WiFi Data Capture: A Comprehensive Guide to Privacy, Compliance, and Best Practices
This guide provides IT leaders with a comprehensive technical reference for implementing WiFi data capture solutions. It focuses on navigating the complex landscape of privacy, legal compliance (GDPR, CCPA), and data ethics, offering actionable best practices for venue operators in hospitality, retail, and large public spaces.
🎧 Listen to this Guide
View Transcript

Executive Summary
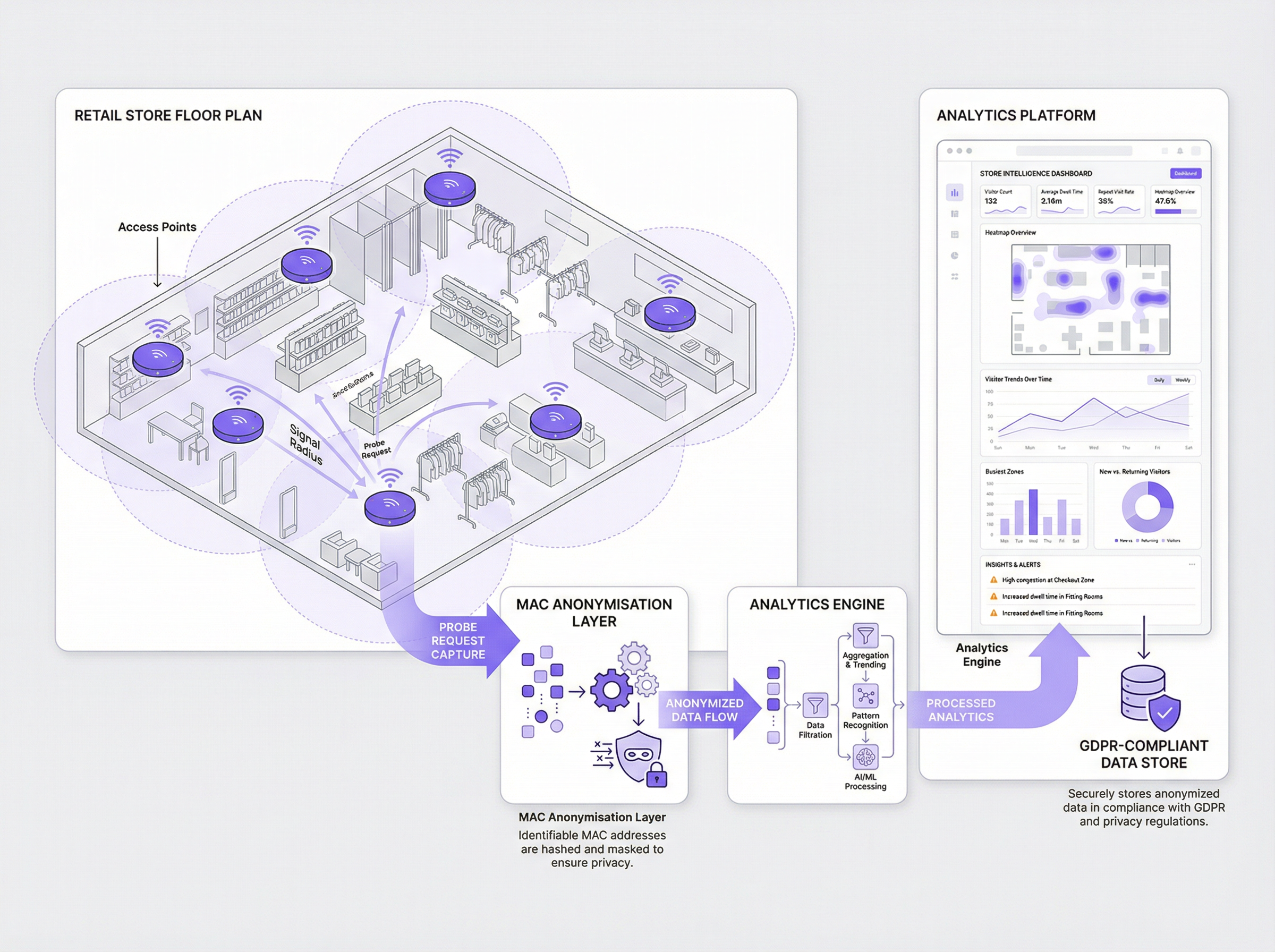
For the modern enterprise, understanding the physical space is as critical as understanding the digital one. WiFi data capture has emerged as a powerful tool for venue operators to gain deep, actionable insights into visitor behaviour, footfall, and spatial utilisation. By analysing the probe requests passively emitted by WiFi-enabled devices, organisations can unlock transformative intelligence to optimise layouts, improve customer experience, and increase operational efficiency. However, this capability comes with significant legal and ethical obligations. Regulators globally, under frameworks like GDPR and CCPA, classify device identifiers such as MAC addresses as personal data. Consequently, their collection and processing are subject to stringent rules regarding consent, anonymisation, and data governance. This guide serves as a practical, authoritative reference for CTOs, IT managers, and network architects. It moves beyond academic theory to provide vendor-neutral, deployment-ready strategies for implementing a WiFi analytics programme that is not only powerful but also secure, compliant, and respectful of user privacy. We will explore the technical architecture, outline robust implementation methodologies, and provide clear, actionable best practices to mitigate risk and maximise ROI.
