The Ultimate Guide to OpenRoaming Architecture and Authentication
This guide provides an authoritative technical reference on WBA OpenRoaming architecture, covering the Passpoint foundation, RADIUS federation, RadSec mTLS security, and step-by-step deployment guidance for enterprise venues. It equips IT managers, network architects, and venue operators with the knowledge to replace captive portals with seamless, secure, and compliant Wi-Fi connectivity that delivers measurable ROI.
🎧 Listen to this Guide
View Transcript

Executive Summary
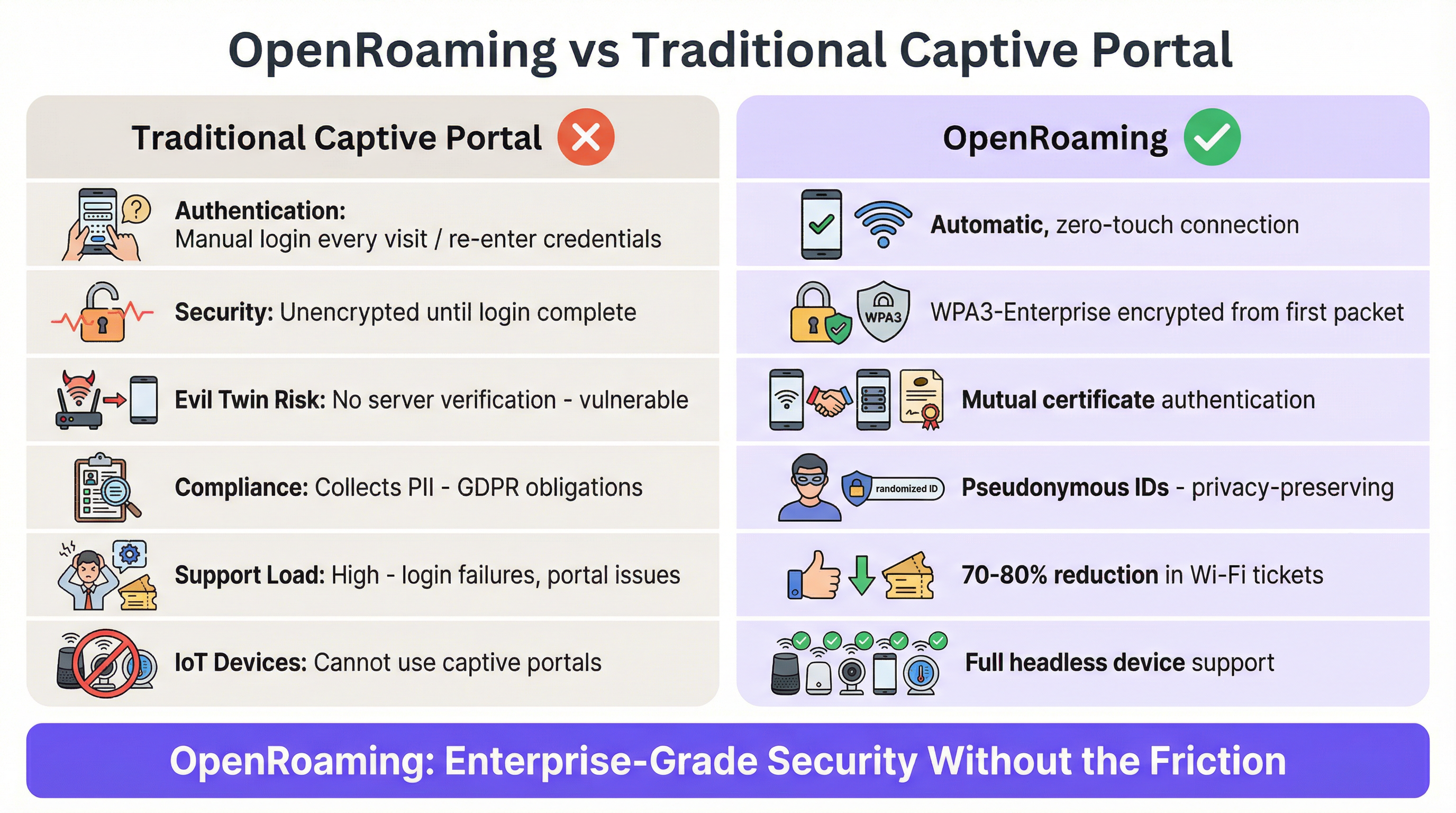
The traditional captive portal model for guest Wi-Fi is broken. For decades, venues have relied on manual login screens that frustrate users, offer poor security, and generate significant support overhead. WBA OpenRoaming represents a fundamental architectural shift, replacing manual authentication with a global federation of secure, automatic connections built on Passpoint (Hotspot 2.0) technology and 802.1X Authentication: Securing Network Access on Modern Devices.
