Walled Garden Configuration for Guest WiFi
This guide provides a comprehensive, vendor-neutral technical reference for configuring walled gardens in enterprise guest WiFi deployments. It covers the architecture of pre-authentication access, the critical role of dynamic DNS resolution, social login domain whitelisting, OS captive portal probe requirements, and compliance considerations under PCI DSS and GDPR. Aimed at IT managers, network architects, and venue operations directors, it delivers actionable implementation guidance with real-world case studies from hospitality, retail, and events environments.
🎧 Listen to this Guide
View Transcript
Executive Summary
A walled garden is a fundamental component of any secure, user-friendly guest WiFi deployment. It defines the limited set of network resources a guest device can access before completing authentication via a captive portal. An incorrect or incomplete walled garden configuration is the single leading cause of guest login failures across enterprise deployments — resulting in a degraded user experience, increased helpdesk tickets, and measurable reputational damage in hospitality and retail environments. For IT managers and network architects, mastering walled garden WiFi configuration is not merely a technical task; it is a critical step in mitigating security risks, ensuring compliance with standards such as PCI DSS v4.0 and GDPR, and maximising the return on investment of a guest WiFi estate. This guide provides a vendor-neutral, actionable framework for designing, implementing, and maintaining a robust walled garden that supports modern authentication methods — including social logins via OAuth 2.0, payment gateways, and OS-level captive portal detection — across enterprise environments including hospitality, retail, events, and public sector organisations.
Technical Deep-Dive
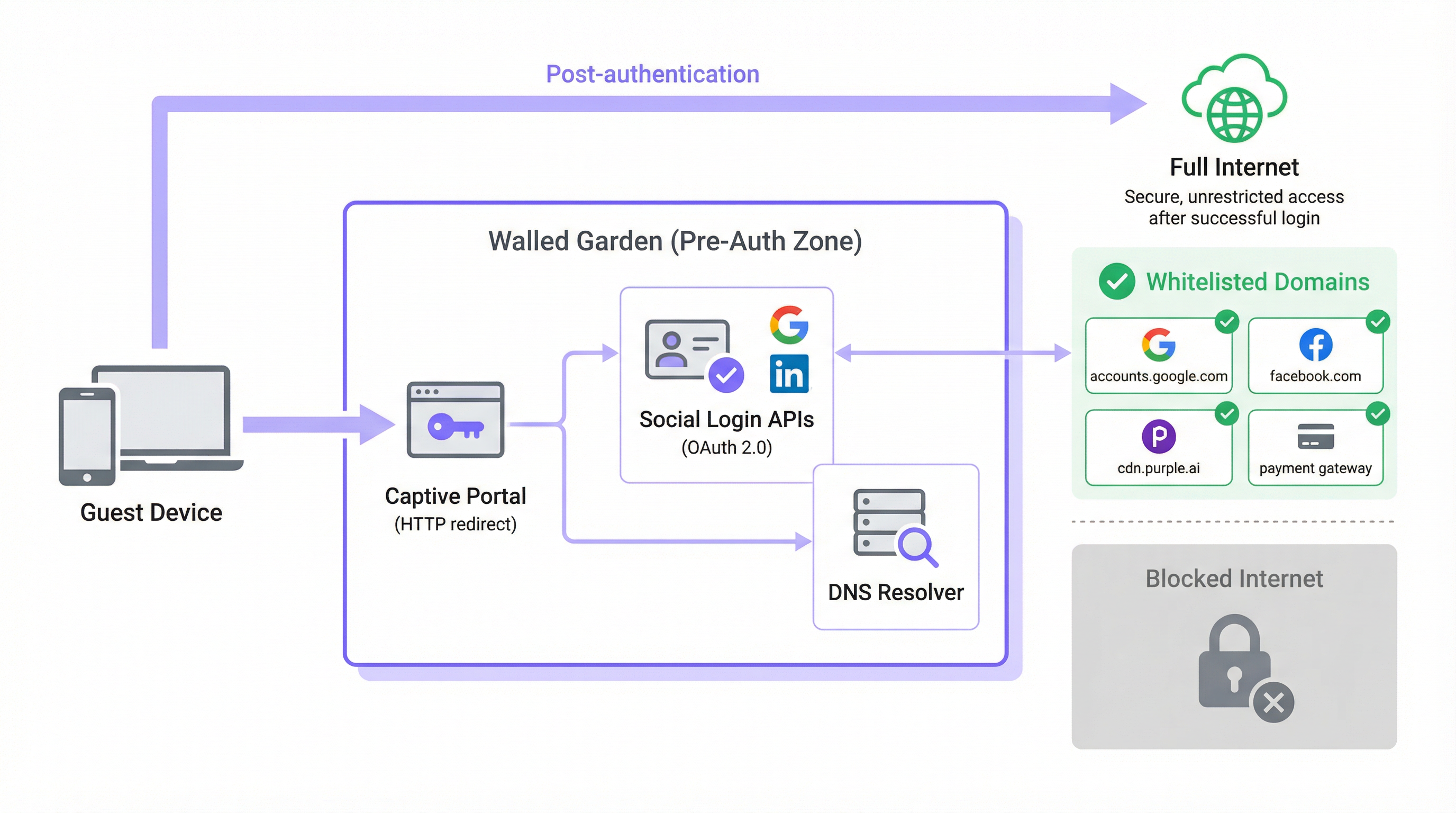
The Anatomy of Pre-Authentication Access
In a typical guest WiFi architecture, when a user's device associates with an open SSID, it is assigned an IP address via DHCP and placed into a pre-authentication role or isolated VLAN by the network controller. In this state, the controller intercepts all outbound HTTP and HTTPS traffic and redirects it to the captive portal splash page. This is the mechanism that forces the guest's browser to the login screen. The walled garden is the explicit exception to this interception rule: a curated whitelist of external domains and IP address ranges that the device is permitted to communicate with freely during the pre-authentication phase.
