Guest WiFi Captive Portals: The Ultimate Guide to Creating a Seamless and Secure User Experience
This guide provides IT leaders and venue operators with a comprehensive technical reference for designing, implementing, and securing guest WiFi captive portals at enterprise scale. It covers the full authentication architecture from RADIUS to CRM integration, GDPR compliance requirements, advanced customisation options including A/B testing and personalised content delivery for Purple AI users, and a proven ROI framework with real-world case studies from hospitality and retail environments.
🎧 Listen to this Guide
View Transcript

Executive Summary
For IT managers, network architects, and venue operators, the guest WiFi network has evolved from a simple amenity to a critical business asset. A well-executed guest wifi captive portal is the gateway to this asset — the first point of interaction with customers and visitors, and a powerful engine for data collection, brand engagement, and revenue generation. This guide provides a comprehensive technical reference for designing, implementing, and securing captive portals to create a seamless user experience while unlocking significant business value.
We explore the core components of captive portal architecture, from initial user association to backend authentication and CRM integration. Key topics include compliance with data privacy regulations such as GDPR and the UK GDPR, implementation of robust security measures aligned with WPA3 and IEEE 802.1X, advanced customisation options including A/B testing and personalised content delivery, and strategies for maximising return on investment. For senior IT professionals, this guide offers actionable, vendor-neutral recommendations to inform procurement decisions and deployment strategies this quarter. By focusing on a frictionless user journey, robust security posture, and data-driven personalisation, organisations can transform their guest WiFi from a cost centre into a powerful tool for customer engagement and business intelligence.
Technical Deep-Dive
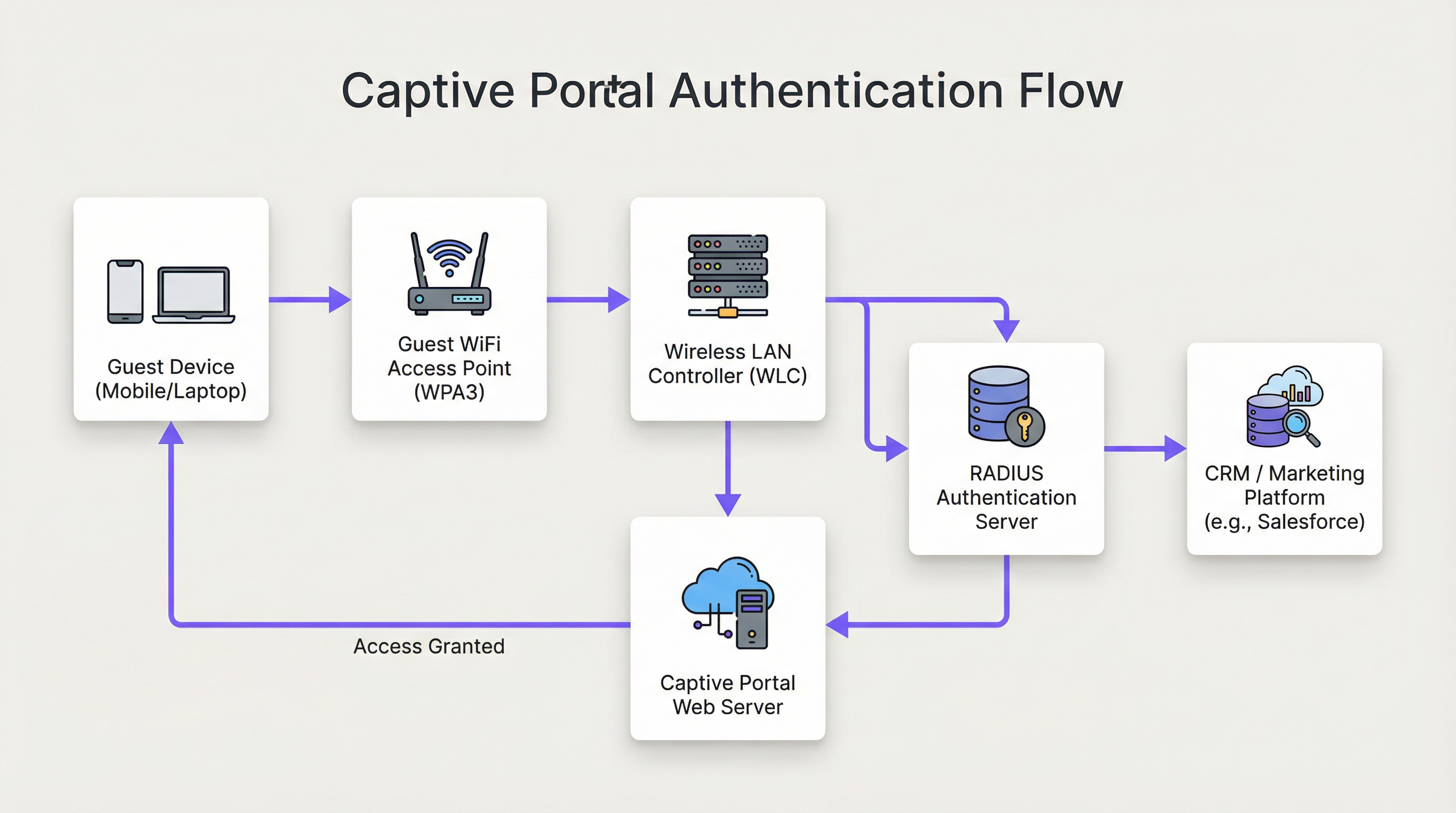
