Understanding and Hardening RADIUS Against MD5 Collision Attacks
This guide provides a comprehensive technical reference on the RADIUS MD5 collision vulnerability (CVE-2024-3596, 'Blast-RADIUS'), explaining how man-in-the-middle attackers can exploit weaknesses in the MD5-based Response Authenticator to forge authentication approvals without knowing user credentials. It is essential reading for IT managers, network architects, and CTOs operating enterprise WiFi in hospitality, retail, events, and public-sector environments who need to assess their exposure, apply immediate mitigations, and plan a strategic migration to modern authentication standards. The guide covers the full attack lifecycle, a phased hardening roadmap, real-world deployment scenarios, and compliance implications under PCI DSS, GDPR, and ISO 27001.
🎧 Listen to this Guide
View Transcript

Executive Summary
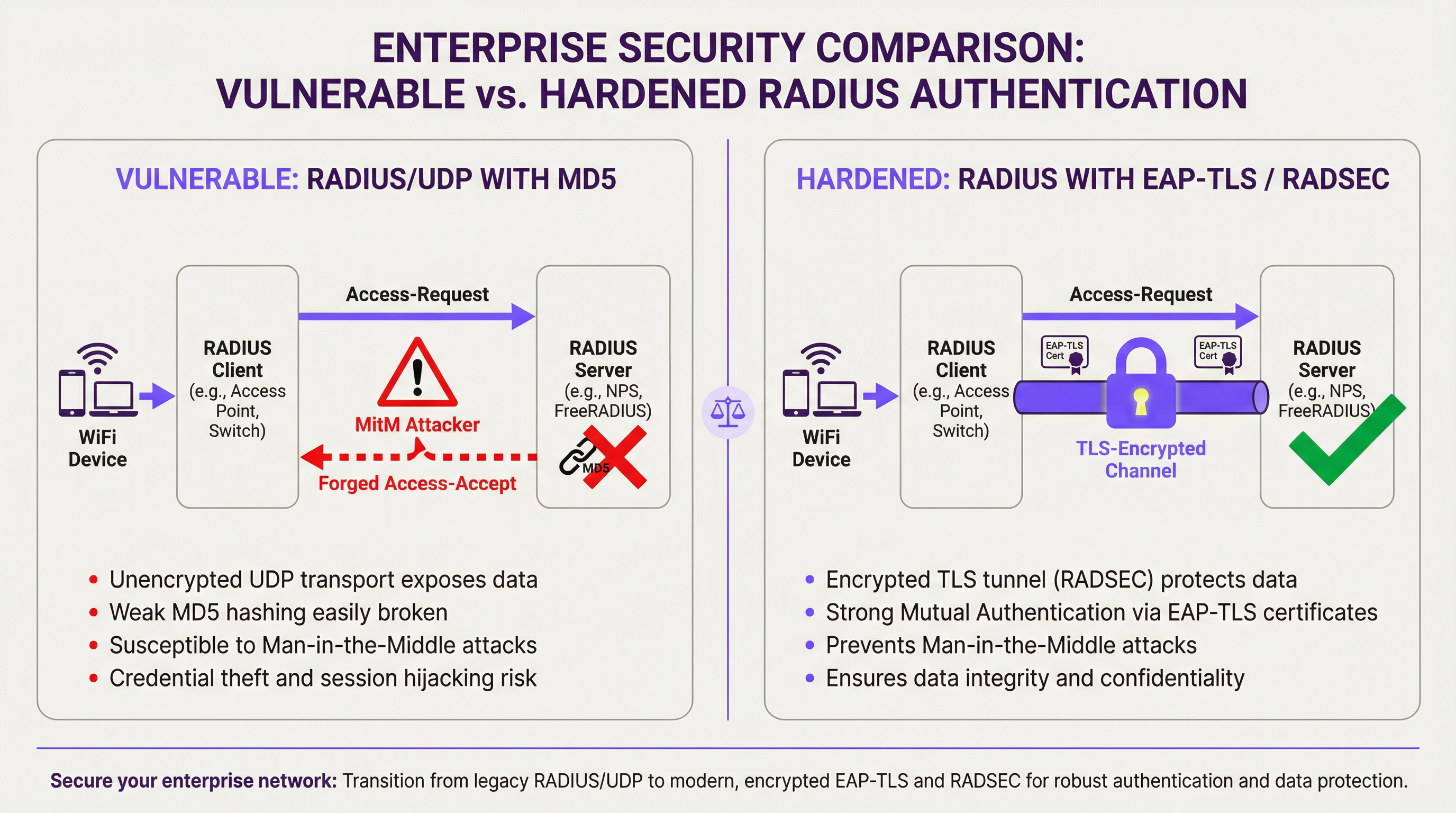
The RADIUS protocol, a cornerstone of enterprise network authentication since 1991, carries a critical and now practically exploitable vulnerability. Disclosed in July 2024 under CVE-2024-3596 and dubbed 'Blast-RADIUS', this flaw allows a man-in-the-middle (MitM) attacker positioned between a RADIUS client and server to forge a valid authentication approval — converting a legitimate 'Access-Reject' into an 'Access-Accept' — without ever knowing a user's password or the shared RADIUS secret. The attack exploits MD5 chosen-prefix collision techniques that, with modern hardware, can be executed in minutes.