Without a properly configured walled garden, the very services required to complete authentication are themselves blocked. Modern captive portals are not monolithic, self-contained applications. They are composites of microservices and third-party APIs. The portal's own assets — HTML, CSS, JavaScript, and images — may be served from a Content Delivery Network (CDN) that is entirely separate from the controller's local infrastructure. Social login functionality depends on reaching OAuth 2.0 endpoints at Google, Facebook, Apple, or Microsoft. If a paid WiFi tier is offered, the portal must communicate with a payment processor such as Stripe or PayPal. Analytics and marketing platforms may load tracking scripts from their own CDN origins. Each of these dependencies represents a domain that must be explicitly permitted in the walled garden, or the authentication flow will fail silently or with a confusing error.
The DNS Resolution Problem
The most technically nuanced aspect of walled garden configuration is the gap between domain-based administration and IP-based enforcement. Whilst network administrators configure the walled garden using human-readable domain names (e.g., accounts.google.com), most network controllers enforce these rules at the IP layer. When a domain is added to the whitelist, the controller performs a DNS lookup to resolve it to one or more IP addresses and adds those IPs to a temporary access control list (ACL).
This creates a significant operational risk with major cloud providers. Google, Meta, Apple, and the leading CDNs use anycast routing and dynamic IP address assignment. The IP address that accounts.google.com resolves to at the time of configuration may be entirely different from the address it resolves to six months later, or even on a different network segment. A static IP whitelist is therefore not a sustainable configuration; it will degrade over time as CDN IP ranges rotate.
The correct solution is dynamic DNS resolution, where the network controller periodically re-resolves each whitelisted domain and updates its ACLs accordingly. Most enterprise-grade controllers from Cisco, Aruba, Ruckus, and Fortinet support this natively. If your controller does not, you are operating with a configuration that will produce intermittent failures that are difficult to diagnose and will worsen over time.
HTTPS Interception and TLS Compliance
A further layer of complexity arises from the prevalence of HTTPS. When a guest device in the pre-authentication state attempts to load a non-whitelisted HTTPS resource, the controller must decide how to handle the request. There are two common approaches, both with significant drawbacks if not managed correctly.