The architecture of a modern guest wifi captive portal solution involves a sophisticated interplay between network hardware, software, and cloud services. At its core, the captive portal intercepts a user's web traffic and redirects them to a specific web page for authentication before granting broader network access. Understanding this flow in detail is essential for any network architect responsible for deploying or maintaining such a system.
Stage 1 — Wireless Association: The user's device discovers and connects to the guest WiFi SSID. At this stage, the device is in a pre-authenticated, walled-garden state. The WLC or AP assigns the device an IP address via DHCP but restricts all outbound traffic except to a defined list of whitelisted domains and the captive portal host itself.
Stage 2 — HTTP/S Redirect: When the user opens a browser or any application that makes an HTTP/S request, the WLC intercepts it. Using either DNS hijacking (where all DNS queries are answered with the portal's IP) or HTTP 302 redirection, the user is forwarded to the captive portal's web server. For modern deployments, HTTP redirection is preferred for reliability across iOS, Android, and Windows clients.
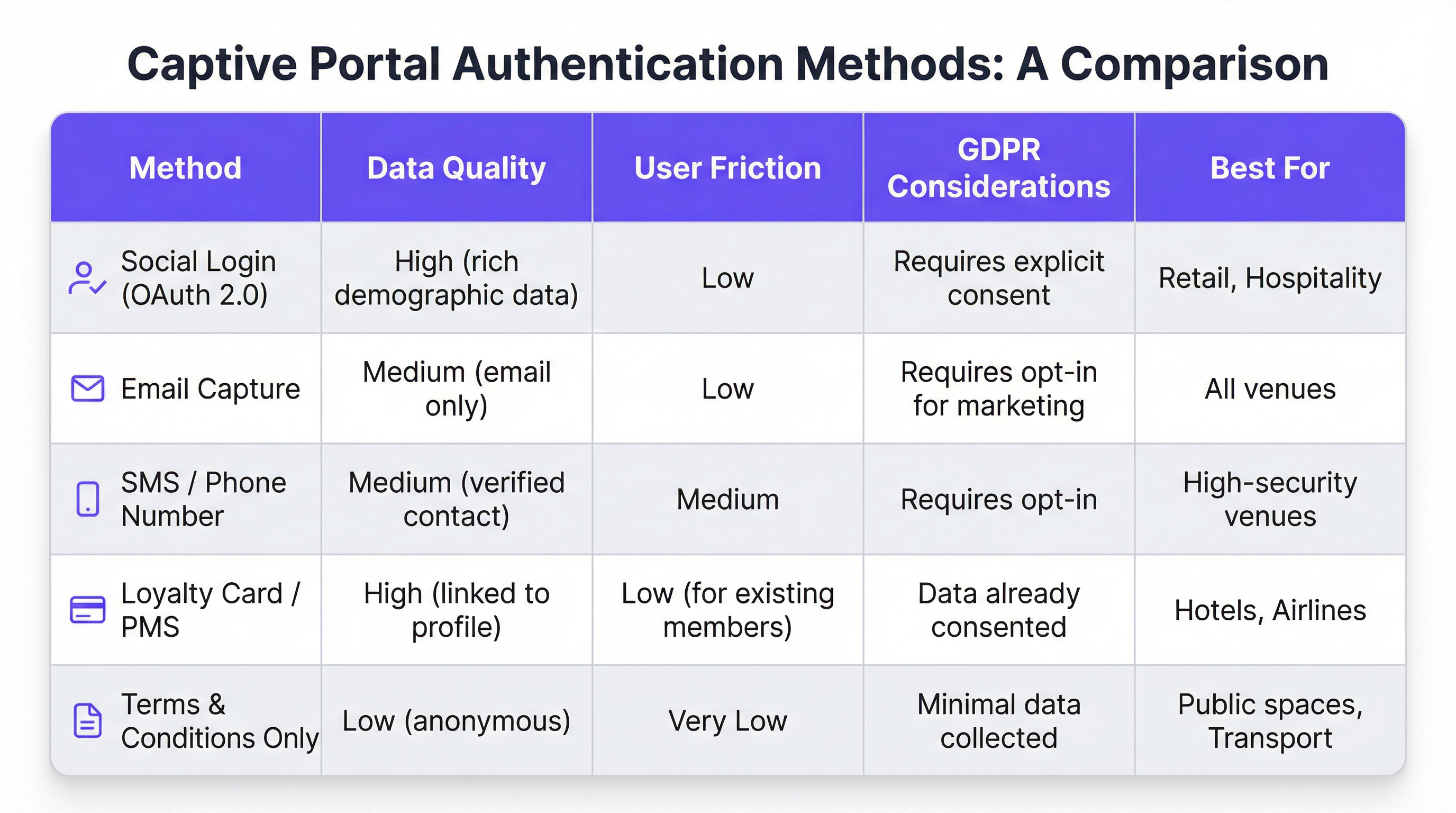
Stage 3 — Portal Interaction and Authentication: The user is presented with the captive portal page. Authentication methods include social login via OAuth 2.0 (Facebook, Google, LinkedIn), email or SMS capture, terms-and-conditions acceptance, or integration with a loyalty programme or Property Management System (PMS) via REST API. The choice of method directly governs the quality of data captured and the friction introduced into the user journey.
Stage 4 — RADIUS Authentication: Upon form submission, the portal service communicates with a RADIUS server (RFC 2865). The RADIUS server validates credentials against a backend data store — a local database, LDAP directory, CRM, or marketing automation platform. RADIUS attributes such as Session-Timeout and Idle-Timeout are used to enforce session policies.
Stage 5 — Access Granted: On successful authentication, the RADIUS server signals the WLC to change the user's authorisation state, granting full internet access. Bandwidth policies, content filtering rules, and session duration limits are enforced at this point via the WLC's policy engine.
