Comprensión y fortalecimiento de RADIUS contra ataques de colisión MD5
This guide provides a comprehensive technical reference on the RADIUS MD5 collision vulnerability (CVE-2024-3596, 'Blast-RADIUS'), explaining how man-in-the-middle attackers can exploit weaknesses in the MD5-based Response Authenticator to forge authentication approvals without knowing user credentials. It is essential reading for IT managers, network architects, and CTOs operating enterprise WiFi in hospitality, retail, events, and public-sector environments who need to assess their exposure, apply immediate mitigations, and plan a strategic migration to modern authentication standards. The guide covers the full attack lifecycle, a phased hardening roadmap, real-world deployment scenarios, and compliance implications under PCI DSS, GDPR, and ISO 27001.
🎧 Listen to this Guide
View Transcript

Resumen ejecutivo
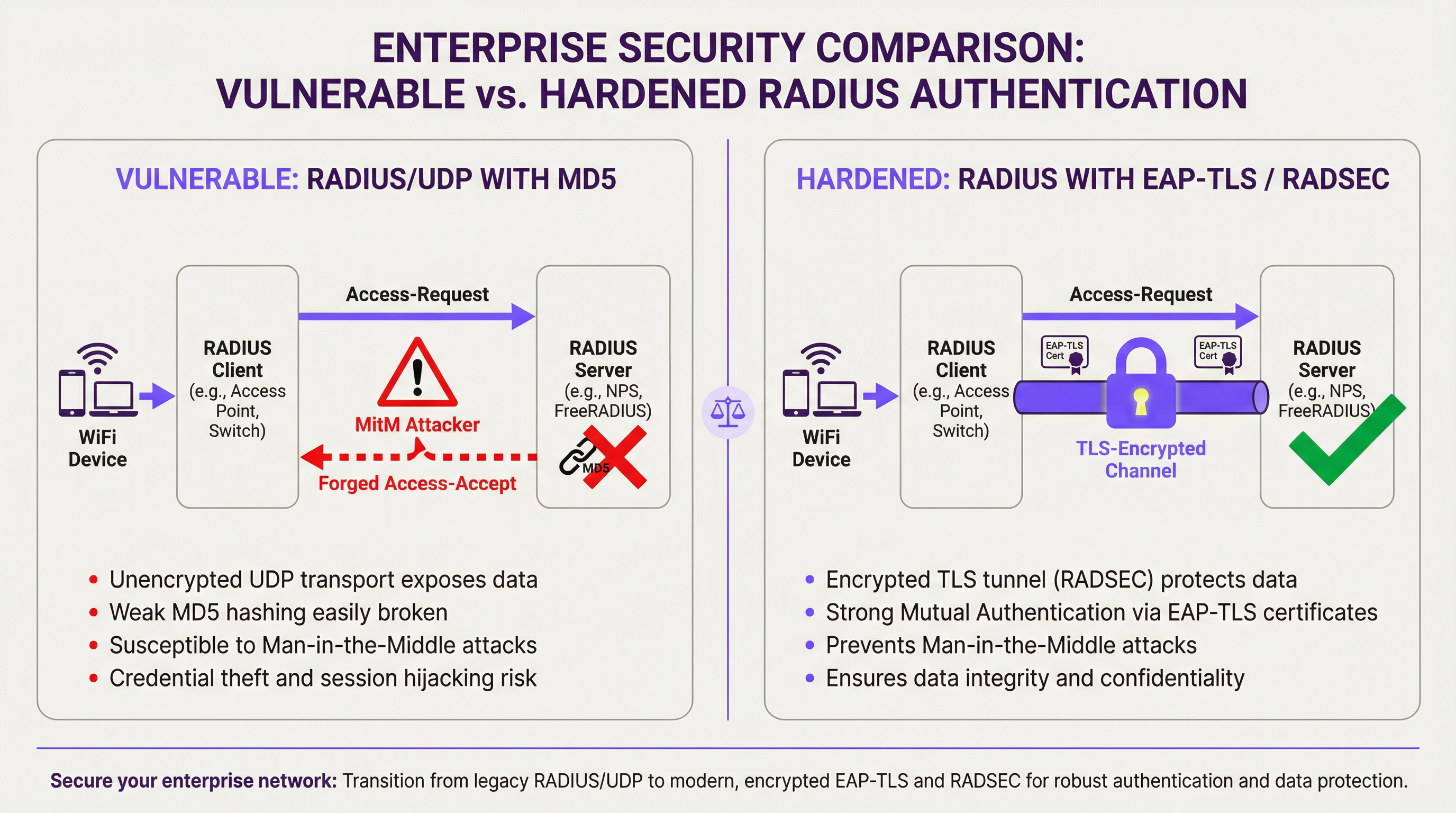
El protocolo RADIUS, piedra angular de la autenticación de redes empresariales desde 1991, presenta una vulnerabilidad crítica y ahora prácticamente explotable. Revelada en julio de 2024 bajo el código CVE-2024-3596 y denominada 'Blast-RADIUS', esta falla permite a un atacante de intermediario (MitM) posicionado entre un cliente y un servidor RADIUS falsificar una aprobación de autenticación válida —convirtiendo un 'Access-Reject' legítimo en un 'Access-Accept'— sin conocer nunca la contraseña de un usuario ni el secreto compartido de RADIUS. El ataque explota técnicas de colisión de prefijo elegido de MD5 que, con hardware moderno, pueden ejecutarse en minutos.