For venue operators and enterprise IT teams, the business risk is direct: an attacker who gains unauthorised network access can move laterally across infrastructure, access point-of-sale systems, exfiltrate guest data, and trigger compliance violations under PCI DSS and GDPR. Every organisation running RADIUS/UDP with PAP, CHAP, or MS-CHAP authentication modes is exposed until patches are applied and architectural changes are planned. The immediate mitigation — enforcing the Message-Authenticator attribute on all RADIUS traffic — is a low-disruption configuration change available from all major vendors. The strategic response is a phased migration to EAP-TLS and RADIUS over TLS (RADSEC).
Technical Deep-Dive
The RADIUS Protocol and Its Cryptographic Heritage
RADIUS (Remote Authentication Dial-In User Service), standardised in RFC 2865, was designed in an era when network security requirements were fundamentally different. The protocol operates over UDP and uses a shared secret between the RADIUS client (typically an access point or network access server) and the RADIUS server to provide a degree of message integrity. Specifically, server responses are 'authenticated' using a construct called the Response Authenticator, calculated as:
MD5(Code || ID || Length || RequestAuthenticator || Attributes || SharedSecret)
This construction was never a proper message authentication code (MAC). It predates HMAC, which was standardised in 1997 precisely to address the weaknesses of raw hash-based MACs. The RADIUS specification was not updated when HMAC was introduced, nor when MD5 collisions were first demonstrated in 2004. This architectural debt has now become a critical liability.
The Blast-RADIUS Attack Mechanics
The Blast-RADIUS attack (CVE-2024-3596) combines three elements: a protocol-level vulnerability in how RADIUS constructs its Response Authenticator, an MD5 chosen-prefix collision technique, and significant speed improvements to the collision computation that make the attack practical in a real-time network interception scenario.
The attack proceeds as follows. A MitM attacker intercepts an Access-Request packet sent from the RADIUS client to the server. The attacker injects a malicious attribute into this request — a carefully crafted payload that will cause a collision between the MD5 hash of the legitimate server response and the MD5 hash of the attacker's desired forged response. When the server returns an Access-Reject (a failed authentication), the attacker uses the pre-computed collision to forge a valid Access-Accept packet, complete with a Response Authenticator that the RADIUS client will accept as genuine. The attacker does not need to know the shared secret or the user's credentials.
Researchers at Boston University, UC San Diego, CWI Amsterdam, and Microsoft demonstrated that with optimised algorithms, the MD5 chosen-prefix collision required for this attack can be computed in under five minutes on commodity hardware. This makes the attack operationally viable for a determined adversary with access to the network path between the RADIUS client and server.
Affected Authentication Modes
The vulnerability affects all RADIUS/UDP deployments using non-EAP authentication methods. The table below summarises the exposure by authentication mode:
| Authentication Mode | Protocol | Vulnerable to Blast-RADIUS? | Notes |
|---|---|---|---|
| PAP | Password Authentication Protocol | Yes | Most common in legacy deployments |
| CHAP | Challenge Handshake Authentication Protocol | Yes | Slightly stronger than PAP, still exposed |
| MS-CHAP / MS-CHAPv2 | Microsoft CHAP | Yes | Common in Windows environments |
| EAP-MD5 | EAP with MD5 | Yes | Deprecated; avoid entirely |
| PEAP (MSCHAPv2 inner) | Protected EAP | No (EAP tunnel protects) | Requires correct server cert validation |
| EAP-TLS | EAP with TLS | No | Recommended gold standard |
| EAP-TTLS | EAP Tunnelled TLS | No | Acceptable alternative |
The critical distinction is that EAP-based methods establish their own cryptographic tunnel for authentication, which is not reliant on the MD5 Response Authenticator. This makes them immune to the specific Blast-RADIUS attack vector.
