Guest WiFi: The Ultimate Guide for Businesses to Enhance Customer Experience and Gather Valuable Data
This guide is the definitive technical reference for IT leaders and venue operators on deploying enterprise-grade guest WiFi. It provides actionable guidance on network architecture, security, and data analytics to transform guest WiFi from a cost centre into a powerful tool for enhancing customer experience and driving business intelligence.
🎧 Listen to this Guide
View Transcript

Executive Summary
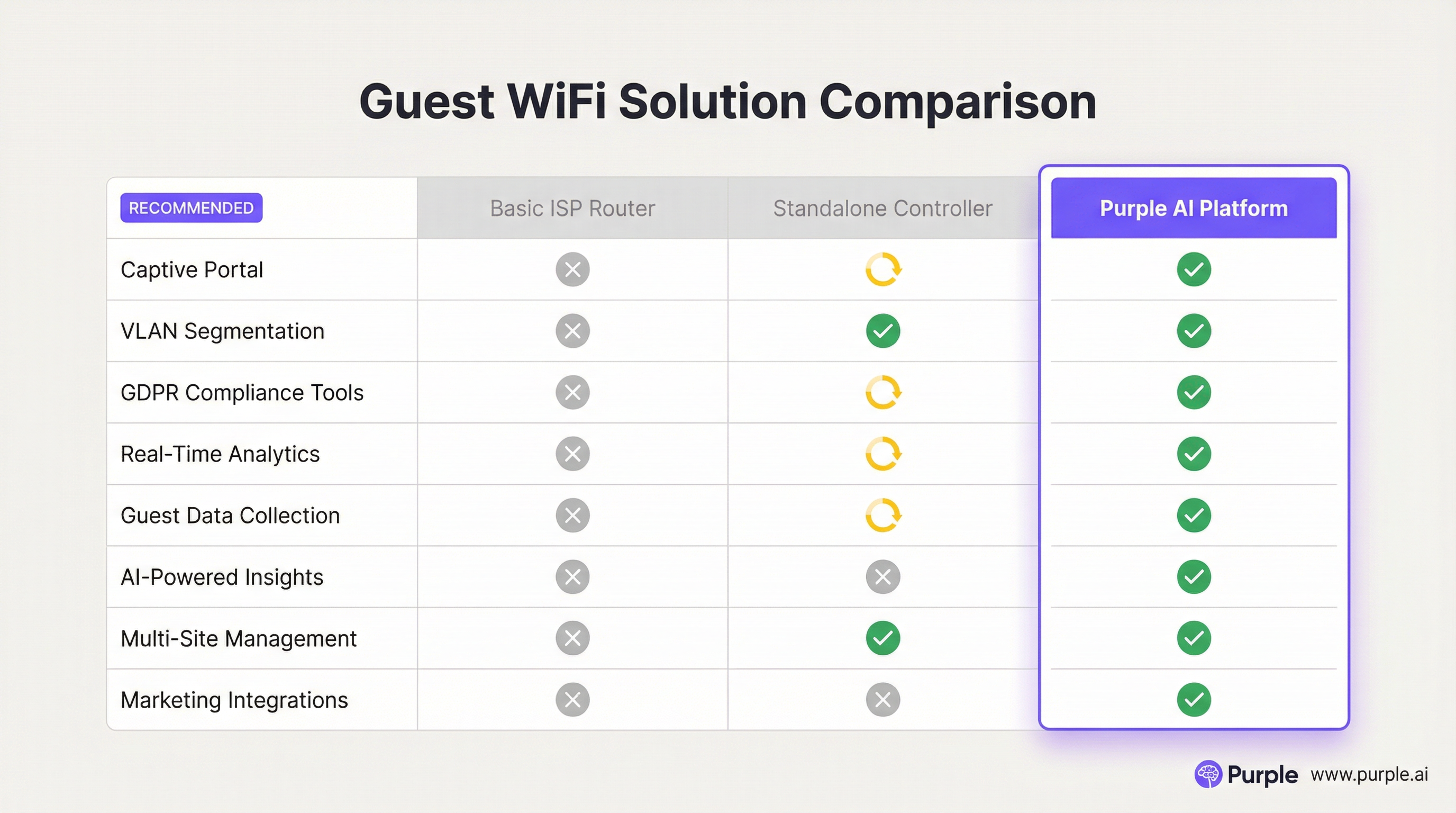
For senior IT professionals and operations directors, guest WiFi has evolved far beyond a simple amenity. Once considered a necessary but peripheral service, it now represents a strategic asset capable of delivering significant ROI. A professionally architected guest WiFi network is no longer just about providing internet access; it is a primary vehicle for enhancing customer experience, gathering unparalleled data on in-venue behaviour, and creating new marketing opportunities. This guide serves as a practical, technical reference for designing, implementing, and managing a secure, high-performance guest WiFi solution. We will move beyond academic theory to provide actionable insights grounded in real-world deployments across hospitality, retail, and large public venues. The focus is on a three-pronged approach: 1) Security and Architecture: Implementing robust network segmentation and access controls to mitigate risk. 2) Data and Analytics: Leveraging a captive portal and WiFi intelligence platform to understand who your customers are and how they behave in your space. 3) Business Impact: Translating that data into measurable outcomes, from improved operational efficiency to increased customer loyalty and revenue. For the CTO, this guide provides the framework for justifying investment in a modern WiFi intelligence platform like Purple AI, moving the conversation from cost to strategic value.
