¿Qué es un controlador WiFi y necesita uno?
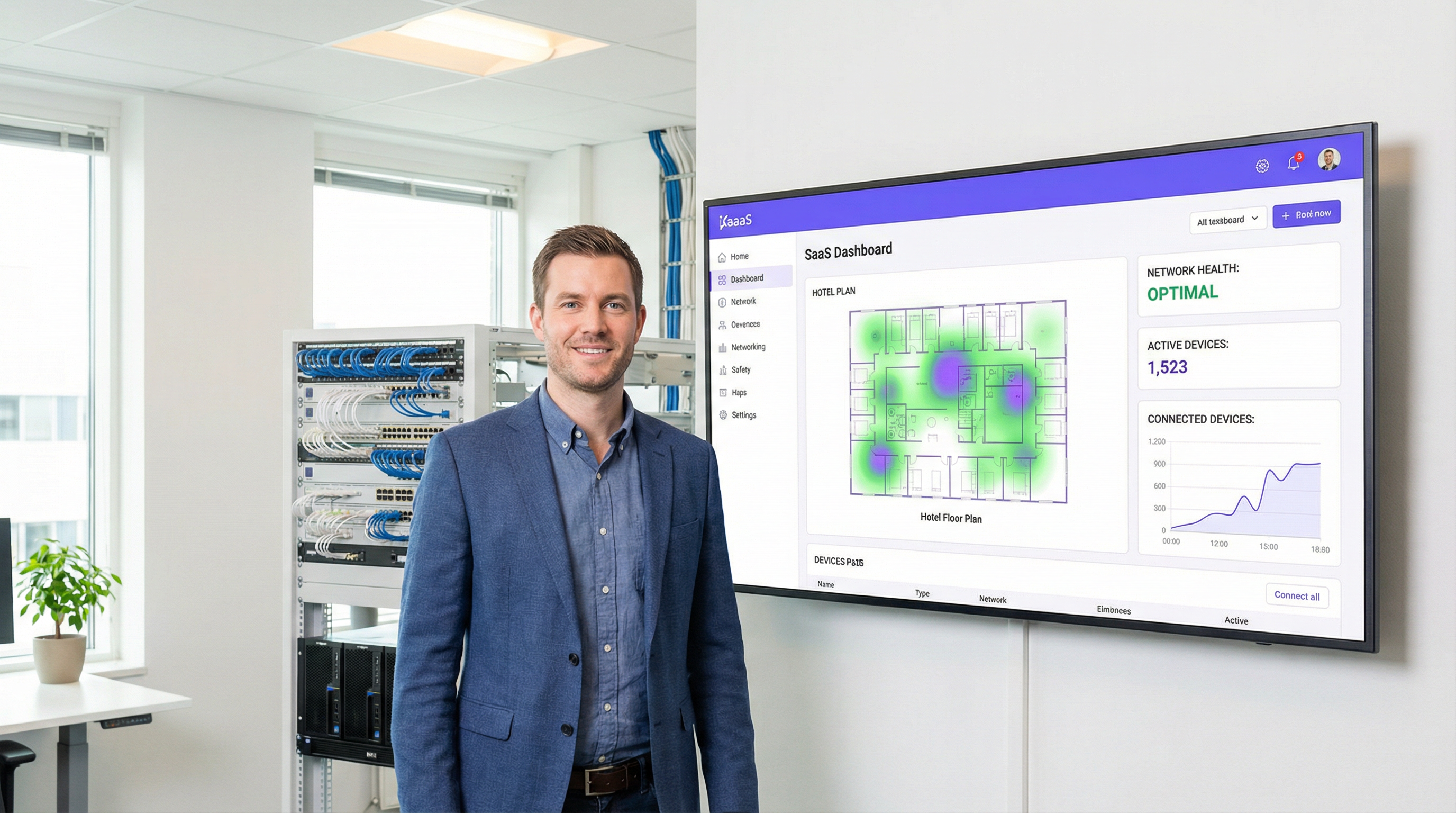
This authoritative guide provides IT leaders and network architects with a practical overview of WiFi controllers, detailing their function, comparing on-premises and cloud-based models, and explaining how they integrate with WiFi intelligence platforms like Purple. It offers actionable insights for deploying scalable, secure, and high-performance wireless networks in enterprise environments such as hospitality, retail, and large venues. By the end, readers will have a clear framework for choosing the right controller architecture and understanding where a platform like Purple adds transformative business value.
