable identity on the network.
- ✓IEEE 802.1X is the standard that enables RADIUS to work with WiFi access points, blocking all network traffic from a device until the RADIUS server has confirmed authorisation.
- ✓EAP-TLS (certificate-based authentication) is the gold standard for corporate devices, eliminating passwords entirely and providing the strongest protection against credential theft and phishing.
- ✓Dynamic VLAN assignment via RADIUS authorization policies is the mechanism that enforces network segmentation — a mandatory control for PCI DSS compliance and a cornerstone of Zero Trust architecture.
- ✓For guest WiFi, RADIUS works in conjunction with a captive portal: the portal handles the user-facing onboarding experience, while RADIUS manages the back-end authentication and session policy enforcement.
- ✓Cloud-based RADIUS platforms such as Purple simplify deployment, provide built-in high availability, and integrate directly with modern identity providers (Azure AD, Google Workspace, Okta), making enterprise-grade network access control accessible for organisations of all sizes.



