GDPR Compliance for Guest WiFi Data Collection
This guide provides IT managers, network architects, and Data Protection Officers with a comprehensive, actionable framework for achieving GDPR compliance across guest WiFi deployments in hospitality, retail, and public-sector venues. It covers the full spectrum of data collected by guest WiFi networks, the legal requirements for obtaining valid consent, best-practice data retention policies, and how to implement a defensible compliance architecture. Venue operators will learn how to transform their guest WiFi from a potential regulatory liability into a strategic asset that builds customer trust and drives measurable business intelligence.
🎧 Listen to this Guide
View Transcript
Executive Summary
This guide provides IT managers, network architects, and venue operators with a practical, actionable framework for ensuring their guest WiFi services are fully compliant with the General Data Protection Regulation (GDPR). We will explore the specific types of data collected through guest WiFi, the legal requirements for consent and data handling, and vendor-neutral best practices for implementing a compliant solution. For the Chief Technology Officer and Data Protection Officer, this document outlines how to mitigate legal and financial risks associated with non-compliance, which can include fines of up to 4% of annual global turnover. For the Operations Director, it demonstrates how a compliant guest WiFi deployment can enhance customer trust and provide valuable, ethically sourced business intelligence. We will cover the technical architecture of a compliant system, from the design of the captive portal to the automation of data retention policies. The guide also includes real-world case studies from hospitality and retail, demonstrating the tangible ROI of a well-architected, compliant guest WiFi platform like Purple. By following the principles in this guide, organisations can transform their guest WiFi from a potential compliance liability into a strategic asset that drives business growth while respecting user privacy.

Technical Deep-Dive
Understanding GDPR compliance for guest WiFi begins with a clear-eyed assessment of the data being processed. Under the regulation, 'personal data' is defined broadly as any information relating to an identified or identifiable natural person. In the context of a guest WiFi network, this encompasses a wider range of data points than many organisations assume. A failure to correctly classify this data is a foundational error in compliance strategy.
Data Categories in Guest WiFi
The data collected via a guest WiFi network can be segmented into four primary categories. Each has distinct implications for GDPR compliance, particularly concerning the legal basis for processing and the required retention period.
| Data Category | Examples | Primary Legal Basis | Key Compliance Consideration |
|---|---|---|---|
| Registration Data | Name, email address, phone number, social media profile data | Consent | Must be freely given, specific, informed, and unambiguous. Data collected must be minimised. |
| Device & Session Data | MAC address, IP address, device type, browser, connection/disconnection timestamps, data usage | Legitimate Interest / Consent | Transparency is key. Users must be informed of this collection. Anonymisation should be used where possible. |
| Location Data | Real-time device location, footfall patterns, dwell times, heatmaps | Explicit Consent | High-risk processing. Requires a clear, specific opt-in. Purpose must be clearly articulated (e.g., 'to improve store layout'). |
| Usage & Browsing Data | Websites visited, applications used (less common) | Explicit Consent | Extremely high-risk and rarely justifiable. Should be avoided unless there is a critical, explicit, and consented purpose. |
The Legal Basis: Consent vs. Legitimate Interest
While Legitimate Interest can be argued for processing basic session data required for network security and performance monitoring (e.g., as per recital 49 of the GDPR), the ICO and other EU data protection authorities have set a high bar. For any data used for marketing, analytics, or user profiling, Consent is the only appropriate legal basis.
According to the ICO, "You must make sure you can demonstrate that consent was freely given, specific and informed, and that it was an unambiguous indication of the individual's wishes."
