Captive Portal Solutions: The Ultimate Guide for Businesses of All Sizes
This guide provides a comprehensive technical reference for IT managers, network architects, and CTOs on deploying effective captive portal solutions. It offers actionable guidance on architecture, vendor selection, and implementation to transform a network access point into a strategic asset for data collection, customer engagement, and ROI generation.
🎧 Listen to this Guide
View Transcript
Captive Portal Solutions: The Ultimate Guide for Businesses of All Sizes

Executive Summary
For any organization providing guest WiFi, the captive portal has evolved from a simple login page into a strategic asset for security, compliance, and marketing. This guide provides a comprehensive technical reference for IT managers, network architects, and CTOs on deploying effective captive portal solutions. It moves beyond theory to offer actionable guidance on architecture, vendor selection, and implementation, demonstrating how to transform a network access point into a powerful tool for data collection, customer engagement, and ROI generation. We will explore how to leverage captive portals to enhance the guest experience in hospitality, drive sales in retail, and ensure robust security in any public-facing environment, all while navigating the complex landscape of data privacy regulations like GDPR. This is not an academic overview; it is a practical playbook for deploying a solution that delivers measurable business impact this quarter.
Technical Deep-Dive
A captive portal operates as a gateway, intercepting a user's initial web request and redirecting them to a dedicated authentication page before granting broader network access. This controlled interaction is fundamental to its function, enabling authentication, policy enforcement, and marketing engagement. The process relies on a coordinated sequence of network events, typically involving a wireless LAN controller (WLC), a gateway or firewall, and an external or internal portal server.
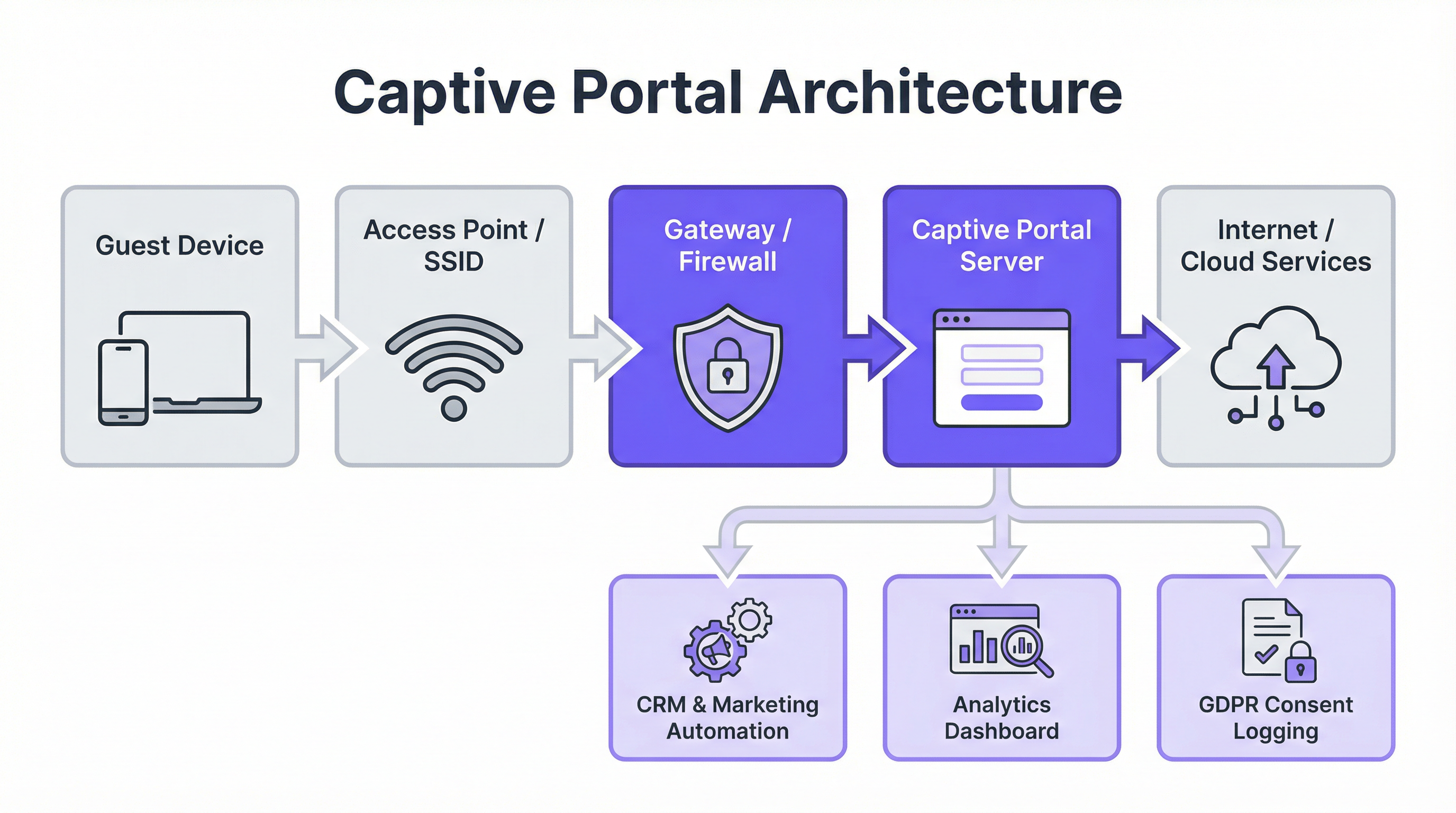
Core Architectural Components:
- Guest Device Connection: The process begins when a user connects their device to the guest SSID. The device's operating system often performs a 'liveness' check by attempting to contact a predefined URL (e.g.,
http://captive.apple.com/hotspot-detect.htmlfor iOS). - DNS & HTTP Interception: The network's gateway or firewall intercepts this initial HTTP request. Instead of allowing it to resolve, it returns a DNS response that points the user's browser to the captive portal server's IP address. This is often achieved via a DNS redirect or by responding with an HTTP 302/307 redirect.