From a security standpoint, WPA3-Enterprise with IEEE 802.1X provides the highest level of protection, encrypting traffic between the client and AP using 192-bit security in WPA3-Enterprise mode. For the portal itself, all communication must use HTTPS with TLS 1.2 or higher. Compliance with PCI DSS v4.0 is mandatory where any payment processing occurs within the portal flow.
For Purple AI users, advanced customisation capabilities extend this architecture significantly. The Purple platform supports A/B testing of portal designs at the venue level, enabling operators to test different layouts, calls-to-action, and authentication flows to optimise conversion rates. Personalised content delivery post-login — such as targeted offers based on a guest's CRM profile or loyalty tier — is achieved via real-time API calls to Salesforce, HubSpot, or any marketing automation platform with a REST API. Purple's analytics engine also provides heatmap overlays and dwell-time analysis, enabling venue operators to correlate WiFi engagement data with physical footfall patterns.
Implementation Guide
Deploying a guest wifi captive portal at enterprise scale requires a structured, phased approach. The following framework is vendor-neutral and applicable across hospitality, retail, events, and public-sector environments.
Phase 1 — Define Business Objectives: Before any technical work begins, document the specific goals of the guest WiFi service. Common objectives include building a first-party marketing database, driving footfall to specific areas of a venue, increasing ancillary revenue through targeted promotions, or simply providing a reliable amenity. These objectives will determine every subsequent design decision, from authentication method to post-login content strategy.
Phase 2 — Network Infrastructure Assessment: Conduct a full audit of your existing wireless infrastructure. Verify that your APs and WLC support captive portal redirection, VLAN tagging, and external RADIUS integration. For high-density environments — stadiums, conference centres, transport hubs — commission a professional RF site survey to ensure adequate coverage and capacity. A poorly performing network will undermine even the most beautifully designed portal.