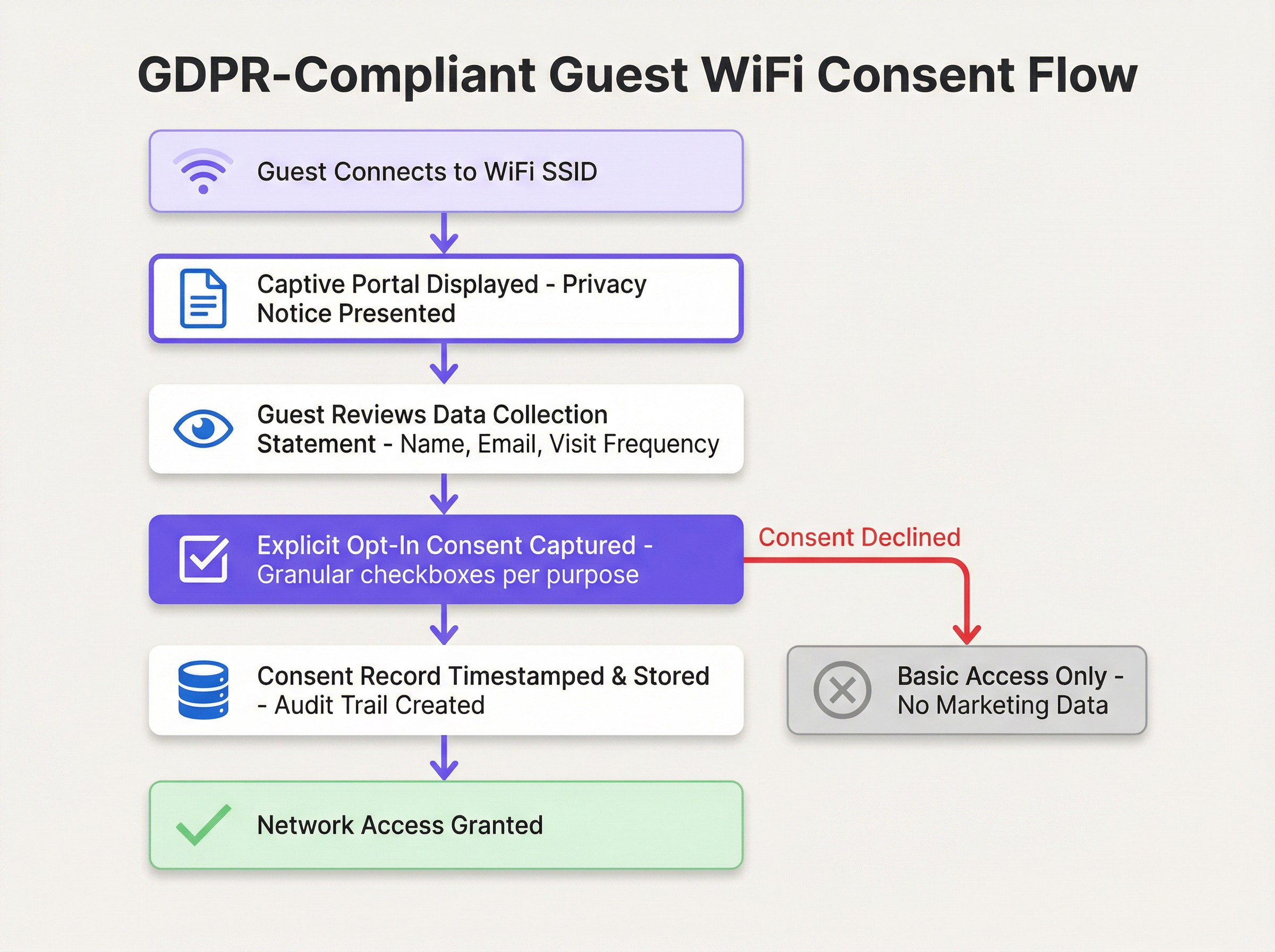
This necessitates a shift from passive acceptance of terms to an active, granular consent mechanism. The architecture of your captive portal is therefore not just a technical consideration, but a legal one.
Architectural Components for Compliance
A GDPR-compliant guest WiFi architecture is built on the principle of Privacy by Design and by Default. This means that data protection is not an add-on, but a core component of the system's design.
- Secure Network Foundation (WPA3/802.1X): Before any data is collected, the network itself must be secure. The use of WPA3 is the current industry standard, providing robust protection against eavesdropping. For enterprise environments, IEEE 802.1X offers port-based network access control, ensuring only authenticated and authorised devices can connect.
- The Compliant Captive Portal: This is the most critical user-facing component. It must present a 'just-in-time' privacy notice before the user enters any information, link to a full and accessible privacy policy, utilise granular unticked checkboxes for each processing purpose, and run over HTTPS to prevent man-in-the-middle attacks.
- Consent Management Platform (CMP): Behind the scenes, a robust CMP is required to log every consent action with an immutable audit trail, manage the consent lifecycle including withdrawal, and integrate with a DSAR workflow to facilitate the easy finding, export, or deletion of a specific user's data.
Implementation Guide
Deploying a GDPR-compliant guest WiFi solution requires a structured approach, moving from policy definition to technical configuration.
