EAP-TLS Authentication Explained: Certificate-Based WiFi Security
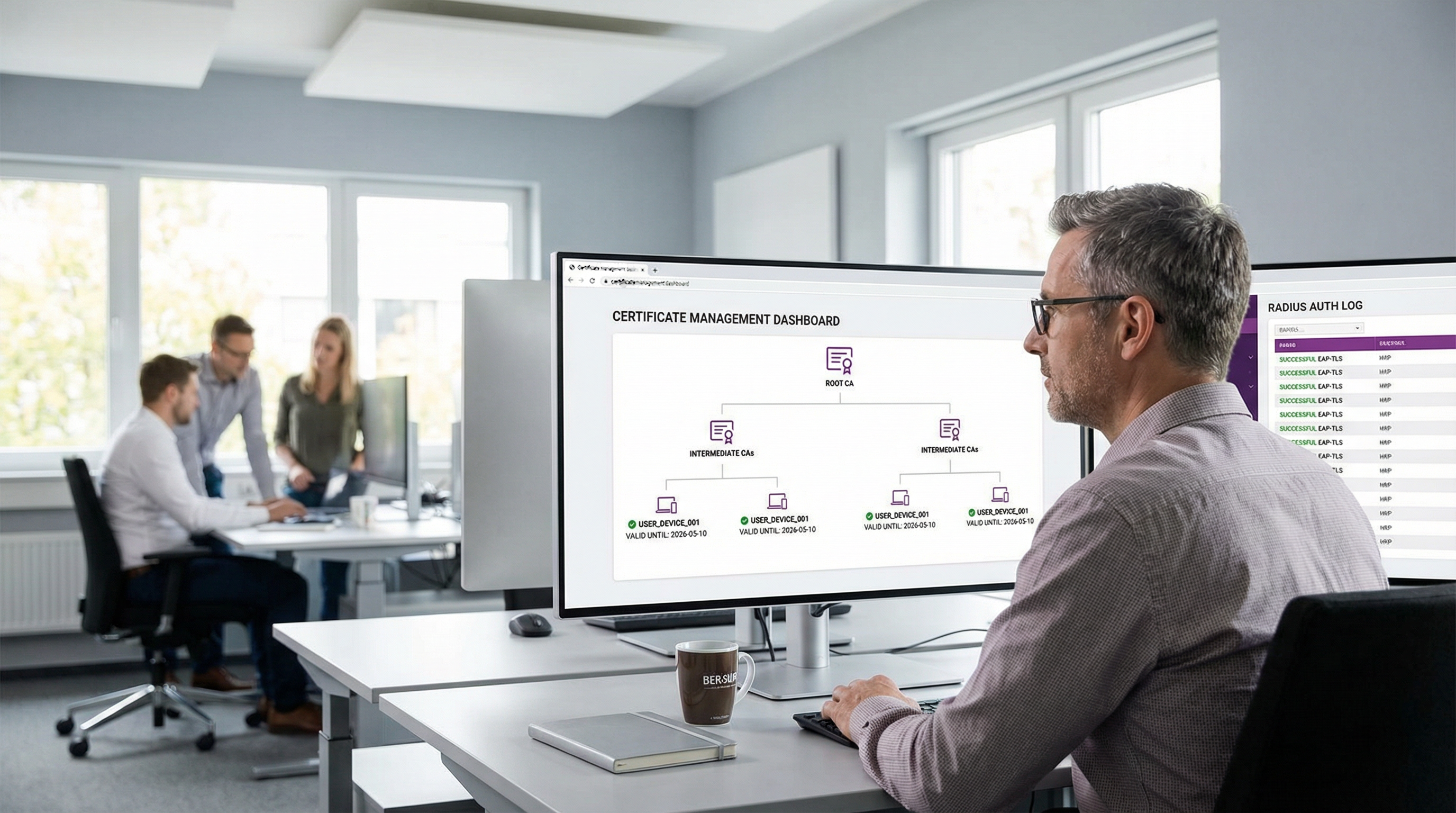
EAP-TLS is the gold standard for enterprise WiFi security, replacing vulnerable password-based authentication with robust, mutually authenticated digital certificates. This guide provides IT managers and network architects with a comprehensive technical deep-dive into the EAP-TLS handshake, architectural requirements, and practical deployment strategies for mixed-device environments.