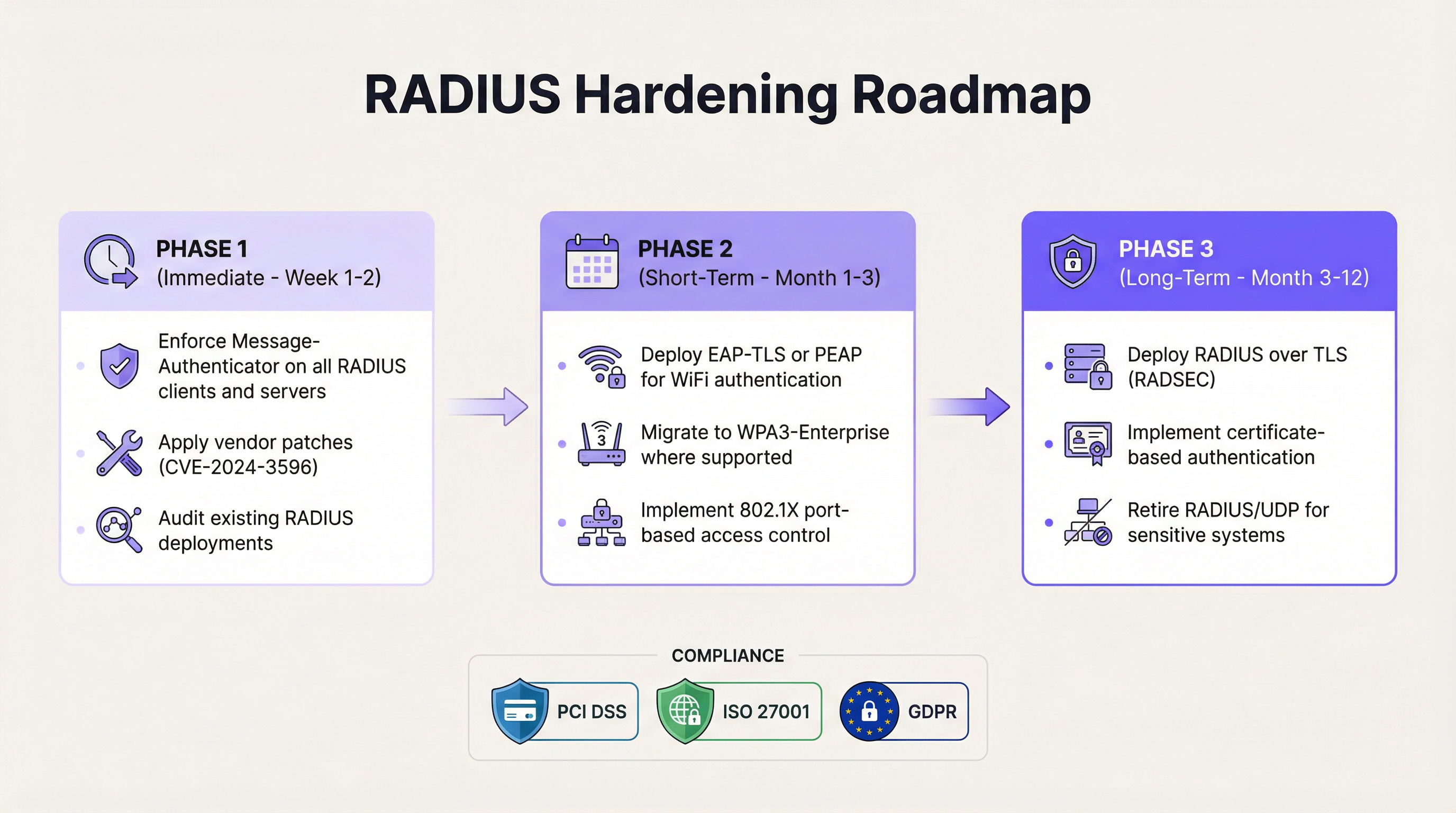
Para los operadores de recintos y los equipos de TI empresariales, el riesgo comercial es directo: un atacante que obtiene acceso no autorizado a la red puede moverse lateralmente por la infraestructura, acceder a sistemas de punto de venta, extraer datos de invitados y provocar violaciones de cumplimiento bajo PCI DSS y GDPR. Toda organización que ejecute RADIUS/UDP con modos de autenticación PAP, CHAP o MS-CHAP está expuesta hasta que se apliquen parches y se planifiquen cambios arquitectónicos. La mitigación inmediata —imponer el atributo Message-Authenticator en todo el tráfico RADIUS— es un cambio de configuración de baja interrupción disponible en todos los proveedores principales. La respuesta estratégica es una migración por fases a EAP-TLS y RADIUS sobre TLS (RADSEC).
