OCSP and Certificate Revocation for WiFi Authentication
This comprehensive guide explores the critical mechanisms of certificate revocation in enterprise WiFi environments, focusing on the transition from CRLs to OCSP. It provides actionable implementation strategies for IT teams managing large-scale, high-density networks where real-time security and low latency are paramount.
🎧 Listen to this Guide
View Transcript

Executive Summary
For enterprise venues operating high-density WiFi networks—from sprawling retail chains to modern conference centres—certificate-based authentication (EAP-TLS) is the definitive standard for securing network access. However, issuing a certificate is only half the lifecycle. The critical operational challenge lies in revocation: ensuring that when a device is compromised, lost, or decommissioned, its network access is terminated immediately. This guide explores the technical architecture of certificate revocation, contrasting legacy Certificate Revocation Lists (CRLs) with the Online Certificate Status Protocol (OCSP). We detail how RADIUS servers integrate with Public Key Infrastructure (PKI) to enforce real-time revocation, the complexities of OCSP stapling in an 802.1X context, and the strategic deployment models required to balance stringent security with seamless user experience. By implementing robust OCSP checking, venue operators can mitigate risk, ensure compliance, and maintain the high throughput required for Guest WiFi and enterprise access.
Listen to our 10-minute executive briefing on this topic:
Technical Deep-Dive
The Mechanics of Revocation in 802.1X
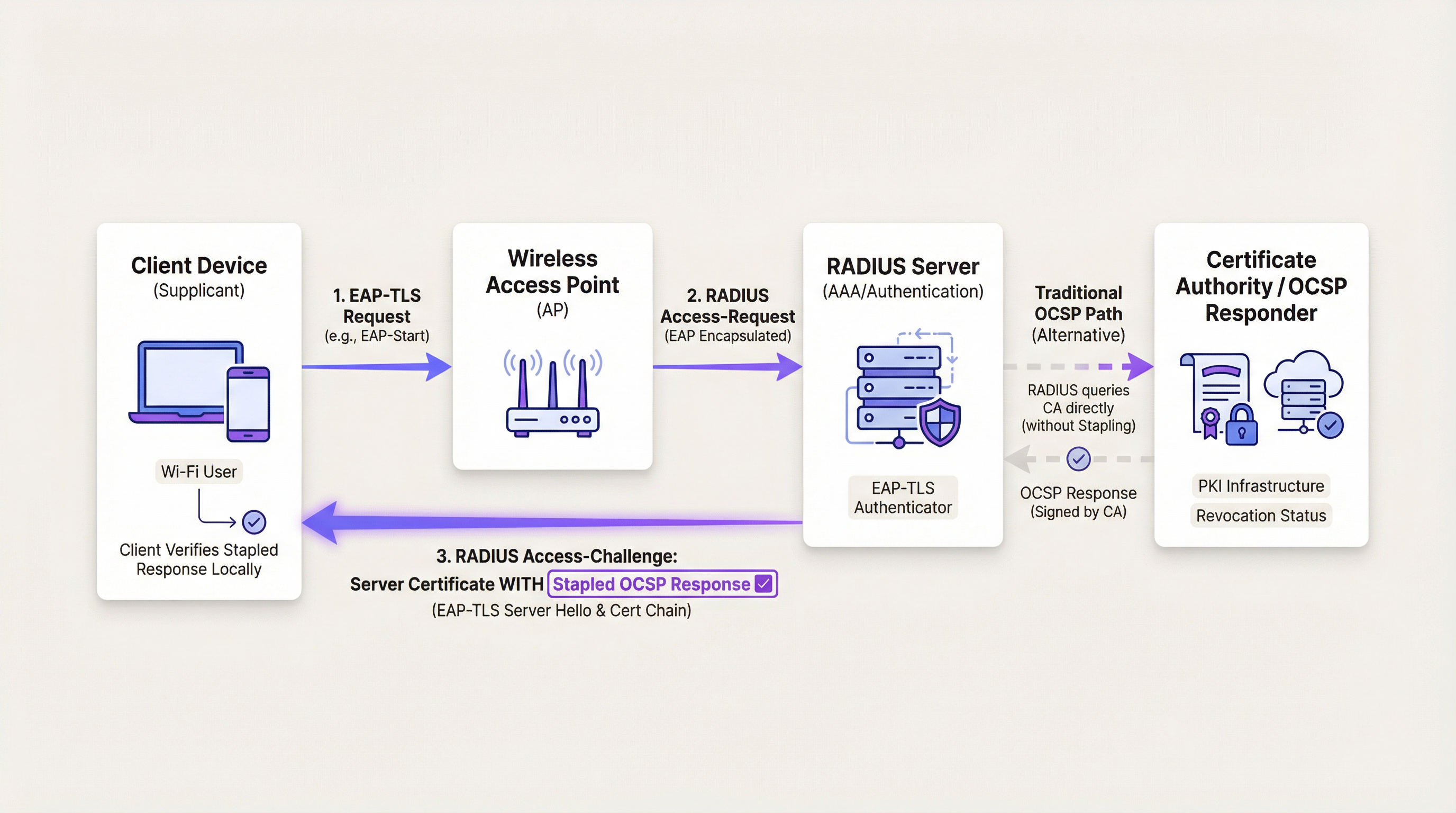
In an 802.1X authentication flow, the Wireless Access Point (AP) acts as an authenticator, passing Extensible Authentication Protocol (EAP) messages between the client device (supplicant) and the RADIUS server. When a client presents a certificate during the EAP-TLS handshake, the RADIUS server must validate its cryptographic integrity, verify its trust chain, and confirm its current revocation status.