Phase 1: Policy and Requirements Definition (Weeks 1-2)
Before deploying any hardware or software, your organisation must define its policies. Convene a stakeholder workshop with representatives from IT, Legal, Marketing, and Operations to agree on the purpose of the guest WiFi. Conduct a Data Minimisation Assessment, documenting the specific business justification for each data point requested. Define and document the retention period for each category of data, and formally select and document the lawful basis for each processing activity.
Phase 2: Technical Solution Design & Vendor Selection (Weeks 3-4)
With a clear policy in place, assess your current network infrastructure for WPA3 and VLAN segmentation capability. Evaluate captive portal and CMP vendors against criteria including customisable portal design, robust and searchable consent audit logs, DSAR automation tools, automated data retention rules, and CRM integration capabilities.

Phase 3: Deployment and Testing (Weeks 5-6)
Deploy the solution in a staging environment first. Configure the captive portal with finalised text and unticked consent boxes, set up data retention rules, and implement role-based access control. Conduct end-to-end testing of the full user journey, including consent acceptance, consent decline, DSAR submission, and automated data deletion.
Phase 4: Production Rollout & Staff Training (Weeks 7-8)
Roll out the solution in a phased manner across venues. Train IT helpdesk and front-of-house staff to answer basic user questions and escalate privacy-specific queries to the Data Protection Officer. Ensure all configurations and processes are thoroughly documented.
Best Practices
Beyond the technical implementation, adhering to industry-standard best practices is crucial for maintaining long-term GDPR compliance and building trust with your users.
Principle of Least Privilege: Grant access to personal data on a strict need-to-know basis using role-based access control (RBAC). Marketing teams should not have access to network security logs, and vice versa.
Regular Audits and Penetration Testing: Schedule annual audits covering consent log review, retention policy verification, and DSAR process testing. Engage a third party for penetration testing of the captive portal and WiFi infrastructure.
User-Facing Transparency: Implement a layered privacy notice on the captive portal, provide a self-service preference centre for users to manage their data, and supplement digital efforts with clear on-site signage in your venue.
Data Anonymisation and Pseudonymisation: Employ anonymisation or pseudonymisation techniques as early in the data lifecycle as possible. For analytics, store a one-way hash of the MAC address rather than the raw identifier, and use pseudonymised identifiers in your analytics database to reduce compliance scope.
Troubleshooting & Risk Mitigation
Even with a well-designed system, operational issues and compliance risks can arise. Proactively identifying and planning for these scenarios is a hallmark of a mature data governance programme.
| Failure Mode | Impact | Mitigation & Solution |
|---|---|---|
| Consent Record Mismatch | High. Inability to prove consent can lead to regulatory fines. | Deploy a CMP with an immutable, timestamped audit log. Immediately remove the user from marketing lists upon dispute. |
| Data Retention Failure | Medium to High. Technical breach of policy, critical if a deletion DSAR is received. | Implement robust monitoring and alerting for all data purge jobs. Manually trigger purge and conduct a post-mortem. |
| Captive Portal Bypass | Low to Medium. Unauthorised network access risk. | Implement strict firewall rules blocking all traffic from unauthenticated devices except DHCP and DNS to the portal. |
| DSAR Process Breakdown | High. Failure to respond within one month violates GDPR Article 15. | Create a dedicated monitored privacy email alias. Conduct mandatory annual staff training on DSAR identification and escalation. |
For proactive risk mitigation, conduct a Data Protection Impact Assessment (DPIA) before deploying or significantly modifying a guest WiFi system. Perform thorough vendor due diligence, reviewing security certifications (ISO 27001, SOC 2) and ensuring a robust Data Processing Addendum is in place. Maintain a documented incident response plan that covers the 72-hour breach notification requirement.
ROI & Business Impact
A GDPR-compliant guest WiFi solution should not be viewed as a cost centre. When implemented correctly, it is a strategic enabler delivering measurable ROI through risk mitigation, enhanced customer trust, and ethical business intelligence.
GDPR fines can reach €20 million or 4% of annual global turnover. A compliant platform costing €50,000 annually represents a fraction of this potential liability. Beyond risk mitigation, anonymised and aggregated data collected with user consent provides powerful insights into footfall, dwell times, visit frequency, and demographic patterns. A retail chain with a €50M annual turnover that avoids a €2M fine and grows its consented marketing database by 10,000 users (at an average lead value of €10) achieves a compelling, multi-dimensional ROI.
