DHCP and DNS Fundamentals for WiFi Network Administrators
An authoritative technical reference for IT leaders and network administrators on the critical roles of DHCP and DNS in enterprise WiFi deployments. This guide provides practical, vendor-neutral guidance for designing, implementing, and troubleshooting robust network services in hospitality, retail, and large-venue environments.
🎧 Listen to this Guide
View Transcript

Executive Summary
For the modern enterprise, guest and staff WiFi is no longer a convenience; it is a core utility that underpins operations, customer engagement, and business intelligence. However, the stability and security of these networks depend entirely on foundational services that are often taken for granted: the Dynamic Host Configuration Protocol (DHCP) and the Domain Name System (DNS). For CTOs, IT managers, and venue directors, a nuanced understanding of these protocols is not merely a technical exercise—it is a matter of risk mitigation, resource optimization, and enabling a superior user experience. Misconfigurations can lead to critical service outages, security vulnerabilities, and a degraded experience that directly impacts customer satisfaction and revenue. This guide provides a practical, actionable framework for architecting DHCP and DNS services for large-scale WiFi networks. It moves beyond academic theory to address real-world challenges, from IP address management in high-density venues to the intricate DNS mechanics that govern captive portal functionality. By adopting the best practices outlined, organizations can ensure their WiFi infrastructure is not only reliable and secure but also a powerful asset for data collection and business growth.
