Authentification SMS pour le WiFi : comment ça marche et quand l'utiliser
A technical reference for IT managers and venue operators on implementing SMS-based WiFi authentication. This guide details the technical workflow, compares it against social login, and provides actionable best practices for deployment in enterprise environments like hotels, retail, and stadiums.
🎧 Écouter ce guide
Voir la transcription
Synthèse
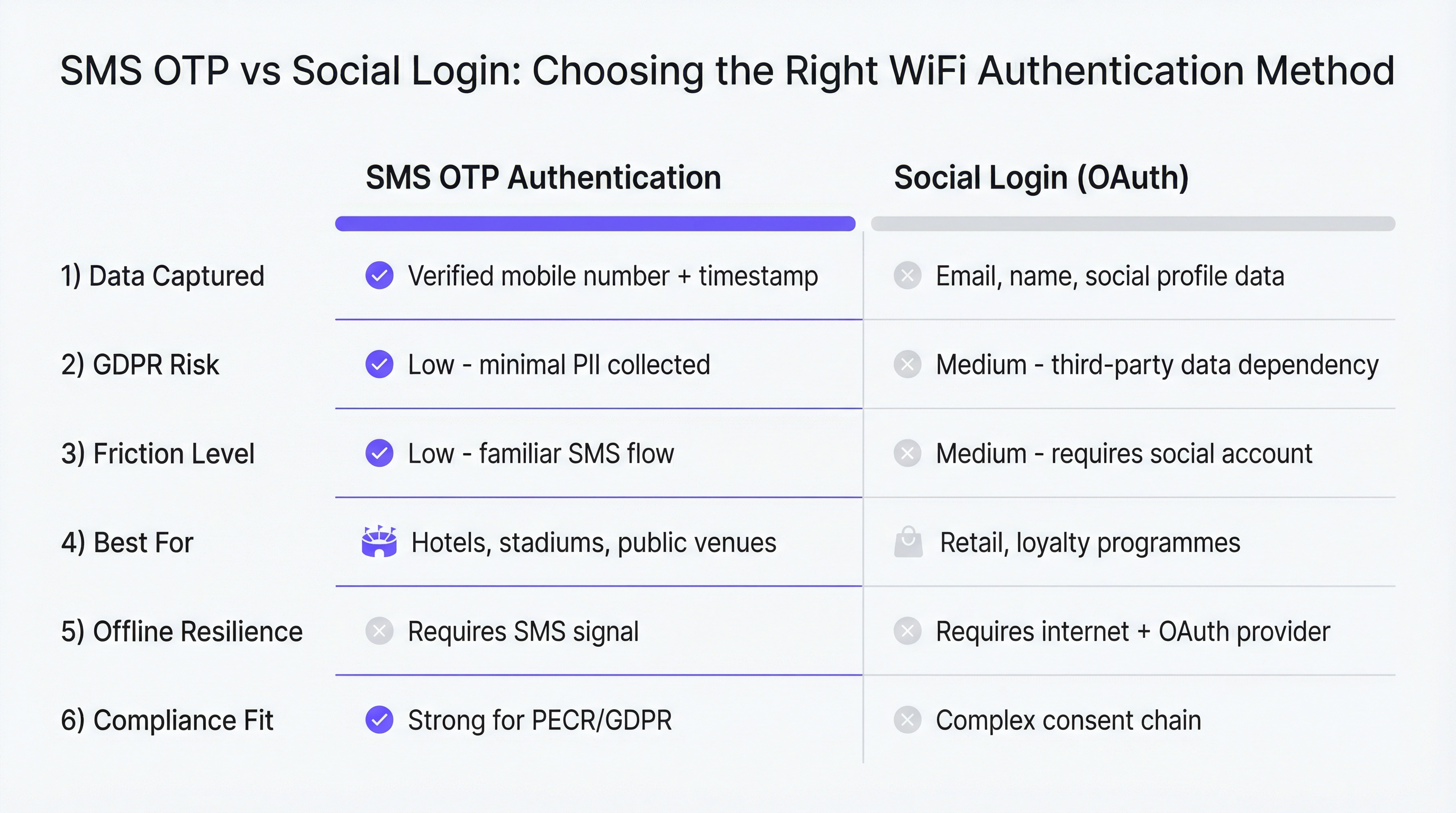
Pour les responsables informatiques et les exploitants de sites, le déploiement d'un WiFi invité ne se limite plus à fournir une connectivité ; c'est un outil stratégique pour l'acquisition de données, le marketing et l'amélioration de l'expérience visiteur. Le choix de la méthode d'authentification est une décision critique ayant des implications directes sur la conformité, la qualité des données et le retour sur investissement. L'authentification par SMS, utilisant un mot de passe à usage unique (OTP) envoyé sur le téléphone mobile de l'utilisateur, s'est imposée comme une méthode robuste, sécurisée et hautement efficace pour les déploiements à grande échelle. Contrairement aux connexions via les réseaux sociaux, qui introduisent des dépendances aux données de tiers et des chaînes de consentement complexes, l'OTP par SMS fournit un lien direct et vérifié avec l'utilisateur via son numéro de mobile. Cette approche minimaliste des données simplifie la conformité au GDPR et au PECR tout en capturant un point d'ancrage d'identité persistant et exploitable. Ce guide fournit un aperçu technique et stratégique complet de l'authentification WiFi par SMS, offrant des modèles de déploiement neutres vis-à-vis des fournisseurs, des stratégies d'atténuation des risques et des indicateurs de ROI clairs pour les directeurs techniques, les architectes réseau et les directeurs des opérations.
