Marketing a través del WiFi para invitados: La guía definitiva para captar leads, impulsar las ventas y mejorar la experiencia del cliente
This guide provides a technical deep-dive into leveraging guest WiFi for marketing, lead capture, and customer analytics. It offers actionable strategies for IT managers and venue operators to transform their WiFi from a cost centre into a powerful, ROI-driven marketing platform, covering architecture, implementation, and compliance.
🎧 Listen to this Guide
View Transcript
Resumen ejecutivo
El WiFi para invitados ya no es una simple comodidad; es un activo estratégico capaz de aportar un valor empresarial sustancial. Para los CTO, directores de TI y directores de recintos, es imperativo cambiar la percepción del WiFi para invitados: de un gasto operativo necesario a un motor proactivo de marketing y analítica. Esta guía proporciona un marco técnico y estratégico para lograr dicha transformación. Al implementar una solución de WiFi para invitados orientada al marketing, las organizaciones pueden capturar valiosos datos de clientes de origen (first-party data), comprender el comportamiento de los visitantes en los espacios físicos e impulsar campañas de marketing segmentadas que generen un retorno de la inversión (ROI) medible. Los componentes principales incluyen una infraestructura de red sólida, un Captive Portal sofisticado para la adquisición de datos y una integración perfecta con plataformas de CRM y automatización de marketing. Es fundamental que esto se ejecute dentro de un marco seguro y normativo, cumpliendo con estándares como WPA3 para la seguridad de la red y GDPR para la privacidad de los datos. El resultado es una potente herramienta que cierra la brecha entre el recorrido del cliente digital y físico, permitiendo experiencias personalizadas e impulsando los ingresos.
Análisis técnico en profundidad
La arquitectura de una solución de marketing a través del WiFi para invitados consta de tres capas principales: la Infraestructura de red, el Captive Portal y plataforma de marketing, y la Capa de integración y analítica.
