WPA2 vs WPA3: What's the Difference and Should You Upgrade?
This guide provides IT managers, network architects, and venue operations directors with a definitive, actionable comparison of WPA2 and WPA3 WiFi security protocols. It explains the critical technical differences — including SAE authentication, Perfect Forward Secrecy, and Enhanced Open — and outlines a practical, phased migration strategy using WPA3 Transition Mode. The guide is essential for any organisation operating guest or staff WiFi in hospitality, retail, events, or public-sector environments who needs to understand the upgrade case, manage device compatibility, and align their wireless security posture with modern compliance requirements.
🎧 Listen to this Guide
View Transcript
Executive Summary
For over a decade, WPA2 has been the baseline for enterprise WiFi security. However, its inherent vulnerabilities — susceptibility to offline dictionary attacks and the KRACK (Key Reinstallation Attack) exploit — now present a tangible and actively-exploited risk to organisations. WPA3, the next-generation security protocol certified by the Wi-Fi Alliance in 2018, directly addresses these flaws by introducing robust authentication with Simultaneous Authentication of Equals (SAE), stronger encryption via GCMP-256, and mandatory Protected Management Frames (PMF). This guide provides a practical, actionable comparison of WPA2 and WPA3 for IT leaders and network architects in hospitality, retail, and large-venue environments. It outlines the business case for upgrading, details a strategic transition path using WPA3 Transition Mode, and offers vendor-neutral best practices to ensure a secure, high-performance wireless network that meets modern compliance and guest experience demands. The key takeaway is that migrating to WPA3 is no longer a question of if, but how — and a phased, strategic approach is the most effective path to mitigating risk and future-proofing your infrastructure.
Technical Deep-Dive
The transition from WPA2 to WPA3 represents a significant architectural shift in wireless security. Understanding the underlying technical differences is crucial for network architects and IT managers to make informed deployment decisions. While WPA2 has been a resilient standard, WPA3 was engineered to neutralise specific, well-documented attack vectors and to provide a more secure foundation for the next decade of wireless connectivity.
Authentication: From PSK to SAE
The most fundamental change between WPA2-Personal and WPA3-Personal is the authentication mechanism. WPA2 uses a Pre-Shared Key (PSK) combined with a 4-way handshake. While effective at the time of its design, this method is vulnerable to offline dictionary attacks. An attacker can passively capture the handshake and then use computational power to guess the password offline, without any further interaction with the network. This makes networks secured with weak or moderately complex passwords highly susceptible to compromise.
WPA3 replaces PSK with Simultaneous Authentication of Equals (SAE), also known as the Dragonfly Key Exchange. SAE is a password-authenticated key agreement protocol that is resistant to offline dictionary attacks. During the authentication process, the password is never exchanged directly. Instead, both the client and the access point use the password to generate cryptographic hashes, which are then exchanged to prove mutual knowledge of the key. An attacker capturing this exchange cannot use it to brute-force the password offline. Any password-guessing attempt must be an active, online attack — far slower and far easier to detect and block.
