Personal Area Networks (PANs): A Comprehensive Guide to Technologies, Security, and Applications
This guide provides a comprehensive technical reference on Personal Area Networks (PANs) for IT leaders and network architects. It covers the core technologies, critical security considerations for enterprise deployments, and practical implementation guidance for leveraging PANs in venues like hotels, retail, and stadiums to enhance operational efficiency and customer experience.
🎧 Listen to this Guide
View Transcript

Executive Summary
Personal Area Networks (PANs) have evolved from simple peripheral connections to a foundational technology for the Internet of Things (IoT) within the enterprise. For IT managers, network architects, and CTOs in sectors such as hospitality, retail, and large public venues, a robust PAN strategy is no longer optional—it is critical for driving operational intelligence, enabling new guest experiences, and maintaining a competitive edge. This guide provides an actionable framework for understanding, deploying, and securing the diverse ecosystem of PAN technologies, including Bluetooth Low Energy (BLE), Zigbee, NFC, and the emerging UWB and Thread/Matter standards. We move beyond academic theory to offer vendor-neutral, practical guidance focused on risk mitigation, compliance, and ROI. The central thesis is that while PANs introduce a complex new layer to the enterprise network, a proactive security posture, grounded in standards like IEEE 802.1X and WPA3, can transform this potential attack surface into a secure, high-value asset. This document will equip you with the technical knowledge to evaluate these technologies and the strategic insight to implement them effectively, ensuring your infrastructure is not only connected but also protected.
Technical Deep-Dive
Understanding the technical nuances of each PAN technology is fundamental to making informed architectural decisions. The choice of protocol directly impacts deployment cost, scalability, security, and the types of applications that can be supported. This section provides a detailed comparison of the most prevalent PAN standards in an enterprise context.
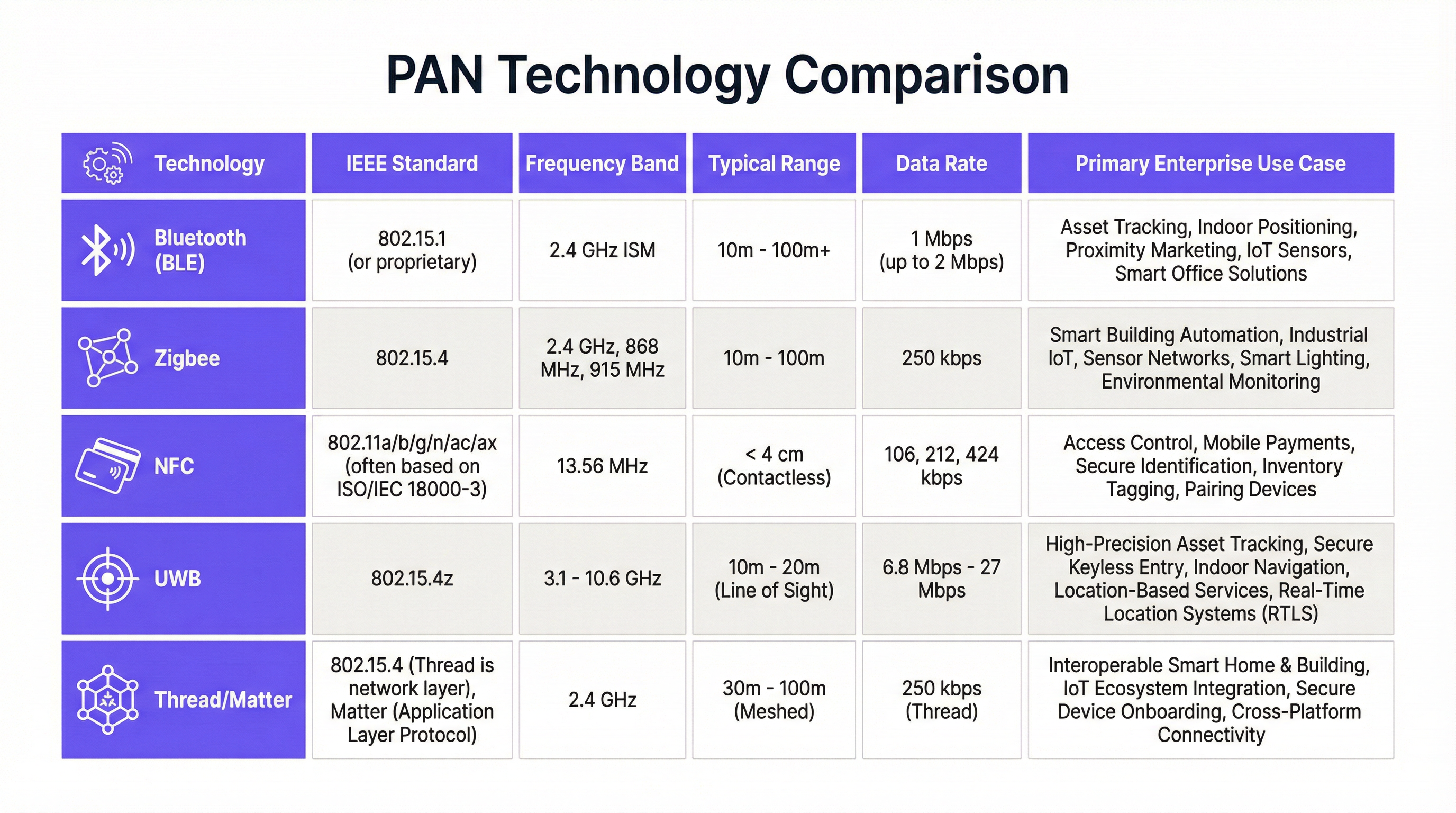
Bluetooth and Bluetooth Low Energy (BLE)
Governed by the IEEE 802.15.1 standard, Bluetooth is the most ubiquitous PAN technology. While Classic Bluetooth is optimized for streaming applications like audio, Bluetooth Low Energy (BLE) is the variant of primary interest for enterprise IoT. Operating in the 2.4 GHz ISM band, BLE is designed for ultra-low power consumption, allowing battery-powered sensors and beacons to operate for years. Its data rate of up to 2 