🎧 Listen to this Guide
View Transcript
Resumen ejecutivo
Un controlador de LAN inalámbrica (WLC), o controlador WiFi, es un componente de red centralizado que administra múltiples puntos de acceso (AP) desde una única interfaz, garantizando la aplicación uniforme de políticas, una administración simplificada y una mayor seguridad en toda la red inalámbrica empresarial. Para los gerentes de TI, arquitectos de redes y CTO que supervisan la conectividad en lugares como hoteles, cadenas minoristas o estadios, el controlador es el cerebro de la operación. Automatiza funciones críticas como la gestión de radiofrecuencia (RF), el roaming de clientes, la autenticación y el balanceo de carga; funciones que son simplemente imposibles de gestionar a escala con AP independientes o "autónomos".
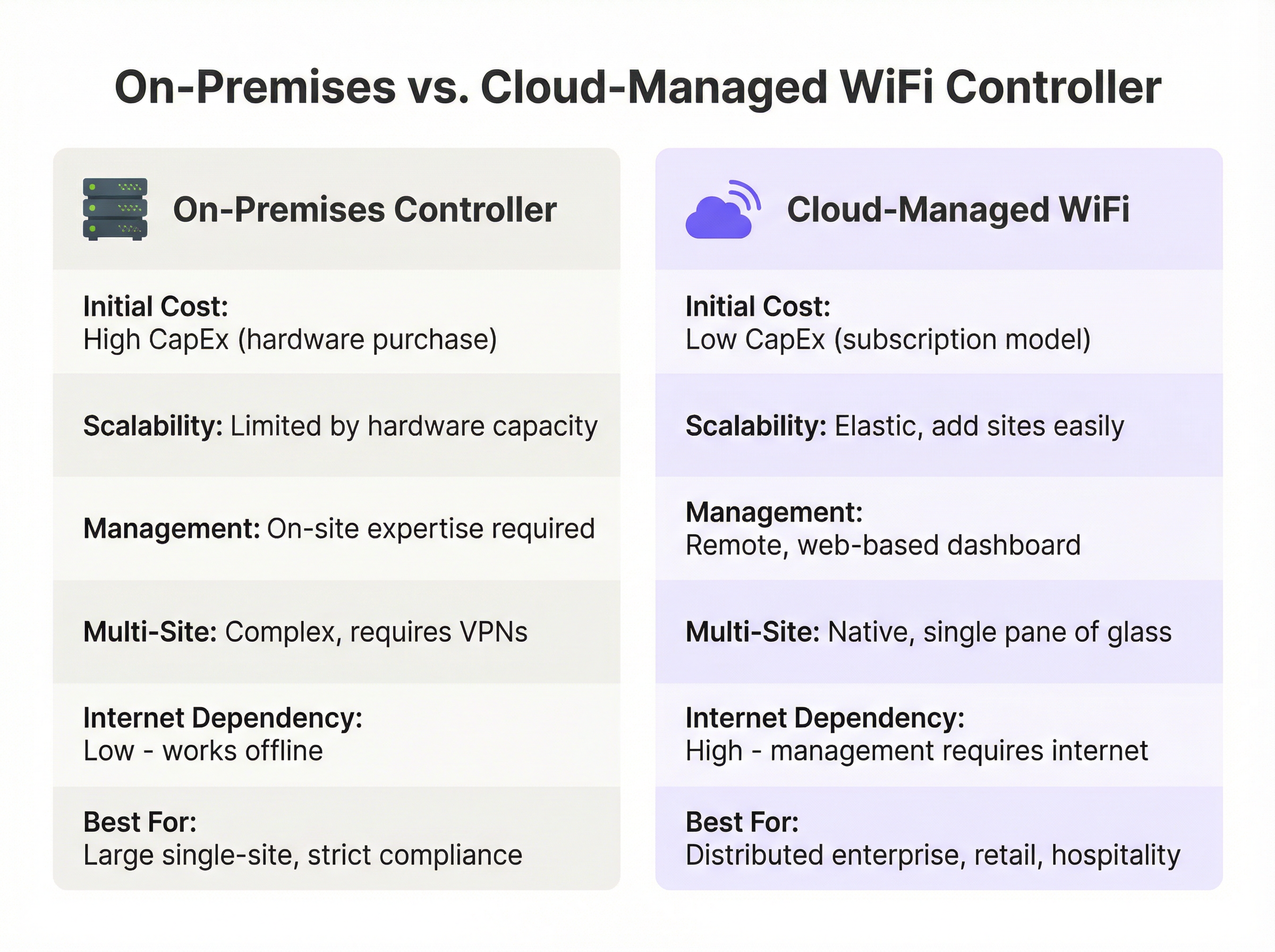
La principal decisión a la que se enfrentan los líderes hoy en día no es si utilizar un controlador, sino qué modelo de implementación adoptar: un controlador de hardware local (on-premises) tradicional o una solución moderna basada en la nube. Los controladores locales ofrecen un control granular y mantienen todo el procesamiento de datos a nivel local, un requisito clave para ciertos marcos de cumplimiento, pero exigen un gasto de capital (CapEx) significativo y experiencia especializada en el sitio. Por el contrario, el WiFi gestionado en la nube traslada la administración a un servicio basado en suscripción, ofreciendo una escalabilidad superior, aprovisionamiento zero-touch para implementaciones en múltiples sitios y una reducción de los gastos operativos.