Why VLAN Segmentation Is Not Sufficient
A common misconception is that isolating RADIUS traffic in a dedicated management VLAN provides adequate protection. While network segmentation is a sound security practice, it does not eliminate the Blast-RADIUS risk. An attacker who has already compromised a device on the management network — through a phishing attack, a supply-chain compromise, or exploitation of another vulnerability — can position themselves as a MitM on the RADIUS traffic path. The attack requires only network-path access, not external internet access. Segmentation reduces the attack surface but does not eliminate the underlying cryptographic weakness.
Implementation Guide
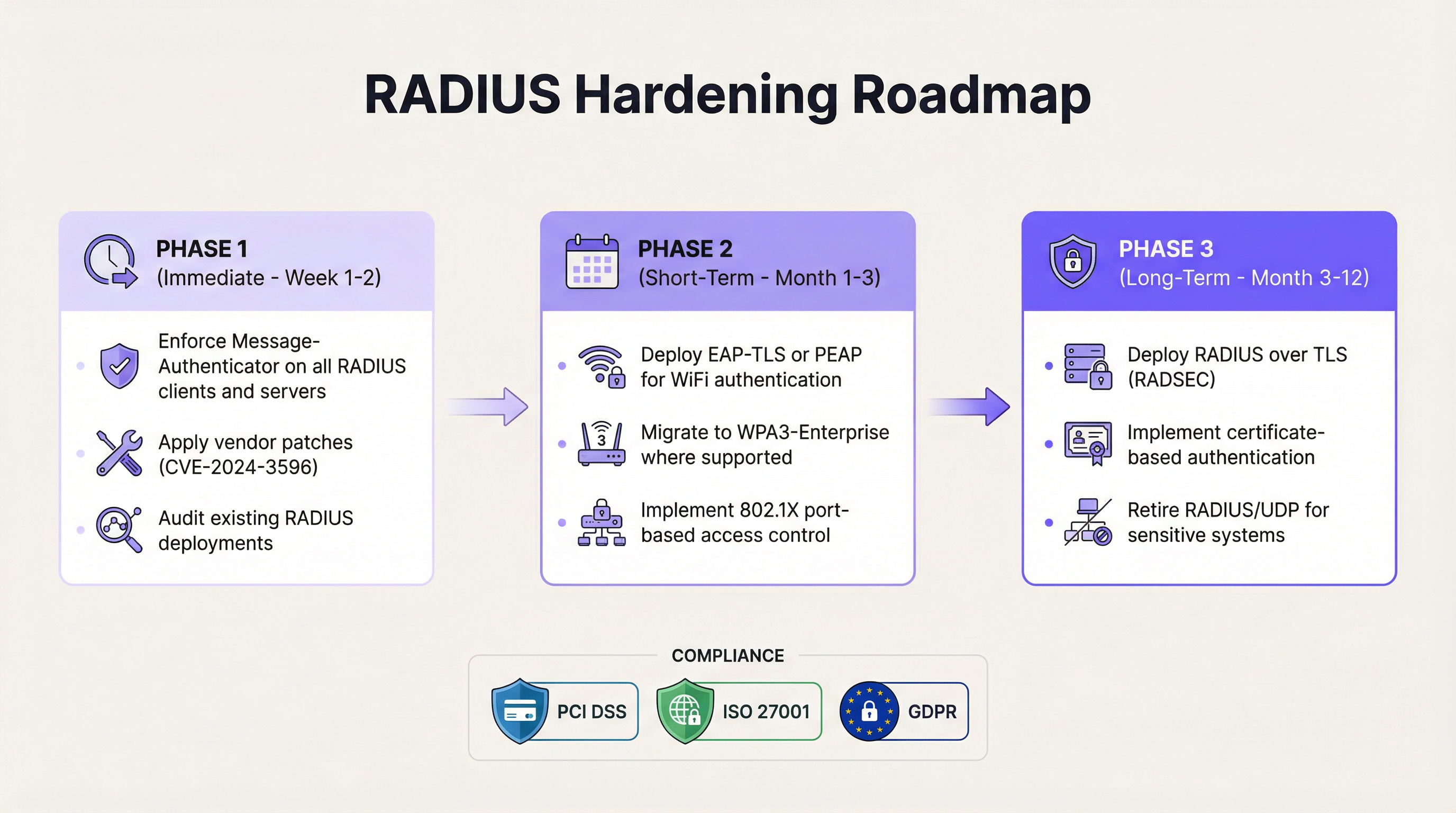
Phase 1: Immediate Hardening (Weeks 1–2)
The first priority is to apply vendor patches for CVE-2024-3596 across all RADIUS infrastructure. All major vendors — including Cisco ISE, Microsoft NPS, FreeRADIUS, Juniper, Aruba, and Ruckus — have released updates. Alongside patching, the critical configuration change is to enforce the Message-Authenticator attribute on all RADIUS clients and servers.