Technical Deep-Dive
A successful guest WiFi deployment rests on a foundation of sound technical architecture. The primary goal is to provide seamless, high-performance internet access to guests without compromising the security or performance of the internal corporate network. This requires a multi-layered approach that addresses hardware, network design, and security protocols.
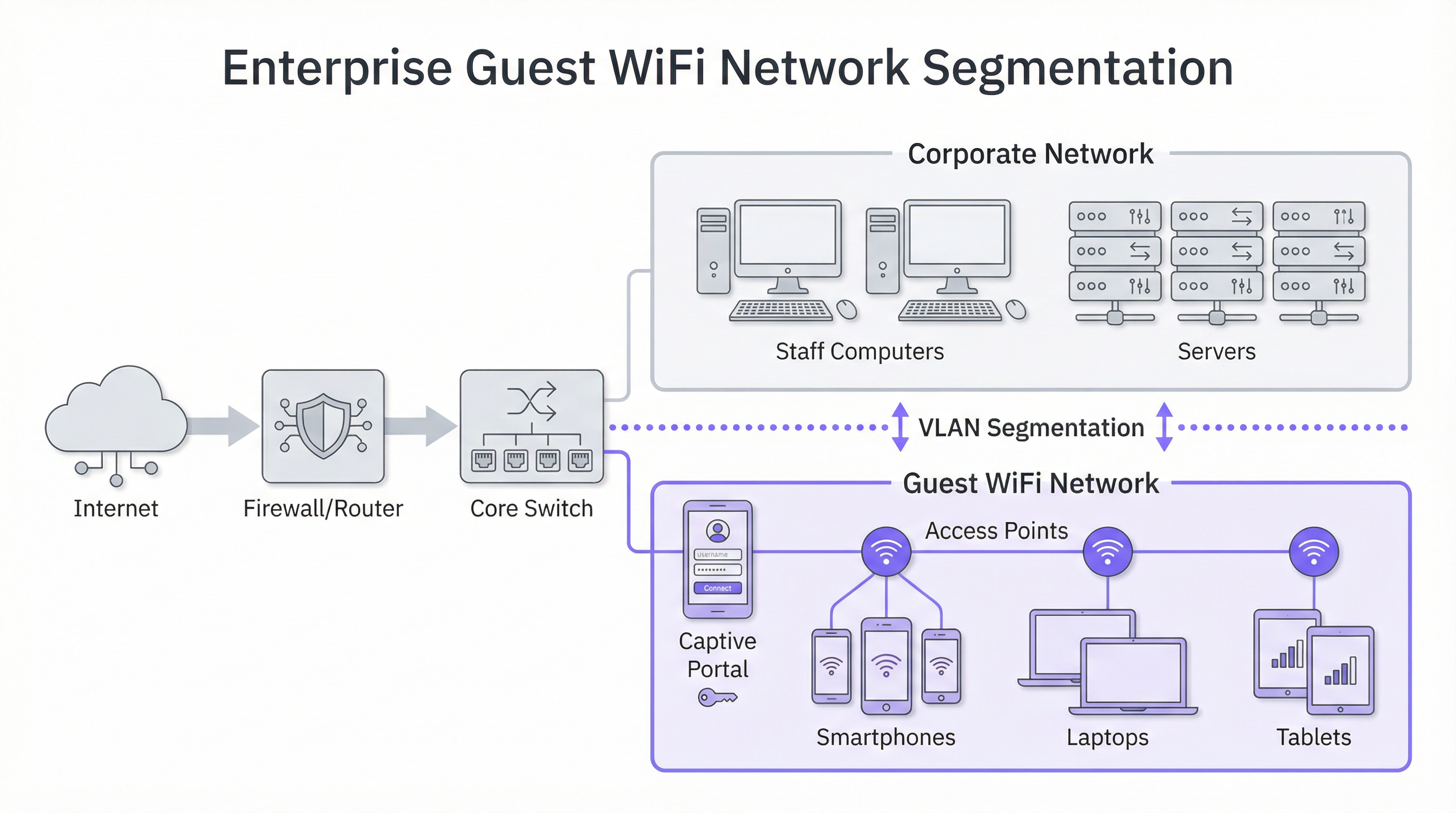
Core Architecture: Segmentation is Non-Negotiable
The single most critical principle in guest WiFi security is network segmentation. A 'flat' network, where guest devices and internal corporate systems (e.g., Point of Sale terminals, staff computers, file servers) share the same logical network, represents an unacceptable security risk. A breach on a single guest device could potentially expose your entire corporate infrastructure. The industry-standard solution is the implementation of VLANs (Virtual Local Area Networks). A VLAN logically divides a single physical network into multiple, isolated broadcast domains. In this model, all guest traffic is confined to its own dedicated VLAN, which is routed directly to the internet and firewalled off from any internal corporate VLANs. This ensures that even if a guest device is compromised, the attack surface is limited strictly to the guest network itself.
Hardware Considerations: Access Points and Controllers
The quality of the user experience is directly tied to the quality and placement of your Wireless Access Points (APs). Hardware selection should be guided by the specific demands of your environment:
- High-Density Venues (Stadiums, Conference Centres): Require high-capacity, 4x4 MU-MIMO (Multi-User, Multiple Input, Multiple Output) APs, often supporting the latest WiFi 6 (802.11ax) or WiFi 6E standards. These are designed to handle a large number of concurrent connections in a concentrated area, mitigating interference and ensuring fair airtime allocation.
- Hospitality and Retail (Hotels, Stores): Coverage and aesthetics are often key. In-room or wall-plate APs can provide excellent, targeted coverage in hotel rooms, while ceiling-mounted APs with a discreet design are suitable for retail floors and public areas. A professional RF (Radio Frequency) site survey is essential before deployment to identify optimal AP locations, minimise channel interference, and eliminate coverage gaps.
