WPA2 vs. WPA3: ¿Cuál es la diferencia y debería actualizar?
This guide provides IT managers, network architects, and venue operations directors with a definitive, actionable comparison of WPA2 and WPA3 WiFi security protocols. It explains the critical technical differences — including SAE authentication, Perfect Forward Secrecy, and Enhanced Open — and outlines a practical, phased migration strategy using WPA3 Transition Mode. The guide is essential for any organisation operating guest or staff WiFi in hospitality, retail, events, or public-sector environments who needs to understand the upgrade case, manage device compatibility, and align their wireless security posture with modern compliance requirements.
🎧 Listen to this Guide
View Transcript
Resumen ejecutivo
Durante más de una década, WPA2 ha sido el estándar de seguridad WiFi empresarial. Sin embargo, sus vulnerabilidades inherentes (la susceptibilidad a ataques de diccionario sin conexión y el exploit KRACK o ataque de reinstalación de claves) representan ahora un riesgo tangible y activamente explotado para las organizaciones. WPA3, el protocolo de seguridad de próxima generación certificado por la Wi-Fi Alliance en 2018, aborda directamente estas deficiencias al introducir una autenticación sólida con Autenticación Simultánea de Iguales (SAE), un cifrado más fuerte mediante GCMP-256 y Marcos de Gestión Protegidos (PMF) obligatorios. Esta guía ofrece una comparación práctica y procesable entre WPA2 y WPA3 para líderes de TI y arquitectos de redes en entornos de hostelería, retail y grandes recintos. Describe el caso de negocio para la actualización, detalla una ruta de transición estratégica utilizando el Modo de Transición WPA3 y ofrece mejores prácticas neutrales en cuanto a proveedores para garantizar una red inalámbrica segura y de alto rendimiento que cumpla con las exigencias modernas de cumplimiento y experiencia del huésped. La conclusión principal es que migrar a WPA3 ya no es una cuestión de si, sino de cómo, y un enfoque estratégico por fases es el camino más eficaz para mitigar riesgos y preparar su infraestructura para el futuro.
Análisis técnico en profundidad
La transición de WPA2 a WPA3 representa un cambio arquitectónico significativo en la seguridad inalámbrica. Comprender las diferencias técnicas subyacentes es crucial para que los arquitectos de redes y los directores de TI tomen decisiones de implementación informadas. Aunque WPA2 ha sido un estándar resistente, WPA3 se diseñó para neutralizar vectores de ataque específicos y bien documentados, y para proporcionar una base más segura para la próxima década de conectividad inalámbrica.
Autenticación: de PSK a SAE
El cambio más fundamental entre WPA2-Personal y WPA3-Personal es el mecanismo de autenticación. WPA2 utiliza una clave precompartida (PSK) combinada con un protocolo de enlace de 4 vías (4-way handshake). Aunque fue eficaz en el momento de su diseño, este método es vulnerable a ataques de diccionario sin conexión. Un atacante puede capturar pasivamente el protocolo de enlace y luego utilizar potencia computacional para adivinar la contraseña sin conexión, sin ninguna interacción adicional con la red. Esto hace que las redes protegidas con contraseñas débiles o moderadamente complejas sean muy susceptibles de verse comprometidas.
WPA3 sustituye PSK por la Autenticación Simultánea de Iguales (SAE), también conocida como intercambio de claves Dragonfly. SAE es un protocolo de acuerdo de claves autenticado por contraseña que es resistente a los ataques de diccionario sin conexión. Durante el proceso de autenticación, la contraseña nunca se intercambia directamente. En su lugar, tanto el cliente como el punto de acceso utilizan la contraseña para generar hashes criptográficos, que luego se intercambian para demostrar el conocimiento mutuo de la clave. Un atacante que capture este intercambio no puede utilizarlo para forzar la contraseña sin conexión. Cualquier intento de adivinar la contraseña debe ser un ataque activo y en línea, mucho más lento y mucho más fácil de detectar y bloquear.