The Message-Authenticator attribute (defined in RFC 2869) provides an HMAC-MD5 integrity check over the entire RADIUS packet. Unlike the Response Authenticator, this construction is not vulnerable to the chosen-prefix collision attack because the HMAC construction binds the hash to the shared secret in a way that prevents the attacker from crafting a valid forgery. Configuring clients and servers to require this attribute — and to reject any message that does not include it — closes the immediate attack vector.
For FreeRADIUS, this involves setting require_message_authenticator = yes in the clients.conf file. For Microsoft NPS, the equivalent policy is enforced through the Network Policy settings. For Cisco ISE, the setting is available in the RADIUS client configuration under the authentication policy. Consult your vendor's specific advisory for CVE-2024-3596 for exact configuration steps.
Phase 2: Authentication Modernisation (Months 1–3)
The medium-term objective is to migrate WiFi authentication from legacy PAP/CHAP modes to EAP-based methods. For enterprise WiFi environments, the recommended path is WPA3-Enterprise with EAP-TLS. This requires deploying a Public Key Infrastructure (PKI) to issue device and/or user certificates, configuring your RADIUS server to validate these certificates, and provisioning client devices with the appropriate certificates and RADIUS server trust anchors.
For environments where certificate deployment is complex — such as venues with high device turnover or BYOD policies — PEAP with MSCHAPv2 provides an acceptable interim step, provided that clients are configured to validate the RADIUS server certificate. Without server certificate validation, PEAP is vulnerable to rogue access point attacks. IEEE 802.1X port-based access control should be implemented on wired infrastructure simultaneously to ensure consistent authentication policy across the network.
Phase 3: Transport Layer Security (Months 3–12)
The long-term architectural goal is to encapsulate all RADIUS traffic within a TLS tunnel using RADIUS over TLS (RADSEC), standardised in RFC 6614. RADSEC replaces UDP with TCP and wraps the entire RADIUS session in a mutually authenticated TLS connection. This provides confidentiality, integrity, and replay protection for all authentication traffic, rendering the MD5 Response Authenticator irrelevant as the transport layer itself is cryptographically secure.
RADSEC is particularly valuable in distributed deployments — such as hotel chains, retail networks, or stadium environments — where RADIUS traffic may traverse intermediate network segments. The IETF is currently progressing RADIUS over TLS and DTLS to standards-track status, reflecting industry consensus that RADIUS/UDP should be deprecated for sensitive deployments.
Best Practices
The following vendor-neutral best practices reflect current industry standards and regulatory guidance for enterprise WiFi authentication security.
Enforce Message-Authenticator universally. Every RADIUS client and server in your estate should be configured to send and require the Message-Authenticator attribute. This is the single highest-impact, lowest-disruption action available today. Per the Blast-RADIUS research team's guidance, this attribute should appear as the first attribute in Access-Accept and Access-Reject responses.
Adopt EAP-TLS as the authentication standard. IEEE 802.1X with EAP-TLS provides mutual certificate-based authentication that is immune to the Blast-RADIUS attack class and aligns with NIST SP 800-120 recommendations for EAP methods in wireless network access. WPA3-Enterprise mandates 192-bit security mode with EAP-TLS for the highest security tier.
Rotate RADIUS shared secrets regularly. While the Blast-RADIUS attack does not require knowledge of the shared secret, strong, unique shared secrets (minimum 32 characters, randomly generated) reduce the risk from other attack classes. Secrets should be rotated at least annually and immediately upon any suspected compromise.
Implement RADIUS accounting and anomaly monitoring. RADIUS accounting logs provide an audit trail of authentication events. Monitoring for anomalous patterns — such as successful authentications from unexpected device types, MAC addresses, or at unusual times — can provide early warning of exploitation. Integrate RADIUS accounting with your SIEM for automated alerting.
Segment RADIUS traffic. While not a complete mitigation, placing RADIUS traffic in a dedicated management VLAN with strict ACLs reduces the population of devices that could be used as a MitM pivot point. Combine with network access control to ensure only authorised devices can reach the RADIUS server.