Security Protocols and Access Control
Beyond segmentation, several security layers must be implemented:
- WPA3 Encryption: The current security standard for WiFi networks. WPA3-Enterprise offers the highest level of security by providing each user with an individual encryption key, but for public guest networks, WPA3-Personal is more common. The key is to move away from legacy protocols like WEP and WPA/WPA2 wherever possible.
- Client Isolation: This is a crucial feature on your wireless controller or APs that prevents guest devices on the same WiFi network from communicating with each other. It effectively places each guest in their own digital bubble, preventing peer-to-peer attacks and the spread of malware within the guest network.
- Captive Portal: The captive portal is the web page a user is redirected to before being granted full network access. From a technical perspective, it serves as an authentication and authorization gateway. It intercepts the user's initial HTTP request and redirects it to a login server. Once the user meets the defined criteria (e.g., accepts terms, enters an email, logs in via social media), the portal authorizes their device's MAC address with the network controller, which then allows traffic to pass to the internet.
Implementation Guide
Deploying a guest WiFi network can be broken down into a phased project, moving from planning and design to configuration and testing.
Phase 1: Discovery and Planning
- Define Business Objectives: What is the primary goal? Is it data collection for marketing, improving on-site experience, or simply providing basic access? The answer dictates the required features and budget.
- Assess Existing Infrastructure: Can your current switching and routing hardware support VLANs? Is your internet backhaul sufficient for the expected number of concurrent users? A common rule of thumb is to budget for 5-10 Mbps per expected concurrent user for a good experience.
- Conduct a Site Survey: Engage a network engineer to perform a physical and RF site survey. This will determine the number and placement of APs required to provide adequate coverage and capacity.
Phase 2: Design and Configuration
- VLAN and IP Schema: Design your network topology. Define a separate VLAN and IP subnet for the guest network (e.g., VLAN 100, 10.100.0.0/16). Configure your core switch to trunk this VLAN to your wireless controller and firewall.