For IT managers and network architects, deploying OpenRoaming is no longer just about improving user experience — it is a strategic imperative to enhance network security, reduce support tickets, and drive measurable ROI through higher network utilisation. This guide provides a comprehensive technical reference for implementing OpenRoaming architecture, navigating the RADIUS federation, and ensuring compliance with modern security standards across enterprise, Retail, and Hospitality environments.
Technical Deep-Dive: The OpenRoaming Architecture
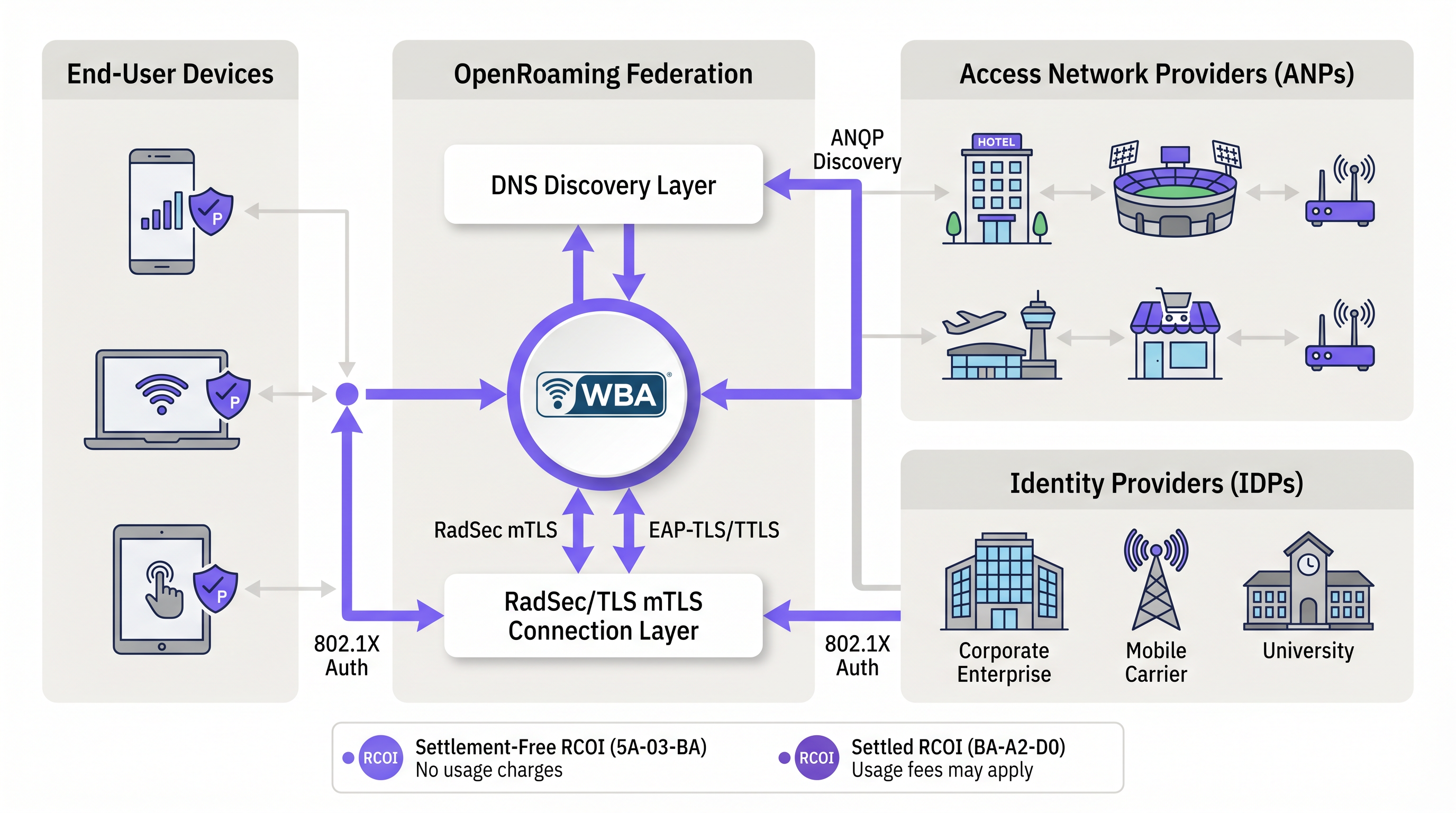
The OpenRoaming architecture operates through a trust federation managed by the Wireless Broadband Alliance (WBA). It bridges the gap between Identity Providers (IDPs) who issue credentials and Access Network Providers (ANPs) who operate the Wi-Fi infrastructure.
The Passpoint Foundation
At the core of OpenRoaming is the Wi-Fi Alliance Passpoint standard (based on IEEE 802.11u). Passpoint enables devices to discover and authenticate to Wi-Fi networks automatically. When a device enters an OpenRoaming-enabled venue, it uses the Access Network Query Protocol (ANQP) to query the access point for supported Roaming Consortium Organization Identifiers (RCOIs) before associating. This pre-association discovery is entirely invisible to the user — the device silently determines whether it holds valid credentials for the network before initiating any connection attempt.
The RADIUS Federation and RadSec