- Portal Authentication: The user is presented with the captive portal's splash page. Here, they must complete a required action, such as entering an email, logging in via a social media provider (OAuth 2.0), entering a voucher code, or simply accepting the Terms of Service. All communication at this stage should be secured via HTTPS to protect user credentials.
- Authentication & Authorization: The portal server validates the user's credentials or action. Upon successful authentication, it communicates with the network controller or gateway, signaling that the device (identified by its MAC address) is now authorized for access. The controller then updates its access control list (ACL) to permit traffic from that device to the internet.
Key Standards and Protocols:
- IEEE 802.1X: While often used for corporate network access, 802.1X provides a framework for port-based network access control that can be integrated with captive portals for more robust, certificate-based authentication.
- WPA3-Enterprise: The latest security standard, offering enhanced protection against offline dictionary attacks and ensuring stronger encryption for sensitive data.
- RADIUS (Remote Authentication Dial-In User Service): A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service. Captive portals frequently use a RADIUS server on the backend to manage user sessions.
- GDPR & Data Privacy: The General Data Protection Regulation mandates explicit, informed consent for data collection. A compliant captive portal must clearly state what data is being collected, for what purpose, and provide a separate, un-checked opt-in for marketing communications.
Implementation Guide
Deploying a captive portal solution requires careful planning that aligns with your existing infrastructure and business objectives. The choice between a controller-based (internal) portal and an external, cloud-based solution is a primary decision point.
Step-by-Step Deployment Process:
- Define Requirements: Determine the primary goal. Is it simple, secure access? Data capture for marketing? Tiered bandwidth for revenue generation? Your objectives will dictate the required features.
- Assess Infrastructure: Identify your current wireless hardware (Access Points, Controllers) and network gateway provider (e.g., Cisco, Aruba, Meraki, Ruckus). Your choice of portal solution must be compatible with your stack.