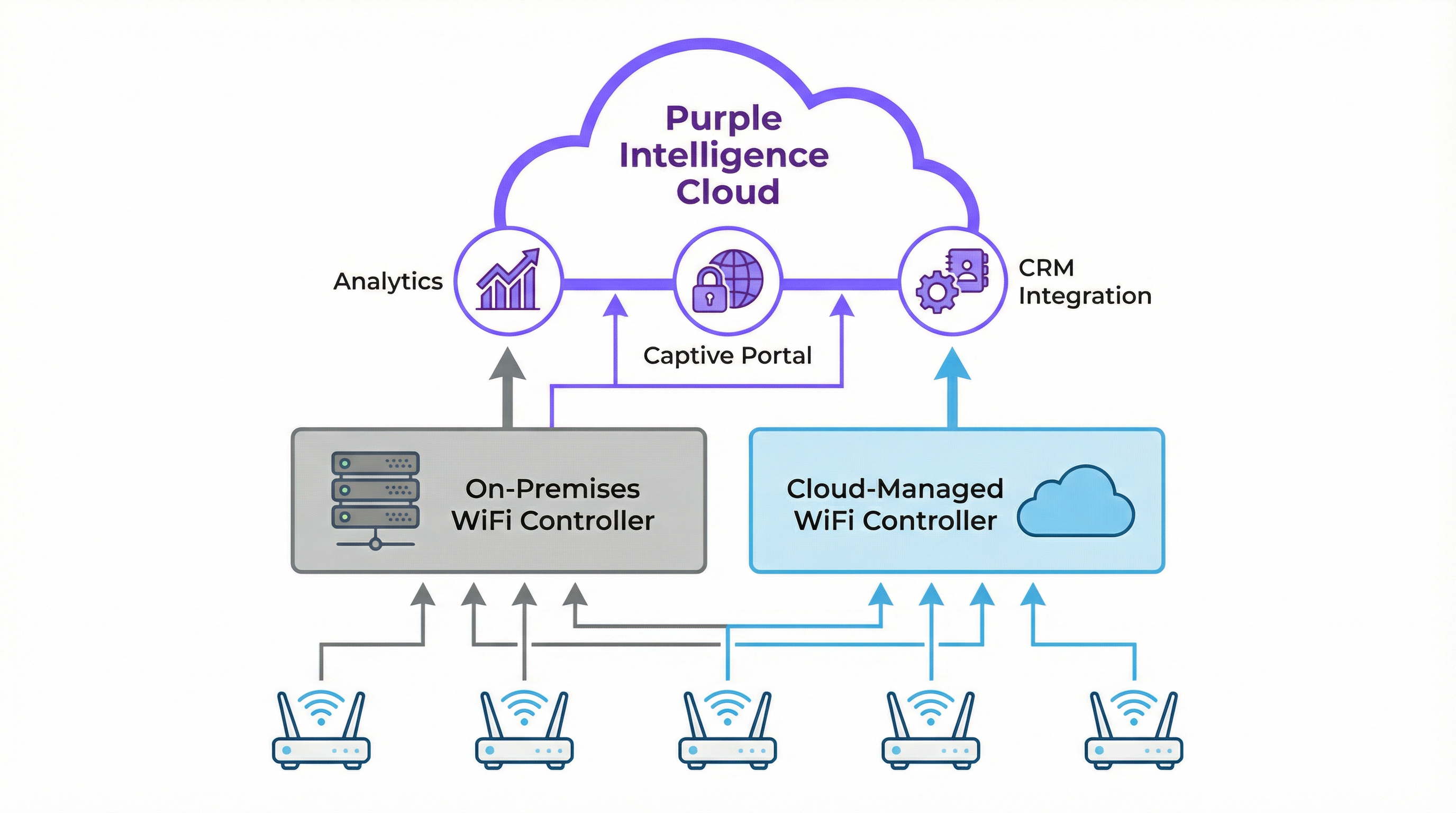
Purple actúa como una potente capa de inteligencia, integrándose con la infraestructura de controladores existente de proveedores como Cisco, Aruba y Ruckus para ofrecer servicios avanzados de WiFi para invitados, analítica y capacidades de marketing sin alterar la estructura central de la red. Esta guía proporciona un análisis técnico profundo de estas arquitecturas para ayudarle a determinar la estrategia adecuada para su organización.
Análisis técnico profundo
En esencia, un controlador WiFi resuelve el problema de la escala. Configurar un solo punto de acceso es sencillo, pero gestionar diez, cien o mil AP de forma individual es insostenible. La arquitectura WLC centraliza esta gestión, creando un sistema unificado e inteligente. Esto se logra típicamente utilizando el protocolo Control and Provisioning of Wireless Access Points (CAPWAP), un estándar IETF definido en RFC 5415. CAPWAP crea un túnel seguro entre cada AP y el controlador, separando las funciones de gestión y control (el "plano de control") del tráfico de datos del usuario final (el "plano de datos").