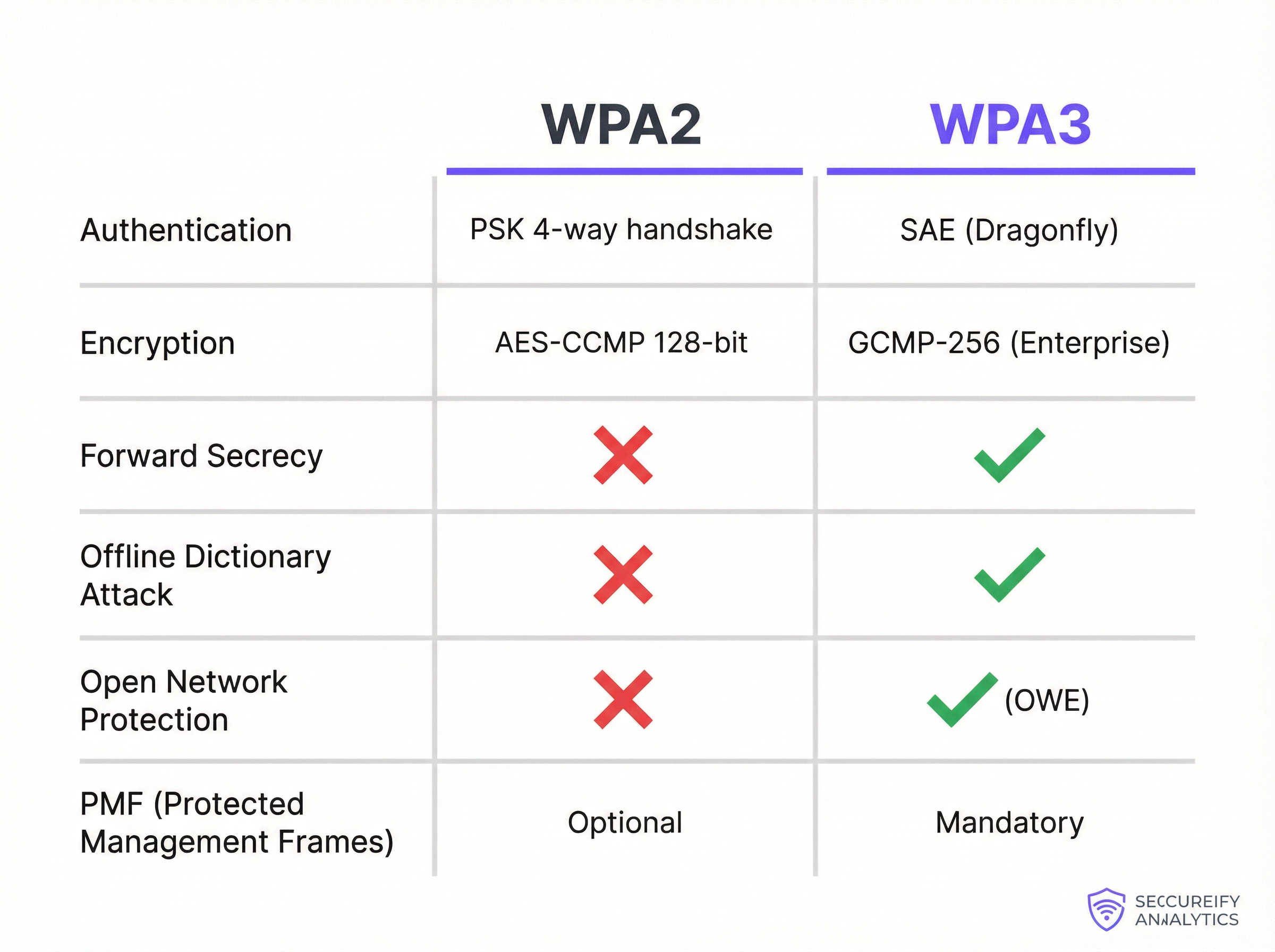
Cifrado, gestión de claves y secreto perfecto hacia adelante
WPA2-Enterprise utiliza AES-CCMP con cifrado de 128 bits, que se ha considerado seguro durante muchos años. WPA3-Enterprise eleva el nivel significativamente, ofreciendo un modo de seguridad de 192 bits opcional alineado con la suite de Algoritmos de Seguridad Nacional Comercial (CNSA). Esto proporciona una postura criptográfica requerida para entornos gubernamentales, de defensa y otros de alta seguridad.
En términos más generales, WPA3 introduce el Secreto Perfecto hacia Adelante (PFS). Con WPA2, si un atacante compromete la contraseña de la red, podría descifrar el tráfico pasado que hubiera capturado y almacenado previamente. WPA3 con SAE garantiza que cada sesión tenga una clave de cifrado única y efímera. Incluso si se compromete una clave de una sola sesión, no se puede utilizar para descifrar ninguna sesión anterior o futura, lo que reduce drásticamente el radio de impacto de cualquier posible brecha.