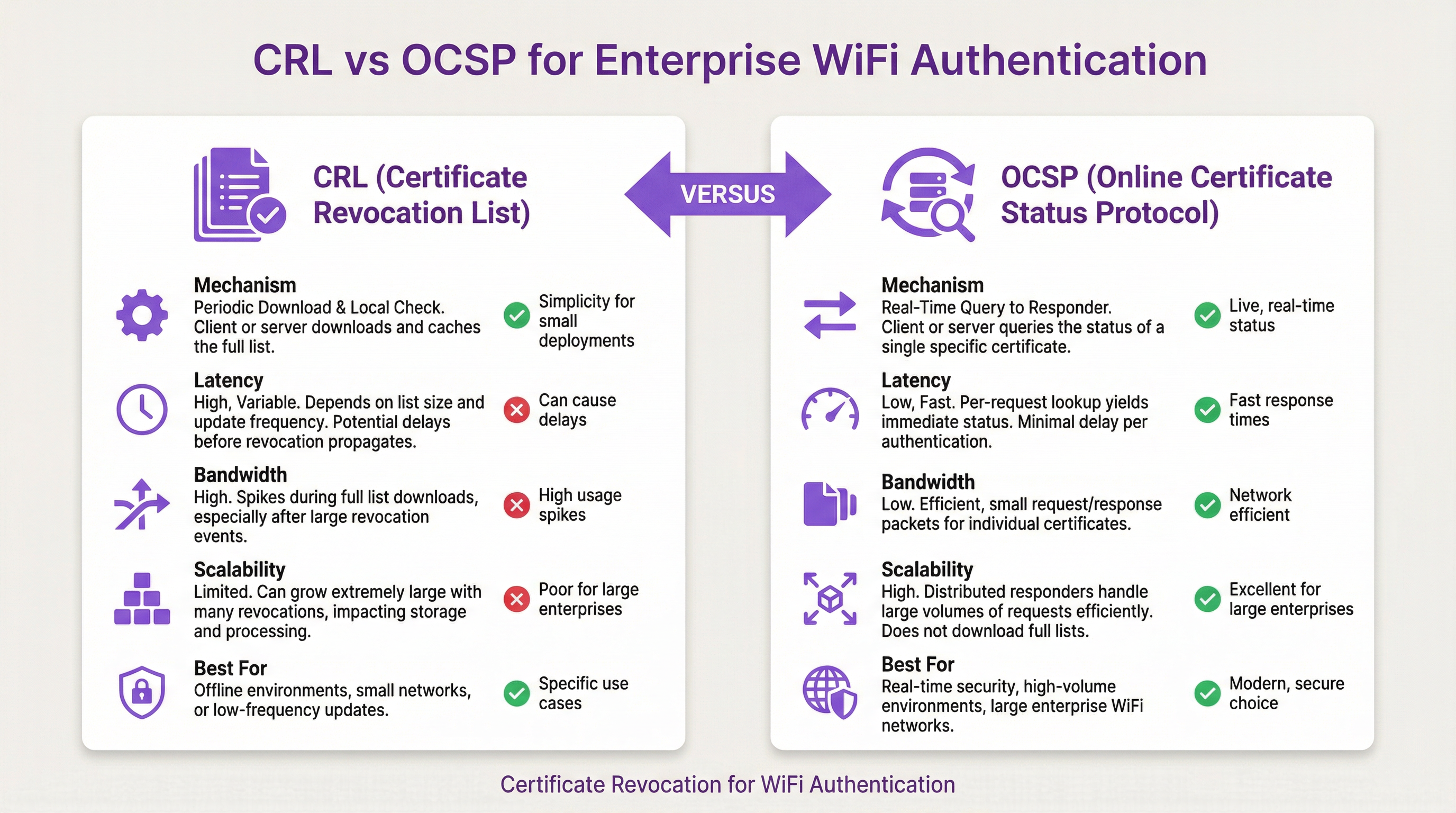
Historically, this was achieved via a Certificate Revocation List (CRL). A CRL is a digitally signed file containing the serial numbers of all revoked certificates issued by a specific Certificate Authority (CA). The RADIUS server downloads this file periodically and caches it locally. While simple to implement, CRLs present significant scalability challenges. In large enterprise environments, such as those found in the Retail sector, CRLs can grow to megabytes in size. Downloading and parsing these lists consumes bandwidth and processing cycles. More critically, CRLs introduce a vulnerability window: the time between a certificate being revoked at the CA and the RADIUS server downloading the updated list.
