SAML Authentication for Staff WiFi
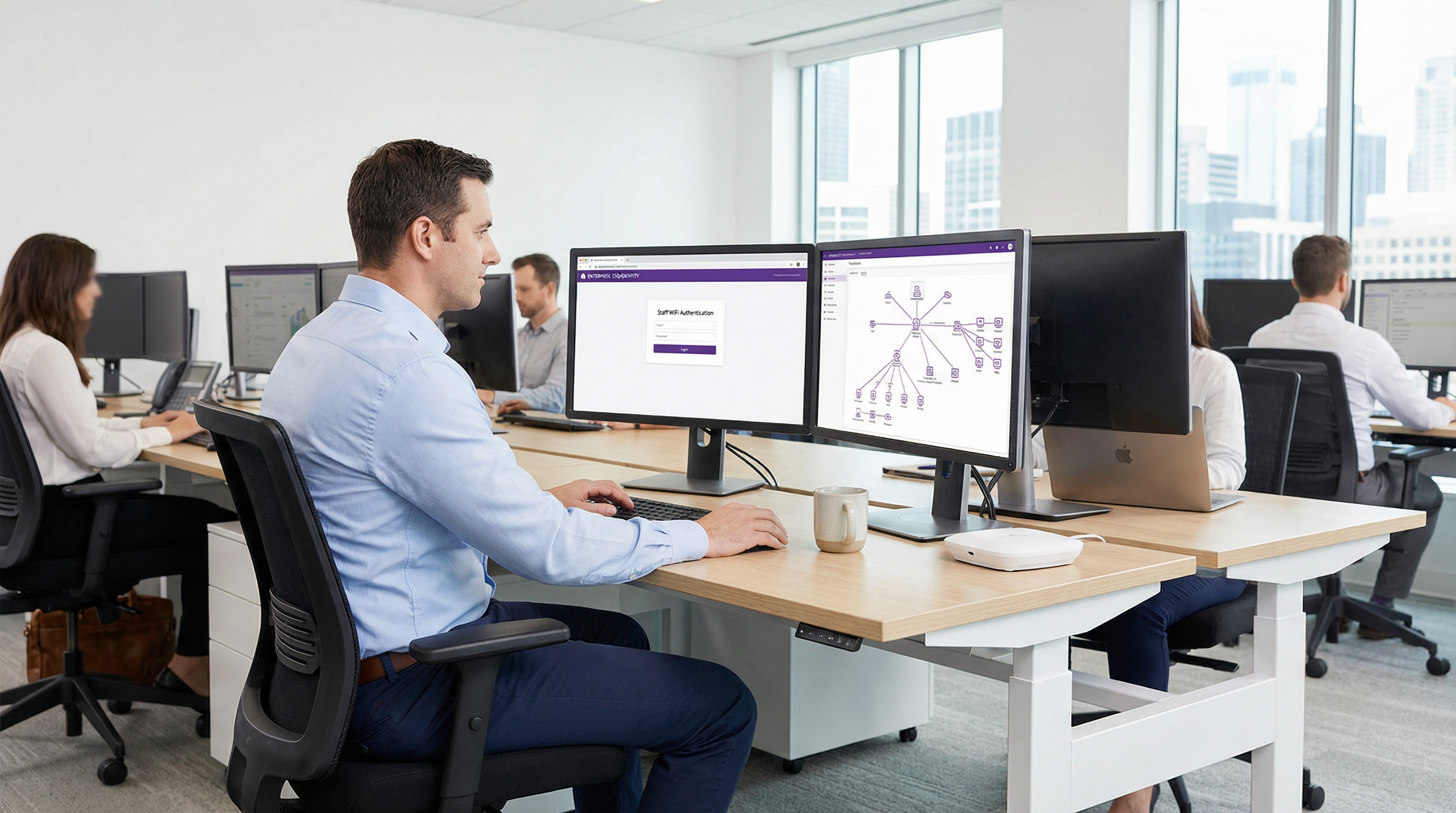
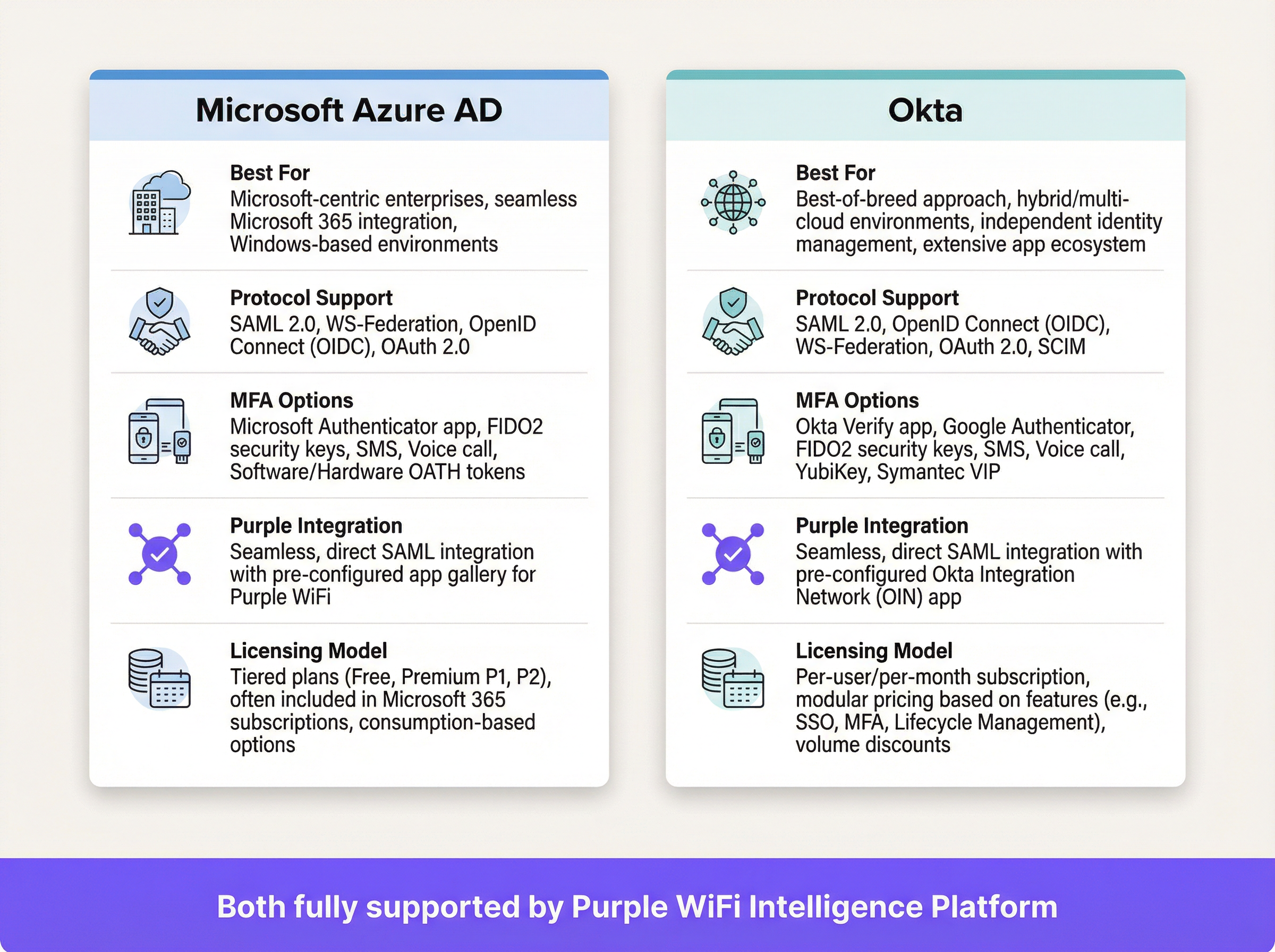
This guide provides a technical deep-dive into leveraging SAML 2.0 for enterprise-grade staff WiFi authentication, covering protocol architecture, Identity Provider integration, and deployment best practices. It equips IT leaders and network architects with actionable guidance on connecting Azure AD or Okta to the Purple WiFi intelligence platform to replace insecure pre-shared keys with robust, identity-driven access control. The result is a measurable improvement in security posture, compliance readiness, and operational efficiency across hotels, retail chains, stadiums, and public-sector venues.