- Select a Vendor/Solution:
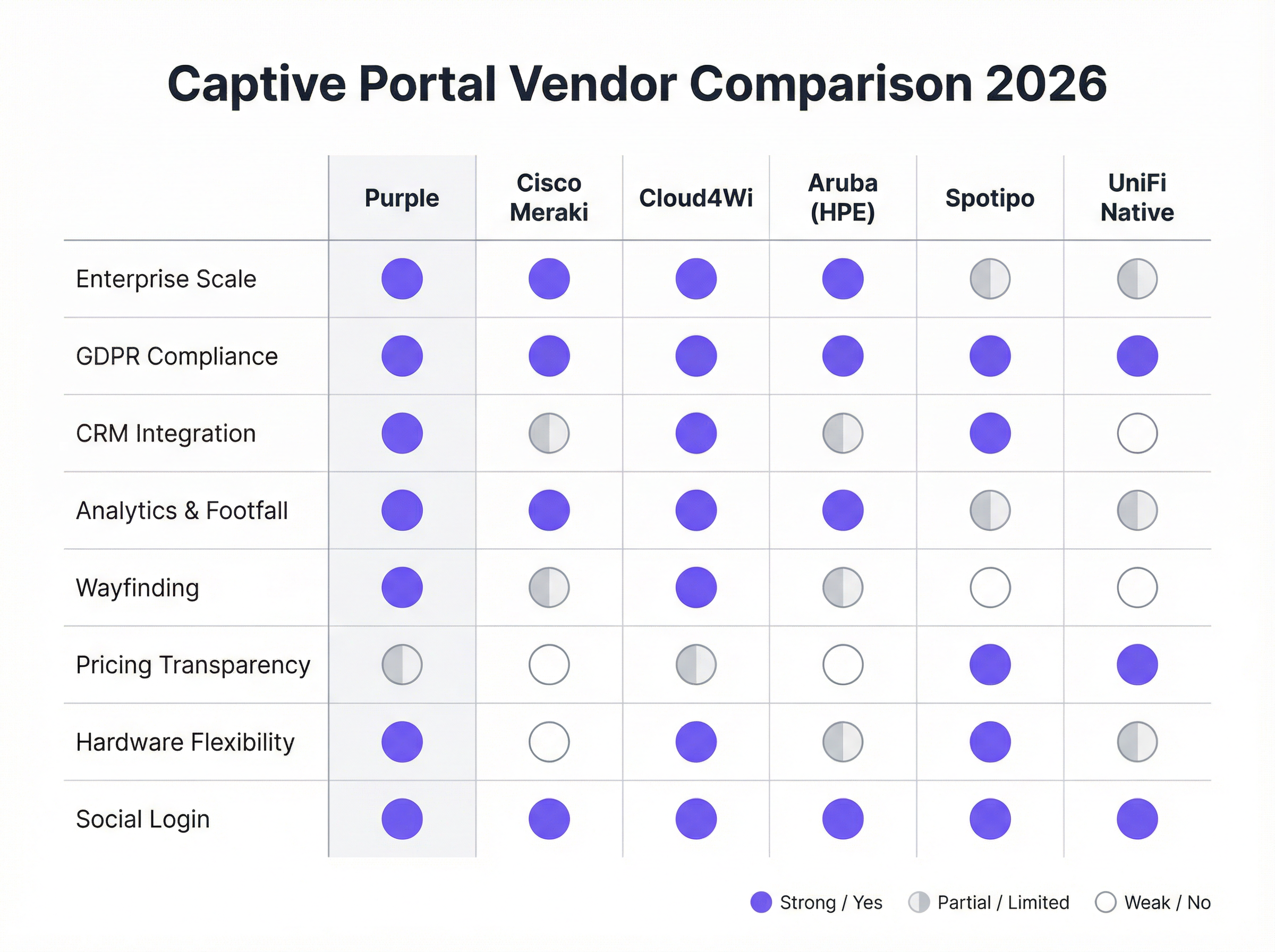
- Hardware-Native Portals (e.g., UniFi Native Portal): Included free with hardware. Good for basic access control but lack advanced marketing and CRM integration features.
- Specialist Cloud Platforms (e.g., Purple, Cloud4Wi, Spotipo): Offer rich feature sets, broad hardware compatibility, and deep integrations. These are ideal for businesses focused on marketing and analytics.