Analyse technique approfondie
Le flux d'authentification SMS est initié lorsqu'un invité se connecte au SSID public et est redirigé vers un Captive Portal. Ce processus, régi par des normes telles que la RFC 7710, intercepte la requête HTTP initiale de l'utilisateur et présente une page de connexion personnalisée. Les composants principaux de cette architecture comprennent :
- Captive Portal : l'interface web où les utilisateurs interagissent avec le système d'authentification. Il capture le numéro de mobile de l'utilisateur.
- Serveur RADIUS/Contrôleur d'accès : le système backend (comme Purple) qui gère la logique d'authentification, les politiques utilisateurs et communique avec le matériel réseau.
- Passerelle SMS : un service tiers (par ex. Twilio, Vonage) qui gère l'envoi et la livraison de l'OTP sur l'appareil mobile de l'utilisateur via un appel API.
- Infrastructure réseau : les points d'accès et contrôleurs WiFi (par ex. Cisco Meraki, Aruba, Ruckus) qui appliquent les politiques d'accès définies par le serveur RADIUS.
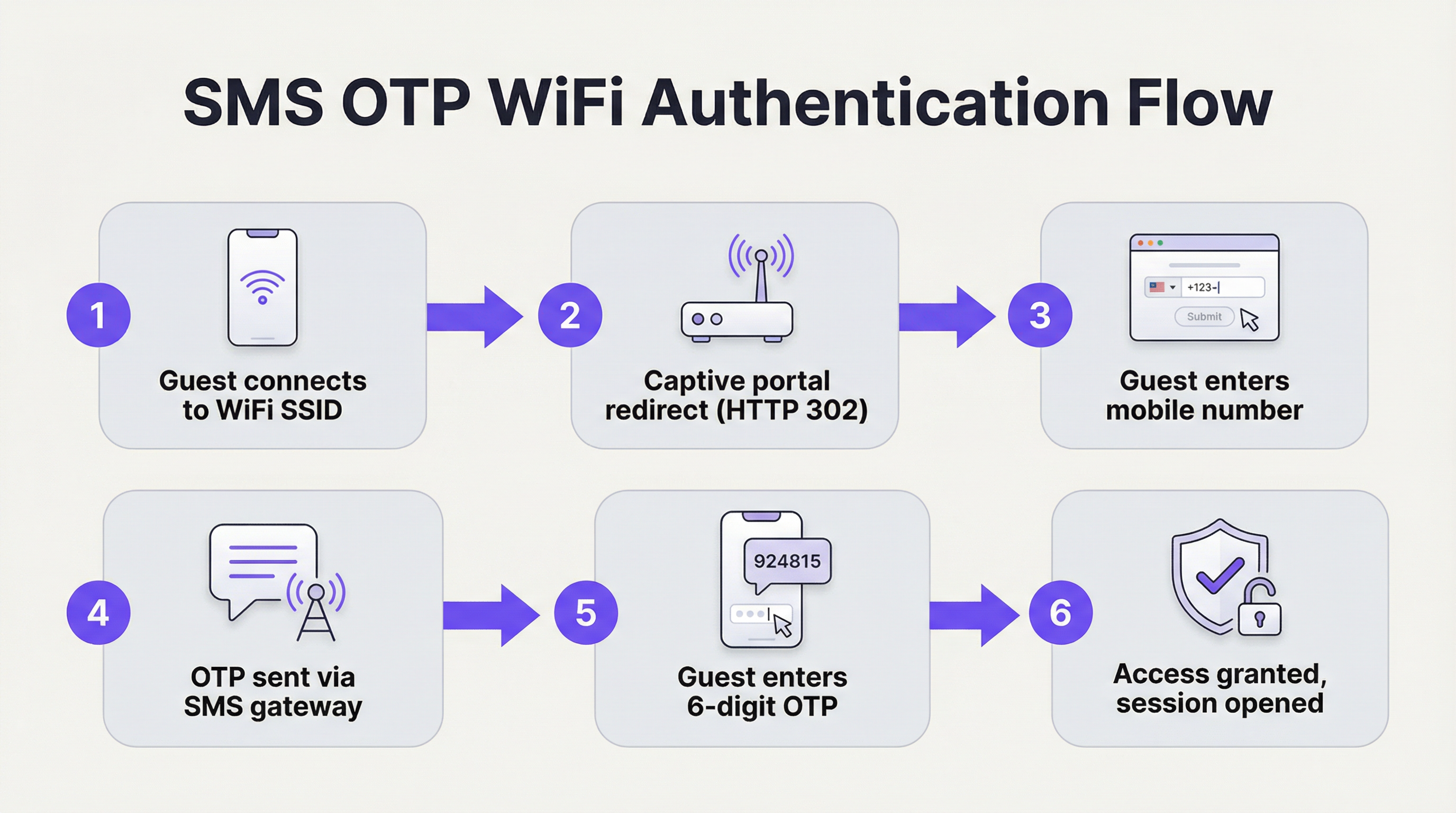
Le flux est le suivant : l'utilisateur saisit son numéro, la plateforme envoie un OTP via la passerelle, l'utilisateur saisit l'OTP et, après validation, le contrôleur d'accès ouvre une session pour l'adresse MAC de l'appareil. Cela crée un enregistrement de données vérifié reliant l'appareil, le numéro de téléphone et l'heure de la session, fournissant un ensemble de données puissant pour l'analyse et le marketing.
Guide de mise en œuvre
Le déploiement d'un système d'authentification SMS résilient nécessite une planification minutieuse. Les étapes suivantes fournissent un cadre neutre vis-à-vis des fournisseurs pour un déploiement réussi :
- Évaluation de l'infrastructure : assurez-vous que votre matériel réseau prend en charge la redirection vers un Captive Portal et l'intégration RADIUS. La plupart des fournisseurs d'équipements d'entreprise sont compatibles.