Protección para redes abiertas: Enhanced Open (OWE)
En recintos de cara al público, como hoteles, aeropuertos y tiendas de retail, las redes WiFi abiertas (sin contraseña) son comunes para el acceso de invitados. En una red abierta tradicional, todo el tráfico se transmite en texto plano, lo que hace que cada usuario sea vulnerable a las escuchas pasivas de cualquier otra persona en la misma red. WPA3 aborda esto con Enhanced Open, que implementa el Cifrado Inalámbrico Oportunista (OWE). OWE crea automáticamente un túnel individual y cifrado entre cada usuario y el punto de acceso, incluso en una red sin contraseña. Esto proporciona una privacidad significativa sin añadir ninguna fricción al proceso de conexión: una mejora crítica para las implementaciones de WiFi para invitados a gran escala.
Marcos de gestión protegidos (PMF)
Los marcos de gestión rigen cómo los dispositivos WiFi gestionan sus conexiones, incluidas la asociación y la desasociación. En WPA2, estos marcos están desprotegidos, lo que permite a un atacante falsificarlos para desautenticar por la fuerza a un usuario legítimo, lo que facilita ataques de denegación de servicio o de intermediario (man-in-the-middle). Aunque los PMF (definidos en IEEE 802.11w) eran opcionales en WPA2, WPA3 exige el uso de Marcos de Gestión Protegidos, garantizando la integridad y autenticidad de estos mensajes de control críticos y protegiendo la estabilidad general de la conexión inalámbrica.
Guía de implementación
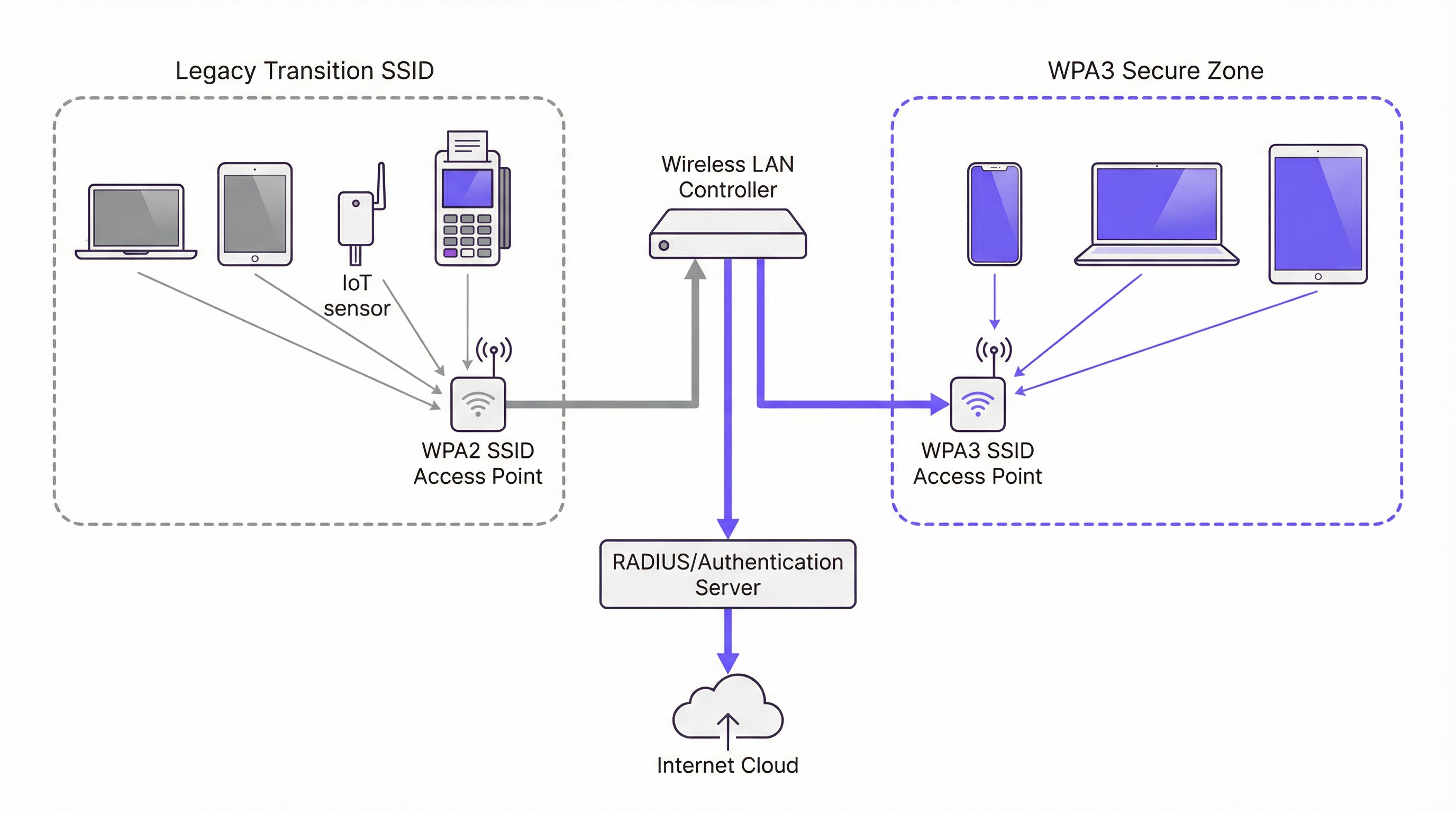
Migrar una red empresarial de WPA2 a WPA3 no es un simple cambio de interruptor, sino un proyecto estratégico que requiere una planificación y ejecución cuidadosas. El objetivo es mejorar la seguridad al tiempo que se minimizan las interrupciones en las operaciones comerciales y la experiencia del usuario. Un enfoque por fases es casi siempre el camino recomendado.