Traditional carrier Wi-Fi roaming relies on static RADIUS routing tables populated through bilateral agreements, secured via IPSec tunnels. This model does not scale to a global, open federation. OpenRoaming solves this by utilising dynamic DNS-based peer discovery (RFC 7585) and RadSec (RADIUS over TLS, RFC 6614).
When an access point receives an authentication request, the local RADIUS proxy performs a DNS NAPTR lookup on the user's realm to dynamically discover the IDP's RadSec server. The signalling is secured using mutual TLS (mTLS) with certificates issued by the WBA's four-level Public Key Infrastructure (PKI), ensuring end-to-end security between the Access Network and the Identity Provider without requiring pre-established bilateral agreements.
Roaming Consortium Organization Identifiers (RCOIs)
OpenRoaming uses specific RCOIs to broadcast policy controls and settlement models. These are advertised in the 802.11 beacon and via ANQP:
| RCOI Value | Model | Description |
|---|---|---|
| 5A-03-BA | Settlement-Free | ANP provides connectivity at no cost to the IDP. Dominant model for enterprise, retail, and hospitality. |
| BA-A2-D0 | Settled | ANP expects financial compensation. Used for premium connectivity scenarios. |
The 12 most significant bits of the RCOI can also be used to define Closed Access Group (CAG) policies, enabling ANPs and IDPs to negotiate Quality of Service tiers, identity proofing levels, and privacy requirements at a granular level.