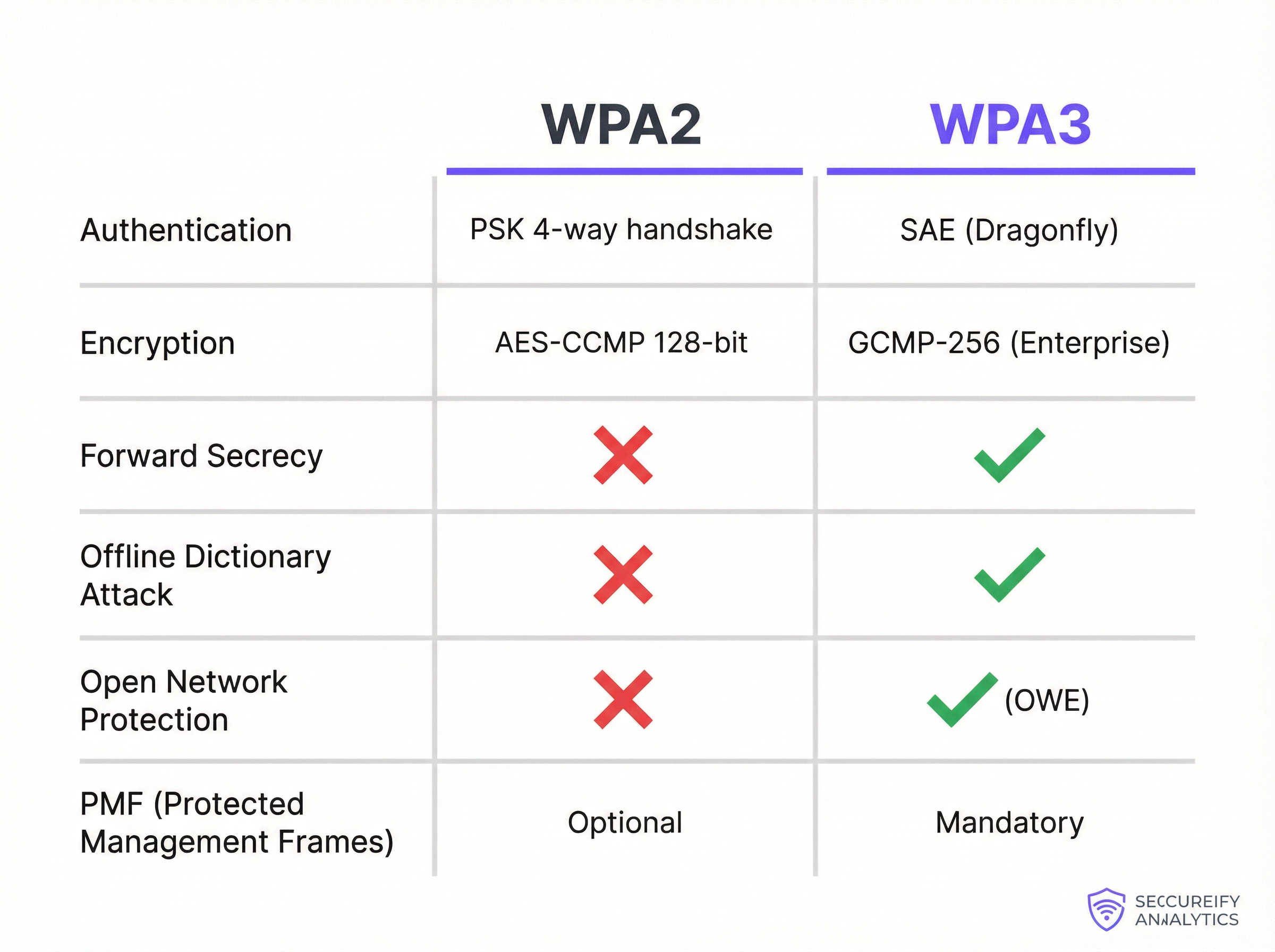
Encryption, Key Management, and Forward Secrecy
WPA2-Enterprise utilises AES-CCMP with 128-bit encryption, which has been considered secure for many years. WPA3-Enterprise raises the bar significantly, offering an optional 192-bit security mode aligned with the Commercial National Security Algorithm (CNSA) suite. This provides a cryptographic posture required for government, defence, and other high-security environments.
More broadly, WPA3 introduces Perfect Forward Secrecy (PFS). With WPA2, if an attacker compromises the network password, they could potentially decrypt past traffic that they had previously captured and stored. WPA3 with SAE ensures that each session has a unique, ephemeral encryption key. Even if a key from a single session is compromised, it cannot be used to decrypt any previous or future sessions — dramatically reducing the blast radius of any potential breach.
Protection for Open Networks: Enhanced Open (OWE)
In public-facing venues such as hotels, airports, and retail stores, open (password-free) WiFi networks are common for guest access. On a traditional open network, all traffic is transmitted in plaintext, making every user vulnerable to passive eavesdropping from anyone else on the same network. WPA3 addresses this with Enhanced Open, which implements Opportunistic Wireless Encryption (OWE). OWE automatically creates an individual, encrypted tunnel between each user and the access point, even on a network with no password. This provides meaningful privacy without adding any friction to the connection process — a critical improvement for guest WiFi deployments at scale.
