Firewall Rules for Guest WiFi Networks
This guide provides IT managers and network architects with an authoritative reference for configuring firewall rules for guest WiFi networks, specifically in support of a Purple deployment. It offers actionable, vendor-neutral guidance on network segmentation, port configuration, and security best practices to ensure both seamless guest access and robust protection of corporate assets.
🎧 Listen to this Guide
View Transcript

Executive Summary
For the modern enterprise, offering guest WiFi is no longer a luxury—it is a mission-critical service that drives customer engagement, provides valuable analytics, and enhances the on-site experience. However, an improperly secured guest network represents one of the most significant attack vectors into the corporate environment. This technical reference guide provides an actionable framework for IT leaders and network architects to implement robust, secure, and high-performance firewall configurations for guest WiFi networks. It focuses on the core principles of network isolation, least-privilege access, and proactive monitoring. By adhering to these vendor-neutral best practices, organisations can mitigate security risks, ensure regulatory compliance (such as PCI DSS and GDPR), and maximise the ROI of their WiFi infrastructure. This document moves beyond academic theory to offer pragmatic, step-by-step guidance and real-world examples tailored for busy technical professionals responsible for deploying and managing enterprise networks in hospitality, retail, and large public venues.
Technical Deep-Dive
The foundational principle of secure guest WiFi architecture is strict network segmentation. The guest network must be treated as an untrusted, external environment, logically separated from the trusted corporate LAN where critical business systems, servers, and employee data reside. This is most effectively achieved using Virtual LANs (VLANs), with a firewall acting as the enforcement point between them.