🎧 Listen to this Guide
View Transcript
Executive Summary
For operators of large-scale venues — hotel chains, retail empires, major event spaces, and public-sector facilities — securing the staff wireless network is a critical component of risk mitigation and operational efficiency. Traditional pre-shared key (PSK) networks present significant security vulnerabilities and administrative overhead: a single compromised credential exposes the entire network, and access management requires manual intervention at every staff change. This guide details a superior approach: implementing Security Assertion Markup Language (SAML) 2.0-based authentication for staff WiFi. By integrating your existing Identity Provider (IdP) — such as Microsoft Azure Active Directory or Okta — with the Purple WiFi intelligence platform, you replace insecure shared passwords with robust, identity-driven access control. This deployment model elevates your security posture in line with PCI DSS and GDPR requirements, and dramatically simplifies user lifecycle management. Staff authenticate using their primary corporate credentials, enabling Single Sign-On (SSO) and ensuring that access rights are automatically revoked upon termination. For the CTO, this translates to a measurable reduction in IT support tickets, enhanced compliance, and a stronger, more defensible network architecture.
Technical Deep-Dive
SAML is an open standard for exchanging authentication and authorisation data between parties — specifically between an Identity Provider (IdP) and a Service Provider (SP). In this context, the IdP is your central user directory (Azure AD, Okta, Ping Identity, or ADFS), and the Purple platform acts as the SP, brokering access to the physical WiFi network.
The SAML 2.0 Authentication Flow
The process enables secure, browser-based authentication for WiFi users without requiring any client-side software installation. When a staff member connects to the designated staff SSID, their device is directed to a captive portal. Instead of a simple password field, this portal initiates a multi-step cryptographic handshake with the IdP to verify the user's identity.