- Firewall Policy: Create a strict firewall policy for the guest VLAN. This policy should block ALL traffic destined for internal corporate subnets and allow only outbound traffic on standard web ports (80, 443) and other necessary services (e.g., DNS, DHCP).
- Wireless Controller/AP Configuration:
- Create a new WLAN/SSID (e.g., "BrandName Free WiFi").
- Assign this SSID to the guest VLAN.
- Enable Client Isolation.
- Configure the security settings (WPA2/WPA3 with a pre-shared key).
- Configure the captive portal settings, pointing to your WiFi intelligence platform (like Purple).
Phase 3: Integration and Testing
- Captive Portal Integration: Configure your WiFi analytics platform. This involves adding your site, defining the login journey (e.g., social login, form fill), and customizing the branding of the portal pages.
- Testing: Thoroughly test the entire user journey from multiple device types (iOS, Android, laptop). Verify that VLAN segmentation is working correctly by attempting to access internal resources from the guest network (these attempts should fail).
- Go-Live: Once testing is complete, broadcast the SSID and monitor initial connections through your analytics dashboard.
Best Practices
- Prioritise the User Experience: The login process should be as frictionless as possible. A complex, multi-step process will lead to high abandonment rates. Offer multiple login options, such as social media accounts, to speed up the process.
- Be Transparent About Data Collection: Your captive portal's terms and conditions must clearly state what data you are collecting and how you intend to use it, in compliance with regulations like GDPR. Provide a link to your full privacy policy.
- Centralise Management: For multi-site organisations, a cloud-based management platform is essential. It allows a small IT team to monitor, manage, and update thousands of APs across hundreds of locations from a single dashboard.
- Integrate with Other Systems: The value of guest WiFi data is magnified when integrated with other business systems. For example, integrating with a CRM can enrich customer profiles, while integrating with a marketing automation platform can trigger targeted email campaigns based on visitor behaviour.
Troubleshooting & Risk Mitigation
Common Failure Modes:
- Poor Performance: Often caused by insufficient internet bandwidth, poor AP placement (coverage gaps), or channel interference in dense environments. Regular monitoring of network health and utilisation is key.
- Captive Portal Issues: Users may not be redirected to the login page. This can be caused by DNS issues or device-specific settings (e.g., private relay). Ensure your DHCP scope provides a reliable public DNS server.
- Authentication Failures: Incorrect configuration of RADIUS (for WPA-Enterprise) or API integrations with the captive portal can prevent users from getting online. Check logs on both the network controller and the portal platform.
Risk Mitigation Strategies:
- Regular Security Audits: Periodically perform penetration testing against your guest network to identify and remediate vulnerabilities.
- Content Filtering: Implement a DNS-based content filtering service on the guest network to block access to malicious or inappropriate websites.
- Session Timeouts: Enforce session duration limits (e.g., 8 hours) to automatically disconnect inactive devices and free up network resources.
ROI & Business Impact
The investment in an enterprise guest WiFi platform delivers returns across multiple domains:
- Increased Customer Loyalty: A reliable, high-performance WiFi experience is now an expectation. Meeting this expectation improves customer satisfaction and encourages repeat visits.
- Data-Driven Operations: Footfall and dwell time analytics provide concrete data to optimise store layouts, staffing schedules, and even rental negotiations in commercial properties. For example, a retail store can use heatmap data to place high-margin products in the most-trafficked zones.
- Enhanced Marketing Capabilities: By converting anonymous visitors into known customers via the captive portal, you build a valuable marketing database. This allows for personalised post-visit communication, targeted promotions, and loyalty program enrolment.
- Direct Revenue Generation: In some venues like airports or conference centres, a tiered bandwidth model (e.g., free basic access, paid premium access) can create a direct revenue stream.
Ultimately, the business impact is the transformation of a physical space into a smart venue. The data gathered from the WiFi network provides the same level of customer insight that e-commerce websites have enjoyed for years, finally bridging the gap between the physical and digital customer journey.

References
[1]: IEEE 802.1X Standard "Port-Based Network Access Control" [2]: PCI Security Standards Council "Payment Card Industry Data Security Standard" [3]: Official GDPR Information "General Data Protection Regulation (GDPR)"
Key Terms & Definitions
Captive Portal
The web page a user is required to view and interact with before being granted access to a public network. It 'captures' them to force an action, such as accepting terms, providing an email, or completing a social login.
This is the primary tool for IT teams to enforce acceptable use policies and for marketing teams to convert anonymous visitors into known customers. It is the gateway between providing a utility and gathering intelligence.