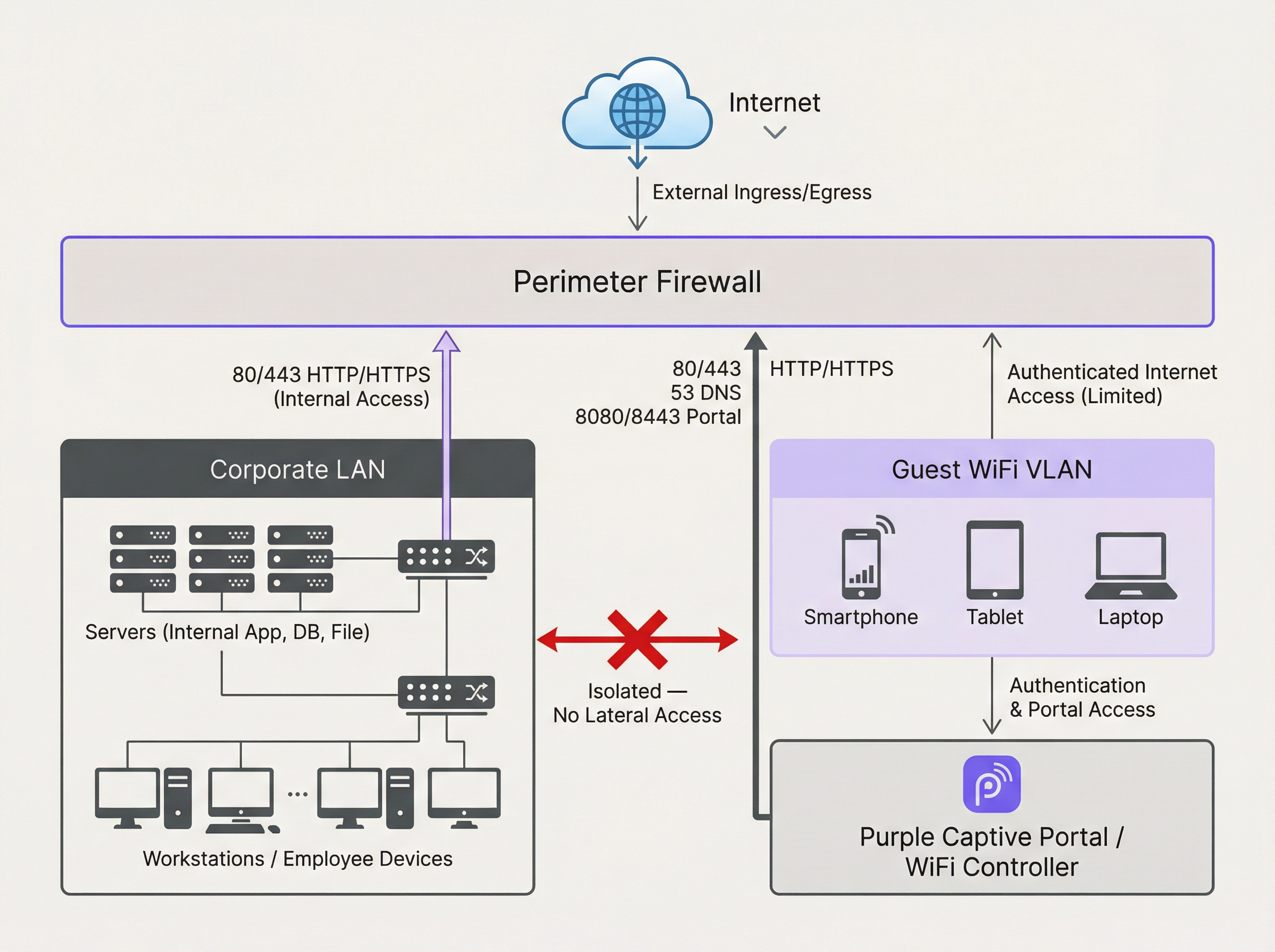
The diagram above illustrates the ideal architecture. All traffic originating from the Guest WiFi VLAN is firewalled and inspected before it can reach the internet or any other network segment. Crucially, a firewall rule must be in place to explicitly deny any traffic initiated from the Guest VLAN to the Corporate LAN. This prevents a compromised guest device from being used as a pivot point to attack internal resources.
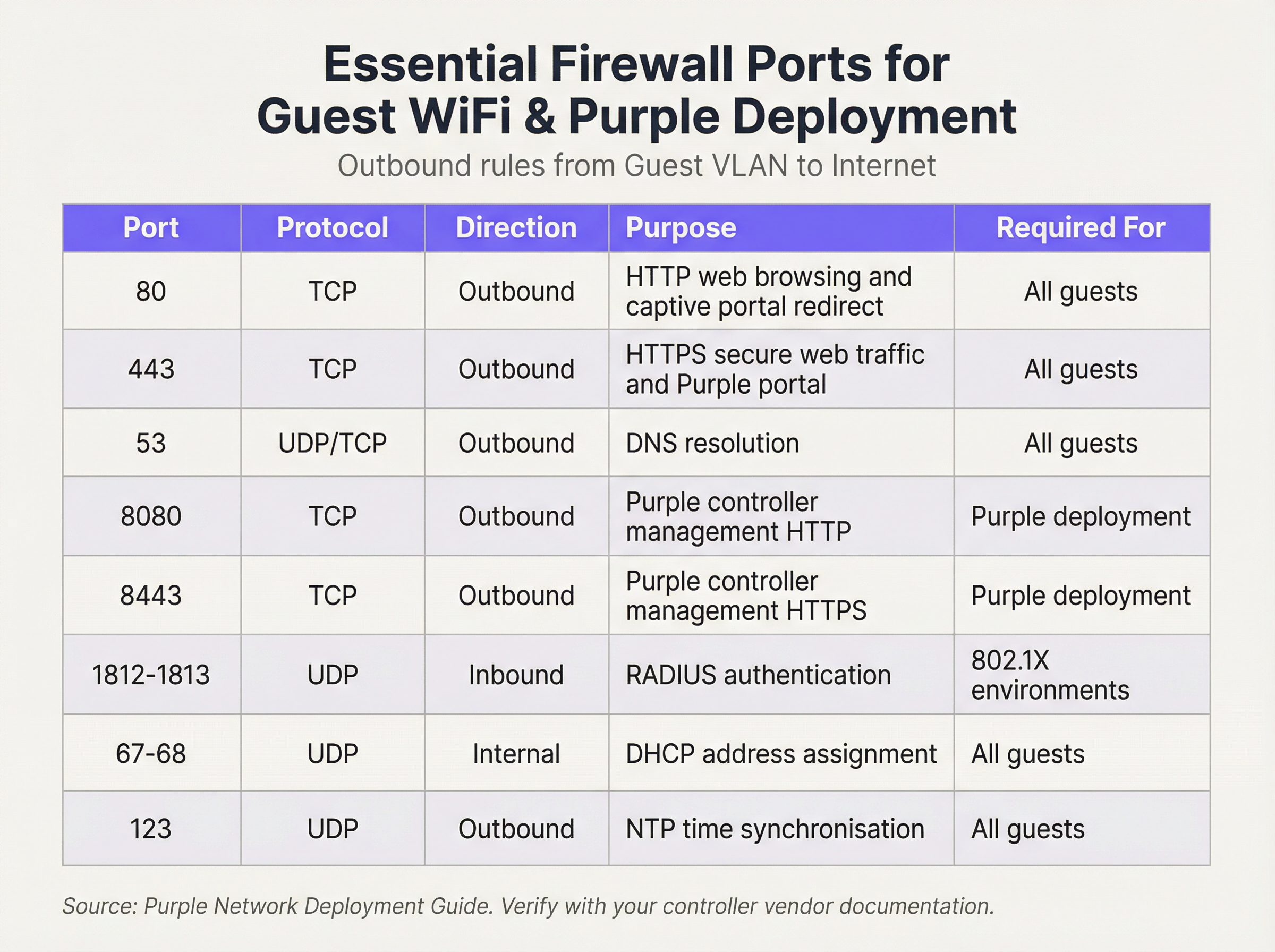
We operate on a ‘Default Deny’ security posture. This means the firewall will block all traffic unless a rule explicitly permits it. The following outbound rules form the baseline for a functional and secure guest network:
Inbound Rules & Port Forwarding:
For the Guest VLAN, the inbound policy is simple: deny all traffic initiated from the internet. There is no valid business reason for an external entity to initiate a connection to a guest’s device. The only exception is for on-premises hardware. If you host your own WiFi controller or Captive Portal server within your network (as opposed to using a cloud-hosted solution), you will need to create a specific Port Forwarding (or Destination NAT) rule. This rule maps a specific port on your public IP address to the internal IP address and port of the controller, for example, forwarding incoming traffic on TCP port 443 to 192.168.100.10:8443. This rule must be as restrictive as possible, specifying the exact source (if known), destination, and port.
Implementation Guide
- VLAN Creation: In your network switches, create a new, dedicated VLAN for guest traffic (e.g., VLAN 100). Assign this VLAN ID to the SSID that broadcasts your guest network.
- Firewall Interface Configuration: Configure a new interface or sub-interface on your firewall and assign it to the guest VLAN. This interface will serve as the default gateway for all guest devices.