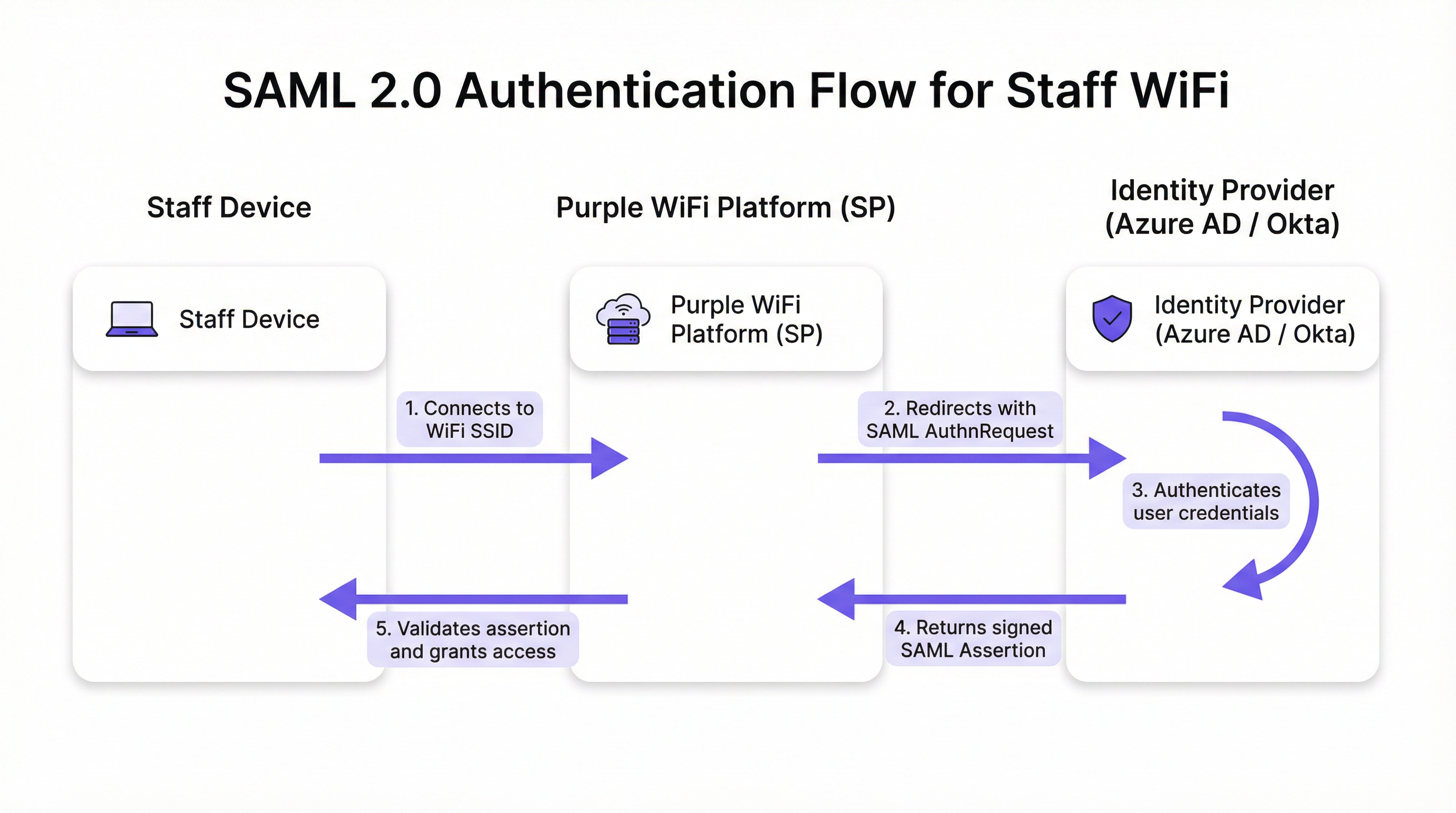
The flow proceeds in five discrete stages. First, the user connects their device — laptop, tablet, or mobile phone — to the staff WiFi SSID, and the Purple platform presents a captive portal. Second, Purple (acting as SP) generates a SAML authentication request (AuthnRequest), an XML document containing information about the SP and the desired authentication parameters. The user's browser is redirected to the IdP's SSO URL with this request embedded. Third, the user arrives at the IdP's familiar login page — their Microsoft 365 or Okta screen — and enters their corporate credentials. The IdP enforces its full range of security policies here, including Multi-Factor Authentication (MFA), device trust checks, and conditional access rules. Fourth, upon successful authentication, the IdP generates a SAML response containing a digitally signed assertion. This assertion is signed with the IdP's private key and contains key information about the authenticated user, including username, email, and group memberships. The user's browser is redirected back to Purple's Assertion Consumer Service (ACS) URL with this signed response. Fifth, Purple receives the SAML response, verifies the digital signature using the IdP's pre-configured public certificate, parses the assertion to confirm authorisation, and instructs the network controller to grant the device full network access.
Relevant Standards and Protocols
SAML 2.0 is the foundational protocol, defining the XML-based messages for assertions, protocols, bindings, and profiles. IEEE 802.1X provides a complementary port-based network access control standard; however, the captive portal SAML approach offers universal device compatibility without requiring complex supplicant configuration on every endpoint, making it ideal for BYOD environments. WPA3-Enterprise, when combined with SAML, provides defence-in-depth: WPA3 encrypts traffic over the air while SAML handles identity verification at the application layer. PCI DSS Requirement 8 mandates the identification and authentication of access to system components, a requirement directly addressed by this architecture.