Las funciones clave del controlador abarcan todo el ciclo de vida de la gestión de redes inalámbricas. La gestión centralizada de AP es el rol más fundamental: desde el controlador, los administradores pueden enviar actualizaciones de firmware, configurar SSID, establecer políticas de seguridad como WPA3-Enterprise y definir VLAN para todos los AP conectados simultáneamente. La gestión dinámica de RF permite al controlador monitorear continuamente el espectro de radiofrecuencia, ajustando automáticamente las asignaciones de canales de los AP y los niveles de potencia para mitigar la interferencia y optimizar la cobertura. El roaming de clientes sin interrupciones es facilitado por el controlador que gestiona las claves de seguridad y el estado de la sesión a medida que los usuarios se mueven entre los AP, aprovechando los estándares 802.11k/v/r para transiciones rápidas. La autenticación y aplicación de políticas permite que el WLC actúe como un guardián central, integrándose con un servidor RADIUS e IEEE 802.1X para otorgar acceso a la red en función de la identidad del usuario y la postura del dispositivo, lo que permite un control de acceso robusto basado en roles.
Local (On-Premises) vs. Gestionado en la nube: El compromiso arquitectónico
La elección estratégica entre un WLC local y uno gestionado en la nube tiene implicaciones significativas en cuanto a costos, escalabilidad y operaciones. La siguiente tabla resume los compromisos clave.