Technical Deep-Dive
The foundation of WiFi analytics lies in the capture of 802.11 management frames, specifically probe requests. Every WiFi-enabled device (smartphone, laptop, tablet) periodically broadcasts these requests to discover nearby wireless networks. Each frame contains several key pieces of information, but the most critical for analytics is the device's Media Access Control (MAC) address—a unique hardware identifier. By deploying sensors or configuring existing access points to listen for these frames, a system can detect the presence, location, and movement of devices within a physical space.
Data Capture Methods:
- Passive Capture: This method involves sensors that passively listen for probe requests without requiring users to connect to the network. It provides a broad view of all devices in an area, offering rich data on total footfall and movement patterns. However, since there is no direct interaction with the user, obtaining explicit consent is challenging, making robust, immediate anonymisation paramount.
- Active Capture (Captive Portal): This method requires a user to actively connect to the venue’s guest WiFi network. The connection process is mediated by a captive portal, which presents a login or splash page. This is the industry-standard mechanism for obtaining explicit, informed user consent before any data is processed. While it only captures data from connected users, it provides a much stronger legal basis for data processing and enables richer, identity-linked analytics if the user authenticates.
The Anonymisation Imperative: Under GDPR, a MAC address is considered personal data. Therefore, it cannot be stored in its raw format. The best practice is to apply a one-way cryptographic hash (e.g., SHA-256) combined with a rotating salt immediately upon capture. This process, known as pseudonymisation, transforms the MAC address into an irreversible, unique identifier that cannot be traced back to the original device. This anonymised ID can then be used for analytics, such as calculating repeat visits, without storing personal data.
Impact of MAC Address Randomisation: Modern mobile operating systems (iOS 14+ and Android 10+) have implemented MAC address randomisation to enhance user privacy. These devices broadcast a different, randomised MAC address for each new WiFi network they probe for. While this is a pro-privacy feature, it presents a significant challenge for traditional analytics platforms, as a single device can appear as multiple unique visitors. Sophisticated analytics engines, like Purple's, employ advanced algorithms to intelligently identify and reconcile these randomised addresses, ensuring the accuracy of visitor metrics. This is a critical technical capability for any modern WiFi analytics deployment.
Implementation Guide
Deploying a compliant WiFi data capture solution requires a structured, multi-stage approach rooted in the principle of 'Privacy by Design'.
Step 1: Infrastructure Assessment Begin by auditing your existing WiFi infrastructure. Modern enterprise-grade access points from vendors like Cisco, Meraki, Aruba, and Ruckus often have built-in capabilities to stream management frames to an analytics server. Determine if your hardware supports this or if dedicated sensors are required. Ensure adequate coverage across all areas where you intend to capture data.
Step 2: Define Your Data Policy & Consent Mechanism This is the most critical step for compliance. Work with your legal and compliance teams to define:
- What data you will collect: Be specific (e.g.,
Key Terms & Definitions
MAC Address (Media Access Control)
A unique, 48-bit hardware number that identifies each device on a network. Under GDPR, it is considered Personal Identifiable Information (PII).
This is the core piece of data captured by WiFi analytics. IT teams must ensure it is never stored in its raw format and is anonymized immediately upon capture.
Probe Request
An 802.11 management frame sent by a WiFi-enabled device to discover nearby wireless networks.
These are the signals that WiFi analytics systems listen for. Understanding the volume and signal strength of probe requests allows the system to determine footfall and location.
Captive Portal
A web page that a user must view and interact with before being granted access to a public WiFi network.
This is the primary and most effective mechanism for an IT team to obtain explicit, informed consent from users before collecting and processing their data for analytics purposes.
Pseudonymization (Hashing)
The process of replacing a data identifier (like a MAC address) with a pseudonym (a cryptographic hash). It is a reversible process if the key is known, but one-way hashing makes it irreversible.
This is the critical technical process for making WiFi data compliant. A raw MAC address is PII; a hashed MAC address is an anonymized data point that can be used for analysis.
MAC Address Randomization
A privacy feature in modern mobile operating systems (iOS, Android) where the device uses a fake, temporary MAC address when searching for networks.
IT teams must be aware that this feature can severely skew analytics data. A modern analytics platform is required to correctly interpret these randomized addresses and avoid overcounting visitors.
GDPR (General Data Protection Regulation)
A comprehensive data protection law in the European Union that governs the processing of personal data.
This is the key regulation governing WiFi data capture in Europe. Any organisation with a European presence or that serves European citizens must ensure their analytics deployment is fully GDPR-compliant.
Data Controller
The entity that determines the purposes and means of processing personal data.
When a venue deploys WiFi analytics, the venue owner (e.g., the retail chain, the hotel) is the Data Controller and is legally responsible for ensuring compliance.