Implementation Guide
Deploying SAML authentication for your staff WiFi involves establishing a cryptographic trust relationship between your IdP and the Purple platform. The following steps are vendor-neutral, though specific UI elements will vary by IdP.
Pre-Deployment Checklist
Before beginning configuration, confirm you have a SAML 2.0-compliant IdP (Azure AD, Okta, Ping Identity, ADFS). Ensure you hold administrative privileges in both your IdP portal and the Purple platform. Define your user groups — for example, 'All-Staff', 'IT-Admins', 'Store-Managers' — as these drive role-based access policies. Verify that your WiFi hardware (access points and controllers) supports captive portal redirection.
Step 1 — Configure the Application in Your IdP
In your IdP, create a new SAML-based application for Purple. Navigate to 'Enterprise Applications' in Azure AD or 'Applications' in Okta and select a custom SAML app. You will need to provide your IdP with two values from the Purple platform: the Assertion Consumer Service (ACS) URL and the Entity ID. Purple provides these in its authentication setup section. Your IdP will, in return, generate its own metadata — typically an XML file or URL — containing the IdP's SSO URL, Entity ID, and X.509 signing certificate. Retain this for the next step.
Step 2 — Configure Claims
This is the most operationally significant configuration step. You must configure the IdP to send specific user attributes in the SAML assertion. Purple requires a unique, persistent identifier for each user as the NameID claim. Best practice is to use an immutable attribute such as user.objectid in Azure AD or user.id in Okta, rather than a mutable email address. Additionally, configure group claims to pass the user's group memberships. This enables dynamic, role-based access policies within Purple without per-user configuration.
Step 3 — Configure the Authentication Method in Purple
In the Purple portal, navigate to the authentication management section and select SAML 2.0 as the method type. Input the IdP's SSO URL, Entity ID, and X.509 certificate obtained in Step 1. Map the attribute names from your IdP's claims configuration to the corresponding fields in Purple. Finally, assign this authentication method to your staff captive portal journey to activate the flow for users connecting to the staff SSID.
Step 4 — Testing and Phased Rollout
Assign the new SAML application to a small pilot group — ideally the IT team — and validate the end-to-end flow on multiple device types (Windows, macOS, iOS, Android). Monitor the SAML sign-in logs in your IdP and the authentication logs in Purple to diagnose any failures. Once validated, gradually expand the user assignment in your IdP to cover all relevant staff groups. Communicate the change to staff clearly, emphasising that they will now use their standard corporate login credentials.
Best Practices
Enforce MFA for all WiFi authentications. This is the single most effective control against credential theft and should be considered non-negotiable for any enterprise deployment. Leverage your IdP's conditional access capabilities to restrict network access based on device compliance status, geographic location, or risk score. Configure short session timeouts within Purple to force periodic re-authentication, ensuring access rights are regularly re-validated against the IdP and mitigating risk from lost or stolen devices. Adhere to the principle of attribute minimisation: only include the attributes necessary for access decisions in the SAML assertion, in compliance with GDPR Article 5's data minimisation principle. For corporate-managed devices, consider combining the SAML captive portal with WPA3-Enterprise and 802.1X for defence-in-depth; the SAML approach is best suited to BYOD or unmanaged endpoints.

Troubleshooting & Risk Mitigation
The most common and impactful failure mode is certificate expiry. The IdP's X.509 signing certificate has a fixed validity period, typically one to three years. When it expires, Purple can no longer validate SAML assertions, causing a complete authentication outage. Mitigation: set redundant calendar reminders at 90, 60, and 30 days before expiry and document the renewal procedure explicitly.