The first approach is a silent drop, where the controller simply blocks the connection. The guest's browser displays a generic "site can't be reached" error, which provides no useful guidance and is often interpreted as a network fault rather than a portal prompt. The second approach is HTTPS interception, where the controller attempts to present a redirect to the captive portal. This requires the controller to act as a man-in-the-middle (MITM) proxy, presenting its own TLS certificate. If this certificate is not trusted by the guest's device — which it almost never is on a public guest network — the browser will display a security warning, which is alarming to users and, in regulated environments, may constitute a compliance issue.
The correct architectural approach is to ensure that all domains required for the authentication flow are whitelisted, allowing their HTTPS traffic to pass through untouched. The captive portal redirect should be triggered by the OS-level probe mechanism rather than by HTTPS interception. This eliminates the certificate trust problem entirely. Modern browsers also implement HTTP Strict Transport Security (HSTS) and, in some cases, certificate pinning. Both mechanisms will cause HTTPS interception to fail outright for major domains, producing a broken connection rather than a redirect — another strong argument for a correctly configured walled garden over a broad HTTPS interception policy.
Captive Network Assistant (CNA) and OS Probe Domains
One of the most frequently overlooked aspects of walled garden configuration is the mechanism by which modern operating systems detect the presence of a captive portal. All major operating systems — iOS, iPadOS, macOS, Android, and Windows — implement a Captive Network Assistant (CNA) that probes a known HTTP endpoint immediately after connecting to a new WiFi network. If the response deviates from the expected value, the OS infers that it is behind a captive portal and automatically launches a browser window to handle the login.
The probe endpoints used by each platform are as follows:
| Operating System | Probe Domain | Expected Response |
|---|---|---|
| Apple (iOS, macOS) | captive.apple.com |
HTTP 200 with specific body |
| Android (Google) | connectivitycheck.gstatic.com |
HTTP 204 No Content |
