Captura de datos WiFi: Una guía completa sobre privacidad, cumplimiento y mejores prácticas
This guide provides IT leaders with a comprehensive technical reference for implementing WiFi data capture solutions. It focuses on navigating the complex landscape of privacy, legal compliance (GDPR, CCPA), and data ethics, offering actionable best practices for venue operators in hospitality, retail, and large public spaces.
🎧 Listen to this Guide
View Transcript

Resumen ejecutivo
Para la empresa moderna, comprender el espacio físico es tan fundamental como comprender el digital. La captura de datos WiFi ha surgido como una herramienta poderosa para que los operadores de recintos obtengan información profunda y procesable sobre el comportamiento de los visitantes, la afluencia y la utilización del espacio. Al analizar las solicitudes de sondeo emitidas pasivamente por dispositivos con WiFi, las organizaciones pueden desbloquear inteligencia transformadora para optimizar la distribución, mejorar la experiencia del cliente y aumentar la eficiencia operativa. Sin embargo, esta capacidad conlleva importantes obligaciones legales y éticas. Los reguladores a nivel mundial, bajo marcos como el GDPR y la CCPA, clasifican los identificadores de dispositivos, como las direcciones MAC, como datos personales. En consecuencia, su recopilación y procesamiento están sujetos a reglas estrictas en cuanto a consentimiento, anonimización y gobernanza de datos. Esta guía sirve como una referencia práctica y autorizada para CTOs, gerentes de TI y arquitectos de redes. Va más allá de la teoría académica para proporcionar estrategias neutrales en cuanto a proveedores y listas para su implementación, con el fin de establecer un programa de análisis WiFi que no solo sea potente, sino también seguro, que cumpla con las normativas y sea respetuoso con la privacidad del usuario. Exploraremos la arquitectura técnica, delinearemos metodologías de implementación sólidas y proporcionaremos mejores prácticas claras y procesables para mitigar riesgos y maximizar el ROI.
Análisis técnico detallado
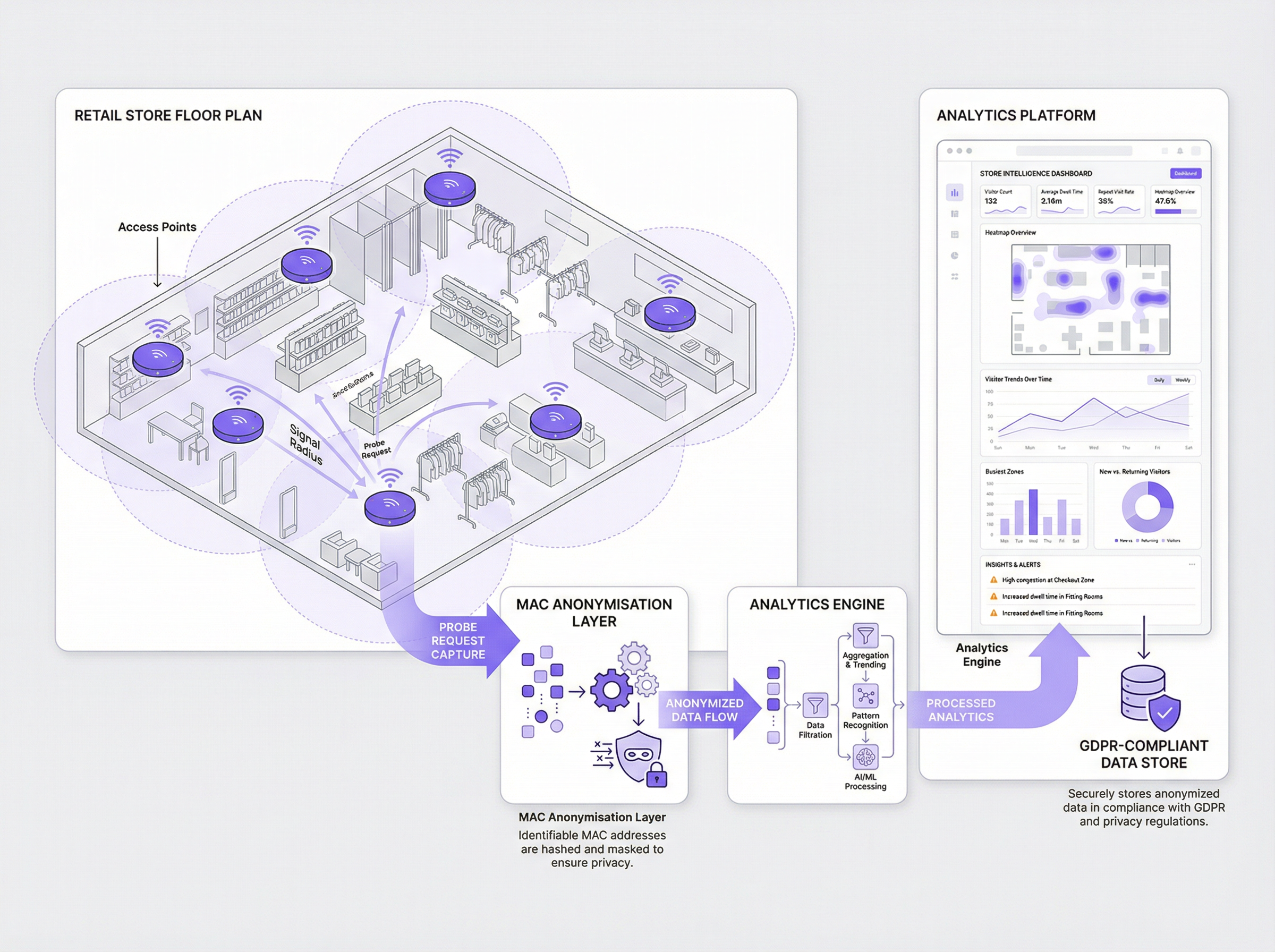