Análisis técnico detallado
El protocolo RADIUS y su herencia criptográfica
RADIUS (Remote Authentication Dial-In User Service), estandarizado en el RFC 2865, fue diseñado en una época en la que los requisitos de seguridad de red eran fundamentalmente diferentes. El protocolo opera sobre UDP y utiliza un secreto compartido entre el cliente RADIUS (generalmente un punto de acceso o servidor de acceso a la red) y el servidor RADIUS para proporcionar cierto grado de integridad en los mensajes. Específicamente, las respuestas del servidor se 'autentican' utilizando una construcción llamada Response Authenticator (Autenticador de respuesta), calculada como:
MD5(Code || ID || Length || RequestAuthenticator || Attributes || SharedSecret)
Esta construcción nunca fue un código de autenticación de mensajes (MAC) adecuado. Es anterior a HMAC, que se estandarizó en 1997 precisamente para abordar las debilidades de los MAC basados en hash sin procesar. La especificación RADIUS no se actualizó cuando se introdujo HMAC, ni cuando se demostraron por primera vez las colisiones MD5 en 2004. Esta deuda arquitectónica se ha convertido ahora en una vulnerabilidad crítica.
Mecánica del ataque Blast-RADIUS
El ataque Blast-RADIUS (CVE-2024-3596) combina tres elementos: una vulnerabilidad a nivel de protocolo en cómo RADIUS construye su Response Authenticator, una técnica de colisión de prefijo elegido de MD5 y mejoras significativas en la velocidad del cálculo de colisiones que hacen que el ataque sea práctico en un escenario de intercepción de red en tiempo real.
El ataque procede de la siguiente manera. Un atacante MitM intercepta un paquete Access-Request enviado desde el cliente RADIUS al servidor. El atacante inyecta un atributo malicioso en esta solicitud: una carga útil cuidadosamente diseñada que causará una colisión entre el hash MD5 de la respuesta legítima del servidor y el hash MD5 de la respuesta falsificada deseada por el atacante. Cuando el servidor devuelve un Access-Reject (una autenticación fallida), el atacante utiliza la colisión precalculada para falsificar un paquete Access-Accept válido, completo con un Response Authenticator que el cliente RADIUS aceptará como genuino. El atacante no necesita conocer el secreto compartido ni las credenciales del usuario.
Investigadores de la Universidad de Boston, UC San Diego, CWI Amsterdam y Microsoft demostraron que, con algoritmos optimizados, la colisión de prefijo elegido de MD5 requerida para este ataque puede calcularse en menos de cinco minutos en hardware comercial. Esto hace que el ataque sea operativamente viable para un adversario decidido con acceso a la ruta de red entre el cliente y el servidor RADIUS.
Modos de autenticación afectados
La vulnerabilidad afecta a todas las implementaciones de RADIUS/UDP que utilizan métodos de autenticación que no son EAP. La siguiente tabla resume la exposición por modo de autenticación:
| Modo de autenticación | Protocolo | ¿Vulnerable a Blast-RADIUS? | Notas |
|---|---|---|---|
| PAP | Password Authentication Protocol | Sí | Más común en implementaciones heredadas |
| CHAP | Challenge Handshake Authentication Protocol | Sí | Ligeramente más fuerte que PAP, pero aún expuesto |
| MS-CHAP / MS-CHAPv2 | Microsoft CHAP | Sí | Común en entornos Windows |
| EAP-MD5 | EAP con MD5 | Sí | Obsoleto; evitar por completo |
| PEAP (MSCHAPv2 interno) | Protected EAP | No (el túnel EAP lo protege) | Requiere la validación correcta del certificado del servidor |
| EAP-TLS | EAP con TLS | No | Estándar de oro recomendado |
| EAP-TTLS | EAP Tunnelled TLS | No | Alternativa aceptable |
La distinción crítica es que los métodos basados en EAP establecen su propio túnel criptográfico para la autenticación, el cual no depende del Response Authenticator de MD5. Esto los hace inmunes al vector de ataque específico de Blast-RADIUS.
Por qué la segmentación de VLAN no es suficiente
Un error común es creer que aislar el tráfico RADIUS en una VLAN de administración dedicada proporciona una protección adecuada. Si bien la segmentación de la red es una práctica de seguridad sólida, no elimina el riesgo de Blast-RADIUS. Un atacante que ya haya comprometido un dispositivo en la red de administración —a través de un ataque de phishing, un compromiso de la cadena de suministro o la explotación de otra vulnerabilidad— puede posicionarse como un MitM en la ruta del tráfico RADIUS. El ataque solo requiere acceso a la ruta de red, no acceso externo a Internet. La segmentación reduce la superficie de ataque, pero no elimina la debilidad criptográfica subyacente.