Protected Management Frames (PMF)
Management frames govern how WiFi devices manage their connections, including association and disassociation. In WPA2, these frames are unprotected, which allows an attacker to spoof them to forcibly de-authenticate a legitimate user, enabling denial-of-service or man-in-the-middle attacks. While PMF (defined in IEEE 802.11w) was optional under WPA2, WPA3 mandates the use of Protected Management Frames, ensuring the integrity and authenticity of these critical control messages and protecting the overall stability of the wireless connection.
Implementation Guide
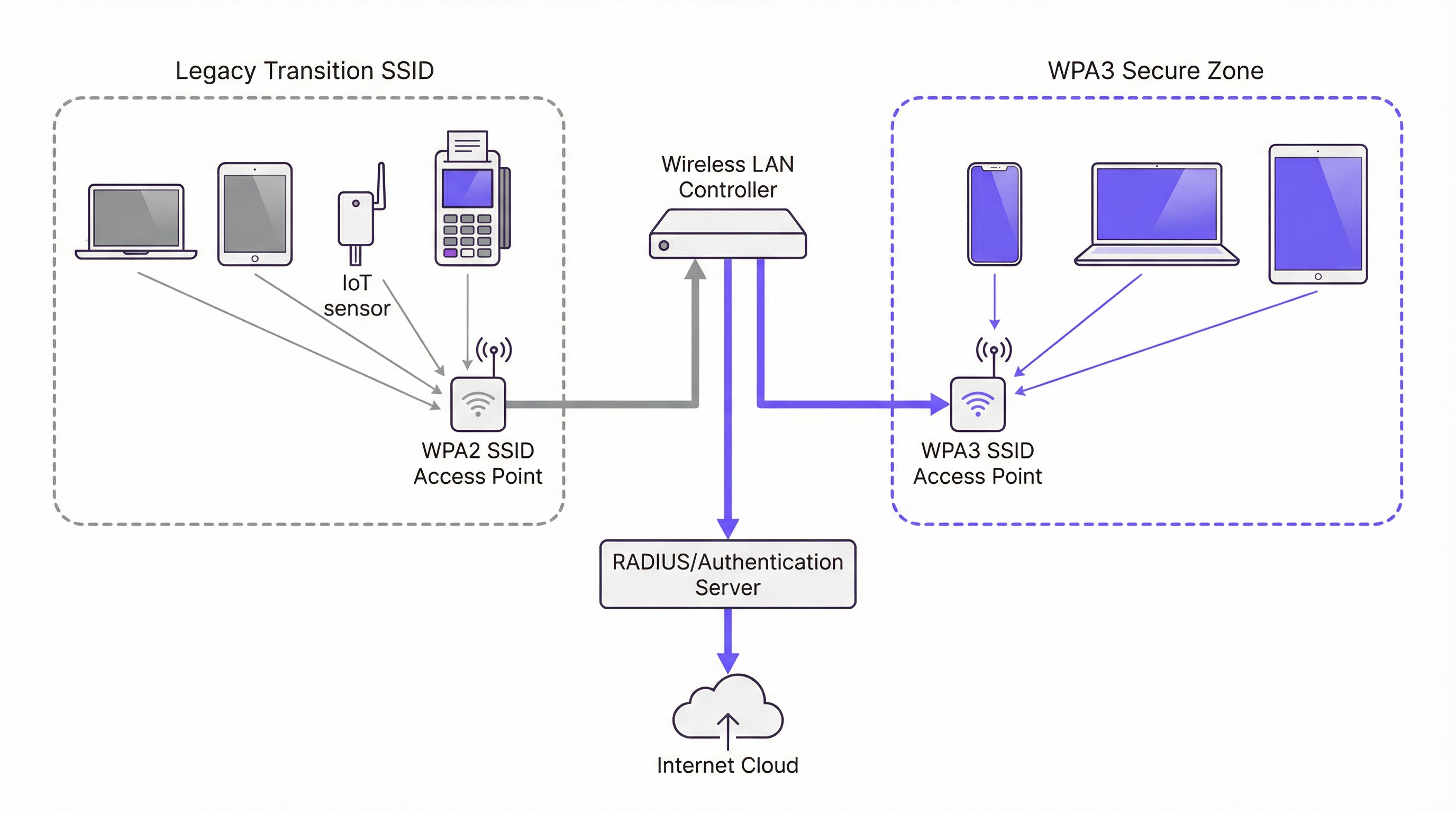
Migrating an enterprise network from WPA2 to WPA3 is not a simple switch-flip but a strategic project that requires careful planning and execution. The goal is to enhance security while minimising disruption to business operations and user experience. A phased approach is almost always the recommended path.