Implementation Guide
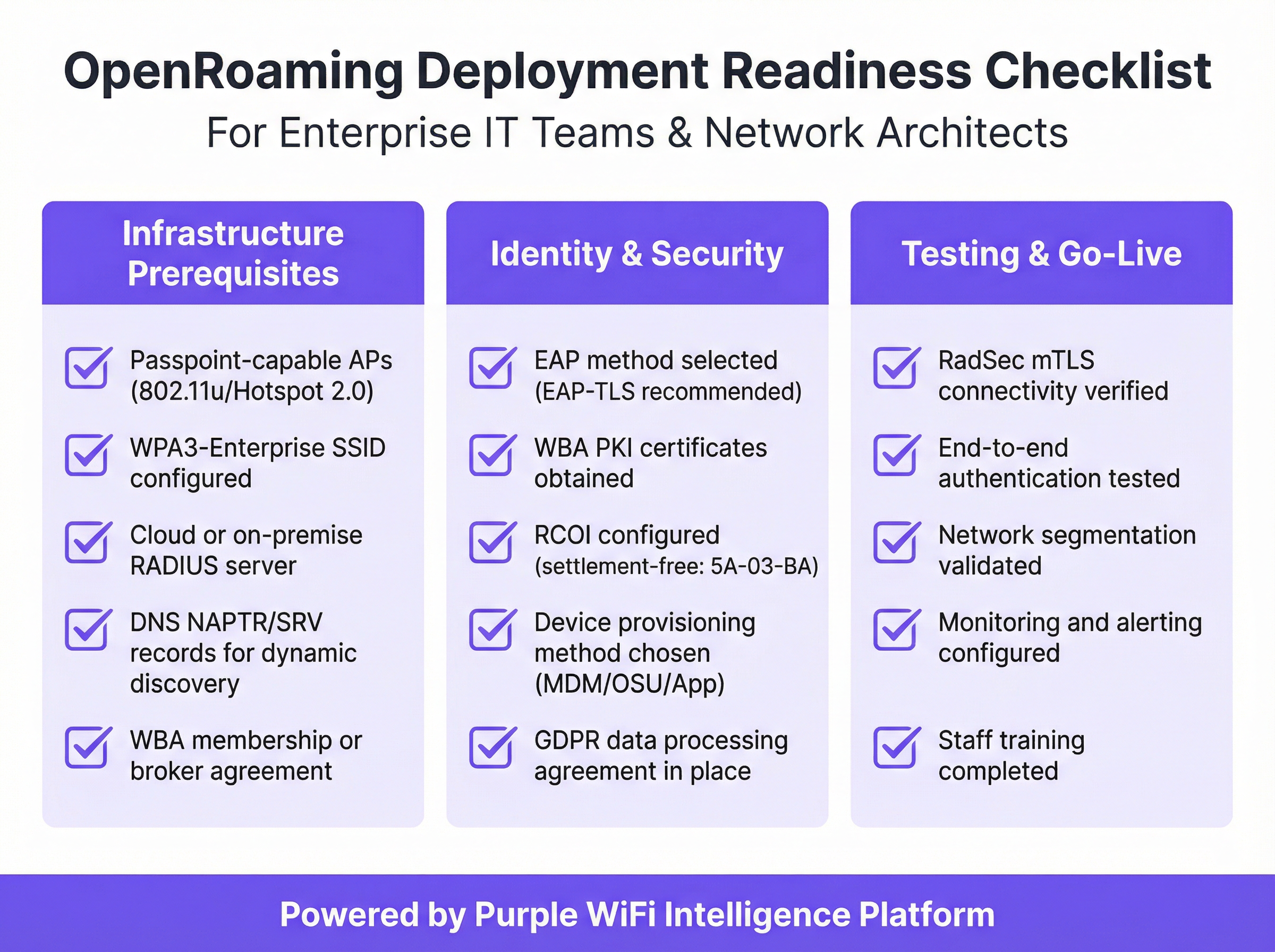
Deploying OpenRoaming requires coordination across network hardware, RADIUS infrastructure, and identity management. For a comprehensive overview of hardware requirements, see our guide on Wireless Access Points Definition Your Ultimate 2026 Guide.