La base de la analítica WiFi radica en la captura de tramas de gestión 802.11, específicamente las solicitudes de sondeo. Todo dispositivo con WiFi (smartphone, laptop, tablet) transmite periódicamente estas solicitudes para descubrir redes inalámbricas cercanas. Cada trama contiene varios datos clave, pero el más crítico para la analítica es la dirección de Control de Acceso al Medio (MAC) del dispositivo: un identificador de hardware único. Al implementar sensores o configurar los puntos de acceso existentes para escuchar estas tramas, un sistema puede detectar la presencia, ubicación y movimiento de los dispositivos dentro de un espacio físico.
Métodos de captura de datos:
- Captura pasiva: Este método utiliza sensores que escuchan pasivamente las solicitudes de sondeo sin requerir que los usuarios se conecten a la red. Proporciona una visión amplia de todos los dispositivos en un área, ofreciendo datos valiosos sobre la afluencia total y los patrones de movimiento. Sin embargo, dado que no hay interacción directa con el usuario, obtener un consentimiento explícito es un desafío, por lo que una anonimización robusta e inmediata es primordial.
- Captura activa (Captive Portal): Este método requiere que el usuario se conecte activamente a la red WiFi de invitados del recinto. El proceso de conexión está mediado por un Captive Portal, que presenta una página de inicio de sesión o de bienvenida. Este es el mecanismo estándar de la industria para obtener el consentimiento explícito e informado del usuario antes de procesar cualquier dato. Aunque solo captura datos de usuarios conectados, proporciona una base legal mucho más sólida para el procesamiento de datos y permite análisis más ricos y vinculados a la identidad si el usuario se autentica.
El imperativo de la anonimización: Bajo el GDPR, una dirección MAC se considera un dato personal. Por lo tanto, no puede almacenarse en su formato original. La mejor práctica es aplicar un hash criptográfico unidireccional (por ejemplo, SHA-256) combinado con un salt rotativo inmediatamente después de la captura. Este proceso, conocido como seudonimización, transforma la dirección MAC en un identificador único e irreversible que no puede rastrearse hasta el dispositivo original. Este ID anonimizado puede usarse luego para análisis, como calcular visitas recurrentes, sin almacenar datos personales.