- DHCP Service: Configure a DHCP server for the guest VLAN to automatically assign IP addresses. Ensure the DHCP scope provides only the IP address, subnet mask, and the firewall’s guest interface as the default gateway. The DNS servers provided should be public resolvers (e.g., 1.1.1.1, 8.8.8.8).
- Outbound Firewall Rules: Create the essential outbound firewall rules as detailed in the port reference table. Start with the most specific rules and end with a ‘Deny All’ rule. The order is critical. The firewall evaluates rules from top to bottom, and the first match determines the action.
- Client Isolation: On your wireless access points, enable the ‘Client Isolation’ (sometimes called ‘AP Isolation’ or ‘Guest Mode’) feature. This is a critical control that prevents guest devices on the same WiFi network from communicating with each other, mitigating the risk of peer-to-peer attacks.
- Logging and Monitoring: Enable detailed logging for all firewall rules, especially for denied traffic. Forward these logs to a central SIEM (Security Information and Event Management) system for correlation and alerting on anomalous activity.
Best Practices
- Use a Stateful Firewall: A stateful firewall tracks the state of active connections and automatically allows return traffic for established sessions. This simplifies rule creation, as you only need to define outbound rules for guest-initiated traffic.
- Audit Regularly: Schedule quarterly reviews of your firewall ruleset. Remove any temporary, unused, or overly permissive rules. Security is a process, not a one-time configuration.
- Address IPv6: Ensure your firewall rules apply to both IPv4 and IPv6 traffic. Many modern devices default to IPv6, and ignoring it can leave a significant security gap.
- Cite Industry Standards: Align your configuration with established security frameworks. For retail, PCI DSS Requirement 1.2.1 explicitly requires restricting traffic between trusted and untrusted networks. For handling personal data, the GDPR mandates ‘technical and organisational measures’ to protect data, for which network segmentation is a fundamental control.