VLAN (Virtual LAN)
A technology that allows network administrators to logically segment a single physical network into multiple, isolated networks. Devices in one VLAN cannot communicate with devices in another unless explicitly allowed by a router or firewall.
For IT architects, this is the most fundamental tool for securing a guest WiFi network. It ensures that any security event on the guest network is contained and cannot impact the sensitive corporate network.
Client Isolation
A security feature on a wireless access point or controller that prevents devices connected to the same WiFi network from communicating with each other. It creates a private virtual network for each user.
In a public venue, you have no control over the security posture of guest devices. Client Isolation is a critical risk mitigation tool that prevents malware from spreading between laptops in a hotel lobby or conference hall.
SSID (Service Set Identifier)
The public name of a Wireless Local Area Network (WLAN). It is the name you see and select from the list of available WiFi networks on your device.
While a simple concept, the SSID is part of the brand experience. It should be clear, professional, and consistent across all locations (e.g., 'BrandName_Free_WiFi').
802.1X
An IEEE standard for Port-Based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN. It is often used in corporate environments to grant access based on user or machine credentials.
While typically used for corporate networks, network architects may encounter 802.1X in more advanced guest scenarios, such as providing secure, seamless access for conference attendees who are part of an educational roaming federation (eduroam).
GDPR (General Data Protection Regulation)
A regulation in EU law on data protection and privacy for all individuals within the European Union and the European Economic Area. It governs how personal data is collected, processed, and stored.
For any business with a European presence, GDPR compliance is mandatory. A guest WiFi platform must provide tools for obtaining explicit consent for data collection via the captive portal and for managing user data access requests.
Heatmap
A graphical representation of data where values are depicted by colour. In the context of WiFi analytics, it shows the physical areas of a venue with the highest and lowest concentrations of visitor devices.
For venue operations directors, heatmaps provide immediate, visual insight into how their space is being used. It helps answer questions like 'What are the most popular paths through my store?' or 'Which seating area in my lobby is underutilised?'
Dwell Time
A metric that measures the amount of time a visitor spends in a specific area or in the venue as a whole. It is calculated by tracking the duration a device is associated with the WiFi network.
This is a critical KPI for retail and hospitality. It helps managers understand engagement. Longer dwell times in a retail store often correlate with higher sales, while tracking dwell time in a restaurant can help optimise table turnover.
Case Studies
A 250-room luxury hotel wants to replace its outdated and slow guest WiFi. The goals are to provide seamless, high-performance coverage in all rooms and public areas, eliminate negative reviews about connectivity, and gather data to better understand guest behaviour in the lobby, bar, and restaurant.
- Infrastructure Upgrade: Deploy a new network core with a 10Gbps-capable firewall and core switch. 2. Site Survey & APs: Conduct a full RF site survey. Deploy one WiFi 6 wall-plate AP in each guest room for perfect coverage. Deploy ceiling-mounted WiFi 6E APs in public areas like the lobby, bar, and conference rooms to handle high device density. 3. Network Design: Create three separate VLANs: Corporate (for hotel staff and systems), Guest (for hotel visitors), and IoT (for smart room devices like thermostats and TVs). Implement strict firewall rules to prevent inter-VLAN routing. 4. Platform Integration: Integrate the network controller with the Purple AI platform. Configure the captive portal with a simple, branded login page offering two options: 'Connect with Room Number & Last Name' (integrating with the hotel's Property Management System) or a quick social media login. 5. Data Analytics: Use the Purple dashboard to create reports on dwell time in the bar, footfall patterns in the lobby throughout the day, and the percentage of guests who are repeat visitors.
A retail chain with 50 stores across the country wants to understand in-store customer behaviour. They currently offer no guest WiFi. The primary goal is to measure footfall, identify popular zones within stores, and build a marketing list, all while minimising the management burden on a small central IT team.
- Hardware Selection: Choose a template of 3-5 cost-effective, cloud-managed WiFi 6 APs per store, depending on the average store size. 2. Centralised Management: Select a cloud-native network vendor and the Purple AI platform. This allows the central IT team to configure, monitor, and manage all 50 stores from a single web-based dashboard without needing to travel to each site. 3. Deployment: Use a third-party contractor for the physical installation of APs at each store, following the template design. The central IT team can then remotely provision the devices once they are online. 4. Captive Portal: Design a simple, mobile-first captive portal that offers a 10% discount voucher in exchange for an email address. This provides a clear value exchange for the customer. 5. ROI Measurement: Use the Purple analytics dashboard to track the growth of the marketing database, view aggregated footfall across all stores, and compare dwell-time heatmaps between high-performing and low-performing locations to identify layout optimisation opportunities.