Phase 1 — Infrastructure and Device Audit. The first step is a comprehensive audit of your entire wireless ecosystem. For access points, identify the make, model, and firmware version of all units and check the manufacturer's documentation for WPA3 support. Most enterprise-grade APs sold since 2019 support WPA3, but a firmware upgrade is typically required. If you use a controller-based architecture, ensure the controller software is updated to a version that supports WPA3 configuration and management. The most critical and challenging part of the audit is the client device inventory. You must catalogue every device connecting to your WiFi network — corporate laptops, smartphones, BYOD devices, and special-purpose hardware like Point-of-Sale (POS) terminals, barcode scanners, IoT sensors, and smart building components.
Phase 2 — Enable WPA3/WPA2 Transition Mode. A full, immediate cutover to WPA3 is not practical for most organisations due to the diversity of client devices. The industry-standard solution is to use WPA3/WPA2 Mixed Mode, also called Transition Mode. In this configuration, the same SSID is broadcast with support for both WPA3 and WPA2 authentication. WPA3-capable clients automatically negotiate and connect using the more secure protocol; legacy clients connect using WPA2. This allows for a seamless user experience during the migration period. In your wireless LAN controller or AP management interface, you will typically find a security setting for your SSID that allows you to select "WPA3+WPA2-Enterprise" or a similar mixed-mode option.
Phase 3 — Create WPA3-Only Secure Zones. As your client device population becomes increasingly WPA3-capable, begin creating WPA3-only SSIDs for specific user groups or device types. Prioritise the devices and users that handle the most sensitive data. For example, create a WPA3-only SSID for the finance department or for corporate executive devices, then use your device management platform to push new network profiles to capable devices, gradually reducing your reliance on the mixed-mode SSID.
Phase 4 — Isolate and Manage Legacy Devices. Inevitably, you will have a long tail of legacy devices that do not support WPA3. Create a separate, dedicated SSID configured for WPA2-only, firewalled from the rest of the corporate network with strict access rules. Simultaneously, develop a hardware refresh lifecycle plan to phase out non-compliant devices over time. For every new device purchase, mandate WPA3 support as a procurement requirement.
Best Practices
The following table summarises the key industry-standard recommendations for a secure WPA3 deployment, drawing on guidance from IEEE 802.1X, Wi-Fi Alliance specifications, and PCI DSS v4.0 requirements.
| Best Practice | Rationale | Priority |
|---|---|---|
| Mandate 802.1X for all corporate SSIDs | Eliminates shared passwords; provides per-user accountability and centralised policy control via RADIUS. | Critical |
| Implement EAP-TLS (certificate-based auth) | Removes password-based attack surface entirely; certificates cannot be phished. | High |
| Enable PMF on all WPA2 networks | Protects against de-authentication and disassociation attacks even before full WPA3 migration. | High |
| Disable legacy data rates (< 6 Mbps) | Removes compatibility with the oldest, least secure clients and improves overall airtime efficiency. | Medium |
| Segment IoT and guest traffic onto dedicated VLANs | Limits the blast radius of any compromise on a legacy device or open network. | Critical |
| Establish a firmware update cadence | Ensures known vulnerabilities are patched promptly across APs and controllers. | High |
| Mandate WPA3 in all new hardware procurement | Prevents accumulation of technical debt and accelerates the migration timeline. | High |
Troubleshooting & Risk Mitigation
Deploying WPA3 can introduce new challenges. The most common failure mode is client connectivity, where devices with outdated wireless drivers or operating systems fail to negotiate a WPA3 connection. The solution is almost always to ensure the latest drivers and OS updates are applied before enabling WPA3. Testing with a representative sample of device types before a broad rollout is a non-negotiable step in any responsible deployment plan.