Phase 3 — Platform Selection: Evaluate captive portal platforms against your business objectives. Key criteria include hardware agnosticism (critical for multi-vendor estates), depth of CRM and marketing automation integrations, quality of analytics and reporting, GDPR compliance tooling, and the ability to customise the portal design without developer resource. For organisations with complex integration requirements, evaluate the platform's API documentation and webhook support.
Phase 4 — User Journey Design: Map the complete user experience from WiFi discovery to post-login engagement. Aim for a maximum of three interactions before the user gains internet access. A/B test different portal designs to identify the layout and authentication flow that maximises completion rates. Ensure the portal is fully responsive and optimised for mobile-first consumption.
Phase 5 — Configuration and Integration: Configure the WLC to redirect unauthenticated users to the portal URL. Define the walled garden to permit access to the portal host, social login domains (accounts.google.com, www.facebook.com, www.linkedin.com), and any CDN resources required to render the portal. Configure RADIUS shared secrets and test the full authentication flow end-to-end before going live.
Phase 6 — Pilot and Rollout: Deploy to a single pilot location and monitor authentication rates, session durations, and error logs for a minimum of two weeks before a full rollout. Establish baseline KPIs against which you will measure the success of the deployment.
Best Practices
Prioritise the User Experience: A slow, confusing, or unreliable captive portal reflects poorly on your brand. Target a sub-15-second end-to-end authentication time. Keep the portal design clean, the instructions unambiguous, and the call-to-action prominent. Every additional click or form field you add will reduce your completion rate.
Enforce Mobile-First Design: Over 75% of guest WiFi connections originate from mobile devices. Your portal must be fully responsive, with touch-friendly UI elements and text that is legible without zooming. Test on both iOS and Android across multiple screen sizes before deployment.
Be Transparent About Data Collection: Present a clear, plain-language explanation of what data you are collecting and how it will be used. Provide a link to your privacy policy and ensure your consent mechanism is compliant with GDPR Article 7. Pre-ticked consent boxes are not valid under GDPR.
Segment Your Network Rigorously: Use VLANs to isolate guest traffic from your corporate network. This is a fundamental security control. Implement firewall rules to prevent guest devices from accessing RFC 1918 address space on your corporate network. Enable client isolation on your APs to prevent guest devices from communicating with each other.
Maintain and Monitor: Captive portal deployments are not set-and-forget. Establish a regular cadence for reviewing authentication logs, updating firmware on APs and WLCs, and auditing your walled garden configuration. Set up alerting for authentication failure rate spikes, which are often the first indicator of a misconfiguration or security incident.
Troubleshooting & Risk Mitigation
The most common failure mode in guest wifi captive portal deployments is the portal failing to load. This is almost always caused by one of three issues: DNS resolution failure (the client cannot resolve the portal hostname), an overly restrictive walled garden (the portal's CDN resources are blocked), or a firewall rule preventing access to the portal's web server on port 443. Systematic diagnosis using a packet capture on the WLC's uplink interface will quickly identify the root cause.
Authentication failures are the second most common issue. These typically stem from incorrect RADIUS shared secrets, clock skew between the WLC and RADIUS server (which causes EAP authentication failures), or issues with the backend data store. Enabling detailed RADIUS logging and correlating timestamps across the WLC, RADIUS server, and portal application logs is the most efficient diagnostic approach.
From a security risk perspective, the most significant threat vector for a guest WiFi network is an unencrypted or weakly encrypted SSID. An open SSID with no encryption exposes all user traffic to passive interception. Always enforce WPA2 or WPA3 encryption. Regularly scan your airspace for rogue access points broadcasting your SSID — a common attack vector known as an "evil twin" attack. Implement wireless intrusion detection and prevention (WIDS/WIPS) capabilities on your WLC or as a standalone overlay system.
ROI & Business Impact
The business case for a sophisticated guest wifi captive portal extends far beyond providing a basic internet connection. The following table summarises the key ROI drivers across different venue types:
| Venue Type | Primary ROI Driver | Typical KPI | Example Outcome |
|---|---|---|---|
| Hotel | Ancillary revenue uplift | Spa/F&B bookings from WiFi users | +42% spa bookings (200-room hotel case study) |
| Retail | Marketing database growth | New opted-in contacts per month | 8,000+ contacts in 6 months (500-store retail case study) |
| Stadium / Events | Sponsor activation | Branded portal impressions | 95%+ portal completion rate at major events |
| Conference Centre | Delegate engagement | Session check-in rate via WiFi | Real-time attendance data for event organisers |
| Public Sector | Citizen engagement | Survey completion rate | Targeted public announcements to verified residents |
The ROI calculation for a guest WiFi investment should account for both direct revenue impact (ancillary sales, marketing campaign revenue) and indirect benefits (improved customer satisfaction scores, reduced churn, richer first-party data). For a hotel with 200 rooms and an average occupancy of 70%, a 42% uplift in spa bookings attributable to WiFi-driven promotions can represent lakhs of rupees in incremental annual revenue — a return that typically justifies the platform investment within the first year of deployment.