| Característica | Controlador local (On-Premises) | WiFi gestionado en la nube |
|---|---|---|
| Modelo de implementación | Dispositivo físico o virtual en un centro de datos local | Plano de gestión alojado por un proveedor externo |
| Costo inicial (CapEx) | Alto: dispositivos de hardware con límites de capacidad específicos | Bajo: no requiere hardware de controlador en el sitio |
| Costo operativo (OpEx) | Costos recurrentes más bajos, pero incluye energía y mantenimiento | Costos recurrentes más altos a través de una licencia de suscripción anual |
| Escalabilidad | Limitada por la capacidad del hardware; las actualizaciones requieren hardware nuevo | Altamente elástica; se agregan nuevos AP y sitios con un ajuste de licencia |
| Gestión en múltiples sitios | Compleja; a menudo requiere VPN o controladores dedicados por sitio | Sencilla; un único panel web proporciona una vista global unificada |
| Dependencia de Internet | Baja; el WiFi central continúa si falla Internet | Alta; se requiere Internet para la gestión y configuración |
| Cumplimiento y datos | Ideal para requisitos estrictos de soberanía de datos | Requiere la debida diligencia del proveedor para el cumplimiento de GDPR y PCI DSS |
Cómo se integra Purple con su controlador
Purple es una plataforma de inteligencia WiFi basada en la nube que funciona como una sofisticada capa superpuesta, mejorando las capacidades de su infraestructura de red existente en lugar de reemplazarla. Se integra a la perfección con arquitecturas de controladores tanto locales como gestionadas en la nube de más de 200 proveedores de hardware.
La integración sigue una secuencia clara. Primero, el controlador WiFi se configura para redirigir todos los dispositivos de invitados nuevos y no autenticados al Captive Portal de Purple. Luego, el usuario se autentica a través de una página de inicio personalizada, utilizando inicios de sesión sociales, el envío de un formulario o perfiles fluidos de Passpoint/OpenRoaming; un proceso que cumple totalmente con GDPR y CCPA. Tras una autenticación exitosa, Purple captura valiosos datos demográficos y de comportamiento con el consentimiento del usuario, los cuales alimentan el motor de analítica y pueden integrarse con su CRM. Finalmente, Purple le indica al controlador que otorgue acceso a Internet al dispositivo, aplicando cualquier política predefinida, como límites de ancho de banda, duración de la sesión o filtrado de contenido a través de Purple Shield.
Este modelo permite a las organizaciones conservar su inversión en hardware robusto de nivel empresarial mientras añaden potentes herramientas de analítica y de interacción con los invitados que impulsan el valor comercial.
Guía de implementación
Implementar o actualizar la arquitectura de su controlador WiFi requiere un enfoque estructurado. Esta guía, independiente del proveedor, describe las fases clave para una implementación exitosa.
Fase 1: Descubrimiento y recopilación de requisitos. Realice un estudio de RF físico o predictivo para determinar el número óptimo y la ubicación de los puntos de acceso, teniendo en cuenta los materiales de construcción, la densidad de usuarios y los requisitos de rendimiento de las aplicaciones. Documente los principales casos de uso (acceso de invitados, personal interno, sistemas de punto de venta, dispositivos IoT), ya que estos dictarán las políticas de segmentación y seguridad. Catalogue su infraestructura de red actual e identifique todos los requisitos normativos, incluidos PCI DSS para el comercio minorista y GDPR para el manejo de datos de ciudadanos de la UE.
Fase 2: Selección de la arquitectura. Utilice la tabla comparativa y el diagrama de flujo de decisiones de esta guía para elegir entre soluciones locales y gestionadas en la nube. Para la mayoría de las empresas con múltiples sitios en los sectores minorista, hotelero y similares, la eficiencia operativa y la escalabilidad de una arquitectura gestionada en la nube presentan un caso de negocio convincente.
Fase 3: Implementación y configuración. Configure VLAN separadas para cada grupo de usuarios (Invitados, Personal, Corporativo, IoT); esta es una medida de seguridad crítica. Para los sistemas gestionados en la nube, registre previamente los AP en el panel de control para habilitar el aprovisionamiento zero-touch. Implemente WPA3-Enterprise con IEEE 802.1X para todas las redes seguras. Para la red de invitados, configure un SSID abierto con el aislamiento de clientes habilitado, forzando todo el tráfico a través del Captive Portal de Purple. Configure la URL del Captive Portal de Purple como la fuente de autenticación externa en la configuración de su controlador y agregue las direcciones IP requeridas a sus listas de control de acceso previas a la autenticación.
Fase 4: Pruebas y validación. Realice un estudio de RF posterior a la implementación para verificar la cobertura. Pruebe el proceso de incorporación (onboarding) para cada grupo de usuarios. Realice pruebas de rendimiento utilizando herramientas como iPerf para garantizar que la red cumpla con los puntos de referencia de rendimiento.