🎧 Listen to this Guide
View Transcript
Executive Summary
For enterprise environments ranging from corporate headquarters to Retail chains and Healthcare facilities, securing wireless access is no longer just an operational requirement—it is a critical compliance mandate. Historically, organisations have relied on PEAP-MSCHAPv2, which secures a username and password within a TLS tunnel. However, in an era of rampant credential harvesting and sophisticated phishing attacks, password-based authentication over WiFi represents a significant vulnerability.
Enter EAP-TLS (Extensible Authentication Protocol - Transport Layer Security). EAP-TLS represents the gold standard in 802.1X network access control. Instead of relying on user-generated passwords, EAP-TLS mandates mutual authentication using X.509 digital certificates. Both the client device and the authentication server must prove their identity before any network access is granted. This approach eliminates the risk of credential theft, mitigates man-in-the-middle (MitM) attacks, and provides a seamless, zero-touch connection experience for managed devices. This technical reference guide explores the mechanics of the EAP-TLS handshake, compares it to legacy methods, and outlines a practical deployment architecture for modern enterprises.
Listen to our companion technical briefing podcast for an executive overview:
Technical Deep-Dive
The EAP-TLS Handshake Explained
The fundamental advantage of EAP-TLS lies in its cryptographic rigor. The authentication process is a multi-step conversation between the Supplicant (the client device), the Authenticator (the WiFi Access Point or switch), and the Authentication Server (typically a RADIUS server).
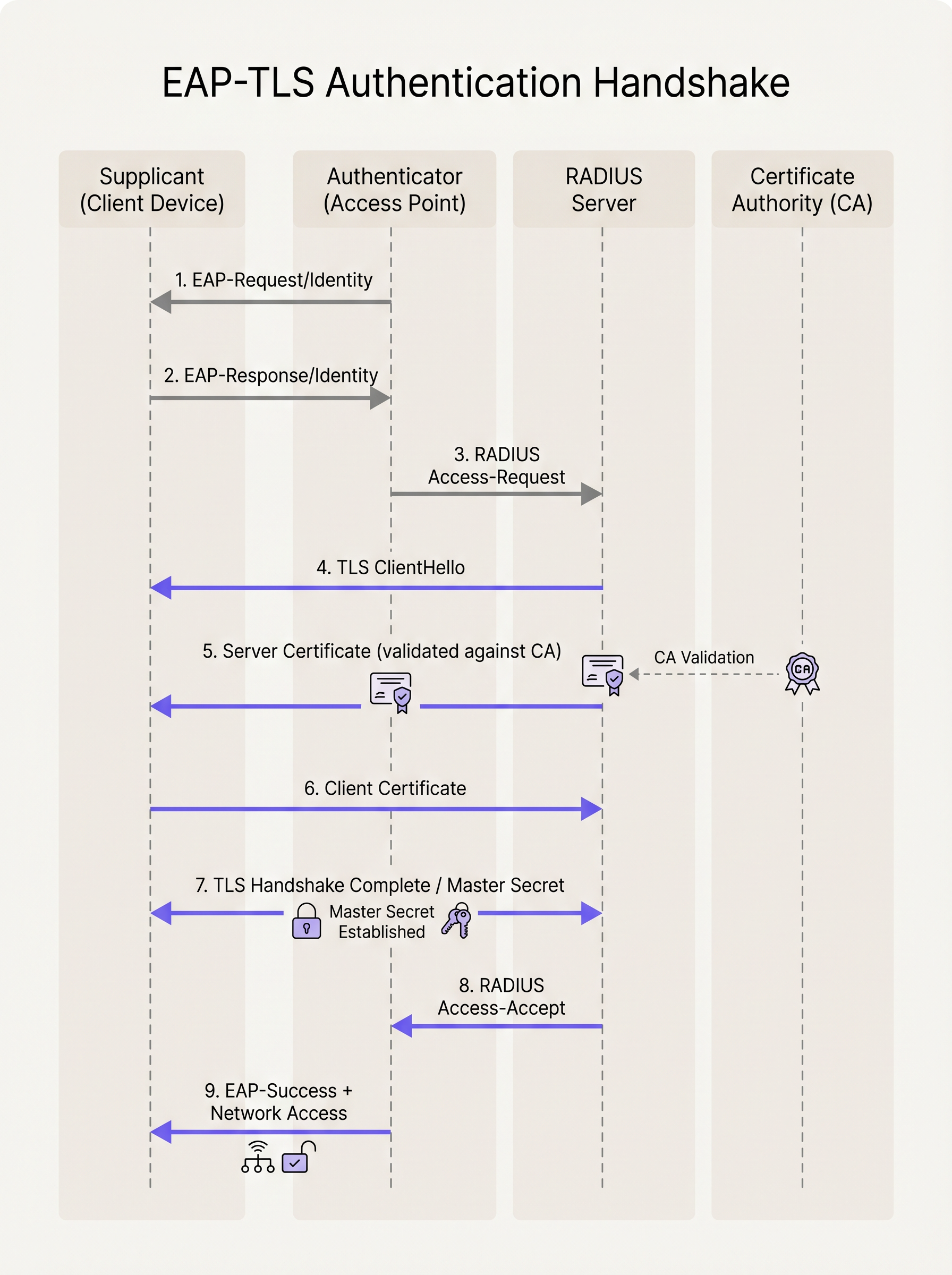
- Initialization: When a device attempts to connect to the SSID, the Access Point blocks all traffic except EAP over LAN (EAPoL) frames. The AP sends an
EAP-Request/Identityto the device. - Identity Response: The device responds with an
EAP-Response/Identity(often an anonymous outer identity for privacy), which the AP forwards to the RADIUS server. - TLS Tunnel Establishment: The RADIUS server initiates the TLS handshake by sending a
TLS ServerHelloalong with its own digital certificate. - Server Validation: The client device examines the server's certificate. It checks the validity dates, the subject alternative name (SAN), and crucially, verifies that the certificate was signed by a trusted Root Certificate Authority (CA) installed in its local trust store.
- Client Certificate Presentation: Once the server is validated, the client device sends its own X.509 certificate (and optionally its certificate chain) back to the RADIUS server.