Align with PCI DSS requirements. PCI DSS v4.0 Requirement 8.6 mandates strong authentication for all accounts. Requirement 1.3 requires network segmentation controls. Organisations processing payment card data must ensure their WiFi authentication architecture meets these requirements, and the Blast-RADIUS vulnerability directly impacts compliance posture for any network segment in scope.
Troubleshooting & Risk Mitigation
Common Failure Modes During Hardening
The most frequent issue encountered when enforcing Message-Authenticator is legacy device incompatibility. Older access points, switches, or VPN concentrators may not support the attribute, causing authentication failures after the server is configured to require it. The recommended approach is to audit all RADIUS clients before enforcing the requirement server-side, and to maintain a list of devices that require firmware updates or replacement.
A second common issue is certificate validation failures during EAP-TLS migration. If client devices are not provisioned with the correct RADIUS server certificate trust anchor, they will reject the server certificate and fail authentication. This is particularly prevalent in BYOD environments. Deploying a Mobile Device Management (MDM) solution to push certificate profiles is the standard resolution.
Shared secret mismatches can occur during RADSEC migration if the TLS certificate Common Name does not match the expected client identifier. Ensure that certificate subject names are consistent with the RADIUS client IP addresses or hostnames configured on the server.
Risk Mitigation for Environments That Cannot Immediately Patch
For environments where immediate patching is not feasible — such as legacy industrial control systems or embedded network devices — the risk can be partially mitigated by implementing strict network access controls that limit which hosts can communicate with the RADIUS server, reducing the opportunity for a MitM attacker to intercept traffic. This is a temporary measure only; a patching and replacement roadmap must be established.
ROI & Business Impact
Quantifying the Risk
The business case for RADIUS hardening is straightforward when framed in terms of breach cost and compliance liability. A successful Blast-RADIUS exploit in a hotel or retail environment could provide an attacker with access to the corporate network, potentially reaching point-of-sale systems, guest data repositories, and back-office infrastructure. The average cost of a data breach in the hospitality sector exceeds £3 million, according to industry benchmarks, with regulatory fines under GDPR potentially adding up to 4% of global annual turnover.
For organisations in scope for PCI DSS, a network authentication failure that results in cardholder data exposure can trigger mandatory forensic investigations, card brand fines, and potential loss of card processing privileges — costs that far exceed the investment required to implement EAP-TLS and RADSEC.
Implementation Cost Benchmarks
The following table provides indicative cost and effort estimates for the three-phase hardening roadmap across typical venue environments:
| Phase | Action | Estimated Effort | Estimated Cost | Risk Reduction |
|---|---|---|---|---|
| Phase 1 | Patch + enforce Message-Authenticator | 1–3 days (IT team) | Staff time only | High (closes immediate CVE) |
| Phase 2 | EAP-TLS / WPA3-Enterprise migration | 2–6 weeks | PKI + MDM licensing | Very High |
| Phase 3 | RADSEC deployment | 4–12 weeks | Infrastructure upgrades | Comprehensive |
Operational Benefits Beyond Security
Migrating to EAP-TLS and RADSEC delivers operational benefits beyond security hardening. Certificate-based authentication eliminates the operational overhead of managing and rotating shared passwords across large device fleets. WPA3-Enterprise improves connection reliability in dense environments — a measurable benefit for stadiums and conference centres where hundreds of devices compete for authentication. RADSEC's TCP transport also provides better reliability than UDP in high-latency or lossy network conditions, improving the authentication experience for end users.

Key Terms & Definitions
RADIUS (Remote Authentication Dial-In User Service)
A client-server networking protocol (RFC 2865) that provides centralised authentication, authorisation, and accounting (AAA) for users connecting to a network. RADIUS clients (access points, switches, VPN concentrators) forward authentication requests to a central RADIUS server, which validates credentials and returns an Access-Accept or Access-Reject response.
IT teams encounter RADIUS as the authentication backbone for enterprise WiFi (802.1X), VPN access, and network device administration. Its age and architectural limitations are now a direct security liability under CVE-2024-3596.
MD5 Chosen-Prefix Collision Attack
A cryptographic attack against the MD5 hash function in which an attacker constructs two different messages with the same MD5 hash, where both messages begin with attacker-chosen prefixes. This is more powerful than a standard collision attack because the attacker can control the meaningful content of both colliding messages.