Guía de implementación
Fase 1: Fortalecimiento inmediato (Semanas 1–2)
La primera prioridad es aplicar los parches de los proveedores para el CVE-2024-3596 en toda la infraestructura RADIUS. Todos los proveedores principales —incluidos Cisco ISE, Microsoft NPS, FreeRADIUS, Juniper, Aruba y Ruckus— han lanzado actualizaciones. Junto con la aplicación de parches, el cambio de configuración crítico es imponer el atributo Message-Authenticator en todos los clientes y servidores RADIUS.
El atributo Message-Authenticator (definido en el RFC 2869) proporciona una verificación de integridad HMAC-MD5 sobre todo el paquete RADIUS. A diferencia del Response Authenticator, esta construcción no es vulnerable al ataque de colisión de prefijo elegido porque la construcción HMAC vincula el hash al secreto compartido de una manera que impide al atacante crear una falsificación válida. Configurar clientes y servidores para que requieran este atributo —y rechacen cualquier mensaje que no lo incluya— cierra el vector de ataque inmediato.
Para FreeRADIUS, esto implica configurar require_message_authenticator = yes en el archivo clients.conf. Para Microsoft NPS, la política equivalente se aplica a través de la configuración de la Política de red. Para Cisco ISE, la configuración está disponible en la configuración del cliente RADIUS bajo la política de autenticación. Consulte el aviso específico de su proveedor para el CVE-2024-3596 para conocer los pasos de configuración exactos.
Fase 2: Modernización de la autenticación (Meses 1–3)
El objetivo a medio plazo es migrar la autenticación WiFi de los modos heredados PAP/CHAP a métodos basados en EAP. Para entornos WiFi empresariales, la ruta recomendada es WPA3-Enterprise con EAP-TLS. Esto requiere implementar una Infraestructura de clave pública (PKI) para emitir certificados de dispositivos y/o usuarios, configurar su servidor RADIUS para validar estos certificados y aprovisionar los dispositivos cliente con los certificados adecuados y los anclajes de confianza del servidor RADIUS.
Para entornos donde la implementación de certificados es compleja —como recintos con alta rotación de dispositivos o políticas BYOD— PEAP con MSCHAPv2 proporciona un paso intermedio aceptable, siempre que los clientes estén configurados para validar el certificado del servidor RADIUS. Sin la validación del certificado del servidor, PEAP es vulnerable a ataques de puntos de acceso no autorizados. El control de acceso basado en puertos IEEE 802.1X debe implementarse en la infraestructura cableada simultáneamente para garantizar una política de autenticación coherente en toda la red.
Fase 3: Seguridad de la capa de transporte (Meses 3–12)
El objetivo arquitectónico a largo plazo es encapsular todo el tráfico RADIUS dentro de un túnel TLS utilizando RADIUS sobre TLS (RADSEC), estandarizado en el RFC 6614. RADSEC reemplaza UDP por TCP y envuelve toda la sesión RADIUS en una conexión TLS mutuamente autenticada. Esto proporciona confidencialidad, integridad y protección contra repeticiones para todo el tráfico de autenticación, lo que hace que el Response Authenticator de MD5 sea irrelevante, ya que la propia capa de transporte es criptográficamente segura.
RADSEC es particularmente valioso en implementaciones distribuidas —como cadenas hoteleras, redes minoristas o entornos de estadios— donde el tráfico RADIUS puede atravesar segmentos de red intermedios. Actualmente, el IETF está avanzando RADIUS sobre TLS y DTLS hacia el estado de seguimiento de estándares, lo que refleja el consenso de la industria de que RADIUS/UDP debería quedar obsoleto para implementaciones confidenciales.
Mejores prácticas
Las siguientes mejores prácticas, independientes del proveedor, reflejan los estándares actuales de la industria y la orientación regulatoria para la seguridad de la autenticación WiFi empresarial.
Imponer Message-Authenticator universalmente. Cada cliente y servidor RADIUS en su infraestructura debe estar configurado para enviar y requerir el atributo Message-Authenticator. Esta es la acción de mayor impacto y menor interrupción disponible en la actualidad. Según la orientación del equipo de investigación de Blast-RADIUS, este atributo debe aparecer como el primer atributo en las respuestas Access-Accept y Access-Reject.
Adoptar EAP-TLS como estándar de autenticación. IEEE 802.1X con EAP-TLS proporciona autenticación mutua basada en certificados que es inmune a la clase de ataque Blast-RADIUS y se alinea con las recomendaciones del NIST SP 800-120 para métodos EAP en el acceso a redes inalámbricas. WPA3-Enterprise exige el modo de seguridad de 192 bits con EAP-TLS para el nivel de seguridad más alto.
Rotar los secretos compartidos de RADIUS regularmente. Si bien el ataque Blast-RADIUS no requiere el conocimiento del secreto compartido, los secretos compartidos fuertes y únicos (mínimo 32 caracteres, generados aleatoriamente) reducen el riesgo de otras clases de ataques. Los secretos deben rotarse al menos anualmente e inmediatamente ante cualquier sospecha de compromiso.