- Mutual Authentication: The RADIUS server validates the client's certificate against its CA or Identity Provider (IdP) integration. It checks for revocation (via CRL or OCSP) and verifies the user or device identity.
- Key Derivation: Upon successful mutual validation, the TLS handshake completes. Both sides independently derive a Master Session Key (MSK).
- Network Access: The RADIUS server sends a
RADIUS Access-Acceptmessage to the AP, containing the MSK. The AP uses this key to establish the final WPA2/WPA3 encryption keys (PTK/GTK) with the client, and opens the network port for standard IP traffic.
EAP-TLS vs. PEAP-MSCHAPv2
Understanding the distinction between EAP-TLS and PEAP is critical for network architects planning a migration.
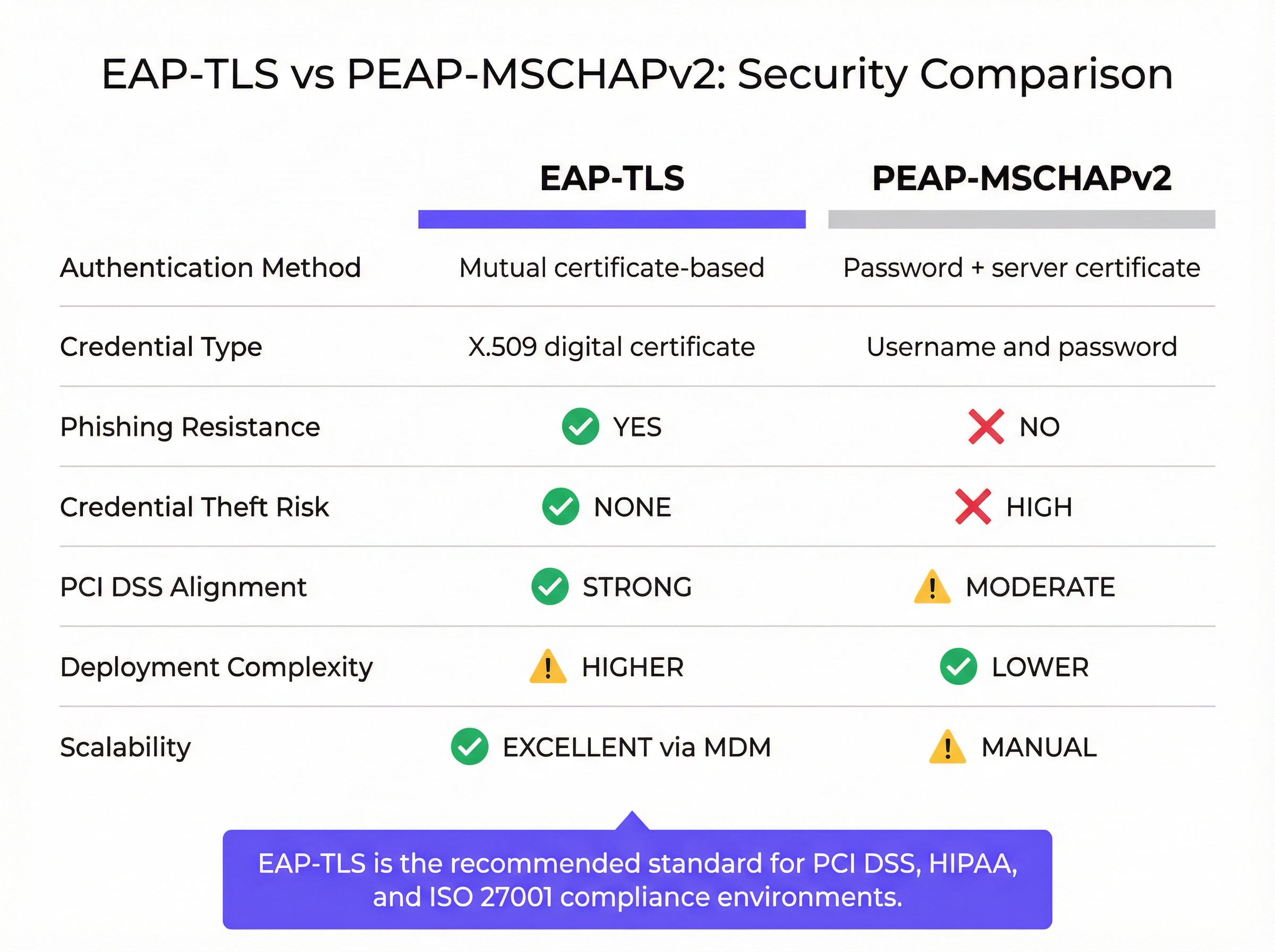
While PEAP establishes a secure TLS tunnel (server-side authentication), the inner authentication still relies on MSCHAPv2, a password-based protocol. If a user connects to a malicious "Evil Twin" Access Point and ignores the server certificate warning, their hashed password can be captured and cracked offline. EAP-TLS eliminates this vector entirely; without the private key corresponding to the client certificate, an attacker cannot authenticate, even if they possess the user's password.
Implementation Guide
Deploying EAP-TLS requires orchestration across three primary infrastructure pillars: the Network Layer, the Authentication Layer, and the Identity/Endpoint Management Layer.