This is the specific attack technique used in Blast-RADIUS. The attacker uses it to forge a RADIUS Response Authenticator that the client will accept as genuine, even though the response content has been modified from Access-Reject to Access-Accept.
Response Authenticator
A 16-byte field in RADIUS response packets (Access-Accept, Access-Reject, Access-Challenge) computed as MD5(Code || ID || Length || RequestAuthenticator || Attributes || SharedSecret). It is intended to verify the integrity of the server response but is not a proper cryptographic MAC and is vulnerable to the Blast-RADIUS attack.
Network architects need to understand that the Response Authenticator is the specific field being forged in a Blast-RADIUS attack. Enforcing the Message-Authenticator attribute provides a stronger integrity check that is not vulnerable to the same collision technique.
Message-Authenticator Attribute
A RADIUS attribute (Attribute 80, defined in RFC 2869) that provides an HMAC-MD5 integrity check over the entire RADIUS packet, including all attributes. Unlike the Response Authenticator, the HMAC construction binds the integrity check to the shared secret in a way that prevents chosen-prefix collision forgery.
Enforcing the Message-Authenticator attribute on all RADIUS clients and servers is the primary short-term mitigation for CVE-2024-3596. IT teams should verify that all RADIUS infrastructure is patched and configured to require this attribute before accepting any response.
EAP-TLS (Extensible Authentication Protocol – Transport Layer Security)
An EAP method (RFC 5216) that uses TLS for mutual certificate-based authentication between the client and the RADIUS server. Both parties must present valid digital certificates from a trusted Certificate Authority. It is immune to the Blast-RADIUS attack and is the recommended gold standard for enterprise WiFi authentication.
CTOs and network architects should treat EAP-TLS as the target state for all enterprise WiFi authentication. It requires a PKI infrastructure but eliminates shared secrets, password-based attacks, and the MD5 vulnerability class entirely.
RADSEC (RADIUS over TLS)
A protocol extension (RFC 6614) that encapsulates RADIUS messages within a mutually authenticated TLS session over TCP, replacing the traditional UDP transport. RADSEC provides confidentiality, integrity, and replay protection for all RADIUS traffic, making transport-layer attacks such as Blast-RADIUS impossible.
RADSEC is the long-term architectural solution for RADIUS security. It is particularly valuable in distributed deployments (hotel chains, retail networks) where RADIUS traffic traverses multiple network segments. Vendors including Cisco, Juniper, Aruba, and FreeRADIUS support RADSEC.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism for devices wishing to connect to a LAN or WLAN. It uses EAP as the authentication framework and RADIUS as the backend authentication server. 802.1X ensures that only authenticated devices can access network resources.
802.1X is the framework within which RADIUS and EAP operate for enterprise WiFi. IT managers implementing WPA2/WPA3-Enterprise are deploying 802.1X. Understanding this relationship is essential for configuring authentication policies and troubleshooting access issues.
WPA3-Enterprise
The enterprise variant of the Wi-Fi Protected Access 3 (WPA3) security standard, which mandates 802.1X authentication and, in its highest security mode (192-bit), requires EAP-TLS with a 384-bit elliptic curve cipher suite. WPA3-Enterprise provides significantly stronger security guarantees than WPA2-Enterprise and is immune to the Blast-RADIUS attack when correctly configured.
Network architects planning new WiFi deployments or major infrastructure refreshes should specify WPA3-Enterprise as the minimum security standard. It is supported by all modern access points and client devices manufactured after 2020.
Man-in-the-Middle (MitM) Attack
An attack in which the adversary secretly intercepts and potentially alters communications between two parties who believe they are communicating directly with each other. In the context of Blast-RADIUS, the MitM is positioned between the RADIUS client (access point) and the RADIUS server, enabling them to intercept and forge authentication responses.
The Blast-RADIUS attack requires MitM positioning. This is achievable through ARP spoofing on a shared network segment, compromise of an intermediate network device, or physical access to network infrastructure. Understanding this threat model helps IT teams prioritise network segmentation and device hardening alongside RADIUS-specific mitigations.
Case Studies
A 350-room luxury hotel chain with 12 properties is running Cisco Meraki access points with Microsoft NPS as the RADIUS server for staff WiFi. Authentication is via MSCHAPv2. The IT director has been alerted to CVE-2024-3596 and needs to assess exposure and implement mitigations without disrupting the 24/7 hotel operations.