Dwell Time
A metric that measures the average amount of time visitors spend in a specific, defined area.
This is one of the most valuable business insights from WiFi analytics. It helps operations directors understand engagement, identify bottlenecks, and measure the success of marketing displays or layout changes.
Case Studies
A 50-store retail chain wants to understand customer behaviour in their flagship stores to inform a nationwide redesign. They need to measure dwell times in different departments, identify popular paths, and understand repeat visitor frequency, all while ensuring strict GDPR compliance.
- Infrastructure: Deploy a Purple-compatible WiFi analytics solution using their existing Meraki MR access points. Configure the Meraki dashboard to stream analytics data to the Purple cloud.
- Consent: Implement a branded captive portal for the guest WiFi network. The portal will feature a single, clear opt-in checkbox: "I agree to allow Purple to analyse my anonymized visit data to help improve the store layout and experience. This data is fully anonymized and will not be used for marketing." A link to the full privacy policy is provided.
- Anonymization: Configure the system to use Purple's patented Cryptographic Anonymization, which hashes the MAC address at the moment of capture. This ensures no PII is ever stored.
- Analysis: Use the Purple dashboard to create zones for each department (e.g., Menswear, Womenswear, Checkout). Track anonymized visitor flow between these zones and measure average dwell times. Use the repeat visitor metric to understand customer loyalty.
- Action: After 90 days, the data reveals that the Menswear department has high traffic but low dwell time. The chain redesigns the department layout to be more open and improves product displays. They then measure the impact of these changes over the next 90 days.
A large conference centre with multiple exhibition halls hosts a variety of third-party events. They want to offer event organisers data on attendee flow and booth popularity, but they are concerned about the privacy implications of tracking attendees across different, unrelated events.
- Data Segregation: The key is to treat each event as a separate entity. The WiFi analytics platform must be configured to use a different rotating salt for its hashing algorithm for each event. This means an anonymized ID from Event A will not be the same as the anonymized ID for the same device at Event B.
- Organiser Portals: Provide each event organiser with a separate, sandboxed view of the analytics data for their event only. They should not have access to historical data from other events or raw data of any kind.
- Consent per Event: The captive portal for each event must be unique and clearly state which organiser is the data controller for that event. Attendees must provide consent for each event they attend.
- Reporting: The platform can then generate reports on footfall, hall traffic, and booth dwell times for each specific event. This data can be sold to organisers as a premium service.
- Data Purge: Implement a strict data retention policy to purge all data associated with an event 30 days after the event concludes.
Scenario Analysis
Q1. A stadium is deploying a new WiFi analytics system to manage crowd flow on match days. Their legal team is concerned about storing location data. What is the most important technical control to implement regarding location?
💡 Hint:Think about the principle of data minimisation.
Show Recommended Approach
The most important control is to not store raw or fine-grained location data (e.g., X-Y coordinates). Instead, the stadium should be divided into large, pre-defined zones (e.g., "North Stand, Level 1", "West Entrance Gate"). The system should only record which zone a device is in, not its precise location within that zone. This minimises the sensitivity of the location data while still providing the necessary operational insights for crowd management.
Q2. A shopping mall uses a third-party to manage its guest WiFi. The third-party offers a 'free' analytics package. What is the number one question the mall's CTO should ask the third-party vendor?
💡 Hint:Who is the Data Controller and what are their responsibilities?
Show Recommended Approach
The CTO must ask: "Where and how is the MAC address anonymized?" They need to get a specific, technical answer. If the vendor cannot confirm that the MAC address is hashed with a salt, on-premise, before it is sent to their cloud, it is a major compliance red flag. The mall, as the Data Controller, is ultimately liable for any data breach or non-compliance, even if it is caused by their vendor.
Q3. A user logs into your guest WiFi and consents to analytics. They later submit a 'Right to be Forgotten' request under GDPR. You have stored their data as a hashed, anonymized ID. What is your technical obligation?
💡 Hint:How does pseudonymization relate to a user's rights?
Show Recommended Approach
Even though the data is pseudonymized, it is still linked to a specific individual, and the user's rights still apply. The analytics platform must have a mechanism to process these requests. When the user made the request, they would have provided an identifier (e.g., the email they used to log in). The platform needs a secure, audited process to look up the anonymized IDs associated with that user account and permanently delete them from the analytics database. Simply saying 'the data is anonymous' is not a compliant response.
Key Takeaways
- ✓WiFi data capture offers powerful insights but carries significant privacy obligations.
- ✓A MAC address is personal data under GDPR; it must be anonymized at the point of capture.
- ✓Explicit user consent via a captive portal is the best practice for compliance.
- ✓Modern analytics platforms are essential to handle challenges like MAC address randomization.
- ✓Adopt a 'Privacy by Design' approach, building compliance into your architecture from day one.
- ✓Transparency with users is not just a legal requirement; it is crucial for building trust.
- ✓Regularly audit your system and policies to ensure ongoing compliance and risk mitigation.