Mejores prácticas
Priorizar la seguridad a través de la segmentación de la red no es negociable. El tráfico de invitados nunca debe compartir una VLAN con el tráfico corporativo o que cumpla con PCI. Habilitar el aislamiento de clientes en las redes de invitados es una característica crítica del WLC que evita que los clientes inalámbricos se comuniquen entre sí, mitigando los riesgos de ataques de igual a igual (peer-to-peer). Centralizar la autenticación con un servidor RADIUS junto con el WLC proporciona una base de datos única y auditable de usuarios y políticas. Las actualizaciones periódicas de firmware tanto para el controlador como para los AP son esenciales, ya que son activos de seguridad críticos. Las soluciones gestionadas en la nube suelen automatizar este proceso, lo que supone una ventaja operativa significativa. Por último, el monitoreo continuo a través del panel del controlador y la analítica de Purple permite a los equipos de TI identificar de manera proactiva problemas de rendimiento, AP no autorizados (rogue APs) y anomalías de seguridad antes de que afecten a los usuarios.
Solución de problemas y mitigación de riesgos
Cuando los clientes no pueden conectarse, el primer paso de diagnóstico es verificar si hay errores de autenticación en el controlador: verifique que el servidor RADIUS sea accesible, que las credenciales del cliente sean correctas y que las direcciones IP del portal de Purple estén correctamente incluidas en la lista blanca de las ACL previas a la autenticación del controlador. El bajo rendimiento inalámbrico generalmente apunta a interferencias de RF o canales sobrecargados, lo que se puede diagnosticar a través del panel de gestión de RF del controlador. Las áreas de alta densidad pueden requerir AP adicionales o una reevaluación de las asignaciones de canales.
Para las implementaciones locales, el riesgo principal es la falla del hardware del controlador. Esto se mitiga implementando controladores en un par de alta disponibilidad (HA), una configuración activa/en espera, y manteniendo copias de seguridad periódicas de la configuración del controlador. Para las redes gestionadas en la nube, el riesgo es la pérdida de conectividad a Internet. Los AP deben configurarse para continuar brindando acceso a la red local durante las interrupciones, y los servicios operativos críticos no deben depender del enlace de gestión en la nube.
ROI e impacto comercial
Una red inalámbrica con la arquitectura adecuada no es un centro de costos; es un facilitador de negocios. El ROI se extiende mucho más allá de proporcionar una simple conexión a Internet. La gestión centralizada reduce drásticamente los gastos generales de TI, como lo demostró McDonald's, donde la analítica y las capacidades de gestión remota de Purple llevaron a una reducción del 90 % en las visitas al sitio de ingenieros de TI, con 4 millones de inicios de sesión WiFi por restaurante al año y 2.5 millones de usuarios únicos capturados en el CRM.
Un WiFi rápido, confiable y de fácil acceso es ahora una expectativa básica en la hotelería y el comercio minorista. Una experiencia fluida, facilitada por el roaming gestionado por el controlador y una incorporación sencilla a través del portal de Purple, impacta directamente en la satisfacción y lealtad del cliente. Al integrar Purple, la red WiFi se transforma en una rica fuente de datos de origen (first-party data), lo que permite a los operadores de los recintos medir la afluencia, los tiempos de permanencia y la frecuencia de los visitantes. Estos datos proporcionan un ROI tangible, y los clientes de Purple ven un ROI promedio del 873 %. Para lugares como centros de conferencias u hoteles, el acceso WiFi premium por niveles también puede convertirse en una fuente de ingresos directa, fácilmente gestionada y automatizada a través del controlador y la plataforma Purple.
Key Terms & Definitions
Wireless LAN Controller (WLC)
A centralized network appliance or cloud service that configures, manages, and monitors wireless access points at scale, handling functions such as RF management, roaming, authentication, and security policy enforcement.
This is the core component for any enterprise-grade WiFi deployment. IT teams use the WLC to avoid having to configure hundreds of APs individually and to ensure a consistent, secure experience across the entire network.