Technical Deep-Dive
The Role of DHCP in WiFi Networks
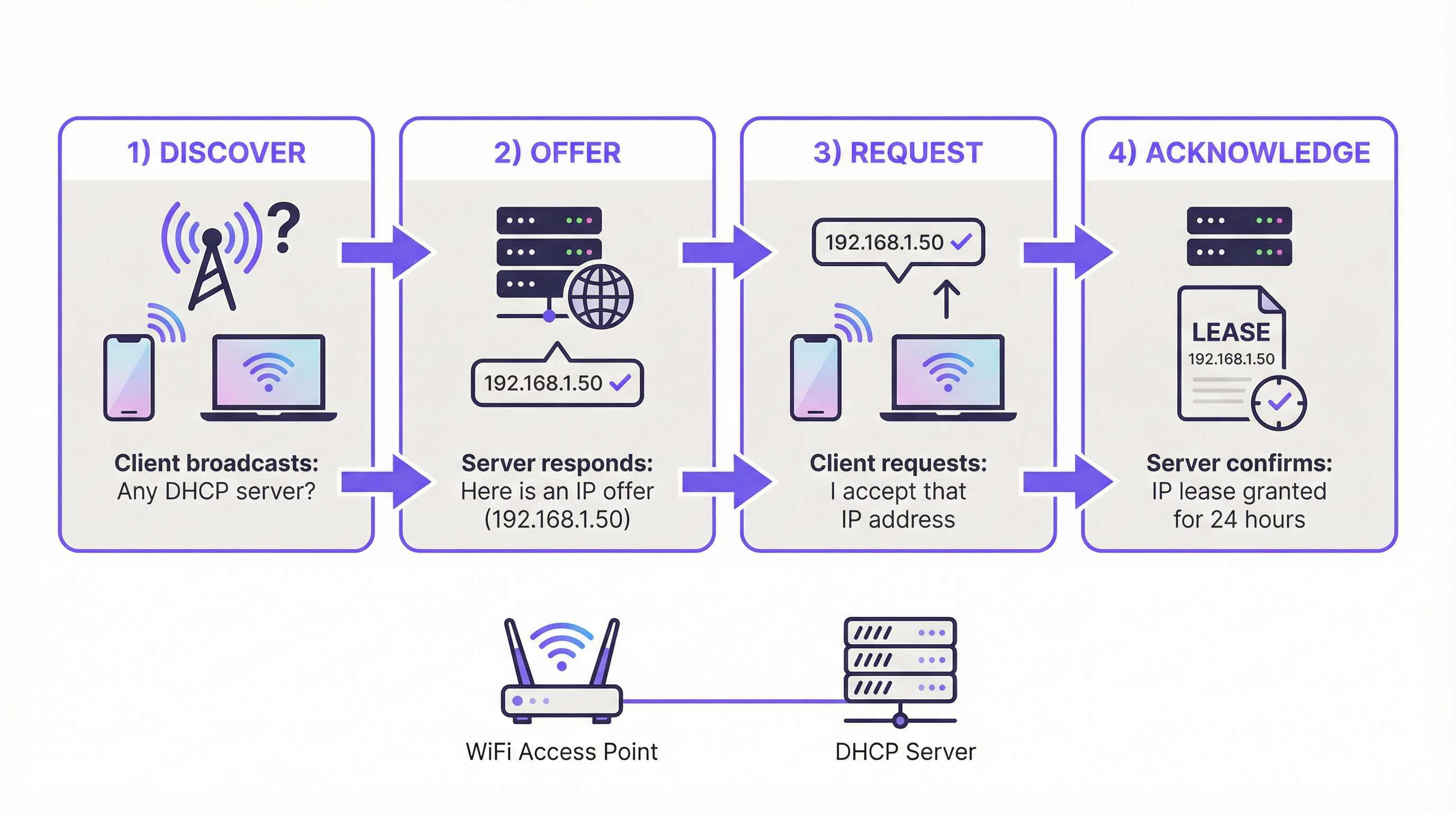
DHCP is the engine of IP address automation. In a WiFi context, where hundreds or thousands of devices can connect and disconnect fluidly, manual IP assignment is an operational impossibility. DHCP automates this through the four-step DORA (Discover, Offer, Request, Acknowledge) process, ensuring every client receives a unique IP address and the necessary configuration to communicate on the network.
Key DHCP Parameters for WiFi:
- Lease Time: This determines how long a device can hold onto an IP address. In high-turnover environments like a coffee shop or a conference, short lease times (e.g., 1-4 hours) are critical for recycling IPs efficiently. In a hotel or corporate office, longer leases (e.g., 24 hours) are more suitable for resident devices.
- Scope Size: A common failure point is under-provisioning the IP address pool. A /24 subnet (254 usable IPs) is often insufficient for enterprise guest networks. A rule of thumb is to provision for at least 2-3 devices per user or room. For a 200-room hotel, this means planning for 400-600 concurrent devices, necessitating a larger subnet (e.g., a /22) to prevent IP address exhaustion during peak times.
- DHCP Options: Beyond the IP address, DHCP provides clients with critical information, most notably the Default Gateway (the router's IP) and the DNS Server address. Option 43 can also be used to provide vendor-specific information to access points for controller discovery.