Infraestructura de red: La base es su hardware de WiFi existente: puntos de acceso (AP), controladores y puertas de enlace (gateways). Para una analítica de ubicación eficaz, la densidad de AP debe ser suficiente para triangular con precisión las posiciones de los dispositivos. La segmentación de la red es primordial; el tráfico de invitados debe estar aislado de la red corporativa mediante VLAN (redes de área local virtuales) y reglas de firewall estrictas. Esto mitiga el riesgo de una brecha de seguridad originada en la red pública. El cumplimiento del estándar IEEE 802.1X para el control de acceso a la red basado en puertos y de WPA3 para un cifrado sólido es un requisito básico para la seguridad de nivel empresarial.
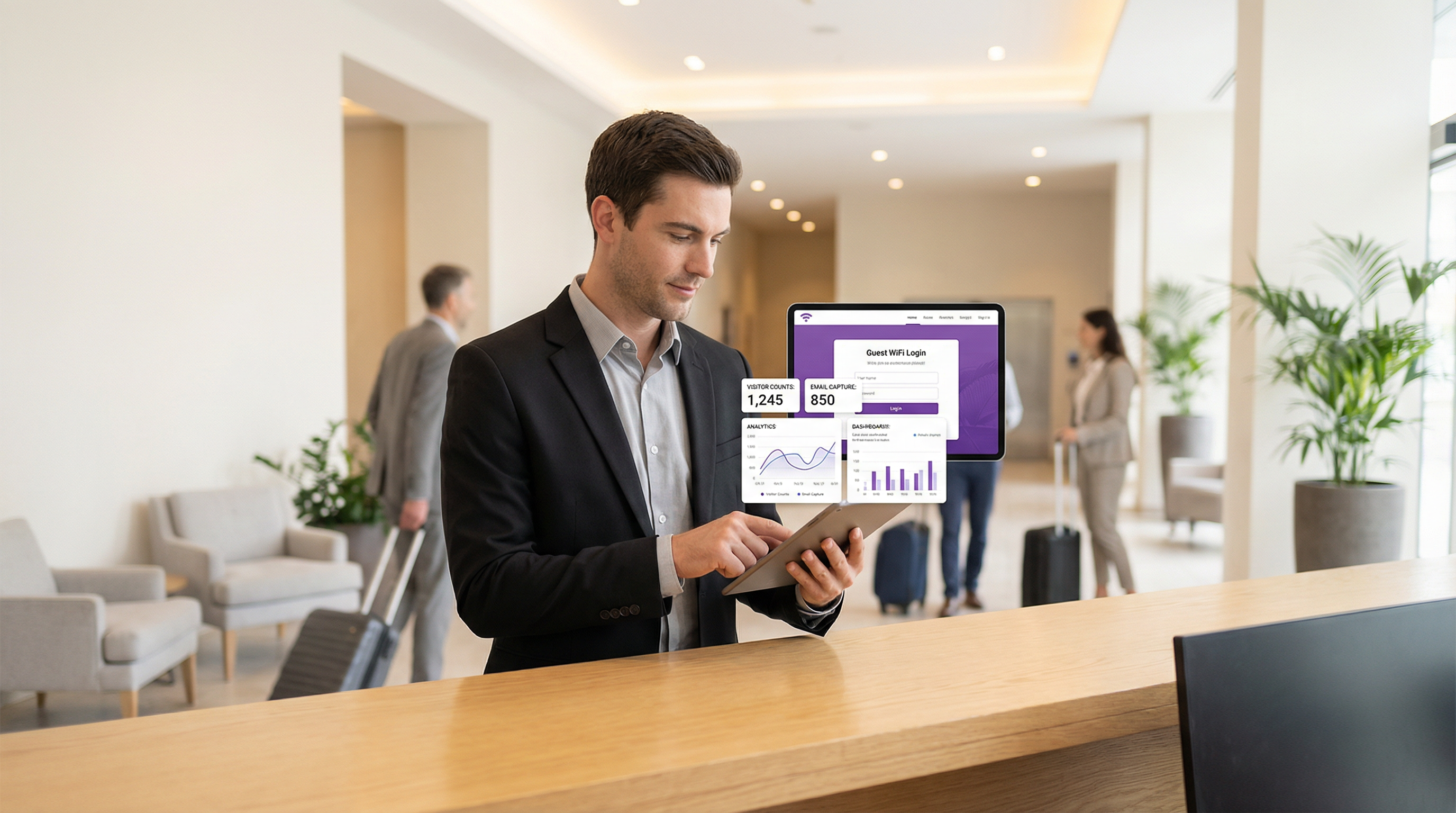
Captive Portal y plataforma de marketing: Esta es la capa de software que se sitúa sobre su hardware de red. Cuando un usuario se conecta al SSID de invitados, es redirigido a un Captive Portal. A diferencia de una simple página de introducción de contraseña, un portal de marketing ofrece múltiples métodos de autenticación:
- Correo electrónico/Relleno de formulario: El método más directo para la captación de leads.
- Inicio de sesión social: (p. ej., Google, LinkedIn, Facebook) Proporciona datos demográficos más completos y validados con el consentimiento del usuario.
- Cupón/Código de acceso: Permite el acceso por niveles y sesiones de tiempo limitado, algo habitual en el sector hotelero.
La plataforma captura estos datos, los vincula a la dirección MAC del dispositivo y los almacena en una base de datos centralizada. Aquí es donde se aplica el cumplimiento del GDPR y otras normativas de privacidad de datos a través de casillas de consentimiento explícito y enlaces claros a las políticas de privacidad.
- Capa de integración y analítica: El verdadero valor de los datos capturados se desbloquea mediante la integración. Utilizando Webhooks y una API REST, la plataforma de marketing por WiFi debe enviar datos en tiempo real a sistemas externos:
- Sistemas CRM (Salesforce, HubSpot): Para enriquecer los perfiles de los clientes con su comportamiento en el recinto.