Mbps and range of over 100 meters make it ideal for applications like indoor positioning, asset tracking, and proximity marketing. From a deployment perspective, BLE benefits from being natively supported in virtually all modern smartphones and tablets, reducing the need for specialized client hardware. However, the crowded 2.4 GHz spectrum can be a source of interference, requiring careful channel planning in dense deployments.
Zigbee
Based on the IEEE 802.15.4 specification, Zigbee also operates in the 2.4 GHz band but is distinguished by its robust mesh networking capabilities. In a Zigbee network, devices can relay data for other devices, extending the network’s range and improving its resilience. This makes it exceptionally well-suited for large-scale, static sensor networks, such as those found in smart buildings for HVAC and lighting control or in industrial environments for equipment monitoring. With a lower data rate of 250 kbps, Zigbee is not intended for large data transfers but excels at reliable, low-latency command-and-control messaging. For network architects, a key consideration is that Zigbee often requires a dedicated gateway to bridge sensor data onto the corporate IP network.
Near Field Communication (NFC)
NFC is a specialized, very short-range technology operating at 13.56 MHz, with a typical range of less than 4 centimeters. Governed by standards like ISO/IEC 14443, its primary strength lies in its intuitive, tap-to-act functionality. This makes it the global standard for contactless payments (and thus subject to PCI DSS compliance) and a popular choice for secure access control, keyless hotel room entry, and interactive marketing (e.g., “smart posters”). The inherent proximity requirement is a security feature, as it makes remote eavesdropping difficult. However, this same limitation means it is unsuitable for any application requiring continuous or long-range connectivity.
Ultra-Wideband (UWB)
UWB represents a significant leap in precision for PANs. Operating across a vast spectrum (3.1 to 10.6 GHz), it transmits rapid pulses to measure time-of-flight with incredible accuracy, enabling location services with a precision of under 30 centimeters. This capability is transformative for high-value asset tracking, secure hands-free access control (as seen in modern vehicles), and real-time location systems (RTLS) in environments like warehouses and hospitals. While more costly to implement than BLE, the ROI for UWB is found in applications where precise location is a critical operational requirement. The market for UWB is projected to grow significantly, indicating its increasing importance in enterprise strategy 1.