The Transition to OCSP
To address the limitations of CRLs, the Online Certificate Status Protocol (OCSP) was developed. OCSP replaces the bulk download model with a real-time, targeted query mechanism. When a client presents a certificate, the RADIUS server extracts the OCSP responder URI from the certificate's Authority Information Access (AIA) extension. It then sends a lightweight HTTP request to the responder, querying the status of that specific certificate serial number. The responder returns a signed response indicating whether the certificate is 'Good', 'Revoked', or 'Unknown'.
This approach eliminates the vulnerability window associated with CRLs, enforcing revocations immediately. It also significantly reduces bandwidth consumption, as the RADIUS server only requests data for certificates actively attempting authentication.
OCSP Stapling in WiFi Environments
OCSP stapling is a performance optimisation technique widely used in web servers. Instead of the client querying the OCSP responder, the server periodically queries the responder for its own certificate status. It then 'staples' the signed response to the certificate it presents to the client during the TLS handshake. This shifts the query burden from the client to the server and reduces the number of external network connections required.
In the context of WiFi authentication, OCSP stapling is highly relevant but nuanced. During EAP-TLS, the RADIUS server presents its own server certificate to the client to prove its identity. The RADIUS server can utilise OCSP stapling here, appending the OCSP response to the EAP-TLS Server Hello. This allows the client device to verify the RADIUS server's revocation status without requiring its own internet connection—a critical feature for devices that have not yet been granted network access.
However, stapling the client's certificate status is not feasible. The client cannot staple its own status because the network does not yet trust the client. Therefore, for client certificate validation, the RADIUS server must perform a traditional OCSP query to the CA.
Implementation Guide
Deploying OCSP in a high-density enterprise environment requires careful architectural planning to ensure both security and availability. The following steps outline a robust deployment strategy.
1. High-Availability CA Infrastructure
The shift to OCSP introduces a critical dependency on the CA's responder infrastructure. If the RADIUS server cannot reach the OCSP responder, it cannot definitively verify the certificate's status. Therefore, the OCSP responder must be highly available, geographically distributed, and placed behind load balancers to handle authentication spikes, such as those experienced during a major conference or sporting event.
2. RADIUS Server Configuration and Caching
To mitigate the latency introduced by real-time OCSP queries, enterprise RADIUS servers must be configured with intelligent caching mechanisms. When a RADIUS server receives a 'Good' response from the OCSP responder, it should cache that response for a configurable duration—typically between 15 and 60 minutes. Subsequent authentication requests from the same client within that window will be validated against the cache, bypassing the external query. This balances the need for real-time security with the performance requirements of a busy network.
3. Failover and Resilience Mechanisms
Network architects must define the RADIUS server's behaviour in the event that the OCSP responder is unreachable. This is known as 'fail open' versus 'fail closed'. In a 'fail closed' configuration, the RADIUS server will deny access if it cannot verify the certificate's status. This is the most secure posture but risks widespread outages if the CA infrastructure fails. In a 'fail open' configuration, the RADIUS server will permit access if the responder is unreachable, prioritising availability over strict security.