Access Point (AP)
A hardware device that creates a wireless local area network (WLAN) by transmitting and receiving radio signals. In a controller-based architecture, APs are 'lightweight' devices whose intelligence is provided by the central WLC.
These are the physical devices installed in ceilings and walls throughout a venue. In enterprise settings, they are often referred to as 'thin' or 'lightweight' APs because the controller provides their configuration and management logic.
Cloud-Managed WiFi
An architecture where the WLC functionality is hosted in the cloud as a subscription service, allowing for centralized management of geographically distributed APs via a web-based dashboard without any on-site controller hardware.
This is the dominant model for retail, hospitality, and distributed enterprises due to its scalability and operational simplicity. Purple is a cloud-native platform that integrates perfectly with this model.
CAPWAP (Control and Provisioning of Wireless Access Points)
An IETF standard protocol (RFC 5415) that enables a WLC to manage a collection of access points by establishing a secure, encrypted tunnel for control traffic and, optionally, data traffic.
This is the technical underpinning of how controllers and APs communicate. Understanding CAPWAP is essential for troubleshooting connectivity issues between the controller and its managed APs, particularly in complex network topologies.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication framework requiring devices to present valid credentials before being granted access to a LAN or WLAN.
This is the gold standard for securing corporate wireless networks. It requires users to authenticate with unique credentials before being granted access, managed by the WLC in conjunction with a RADIUS server. It is a key requirement for PCI DSS and ISO 27001 compliance.
Captive Portal
A web page displayed to newly connected users of a WiFi network before they are granted broader internet access, typically used for authentication, terms-of-service acceptance, or data capture.
This is Purple's core entry point for guest users. The WLC is configured to redirect all unauthenticated guest devices to the Purple captive portal, which then handles the entire user onboarding journey, from authentication to data capture.
Network Segmentation
The practice of dividing a computer network into distinct subnetworks (VLANs) to improve security, performance, and compliance by preventing unauthorized traffic between segments.
This is a non-negotiable best practice enforced via the WLC. Separating guest traffic from corporate and POS systems is a fundamental security requirement and a compliance obligation under PCI DSS for any organization processing card payments.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards mandating that all companies that accept, process, store, or transmit credit card information maintain a secure environment, including strict network segmentation requirements.
For any retail or hospitality client, the WLC and network architecture must be configured to meet PCI DSS requirements. Failure to comply can result in significant fines and the revocation of the ability to process card payments.
Case Studies
A 250-room luxury hotel needs to upgrade its legacy WiFi network to provide seamless, high-performance coverage for guests and staff while enabling marketing to capture guest data for loyalty programs. The hotel has a central server room and a dedicated IT team.
1. Architecture Choice: A hybrid approach is recommended. Deploy on-premises controllers in a high-availability (HA) pair to manage all on-site access points. This ensures maximum performance and resilience for in-room streaming and staff operational systems. 2. Network Segmentation: Create distinct VLANs and SSIDs: 'HotelGuest' (open, with captive portal), 'Staff_Secure' (WPA3-Enterprise with 802.1X), and 'POS_Systems' (WPA3-Enterprise, highly restricted, firewalled from guest VLAN). 3. Purple Integration: Configure the controllers to redirect the 'HotelGuest' SSID to the Purple cloud-based captive portal. The portal handles guest authentication via room number and last name, or social login, and captures opt-in marketing consent. 4. Policy Enforcement: The controller enforces a bandwidth limit of 25 Mbps per guest device, while the Purple platform manages session duration and feeds data directly into the hotel's Salesforce CRM, enabling targeted loyalty campaigns.
A retail chain with 80 stores across the country wants to standardize its in-store guest WiFi experience, centrally manage all networks, and use WiFi analytics to understand customer footfall patterns. Each store has limited on-site technical staff.
1. Architecture Choice: A fully cloud-managed WiFi solution is the clear choice. Equip each store with cloud-managed access points from a single vendor. There is no need for an on-premises controller in any store. 2. Zero-Touch Provisioning: APs are pre-configured in the central cloud dashboard and shipped to each store. The local store manager simply plugs them in — the AP automatically downloads its configuration. 3. Centralized Management: From corporate headquarters, the IT team uses a single web dashboard to monitor all 80 stores, push configuration updates, and manage security policies simultaneously. 4. Purple Integration: The cloud controller is configured globally to use Purple for guest authentication across all stores, ensuring a consistent branded experience. Purple's analytics dashboard provides footfall, dwell time, and loyalty metrics for every store, enabling direct comparison of performance across the estate.