Thread and Matter
Thread is an IPv6-based mesh networking protocol also built on IEEE 802.15.4, designed to provide reliable, secure, and scalable connectivity for IoT devices. Unlike Zigbee, it is IP-native, which simplifies integration with existing network infrastructure. Matter is an application layer protocol that runs on top of Thread, Wi-Fi, and Ethernet. Its goal is to create a unified, interoperable ecosystem for smart devices, regardless of the manufacturer. For CTOs planning smart building projects, the emergence of the Matter standard is a critical development, promising to reduce vendor lock-in and simplify device management.
Implementation Guide
Deploying PAN technologies within an enterprise environment requires a structured approach that moves from defining business objectives to network integration and ongoing management. A successful implementation hinges on aligning the chosen technology with specific use cases and integrating it securely into the existing network fabric.
Step 1: Define Business Objectives and Use Cases Before any hardware is purchased, IT leaders must collaborate with operations directors to clearly define the goals. Are you trying to improve guest experience in a hotel with keyless entry? Or optimize stock management in retail with asset tracking? The use case dictates the technology. For example, a proximity marketing campaign would leverage BLE, while a secure payment terminal requires NFC.
Step 2: Conduct a Site Survey and Spectrum Analysis For RF-based technologies like BLE, Zigbee, and UWB, a thorough site survey is non-negotiable. This involves mapping out the physical environment to identify potential sources of RF interference (like Wi-Fi access points, microwave ovens, and building materials like concrete and metal) that can impact signal propagation. Using a spectrum analyzer to assess the 2.4 GHz band is particularly crucial in venues with dense Wi-Fi deployments. This analysis will inform the placement of gateways, anchors, and sensors to ensure reliable coverage.
Step 3: Design the Network Architecture This phase involves deciding how PAN data will be backhauled to the corporate network. Will you use dedicated gateways for Zigbee or Thread? Or will you leverage your existing Wi-Fi infrastructure to backhaul data from BLE devices? A key architectural decision is network segmentation. All PAN-related traffic should be isolated on its own VLAN, separate from critical corporate and guest networks. This is a foundational security measure to contain any potential breach originating from an IoT device.
Step 4: Device Onboarding and Provisioning Securely onboarding thousands of IoT devices is a significant logistical challenge. Manual provisioning is not scalable. Solutions should support zero-touch provisioning where possible, using certificate-based authentication (leveraging a private CA or trusted third-party CA) to ensure that only authorized devices can join the network. This process should be integrated with an asset management system to maintain a complete inventory of all connected PAN devices.
Step 5: Integration with Enterprise Systems The data collected from PAN devices is only valuable when it is integrated with other business systems. This could involve sending location data from a UWB RTLS to a warehouse management system, feeding occupancy data from BLE sensors into a building management system, or linking NFC access events to a security information and event management (SIEM) platform. This integration must be done via secure, authenticated APIs.
Step 6: Monitoring and Lifecycle Management Post-deployment, the network operations team needs visibility into the health and security of the PAN. This includes monitoring device status, battery levels, and network performance. Crucially, it also involves a robust process for firmware updates. As new vulnerabilities are discovered in Bluetooth or Zigbee stacks, the ability to patch devices over-the-air is a critical security requirement. Any device that cannot be updated should be considered a significant liability.
Best Practices
Adhering to industry-standard best practices is essential for mitigating the risks associated with enterprise PAN deployments. These recommendations focus on creating a resilient and secure network architecture.