- Sélection de la plateforme : choisissez une plateforme d'intelligence WiFi offrant des fonctionnalités robustes d'authentification SMS, y compris la prise en charge de passerelles multiples et des analyses détaillées.
- Configuration de la passerelle : sélectionnez et configurez au moins deux fournisseurs de passerelles SMS pour assurer la redondance. Privilégiez les fournisseurs ayant des taux de délivrabilité élevés dans vos principales régions d'exploitation.
- Conception du portail : concevez un Captive Portal épuré et orienté mobile. Il doit inclure un sélecteur d'indicatif téléphonique international, un appel à l'action clair et des cases à cocher distinctes et non cochées par défaut pour le consentement marketing et l'acceptation des conditions d'utilisation.
- Définition des politiques : configurez les politiques de session, notamment la durée de la session, les limites de bande passante et les fenêtres de réauthentification. Pour un hôtel, une session de 24 heures est standard ; pour une conférence, une session de 4 heures pourrait être plus appropriée.
- Tests et mise en production : testez le flux de bout en bout avec plusieurs types d'appareils et des numéros internationaux avant le déploiement complet.
Bonnes pratiques
- La redondance est essentielle : ne vous fiez jamais à une seule passerelle SMS. Les conditions du réseau et les pannes des fournisseurs peuvent perturber la livraison des OTP. Configurez un basculement automatique.
- Privilégiez l'expérience utilisateur : le processus de connexion doit être sans friction. Fournissez des instructions et des messages d'erreur clairs. Proposez une méthode d'authentification de secours (par ex. e-mail) pour les utilisateurs sans couverture réseau mobile.