The immediate priority is to confirm that Microsoft NPS has been updated to include the Message-Authenticator enforcement patch (released July 2024). In NPS, navigate to the RADIUS Clients and Servers configuration and enable the 'Require Message-Authenticator' setting for all configured RADIUS clients. On the Meraki side, confirm that the firmware version supports sending the Message-Authenticator attribute in Access-Request packets — Meraki released a firmware update addressing CVE-2024-3596 in Q3 2024. This configuration change can be deployed during a low-traffic window (typically 03:00–05:00 local time) with minimal guest impact, as it affects only staff authentication. Once Phase 1 is stable, plan the migration from MSCHAPv2 to EAP-TLS. Deploy a Microsoft Active Directory Certificate Services (ADCS) PKI to issue computer certificates to all staff devices via Group Policy. Configure NPS with an EAP-TLS network policy and update the Meraki SSID security settings to WPA2/WPA3-Enterprise with EAP-TLS. Use Meraki's Systems Manager MDM to push the NPS server certificate trust anchor to all managed devices. Roll out property-by-property to manage risk, starting with the lowest-occupancy property.
A national retail chain with 200 stores uses a centralised FreeRADIUS server for 802.1X authentication on its store network infrastructure. Each store has a mix of managed corporate devices (Windows laptops, handheld scanners) and unmanaged IoT devices (digital signage, payment terminals). The network team needs to harden against Blast-RADIUS while maintaining PCI DSS compliance for the payment card environment.
Begin with a network segmentation audit to confirm that RADIUS traffic between store access points and the central FreeRADIUS server is isolated from the payment card data environment (CDE). If RADIUS traffic traverses any segment that is in PCI DSS scope, this must be addressed as a priority. Update FreeRADIUS to version 3.2.3 or later, which includes the Message-Authenticator enforcement fix. In the FreeRADIUS clients.conf file, add 'require_message_authenticator = yes' for all store RADIUS clients. For the managed device fleet, deploy EAP-TLS using an existing PKI or a cloud certificate authority. For unmanaged IoT devices that cannot support 802.1X, implement MAC Authentication Bypass (MAB) on a separate, isolated VLAN with strict firewall rules preventing lateral movement to the CDE. This ensures that even if an IoT device's MAC address is spoofed, the attacker gains access only to the IoT VLAN, not the corporate or payment network. For the RADSEC migration, deploy a RADSEC proxy at each store that terminates the local UDP RADIUS traffic and forwards it over TLS to the central FreeRADIUS server, avoiding the need to upgrade every store's network device firmware simultaneously.
Scenario Analysis
Q1. Your organisation operates a 500-seat conference centre that hosts corporate events. The venue WiFi uses WPA2-Enterprise with PEAP/MSCHAPv2 and a FreeRADIUS server. A security consultant has flagged CVE-2024-3596 in their report. The venue director wants to know: (a) Are you currently vulnerable? (b) What is the minimum action required to close the immediate risk? (c) What is the recommended long-term architecture?
💡 Hint:Consider whether PEAP provides immunity to Blast-RADIUS, and what conditions must be met for that immunity to hold. Also consider the operational constraints of a 24/7 venue environment when planning the remediation timeline.
Show Recommended Approach
(a) PEAP with MSCHAPv2 uses an EAP tunnel that protects the inner authentication from the Blast-RADIUS attack, so you are not directly vulnerable to CVE-2024-3596 — provided that clients are correctly configured to validate the FreeRADIUS server certificate. If certificate validation is not enforced, you are vulnerable to rogue access point attacks, which is a separate but equally serious risk. You should still update FreeRADIUS to the patched version and enforce Message-Authenticator as a defence-in-depth measure. (b) The minimum immediate action is to update FreeRADIUS to version 3.2.3 or later and enforce Message-Authenticator in clients.conf. Simultaneously, audit all client devices to confirm server certificate validation is enabled. (c) The recommended long-term architecture is WPA3-Enterprise with EAP-TLS, backed by a PKI for certificate issuance. For a conference centre with high device turnover and BYOD, consider a cloud-based certificate authority with automated provisioning to reduce the operational burden of certificate management.
Q2. A retail chain's security team has completed a RADIUS audit and identified three categories of devices on their store networks: (1) managed Windows laptops using MS-CHAP, (2) Android handheld scanners using PAP, (3) IoT digital signage devices that do not support 802.1X at all. Prioritise the remediation actions and explain the rationale for each device category.
💡 Hint:Consider the relative vulnerability of each authentication mode, the feasibility of migrating each device category to EAP, and the appropriate network architecture for devices that cannot support 802.1X.