A recommended hybrid approach involves configuring the RADIUS server to attempt an OCSP query first. If the responder is unreachable, the server falls back to a locally cached CRL. This provides resilience against CA outages while maintaining a baseline level of revocation checking.
Best Practices
- Minimise Certificate Lifespans: While revocation handles premature invalidation, the most effective security control is a short certificate lifespan. Implement automated certificate provisioning via MDM to issue certificates valid for days or weeks, rather than years. This reduces reliance on revocation mechanisms entirely. For further reading on modern device security, refer to our guide on 802.1X Authentication: Securing Network Access on Modern Devices.
- Monitor OCSP Latency: Continuously monitor the latency of OCSP queries from your RADIUS servers to the CA infrastructure. High latency will directly impact the user experience, leading to authentication timeouts and dropped connections.
- Implement Strict CA Access Controls: The security of your WiFi network is intrinsically linked to the security of your CA. Ensure strict access controls, multi-factor authentication, and comprehensive auditing are in place for all CA management interfaces.
Troubleshooting & Risk Mitigation
When deploying OCSP, IT teams frequently encounter several common failure modes:
- Authentication Timeouts: If the OCSP responder is slow to reply, the EAP-TLS handshake may time out. This is often caused by network congestion or an under-provisioned CA infrastructure. Mitigation involves optimising OCSP caching on the RADIUS server and scaling the responder infrastructure.
- Clock Skew: OCSP responses are time-stamped and signed. If the clock on the RADIUS server is out of sync with the CA, the server may reject a valid OCSP response as expired. Ensure all infrastructure components are synchronised via reliable NTP servers.
- Firewall Blocking: OCSP queries typically use HTTP (port 80) or HTTPS (port 443). Ensure that firewalls between the RADIUS server and the CA infrastructure are configured to permit this traffic. Modern implementations increasingly use HTTPS to protect privacy and prevent network observers from analysing certificate queries.
ROI & Business Impact
Implementing robust certificate revocation mechanisms delivers measurable business value beyond raw security compliance.
- Risk Mitigation: By eliminating the vulnerability window associated with CRLs, OCSP significantly reduces the risk of a compromised device accessing sensitive corporate resources. This protects intellectual property and mitigates the financial and reputational damage of a data breach.
- Operational Efficiency: Automating revocation checks via OCSP reduces the administrative overhead associated with managing massive CRL files. IT teams can focus on strategic initiatives rather than troubleshooting CRL download failures.
- Compliance Enablement: For venues operating in regulated industries, such as Healthcare or finance, strict access controls and real-time revocation are often mandatory compliance requirements (e.g., HIPAA, PCI DSS). A robust OCSP deployment ensures continuous compliance and simplifies audit processes.
Key Terms & Definitions
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time.
Used by RADIUS servers to instantly verify if a device's certificate has been revoked, closing the vulnerability window associated with legacy CRLs.
CRL (Certificate Revocation List)
A periodically updated, digitally signed list of certificate serial numbers that have been revoked by the issuing Certificate Authority.
The legacy method for revocation checking. It suffers from scalability issues and introduces a vulnerability window between updates.
OCSP Stapling
A mechanism where the certificate presenter (e.g., a RADIUS server) obtains a time-stamped OCSP response from the CA and appends it to the certificate during the TLS handshake.
Used to improve performance and privacy by offloading the OCSP query burden from the client device.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A highly secure 802.1X authentication method that requires mutual certificate-based authentication between the client and the RADIUS server.
The standard protocol used in enterprise WiFi environments that necessitates robust certificate revocation checking.
Vulnerability Window
The period of time between a certificate being revoked at the CA and the enforcing system (e.g., RADIUS server) becoming aware of the revocation.
A primary driver for adopting OCSP over CRLs, as OCSP effectively reduces this window to near zero.
Fail Open vs. Fail Closed
A configuration decision determining the system's behaviour when a dependency (like an OCSP responder) is unreachable. 'Fail open' allows access; 'fail closed' denies access.
A critical architectural decision for IT teams balancing network availability against strict security compliance.
AIA (Authority Information Access)
An extension within an X.509 certificate that indicates how to access information and services for the issuer of the certificate, including the OCSP responder URI.
The RADIUS server reads this extension to determine exactly where to send the OCSP query for a specific client certificate.
Supplicant
The software client on a device (e.g., a laptop or smartphone) that attempts to access the network and responds to authentication requests.
The entity presenting the client certificate that the RADIUS server must validate against the OCSP responder.