Fase 1: Auditoría de infraestructura y dispositivos. El primer paso es una auditoría exhaustiva de todo su ecosistema inalámbrico. Para los puntos de acceso, identifique la marca, el modelo y la versión de firmware de todas las unidades y consulte la documentación del fabricante para comprobar la compatibilidad con WPA3. La mayoría de los AP de nivel empresarial vendidos desde 2019 admiten WPA3, pero normalmente se requiere una actualización de firmware. Si utiliza una arquitectura basada en controladores, asegúrese de que el software del controlador esté actualizado a una versión que admita la configuración y gestión de WPA3. La parte más crítica y desafiante de la auditoría es el inventario de dispositivos cliente. Debe catalogar cada dispositivo que se conecte a su red WiFi: portátiles corporativos, smartphones, dispositivos BYOD y hardware de propósito especial como terminales de punto de venta (POS), escáneres de códigos de barras, sensores IoT y componentes de edificios inteligentes.
Fase 2: Habilitar el Modo de Transición WPA3/WPA2. Un cambio completo e inmediato a WPA3 no es práctico para la mayoría de las organizaciones debido a la diversidad de dispositivos cliente. La solución estándar de la industria es utilizar el Modo Mixto WPA3/WPA2, también llamado Modo de Transición. En esta configuración, el mismo SSID se emite con soporte para la autenticación tanto WPA3 como WPA2. Los clientes compatibles con WPA3 negocian y se conectan automáticamente utilizando el protocolo más seguro; los clientes heredados se conectan utilizando WPA2. Esto permite una experiencia de usuario fluida durante el período de migración. En el controlador de su LAN inalámbrica o en la interfaz de gestión de AP, normalmente encontrará una configuración de seguridad para su SSID que le permite seleccionar "WPA3+WPA2-Enterprise" o una opción de modo mixto similar.
Fase 3: Crear zonas seguras exclusivas para WPA3. A medida que su población de dispositivos cliente sea cada vez más compatible con WPA3, comience a crear SSID exclusivos para WPA3 para grupos de usuarios o tipos de dispositivos específicos. Priorice los dispositivos y usuarios que manejan los datos más confidenciales. Por ejemplo, cree un SSID exclusivo para WPA3 para el departamento de finanzas o para los dispositivos de los ejecutivos corporativos, y luego utilice su plataforma de gestión de dispositivos para enviar nuevos perfiles de red a los dispositivos compatibles, reduciendo gradualmente su dependencia del SSID de modo mixto.
Fase 4: Aislar y gestionar dispositivos heredados. Inevitablemente, tendrá una larga lista de dispositivos heredados que no admiten WPA3. Cree un SSID separado y dedicado configurado solo para WPA2, protegido por un firewall del resto de la red corporativa con reglas de acceso estrictas. Simultáneamente, desarrolle un plan de ciclo de vida de renovación de hardware para eliminar gradualmente los dispositivos no compatibles con el tiempo. Para cada compra de un nuevo dispositivo, exija la compatibilidad con WPA3 como requisito de adquisición.