- Automatización de marketing (Mailchimp, Klaviyo): Para activar campañas automatizadas de correo electrónico/SMS (p. ej., una oferta de "bienvenida de nuevo" para un visitante recurrente).
- Herramientas de Business Intelligence (BI): Para correlacionar la analítica del WiFi con los datos de ventas.
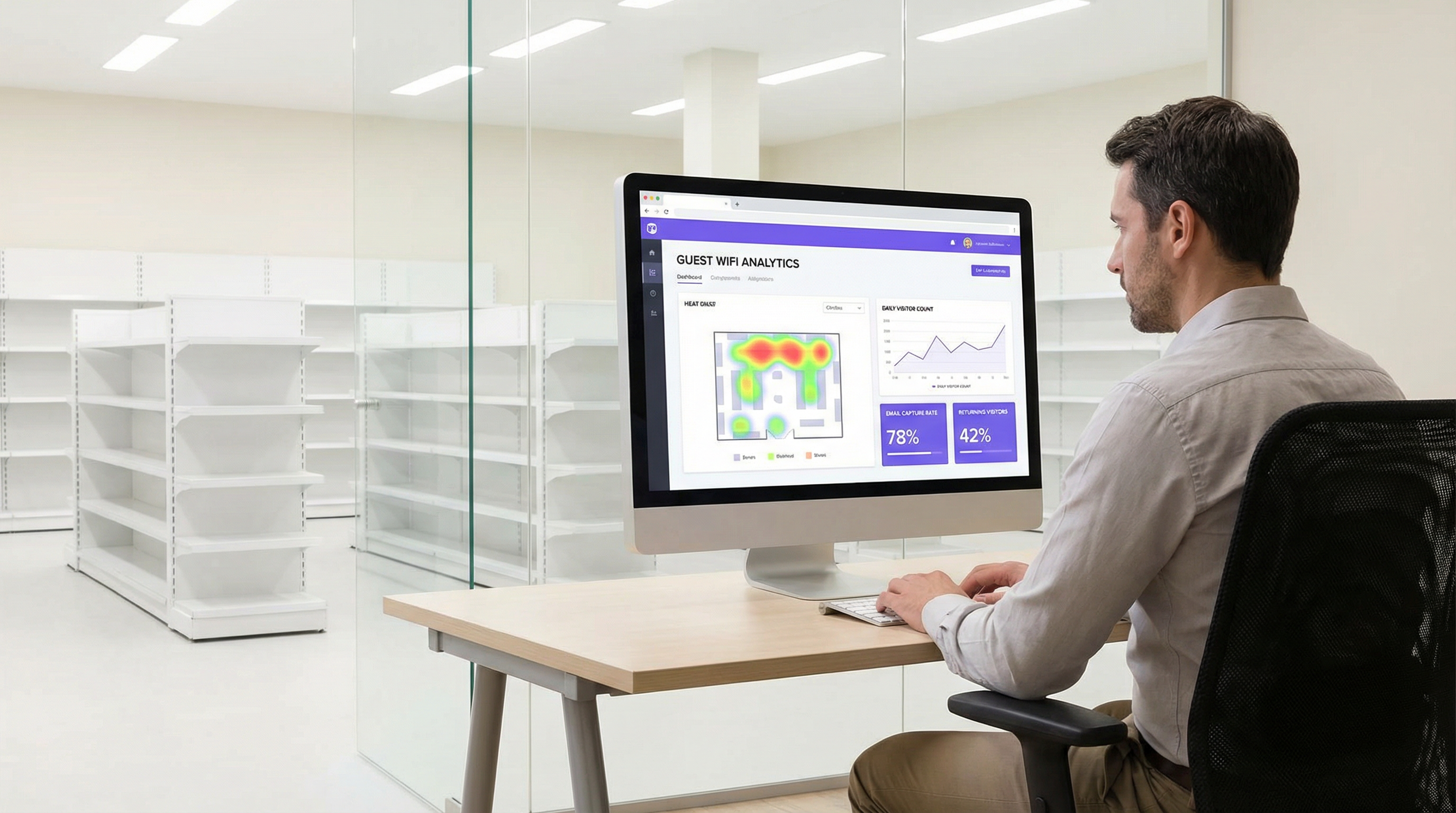
Esta capa también proporciona el panel de analítica, ofreciendo información sobre la afluencia, los tiempos de permanencia, la fidelidad de los visitantes y los mapas de calor de ubicación.