Scenario Analysis
Q1. A large conference centre is hosting a 3-day tech event with 5,000 attendees, each carrying at least two devices (laptop and smartphone). The event organiser wants to provide free, high-performance WiFi. What are the three most critical technical considerations for the network architect to ensure a successful deployment?
💡 Hint:Think about capacity, interference, and traffic management in a high-density environment.
Show Recommended Approach
- Capacity & Density Planning: The primary concern is the sheer number of concurrent connections. The architect must use high-density WiFi 6 or 6E APs and perform a detailed RF site survey to ensure sufficient APs are deployed in session halls and common areas. 2. Backhaul & Throughput: The internet connection must be able to handle the aggregated load. A 10Gbps (or higher) redundant internet connection is likely required. QoS (Quality of Service) policies should be implemented to prioritise interactive traffic (like web browsing) over bulk traffic. 3. Efficient Onboarding: With thousands of users connecting at once, the authentication process must be extremely efficient. An open network (no encryption) with a simple, click-through captive portal is the most practical approach to avoid configuration issues for non-technical users and minimise support requests.
Q2. A restaurant chain is using a basic guest WiFi solution from their ISP. They have noticed that the WiFi performance is slow during peak hours, and they have no visibility into who is using the network. What is the most compelling argument for the IT manager to make to the CTO to justify an upgrade to a platform like Purple AI?
💡 Hint:Focus on the transition from a cost/utility to a business intelligence tool.
Show Recommended Approach
The most compelling argument is the shift from viewing WiFi as a cost centre to an ROI-generating asset. The IT manager should frame the investment not as an IT upgrade, but as a business intelligence project. The key points would be: 1) Problem/Opportunity: We are currently blind to our customer behaviour. We don't know our ratio of new vs. repeat diners, our busiest times by actual customer count (not just sales), or how long customers stay. 2) Solution: A platform like Purple AI will not only solve the performance issues with better hardware management but will give us a dashboard to visualise this critical data. 3. ROI: By collecting emails via a captive portal, we can build a marketing database to drive repeat business. By analysing dwell times, we can optimise seating and staffing for peak periods, improving table turnover and revenue. The cost of the platform is offset by the value of this new data and the marketing capabilities it unlocks.
Q3. A hospital wants to provide guest WiFi to patients and visitors. The hospital's CIO is extremely concerned about the security of patient data and compliance with healthcare regulations (like HIPAA). How would you design the guest network to address these specific concerns?
💡 Hint:Security and isolation are paramount. How do you create a 'hermetically sealed' guest network?
Show Recommended Approach
The design must prioritise security above all else. 1. Extreme Segmentation: Implement a guest VLAN that is completely firewalled from all other hospital networks, especially those containing Electronic Health Records (EHR). The firewall rules should be 'deny-all' by default, with an explicit rule to only allow guest VLAN traffic out to the internet. There should be absolutely no route from the guest network to any internal network. 2. Physical & Logical Separation: Where possible, use a physically separate internet line for guest traffic. If not feasible, use a high-end firewall capable of deep packet inspection and intrusion prevention on the guest traffic. 3. Strict Access Control: Enable Client Isolation on all APs to prevent any patient or visitor devices from communicating with each other. Implement a captive portal that requires acceptance of a stringent acceptable use policy and displays clear warnings against attempting to access clinical systems. 4. No Data Collection: For maximum privacy and minimum risk, the captive portal should be a simple 'click-to-accept' with no personal data collection (no email, no social login). The focus is purely on providing access, not marketing.
Key Takeaways
- ✓Guest WiFi is no longer a simple amenity; it is a strategic tool for data collection and customer engagement.
- ✓Network segmentation (using VLANs) is the most critical security measure to protect your corporate network.
- ✓A captive portal is the gateway to converting anonymous visitors into known customers and enforcing legal terms.
- ✓High-quality Access Points and a professional RF site survey are essential for a positive user experience.
- ✓WiFi analytics platforms like Purple AI provide actionable insights into footfall, dwell time, and visitor behaviour.
- ✓Compliance with data privacy regulations like GDPR is mandatory and must be designed into your solution.
- ✓The ROI of a professional guest WiFi solution is realised through improved operations, enhanced marketing, and increased customer loyalty.