Key Terms & Definitions
Captive Portal
A web page that a network operator presents to a newly connected user before granting broader access to the internet. The portal intercepts all HTTP/S traffic from the unauthenticated device and redirects it to a designated URL.
This is the primary mechanism for authenticating, communicating with, and collecting data from users on a guest WiFi network. IT teams configure this at the WLC or AP level to control access and gather marketing consent.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol (RFC 2865) that provides centralised Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service. It operates over UDP and uses a shared secret for security.
RADIUS is the backend authentication engine for most enterprise captive portal deployments. When a user submits their login credentials, the portal sends an Access-Request to the RADIUS server, which responds with an Access-Accept or Access-Reject. IT teams must configure the correct RADIUS shared secret on both the WLC and the portal platform.
Walled Garden
A restricted network environment in which a pre-authenticated user can only access a defined list of approved domains and IP addresses, typically limited to the captive portal itself and any resources required to render it.
Before a user completes the captive portal login, they are in a walled garden. Network architects must carefully define the walled garden whitelist to include all resources required for the portal to function (including social login provider domains) while blocking all other internet access.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism for devices wishing to attach to a LAN or WLAN. It requires a supplicant (client device), an authenticator (AP or switch), and an authentication server (RADIUS).
802.1X is the foundation of enterprise-grade wireless security. When combined with WPA3-Enterprise, it provides per-user, per-session encryption keys and strong mutual authentication. Network architects should specify 802.1X for any deployment where security is a primary concern.
WPA3 (Wi-Fi Protected Access 3)
The third generation of the WPA security certification programme for wireless networks, introduced by the Wi-Fi Alliance in 2018. WPA3-Personal uses Simultaneous Authentication of Equals (SAE) to replace the vulnerable PSK handshake, while WPA3-Enterprise offers 192-bit security mode.
WPA3 should be the default security protocol for any new guest WiFi deployment. It provides significant security improvements over WPA2, including protection against offline dictionary attacks and forward secrecy. IT teams should verify WPA3 client support before mandating it as the sole security mode.
GDPR (General Data Protection Regulation)
A regulation in EU law (Regulation 2016/679) on data protection and privacy, applicable to all organisations processing personal data of individuals in the EU/EEA. The UK GDPR is a retained version of the regulation applicable in the United Kingdom post-Brexit.
GDPR compliance is a legal obligation for any organisation collecting personal data via a guest WiFi captive portal. Key requirements include a lawful basis for processing (typically consent), transparent privacy notices, the right to erasure, and data minimisation. Non-compliance can result in fines of up to €20 million or 4% of global annual turnover, whichever is higher.
OAuth 2.0
An open standard for access delegation (RFC 6749) that allows users to grant third-party applications limited access to their accounts on other services without exposing their passwords. It is the protocol underpinning social login functionality.
OAuth 2.0 is the technology that powers 'Log in with Google/Facebook/LinkedIn' on captive portals. It provides a secure, user-friendly authentication flow and, with the user's consent, allows the portal to retrieve profile data (name, email, age range, gender) from the social platform. IT teams must register the portal as an OAuth application with each social provider and configure the correct redirect URIs.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards (currently v4.0) designed to ensure that all companies that accept, process, store, or transmit credit card information maintain a secure environment. Compliance is mandated by the major card schemes.
PCI DSS compliance is mandatory for any captive portal that processes payments for premium WiFi access or any other service. Key requirements include network segmentation, encryption of cardholder data in transit and at rest, and regular penetration testing. IT teams should engage a Qualified Security Assessor (QSA) to validate compliance.
VLAN (Virtual Local Area Network)
A logical segmentation of a physical network into multiple isolated broadcast domains, configured at the switch or WLC level. Traffic on one VLAN cannot communicate with traffic on another VLAN without passing through a router or firewall.