Show Recommended Approach
All three categories require action, but the approach differs. Category 1 (Windows laptops, MS-CHAP): Highest priority for EAP-TLS migration because MS-CHAP is directly vulnerable to Blast-RADIUS. Deploy computer certificates via Group Policy and migrate to EAP-TLS within 30–60 days. Enforce Message-Authenticator immediately as an interim measure. Category 2 (Android scanners, PAP): Also directly vulnerable. PAP transmits credentials in a form that is trivially readable if the RADIUS traffic is intercepted, making this the highest-risk category from a credential exposure perspective as well. Migrate to PEAP or EAP-TLS using Android's built-in 802.1X support. If the scanner firmware does not support EAP, prioritise firmware updates or device replacement. Category 3 (IoT signage, no 802.1X): Cannot be migrated to EAP. Implement MAC Authentication Bypass (MAB) on a dedicated IoT VLAN with strict firewall rules preventing access to the corporate network or CDE. Accept that MAB provides weaker authentication (MAC addresses can be spoofed) and compensate with network monitoring and anomaly detection.
Q3. A CTO at a 50-property hotel chain asks you to present the business case for a full RADIUS modernisation programme (EAP-TLS + RADSEC) with an estimated budget of £180,000 over 12 months. She wants to understand: the risk being mitigated, the compliance benefits, and the operational ROI beyond security. How do you structure the business case?
💡 Hint:Frame the business case around three pillars: risk quantification (what is the cost of a breach?), compliance value (what fines or audit costs does this avoid?), and operational efficiency (what does this enable beyond security?). Use the 350-room hotel scenario as a reference point.
Show Recommended Approach
Structure the business case around three pillars. Risk Quantification: A successful Blast-RADIUS exploit at a single property could provide network access to guest PII, payment systems, and back-office infrastructure. The average hospitality data breach costs £3M+ in remediation, notification, and reputational damage. At 50 properties, the aggregate risk is significant. The £180,000 investment represents less than 6% of a single breach cost. Compliance Value: PCI DSS v4.0 requires strong authentication for all systems in scope. EAP-TLS and RADSEC directly satisfy Requirements 8.6 (authentication management) and 1.3 (network segmentation). Avoiding a PCI DSS Level 1 forensic investigation (typically £50,000–£150,000) and potential card brand fines justifies the programme cost. GDPR Article 32 requires 'appropriate technical measures' — a documented modernisation programme demonstrates compliance due diligence. Operational ROI: Certificate-based authentication eliminates the overhead of managing shared WiFi passwords across 50 properties (estimated 2–4 hours per property per year for rotation and distribution). WPA3-Enterprise improves connection reliability in high-density environments, directly improving guest satisfaction scores. RADSEC's TCP transport reduces authentication failures in properties with high-latency WAN connections. Combined, these operational benefits represent an estimated 200–300 IT hours per year in saved administration time.
Key Takeaways
- ✓CVE-2024-3596 ('Blast-RADIUS') is a practically exploitable vulnerability in RADIUS/UDP that allows a man-in-the-middle attacker to forge authentication approvals without knowing user credentials, affecting all PAP, CHAP, and MS-CHAP deployments.
- ✓The attack exploits the MD5-based Response Authenticator field in RADIUS responses using a chosen-prefix collision technique that can be executed in minutes on modern hardware — making this a real operational threat, not a theoretical one.
- ✓The immediate mitigation is to apply vendor patches for CVE-2024-3596 and enforce the Message-Authenticator attribute on all RADIUS clients and servers — a low-disruption configuration change available from all major vendors including Cisco, Microsoft NPS, FreeRADIUS, Aruba, and Ruckus.
- ✓EAP-based authentication methods (EAP-TLS, PEAP, EAP-TTLS) are immune to the Blast-RADIUS attack, making migration to WPA3-Enterprise with EAP-TLS the recommended medium-term strategic response.
- ✓RADIUS over TLS (RADSEC, RFC 6614) is the long-term architectural solution, encapsulating all RADIUS traffic in a mutually authenticated TLS tunnel and eliminating the transport-layer vulnerability entirely.
- ✓For hospitality, retail, and venue operators, the compliance implications are direct: a successful exploit can trigger PCI DSS violations, GDPR data breach notifications, and significant financial and reputational damage that far exceeds the cost of remediation.
- ✓Network segmentation (dedicated RADIUS VLANs) reduces the attack surface but does not eliminate the vulnerability — it must be combined with Message-Authenticator enforcement and EAP migration to provide genuine protection.