- Conformité dès la conception (Compliance by Design) : intégrez la confidentialité des données au système. Recueillez un consentement explicite et distinct pour les communications marketing. Assurez-vous que vos politiques de conservation des données sont alignées sur les exigences du GDPR.
- Surveillez et analysez : utilisez les données capturées pour comprendre le comportement des visiteurs, les temps de séjour et les modèles de fréquentation. Intégrez ces données à votre CRM et à vos plateformes de marketing automation pour stimuler l'engagement.
Dépannage et atténuation des risques
- Échec de livraison de l'OTP : le problème le plus courant. Causé par une mauvaise couverture mobile sur le site ou des problèmes de délivrabilité de la passerelle. Atténuez ce risque grâce à la redondance des passerelles et en proposant une méthode d'authentification de secours.
- Problèmes liés aux numéros internationaux : une mauvaise gestion du formatage des numéros E.164 peut empêcher les invités internationaux de recevoir les OTP. Testez minutieusement.
- Gonflement de trafic SMS (SMS Pumping) / Fraude téléphonique : des acteurs malveillants peuvent abuser du formulaire OTP pour générer de gros volumes de SMS, faisant grimper les coûts. Atténuez ce risque avec une limitation stricte du débit (par ex. max 3 requêtes OTP par numéro et par heure) et l'implémentation d'un CAPTCHA.
ROI et impact commercial
L'investissement dans un système d'authentification SMS offre des retours sur plusieurs fonctions de l'entreprise :
- Marketing : construit une base de données vérifiée et de haute qualité de numéros de mobile pour des campagnes de marketing SMS ciblées, favorisant les visites répétées et augmentant la valeur à vie du client.
- Opérations : fournit des analyses riches sur la fréquentation des visiteurs, les temps de séjour et les modèles de déplacement, permettant d'optimiser le personnel, l'agencement et l'allocation des ressources.
- Informatique et sécurité : réduit la charge de conformité par rapport à la connexion via les réseaux sociaux et fournit un registre sécurisé et auditable des accès réseau, répondant aux exigences légales en matière de fourniture de WiFi public dans de nombreuses juridictions.

Termes clés et définitions
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted. It intercepts traffic and redirects the user to a login page.
This is the primary user interface for any guest WiFi authentication method, including SMS OTP. Its design and usability directly impact guest experience and data capture rates.
SMS Gateway
A service that allows a computer to send or receive Short Message Service (SMS) transmissions to or from a telecommunications network. Most gateways use APIs to integrate with software platforms.
This is the engine that powers SMS authentication. The choice of gateway provider affects OTP delivery speed, reliability, and cost.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
In a guest WiFi context, the RADIUS server is the brain that communicates with the network hardware to grant or deny access based on the authentication result from the captive portal.
E.164
An international telephone numbering plan that ensures each device on the public switched telephone network has a globally unique number.
Your captive portal must correctly process numbers in E.164 format (e.g., +447123456789) to successfully authenticate international guests. Failure to do so is a common point of failure.
SSID (Service Set Identifier)
The primary name associated with an 802.11 wireless local area network (WLAN). It's the human-readable name a user sees when they scan for WiFi networks.
IT teams will often configure separate SSIDs for guest and corporate networks. The guest SSID is the one configured to trigger the captive portal and SMS authentication.
MAC Address (Media Access Control Address)
A unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment.
The access controller uses the MAC address to identify a specific device during a session. While MAC randomization on modern devices complicates long-term tracking, the verified phone number becomes the persistent identifier.
GDPR (General Data Protection Regulation)
A regulation in EU law on data protection and privacy in the European Union and the European Economic Area.
SMS authentication, with its minimal data collection and clear consent model, provides a straightforward path to GDPR compliance for guest WiFi services.
SMS Pumping (Toll Fraud)
A type of fraud where attackers exploit a business's SMS services by triggering a high volume of OTPs to premium-rate numbers they control.
This is a significant financial risk for any large-scale SMS auth deployment. It must be mitigated with strict rate-limiting and security measures like CAPTCHA.
Études de cas
A 200-room luxury hotel in central London needs to replace its insecure, open WiFi network. The goal is to capture guest data for marketing, understand guest movements between the lobby, bar, and spa, and ensure compliance with UK GDPR. The guest demographic is highly international.