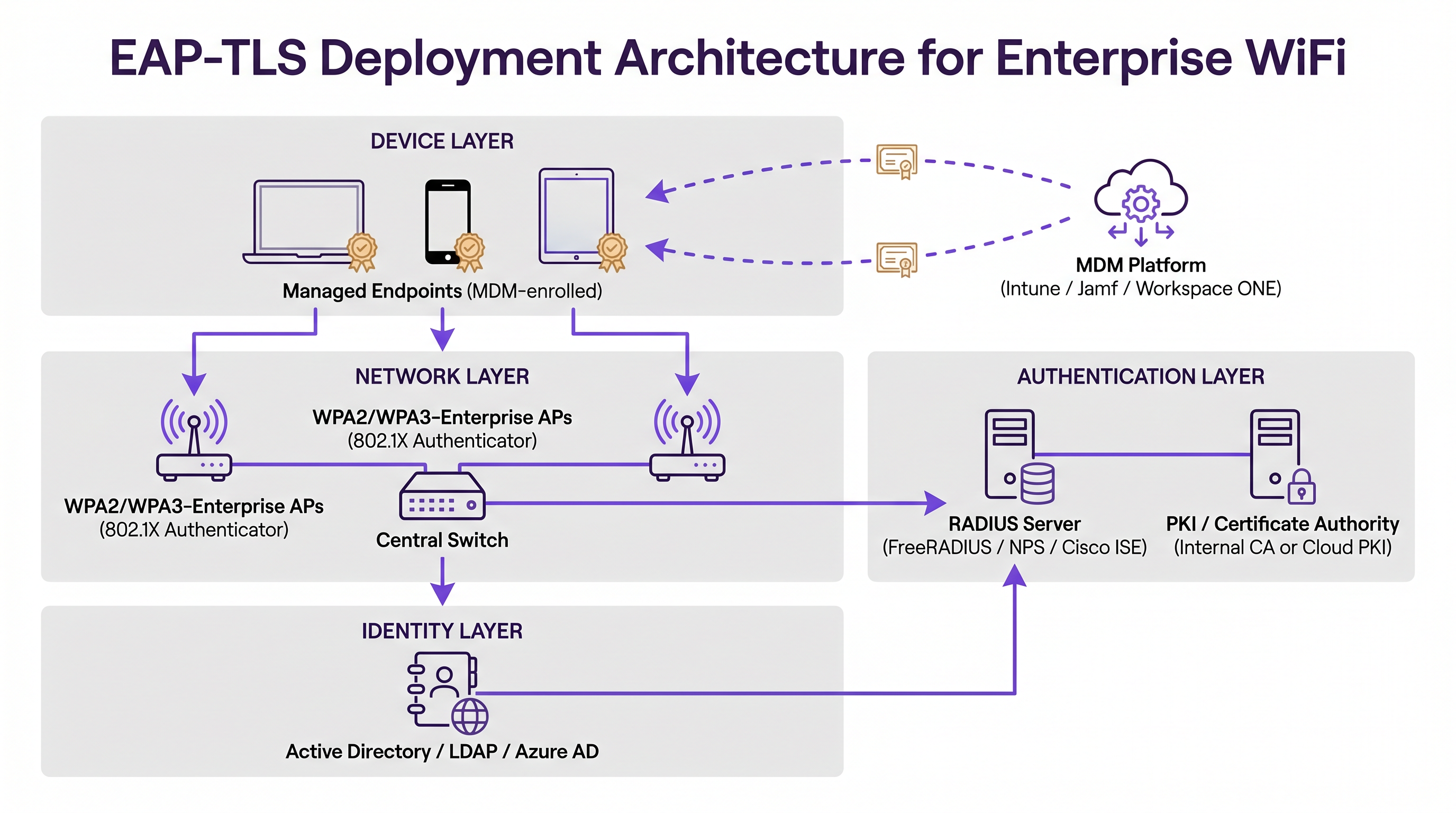
1. Public Key Infrastructure (PKI)
You must have a mechanism to issue and manage X.509 certificates. Historically, this meant deploying an on-premise Microsoft Active Directory Certificate Services (AD CS) environment. Today, modern architectures leverage Cloud PKI solutions integrated with Identity Providers (IdPs) like Azure AD, Okta, or Google Workspace. These cloud-native CAs simplify the issuance and revocation lifecycle.
2. RADIUS Authentication Server
The RADIUS server (e.g., FreeRADIUS, Cisco ISE, Aruba ClearPass, or cloud-based RADIUS) must be configured to support EAP-TLS. It requires its own server certificate, signed by a CA trusted by all client devices. If you are integrating with a modern IdP, you may find our guide on Okta and RADIUS: Extending Your Identity Provider to WiFi Authentication particularly useful for bridging cloud identity with on-premise network hardware.
3. Mobile Device Management (MDM)
The most significant hurdle in EAP-TLS deployment is provisioning certificates to client devices. Manual installation is not scalable. You must leverage an MDM platform (such as Microsoft Intune, Jamf Pro, or VMware Workspace ONE) to automate this process. The MDM profile must deploy:
- The Root CA certificate (to trust the RADIUS server).
- The individual Client Certificate (often generated via SCEP or EST protocols).
- The WiFi profile configured to use WPA2/WPA3-Enterprise, EAP-TLS, and specifically referencing the deployed certificates.