Performance degradation is another concern, though in practice it is rarely caused by WPA3 itself. More often, it results from misconfigured access points or buggy firmware versions. Validating new firmware in a lab environment before production deployment, and closely monitoring key metrics such as latency, packet drop rates, and retransmission counts after any configuration change, will allow you to identify and resolve issues quickly.
The most persistent challenge is managing IoT and headless devices that lack the sophisticated supplicants of modern operating systems. These devices should be isolated on a dedicated, hardened WPA2-only SSID with strict firewall rules. This is not a permanent solution but a risk-containment measure while a replacement plan is developed and executed.
ROI & Business Impact
The ROI of a WPA3 upgrade is primarily driven by risk mitigation. The vulnerabilities in WPA2 are actively exploited, and a successful attack on a wireless network can lead to data exfiltration, reputational damage, and significant compliance penalties under frameworks such as PCI DSS v4.0 and GDPR. The cost of a single breach — encompassing forensic investigation, legal fees, customer notification, and regulatory fines — can easily reach hundreds of thousands of pounds. The investment in a WPA3-capable infrastructure is a fraction of this potential cost.
Beyond risk, there is a direct impact on guest experience and brand trust. In public-facing venues, the security of guest WiFi is part of the brand promise. WPA3 Enhanced Open allows venues to provide seamless, password-free access while ensuring each user's traffic is encrypted and isolated from other users on the same network. This builds trust and enhances the overall guest experience without adding operational complexity.
Finally, WPA3 is a future-proofing investment. It is the security foundation for WiFi 6, 6E, and WiFi 7. Delaying the transition only accumulates technical debt, making the eventual migration more complex and costly. A strategic, phased upgrade to WPA3 is a fiscally responsible approach to long-term network architecture planning that delivers compounding returns over the lifecycle of the infrastructure investment.
Key Terms & Definitions
SAE (Simultaneous Authentication of Equals)
A password-authenticated key agreement protocol, also known as the Dragonfly handshake, that replaces WPA2's Pre-Shared Key (PSK) mechanism. SAE prevents offline dictionary attacks by ensuring the password is never transmitted or exposed during the authentication process. Both parties prove knowledge of the password through cryptographic exchange, making passive capture of the handshake useless to an attacker.
IT teams encounter SAE when configuring WPA3-Personal SSIDs. It is the primary reason WPA3-Personal is significantly more secure than WPA2-PSK and is the first capability to verify when assessing WPA3 readiness.
GCMP-256 (Galois/Counter Mode Protocol, 256-bit)
The encryption cipher used in WPA3-Enterprise's 192-bit security mode. GCMP-256 provides both data confidentiality and data integrity (authentication) in a single, highly efficient operation. It is aligned with the Commercial National Security Algorithm (CNSA) suite and represents a significant improvement over WPA2's AES-CCMP-128.
Relevant for network architects designing networks for government, defence, financial services, or healthcare environments where regulatory requirements mandate the highest available encryption standards.
Perfect Forward Secrecy (PFS)
A cryptographic property that ensures each communication session uses a unique, ephemeral encryption key. If a session key is compromised, it cannot be used to decrypt any past or future sessions. WPA3 achieves PFS through the SAE handshake, which generates a unique Pairwise Master Key (PMK) for each session.
Critical for environments where sensitive data is transmitted over WiFi and where the threat of 'capture now, decrypt later' attacks is a concern. PFS is a key differentiator between WPA2 and WPA3 from a data protection standpoint.