Clock skew is the second most frequent cause of authentication failures. SAML assertions contain a validity window, and if the clocks on the IdP and the Purple platform diverge by more than a few minutes, assertions will be rejected as expired or not-yet-valid. Ensure both systems synchronise to a reliable NTP source.
An incorrect ACS URL during initial setup is a common configuration error. A single character typo means the IdP sends the signed assertion to a non-existent endpoint. Always copy-paste the ACS URL directly from the Purple platform rather than typing it manually.
Finally, disable IdP-initiated login for this application. Network access should only ever be initiated from the SP (the WiFi connection event). Permitting IdP-initiated flows opens the door to certain SAML-based injection attacks and is an unnecessary security risk in this deployment model.
ROI & Business Impact
The business case for SAML-based staff WiFi authentication is compelling across all venue types. The elimination of shared passwords removes the need for periodic, disruptive password rotations and the associated helpdesk tickets. Organisations typically report a reduction of over 50% in WiFi-related IT support requests following deployment. User lifecycle automation is the most significant operational gain: when a staff member is offboarded and their IdP account is disabled, their WiFi access is revoked instantly and automatically, closing a security gap that PSK-based networks leave open indefinitely. From a compliance perspective, SAML provides an auditable, individual-level access log, directly supporting PCI DSS Requirement 8 and GDPR accountability obligations. The seamless SSO experience — one set of credentials for email, applications, and WiFi — reduces friction for staff and increases productivity, particularly for operational teams who move between areas of a venue throughout the day.
References
[1] OASIS Security Services (SAML) TC. "SAML V2.0 Executive Overview." April 2008. https://www.oasis-open.org/committees/download.php/27819/sstc-saml-exec-overview-2.0-cd-01.pdf
[2] General Data Protection Regulation (GDPR). Article 5, Principles relating to processing of personal data. https://gdpr-info.eu/art-5-gdpr/
[3] PCI Security Standards Council. "PCI DSS v4.0 Requirement 8: Identify Users and Authenticate Access to System Components." 2022. https://www.pcisecuritystandards.org/
Key Terms & Definitions
SAML Assertion
An XML document, digitally signed by the Identity Provider, that declares who a user is and provides additional attributes about them. It is the cryptographic 'digital passport' that the Service Provider trusts to make an access decision.
When troubleshooting authentication failures, IT teams inspect the SAML assertion to verify that the IdP is sending the correct user attributes and that the digital signature is valid. It is the core piece of evidence in every authentication transaction.
Identity Provider (IdP)
The system that manages user identities and authenticates them. It is the authoritative source of truth for user identity within an organisation.
In a corporate environment, this is the central user directory — Azure AD, Okta, Ping Identity, or ADFS. It is where IT teams add, remove, and manage all staff accounts and enforce security policies like MFA.
Service Provider (SP)
The application or service that requires authentication before granting access. It trusts the Identity Provider to perform the authentication and relies on the SAML assertion as proof.
For SAML WiFi authentication, the Purple platform is the Service Provider. It consumes the SAML assertion from the IdP to make a network access control decision for the connecting device.
Assertion Consumer Service (ACS) URL
A specific endpoint on the Service Provider designed to receive and process SAML assertions from the Identity Provider after a successful authentication event.
This is one of the most critical configuration parameters. If the ACS URL is incorrectly entered in the IdP settings, the IdP will not know where to send the user after login, and authentication will fail with a redirect error.
Entity ID
A globally unique identifier for an Identity Provider or Service Provider within the SAML protocol. It acts as a unique name to ensure each party is communicating with the correct counterpart.
Typically formatted as a URL, the Entity ID does not need to resolve to a real webpage. It functions like a unique identifier in a directory, preventing one SP from accidentally consuming assertions intended for another.
SAML Metadata
An XML document containing all necessary configuration information about a SAML party — including its Entity ID, endpoint URLs (such as the ACS URL), and public X.509 signing certificate.