Step 1: Infrastructure Readiness Assessment
Verify that your access points and wireless LAN controllers support Passpoint/Hotspot 2.0 (IEEE 802.11u). Most enterprise-grade equipment manufactured after 2018 includes native support. Configure a dedicated SSID secured with WPA3-Enterprise (or WPA2-Enterprise for legacy device compatibility). This SSID will carry OpenRoaming traffic and must be configured with the appropriate ANQP settings to broadcast your RCOI.
Step 2: WBA Membership and Broker Engagement
To participate in the OpenRoaming federation, your organisation must either join the WBA directly or engage an authorised WBA broker. The broker will assign your organisation a WBA Identity (WBAID), issue your RadSec certificates under the WBA PKI, and configure your DNS NAPTR/SRV records to enable dynamic discovery. This is the foundational step that connects your infrastructure to the global federation.
Step 3: RADIUS Infrastructure Configuration
Your RADIUS server must be configured to route authentication requests to the OpenRoaming federation. This involves configuring RadSec to establish mTLS connections using your WBA-issued certificates. The RADIUS proxy must be capable of performing DNS NAPTR lookups to dynamically resolve IDP endpoints. Cloud-based RADIUS solutions can significantly simplify this step by abstracting the complex DNS discovery and certificate management processes.
Step 4: Device Provisioning Strategy
Getting Passpoint profiles onto user devices is the primary operational consideration. Four approaches are available:
| Method | Best For | Mechanism |
|---|---|---|
| MDM Push | Managed corporate devices | Intune, Jamf, or Workspace ONE push profiles automatically |
| Online Sign-Up (OSU) | Consumer-facing deployments | Standardised self-enrolment via the Passpoint OSU protocol |
| App-Based Provisioning | Loyalty programme members | Mobile app installs Passpoint profile post-authentication |
| QR Code Enrolment | Hospitality check-in | Physical QR code triggers profile installation |
Step 5: Policy Configuration and VLAN Segmentation
Configure your WLAN controller to broadcast the appropriate OpenRoaming RCOIs via ANQP. Implement dynamic VLAN assignment via RADIUS attributes to ensure guest traffic is isolated from corporate networks. This is non-negotiable for PCI DSS compliance in Retail environments and best practice across all verticals.
Best Practices for Security and Compliance
OpenRoaming fundamentally improves the security posture of venue Wi-Fi, moving from open, unencrypted networks to robust enterprise-grade security. For a deeper dive into the underlying authentication mechanisms, review 802.1X Authentication: Securing Network Access on Modern Devices.
WPA3-Enterprise and 802.1X Authentication
Unlike captive portals where traffic is unencrypted until login, OpenRoaming utilises WPA3-Enterprise encryption from the very first packet. The 802.1X mutual authentication process ensures that the user's device cryptographically verifies the network's identity before transmitting any credentials, eliminating the risk of "Evil Twin" rogue access points — a vulnerability that traditional captive portals cannot address.
Privacy and GDPR Compliance
Traditional captive portals often collect extensive Personally Identifiable Information (PII), creating significant GDPR compliance burdens. OpenRoaming authenticates users via pseudonymous identifiers such as the Chargeable-User-Identity (CUI) attribute. The venue verifies that the user is legitimate without necessarily ingesting their raw PII, aligning with GDPR data minimisation principles and reducing the scope of your data processing obligations.
Network Segmentation and PCI DSS
For Retail environments, PCI DSS compliance is critical. OpenRoaming traffic must be strictly segmented from Point of Sale (POS) systems and corporate networks. Utilise dynamic VLAN assignment via RADIUS attributes to isolate guest traffic immediately upon authentication, placing it in a VRF instance with only a default internet route and explicit deny rules for all internal RFC 1918 address space.
Case Studies: OpenRoaming in Production
Case Study 1: RAI Amsterdam Convention Centre (Events & Conferencing)
The RAI Amsterdam Convention Centre, one of Europe's largest event venues hosting 1.5 million guests annually, deployed Wi-Fi 6 with WBA OpenRoaming in 2023. At Cisco Live Europe, over 18,000 attendees had access to seamless OpenRoaming connectivity, consuming more than 77 terabytes of data over four days. Attendees spent an average of six hours on the network. The deployment demonstrated how OpenRoaming eliminates the connection surge that typically occurs when event gates open, distributing authentication load evenly across the federation. For Transport hubs and conference centres, this case study is the definitive proof of concept.