OWE (Opportunistic Wireless Encryption)
A WiFi security mechanism defined in RFC 8110 and implemented in WPA3 as 'Enhanced Open'. OWE automatically establishes an encrypted connection between each client and the access point on an open (password-free) network, providing individualised data encryption without any user interaction or credential exchange.
The standard configuration for guest and public WiFi in hospitality, retail, and venue environments. OWE allows operators to provide seamless connectivity while protecting users from passive eavesdropping, directly addressing a long-standing privacy concern with traditional open networks.
PMF (Protected Management Frames)
A security mechanism defined in IEEE 802.11w that encrypts and authenticates WiFi management frames, such as de-authentication and disassociation frames. Without PMF, an attacker can spoof these frames to forcibly disconnect legitimate users from the network. PMF is optional in WPA2 but mandatory in WPA3.
IT teams should enable PMF on all WPA2 networks as a hardening measure, even before migrating to WPA3. It is a simple configuration change that provides meaningful protection against denial-of-service attacks.
WPA3 Transition Mode
A mixed-mode SSID configuration that simultaneously supports both WPA3 and WPA2 authentication on the same network name (SSID). WPA3-capable clients automatically negotiate and use the more secure WPA3 protocol; legacy WPA2-only clients connect using the older protocol. This is the primary mechanism for managing the migration from WPA2 to WPA3 in environments with mixed device populations.
The recommended starting point for any WPA3 migration. IT teams should enable transition mode on existing SSIDs as the first step, then monitor which devices are connecting via WPA2 to identify the remaining legacy device population.
802.1X / RADIUS Authentication
An IEEE standard for port-based network access control. In the context of enterprise WiFi, 802.1X uses a RADIUS (Remote Authentication Dial-In User Service) server to authenticate individual users or devices before granting network access. This provides per-user accountability and centralised access control, replacing the single shared password of PSK-based networks.
The mandatory authentication framework for any corporate WiFi network carrying sensitive data. Both WPA2-Enterprise and WPA3-Enterprise use 802.1X as their authentication layer. IT teams should use this in conjunction with EAP-TLS (certificate-based authentication) for the highest security posture.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A certificate-based WiFi authentication method that uses digital certificates on both the client and the authentication server to establish mutual trust, without requiring a password. EAP-TLS is considered the gold standard for enterprise WiFi authentication as it eliminates the risk of password phishing, credential theft, and brute-force attacks.
IT teams should prioritise EAP-TLS over password-based EAP methods (like PEAP-MSCHAPv2) for all corporate devices. It requires a Public Key Infrastructure (PKI) to manage and distribute certificates, but this investment is justified by the significant security improvement.
KRACK (Key Reinstallation Attack)
A vulnerability discovered in 2017 that exploits a flaw in the WPA2 four-way handshake. By manipulating and replaying cryptographic handshake messages, an attacker can force a victim's device to reinstall an already-in-use encryption key, causing nonce reuse and potentially allowing the attacker to decrypt, replay, or forge network packets. WPA3's SAE handshake is not susceptible to KRACK.
KRACK is a key reason for migrating to WPA3. While patches were released for many devices, not all devices received updates, and the underlying vulnerability is a structural weakness of the WPA2 handshake design. IT teams should treat unpatched devices as a significant risk.
Case Studies
A 450-room luxury hotel group with 12 properties needs to upgrade its guest and staff WiFi. The network currently runs WPA2-PSK for guests and WPA2-Enterprise for staff. The IT director is concerned about PCI DSS compliance for the payment systems on the staff network, and wants to improve guest privacy without adding a password requirement to the guest network. The estate includes a mix of Cisco Catalyst 9130 APs (WPA3-capable) and older Cisco 2800 series APs (WPA2-only). What is the recommended migration strategy?