VLAN segmentation is the primary mechanism for isolating guest WiFi traffic from the corporate network. IT teams should assign guest WiFi traffic to a dedicated VLAN and enforce strict firewall rules at the inter-VLAN routing point to prevent guest devices from accessing internal resources.
Case Studies
A 200-room luxury hotel wants to replace its outdated voucher-based guest WiFi system with a modern captive portal. The goals are to provide a seamless login experience for guests, promote hotel amenities, and integrate with their existing CRM (Salesforce) to track guest preferences. The hotel has a mixed-vendor wireless estate comprising both Cisco WLCs and Meraki cloud-managed APs.
The recommended approach is to deploy a cloud-based, hardware-agnostic captive portal platform such as Purple, which offers native support for both Cisco and Meraki hardware and a pre-built Salesforce integration. The implementation proceeds as follows: (1) Create a dedicated guest SSID on both the Cisco WLC and Meraki dashboard, tagged to a guest VLAN (e.g., VLAN 100) that is isolated from the corporate network. (2) Configure both controllers to redirect unauthenticated HTTP/S traffic to the Purple-hosted captive portal URL. Define the walled garden to permit access to the portal host, Salesforce domains, and social login providers. (3) Design a branded portal with two authentication paths: social login (LinkedIn, Facebook) for transient guests, and room number plus surname authentication for registered guests, validated in real-time against the hotel's PMS via a REST API call. (4) Configure the post-login redirect to a personalised welcome page that queries Salesforce for the guest's loyalty tier and surfaces relevant offers for the hotel's spa and restaurant. (5) Configure Purple's Salesforce connector to push all login events, demographic data, and session metadata to Salesforce in real-time, enriching the guest's contact record. (6) Enable Purple's analytics dashboard to track daily active users, authentication method split, and dwell time by venue zone. Establish a baseline and review monthly.
A national retail chain with 500 stores wants to implement guest WiFi to track in-store footfall, build a first-party marketing database, and send personalised promotional offers to customers. The IT team is concerned about the cost and disruption of replacing the diverse range of wireless hardware across the estate, which includes equipment from at least four different vendors.
The critical success factor for this deployment is hardware agnosticism. Select a cloud-based captive portal platform that supports all four vendors via standard RADIUS and HTTP redirection protocols, avoiding any hardware replacement. The implementation proceeds as follows: (1) Conduct a hardware audit across all 500 stores to document AP and controller models, firmware versions, and current SSID configurations. Identify any hardware that cannot support external RADIUS or HTTP redirection and plan for targeted upgrades at those locations only. (2) Deploy the captive portal platform in a phased rollout, starting with a 20-store pilot in a single region. Configure each store's hardware to redirect guest traffic to the centralised portal. (3) Design a single, mobile-optimised portal page with email capture as the primary authentication method, supplemented by social login. Ensure the consent mechanism is GDPR-compliant with a clear opt-in for marketing communications. (4) Configure the platform's marketing automation connector to push new contacts to the chain's email marketing platform (e.g., Klaviyo or Salesforce Marketing Cloud) in real-time. (5) Implement Purple's footfall analytics to track dwell time and repeat visit frequency by store. Use this data to identify high-performing stores and replicate their layout and offer strategies. (6) After a 4-week pilot, review KPIs (authentication rate, opt-in rate, email open rate) and iterate on the portal design before rolling out to the remaining 480 stores.
Scenario Analysis
Q1. A 500-store national retail chain wants to implement guest WiFi across its entire estate to build a first-party marketing database. The IT director has confirmed that the chain uses wireless hardware from four different vendors and has no budget for hardware replacement. The marketing director wants to send personalised promotional emails to customers within 24 hours of their in-store WiFi session. What is the most critical platform selection criterion, and what integration architecture would you recommend?
💡 Hint:Consider the hardware diversity challenge and the real-time data pipeline requirement between the captive portal and the email marketing platform.
Show Recommended Approach
The most critical platform selection criterion is hardware agnosticism — the platform must support all four wireless vendors via standard RADIUS and HTTP redirection protocols without requiring proprietary hardware or firmware modifications. For the integration architecture, configure the platform to push login events and contact data to the email marketing platform via a real-time webhook or API connector. This ensures that new contacts are available for campaign targeting within minutes of authentication, well within the 24-hour window. Ensure the consent mechanism on the portal captures explicit opt-in for marketing emails (GDPR Article 7), and configure the email platform to suppress contacts who have not opted in. Implement a data deduplication process to handle users who log in at multiple stores.