Best Practices
- Automate Certificate Lifecycle Management: Certificates expire. If you lack an automated renewal mechanism (like SCEP/EST via MDM), devices will silently drop off the network when their certificates expire, leading to massive support ticket spikes. Set validity periods that balance security (e.g., 1 year) with operational overhead.
- Enforce Strict Server Validation: Configure client WiFi profiles to strictly validate the RADIUS server's certificate. Specify the exact server names and trusted Root CAs in the profile. Do not allow users to bypass certificate warnings.
- Implement Robust Revocation: Ensure your RADIUS server checks Certificate Revocation Lists (CRLs) or uses the Online Certificate Status Protocol (OCSP). When an employee departs or a device is lost, revoking the certificate must immediately terminate network access.
- Handle the Mixed-Device Fleet: EAP-TLS is perfect for managed corporate devices. However, you will encounter unmanaged BYOD (Bring Your Own Device) and guest devices. For guests, deploy a robust captive portal solution like Purple's Guest WiFi. For staff BYOD, consider an onboarding portal that temporarily provisions a certificate, or utilize a separate SSID with a different authentication method, isolated from the core corporate network.
Troubleshooting & Risk Mitigation
When EAP-TLS fails, the symptoms are often opaque to the end-user. The device simply fails to connect. IT teams must rely on RADIUS logs for diagnostics.
- Error: "Unknown CA" or "Untrusted Root": The client device does not have the Root CA certificate that signed the RADIUS server's certificate in its trust store. Verify the MDM payload.
- Error: "Certificate Expired": Either the client certificate or the server certificate has passed its
NotAfterdate. Check the certificate lifecycle automation. - Error: "Client Certificate Not Found": The device is attempting EAP-TLS but cannot locate a valid certificate matching the criteria specified in the WiFi profile. Ensure the certificate was successfully deployed by the MDM and that the Subject Alternative Name (SAN) matches the expected format (e.g., User Principal Name or MAC address).
- Clock Skew: TLS relies on accurate timekeeping. If a device's system clock is significantly out of sync with the RADIUS server, certificate validation will fail because the certificates will appear to be "not yet valid" or "expired."
ROI & Business Impact
Transitioning to EAP-TLS represents a significant maturation of an organisation's security posture. The primary Return on Investment (ROI) is risk mitigation. By eliminating password-based WiFi authentication, you drastically reduce the attack surface for credential theft and lateral movement within the network. This is particularly critical in Hospitality and enterprise environments where network segmentation is paramount.
Furthermore, EAP-TLS improves the end-user experience. Once provisioned via MDM, the connection is entirely zero-touch. Users never have to update WiFi passwords when their corporate password expires, reducing helpdesk calls related to connectivity issues. By combining EAP-TLS for managed staff devices with intelligent WiFi Analytics and captive portals for guests, venues can achieve a secure, high-performance wireless environment that supports both operational security and customer engagement.
Key Terms & Definitions
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An 802.1X authentication method that requires mutual authentication using digital certificates on both the client and the server, eliminating the need for passwords.
The most secure standard for enterprise WiFi authentication, widely mandated for compliance in high-security environments.
Supplicant
The client device (laptop, smartphone, tablet) attempting to connect to the secure network.
The supplicant software must support EAP-TLS and have access to the device's certificate store.
Authenticator
The network device (typically a WiFi Access Point or network switch) that facilitates the authentication process by passing EAP messages between the Supplicant and the Authentication Server.
The AP does not perform the authentication itself; it acts as a gatekeeper until the RADIUS server issues an Access-Accept.
RADIUS Server
Remote Authentication Dial-In User Service. The central server that validates the credentials (certificates in the case of EAP-TLS) and authorizes network access.
The RADIUS server integrates with the PKI or Identity Provider to verify the validity and revocation status of the client certificate.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
You need a PKI (either on-premise or cloud-based) to issue the certificates required for EAP-TLS.
X.509 Certificate
A standard format for public key certificates, digital documents that securely associate cryptographic key pairs with identities such as websites, individuals, or organizations.
This is the 'digital passport' used in EAP-TLS instead of a password.
SCEP / EST
Simple Certificate Enrollment Protocol / Enrollment over Secure Transport. Protocols used by MDM platforms to automate the request and installation of certificates onto client devices.