DNS and its Impact on the WiFi User Experience
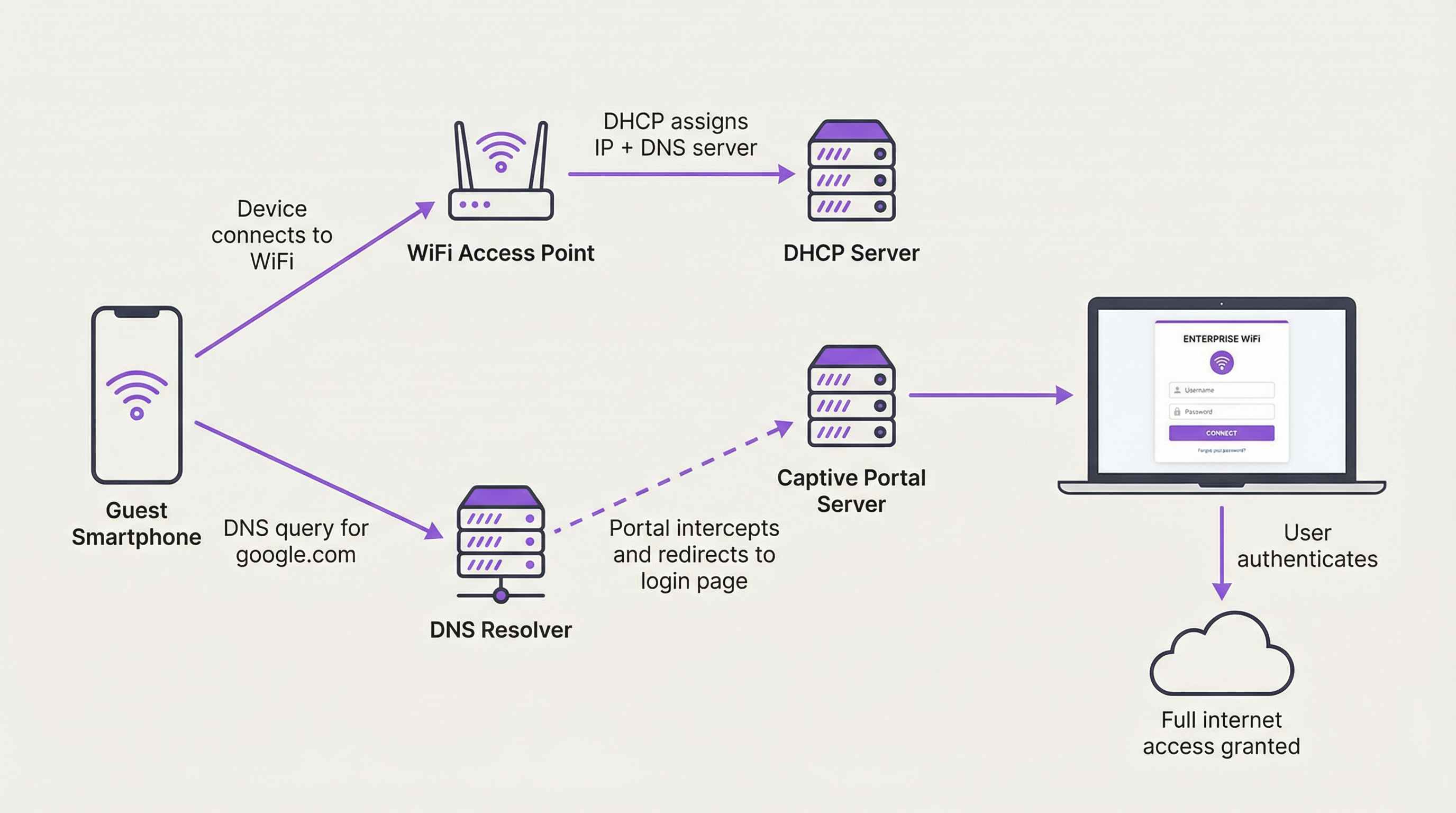
DNS translates human-readable domain names (e.g., purple.ai) into machine-readable IP addresses. In the context of guest WiFi, its role is pivotal, particularly for captive portals.
The Captive Portal Intercept:
When a new guest device connects, it is firewalled from the public internet. When the user opens a browser and tries to navigate to any website, the network's DNS server intercepts this request. Instead of resolving the requested domain to its public IP, the DNS server responds with the IP address of the captive portal server itself. This forces the user's browser to load the authentication page. This is a form of controlled DNS hijacking and is fundamental to the captive portal workflow.
Common DNS Misconfigurations:
- Allowing External DNS: If firewall rules permit guest clients to send DNS queries to external resolvers (like Google's 8.8.8.8 or Cloudflare's 1.1.1.1) before authentication, the captive portal can be bypassed. All DNS traffic from unauthenticated clients must be forced to the internal resolver.
- Split-Horizon DNS: In environments with both guest and internal networks, a split-horizon (or split-brain) DNS architecture is essential. This means your DNS server provides different responses depending on who is asking. An employee on the staff WiFi querying an internal server name should get a private IP address, while a guest should not be able to resolve that name at all. This is a critical security boundary.