Guía de implementación
La implementación de una solución de marketing a través del WiFi para invitados requiere un enfoque por fases:
Definir los objetivos de negocio: ¿Cuáles son las metas principales? ¿Aumentar el tamaño de la lista de correo en un 25 %? ¿Impulsar un aumento del 10 % en la repetición de negocios? ¿Vincular el 5 % de las ventas en tienda a una promoción basada en el WiFi? Es esencial contar con KPI claros.
Auditoría de la infraestructura: Evalúe su red actual. ¿Es adecuada la cobertura de los AP para la analítica de ubicación? ¿Admite su puerta de enlace la integración con plataformas de Captive Portal de terceros? A menudo se requiere un estudio exhaustivo del sitio.
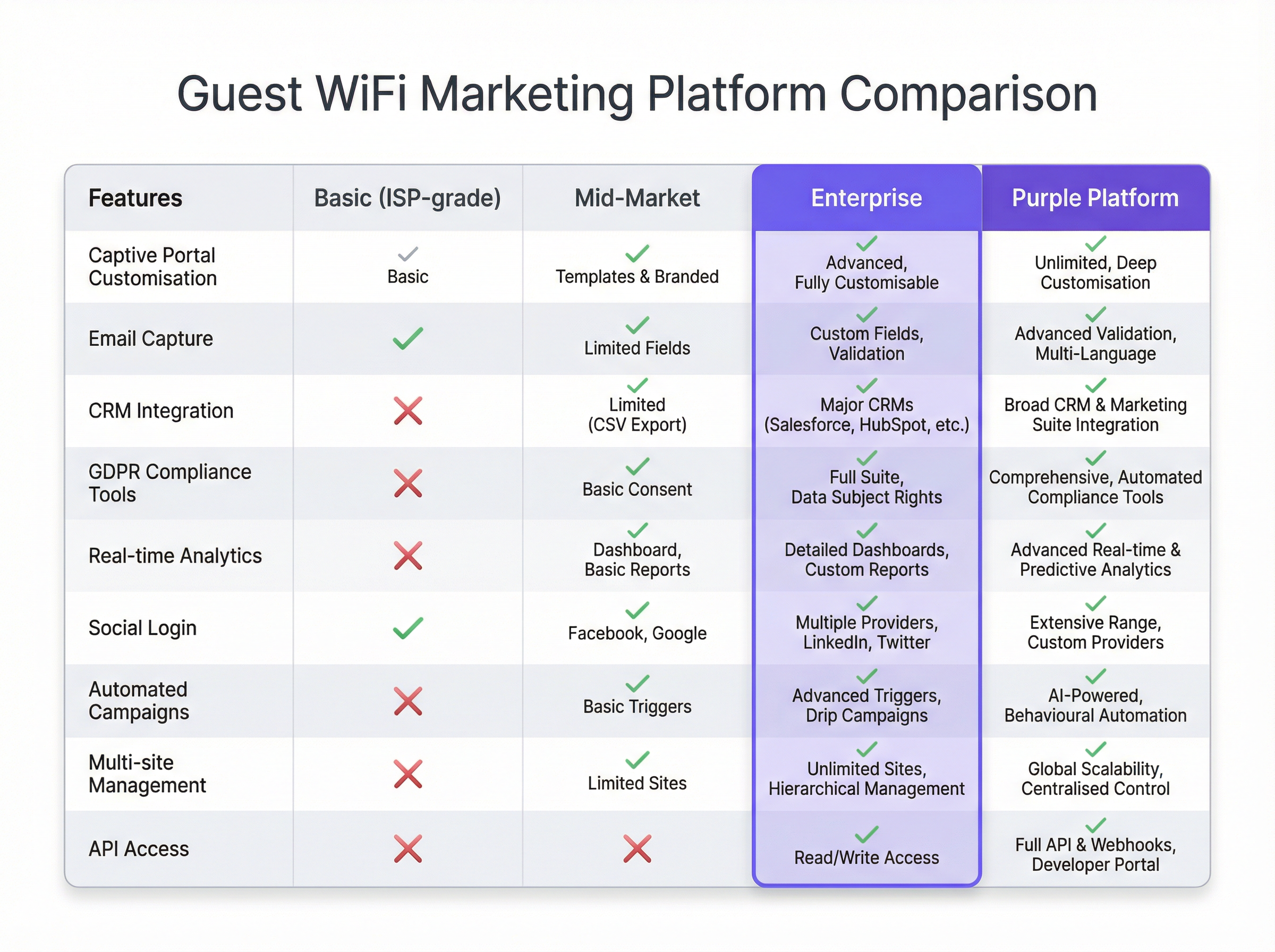
Selección de la plataforma: Elija una plataforma que cumpla con sus objetivos. Las consideraciones clave incluyen la amplitud de las integraciones de CRM, la sofisticación de su analítica y la solidez de sus herramientas de cumplimiento normativo. Consulte la tabla comparativa a continuación para obtener una descripción general neutral.
Diseñar el recorrido del cliente: Trace la experiencia del usuario desde la conexión hasta la comunicación posterior a la visita. Diseñe un Captive Portal limpio y optimizado para móviles (mobile-first) con un claro intercambio de valor (p. ej., "WiFi gratis a cambio de su correo electrónico y un cupón de descuento del 15 %").
Configurar e integrar: Configure el Captive Portal, establezca los activadores de automatización de marketing y cree los enlaces de la API con su CRM. Esta es una tarea técnica que requiere la colaboración entre los equipos de red y de marketing.