Case Study 2: Delhaize Retail Chain (Retail)
Belgian retail group Delhaize deployed OpenRoaming across its store network to improve customer connectivity and streamline operations. The deployment resolved persistent issues with captive portal conversion rates — a challenge facing all Retail operators as customers increasingly default to mobile data rather than engaging with manual login screens. By enabling automatic, secure connectivity for loyalty app users, Delhaize increased Wi-Fi adoption and improved the quality of in-store analytics data, directly supporting merchandising and space utilisation decisions. This aligns with the broader trend of integrating WiFi Analytics with retail intelligence platforms.
Troubleshooting & Risk Mitigation
While OpenRoaming simplifies the end-user experience, the underlying infrastructure is complex. Network architects must proactively mitigate common failure modes:
RadSec Certificate Expiry is the most critical operational risk. The mTLS connections rely on WBA PKI certificates. A lapsed certificate will immediately break federation routing, causing silent authentication failures. Implement monitoring with at least 60 days' advance warning and a defined renewal process.
DNS Resolution Failures are the second most common cause of OpenRoaming outages. Dynamic peer discovery depends on reliable DNS resolution of NAPTR and SRV records. Ensure your RADIUS proxies have redundant, high-performance DNS forwarders configured and test DNS resolution as part of your regular network health checks.
Legacy Device Compatibility must be planned for during transition. While modern iOS, Android, Windows, and macOS devices natively support Passpoint, older devices do not. Maintain a parallel traditional Guest WiFi network during the transition period to ensure universal coverage.
RADIUS Proxy Misconfiguration can cause realm-based routing failures. Ensure your proxy correctly handles the EAP-Identity realm and that your DNS NAPTR records are correctly formatted for RFC 7585 discovery. Test with multiple IDP realms before go-live.
ROI & Business Impact
The business case for OpenRoaming extends far beyond technical elegance. Venue operators can expect measurable returns across several vectors:
| Metric | Typical Outcome | Source |
|---|---|---|
| Wi-Fi support ticket reduction | 70–80% decrease | WBA deployment reports |
| Wi-Fi adoption rate increase | 40–50% increase | WBA airport deployment data |
| Data consumption per user | Significantly higher vs. captive portal | RAI Amsterdam case study |
| PII compliance risk | Substantially reduced | GDPR pseudonymous ID model |
By adopting OpenRoaming, venues provide the Modern Hospitality WiFi Solutions Your Guests Deserve, transitioning Wi-Fi from a frustrating utility into a seamless, invisible enabler of the digital experience. The integration with WiFi Analytics platforms becomes more valuable as higher attach rates produce richer, more representative data sets. For organisations exploring the broader network modernisation picture, the The Core SD WAN Benefits for Modern Businesses provides complementary context on how OpenRoaming fits within a modern, software-defined network architecture.
The Healthcare sector also stands to benefit significantly, with OpenRoaming enabling secure, automatic connectivity for visiting clinicians and medical IoT devices — without the compliance risks of open guest networks or the operational overhead of per-device captive portal management.
Key Terms & Definitions
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance certification programme based on IEEE 802.11u that enables devices to automatically discover and authenticate to Wi-Fi networks without user intervention, using pre-provisioned credentials.
The foundational technology that makes the seamless OpenRoaming experience possible on the end-user device. Without Passpoint support on both the AP and the device, OpenRoaming cannot function.
RadSec
A protocol (RFC 6614) that transports RADIUS packets over a TCP and TLS connection, providing encrypted, reliable, and authenticated delivery of authentication signalling.
Used to secure authentication traffic traversing the public internet between the venue's RADIUS proxy and the global OpenRoaming federation. Replaces the legacy IPSec tunnel model.