Troubleshooting & Risk Mitigation
- Issue: Captive Portal Not Loading: This is almost always a DNS or firewall rule issue. Ensure the guest can resolve the portal’s hostname (check Port 53) and that traffic to the portal’s IP address and port (usually 80/443) is allowed before authentication.
- Issue: Slow Guest WiFi: Overly permissive firewall rules can allow broadcast storms or malicious traffic to consume bandwidth. Implement the principle of least privilege to restrict traffic to only what is necessary.
- Risk: Zero-Day Worm: A guest connects with a device infected with a zero-day worm that spreads automatically. Mitigation: Client Isolation is your primary defence, as it prevents the worm from spreading to other guests on the same WiFi network. Strict egress filtering can also block the command-and-control traffic the malware needs to operate.
ROI & Business Impact
A secure and well-managed guest WiFi network is a direct contributor to business success. In retail environments, it enables access to Purple’s analytics, providing insights into footfall, dwell times, and customer behaviour that directly inform marketing and operational decisions. In hospitality, a high-performance guest network is a key driver of guest satisfaction and positive reviews. By investing in a proper firewall architecture, you are not just mitigating risk; you are ensuring the reliability and performance of a critical business intelligence and customer engagement platform. A secure deployment builds trust and protects the brand, delivering a clear return on investment by preventing costly data breaches and compliance failures.

Podcast Briefing
For an audible summary of these key points, listen to our 10-minute technical briefing.
Key Terms & Definitions
VLAN (Virtual LAN)
A method of creating logically separate networks on the same physical network infrastructure. Devices on different VLANs cannot communicate without passing through a router or firewall.
IT teams use VLANs as the primary tool to enforce segmentation between the guest network and the corporate network, which is a foundational requirement for security and compliance.
Firewall Egress Filtering
The practice of filtering traffic as it leaves a network, as opposed to when it enters. It controls what outbound connections internal devices are permitted to make.
For a guest network, egress filtering is critical. By only allowing outbound traffic on specific ports (like 80 and 443), you can block malware, prevent users from running unauthorised services, and reduce your attack surface.
Client/AP Isolation
A security feature on wireless access points that prevents devices connected to the same WiFi network from communicating directly with each other.
This is a critical defence against peer-to-peer attacks on the guest network. If one guest's device is compromised, Client Isolation prevents it from attacking other guests' laptops or phones in the same venue.
Stateful Firewall
A firewall that tracks the state of network connections (e.g., TCP streams). It automatically allows return traffic for connections that were initiated from inside the network.
Using a stateful firewall simplifies administration. An IT manager only needs to write a rule allowing a guest to connect to a website on port 443; the firewall automatically handles the return traffic without needing a complex inbound rule.
Default Deny
A security posture where any traffic that is not explicitly permitted by a firewall rule is blocked.
This is a best-practice principle for all firewall configuration. It ensures that any new or un-categorised traffic is blocked by default, providing a much higher level of security than a 'default allow' policy.
PCI DSS
The Payment Card Industry Data Security Standard, a set of security standards designed to ensure that all companies that accept, process, store or transmit credit card information maintain a secure environment.
For any retail or hospitality business, proving that the guest WiFi network is robustly isolated from the network that handles payments (the Cardholder Data Environment) is a fundamental requirement for passing a PCI DSS audit.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted. It is used for authentication, payment, or accepting terms of service.
The firewall must be configured to allow unauthenticated users to access the captive portal (and its supporting services like DNS) before they have full internet access. This pre-authentication access is often managed via a walled-garden configuration.
Port Forwarding (Destination NAT)
A technique used to redirect a communication request from one address and port number combination to another while the packets are traversing a network gateway, such as a router or firewall.
If a venue hosts its own on-premise WiFi controller, IT teams must configure port forwarding to allow guest devices on the internet to reach the captive portal on the internal network. This is a critical step for enabling the guest journey.
Case Studies
A 200-room hotel is experiencing frequent guest complaints about slow WiFi and connection drops. An initial check reveals a flat network architecture where guest and hotel operational traffic (CCTV, staff PCs) share the same subnet. The firewall has a permissive 'allow any-to-any' rule for all internal traffic.