By framing the discussion around risk mitigation, customer trust, and ethical data-driven decision-making, IT leaders can demonstrate that a GDPR-compliant guest WiFi solution is not just a legal necessity, but a powerful engine for business growth.
Key Terms & Definitions
GDPR (General Data Protection Regulation)
The EU's primary data protection law, which came into force on 25 May 2018 and was retained in UK law post-Brexit as the UK GDPR. It governs how organizations collect, process, store, and share personal data of individuals in the UK and EU. Non-compliance can result in fines of up to €20 million or 4% of annual global turnover.
IT teams encounter GDPR as the overarching legal framework governing every aspect of their guest WiFi data collection. It is the source of all consent, retention, and transparency requirements discussed in this guide.
Captive Portal
A web page presented to a user when they first connect to a guest WiFi network, before they are granted full internet access. It is the primary mechanism for presenting privacy notices, capturing consent, and collecting registration data (e.g., name, email). Under GDPR, the design of the captive portal is a critical compliance control.
Network architects and IT managers configure captive portals as part of the guest WiFi deployment. The portal's design — specifically the consent checkboxes and privacy notice — directly determines the organization's GDPR compliance posture.
Data Controller
The organization that determines the purposes and means of processing personal data. When a hotel, retailer, or venue operator deploys guest WiFi and decides what data to collect and why, they become the Data Controller and bear primary responsibility for GDPR compliance.
Venue operators are often surprised to learn they are the Data Controller for their guest WiFi, not their technology vendor. This distinction is critical because it means the legal obligations and potential fines fall on the venue operator, not the platform provider.
Data Processor
An organization that processes personal data on behalf of a Data Controller. A guest WiFi platform provider like Purple acts as a Data Processor. The relationship must be governed by a formal Data Processing Addendum (DPA) that defines the processor's obligations and restrictions.
IT managers must ensure that a DPA is in place with every technology vendor that handles personal data collected via the guest WiFi. Without a DPA, the organization is in breach of GDPR Article 28.
Consent Management Platform (CMP)
A software system that manages the collection, storage, and lifecycle of user consent. In a guest WiFi context, a CMP records every consent event with a timestamp, the specific purposes consented to, and the version of the privacy notice presented. It also manages consent withdrawal and integrates with DSAR workflows.
A CMP is the technical backbone of GDPR compliance for guest WiFi. IT managers should evaluate any guest WiFi platform on the robustness of its CMP capabilities, particularly the immutability and searchability of its consent audit log.
Data Subject Access Request (DSAR)
A formal request from an individual (the 'data subject') to an organization, asking for a copy of all personal data held about them, or requesting that their data be corrected or deleted. Under GDPR, organizations must respond to DSARs within one calendar month.
IT managers and DPOs must have a documented, tested process for handling DSARs. Guest WiFi platforms should provide tools to quickly search for and export or delete a specific user's data, reducing the operational burden of fulfilling these requests.
Data Minimisation
A core GDPR principle (Article 5(1)(c)) requiring that personal data collected must be 'adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed.' In practice, this means only collecting the data you genuinely need for a specific, stated purpose.
Data minimisation is the most commonly violated principle in guest WiFi deployments. IT managers should challenge every data field on the captive portal with the question: 'What specific business purpose does this serve, and can we achieve that purpose without this data?'
Data Protection Impact Assessment (DPIA)
A formal process for identifying and minimizing the data protection risks of a project or system. Under GDPR Article 35, a DPIA is legally mandatory before undertaking any processing that is 'likely to result in a high risk' to individuals' rights and freedoms. This includes large-scale location tracking and systematic behavioural profiling.
IT managers and DPOs must conduct a DPIA before deploying guest WiFi systems that include footfall analytics, real-time location tracking, or marketing profiling. Failure to conduct a required DPIA is itself a GDPR violation.
Pseudonymisation
A data processing technique that replaces directly identifying information (e.g., a name or email address) with an artificial identifier, such that the data can no longer be attributed to a specific individual without the use of additional information kept separately. Unlike anonymisation, pseudonymisation is reversible.
IT architects use pseudonymisation in guest WiFi analytics databases to reduce the risk associated with a data breach. If the analytics database is compromised, the attacker cannot directly identify individuals. The 'key' linking the pseudonym to the real identity is stored separately with stronger access controls.
ICO (Information Commissioner's Office)
The UK's independent authority set up to uphold information rights in the public interest, promoting openness by public bodies and data privacy for individuals. The ICO is the primary supervisory authority for GDPR compliance in the UK. It has the power to issue fines, conduct audits, and publish enforcement actions.