Implementar la contabilidad de RADIUS y el monitoreo de anomalías. Los registros de contabilidad de RADIUS proporcionan un registro de auditoría de los eventos de autenticación. El monitoreo de patrones anómalos —como autenticaciones exitosas desde tipos de dispositivos inesperados, direcciones MAC o en horarios inusuales— puede proporcionar una alerta temprana de explotación. Integre la contabilidad de RADIUS con su SIEM para obtener alertas automatizadas.
Segmentar el tráfico RADIUS. Aunque no es una mitigación completa, colocar el tráfico RADIUS en una VLAN de administración dedicada con ACL estrictas reduce la población de dispositivos que podrían usarse como punto de pivote MitM. Combínelo con el control de acceso a la red para garantizar que solo los dispositivos autorizados puedan comunicarse con el servidor RADIUS.
Alinearse con los requisitos de PCI DSS. El Requisito 8.6 de PCI DSS v4.0 exige una autenticación sólida para todas las cuentas. El Requisito 1.3 exige controles de segmentación de red. Las organizaciones que procesan datos de tarjetas de pago deben asegurarse de que su arquitectura de autenticación WiFi cumpla con estos requisitos, y la vulnerabilidad Blast-RADIUS afecta directamente la postura de cumplimiento para cualquier segmento de red dentro del alcance.
Solución de problemas y mitigación de riesgos
Modos de falla comunes durante el fortalecimiento
El problema más frecuente que se encuentra al imponer Message-Authenticator es la incompatibilidad de dispositivos heredados. Es posible que los puntos de acceso, conmutadores o concentradores VPN más antiguos no admitan el atributo, lo que provoca fallas de autenticación después de que el servidor se configura para requerirlo. El enfoque recomendado es auditar todos los clientes RADIUS antes de imponer el requisito en el lado del servidor, y mantener una lista de dispositivos que requieren actualizaciones de firmware o reemplazo.
Un segundo problema común son las fallas de validación de certificados durante la migración a EAP-TLS. Si los dispositivos cliente no están aprovisionados con el anclaje de confianza correcto del certificado del servidor RADIUS, rechazarán el certificado del servidor y fallará la autenticación. Esto es particularmente frecuente en entornos BYOD. La implementación de una solución de gestión de dispositivos móviles (MDM) para enviar perfiles de certificados es la resolución estándar.
Las incompatibilidades de secretos compartidos pueden ocurrir durante la migración a RADSEC si el nombre común (Common Name) del certificado TLS no coincide con el identificador de cliente esperado. Asegúrese de que los nombres de los sujetos de los certificados sean coherentes con las direcciones IP o los nombres de host de los clientes RADIUS configurados en el servidor.
Mitigación de riesgos para entornos que no pueden aplicar parches de inmediato
Para entornos donde la aplicación inmediata de parches no es factible —como sistemas de control industrial heredados o dispositivos de red integrados— el riesgo puede mitigarse parcialmente implementando controles estrictos de acceso a la red que limiten qué hosts pueden comunicarse con el servidor RADIUS, reduciendo la oportunidad de que un atacante MitM intercepte el tráfico. Esta es solo una medida temporal; se debe establecer una hoja de ruta de aplicación de parches y reemplazo.
ROI e impacto comercial
Cuantificación del riesgo
El caso de negocio para el fortalecimiento de RADIUS es sencillo cuando se enmarca en términos de costos por violaciones de seguridad y responsabilidad de cumplimiento. Un exploit exitoso de Blast-RADIUS en un entorno hotelero o minorista podría proporcionar a un atacante acceso a la red corporativa, llegando potencialmente a sistemas de punto de venta, repositorios de datos de invitados e infraestructura administrativa. El costo promedio de una violación de datos en el sector hotelero supera los 3 millones de libras esterlinas, según los puntos de referencia de la industria, y las multas regulatorias bajo GDPR podrían sumar hasta el 4% de la facturación anual global.
Para las organizaciones dentro del alcance de PCI DSS, una falla de autenticación de red que resulte en la exposición de datos de los titulares de tarjetas puede desencadenar investigaciones forenses obligatorias, multas de las marcas de tarjetas y la posible pérdida de privilegios de procesamiento de tarjetas: costos que superan con creces la inversión requerida para implementar EAP-TLS y RADSEC.
Puntos de referencia de costos de implementación
La siguiente tabla proporciona estimaciones indicativas de costos y esfuerzos para la hoja de ruta de fortalecimiento de tres fases en entornos de recintos típicos:
| Fase | Acción | Esfuerzo estimado | Costo estimado | Reducción de riesgos |
|---|---|---|---|---|
| Fase 1 | Parche + imponer Message-Authenticator | 1–3 días (equipo de TI) | Solo tiempo del personal | Alta (cierra el CVE inmediato) |
| Fase 2 | Migración a EAP-TLS / WPA3-Enterprise | 2–6 semanas | Licencias de PKI + MDM | Muy alta |
| Fase 3 | Implementación de RADSEC | 4–12 semanas | Actualizaciones de infraestructura | Integral |
Beneficios operativos más allá de la seguridad
La migración a EAP-TLS y RADSEC ofrece beneficios operativos más allá del fortalecimiento de la seguridad. La autenticación basada en certificados elimina la carga operativa de administrar y rotar contraseñas compartidas en grandes flotas de dispositivos. WPA3-Enterprise mejora la confiabilidad de la conexión en entornos densos: un beneficio medible para estadios y centros de conferencias donde cientos de dispositivos compiten por la autenticación. El transporte TCP de RADSEC también proporciona una mejor confiabilidad que UDP en condiciones de red con alta latencia o pérdida de paquetes, mejorando la experiencia de autenticación para los usuarios finales.