Scenario Analysis
Q1. A large conference center is preparing for a major tech summit expecting 10,000 concurrent users, all requiring high-throughput video streaming. They have a large, expert IT team on-site and a dedicated server room. Which controller architecture should they primarily rely on and why?
💡 Hint:Consider the requirements for latency, throughput, and the value of on-site expertise in a single-location, high-density scenario.
Show Recommended Approach
They should deploy a high-capacity, on-premises controller cluster in a high-availability (active/standby) configuration. For a high-density, single-site event, minimizing latency and maximizing throughput is critical. Routing all traffic through a powerful on-site controller avoids the latency of cloud-based data paths and provides the advanced RF management needed to handle 10,000 concurrent users. The presence of an expert on-site IT team mitigates the management overhead of an on-premises solution. Purple would be integrated as an overlay for guest authentication and analytics.
Q2. A fast-growing coffee shop chain plans to expand from 10 to 50 locations in the next year. They want to offer a consistent, branded guest WiFi experience at all stores and use the data for marketing campaigns. Their corporate IT team consists of just two people. What is the single most critical feature they should look for in a WiFi solution?
💡 Hint:Think about the operational challenge of deploying and managing 50 separate locations with a two-person IT team.
Show Recommended Approach
The most critical feature is zero-touch provisioning via a cloud-based management dashboard. This will allow their small IT team to pre-configure access points in the cloud dashboard and ship them to new stores. The local store manager simply plugs in the AP, and it automatically downloads its configuration — no specialist IT visit required. A cloud architecture is essential for them to scale rapidly and manage all 50 locations from a single interface, ensuring a consistent guest experience and centralized data collection via Purple.
Q3. A hospital needs to provide guest WiFi for patients and visitors while ensuring that patient health records, stored on a separate internal clinical network, remain completely isolated and secure. How should the IT team use a WLC to achieve this, and what specific configuration steps are required?
💡 Hint:Focus on the security and traffic separation capabilities of the WLC, and consider both the technical and compliance dimensions.
Show Recommended Approach
The IT team must use the WLC to implement strict network segmentation. The specific steps are: (1) Create a dedicated 'Guest' SSID on a separate VLAN (e.g., VLAN 100) that is completely firewalled from all internal clinical VLANs. (2) Configure an Access Control List (ACL) on the controller that explicitly denies any traffic originating from VLAN 100 from reaching the internal network segments. (3) Enable 'client isolation' on the guest SSID to prevent guest devices from communicating with each other. (4) Configure the guest SSID to redirect unauthenticated clients to the Purple captive portal for terms-of-service acceptance. This architecture ensures compliance with healthcare data regulations and protects patient data from both external and internal threats.
Key Takeaways
- ✓A WiFi Controller (WLC) centralizes the management of multiple access points, providing the consistency, security, and scalability that enterprise wireless networks demand.
- ✓The primary architectural choice is between on-premises controllers (high control, high CapEx, ideal for single-site or strict compliance environments) and cloud-managed controllers (high scalability, subscription-based, ideal for distributed enterprises).
- ✓Cloud-managed WiFi is the dominant choice for distributed enterprises in retail and hospitality due to zero-touch provisioning, single-pane-of-glass management, and elastic scalability.
- ✓Purple is a cloud-based intelligence platform that acts as an overlay on existing WiFi infrastructure — it does not replace the controller, but enhances it with guest authentication, analytics, and CRM integration.
- ✓Security is non-negotiable: use the WLC to enforce network segmentation (separate VLANs for guests, staff, and POS), enable client isolation on guest networks, and implement WPA3-Enterprise with IEEE 802.1X for secure access.
- ✓The ROI of a modern WiFi architecture is driven by operational efficiency, enhanced customer experience, and the business intelligence derived from WiFi analytics — Purple customers see an average ROI of 873%.
- ✓The core framework: your controller manages the APs; a platform like Purple manages the users — turning connectivity from a cost centre into a source of measurable business value.