Case Studies
A 500-room luxury hotel in the [Hospitality](/industries/hospitality) sector is upgrading its back-of-house WiFi network to use EAP-TLS for staff devices. They currently use a centralized RADIUS server in their corporate data centre, connected via SD-WAN. They are concerned that real-time OCSP queries to their cloud-based CA will cause authentication timeouts during shift changes when hundreds of staff connect simultaneously.
The implementation must prioritize low-latency authentication without compromising security. The solution involves three steps: 1) Deploy a localized RADIUS proxy at the hotel property to handle the initial EAP termination. 2) Configure the RADIUS proxy to perform OCSP queries and cache the 'Good' responses for 60 minutes. 3) Implement a fallback mechanism where the RADIUS proxy relies on a locally downloaded, daily CRL if the SD-WAN link to the cloud CA fails.
A large public-sector organisation is deploying [Sensors](/products/sensors) across multiple municipal buildings. These IoT devices authenticate via 802.1X using certificates with a 5-year lifespan. The IT security team requires immediate network disconnection if a sensor is reported stolen.
Given the long certificate lifespan, robust revocation is critical. The organisation must configure their RADIUS servers to perform mandatory OCSP queries for every authentication request from the sensor VLAN. Caching should be disabled or set to a very short duration (e.g., 5 minutes). The RADIUS servers must be configured to 'fail closed'—if the OCSP responder is unreachable, the sensor is denied access.
Scenario Analysis
Q1. Your organisation is migrating from a daily CRL download to real-time OCSP checking for your corporate WiFi. During the pilot phase, you notice a significant increase in authentication timeouts, particularly for users roaming between buildings. What is the most likely cause and the recommended mitigation?
💡 Hint:Consider the latency introduced by external network queries during the EAP-TLS handshake.
Show Recommended Approach
The timeouts are likely caused by the latency of performing an external HTTP query to the OCSP responder for every authentication event, including fast reconnects during roaming. The recommended mitigation is to configure OCSP caching on the RADIUS server. By caching 'Good' responses for a period (e.g., 30 minutes), subsequent roam events will be validated locally against the cache, eliminating the external query latency and preventing timeouts.
Q2. A critical security audit requires that no compromised device can access the network for more than 5 minutes after its certificate is revoked in the MDM platform. Your RADIUS server is configured to use OCSP with a 60-minute cache. Does this configuration meet the audit requirement?
💡 Hint:Analyze the relationship between the cache duration and the vulnerability window.
Show Recommended Approach
No, this configuration fails the audit requirement. The 60-minute cache creates a vulnerability window of up to one hour. If a device authenticates and its 'Good' status is cached, and the certificate is revoked 1 minute later, the RADIUS server will continue to permit access for the remaining 59 minutes based on the cached response. To meet the 5-minute requirement, the OCSP cache duration must be reduced to 5 minutes or less, though this will increase the query load on the CA infrastructure.
Q3. During a major ISP outage, your cloud-based OCSP responder becomes unreachable. Your RADIUS server is configured for OCSP checking with a 'fail closed' policy. What is the impact on the network, and how could the architecture be improved for resilience?
💡 Hint:Consider the implications of 'fail closed' when a critical dependency is unavailable.
Show Recommended Approach
The impact is a total outage for all new WiFi authentications. Because the RADIUS server cannot reach the responder and is configured to 'fail closed', it will deny all access requests. To improve resilience, the architecture should implement a fallback mechanism. The RADIUS server should be configured to attempt OCSP first, and if unreachable, fall back to a locally cached CRL. This allows authentications to proceed using the last known good revocation state during the ISP outage.
Key Takeaways
- ✓OCSP replaces bulky CRL downloads with real-time, targeted certificate status queries, eliminating the vulnerability window.
- ✓In 802.1X environments, the RADIUS server performs the OCSP query to validate the client's certificate before granting network access.
- ✓OCSP stapling allows the RADIUS server to prove its own validity to the client without requiring the client to query the CA.
- ✓Intelligent caching of 'Good' OCSP responses on the RADIUS server is critical to prevent authentication timeouts in high-density venues.
- ✓Implementing a CRL fallback mechanism ensures network resilience if the primary OCSP responder becomes unreachable.
- ✓A 'fail closed' configuration maximizes security but risks widespread outages, whereas 'fail open' prioritizes availability.
- ✓Robust certificate lifecycle management, including short certificate lifespans, reduces reliance on revocation mechanisms.