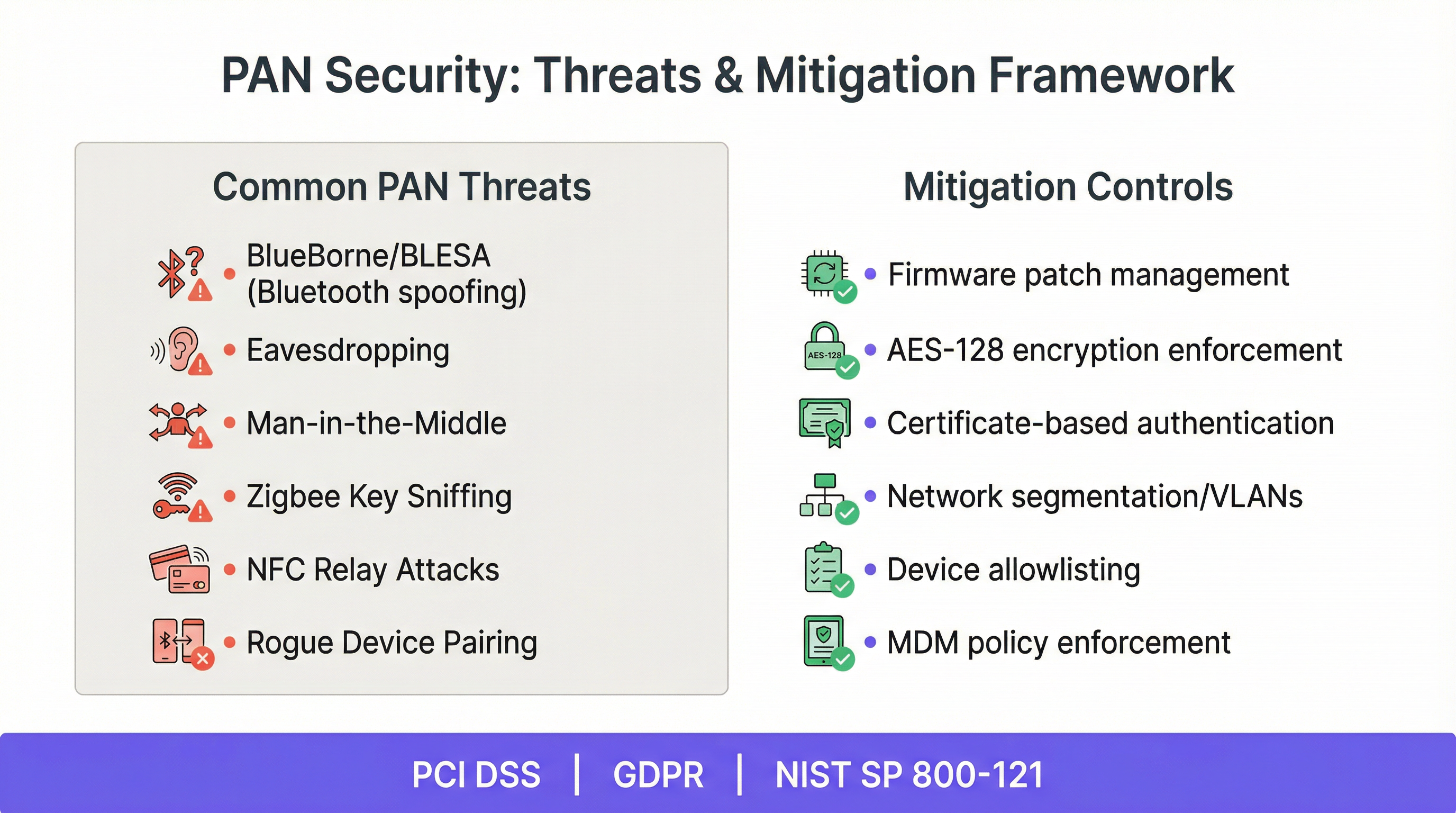
1. Enforce Strong Encryption and Authentication: All wireless PAN traffic must be encrypted. For BLE, this means enforcing AES-128 encryption. For Zigbee, it involves using the security features of the Zigbee 3.0 specification. Never rely on default or easily guessable keys. Where possible, move beyond pre-shared keys (PSKs) and implement enterprise-grade authentication using IEEE 802.1X with EAP-TLS, which uses digital certificates for both the device and the network.
2. Implement Strict Network Segmentation: This is the most critical architectural control. PAN devices should be placed on a dedicated VLAN that is firewalled from all other networks. Access control lists (ACLs) should be configured to restrict traffic, allowing devices to communicate only with their specific gateway or management platform and nothing else. This principle of least privilege prevents a compromised IoT sensor from being used as a pivot point to attack more critical systems.
3. Maintain a Comprehensive Device Inventory: You cannot secure what you do not know you have. Maintain a real-time, accurate inventory of every PAN device on your network. This inventory should include the device type, MAC address, firmware version, physical location, and owner. This is foundational for both security monitoring and operational management.
4. Establish a Robust Patch Management Program: PAN device firmware is a frequent source of vulnerabilities, as seen with disclosures like BlueBorne and BLESA 2. Your deployment strategy must include a process for monitoring vulnerability announcements from device vendors and the ability to deploy firmware updates over-the-air (OTA) in a timely manner. Devices that are not patchable present an unacceptable risk to the enterprise.