Impacto de la aleatorización de direcciones MAC: Los sistemas operativos móviles modernos (iOS 14+ y Android 10+) han implementado la aleatorización de direcciones MAC para mejorar la privacidad del usuario. Estos dispositivos transmiten una dirección MAC diferente y aleatoria para cada nueva red WiFi que sondean. Si bien esta es una función a favor de la privacidad, presenta un desafío significativo para las plataformas de análisis tradicionales, ya que un solo dispositivo puede aparecer como múltiples visitantes únicos. Los motores de análisis sofisticados, como los de Purple, emplean algoritmos avanzados para identificar y conciliar de manera inteligente estas direcciones aleatorias, garantizando la precisión de las métricas de visitantes. Esta es una capacidad técnica crítica para cualquier implementación moderna de análisis WiFi.
Guía de implementación
Implementar una solución de captura de datos WiFi que cumpla con las normativas requiere un enfoque estructurado y de múltiples etapas basado en el principio de 'Privacidad desde el diseño'.
Paso 1: Evaluación de la infraestructura Comience por auditar su infraestructura WiFi existente. Los puntos de acceso modernos de nivel empresarial de proveedores como Cisco, Meraki, Aruba y Ruckus a menudo tienen capacidades integradas para transmitir tramas de gestión a un servidor de análisis. Determine si su hardware es compatible con esto o si se requieren sensores dedicados. Asegure una cobertura adecuada en todas las áreas donde pretende capturar datos.
Paso 2: Definir su política de datos y mecanismo de consentimiento Este es el paso más crítico para el cumplimiento normativo. Trabaje con sus equipos legales y de cumplimiento para definir:
- Qué datos recopilará: Sea específico (por ejemplo, "
Key Terms & Definitions
MAC Address (Media Access Control)
A unique, 48-bit hardware number that identifies each device on a network. Under GDPR, it is considered Personal Identifiable Information (PII).
This is the core piece of data captured by WiFi analytics. IT teams must ensure it is never stored in its raw format and is anonymized immediately upon capture.
Probe Request
An 802.11 management frame sent by a WiFi-enabled device to discover nearby wireless networks.
These are the signals that WiFi analytics systems listen for. Understanding the volume and signal strength of probe requests allows the system to determine footfall and location.
Captive Portal
A web page that a user must view and interact with before being granted access to a public WiFi network.
This is the primary and most effective mechanism for an IT team to obtain explicit, informed consent from users before collecting and processing their data for analytics purposes.
Pseudonymization (Hashing)
The process of replacing a data identifier (like a MAC address) with a pseudonym (a cryptographic hash). It is a reversible process if the key is known, but one-way hashing makes it irreversible.
This is the critical technical process for making WiFi data compliant. A raw MAC address is PII; a hashed MAC address is an anonymized data point that can be used for analysis.
MAC Address Randomization
A privacy feature in modern mobile operating systems (iOS, Android) where the device uses a fake, temporary MAC address when searching for networks.
IT teams must be aware that this feature can severely skew analytics data. A modern analytics platform is required to correctly interpret these randomized addresses and avoid overcounting visitors.
GDPR (General Data Protection Regulation)
A comprehensive data protection law in the European Union that governs the processing of personal data.
This is the key regulation governing WiFi data capture in Europe. Any organisation with a European presence or that serves European citizens must ensure their analytics deployment is fully GDPR-compliant.
Data Controller
The entity that determines the purposes and means of processing personal data.
When a venue deploys WiFi analytics, the venue owner (e.g., the retail chain, the hotel) is the Data Controller and is legally responsible for ensuring compliance.
Dwell Time
A metric that measures the average amount of time visitors spend in a specific, defined area.
This is one of the most valuable business insights from WiFi analytics. It helps operations directors understand engagement, identify bottlenecks, and measure the success of marketing displays or layout changes.
Case Studies
A 50-store retail chain wants to understand customer behaviour in their flagship stores to inform a nationwide redesign. They need to measure dwell times in different departments, identify popular paths, and understand repeat visitor frequency, all while ensuring strict GDPR compliance.
- Infrastructure: Deploy a Purple-compatible WiFi analytics solution using their existing Meraki MR access points. Configure the Meraki dashboard to stream analytics data to the Purple cloud.