Prueba piloto e iteración: Realice el lanzamiento en un número limitado de ubicaciones. Supervise las tasas de conexión, la calidad de la captura de datos y el rendimiento de las campañas. Utilice la información obtenida para perfeccionar el enfoque antes de una implementación completa.
Mejores prácticas
- Priorizar la experiencia del usuario: Un proceso de inicio de sesión lento, complejo o poco fiable acabará con la adopción. Mantenga los formularios breves y el proceso de conexión fluido.
- Ofrecer un intercambio de valor claro: Los usuarios están más dispuestos a compartir datos si reciben un valor tangible a cambio. Esto podría ser una velocidad premium, un descuento o contenido exclusivo.
- Integrar el cumplimiento normativo en el diseño: La privacidad de los datos no es una idea de último momento. Asegúrese de que cada paso, desde el consentimiento en el Captive Portal hasta la gestión de datos en el CRM, cumpla con el GDPR/CCPA.
- Segmentar y personalizar: No envíe el mismo mensaje a todos los usuarios. Utilice los datos para segmentar a su audiencia (p. ej., visitantes primerizos frente a recurrentes) y personalizar la comunicación.
- Proteger la red: Audite periódicamente la segmentación de su red y las reglas del firewall. Las redes de invitados son un vector de ataque común.
Resolución de problemas y mitigación de riesgos
- Bajas tasas de conexión: A menudo causadas por una mala experiencia del usuario. Simplifique el proceso de inicio de sesión, mejore el rendimiento de la red o aumente la visibilidad del servicio WiFi.
- Mala calidad de los datos: Implemente la validación de correo electrónico en tiempo real en su Captive Portal para reducir las entradas falsas o mal escritas. Priorice los inicios de sesión sociales para obtener datos verificados y de mayor calidad.