5. Utilize Mobile Device Management (MDM) for BYOD Scenarios: In many PAN applications, the interacting device is a user’s smartphone (e.g., for BLE-based access or NFC payments). In these cases, an MDM or Unified Endpoint Management (UEM) solution should be used to enforce security policies on the mobile device itself, such as requiring a passcode, enabling encryption, and ensuring the operating system is up to date.
Troubleshooting & Risk Mitigation
Even with careful planning, PAN deployments can encounter issues. Proactive risk mitigation involves anticipating common failure modes and having a plan to address them.
| Common Problem | Symptoms | Mitigation & Troubleshooting Steps |
|---|---|---|
| RF Interference | Unreliable connectivity, high latency, frequent device drop-offs. | 1. Use a spectrum analyzer to identify the source of interference (e.g., Wi-Fi, microwaves). 2. Change Zigbee or Wi-Fi channels to avoid overlap (e.g., use Wi-Fi channels 1, 6, 11 and Zigbee channels 15, 20, 25). 3. Relocate gateways or devices to improve signal-to-noise ratio. 4. In extreme cases, shield sensitive equipment or the interference source. |
| Device Spoofing | Unauthorized device gains access by impersonating a legitimate one (e.g., BIAS/BLESA attacks). | 1. Enforce strong, certificate-based authentication (EAP-TLS). 2. Keep firmware updated with the latest security patches from vendors. 3. Implement network-level monitoring to detect anomalies, such as a device connecting from an unusual location. |
| Battery Drain | Battery-powered devices fail prematurely, causing operational disruption. | 1. Ensure devices are configured with the correct power-saving parameters (e.g., advertising interval in BLE). 2. Monitor battery levels proactively and set alerts for low-battery states. 3. During site surveys, verify that devices are not placed in locations where they have to transmit at maximum power to reach a gateway. |
| Gateway Failure | Loss of connectivity for an entire segment of the PAN. | 1. Deploy redundant gateways in critical areas. 2. Configure automated failover between gateways. 3. Implement a monitoring system that provides immediate alerts upon gateway failure. |
| Data Eavesdropping | Sensitive data is intercepted by an unauthorized party. | 1. Mandate strong, end-to-end encryption for all PAN traffic. 2. Ensure that encryption keys are managed securely and rotated periodically. 3. For NFC, educate users on safe tapping practices to prevent skimming. |
ROI & Business Impact
For a CTO or IT Director, justifying investment in PAN technologies requires a clear articulation of the return on investment (ROI) and business impact. The benefits typically fall into three categories: operational efficiency, enhanced customer experience, and new revenue streams.
Operational Efficiency: This is often the most straightforward area to measure. For example, in a large warehouse, a UWB-based RTLS can reduce the time staff spend searching for equipment. By measuring the average search time before and after implementation and multiplying by labor costs, a direct cost saving can be calculated. Similarly, in a smart building, Zigbee-controlled HVAC and lighting can reduce energy consumption by 15-20%, a figure that can be directly translated into financial savings from utility bills.
Enhanced Customer/Guest Experience: While harder to quantify directly, the impact on customer satisfaction and loyalty is significant. In hospitality, offering seamless, keyless room entry via a guest's smartphone (using BLE or NFC) removes a common point of friction at check-in. In retail, BLE-powered indoor navigation can guide shoppers to products, improving their in-store experience. These benefits are measured through metrics like Net Promoter Score (NPS), customer satisfaction (CSAT) surveys, and repeat business rates.
New Revenue Streams: PAN technologies can unlock entirely new business models. A stadium operator can use a BLE-based proximity solution to offer seat upgrades or deliver targeted promotions for merchandise and concessions directly to fans' phones during an event. Retailers can use footfall analytics derived from PAN sensors to sell premium placement opportunities to brands. The ROI here is measured by the direct revenue generated from these new services.
Ultimately, the business case for a PAN deployment rests on a clear understanding of the costs (hardware, installation, software, ongoing management) versus the quantifiable benefits. A successful project will deliver a positive ROI within a 12-24 month timeframe, while also providing strategic advantages that are harder to measure but equally important for long-term success.