- Immediate Action: Create a new Guest VLAN (e.g., VLAN 200) and a corresponding guest SSID. 2. Segmentation: Migrate all guest-facing access points to the new VLAN. 3. Firewall Policy: Create a new zone and interface for the Guest VLAN on the firewall. Implement a strict outbound policy allowing only ports 53, 80, 443, and 123. Add a rule to explicitly deny any traffic from the Guest VLAN to the corporate VLAN. 4. Enable Client Isolation: Activate AP/Client Isolation on the wireless controller for the guest SSID. 5. Remove Permissive Rule: Once guest traffic is successfully segmented, remove the legacy 'allow any-to-any' rule and replace it with specific rules for required corporate traffic.
A retail chain is opening a new flagship store and needs to provide guest WiFi that is compliant with PCI DSS 4.0. The store will have point-of-sale (POS) terminals, inventory scanners, and corporate PCs on the same physical network infrastructure.
- Define CDE: The first step is to define the Cardholder Data Environment (CDE). Create a dedicated VLAN for all POS terminals. 2. Isolate Guest Network: Create a separate VLAN for guest WiFi. 3. Isolate Corporate Services: Create a third VLAN for other corporate services like inventory scanners and staff PCs. 4. Firewall Enforcement: The firewall must enforce strict segmentation. There must be an explicit 'deny all' rule for any traffic originating from the Guest VLAN or the Corporate Services VLAN to the CDE VLAN. 5. Restrict CDE Egress: The CDE VLAN should only be allowed outbound access to the specific IP addresses of the payment processor, and nothing else. 6. Prove Isolation: Use tools like
nmapor a vulnerability scanner to run tests from the guest network to prove that no CDE hosts or ports are reachable.
Scenario Analysis
Q1. A stadium is hosting a major sporting event and expects 50,000 concurrent users on its guest WiFi. What is the most critical firewall consideration to ensure network stability and security?
💡 Hint:Consider the impact of broadcast and multicast traffic in such a high-density environment.
Show Recommended Approach
The most critical consideration is the aggressive filtering of all unnecessary traffic, particularly broadcast and multicast traffic (like mDNS), at the firewall and access point level. In a high-density environment, this traffic can quickly lead to a broadcast storm, consuming all available bandwidth and bringing the network to a halt. Strict egress rules allowing only essential web and DNS traffic, combined with Client Isolation, are paramount.
Q2. You discover that a previous administrator has configured the guest network to use the internal corporate DNS servers. What are the risks, and what is the immediate remediation?
💡 Hint:What information can be gleaned from internal DNS records?
Show Recommended Approach
The risks are significant. It exposes the names and IP addresses of all internal corporate servers (e.g., payroll.internal.corp, dc01.internal.corp) to anyone on the guest network, providing a detailed map for an attacker. It also creates a potential vector for DNS cache poisoning attacks against the corporate network. The immediate remediation is to change the DHCP configuration for the guest VLAN to assign public DNS servers only (e.g., 1.1.1.1, 8.8.8.8) and ensure the firewall blocks the guest VLAN from sending any traffic to the internal DNS servers.
Q3. A user reports they cannot access their corporate VPN over the guest WiFi. Your firewall logs show denied UDP traffic on port 500 and 4500 from the user's IP. What is the issue and how would you decide whether to resolve it?
💡 Hint:What protocol uses UDP ports 500 and 4500?
Show Recommended Approach
The issue is that the firewall is blocking the IKE and IPsec NAT-T protocols, which are commonly used to establish IPsec VPN tunnels. The decision to resolve this is a policy-level one. For a venue catering to business travellers (like a hotel or conference centre), allowing VPN access is often a business requirement. The resolution would be to create a specific outbound firewall rule to allow UDP traffic on ports 500 and 4500. For a public library or school, the policy might be to block VPNs to ensure traffic can be filtered. The decision must balance user needs against the organisation's security policy and risk tolerance.
Key Takeaways
- ✓Always isolate guest WiFi traffic on its own dedicated VLAN.
- ✓Operate on a 'Default Deny' firewall policy; only allow what is essential.
- ✓Enable Client Isolation on access points to prevent peer-to-peer attacks.
- ✓Use public DNS servers for guests; never expose internal DNS.
- ✓Strictly limit inbound traffic and only use port forwarding for specific, on-premise services.
- ✓Regularly audit firewall rules and monitor logs for anomalies.
- ✓A secure guest network is a prerequisite for compliance (PCI DSS, GDPR) and leveraging WiFi analytics.