UK-based venue operators must comply with UK GDPR as enforced by the ICO. IT managers should monitor ICO guidance and enforcement notices, as these provide practical interpretation of how the law applies to specific scenarios, including guest WiFi.
Case Studies
A 250-room, four-star hotel group with 12 properties across the UK wants to deploy guest WiFi across all sites. Their primary goals are to provide a seamless connectivity experience for guests, build a consented marketing database for their loyalty programme, and gain footfall analytics to optimise lobby and restaurant layouts. Their current setup is a basic, unmanaged open WiFi network with no captive portal. How should they approach a GDPR-compliant deployment?
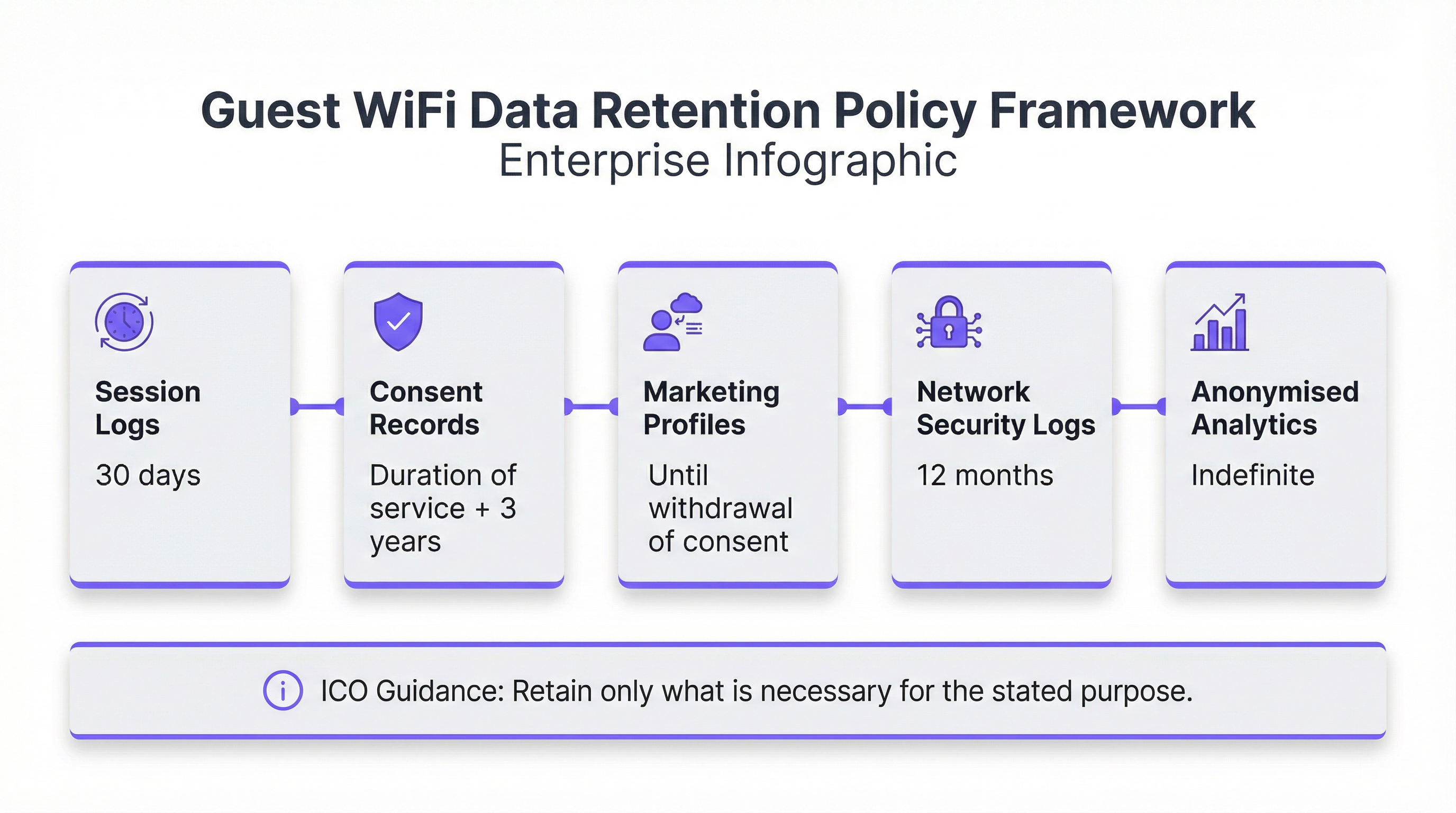
The deployment should follow a four-phase approach. In Phase 1 (Policy), the hotel group must convene a workshop with IT, Marketing, Legal, and the DPO. They need to define three distinct processing purposes: (1) providing network access, (2) marketing communications for the loyalty programme, and (3) footfall analytics. Each purpose requires a separate legal basis and consent mechanism. In Phase 2 (Design), they should select a managed guest WiFi platform such as Purple, which provides a customizable captive portal, a consent management platform, and integrated analytics. The captive portal should be designed with a clear, two-step flow: first, a mandatory acceptance of terms for network access (which can use Legitimate Interest for basic session data); second, two separate, optional, unticked checkboxes — one for 'Loyalty Programme Marketing' and one for 'Anonymous Footfall Analytics'. The privacy notice must be concise and clearly explain each purpose. In Phase 3 (Deployment), the solution should be staged at a single property first. The team must configure automated data retention rules: session logs purged after 30 days, marketing profiles retained until consent is withdrawn, and footfall analytics data anonymised at the point of collection and retained indefinitely. In Phase 4 (Rollout), the solution is deployed to all 12 properties with a phased rollout over 8 weeks. Front desk staff are trained to direct guests to the WiFi and to escalate any data queries to the DPO.
A national retail chain with 85 stores wants to use their guest WiFi to run footfall heatmaps and measure the effectiveness of in-store promotional displays. Their marketing team wants to use the WiFi to send push notifications to customers who are currently in-store. Their IT team is concerned about GDPR compliance, particularly around the use of MAC addresses for tracking. How should the IT manager advise the business?