- Consent: Implement a branded captive portal for the guest WiFi network. The portal will feature a single, clear opt-in checkbox: "I agree to allow Purple to analyse my anonymized visit data to help improve the store layout and experience. This data is fully anonymized and will not be used for marketing." A link to the full privacy policy is provided.
- Anonymization: Configure the system to use Purple's patented Cryptographic Anonymization, which hashes the MAC address at the moment of capture. This ensures no PII is ever stored.
- Analysis: Use the Purple dashboard to create zones for each department (e.g., Menswear, Womenswear, Checkout). Track anonymized visitor flow between these zones and measure average dwell times. Use the repeat visitor metric to understand customer loyalty.
- Action: After 90 days, the data reveals that the Menswear department has high traffic but low dwell time. The chain redesigns the department layout to be more open and improves product displays. They then measure the impact of these changes over the next 90 days.
A large conference centre with multiple exhibition halls hosts a variety of third-party events. They want to offer event organisers data on attendee flow and booth popularity, but they are concerned about the privacy implications of tracking attendees across different, unrelated events.
- Data Segregation: The key is to treat each event as a separate entity. The WiFi analytics platform must be configured to use a different rotating salt for its hashing algorithm for each event. This means an anonymized ID from Event A will not be the same as the anonymized ID for the same device at Event B.
- Organiser Portals: Provide each event organiser with a separate, sandboxed view of the analytics data for their event only. They should not have access to historical data from other events or raw data of any kind.
- Consent per Event: The captive portal for each event must be unique and clearly state which organiser is the data controller for that event. Attendees must provide consent for each event they attend.
- Reporting: The platform can then generate reports on footfall, hall traffic, and booth dwell times for each specific event. This data can be sold to organisers as a premium service.
- Data Purge: Implement a strict data retention policy to purge all data associated with an event 30 days after the event concludes.
Scenario Analysis
Q1. A stadium is deploying a new WiFi analytics system to manage crowd flow on match days. Their legal team is concerned about storing location data. What is the most important technical control to implement regarding location?
💡 Hint:Think about the principle of data minimisation.
Show Recommended Approach
The most important control is to not store raw or fine-grained location data (e.g., X-Y coordinates). Instead, the stadium should be divided into large, pre-defined zones (e.g., "North Stand, Level 1", "West Entrance Gate"). The system should only record which zone a device is in, not its precise location within that zone. This minimises the sensitivity of the location data while still providing the necessary operational insights for crowd management.
Q2. A shopping mall uses a third-party to manage its guest WiFi. The third-party offers a 'free' analytics package. What is the number one question the mall's CTO should ask the third-party vendor?
💡 Hint:Who is the Data Controller and what are their responsibilities?
Show Recommended Approach
The CTO must ask: "Where and how is the MAC address anonymized?" They need to get a specific, technical answer. If the vendor cannot confirm that the MAC address is hashed with a salt, on-premise, before it is sent to their cloud, it is a major compliance red flag. The mall, as the Data Controller, is ultimately liable for any data breach or non-compliance, even if it is caused by their vendor.
Q3. A user logs into your guest WiFi and consents to analytics. They later submit a 'Right to be Forgotten' request under GDPR. You have stored their data as a hashed, anonymized ID. What is your technical obligation?
💡 Hint:How does pseudonymization relate to a user's rights?
Show Recommended Approach
Even though the data is pseudonymized, it is still linked to a specific individual, and the user's rights still apply. The analytics platform must have a mechanism to process these requests. When the user made the request, they would have provided an identifier (e.g., the email they used to log in). The platform needs a secure, audited process to look up the anonymized IDs associated with that user account and permanently delete them from the analytics database. Simply saying 'the data is anonymous' is not a compliant response.
Key Takeaways
- ✓WiFi data capture offers powerful insights but carries significant privacy obligations.
- ✓A MAC address is personal data under GDPR; it must be anonymized at the point of capture.
- ✓Explicit user consent via a captive portal is the best practice for compliance.
- ✓Modern analytics platforms are essential to handle challenges like MAC address randomization.
- ✓Adopt a 'Privacy by Design' approach, building compliance into your architecture from day one.
- ✓Transparency with users is not just a legal requirement; it is crucial for building trust.
- ✓Regularly audit your system and policies to ensure ongoing compliance and risk mitigation.