Exchanging metadata files is the most reliable method for configuring a SAML trust relationship. Rather than manually copying individual values, administrators can upload the metadata XML from the other party to auto-populate the configuration, reducing the risk of transcription errors.
Claim
A piece of information about a user — an attribute — that is included in the SAML assertion by the Identity Provider. Common claims include username, email address, department, and group memberships.
IT teams configure claims in the IdP to control what information the SP receives. Sending group membership claims to Purple enables role-based access policies and dynamic VLAN assignment based on a user's job function.
Single Sign-On (SSO)
An authentication scheme that allows a user to authenticate once with a single set of credentials and gain access to multiple independent systems and applications without re-entering credentials for each.
SAML is a primary technical enabler of SSO. By using SAML for WiFi authentication, staff use the same corporate login they use for email, HR systems, and other applications to get online — a seamless experience that reduces friction and eliminates the need for separate WiFi passwords.
X.509 Certificate
A digital certificate standard used to verify the identity of a party and to sign or encrypt data. In SAML, the IdP uses its private key to sign assertions, and the SP uses the IdP's X.509 public certificate to verify those signatures.
This certificate is the foundation of trust in a SAML deployment. Its expiration is the single most common cause of complete authentication outages and must be proactively managed.
Case Studies
A global hotel chain with 300 properties needs to replace its insecure, single PSK for staff WiFi. The chain uses Microsoft 365 and Azure AD as its corporate identity platform. They need a solution that can be centrally managed, provides a seamless experience for staff, and revokes access immediately when an employee leaves the organisation.
The IT team creates a new Enterprise Application in Azure AD for the Purple platform. They configure the application with the Entity ID and ACS URL from their Purple instance. Critically, they configure the claims to send the user's group membership — for example, 'Hotel-Staff' and 'IT-Admin' — and use user.objectid as the unique NameID to ensure a stable, immutable identifier. In Purple, they create a new SAML authentication method, uploading the Azure AD metadata XML to establish the trust relationship. They then create two access policies: one for 'Hotel-Staff' that grants access to the general staff network VLAN, and a second for 'IT-Admin' that grants privileged access to the management VLAN. This configuration is tied to a single 'Staff' SSID broadcast across all 300 properties via the chain's centralised network management platform. A new staff member at any hotel is automatically granted the correct level of WiFi access as soon as their user account is added to the relevant group in Azure AD — no local IT intervention required. When a staff member leaves, disabling their Azure AD account immediately revokes their WiFi access at all 300 properties simultaneously.
A large conference centre hosts multiple third-party events simultaneously. They need to provide secure WiFi for event staff from different organisations, each with their own identity systems. They cannot issue credentials to external staff and must ensure that staff from one event cannot access the network resources of another.
The conference centre's IT team uses Purple's support for multiple SAML Identity Providers. For each major event organiser, they configure a separate SAML trust relationship within the Purple platform. Organiser A (using Okta) and Organiser B (using Google Workspace) are set up as distinct IdPs. The captive portal is configured to present an organisation selection step, directing users to their respective IdP for authentication. Using group claims passed by each IdP, Purple maps users to event-specific VLANs, ensuring complete network traffic segregation between events. Access for each organiser's staff automatically expires at the end of the event based on pre-set journey rules configured in Purple, requiring no manual deprovisioning.
Scenario Analysis
Q1. Your CFO has reported that a former employee's personal device was found still connected to the staff WiFi network two weeks after their departure. Your current system uses a single WPA2-PSK that is rotated quarterly. How would a SAML-based approach mitigate this specific risk, and what additional controls would you recommend?
💡 Hint:Consider the user lifecycle, the source of authentication authority, and the role of session timeouts.