Deploy a new WPA2-secured SSID named 'TheGrand_GuestWiFi'. Configure a captive portal with SMS authentication as the primary method. The portal will feature the hotel's branding and an international number input. Select two SMS gateways: a UK-based provider for domestic numbers and a global provider like Vonage for international numbers, with automatic failover. Set a 24-hour session time. The portal will include a separate, un-ticked checkbox for guests to opt-in to the hotel's 'VIP Offers' SMS list. The Purple platform will be used to track device movements between APs in different zones (bar, spa, lobby) to build a behavioral profile.
A large exhibition centre hosting multiple B2B and B2C events per week needs to provide reliable WiFi for up to 10,000 concurrent users. They need to segment data by event and provide sponsors with post-event analytics on attendee engagement.
Implement a robust WiFi infrastructure with high-density APs. Use SMS authentication with event-specific SSIDs or access codes. Set short session times (e.g., 4 hours) to align with event durations and capture fresh data for each event. Implement strict rate limiting and CAPTCHA to prevent SMS toll fraud during high-traffic periods. Use the WiFi analytics platform to create separate dashboards for each event, tracking metrics like total authenticated users, peak concurrency, and popular zones. This data can be packaged into a post-event report for sponsors.
Analyse de scénario
Q1. You are deploying guest WiFi in a new-build, 50-story office tower with a mixed-use ground floor (cafes, retail). The building has a DAS (Distributed Antenna System) for cellular, but coverage can be inconsistent in elevator cores and basements. How do you design the authentication flow to maximize both security and user convenience?
💡 Astuce :Consider the physical environment and potential points of failure. A single authentication method may not be sufficient.
Afficher l'approche recommandée
The recommended approach is a multi-factor authentication strategy. The primary method should be SMS OTP due to its security and data quality benefits. However, to mitigate the risk of poor cellular coverage in specific areas, the captive portal must offer a clear, secondary option for 'email-based verification'. This ensures that users who cannot receive an SMS can still get online. The portal logic should prioritize SMS but make the email fallback easily accessible after a single failed SMS attempt.
Q2. A retail chain with 300 stores wants to use WiFi analytics to measure the effectiveness of a new window display. They need to know how many people walk past a store vs. how many enter. They are currently using a simple 'click-to-connect' open network. Why is this method insufficient, and what should they replace it with?
💡 Astuce :Think about what data is needed to differentiate between a passer-by and an in-store visitor. How can you reliably identify a returning visitor?
Afficher l'approche recommandée
'Click-to-connect' is insufficient because it doesn't provide a persistent user identifier. Due to MAC address randomization, you can't reliably tell if a device seen outside is the same one that later connects inside. They should replace it with SMS authentication. By capturing a verified phone number, they create a persistent ID for each visitor. This allows them to correlate 'probe requests' (from devices outside) with 'connection events' (from devices inside) and accurately measure their walk-in rate, as well as track repeat visits over time.
Q3. Your CFO has questioned the monthly cost of your SMS gateway service. Prepare a business case justifying the expense. What are the three key pillars of your argument?
💡 Astuce :Frame the cost as an investment, not an expense. What is the tangible business value generated by the data you are collecting?
Afficher l'approche recommandée
The business case rests on three pillars: 1) Enhanced Marketing ROI: The verified mobile numbers collected are a high-quality asset for targeted SMS marketing, leading to measurable increases in repeat visits and customer spend. 2) Operational Intelligence: The analytics derived from authenticated sessions (footfall, dwell time) allow us to optimize staffing and layout, leading to direct cost savings and revenue uplift. 3) Compliance & Risk Mitigation: SMS auth provides a robust, auditable trail of network access, fulfilling legal obligations and reducing the company's risk profile compared to less secure methods. The gateway cost is a small investment to unlock this significant business value.
Points clés à retenir
- ✓SMS authentication provides a verified, persistent mobile number, a high-value asset for marketing and analytics.
- ✓The technical flow involves a captive portal redirect, phone number submission, and OTP validation via an SMS gateway.
- ✓Compared to social login, SMS auth offers a simpler GDPR compliance profile and is not dependent on third-party social media platforms.
- ✓Key deployment best practices include using redundant SMS gateways, implementing strict rate limiting, and capturing explicit marketing consent.
- ✓The primary risk is OTP delivery failure due to poor cellular coverage, which should be mitigated with a fallback authentication method.
- ✓The ROI of SMS auth is driven by improved marketing effectiveness, operational insights from analytics, and a stronger compliance posture.
- ✓SMS auth is the preferred method for large, diverse-audience venues like hotels, stadiums, and public-sector organizations.