Crucial for scaling EAP-TLS deployments, ensuring devices receive and renew certificates without user intervention.
Evil Twin Attack
A rogue WiFi access point that masquerades as a legitimate corporate network to eavesdrop on wireless communications or harvest credentials.
EAP-TLS defeats Evil Twin attacks because the rogue AP cannot present a valid server certificate signed by the company's trusted Root CA.
Case Studies
A large [Retail](/industries/retail) chain with 500 locations needs to secure WiFi access for their corporate-issued point-of-sale (POS) tablets. They currently use a single Pre-Shared Key (PSK) across all stores, which was recently leaked. They use Microsoft Intune for device management. How should they secure the network?
- Deploy a Cloud PKI integrated with their Azure AD environment.
- Configure Intune to use SCEP (Simple Certificate Enrollment Protocol) to automatically generate and push unique device certificates to each POS tablet.
- Push a new WiFi profile via Intune configured for WPA3-Enterprise and EAP-TLS, specifying the new client certificate and the trusted Root CA.
- Configure the central RADIUS server to authenticate the tablets based on these certificates.
- Once all tablets are successfully authenticating via EAP-TLS, disable the legacy PSK SSID.
A [Transport](/industries/transport) hub (airport) wants to provide secure WiFi for its operational staff (baggage handlers, security) using managed iPads, while keeping guest traffic completely separate.
- Implement EAP-TLS on a dedicated, hidden SSID (e.g., 'Airport-Ops-Secure') for the managed iPads, pushing certificates via their MDM platform.
- Ensure the RADIUS server maps these authenticated devices to a specific, restricted VLAN that only has access to necessary operational servers.
- Deploy a separate, open SSID (e.g., 'Airport-Free-WiFi') for passengers, utilizing a captive portal for terms-of-service acceptance and bandwidth limiting.
Scenario Analysis
Q1. Your organisation is migrating from PEAP to EAP-TLS. During the pilot phase, several Windows laptops fail to connect. The RADIUS logs show 'Unknown CA' errors during the TLS handshake. What is the most likely cause?
💡 Hint:Think about the 'Mutual' part of mutual authentication. What does the client need to trust the server?
Show Recommended Approach
The client devices are missing the Root CA certificate in their local trust store that signed the RADIUS server's certificate. The MDM payload needs to be updated to ensure the Root CA is pushed to the devices alongside the client certificate.
Q2. A hotel wants to use EAP-TLS for all devices, including guest smartphones, to ensure maximum security. Is this a viable strategy?
💡 Hint:Consider the provisioning process for EAP-TLS.
Show Recommended Approach
No, this is not a viable strategy. EAP-TLS requires client certificates to be installed on the device. While this is easy for managed corporate devices via MDM, you cannot force guests to install certificates or MDM profiles on their personal devices. For guests, a captive portal (like Purple Guest WiFi) combined with WPA2/WPA3-Personal (or OWE) is the industry standard.
Q3. You have successfully deployed EAP-TLS. An employee reports their corporate laptop was stolen. What is the immediate technical action required to secure the network?
💡 Hint:How do you invalidate a digital certificate before its expiration date?
Show Recommended Approach
You must revoke the client certificate associated with that specific laptop within your PKI/CA. Ensure that your RADIUS server is configured to check the Certificate Revocation List (CRL) or use OCSP, so that the revoked certificate is immediately rejected upon the next connection attempt.
Key Takeaways
- ✓EAP-TLS is the most secure 802.1X authentication method, replacing passwords with mutual certificate-based authentication.
- ✓It eliminates the risk of credential theft and Evil Twin attacks inherent in password-based protocols like PEAP-MSCHAPv2.
- ✓A successful deployment requires coordination between a PKI (to issue certificates), a RADIUS server (to authenticate), and an MDM platform (to provision devices).
- ✓Automated certificate lifecycle management (via SCEP/EST) is critical to prevent mass connectivity outages when certificates expire.
- ✓EAP-TLS is ideal for managed corporate devices; unmanaged BYOD and guest devices require separate onboarding or captive portal strategies.
- ✓Implementing EAP-TLS strongly aligns with compliance mandates like PCI DSS and ISO 27001 by securing network access control.