Key Terms & Definitions
RADIUS (Remote Authentication Dial-In User Service)
A client-server networking protocol (RFC 2865) that provides centralised authentication, authorisation, and accounting (AAA) for users connecting to a network. RADIUS clients (access points, switches, VPN concentrators) forward authentication requests to a central RADIUS server, which validates credentials and returns an Access-Accept or Access-Reject response.
IT teams encounter RADIUS as the authentication backbone for enterprise WiFi (802.1X), VPN access, and network device administration. Its age and architectural limitations are now a direct security liability under CVE-2024-3596.
MD5 Chosen-Prefix Collision Attack
A cryptographic attack against the MD5 hash function in which an attacker constructs two different messages with the same MD5 hash, where both messages begin with attacker-chosen prefixes. This is more powerful than a standard collision attack because the attacker can control the meaningful content of both colliding messages.
This is the specific attack technique used in Blast-RADIUS. The attacker uses it to forge a RADIUS Response Authenticator that the client will accept as genuine, even though the response content has been modified from Access-Reject to Access-Accept.
Response Authenticator
A 16-byte field in RADIUS response packets (Access-Accept, Access-Reject, Access-Challenge) computed as MD5(Code || ID || Length || RequestAuthenticator || Attributes || SharedSecret). It is intended to verify the integrity of the server response but is not a proper cryptographic MAC and is vulnerable to the Blast-RADIUS attack.
Network architects need to understand that the Response Authenticator is the specific field being forged in a Blast-RADIUS attack. Enforcing the Message-Authenticator attribute provides a stronger integrity check that is not vulnerable to the same collision technique.
Message-Authenticator Attribute
A RADIUS attribute (Attribute 80, defined in RFC 2869) that provides an HMAC-MD5 integrity check over the entire RADIUS packet, including all attributes. Unlike the Response Authenticator, the HMAC construction binds the integrity check to the shared secret in a way that prevents chosen-prefix collision forgery.
Enforcing the Message-Authenticator attribute on all RADIUS clients and servers is the primary short-term mitigation for CVE-2024-3596. IT teams should verify that all RADIUS infrastructure is patched and configured to require this attribute before accepting any response.
EAP-TLS (Extensible Authentication Protocol – Transport Layer Security)
An EAP method (RFC 5216) that uses TLS for mutual certificate-based authentication between the client and the RADIUS server. Both parties must present valid digital certificates from a trusted Certificate Authority. It is immune to the Blast-RADIUS attack and is the recommended gold standard for enterprise WiFi authentication.
CTOs and network architects should treat EAP-TLS as the target state for all enterprise WiFi authentication. It requires a PKI infrastructure but eliminates shared secrets, password-based attacks, and the MD5 vulnerability class entirely.
RADSEC (RADIUS over TLS)
A protocol extension (RFC 6614) that encapsulates RADIUS messages within a mutually authenticated TLS session over TCP, replacing the traditional UDP transport. RADSEC provides confidentiality, integrity, and replay protection for all RADIUS traffic, making transport-layer attacks such as Blast-RADIUS impossible.
RADSEC is the long-term architectural solution for RADIUS security. It is particularly valuable in distributed deployments (hotel chains, retail networks) where RADIUS traffic traverses multiple network segments. Vendors including Cisco, Juniper, Aruba, and FreeRADIUS support RADSEC.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism for devices wishing to connect to a LAN or WLAN. It uses EAP as the authentication framework and RADIUS as the backend authentication server. 802.1X ensures that only authenticated devices can access network resources.
802.1X is the framework within which RADIUS and EAP operate for enterprise WiFi. IT managers implementing WPA2/WPA3-Enterprise are deploying 802.1X. Understanding this relationship is essential for configuring authentication policies and troubleshooting access issues.
WPA3-Enterprise
The enterprise variant of the Wi-Fi Protected Access 3 (WPA3) security standard, which mandates 802.1X authentication and, in its highest security mode (192-bit), requires EAP-TLS with a 384-bit elliptic curve cipher suite. WPA3-Enterprise provides significantly stronger security guarantees than WPA2-Enterprise and is immune to the Blast-RADIUS attack when correctly configured.
Network architects planning new WiFi deployments or major infrastructure refreshes should specify WPA3-Enterprise as the minimum security standard. It is supported by all modern access points and client devices manufactured after 2020.