Mejores prácticas
La siguiente tabla resume las recomendaciones clave estándar de la industria para una implementación segura de WPA3, basándose en las directrices de IEEE 802.1X, las especificaciones de la Wi-Fi Alliance y los requisitos de PCI DSS v4.0.
| Mejor práctica | Justificación | Prioridad |
|---|---|---|
| Exigir 802.1X para todos los SSID corporativos | Elimina las contraseñas compartidas; proporciona responsabilidad por usuario y control de políticas centralizado a través de RADIUS. | Crítica |
| Implementar EAP-TLS (autenticación basada en certificados) | Elimina por completo la superficie de ataque basada en contraseñas; los certificados no pueden ser objeto de phishing. | Alta |
| Habilitar PMF en todas las redes WPA2 | Protege contra ataques de desautenticación y desasociación incluso antes de la migración completa a WPA3. | Alta |
| Deshabilitar velocidades de datos heredadas (< 6 Mbps) | Elimina la compatibilidad con los clientes más antiguos y menos seguros, y mejora la eficiencia general del tiempo de transmisión. | Media |
| Segmentar el tráfico de IoT e invitados en VLAN dedicadas | Limita el radio de impacto de cualquier compromiso en un dispositivo heredado o red abierta. | Crítica |
| Establecer una cadencia de actualización de firmware | Garantiza que las vulnerabilidades conocidas se parcheen rápidamente en los AP y controladores. | Alta |
| Exigir WPA3 en todas las adquisiciones de hardware nuevo | Evita la acumulación de deuda técnica y acelera el cronograma de migración. | Alta |
Resolución de problemas y mitigación de riesgos
La implementación de WPA3 puede introducir nuevos desafíos. El modo de fallo más común es la conectividad del cliente, donde los dispositivos con controladores inalámbricos o sistemas operativos obsoletos no logran negociar una conexión WPA3. La solución es casi siempre asegurarse de que se apliquen los controladores y actualizaciones del sistema operativo más recientes antes de habilitar WPA3. Realizar pruebas con una muestra representativa de tipos de dispositivos antes de un despliegue generalizado es un paso innegociable en cualquier plan de implementación responsable.
La degradación del rendimiento es otra preocupación, aunque en la práctica rara vez es causada por el propio WPA3. Con mayor frecuencia, es el resultado de puntos de acceso mal configurados o versiones de firmware con errores. Validar el nuevo firmware en un entorno de laboratorio antes de la implementación en producción, y supervisar de cerca métricas clave como la latencia, las tasas de pérdida de paquetes y los recuentos de retransmisión después de cualquier cambio de configuración, le permitirá identificar y resolver problemas rápidamente.
El desafío más persistente es la gestión de dispositivos IoT y sin interfaz gráfica (headless) que carecen de los sofisticados suplicantes de los sistemas operativos modernos. Estos dispositivos deben aislarse en un SSID dedicado y reforzado solo para WPA2 con reglas de firewall estrictas. Esta no es una solución permanente, sino una medida de contención de riesgos mientras se desarrolla y ejecuta un plan de sustitución.
ROI e impacto empresarial
El ROI de una actualización a WPA3 está impulsado principalmente por la mitigación de riesgos. Las vulnerabilidades en WPA2 se explotan activamente, y un ataque exitoso a una red inalámbrica puede provocar la exfiltración de datos, daños a la reputación y sanciones de cumplimiento significativas bajo marcos como PCI DSS v4.0 y GDPR. El coste de una sola brecha (que abarca la investigación forense, los honorarios legales, la notificación a los clientes y las multas regulatorias) puede alcanzar fácilmente cientos de miles de euros. La inversión en una infraestructura compatible con WPA3 es una fracción de este coste potencial.
Más allá del riesgo, existe un impacto directo en la experiencia del huésped y la confianza en la marca. En los recintos de cara al público, la seguridad del WiFi para invitados es parte de la promesa de la marca. WPA3 Enhanced Open permite a los recintos proporcionar un acceso fluido y sin contraseñas, al tiempo que garantiza que el tráfico de cada usuario esté cifrado y aislado de otros usuarios en la misma red. Esto genera confianza y mejora la experiencia general del huésped sin añadir complejidad operativa.
Por último, WPA3 es una inversión de futuro. Es la base de seguridad para WiFi 6, 6E y WiFi 7. Retrasar la transición solo acumula deuda técnica, lo que hace que la eventual migración sea más compleja y costosa. Una actualización estratégica y por fases a WPA3 es un enfoque fiscalmente responsable para la planificación de la arquitectura de red a largo plazo que ofrece rendimientos compuestos a lo largo del ciclo de vida de la inversión en infraestructura.