Key Terms & Definitions
Mesh Networking
A network topology where devices (nodes) connect directly, dynamically, and non-hierarchically to as many other nodes as possible and cooperate with one another to efficiently route data to and from clients.
In the context of PANs, technologies like Zigbee and Thread use mesh networking to extend their range and improve reliability in large buildings. If one node fails, the network can automatically re-route traffic, making it ideal for infrastructure like smart lighting.
IEEE 802.15.4
An IEEE standard that specifies the physical layer and media access control for low-rate wireless personal area networks (LR-WPANs).
This is the foundational standard upon which several key PAN technologies are built, including Zigbee and Thread. When a vendor claims compliance with this standard, it ensures a baseline level of interoperability at the lower network layers.
Pairing
The process of establishing a trusted connection between two Bluetooth devices, creating a shared secret key that is used to encrypt future communications.
While pairing is a fundamental Bluetooth security feature, vulnerabilities like BIAS and BLESA have shown that the process itself can be attacked. IT teams must ensure devices are patched against these vulnerabilities to maintain the integrity of paired connections.
Gateway
A hardware device that acts as a bridge between a PAN (like a Zigbee network) and a larger IP-based network (like the corporate LAN or the internet).
For non-IP-native PAN technologies, the gateway is a critical piece of infrastructure but also a potential bottleneck and security risk. Network architects must ensure gateways are secure, redundant, and properly firewalled.
Beacon
A small, low-power hardware transmitter that broadcasts a unique identifier using Bluetooth Low Energy.
In retail and hospitality, beacons are used for proximity marketing and indoor navigation. Smartphones and other devices can listen for these beacon signals to trigger location-aware actions, such as displaying a promotion or guiding a user through a venue.
Time-of-Flight (ToF)
A method for measuring the distance between a sensor and an object, based on the time difference between the emission of a signal and its return to the sensor after being reflected by the object.
UWB technology uses ToF to achieve its high-precision location tracking. By measuring the propagation time of radio signals, it can calculate distances with centimeter-level accuracy, which is far more precise than methods based on signal strength (RSSI).
Network Segmentation
The practice of splitting a computer network into subnetworks, each being a network segment. The main advantage is to improve security and performance.
For IT managers, this is the most important security control for PAN deployments. Placing all IoT devices on a separate VLAN (a form of segmentation) prevents a compromised device from accessing sensitive corporate data.
Over-the-Air (OTA) Update
The wireless delivery of new software, firmware, or other data to mobile devices.
The ability to perform OTA updates is a critical requirement for any enterprise PAN device. Without it, patching security vulnerabilities becomes a manual, costly, and often impossible task, leaving the network exposed to known threats.
Case Studies
A 500-room luxury hotel wants to implement keyless entry and smart room controls (lighting, thermostat) to enhance guest experience and improve energy efficiency. The hotel has a modern Wi-Fi 6 network but has experienced issues with IoT device security in the past. They need a secure, scalable, and reliable solution.
A hybrid approach is recommended. For keyless entry, Bluetooth Low Energy (BLE) is the ideal choice. The hotel would deploy BLE-enabled door locks. Guests would use the hotel's mobile app, which leverages the native BLE capabilities of their smartphone to act as a room key. This provides a seamless experience. For the in-room smart controls, Zigbee is the more robust solution. Each room would have a small Zigbee network of lights and a thermostat connected to a central in-room gateway. This creates a dedicated, low-interference network for critical room functions. These Zigbee gateways would then be connected to the hotel's wired network and placed on a dedicated, firewalled VLAN, completely isolated from both guest and corporate traffic. All traffic from the gateways to the central management server would be encrypted using TLS. This architecture ensures that the high-traffic, guest-facing Wi-Fi network is not burdened with IoT control traffic, and the critical room systems are protected by multiple layers of security.
A large retail chain with 200 stores wants to track high-value assets (e.g., mobile payment terminals, specialized equipment) in real-time to reduce loss and improve operational efficiency. They also want to gather analytics on customer footfall patterns. The environment is RF-congested with extensive Wi-Fi and cellular usage.