Man-in-the-Middle (MitM) Attack
An attack in which the adversary secretly intercepts and potentially alters communications between two parties who believe they are communicating directly with each other. In the context of Blast-RADIUS, the MitM is positioned between the RADIUS client (access point) and the RADIUS server, enabling them to intercept and forge authentication responses.
The Blast-RADIUS attack requires MitM positioning. This is achievable through ARP spoofing on a shared network segment, compromise of an intermediate network device, or physical access to network infrastructure. Understanding this threat model helps IT teams prioritise network segmentation and device hardening alongside RADIUS-specific mitigations.
Case Studies
A 350-room luxury hotel chain with 12 properties is running Cisco Meraki access points with Microsoft NPS as the RADIUS server for staff WiFi. Authentication is via MSCHAPv2. The IT director has been alerted to CVE-2024-3596 and needs to assess exposure and implement mitigations without disrupting the 24/7 hotel operations.
The immediate priority is to confirm that Microsoft NPS has been updated to include the Message-Authenticator enforcement patch (released July 2024). In NPS, navigate to the RADIUS Clients and Servers configuration and enable the 'Require Message-Authenticator' setting for all configured RADIUS clients. On the Meraki side, confirm that the firmware version supports sending the Message-Authenticator attribute in Access-Request packets — Meraki released a firmware update addressing CVE-2024-3596 in Q3 2024. This configuration change can be deployed during a low-traffic window (typically 03:00–05:00 local time) with minimal guest impact, as it affects only staff authentication. Once Phase 1 is stable, plan the migration from MSCHAPv2 to EAP-TLS. Deploy a Microsoft Active Directory Certificate Services (ADCS) PKI to issue computer certificates to all staff devices via Group Policy. Configure NPS with an EAP-TLS network policy and update the Meraki SSID security settings to WPA2/WPA3-Enterprise with EAP-TLS. Use Meraki's Systems Manager MDM to push the NPS server certificate trust anchor to all managed devices. Roll out property-by-property to manage risk, starting with the lowest-occupancy property.
A national retail chain with 200 stores uses a centralised FreeRADIUS server for 802.1X authentication on its store network infrastructure. Each store has a mix of managed corporate devices (Windows laptops, handheld scanners) and unmanaged IoT devices (digital signage, payment terminals). The network team needs to harden against Blast-RADIUS while maintaining PCI DSS compliance for the payment card environment.
Begin with a network segmentation audit to confirm that RADIUS traffic between store access points and the central FreeRADIUS server is isolated from the payment card data environment (CDE). If RADIUS traffic traverses any segment that is in PCI DSS scope, this must be addressed as a priority. Update FreeRADIUS to version 3.2.3 or later, which includes the Message-Authenticator enforcement fix. In the FreeRADIUS clients.conf file, add 'require_message_authenticator = yes' for all store RADIUS clients. For the managed device fleet, deploy EAP-TLS using an existing PKI or a cloud certificate authority. For unmanaged IoT devices that cannot support 802.1X, implement MAC Authentication Bypass (MAB) on a separate, isolated VLAN with strict firewall rules preventing lateral movement to the CDE. This ensures that even if an IoT device's MAC address is spoofed, the attacker gains access only to the IoT VLAN, not the corporate or payment network. For the RADSEC migration, deploy a RADSEC proxy at each store that terminates the local UDP RADIUS traffic and forwards it over TLS to the central FreeRADIUS server, avoiding the need to upgrade every store's network device firmware simultaneously.
Scenario Analysis
Q1. Your organisation operates a 500-seat conference centre that hosts corporate events. The venue WiFi uses WPA2-Enterprise with PEAP/MSCHAPv2 and a FreeRADIUS server. A security consultant has flagged CVE-2024-3596 in their report. The venue director wants to know: (a) Are you currently vulnerable? (b) What is the minimum action required to close the immediate risk? (c) What is the recommended long-term architecture?
💡 Hint:Consider whether PEAP provides immunity to Blast-RADIUS, and what conditions must be met for that immunity to hold. Also consider the operational constraints of a 24/7 venue environment when planning the remediation timeline.
Show Recommended Approach
(a) PEAP with MSCHAPv2 uses an EAP tunnel that protects the inner authentication from the Blast-RADIUS attack, so you are not directly vulnerable to CVE-2024-3596 — provided that clients are correctly configured to validate the FreeRADIUS server certificate. If certificate validation is not enforced, you are vulnerable to rogue access point attacks, which is a separate but equally serious risk. You should still update FreeRADIUS to the patched version and enforce Message-Authenticator as a defence-in-depth measure. (b) The minimum immediate action is to update FreeRADIUS to version 3.2.3 or later and enforce Message-Authenticator in clients.conf. Simultaneously, audit all client devices to confirm server certificate validation is enabled. (c) The recommended long-term architecture is WPA3-Enterprise with EAP-TLS, backed by a PKI for certificate issuance. For a conference centre with high device turnover and BYOD, consider a cloud-based certificate authority with automated provisioning to reduce the operational burden of certificate management.