RCOI (Roaming Consortium Organization Identifier)
A 3-octet or 5-octet identifier broadcast by access points in 802.11 beacons and ANQP responses to indicate which roaming federations and settlement policies the network supports.
Devices read the RCOI to determine if they hold valid credentials to connect before attempting authentication. The settlement-free RCOI (5A-03-BA) is the standard for enterprise deployments.
ANQP (Access Network Query Protocol)
An IEEE 802.11 protocol used by devices to query access points for network information — including supported RCOIs, venue name, and NAI realm list — prior to association.
Enables devices to silently evaluate whether a network supports their credentials without disrupting the user or initiating a connection attempt.
Identity Provider (IDP)
An organisation that maintains user identities and issues the Passpoint credentials (certificates or profiles) used for OpenRoaming authentication.
Mobile carriers, corporate IT departments, and loyalty programmes act as IDPs. The IDP authenticates the user and signals the result to the ANP via the RADIUS federation.
Access Network Provider (ANP)
The venue or organisation that operates the physical Wi-Fi infrastructure, broadcasts OpenRoaming RCOIs, and enforces local access policies.
Hotels, stadiums, retail stores, and enterprise offices act as ANPs. The ANP controls what authenticated users can access, regardless of which IDP authenticated them.
WBA PKI
The four-level Public Key Infrastructure managed by the Wireless Broadband Alliance, used to issue the mTLS certificates required for RadSec connections between federation participants.
Provides the foundational cryptographic trust that allows thousands of independent networks to securely federate without pre-established bilateral agreements.
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism for devices wishing to attach to a LAN or WLAN, using EAP (Extensible Authentication Protocol) methods.
The robust security framework underpinning OpenRoaming. It prevents unauthorised access and enables WPA3-Enterprise encryption from the first data packet.
Chargeable-User-Identity (CUI)
A RADIUS attribute (RFC 4372) that provides a pseudonymous, stable identifier for a user across multiple sessions, without exposing their actual identity to the access network.
Enables venues to track unique visitors for analytics purposes while minimising PII collection, directly supporting GDPR data minimisation compliance.
Case Studies
A 500-room luxury hotel currently uses a captive portal requiring guests to log in with their room number and last name. They are experiencing high support volumes and poor guest satisfaction scores regarding Wi-Fi. They want to implement OpenRoaming but are concerned about losing the ability to tier bandwidth for VIP guests and loyalty programme members.
The hotel should deploy OpenRoaming using the settlement-free RCOI (5A-03-BA), with the hotel's loyalty app acting as an Identity Provider. When a VIP loyalty member authenticates, the IDP's RADIUS Access-Accept response includes Vendor-Specific Attributes (VSAs) that instruct the hotel's WLAN controller to assign the user to a premium QoS profile and a dedicated high-bandwidth VLAN. Standard guests authenticated via a third-party IDP (e.g., their mobile carrier) receive the default QoS profile. The hotel's RADIUS server acts as the policy enforcement point, translating IDP-supplied identity attributes into local network policies.
A large retail chain with 200 stores wants to deploy OpenRoaming to improve customer connectivity and feed their WiFi Analytics platform with richer footfall data. Their security team is concerned about PCI DSS compliance and the risk of guest devices accessing the corporate network or point-of-sale systems.
The retail chain must implement strict network segmentation as a prerequisite to deployment. The OpenRoaming SSID must be mapped to an isolated guest VLAN at the access layer (the AP or distribution switch). The RADIUS server should enforce dynamic VLAN assignment, ensuring all OpenRoaming-authenticated users are placed into a VRF instance with only a default route to the internet and explicit ACL deny rules for all RFC 1918 internal address space. The OpenRoaming RADIUS proxy should be deployed in a DMZ, with no direct routing path to the corporate network. A quarterly penetration test should verify that the segmentation boundary holds.