The recommended approach is a phased, property-by-property migration that prioritises the highest-risk network segments first. For properties with Cisco 9130 APs, the immediate action is to update the controller software (Cisco IOS-XE) to a version that supports WPA3, then enable WPA3-Enterprise Transition Mode on the staff SSID. This allows WPA3-capable corporate devices to automatically use the more secure protocol while legacy devices continue to connect via WPA2-Enterprise. For the guest network, enable WPA3 Enhanced Open (OWE) on a new SSID. This provides automatic, per-user encryption for all guests without requiring a password, directly addressing the privacy concern. For properties with legacy Cisco 2800 APs, these units should be placed on a hardware refresh roadmap. In the interim, harden the existing WPA2-Enterprise configuration by ensuring 802.1X with EAP-TLS (certificate-based authentication) is in use for all staff devices. For PCI DSS compliance, ensure the payment systems are on a dedicated, isolated SSID or VLAN with the strictest possible access controls, and document the compensating controls in place while the hardware refresh is underway. The migration should be completed property by property, starting with the highest-revenue or highest-risk locations, to manage change and validate the configuration before a full estate rollout.
A national retail chain with 250 stores is preparing for a PCI DSS v4.0 audit. Each store has a mix of corporate WiFi (for staff devices and POS terminals) and guest WiFi (for customer-facing promotions and loyalty app connectivity). The IT security team has been told by the auditors that their current WPA2-PSK configuration for the staff network is a finding. The POS terminals are a mix of modern Android-based units (WPA3-capable) and older Windows CE-based units (WPA2-only). How should the IT team respond to the audit finding and plan the remediation?
The audit finding is valid. WPA2-PSK for a network carrying payment card data is a significant risk, as a single compromised password exposes the entire network. The immediate remediation for the staff network is to migrate from WPA2-PSK to WPA2-Enterprise with 802.1X authentication, using a RADIUS server (e.g., Cisco ISE, Aruba ClearPass, or a cloud-based RADIUS service). This provides per-device authentication and eliminates the shared password vulnerability. This action alone resolves the audit finding and is achievable without any hardware changes. In parallel, the team should audit all POS terminals and other staff devices for WPA3 capability. For the modern Android POS terminals, enable WPA3-Enterprise Transition Mode on the staff SSID. For the legacy Windows CE units, these must be placed on a dedicated, isolated SSID with WPA2-Enterprise and strict VLAN-based network segmentation, ensuring they can only communicate with the payment processing server and nothing else. For the guest network, implement WPA3 Enhanced Open to provide customer privacy. This also demonstrates a proactive security posture to the auditors, which is beneficial for the overall compliance assessment.
Scenario Analysis
Q1. A 20,000-seat stadium is deploying a new WiFi network for a major multi-day event. The network must support 15,000 concurrent guest connections and a separate staff network for 500 employees handling ticketing and point-of-sale. The IT team has a budget for new WiFi 6E access points. The event organiser wants to offer free, seamless WiFi to all attendees without a password. What security protocol configuration would you recommend for the guest and staff networks, and why?
💡 Hint:Consider the specific use case for each network segment. The guest network requires seamless access with privacy; the staff network requires strong authentication for PCI DSS compliance. WPA3 has specific features designed for each of these scenarios.
Show Recommended Approach
For the guest network, the correct configuration is WPA3 Enhanced Open (OWE). This provides automatic, per-user encrypted tunnels without requiring a password, delivering the seamless experience the organiser wants while protecting each attendee's traffic from eavesdropping by other users. A traditional open network would leave all guest traffic in plaintext. For the staff network, the configuration should be WPA3-Enterprise with 802.1X authentication using a RADIUS server. Since the staff are handling payment card data via POS terminals, this is a PCI DSS requirement. If the POS terminals support it, EAP-TLS (certificate-based authentication) is the preferred EAP method. The two networks should be on completely separate VLANs with strict firewall rules between them. Since the new APs are WiFi 6E, they will natively support WPA3, so no transition mode is required for a greenfield deployment.
Q2. An IT manager at a 50-store retail chain has just received a penetration test report showing that the WPA2-PSK password for the staff network was cracked using an offline dictionary attack. The password was 12 characters long and considered 'strong'. The manager needs to remediate the finding immediately. What is the most effective immediate action, and what is the longer-term strategic recommendation?