Q2. A retail chain's security team has completed a RADIUS audit and identified three categories of devices on their store networks: (1) managed Windows laptops using MS-CHAP, (2) Android handheld scanners using PAP, (3) IoT digital signage devices that do not support 802.1X at all. Prioritise the remediation actions and explain the rationale for each device category.
💡 Hint:Consider the relative vulnerability of each authentication mode, the feasibility of migrating each device category to EAP, and the appropriate network architecture for devices that cannot support 802.1X.
Show Recommended Approach
All three categories require action, but the approach differs. Category 1 (Windows laptops, MS-CHAP): Highest priority for EAP-TLS migration because MS-CHAP is directly vulnerable to Blast-RADIUS. Deploy computer certificates via Group Policy and migrate to EAP-TLS within 30–60 days. Enforce Message-Authenticator immediately as an interim measure. Category 2 (Android scanners, PAP): Also directly vulnerable. PAP transmits credentials in a form that is trivially readable if the RADIUS traffic is intercepted, making this the highest-risk category from a credential exposure perspective as well. Migrate to PEAP or EAP-TLS using Android's built-in 802.1X support. If the scanner firmware does not support EAP, prioritise firmware updates or device replacement. Category 3 (IoT signage, no 802.1X): Cannot be migrated to EAP. Implement MAC Authentication Bypass (MAB) on a dedicated IoT VLAN with strict firewall rules preventing access to the corporate network or CDE. Accept that MAB provides weaker authentication (MAC addresses can be spoofed) and compensate with network monitoring and anomaly detection.
Q3. A CTO at a 50-property hotel chain asks you to present the business case for a full RADIUS modernisation programme (EAP-TLS + RADSEC) with an estimated budget of £180,000 over 12 months. She wants to understand: the risk being mitigated, the compliance benefits, and the operational ROI beyond security. How do you structure the business case?
💡 Hint:Frame the business case around three pillars: risk quantification (what is the cost of a breach?), compliance value (what fines or audit costs does this avoid?), and operational efficiency (what does this enable beyond security?). Use the 350-room hotel scenario as a reference point.
Show Recommended Approach
Structure the business case around three pillars. Risk Quantification: A successful Blast-RADIUS exploit at a single property could provide network access to guest PII, payment systems, and back-office infrastructure. The average hospitality data breach costs £3M+ in remediation, notification, and reputational damage. At 50 properties, the aggregate risk is significant. The £180,000 investment represents less than 6% of a single breach cost. Compliance Value: PCI DSS v4.0 requires strong authentication for all systems in scope. EAP-TLS and RADSEC directly satisfy Requirements 8.6 (authentication management) and 1.3 (network segmentation). Avoiding a PCI DSS Level 1 forensic investigation (typically £50,000–£150,000) and potential card brand fines justifies the programme cost. GDPR Article 32 requires 'appropriate technical measures' — a documented modernisation programme demonstrates compliance due diligence. Operational ROI: Certificate-based authentication eliminates the overhead of managing shared WiFi passwords across 50 properties (estimated 2–4 hours per property per year for rotation and distribution). WPA3-Enterprise improves connection reliability in high-density environments, directly improving guest satisfaction scores. RADSEC's TCP transport reduces authentication failures in properties with high-latency WAN connections. Combined, these operational benefits represent an estimated 200–300 IT hours per year in saved administration time.
Key Takeaways
- ✓CVE-2024-3596 ('Blast-RADIUS') is a practically exploitable vulnerability in RADIUS/UDP that allows a man-in-the-middle attacker to forge authentication approvals without knowing user credentials, affecting all PAP, CHAP, and MS-CHAP deployments.
- ✓The attack exploits the MD5-based Response Authenticator field in RADIUS responses using a chosen-prefix collision technique that can be executed in minutes on modern hardware — making this a real operational threat, not a theoretical one.
- ✓The immediate mitigation is to apply vendor patches for CVE-2024-3596 and enforce the Message-Authenticator attribute on all RADIUS clients and servers — a low-disruption configuration change available from all major vendors including Cisco, Microsoft NPS, FreeRADIUS, Aruba, and Ruckus.
- ✓EAP-based authentication methods (EAP-TLS, PEAP, EAP-TTLS) are immune to the Blast-RADIUS attack, making migration to WPA3-Enterprise with EAP-TLS the recommended medium-term strategic response.
- ✓RADIUS over TLS (RADSEC, RFC 6614) is the long-term architectural solution, encapsulating all RADIUS traffic in a mutually authenticated TLS tunnel and eliminating the transport-layer vulnerability entirely.
- ✓For hospitality, retail, and venue operators, the compliance implications are direct: a successful exploit can trigger PCI DSS violations, GDPR data breach notifications, and significant financial and reputational damage that far exceeds the cost of remediation.
- ✓Network segmentation (dedicated RADIUS VLANs) reduces the attack surface but does not eliminate the vulnerability — it must be combined with Message-Authenticator enforcement and EAP migration to provide genuine protection.