For the high-value asset tracking, Ultra-Wideband (UWB) is the superior technology due to its high precision (<30cm). UWB anchors would be installed throughout the back-of-house and on the retail floor. Each asset would be fitted with a UWB tag. This allows for real-time location tracking with enough accuracy to know if an asset has left a specific zone or the building itself. For the customer footfall analytics, BLE beacons are a more cost-effective and scalable solution. Beacons would be placed throughout the store. By detecting the signals from these beacons using sensors or by having customers opt-in via a store app, the retailer can generate heatmaps of customer movement and dwell time. The UWB and BLE systems would operate on separate, dedicated networks, each on its own VLAN. The UWB data provides precise location for security, while the BLE data provides broader analytics for marketing and operations. This dual-technology approach provides the best ROI by using the more expensive UWB only where precision is essential.
Scenario Analysis
Q1. A conference centre is hosting a major tech event and wants to provide attendees with indoor navigation to different sessions and exhibitor booths. They also want to monitor crowd density in real-time to comply with health and safety regulations. What PAN technology or technologies would you recommend and why?
💡 Hint:Consider the scale of the environment and the need for both individual guidance and aggregate data. Think about the devices attendees are likely to have.
Show Recommended Approach
The best solution would be based on Bluetooth Low Energy (BLE). For indoor navigation, a network of BLE beacons would be deployed throughout the venue. Attendees would use the event's mobile app, which would detect the beacons and provide turn-by-turn directions. This leverages the attendees' own smartphones, requiring no special hardware. For crowd density monitoring, fixed BLE sensors can be used to anonymously detect the number of Bluetooth devices (smartphones) in a given area. This provides a real-time, privacy-respecting measure of crowd density that can be fed into a central dashboard for the event operations team. BLE is cost-effective, scalable for a large venue, and leverages existing user devices, making it the ideal choice.
Q2. A hospital wants to track the location of critical mobile medical equipment (like infusion pumps and ventilators) to ensure they can be found quickly in an emergency. The environment is a complex, multi-floor building with significant RF interference from medical imaging equipment. Accuracy is the top priority. What is your recommendation?
💡 Hint:The key requirement is accuracy in a challenging RF environment. Which PAN technology excels at high-precision location services?
Show Recommended Approach
Ultra-Wideband (UWB) is the most appropriate technology for this use case. While more expensive than BLE, its ability to provide centimeter-level accuracy is essential for locating life-critical equipment in an emergency. UWB's use of a wide spectrum also makes it more resilient to the RF interference common in hospital environments. A network of UWB anchors would be installed, and each piece of equipment would be tagged. The system would provide a real-time map of all assets, drastically reducing search times for clinical staff. The high cost is justified by the immense clinical value and risk reduction.
Q3. Your company is planning a new smart office building. The goal is to have a fully integrated system where lighting, HVAC, and security systems from different manufacturers can all work together seamlessly. The system must be secure, scalable, and future-proof. Which emerging PAN ecosystem should you be specifying in your design requirements?
💡 Hint:Think about the latest industry-wide initiatives for IoT interoperability. The goal is to avoid vendor lock-in.
Show Recommended Approach
The design requirements should specify Matter-compliant devices. Matter is an application-layer interoperability standard designed to solve this exact problem. By specifying Matter, you ensure that devices from different vendors can communicate and work together securely. Underneath the Matter layer, you should specify Thread as the primary mesh networking protocol for battery-powered devices like sensors, and Wi-Fi for high-bandwidth devices. This combination of Matter and Thread creates a secure, IP-based, and scalable network that is supported by all major technology companies, making it a future-proof choice that avoids vendor lock-in and simplifies management.
Key Takeaways
- ✓PANs are a critical component of modern enterprise IoT strategy, enabling applications from asset tracking to smart building control.
- ✓Choosing the right PAN technology (BLE, Zigbee, NFC, UWB) depends entirely on the specific use case, balancing cost, range, and precision.
- ✓Security is paramount. All PAN deployments must be built on a foundation of strong encryption, authentication, and strict network segmentation.
- ✓Isolating all PAN/IoT devices on a dedicated, firewalled VLAN is the single most important security measure you can take.
- ✓A robust patch management process to apply over-the-air (OTA) firmware updates is non-negotiable for mitigating vulnerabilities.
- ✓The ROI of PANs can be measured in operational efficiency, enhanced customer experience, and the creation of new revenue streams.
- ✓The emerging Matter standard promises to unify the fragmented smart device ecosystem, simplifying deployment and reducing vendor lock-in.