Implementation Guide
Architecting DHCP and DNS for enterprise WiFi requires a structured approach. The following provides a vendor-neutral deployment model.
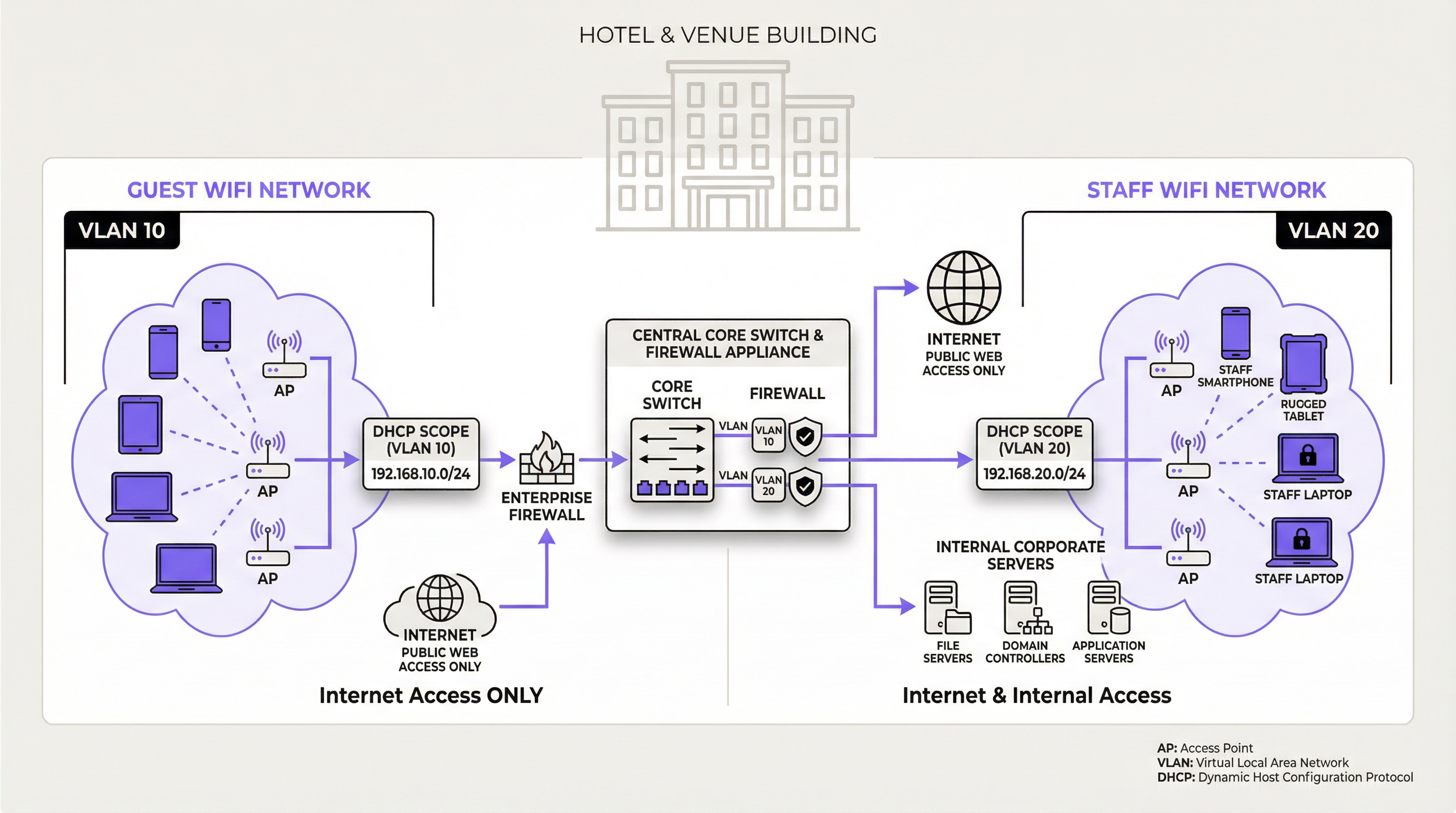
Step 1: Network Segmentation
This is the absolute foundation. Guest and staff/corporate traffic must be logically separated using VLANs. This is a fundamental requirement for security standards like PCI DSS and GDPR.