Q2. A conference centre is hosting a high-profile international event for 5,000 attendees over three days. The event organiser wants to provide a fast, seamless WiFi experience with a branded captive portal, but the centre's IT team is concerned about: (a) the security implications of 5,000 unknown devices on the network, (b) the performance of the captive portal under peak load, and (c) GDPR compliance given the international audience. What are your recommendations for each concern?
💡 Hint:Address each concern separately: security (segmentation and encryption), performance (load testing and CDN), and GDPR (consent mechanism and data residency).
Show Recommended Approach
(a) Security: Implement WPA3-Personal or WPA3-Enterprise on the event SSID. Create a dedicated VLAN for event traffic, completely isolated from the centre's corporate network. Enable client isolation on all APs to prevent device-to-device communication. Deploy a content filtering policy to block known malicious domains. Enable WIDS/WIPS to detect rogue APs. (b) Performance: Load test the captive portal platform to verify it can handle 5,000 concurrent authentication requests. Use a cloud-based portal platform with auto-scaling capabilities. Ensure the portal page is served from a CDN to minimise latency for international attendees. Pre-stage the RADIUS server with event attendee credentials if using pre-registration, to reduce authentication latency. (c) GDPR: Ensure the consent mechanism is available in all relevant languages. Use a cloud-based portal platform with data residency options to ensure EU citizen data is processed and stored within the EU/EEA. Implement a data retention policy that deletes personal data within the timeframe specified in your privacy notice. Appoint a Data Protection Officer if not already in place.
Q3. Following a routine security audit, your organisation's penetration testers have identified that the guest WiFi captive portal at your flagship venue is being served over HTTP rather than HTTPS, and that the guest VLAN has a misconfigured firewall rule that permits access to a subnet containing file servers. Describe the specific risks these two findings present and the remediation steps you would take.
💡 Hint:Consider the attack vectors enabled by each misconfiguration: man-in-the-middle for the HTTP finding, and lateral movement for the VLAN finding.
Show Recommended Approach
Finding 1 (HTTP portal): The risk is a man-in-the-middle (MitM) attack. An attacker on the same network segment can intercept the unencrypted HTTP traffic between the user's device and the portal server, capturing login credentials, session tokens, and any personal data submitted via the portal form. Remediation: Immediately provision a TLS certificate for the portal domain (a free Let's Encrypt certificate is acceptable for most deployments) and configure the portal web server to enforce HTTPS and redirect all HTTP requests to HTTPS. Update the WLC redirect URL to use HTTPS. Verify the certificate chain is valid and that HSTS is configured. Finding 2 (VLAN misconfiguration): The risk is lateral movement. A guest device that has authenticated to the WiFi network could access the file server subnet, potentially exfiltrating sensitive data or deploying malware. Remediation: Immediately review and correct the firewall ACL at the inter-VLAN routing point to deny all traffic from the guest VLAN to the file server subnet. Implement a default-deny policy on the guest VLAN firewall rule set, with explicit permit rules only for internet-bound traffic. Review all inter-VLAN rules as part of a broader firewall audit.
Key Takeaways
- ✓A guest WiFi captive portal is a strategic business asset — not a utility. It is the primary mechanism for customer data collection, brand engagement, and revenue generation from your wireless network.
- ✓The authentication method you choose (social login, email capture, PMS integration, T&C only) directly determines the quality of data you collect and the friction you introduce. Match the method to your business objectives.
- ✓Security is non-negotiable: enforce WPA3 encryption, segment guest traffic onto a dedicated VLAN, serve the portal over HTTPS, and comply with PCI DSS if processing payments.
- ✓GDPR compliance requires a valid lawful basis for processing (typically explicit consent), a transparent privacy notice, and a documented data retention and deletion policy. Fines of up to 4% of global turnover apply for non-compliance.
- ✓Hardware agnosticism is the most critical platform selection criterion for multi-site, multi-vendor deployments. A cloud-based platform avoids costly hardware replacement programmes.
- ✓The 15-Second Rule: if end-to-end authentication takes longer than 15 seconds, completion rates will drop significantly. Benchmark and optimise your RADIUS response times and portal page load speed.
- ✓Measure ROI using concrete business metrics: marketing database growth, ancillary revenue uplift, customer dwell time, and repeat visit frequency. These metrics justify the investment and guide ongoing optimisation.