Key Terms & Definitions
SAE (Simultaneous Authentication of Equals)
A password-authenticated key agreement protocol, also known as the Dragonfly handshake, that replaces WPA2's Pre-Shared Key (PSK) mechanism. SAE prevents offline dictionary attacks by ensuring the password is never transmitted or exposed during the authentication process. Both parties prove knowledge of the password through cryptographic exchange, making passive capture of the handshake useless to an attacker.
IT teams encounter SAE when configuring WPA3-Personal SSIDs. It is the primary reason WPA3-Personal is significantly more secure than WPA2-PSK and is the first capability to verify when assessing WPA3 readiness.
GCMP-256 (Galois/Counter Mode Protocol, 256-bit)
The encryption cipher used in WPA3-Enterprise's 192-bit security mode. GCMP-256 provides both data confidentiality and data integrity (authentication) in a single, highly efficient operation. It is aligned with the Commercial National Security Algorithm (CNSA) suite and represents a significant improvement over WPA2's AES-CCMP-128.
Relevant for network architects designing networks for government, defence, financial services, or healthcare environments where regulatory requirements mandate the highest available encryption standards.
Perfect Forward Secrecy (PFS)
A cryptographic property that ensures each communication session uses a unique, ephemeral encryption key. If a session key is compromised, it cannot be used to decrypt any past or future sessions. WPA3 achieves PFS through the SAE handshake, which generates a unique Pairwise Master Key (PMK) for each session.
Critical for environments where sensitive data is transmitted over WiFi and where the threat of 'capture now, decrypt later' attacks is a concern. PFS is a key differentiator between WPA2 and WPA3 from a data protection standpoint.
OWE (Opportunistic Wireless Encryption)
A WiFi security mechanism defined in RFC 8110 and implemented in WPA3 as 'Enhanced Open'. OWE automatically establishes an encrypted connection between each client and the access point on an open (password-free) network, providing individualised data encryption without any user interaction or credential exchange.
The standard configuration for guest and public WiFi in hospitality, retail, and venue environments. OWE allows operators to provide seamless connectivity while protecting users from passive eavesdropping, directly addressing a long-standing privacy concern with traditional open networks.
PMF (Protected Management Frames)
A security mechanism defined in IEEE 802.11w that encrypts and authenticates WiFi management frames, such as de-authentication and disassociation frames. Without PMF, an attacker can spoof these frames to forcibly disconnect legitimate users from the network. PMF is optional in WPA2 but mandatory in WPA3.
IT teams should enable PMF on all WPA2 networks as a hardening measure, even before migrating to WPA3. It is a simple configuration change that provides meaningful protection against denial-of-service attacks.
WPA3 Transition Mode
A mixed-mode SSID configuration that simultaneously supports both WPA3 and WPA2 authentication on the same network name (SSID). WPA3-capable clients automatically negotiate and use the more secure WPA3 protocol; legacy WPA2-only clients connect using the older protocol. This is the primary mechanism for managing the migration from WPA2 to WPA3 in environments with mixed device populations.
The recommended starting point for any WPA3 migration. IT teams should enable transition mode on existing SSIDs as the first step, then monitor which devices are connecting via WPA2 to identify the remaining legacy device population.
802.1X / RADIUS Authentication
An IEEE standard for port-based network access control. In the context of enterprise WiFi, 802.1X uses a RADIUS (Remote Authentication Dial-In User Service) server to authenticate individual users or devices before granting network access. This provides per-user accountability and centralised access control, replacing the single shared password of PSK-based networks.
The mandatory authentication framework for any corporate WiFi network carrying sensitive data. Both WPA2-Enterprise and WPA3-Enterprise use 802.1X as their authentication layer. IT teams should use this in conjunction with EAP-TLS (certificate-based authentication) for the highest security posture.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A certificate-based WiFi authentication method that uses digital certificates on both the client and the authentication server to establish mutual trust, without requiring a password. EAP-TLS is considered the gold standard for enterprise WiFi authentication as it eliminates the risk of password phishing, credential theft, and brute-force attacks.
IT teams should prioritise EAP-TLS over password-based EAP methods (like PEAP-MSCHAPv2) for all corporate devices. It requires a Public Key Infrastructure (PKI) to manage and distribute certificates, but this investment is justified by the significant security improvement.
KRACK (Key Reinstallation Attack)
A vulnerability discovered in 2017 that exploits a flaw in the WPA2 four-way handshake. By manipulating and replaying cryptographic handshake messages, an attacker can force a victim's device to reinstall an already-in-use encryption key, causing nonce reuse and potentially allowing the attacker to decrypt, replay, or forge network packets. WPA3's SAE handshake is not susceptible to KRACK.