Show Recommended Approach
A SAML-based approach directly links WiFi access to the employee's active status in the central Identity Provider. The moment the employee's account is disabled or deleted as part of the standard offboarding process, their ability to authenticate to any SAML-integrated service — including the WiFi — is instantly and automatically revoked. The IdP will no longer issue a valid SAML assertion for that user, meaning they cannot re-authenticate. To address the specific scenario of a device that is already connected, configure short session timeouts in Purple (e.g., 8-hour sessions aligned with a working day). When the session expires, the device must re-authenticate; the disabled IdP account will prevent this. This eliminates the security gap inherent in long-lived shared secrets like a PSK, where a device that has already connected remains online indefinitely.
Q2. A stadium is implementing SAML authentication for its 500 event-day staff. They want to ensure that cashiers using point-of-sale terminals can only access the PCI-compliant network segment, while operations staff can access the general corporate network. How would you design the SAML claims configuration and network policy to achieve this segmentation?
💡 Hint:Think about how to pass role information from the IdP to the network infrastructure via the SAML assertion, and how Purple can act on that information.
Show Recommended Approach
The solution is to use group claims and dynamic VLAN assignment. In the IdP (Azure AD or Okta), create two security groups: 'POS-Staff' and 'Ops-Staff'. Configure the SAML application to include the user's group membership as a claim in the assertion. In the Purple platform, create two user access profiles that map to these group names. Configure the 'POS-Staff' profile to assign users to the PCI-compliant VLAN (e.g., VLAN 10) and the 'Ops-Staff' profile to assign users to the corporate VLAN (e.g., VLAN 20). When a user authenticates, Purple reads the group claim from the SAML assertion and instructs the network controller — via RADIUS attributes or API — to place the user's device in the appropriate VLAN. Network traffic is then segregated at the infrastructure level, ensuring POS terminals can only reach the payment processing network, regardless of where they connect in the stadium.
Q3. You are planning a rollout of SAML WiFi authentication to a retail chain with 1,000 stores. The store managers are not technically proficient. What is the single most important operational risk to proactively manage, and what is your communication and contingency plan?
💡 Hint:What is the one component in the SAML trust relationship that has a fixed expiry date and whose failure would cause a simultaneous outage across all 1,000 stores?
Show Recommended Approach
The single most critical operational risk is the expiration of the IdP's SAML signing certificate. If it expires, all 1,000 stores will lose staff WiFi access simultaneously, as Purple will be unable to validate any SAML assertions. The mitigation plan has two components. Technically: set multiple, redundant calendar reminders for the certificate's expiry date for the entire IT team, starting 90 days out. Document the step-by-step procedure for generating a new certificate in the IdP and updating it in the Purple platform. Ensure at least two team members are trained on this procedure. Aim to complete the renewal at least 30 days before expiry to allow for testing. For communication: proactively inform the retail operations director about the planned maintenance window for the certificate renewal. There is no need to inform individual store managers for a planned renewal, as the goal is a zero-downtime cutover. In the event of an unplanned outage, the communication plan should be to immediately notify the operations director of the issue and provide a realistic ETA for resolution. A temporary fallback — such as a time-limited PSK for critical operations — should be documented in the business continuity plan.
Key Takeaways
- ✓Replace insecure staff WiFi pre-shared keys with robust, identity-driven SAML 2.0 authentication to eliminate shared credential vulnerabilities.
- ✓Integrate your existing Identity Provider — Azure AD or Okta — with Purple to leverage a single source of truth for user identity across all applications and network access.
- ✓Automate user onboarding and offboarding: WiFi access is granted and revoked automatically as part of your existing IdP user lifecycle management processes.
- ✓Enforce Multi-Factor Authentication and conditional access policies at the IdP level to protect network entry against credential theft and compromised devices.
- ✓Use group claims within the SAML assertion to enable dynamic, role-based network access and VLAN segmentation without per-user configuration in Purple.
- ✓Achieve compliance with PCI DSS Requirement 8 and GDPR accountability obligations through auditable, individual-level access logs tied to verified corporate identities.
- ✓Proactively manage the IdP signing certificate expiry — the number one cause of SAML authentication outages — with redundant reminders and a documented renewal procedure.