- Infracciones de cumplimiento normativo: El mayor riesgo. Trabaje con los equipos legales para garantizar que todo su flujo de datos cumpla con la normativa. Utilice una plataforma con herramientas de cumplimiento normativas integradas y automatizadas para gestionar el consentimiento y las solicitudes de los interesados.
- ROI negativo: Esto ocurre cuando se recopilan datos pero no se actúa en consecuencia. Asegúrese de que la capa de integración funciona y de que los equipos de marketing utilizan activamente los datos para ejecutar campañas segmentadas.
ROI e impacto empresarial
El ROI del marketing a través del WiFi para invitados se mide en varios ejes:
- Crecimiento de la base de datos de marketing: Realice un seguimiento de los nuevos contactos netos adquiridos a través de la plataforma WiFi. Asigne un valor a cada lead en función de los puntos de referencia del sector.
- Aumento de las ventas: Atribuya los ingresos a las promociones impulsadas por el WiFi. Por ejemplo, realice un seguimiento de la tasa de canje de los códigos de descuento ofrecidos en el Captive Portal.
- Mejora de la fidelidad del cliente: Mida el aumento de las visitas repetidas de clientes conocidos tras la implementación del sistema.
- Eficiencia operativa: Utilice los datos de afluencia y tiempo de permanencia para optimizar los niveles de personal, la distribución de las tiendas y los horarios de apertura.
Al conectar el comportamiento offline con los perfiles digitales, el marketing a través del WiFi para invitados proporciona el eslabón perdido en el recorrido omnicanal del cliente, ofreciendo un impacto claro y medible en los resultados finales.
Key Terms & Definitions
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted. In a marketing context, it's the primary tool for data capture.
IT teams deploy captive portals as the gateway to the guest network. It's the bridge between the network infrastructure and the marketing platform.
MAC Address (Media Access Control)
A unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment.
The WiFi marketing platform links a user's captured data (e.g., email) to their device's MAC address to track their presence and behaviour (dwell time, repeat visits) anonymously.
VLAN (Virtual Local Area Network)
A logical grouping of devices in the same broadcast domain. VLANs are usually configured on switches by placing some interfaces into one broadcast domain and some into another.
This is the fundamental mechanism IT teams use to segregate the guest WiFi network from the secure internal corporate network, preventing lateral movement by attackers.
GDPR (General Data Protection Regulation)
A regulation in EU law on data protection and privacy in the European Union and the European Economic Area.
For any organisation collecting data from EU citizens, GDPR compliance is mandatory. IT and marketing teams must ensure the WiFi platform provides tools for explicit consent, data access requests, and the right to be forgotten.
Webhook
An automated message sent from an app when something happens. It has a message—or payload—and is sent to a unique URL—a webhook URL.
This is how a WiFi platform can instantly notify a CRM when a new guest connects. For example, a webhook can trigger an action in Salesforce to create a new lead record the moment a guest logs into the WiFi.
Presence Analytics
The analysis of data from WiFi signals to understand how many people are in a physical space, without identifying them personally.
Venue operators use this data to understand footfall patterns, peak hours, and popular areas, allowing them to optimise staffing, layout, and operations.
Location Analytics
A more granular form of analytics that uses the signal strength from multiple access points to triangulate a device's position within a venue.
This provides heatmaps and path analysis, showing where visitors spend the most time and the routes they take. It requires a higher density of APs than simple presence analytics.
WPA3 (Wi-Fi Protected Access 3)
The latest generation of security for wireless networks. It provides more robust authentication and increased cryptographic strength.
Network architects should specify WPA3-compatible hardware for all new deployments to provide the highest level of security for guest and corporate wireless networks.
Case Studies
A 200-room luxury hotel wants to increase direct bookings and build a guest database for marketing, moving away from reliance on Online Travel Agencies (OTAs). They have a modern Cisco Meraki network infrastructure.