The IT manager should advise the business that this use case is achievable but requires careful architectural decisions. First, regarding MAC address tracking: modern mobile devices (iOS 14+ and Android 10+) use MAC address randomization by default, which means that a MAC address is not a stable, persistent identifier for a specific device. However, it is still considered personal data when collected, as it can be combined with other data to identify an individual. The IT manager should recommend that the analytics platform anonymise the MAC address immediately upon collection (using a one-way hash), and that the analytics dashboard only ever display aggregated, anonymised data. This significantly reduces the GDPR risk. Second, regarding in-store push notifications: this is a high-risk processing activity that requires explicit, specific consent. The captive portal must include a specific, unticked checkbox that reads: 'I consent to receiving personalised offers and notifications while I am connected to the store WiFi.' The purpose must be clearly explained. Third, the IT manager should recommend conducting a DPIA before deploying the push notification feature, as it involves real-time location-based processing of personal data. The DPIA should assess the risk to user privacy and document the mitigations in place. A platform like Purple can support this use case with its consent management, analytics, and marketing automation capabilities, while providing the audit trail needed to demonstrate compliance.
Scenario Analysis
Q1. You are the IT Manager for a 50-store retail chain. Your Marketing Director wants to deploy guest WiFi and use it to send in-store push notifications to customers who have previously visited any of your stores. The notifications would be triggered when a known device (identified by MAC address) reconnects to any store's WiFi. Your DPO has flagged this as high-risk. What steps must you take before this feature can be deployed, and what technical safeguards are required?
💡 Hint:Consider the DPIA trigger checklist, the specific consent required for cross-store device tracking, and the technical challenges of MAC address randomization on modern devices.
Show Recommended Approach
Before deploying this feature, you must: (1) Conduct a mandatory Data Protection Impact Assessment (DPIA), as this involves systematic monitoring of individuals across multiple locations using device identifiers — a clear GDPR Article 35 trigger. The DPIA must document the risks and the mitigations. (2) Redesign the captive portal to include a specific, unticked consent checkbox that clearly explains cross-store device recognition and targeted notifications. The language must be explicit: 'I consent to [Brand] recognising my device across all stores and sending me personalised offers when I connect.' (3) Address the MAC randomization challenge: since modern iOS and Android devices randomize MAC addresses, you cannot reliably use raw MAC addresses for cross-store recognition. You must instead require users to authenticate via a persistent identifier such as an email address or social login, which then becomes the cross-store tracking key. (4) Implement a Data Processing Addendum with your push notification provider. (5) Provide a clear, accessible opt-out mechanism in every push notification and in a self-service preference center. Only after completing these steps and obtaining sign-off from the DPO should the feature be deployed.