- Guest VLAN: Unrestricted access to the internet (post-authentication), but completely firewalled from all internal corporate resources.
- Staff VLAN: Access to the internet and specific, role-based access to internal resources (file servers, databases, etc.).
- Management VLAN: For network infrastructure devices like access points, switches, and controllers.
Step 2: DHCP & DNS Server Architecture
- Centralized Model: For multi-site organizations (e.g., retail chains), a centralized DHCP/DNS server at a head office or data center provides consistent management. Each remote site uses DHCP Relay Agents (IP helpers) on its local router/switch to forward DHCP requests to the central server. Risk: High dependency on the WAN link.
- Decentralized/Distributed Model: For large single-site venues (stadiums, airports) or where site autonomy is critical, deploying redundant DHCP/DNS servers locally is the best practice. This provides maximum resilience and performance, as a WAN failure will not impact local network services.
- Cloud-based Model: Some cloud-managed networking solutions offer integrated DHCP and DNS services. This simplifies management but requires careful evaluation of the security and feature set.
Step 3: DHCP Scope and Lease Configuration
For each VLAN, create a dedicated DHCP scope.
| Network | VLAN ID | Example Subnet | Recommended Lease Time | Key Considerations |
|---|---|---|---|---|
| Guest WiFi | 10 | 10.10.0.0/21 |
1-8 Hours | Size for peak capacity (3x users). Short lease. |
| Staff WiFi | 20 | 192.168.20.0/24 |
24 Hours | Longer lease for persistent devices. |
| IoT / Scanners | 30 | 192.168.30.0/24 |
7 Days / Static | Use static reservations for critical infrastructure. |
Best Practices
- Enable DHCP Snooping: This is a Layer 2 security feature on switches that validates DHCP messages. It prevents rogue DHCP servers from being introduced to the network, which is a common attack vector.
- Monitor DHCP Scope Utilization: Actively monitor the number of available IPs in your DHCP pools. Set up alerts to notify you when utilization exceeds a threshold (e.g., 85%) to proactively prevent address exhaustion.
- Use Redundant Servers: For any enterprise-grade deployment, DHCP and DNS services should be deployed in a redundant pair (e.g., a failover cluster) to eliminate single points of failure.
- Document DHCP Reservations: For critical infrastructure devices that require a consistent IP address (e.g., printers, servers, access points), use DHCP reservations tied to the device's MAC address. This centralizes IP management rather than using static IPs configured on the devices themselves.
Troubleshooting & Risk Mitigation
| Symptom | Potential Cause | Mitigation / Solution |
|---|---|---|
| Users cannot get an IP address. | DHCP Scope Exhaustion: The pool of available IP addresses is empty. | Increase the size of the subnet. Decrease the DHCP lease time to recycle addresses faster. |
| Users get a 'self-assigned' IP. | No DHCP Server Reachable: The client's DHCP Discover packet is not reaching a server. | Check for VLAN misconfigurations. Ensure DHCP Relay/IP Helper addresses are correctly configured on routers/L3 switches. |
| Users are directed to wrong websites. | Rogue DHCP Server or DNS Hijacking: An unauthorized device is issuing malicious network settings. | Enable DHCP Snooping on all access switches. Use DNS security extensions (DNSSEC) if supported. |
| Captive portal page does not load. | DNS Bypass: Client is using an external DNS server. Firewall Issue: Traffic to the portal server is blocked. | Create firewall rules to block all outbound DNS (Port 53) from unauthenticated clients except to the internal resolver. |
ROI & Business Impact
A well-architected DHCP and DNS infrastructure delivers tangible business value beyond simply providing internet access. The primary ROI is derived from risk reduction and operational efficiency. A stable network minimizes costly downtime and reduces the number of support tickets related to connectivity issues. For a large hotel, avoiding a single hour of guest WiFi outage during a major conference can prevent significant reputational damage and service credit demands. Furthermore, the reliable operation of the captive portal, which depends on DNS, is the gateway to collecting valuable customer data for marketing and analytics, as facilitated by platforms like Purple. This data enables personalized engagement, drives loyalty, and provides footfall analytics that can optimize venue layout and operations, delivering a direct and measurable impact on revenue.