- Full-Stack Solutions (e.g., Cisco Meraki): Provide tightly integrated hardware and software, simplifying deployment but creating vendor lock-in.
- Configure the Splash Page: Design the user-facing login page. Ensure it is mobile-responsive, reflects your brand identity, and clearly presents the required login methods and compliance checkboxes.
- Integrate with Backend Systems: Connect the portal to your CRM (e.g., Salesforce, HubSpot), marketing automation platform (e.g., Klaviyo), and any Property Management Systems (PMS) for hospitality.
- Test the User Journey: Thoroughly test the connection and authentication process on various devices (iOS, Android, laptops) to ensure a seamless experience. Verify that data is flowing correctly into your integrated systems.
- Monitor and Optimize: Use the platform's analytics to monitor usage, track login success rates, and measure marketing ROI. Refine your splash page and offers based on performance data.
Best Practices
- Prioritize the User Experience: A slow, confusing, or multi-step login process will lead to high abandonment rates. Offer frictionless login options like social media or a simple 'click-to-connect' where appropriate.
- Ensure GDPR/CCPA Compliance: Never pre-check marketing opt-in boxes. Provide clear links to your Privacy Policy and Terms of Service. Log user consent with timestamps for audit purposes.
- Segment Your Network: Always run your guest WiFi on a separate VLAN, completely isolated from your corporate network, to mitigate security risks.
- Use HTTPS Everywhere: The captive portal page itself, and all subsequent interactions, must be encrypted with SSL/TLS to protect user data in transit.
- Leverage Data for Personalization: Use the data collected to personalize the post-login experience. For example, a returning hotel guest could be greeted by name and offered a loyalty discount.
Troubleshooting & Risk Mitigation
- Problem: Redirection Fails (Stuck on 'Connecting'): Often caused by DNS issues or firewall rules blocking the redirect. Ensure the gateway can correctly resolve and redirect to the portal server. Some devices with VPNs or custom DNS settings may also fail to redirect.
- Problem: Social Login Fails: This can happen if the portal server's IP address is not whitelisted in the social media provider's developer console (e.g., Facebook Login for Business). API keys and allowed redirect URIs must be correctly configured.
- Risk: 'Evil Twin' Attacks: An attacker sets up a rogue access point with the same SSID as your legitimate network. Users unknowingly connect to the attacker's network, which presents a fake captive portal to steal credentials. Mitigation involves deploying a Wireless Intrusion Prevention System (WIPS) and using WPA3-Enterprise security.
- Risk: Data Breach: If the captive portal server or its connected database is compromised, all collected user data is at risk. Mitigation requires robust server security, data encryption at rest, and adherence to PCI DSS standards if payments are processed.
ROI & Business Impact
The business case for a strategic captive portal solution extends far beyond providing internet access. The ROI is measured through direct and indirect revenue generation, enhanced marketing capabilities, and improved operational efficiency.
- Direct Revenue: Hotels and conference centers can offer tiered bandwidth, charging a premium for high-speed access suitable for video streaming or conferencing.
- Marketing Database Growth: For a retail chain, capturing 5,000 new, high-intent email addresses per month from in-store visitors provides a direct channel for targeted promotions, driving repeat visits and sales.
- Increased Customer Lifetime Value (CLV): By integrating with a CRM, businesses can identify repeat visitors and enroll them in loyalty programs, increasing visit frequency and average spend.
- Operational Insights: Footfall analytics, dwell time data, and visitor flow maps allow venues to optimize staffing, store layouts, and even rental rates for specific zones in a shopping mall.

By viewing guest WiFi as a customer intelligence channel rather than an IT cost center, organizations can unlock significant, measurable value that directly impacts the bottom line.
Key Terms & Definitions
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted. It acts as a customizable gateway for authentication, policy acceptance, and marketing.
This is the core technology being discussed. IT teams deploy it to control and monetize guest WiFi access in venues like hotels, retail stores, and stadiums.
SSID (Service Set Identifier)
The name of a wireless network that is broadcasted by an access point. It's the name you see when you search for WiFi networks on your device.