KRACK is a key reason for migrating to WPA3. While patches were released for many devices, not all devices received updates, and the underlying vulnerability is a structural weakness of the WPA2 handshake design. IT teams should treat unpatched devices as a significant risk.
Case Studies
A 450-room luxury hotel group with 12 properties needs to upgrade its guest and staff WiFi. The network currently runs WPA2-PSK for guests and WPA2-Enterprise for staff. The IT director is concerned about PCI DSS compliance for the payment systems on the staff network, and wants to improve guest privacy without adding a password requirement to the guest network. The estate includes a mix of Cisco Catalyst 9130 APs (WPA3-capable) and older Cisco 2800 series APs (WPA2-only). What is the recommended migration strategy?
The recommended approach is a phased, property-by-property migration that prioritises the highest-risk network segments first. For properties with Cisco 9130 APs, the immediate action is to update the controller software (Cisco IOS-XE) to a version that supports WPA3, then enable WPA3-Enterprise Transition Mode on the staff SSID. This allows WPA3-capable corporate devices to automatically use the more secure protocol while legacy devices continue to connect via WPA2-Enterprise. For the guest network, enable WPA3 Enhanced Open (OWE) on a new SSID. This provides automatic, per-user encryption for all guests without requiring a password, directly addressing the privacy concern. For properties with legacy Cisco 2800 APs, these units should be placed on a hardware refresh roadmap. In the interim, harden the existing WPA2-Enterprise configuration by ensuring 802.1X with EAP-TLS (certificate-based authentication) is in use for all staff devices. For PCI DSS compliance, ensure the payment systems are on a dedicated, isolated SSID or VLAN with the strictest possible access controls, and document the compensating controls in place while the hardware refresh is underway. The migration should be completed property by property, starting with the highest-revenue or highest-risk locations, to manage change and validate the configuration before a full estate rollout.
A national retail chain with 250 stores is preparing for a PCI DSS v4.0 audit. Each store has a mix of corporate WiFi (for staff devices and POS terminals) and guest WiFi (for customer-facing promotions and loyalty app connectivity). The IT security team has been told by the auditors that their current WPA2-PSK configuration for the staff network is a finding. The POS terminals are a mix of modern Android-based units (WPA3-capable) and older Windows CE-based units (WPA2-only). How should the IT team respond to the audit finding and plan the remediation?
The audit finding is valid. WPA2-PSK for a network carrying payment card data is a significant risk, as a single compromised password exposes the entire network. The immediate remediation for the staff network is to migrate from WPA2-PSK to WPA2-Enterprise with 802.1X authentication, using a RADIUS server (e.g., Cisco ISE, Aruba ClearPass, or a cloud-based RADIUS service). This provides per-device authentication and eliminates the shared password vulnerability. This action alone resolves the audit finding and is achievable without any hardware changes. In parallel, the team should audit all POS terminals and other staff devices for WPA3 capability. For the modern Android POS terminals, enable WPA3-Enterprise Transition Mode on the staff SSID. For the legacy Windows CE units, these must be placed on a dedicated, isolated SSID with WPA2-Enterprise and strict VLAN-based network segmentation, ensuring they can only communicate with the payment processing server and nothing else. For the guest network, implement WPA3 Enhanced Open to provide customer privacy. This also demonstrates a proactive security posture to the auditors, which is beneficial for the overall compliance assessment.
Scenario Analysis
Q1. A 20,000-seat stadium is deploying a new WiFi network for a major multi-day event. The network must support 15,000 concurrent guest connections and a separate staff network for 500 employees handling ticketing and point-of-sale. The IT team has a budget for new WiFi 6E access points. The event organiser wants to offer free, seamless WiFi to all attendees without a password. What security protocol configuration would you recommend for the guest and staff networks, and why?
💡 Hint:Consider the specific use case for each network segment. The guest network requires seamless access with privacy; the staff network requires strong authentication for PCI DSS compliance. WPA3 has specific features designed for each of these scenarios.
Show Recommended Approach
For the guest network, the correct configuration is WPA3 Enhanced Open (OWE). This provides automatic, per-user encrypted tunnels without requiring a password, delivering the seamless experience the organiser wants while protecting each attendee's traffic from eavesdropping by other users. A traditional open network would leave all guest traffic in plaintext. For the staff network, the configuration should be WPA3-Enterprise with 802.1X authentication using a RADIUS server. Since the staff are handling payment card data via POS terminals, this is a PCI DSS requirement. If the POS terminals support it, EAP-TLS (certificate-based authentication) is the preferred EAP method. The two networks should be on completely separate VLANs with strict firewall rules between them. Since the new APs are WiFi 6E, they will natively support WPA3, so no transition mode is required for a greenfield deployment.