Key Terms & Definitions
DHCP Lease Time
The duration for which a DHCP server grants a client the right to use an assigned IP address.
IT teams must balance lease time against device turnover. Short leases in high-traffic venues prevent IP exhaustion, while long leases in corporate environments reduce unnecessary network chatter.
DHCP Scope
A defined range of IP addresses that a DHCP server is authorized to distribute to clients on a specific subnet.
This is the pool of available addresses. If the scope is too small for the number of connecting devices, new users will be denied access, leading to service outages.
DHCP Relay Agent (IP Helper)
A router or switch configuration that forwards DHCP broadcast packets from one subnet to a DHCP server on another subnet.
This is essential for centralized DHCP management. It allows a single DHCP server in a data center to serve multiple VLANs and remote sites without needing a server in every location.
DHCP Snooping
A Layer 2 security feature that filters DHCP messages, blocking responses from untrusted ports to prevent rogue DHCP servers.
This is a critical security control to prevent man-in-the-middle attacks where an attacker's device could start issuing malicious IP configurations to clients.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
For venue operators, this is the primary mechanism for user authentication, presenting terms of service, and capturing marketing data. Its functionality is entirely dependent on correct DNS and firewall configuration.
Split-Horizon DNS (Split-Brain DNS)
A DNS configuration where the server provides different responses (different IP addresses) for the same domain name depending on the source of the query.
This is used to securely separate internal and external users. It ensures an employee can resolve `intranet.company.com` to a private IP while a guest on the public WiFi cannot resolve it at all.
VLAN (Virtual Local Area Network)
A method of creating logically separate networks on the same physical network infrastructure.
This is the fundamental tool for network segmentation. IT teams must use VLANs to isolate guest traffic from secure corporate and payment-card (PCI) traffic as a baseline security measure.
IP Address Exhaustion
A state where all available IP addresses in a DHCP scope have been leased, preventing new devices from connecting to the network.
This is the most common failure mode for poorly planned guest WiFi networks. It is a direct result of underestimating device density and setting lease times that are too long for the environment.
Case Studies
A 500-room luxury hotel is experiencing frequent complaints about WiFi connectivity, especially during large conferences. Guests report being unable to connect, and the IT team is constantly "rebooting the router". They are using a single /24 subnet for their guest network, provided by their ISP's basic firewall.
The core issue is DHCP scope exhaustion and a lack of enterprise-grade architecture.
- Immediate Triage: Lower the DHCP lease time on the existing firewall from the default (often 24 hours) to 1 hour. This will more rapidly recycle the limited IP addresses as conference attendees come and go.
- Strategic Redesign: Procure and deploy two dedicated servers to run as a DHCP failover cluster. This provides redundancy.
- Implement VLANs: Create a new, dedicated Guest WiFi VLAN (e.g., VLAN 100).
- Expand IP Scope: Assign a significantly larger subnet to the new guest VLAN, such as a /21 (which provides 2046 usable IPs). This accommodates the 500 rooms plus multiple devices per guest and conference attendees (500 rooms * 3 devices/room = 1500 IPs needed at a minimum).
- Configure DHCP Relay: On the hotel's core switch/router, configure an IP Helper address on the Guest VLAN interface, pointing to the new DHCP servers. This directs all guest DHCP requests to the dedicated servers.