Q2. Your organization has received a Data Subject Access Request from a former hotel guest who stayed 18 months ago. They are requesting a copy of all personal data you hold about them, including their WiFi session history. Your current guest WiFi platform stores session logs indefinitely. What are your immediate obligations, and what systemic changes should you make?
💡 Hint:Consider the one-month response deadline, the data minimisation principle, and the need for a documented retention policy.
Show Recommended Approach
Your immediate obligations are: (1) Acknowledge the DSAR in writing within 5 working days, confirming you have received it and will respond within one calendar month. (2) Search all systems — your guest WiFi CMP, CRM, and any email marketing platforms — for all personal data associated with this individual. (3) Compile and provide a copy of all data found, in a commonly used electronic format, within one calendar month of receipt. This includes session logs, consent records, and any marketing profile data. The systemic change required is urgent: storing session logs indefinitely is a clear violation of the GDPR data minimisation and storage limitation principles. You must immediately define and implement a data retention policy. Session logs should be purged after 30-90 days. You must configure automated retention rules in your guest WiFi platform to enforce this policy going forward. Additionally, you should implement a formal DSAR intake process — a dedicated privacy email alias, a trained point of contact, and a documented workflow — to ensure future requests are handled efficiently and within the statutory deadline.
Q3. A conference centre is deploying guest WiFi for a major three-day event with 5,000 attendees. The event organiser wants to use the WiFi analytics to provide sponsors with data on how many unique visitors attended each sponsor's exhibition stand. The data would be presented as a report showing stand visit counts and average dwell times per stand. Is this use case GDPR-compliant as described, and what conditions must be met for it to proceed?
💡 Hint:Consider the distinction between anonymised aggregate data and personal data, and the specific consent required for location-based analytics.
Show Recommended Approach
The use case as described is potentially compliant, but only under specific conditions. The key question is whether the data provided to sponsors is truly anonymised and aggregated, or whether it could be used to identify individuals. If the report shows only aggregate counts (e.g., 'Stand A received 342 unique device visits with an average dwell time of 4.2 minutes'), and if the underlying device-level data has been irreversibly anonymised before any analysis, then this data is no longer personal data and can be shared with sponsors without restriction. However, to get to this point, the following conditions must be met: (1) The captive portal for the event WiFi must include a specific, unticked consent checkbox for 'Anonymous footfall analytics to measure event attendance and stand popularity.' The purpose and the fact that aggregated data will be shared with event sponsors must be clearly disclosed. (2) The analytics platform must anonymise device identifiers (e.g., hash the MAC address) at the point of collection, before any analysis is performed. (3) The reports shared with sponsors must contain only aggregated data with no possibility of re-identification. If any stand had very few visitors, the data for that stand should be suppressed to prevent re-identification. (4) A DPIA should be conducted given the large scale of the data collection. If these conditions are met, the use case is compliant and represents a legitimate and valuable application of guest WiFi analytics.
Key Takeaways
- ✓Guest WiFi networks collect four categories of personal data under GDPR: registration data, device and session data, location data, and usage data. Each requires a distinct legal basis and compliance approach.
- ✓Consent for marketing and analytics must be freely given, specific, informed, and unambiguous. This means separate, unticked checkboxes for each purpose on the captive portal — never bundled with the terms of service for network access.
- ✓A robust data retention policy is non-negotiable. Session logs should be purged after 30 days, consent records retained for 2 years post-last-interaction, and marketing profiles deleted upon consent withdrawal. Automate these rules in your CMP.
- ✓A Data Protection Impact Assessment (DPIA) is legally mandatory before deploying guest WiFi systems that involve large-scale location tracking, behavioural profiling, or processing data from vulnerable groups.
- ✓Your guest WiFi vendor is a Data Processor. A formal Data Processing Addendum (DPA) must be in place before any personal data is shared with them. Evaluate vendors on their security certifications (ISO 27001, SOC 2) and GDPR compliance documentation.
- ✓GDPR compliance for guest WiFi is not just a cost — it is a strategic enabler. A compliant platform mitigates fines of up to 4% of global turnover, builds customer trust, and provides ethically sourced business intelligence that drives operational and marketing ROI.
- ✓In the event of a personal data breach, the 72-hour notification clock starts the moment you become aware of it. Build this timeline into your incident response plan and ensure your team knows to notify before the investigation is complete.