Scenario Analysis
Q1. Your venue is experiencing frequent silent authentication failures for a subset of OpenRoaming users. Packet captures confirm the EAP-Identity response is received by the AP, but no RADIUS Access-Request ever reaches the Identity Provider. What is the most likely architectural failure point, and how would you diagnose it?
💡 Hint:Consider the steps required for the RADIUS proxy to locate the correct destination for the specific user's realm before it can forward the authentication request.
Show Recommended Approach
The most likely failure point is DNS resolution at the RADIUS proxy. OpenRoaming relies on dynamic discovery (RFC 7585), requiring the proxy to perform a DNS NAPTR/SRV lookup on the realm provided in the EAP-Identity. If DNS fails, the proxy cannot determine the IP address of the IDP's RadSec server, resulting in a silent failure. Diagnose by running a manual NAPTR lookup from the RADIUS proxy for the affected realm, verifying that the correct SRV records are returned and that the RadSec server IP is reachable on port 2083.
Q2. A hospital IT director wants to deploy OpenRoaming to improve connectivity for visiting clinicians and medical IoT devices, but mandates that all guest traffic must be encrypted over the air from the moment of connection to comply with internal security policy. They currently use a captive portal with WPA2-Personal (PSK). Does OpenRoaming satisfy this requirement, and how does the encryption model differ?
💡 Hint:Compare the encryption timing of captive portals versus 802.1X-based authentication, and consider what happens to traffic before the captive portal login is completed.
Show Recommended Approach
Yes, OpenRoaming fully satisfies this requirement. With a captive portal, traffic is unencrypted over the air until the user completes the login process — creating a vulnerability window. OpenRoaming uses 802.1X authentication and WPA3-Enterprise (or WPA2-Enterprise), which establishes a unique, cryptographically secure encrypted session via a 4-way handshake immediately upon successful authentication, before any user data is transmitted. Each session uses a unique PMK derived from the EAP exchange, ensuring per-session encryption that is far stronger than the shared PSK model.
Q3. You are configuring the WLAN controller for a new stadium deployment that will participate in the settlement-free OpenRoaming federation. A colleague suggests also broadcasting the settled RCOI to maximise compatibility. What are the implications of broadcasting both RCOIs simultaneously, and what is your recommendation?
💡 Hint:Consider the commercial and operational implications of the settled RCOI, and how devices prioritise RCOI matching.
Show Recommended Approach
Broadcasting the settled RCOI (BA-A2-D0) alongside the settlement-free RCOI (5A-03-BA) is technically possible but carries significant commercial risk. The settled RCOI signals to Identity Providers that the ANP expects financial compensation for connectivity. This may deter IDPs from allowing their users to connect, as they would incur charges. For a stadium seeking maximum user adoption and seamless connectivity, broadcasting only the settlement-free RCOI is the correct approach. The settled RCOI should only be used when a specific commercial settlement agreement is in place with the relevant IDPs.
Key Takeaways
- ✓OpenRoaming replaces manual captive portals with automatic, zero-touch Wi-Fi connectivity built on Passpoint (IEEE 802.11u) and 802.1X authentication.
- ✓The global federation scales through dynamic DNS-based peer discovery (RFC 7585) and RadSec mTLS (RFC 6614), eliminating the need for static routing tables or bilateral agreements.
- ✓WPA3-Enterprise encryption is established from the very first packet, and mutual certificate authentication eliminates Evil Twin attack vectors.
- ✓Pseudonymous identifiers (Chargeable-User-Identity) minimise PII collection, directly reducing GDPR compliance obligations for venue operators.
- ✓Venues typically report a 70-80% reduction in Wi-Fi-related support tickets and a 40-50% increase in Wi-Fi adoption rates after deployment.
- ✓Certificate lifecycle management is the single most critical operational task — expired WBA PKI certificates cause silent RadSec failures.
- ✓Dynamic VLAN assignment via RADIUS is mandatory for PCI DSS compliance in retail environments and best practice across all verticals.