💡 Hint:The root cause is not the password strength — it is the use of PSK. Consider what authentication mechanism would eliminate this entire class of vulnerability, regardless of password complexity.
Show Recommended Approach
The immediate action is to change the PSK to a highly complex, randomly generated passphrase (at least 20 characters) to reduce the risk while the longer-term fix is implemented. However, the strategic recommendation is to migrate from WPA2-PSK to WPA2-Enterprise with 802.1X authentication. This eliminates the shared password entirely. Each device or user authenticates individually against a RADIUS server, and there is no single password to crack. The preferred EAP method is EAP-TLS, which uses digital certificates instead of passwords, making offline dictionary attacks impossible. In parallel, the team should assess the WPA3 readiness of their access points and begin planning a migration to WPA3-Enterprise, which provides the additional protection of SAE and Perfect Forward Secrecy. The key insight is that the problem is not the password strength but the use of a shared secret — 802.1X eliminates this vulnerability class entirely.
Q3. A large conference centre is planning to upgrade its WiFi infrastructure. The venue hosts events ranging from small corporate meetings to large trade shows with 5,000+ attendees. The IT team is evaluating whether to deploy WPA3-only, WPA2-only, or a mixed WPA3/WPA2 configuration. The venue's device inventory shows that 85% of client devices are modern smartphones and laptops that support WPA3, but 15% are older event management tablets and barcode scanners that only support WPA2. What is the recommended SSID architecture?
💡 Hint:Consider the different user groups and device types. A single SSID for all devices may not be the optimal solution. Think about how to provide the highest security for the majority while managing the risk of the legacy minority.
Show Recommended Approach
The recommended architecture is a three-SSID model. First, a WPA3-Enterprise SSID for staff corporate devices (the modern laptops and smartphones), providing the highest security with 802.1X authentication. Second, a WPA3 Enhanced Open SSID for event attendees and guests, providing seamless, encrypted public access. Third, a dedicated WPA2-Enterprise (or WPA2-PSK) SSID, isolated on its own VLAN with strict firewall rules, for the legacy event management tablets and barcode scanners. This architecture ensures that the 85% of capable devices get the full benefit of WPA3, while the legacy 15% are contained and managed without compromising the security of the rest of the network. The legacy SSID should be treated as a temporary measure, with a hardware refresh plan to replace the non-compliant devices within a defined timeframe. Using WPA3 Transition Mode on a single SSID is an alternative but less preferable option, as it means the entire SSID operates at WPA2 security levels for any client that connects via WPA2.
Key Takeaways
- ✓WPA3 replaces WPA2's vulnerable PSK 4-way handshake with SAE (Simultaneous Authentication of Equals), which completely eliminates offline dictionary attacks — the most common method used to crack WiFi passwords.
- ✓WPA3 introduces Perfect Forward Secrecy, ensuring that a compromised session key cannot be used to decrypt previously captured traffic, defeating 'steal now, decrypt later' attack strategies.
- ✓WPA3 Enhanced Open (OWE) provides automatic, per-user encrypted tunnels on open, password-free networks — the optimal configuration for guest WiFi in hotels, retail stores, and stadiums.
- ✓WPA3 Transition Mode is the recommended migration path: it allows a single SSID to support both WPA2 and WPA3 clients simultaneously, enabling a phased migration without disrupting legacy devices.
- ✓The most critical immediate action for any organisation still using WPA2-PSK on a corporate network is to migrate to 802.1X authentication — this eliminates the shared password vulnerability regardless of WPA version.
- ✓A comprehensive device audit is the non-negotiable first step in any WPA3 migration. Legacy IoT and headless devices that cannot support WPA3 must be isolated on dedicated, firewalled network segments.
- ✓WPA3 is the security foundation for WiFi 6, 6E, and WiFi 7. Mandating WPA3 support in all new hardware procurement is the most effective long-term strategy for managing the transition and preventing the accumulation of technical debt.