IT teams configure a specific SSID for guest access (e.g., \'Hotel Guest WiFi\') which is then associated with the captive portal policy. Clear and distinct SSIDs are crucial for user experience and security.
VLAN (Virtual Local Area Network)
A method of creating logically separate networks on the same physical network infrastructure. Traffic from one VLAN is isolated from another.
This is a critical security best practice. IT architects MUST place the guest WiFi network on a separate VLAN from the corporate network to prevent guests from accessing sensitive internal resources.
MAC Address (Media Access Control Address)
A unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment.
The captive portal system uses the device's MAC address to identify it and track its authentication status. Once a device is authenticated, its MAC address is added to an allow list on the gateway.
GDPR (General Data Protection Regulation)
A regulation in EU law on data protection and privacy for all individuals within the European Union and the European Economic Area. It governs how personal data is collected, processed, and stored.
For any business operating in or serving customers from the EU, the captive portal must be GDPR-compliant. This means obtaining explicit, un-coerced consent for data collection and marketing, which has major implications for portal design and data handling.
CRM (Customer Relationship Management)
Software that helps companies manage and analyze customer interactions and data throughout the customer lifecycle, with the goal of improving business relationships.
Integrating the captive portal with a CRM like Salesforce or HubSpot is how you turn WiFi access into a marketing asset. It allows guest data (email, name) to be automatically synced for targeted campaigns.
WPA3 (Wi-Fi Protected Access 3)
The latest generation of WiFi security standard, offering enhanced security features over its predecessor, WPA2, including protection against brute-force attacks.
Network architects should specify WPA3-Enterprise for the highest level of security on their guest networks. It ensures that the connection between the user's device and the access point is strongly encrypted.
Footfall Analytics
The process of analyzing data about customer traffic and behavior in a physical location, such as a retail store or a shopping mall.
Advanced captive portal solutions like Purple provide footfall analytics by analyzing WiFi connection data. This gives venue operators valuable insights into visitor numbers, dwell times, and movement patterns, which can be used to optimize operations and marketing.
Case Studies
A 250-room upscale hotel wants to replace its outdated, unreliable guest WiFi system. The goals are to provide a seamless, premium connectivity experience, gather guest data to personalize marketing, and create a new revenue stream from high-speed internet access. The existing hardware is a mix of older Cisco and Ruckus access points.
- Infrastructure Upgrade & Vendor Selection: The mixed hardware is inefficient. Standardize on a single vendor for new WiFi 6/6E access points. Select a cloud-based captive portal provider like Purple that offers broad hardware compatibility and robust PMS integration. 2. Portal Configuration: Design a branded splash page that authenticates users via Room Number + Surname. This validates their guest status via a real-time PMS lookup. 3. Tiered Access Model: Configure two tiers: a) Standard Access (Free): 5 Mbps, suitable for email and web browsing, offered complimentary. b) Premium Access ($15/day): 100 Mbps, for streaming 4K video and video conferencing. The PMS integration allows the charge to be automatically added to the guest's room bill. 4. Marketing Integration: On successful login, redirect guests to a welcome page promoting hotel amenities (spa, restaurant). Use the collected email addresses (with GDPR-compliant consent) for post-stay feedback surveys and targeted offers for future bookings. 5. Security: Deploy the guest network on a separate VLAN, isolated from the hotel's corporate and operational networks. Enforce WPA3 security on the new access points.
A national retail chain with 200 stores wants to leverage in-store guest WiFi to increase its loyalty program membership and measure the impact of digital advertising on physical foot traffic. They currently use Cisco Meraki across all locations.