Q2. An IT manager at a 50-store retail chain has just received a penetration test report showing that the WPA2-PSK password for the staff network was cracked using an offline dictionary attack. The password was 12 characters long and considered 'strong'. The manager needs to remediate the finding immediately. What is the most effective immediate action, and what is the longer-term strategic recommendation?
💡 Hint:The root cause is not the password strength — it is the use of PSK. Consider what authentication mechanism would eliminate this entire class of vulnerability, regardless of password complexity.
Show Recommended Approach
The immediate action is to change the PSK to a highly complex, randomly generated passphrase (at least 20 characters) to reduce the risk while the longer-term fix is implemented. However, the strategic recommendation is to migrate from WPA2-PSK to WPA2-Enterprise with 802.1X authentication. This eliminates the shared password entirely. Each device or user authenticates individually against a RADIUS server, and there is no single password to crack. The preferred EAP method is EAP-TLS, which uses digital certificates instead of passwords, making offline dictionary attacks impossible. In parallel, the team should assess the WPA3 readiness of their access points and begin planning a migration to WPA3-Enterprise, which provides the additional protection of SAE and Perfect Forward Secrecy. The key insight is that the problem is not the password strength but the use of a shared secret — 802.1X eliminates this vulnerability class entirely.
Q3. A large conference centre is planning to upgrade its WiFi infrastructure. The venue hosts events ranging from small corporate meetings to large trade shows with 5,000+ attendees. The IT team is evaluating whether to deploy WPA3-only, WPA2-only, or a mixed WPA3/WPA2 configuration. The venue's device inventory shows that 85% of client devices are modern smartphones and laptops that support WPA3, but 15% are older event management tablets and barcode scanners that only support WPA2. What is the recommended SSID architecture?
💡 Hint:Consider the different user groups and device types. A single SSID for all devices may not be the optimal solution. Think about how to provide the highest security for the majority while managing the risk of the legacy minority.
Show Recommended Approach
The recommended architecture is a three-SSID model. First, a WPA3-Enterprise SSID for staff corporate devices (the modern laptops and smartphones), providing the highest security with 802.1X authentication. Second, a WPA3 Enhanced Open SSID for event attendees and guests, providing seamless, encrypted public access. Third, a dedicated WPA2-Enterprise (or WPA2-PSK) SSID, isolated on its own VLAN with strict firewall rules, for the legacy event management tablets and barcode scanners. This architecture ensures that the 85% of capable devices get the full benefit of WPA3, while the legacy 15% are contained and managed without compromising the security of the rest of the network. The legacy SSID should be treated as a temporary measure, with a hardware refresh plan to replace the non-compliant devices within a defined timeframe. Using WPA3 Transition Mode on a single SSID is an alternative but less preferable option, as it means the entire SSID operates at WPA2 security levels for any client that connects via WPA2.
Key Takeaways
- ✓WPA3 replaces WPA2's vulnerable PSK 4-way handshake with SAE (Simultaneous Authentication of Equals), which completely eliminates offline dictionary attacks — the most common method used to crack WiFi passwords.
- ✓WPA3 introduces Perfect Forward Secrecy, ensuring that a compromised session key cannot be used to decrypt previously captured traffic, defeating 'steal now, decrypt later' attack strategies.
- ✓WPA3 Enhanced Open (OWE) provides automatic, per-user encrypted tunnels on open, password-free networks — the optimal configuration for guest WiFi in hotels, retail stores, and stadiums.
- ✓WPA3 Transition Mode is the recommended migration path: it allows a single SSID to support both WPA2 and WPA3 clients simultaneously, enabling a phased migration without disrupting legacy devices.
- ✓The most critical immediate action for any organisation still using WPA2-PSK on a corporate network is to migrate to 802.1X authentication — this eliminates the shared password vulnerability regardless of WPA version.
- ✓A comprehensive device audit is the non-negotiable first step in any WPA3 migration. Legacy IoT and headless devices that cannot support WPA3 must be isolated on dedicated, firewalled network segments.
- ✓WPA3 is the security foundation for WiFi 6, 6E, and WiFi 7. Mandating WPA3 support in all new hardware procurement is the most effective long-term strategy for managing the transition and preventing the accumulation of technical debt.