- Monitoring: Implement monitoring on the new DHCP servers to track scope utilization in real-time.
A retail chain with 100 stores wants to implement a branded guest WiFi captive portal to gather marketing data. They notice that some tech-savvy customers are able to get online without ever seeing the login page. Their current setup has a simple guest network at each store using the local ISP router.
The problem is DNS leakage, allowing clients to bypass the captive portal redirect.
- Firewall Policy Implementation: At each store, the firewall controlling the guest network must be configured with a new outbound rule. This rule should DENY all traffic from the Guest WiFi subnet with a destination port of 53 (DNS), for all destination IPs EXCEPT for the IP address of the store's own internal DNS resolver (which may be the router itself or a designated server).
- DNS Interception: Ensure the internal DNS resolver is configured to intercept all DNS queries from unauthenticated clients and redirect them to the captive portal's IP address.
- Centralized Management (Optional but Recommended): For better consistency, deploy a standardized firewall configuration to all 100 stores using a central management platform (e.g., Meraki, FortiManager). This ensures the anti-bypass rule is applied uniformly and cannot be accidentally misconfigured by local staff.
Scenario Analysis
Q1. You are designing the network for a new 10,000-seat sports stadium. The client wants seamless WiFi for all attendees. What DHCP lease time would you recommend for the public guest network and why?
💡 Hint:Consider the duration of an average event and the sheer volume of unique devices over a short period.
Show Recommended Approach
A very short lease time, such as 30-60 minutes, is recommended. During a 3-4 hour event, thousands of devices will connect and disconnect. A short lease ensures that IP addresses from departed fans are rapidly recycled and made available to new or reconnecting devices, preventing IP address exhaustion in such a high-density, high-turnover environment.
Q2. A hospital wants to provide guest WiFi but is concerned about security and compliance with health data regulations (e.g., HIPAA). What is the single most important architectural principle you must enforce regarding their guest and internal networks?
💡 Hint:How do you ensure guest devices can never, under any circumstances, communicate with internal clinical systems?
Show Recommended Approach
The single most important principle is strict network segmentation using VLANs and restrictive firewall rules. The guest WiFi network must be on its own isolated VLAN and all traffic from this VLAN must be explicitly denied from reaching any internal network segment, especially those containing clinical systems or patient data. There should be zero trust and zero connectivity between the two environments.
Q3. Your company's CFO is questioning the expense of dedicated DHCP/DNS servers, arguing that the firewall provided by the ISP should be sufficient. How do you justify the investment in terms of business risk?
💡 Hint:Translate technical benefits (redundancy, scalability) into business outcomes (risk mitigation, uptime, user experience).
Show Recommended Approach
The justification is a risk-mitigation and business continuity argument. While the ISP firewall provides basic functionality, it represents a single point of failure with limited scalability and management features. For an enterprise, a DHCP or DNS failure is not an IT issue; it's a business outage. For a hotel, it means unhappy guests and refunds. For a retail store, it means point-of-sale systems or customer analytics could fail. Investing in redundant, dedicated servers is like buying insurance; it protects against costly downtime and ensures the network can scale with business demand, directly protecting revenue and customer satisfaction.
Key Takeaways
- ✓DHCP and DNS are foundational services that determine the stability and security of any enterprise WiFi network.
- ✓Always right-size your DHCP scope for peak device density (The 3:1 Rule) and use short lease times in high-turnover venues.
- ✓Strict network segmentation using VLANs to separate guest and staff traffic is a non-negotiable security requirement.
- ✓Captive portal functionality relies on intercepting and redirecting DNS queries; block external DNS for unauthenticated users to prevent bypass.
- ✓Use DHCP Snooping to prevent rogue DHCP servers and other man-in-the-middle attacks.
- ✓For enterprise scale, use redundant, dedicated DHCP/DNS servers to eliminate single points of failure and ensure business continuity.
- ✓Monitor DHCP scope utilization proactively to prevent IP address exhaustion before it impacts users.