- Vendor Selection: Since the hardware is standardized on Cisco Meraki, a solution with deep Meraki integration is ideal. Adentro (formerly Zenreach) is a strong candidate due to its focus on the 'Walk-Through Rate' metric, but Purple also offers robust Meraki integration with more flexible pricing. Let's proceed with Purple for its balance of features and cost-effectiveness. 2. Portal Configuration: Configure the captive portal to offer two login methods: a) Social Login (Facebook/Google) for quick access, and b) 'Join Our Loyalty Program' form that captures name, email, and mobile number in exchange for a 10% off digital coupon. 3. CRM & Ad Platform Integration: Connect the portal directly to the company's Salesforce CRM and Facebook Ads account. New loyalty sign-ups are automatically added to Salesforce. The platform will capture the MAC addresses of devices that connect to WiFi. 4. Attribution Measurement: When a customer who has previously logged into the WiFi sees a Facebook ad for the brand and subsequently enters a store (their device is detected by the WiFi network), this is recorded as a 'Walk-Through'. This allows the marketing team to directly measure the ROI of their ad spend on driving in-store traffic. 5. Analytics: Use the platform's analytics dashboard to monitor new loyalty sign-ups per store, identify peak traffic hours, and analyze customer dwell times to optimize store layouts and staffing.
Scenario Analysis
Q1. Your organization is a fast-growing chain of 50 coffee shops using a mix of different consumer-grade routers. The marketing team wants to build a customer email list. What is your primary recommendation for a captive portal strategy?
💡 Hint:Consider the challenges of managing a diverse and non-enterprise hardware environment and the primary goal of marketing data collection.
Show Recommended Approach
The primary recommendation is to deploy a hardware-agnostic, cloud-based captive portal solution like Spotipo or Purple. This approach avoids a costly and immediate hardware replacement across all 50 stores. These platforms are designed to work with a wide range of hardware and provide the centralized management and CRM integration needed to meet the marketing team's goal of building an email list. A simple, email-based login should be implemented to maximize sign-ups.
Q2. A large conference center is hosting a cybersecurity summit and needs to provide WiFi for 5,000 attendees. The summit organizers are concerned about security. How would you configure the captive portal and network?
💡 Hint:Focus on security and scalability. How do you authenticate a large number of users securely while protecting them and your network?
Show Recommended Approach
- Network Segmentation: Create a dedicated VLAN for attendee WiFi, completely isolated from the center's operational network. 2. Security Protocol: Enforce WPA3-Enterprise for robust encryption. 3. Authentication: Use a voucher-based system. Each attendee receives a unique, single-use code upon registration. This prevents unauthorized access and provides a clear audit trail. 4. Portal Configuration: The portal should be minimal, requiring only the voucher code. Disable social logins or open forms to reduce the attack surface. 5. Bandwidth Management: Implement per-user bandwidth limits to ensure fair usage and prevent network saturation. 6. Monitoring: Actively monitor the network for rogue access points or suspicious activity using a WIPS.
Q3. A hospital wants to provide guest WiFi in its waiting rooms but is extremely concerned about HIPAA compliance and protecting patient data. What is the most critical architectural decision to ensure security?
💡 Hint:What is the single most important measure to prevent any possibility of guest traffic interfering with sensitive internal systems?
Show Recommended Approach
The most critical architectural decision is the strict implementation of network segmentation using a VLAN. The guest WiFi network must be on its own VLAN, completely firewalled off from the hospital's internal clinical network where Electronic Health Records (EHR) and other sensitive patient data reside. There should be no routes and no trust between the guest VLAN and the internal VLAN. This ensures that even if a guest device is compromised, it has no network path to access sensitive internal systems, forming the foundation of a HIPAA-compliant guest WiFi strategy.
Key Takeaways
- ✓A captive portal is a strategic asset for security, compliance, and marketing, not just a login page.
- ✓The core architecture involves DNS/HTTP interception to redirect users to a portal for authentication before granting internet access.
- ✓Choosing between hardware-native portals and specialist cloud platforms depends on your business goals, particularly regarding marketing and data analytics.
- ✓GDPR and CCPA compliance are non-negotiable; portals must be designed for explicit, logged user consent.
- ✓Security best practices, like network segmentation (VLANs) and WPA3 encryption, are critical to mitigate risks like 'Evil Twin' attacks.
- ✓The ROI of a captive portal is measured in direct revenue (tiered access), marketing database growth, and operational insights from footfall analytics.
- ✓A seamless user experience is paramount; a complex login process will lead to high abandonment and low data capture.