The hotel integrates Purple with their Meraki dashboard. They configure a captive portal offering two tiers of WiFi: a free, standard-speed service requiring email and consent for marketing, and a paid, high-speed premium service. The captured email is sent via webhook to their HubSpot CRM and added to a 'New Guest' workflow. This workflow sends a welcome email with a 10% discount code for their next direct booking. The hotel also uses the presence analytics to understand guest flow in the lobby, bar, and spa, helping them optimise staffing.
A retail chain with 50 stores wants to understand in-store customer behaviour and drive footfall through targeted promotions. They use a mix of Aruba and Ruckus hardware.
The chain deploys a hardware-agnostic platform like Purple across all 50 stores. They use a social login (Facebook/Google) on their captive portal to gather rich demographic data. This data is fed into their central BI tool. They identify that their highest-value customers (those with high repeat visits and long dwell times) are predominantly in the 25-34 age bracket. They then run a targeted Facebook ad campaign aimed at this demographic in the geographic areas around their underperforming stores, promoting a new product line. The WiFi analytics are then used to measure the uplift in footfall from this specific demographic post-campaign.
Scenario Analysis
Q1. A large conference centre is hosting a 3-day tech event with 5,000 attendees. They want to provide WiFi while also giving event sponsors opportunities for lead generation. How would you architect the WiFi solution?
💡 Hint:Consider tiered access and how to provide value to both attendees and sponsors.
Show Recommended Approach
Implement a two-tiered WiFi system. Tier 1 is a free, baseline-speed service for all attendees, with a captive portal that requires only email registration. This builds the centre's own marketing list. Tier 2 is a sponsored, high-speed premium service. Attendees can access it by opting-in to share their details (name, email, company) with a specific sponsor. Each major sponsor gets their own 'branded' access portal. This provides high-quality leads for sponsors and a clear value exchange for attendees (premium speed for data). The network must be robust with high AP density in breakout rooms and the main hall to handle the load.
Q2. A public library wants to offer free WiFi but is concerned about GDPR compliance and data security. They have a limited budget and minimal IT staff. What is the most critical first step in their deployment?
💡 Hint:What is the single most important security measure for any guest network?
Show Recommended Approach
The most critical first step is to ensure complete network segmentation. Using a VLAN, the guest WiFi network must be entirely isolated from the library's internal administrative network. This prevents any possibility of a user on the public network accessing sensitive internal systems, like the library management system or staff computers. Before even considering data capture, this fundamental security measure must be implemented and verified. A simple, reliable firewall rule blocking all traffic between the guest VLAN and the internal VLAN is essential.
Q3. A restaurant chain notices a high connection rate on their guest WiFi but a very low open rate on their marketing emails. What is the likely cause and how would you troubleshoot it?
💡 Hint:Think about the quality of the data being captured at the source.
Show Recommended Approach
The most likely cause is poor data quality, specifically fake or mistyped email addresses being entered on the captive portal. To troubleshoot, first analyse the captured data for obvious fake domains (e.g., test@test.com). The best long-term solution is to implement real-time email validation via an API on the captive portal. This checks if an email address is valid before the user is granted access. An alternative or complementary solution is to incentivise social logins, which provide verified email addresses and richer data, leading to higher engagement.
Key Takeaways
- ✓Guest WiFi can be transformed from a cost centre into a powerful marketing and analytics tool.
- ✓A captive portal is the gateway for capturing valuable first-party customer data with their consent.
- ✓Seamless integration with CRM and marketing platforms is crucial for acting on captured data and proving ROI.
- ✓Network segmentation (using VLANs) is the most critical security measure to protect your corporate network.
- ✓Compliance with data privacy regulations like GDPR is non-negotiable and must be built into the system design.
- ✓A clear value exchange (e.g., a discount for an email) is essential to maximise user adoption and data capture rates.
- ✓WiFi analytics provide unprecedented insight into customer behaviour in physical spaces, bridging the online-offline gap.