| Windows | www.msftconnecttest.com |
HTTP 200 with specific body |
| Firefox / Mozilla | detectportal.firefox.com |
HTTP 200 with specific body |
If any of these probe domains are blocked by the walled garden, the OS will never detect the captive portal. From the guest's perspective, the WiFi network simply has no internet access. This is one of the most common misconfiguration failures observed in production deployments and is entirely preventable by including these domains in the baseline whitelist.
Implementation Guide
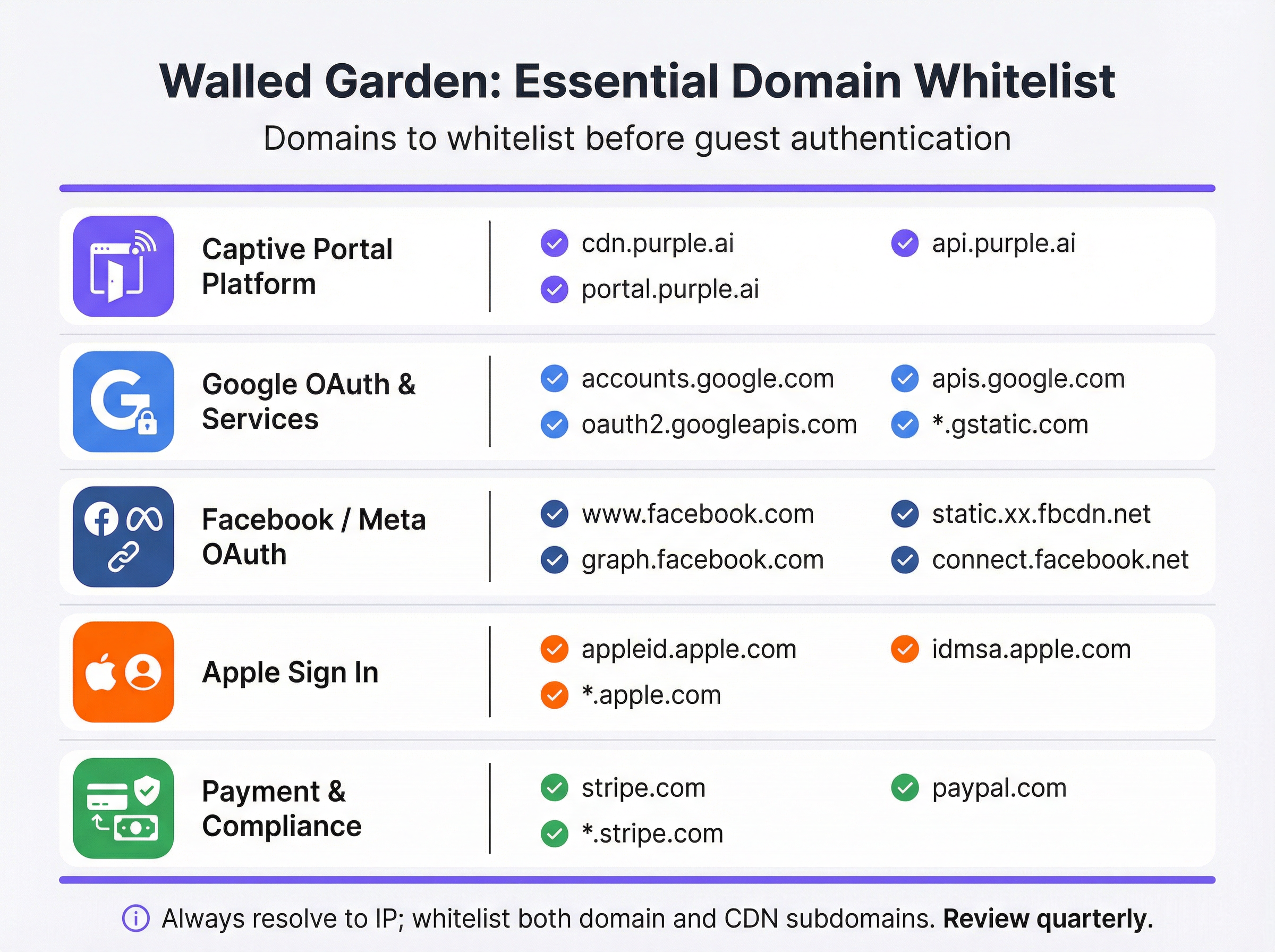
Step 1: Baseline Domain Discovery
Before touching your controller configuration, conduct a thorough audit of every external service your captive portal depends on. This is best accomplished by loading the portal in a browser with developer tools open and inspecting the network tab to identify all external resource requests. The resulting list should be categorised as follows:
| Category | Purpose | Essential Domains |
|---|---|---|
| Captive Portal Platform | Serves splash page assets and handles auth logic. | *.purple.ai, cdn.your-vendor.com |
| Google OAuth | Enables Google Sign-In. | accounts.google.com, oauth2.googleapis.com, apis.google.com, *.gstatic.com |
| Facebook / Meta OAuth | Enables Facebook Login. | www.facebook.com, graph.facebook.com, connect.facebook.net, *.fbcdn.net |
| Apple Sign In | Enables Sign in with Apple. | appleid.apple.com, idmsa.apple.com, *.apple.com |
| OS Captive Portal Probes | Enables automatic portal detection. | captive.apple.com, connectivitycheck.gstatic.com, www.msftconnecttest.com |
| Payment Gateways | Processes payments for premium tiers. | *.stripe.com, *.paypal.com |
| Analytics / Marketing | Loads tracking and analytics scripts. | Vendor-specific (e.g., *.segment.com, *.mixpanel.com) |
Step 2: Controller Configuration
Implementation varies by vendor, but the underlying principles are universal. Navigate to the captive portal or splash page configuration in your network controller's management interface — in Cisco Meraki, this is found under Wireless > Configure > Splash Page; in Aruba Central, it is the Captive Portal Profile; in Fortinet, it is within Security Policies > Captive Portal. Locate the pre-authentication access or walled garden whitelist section and proceed as follows:
- Enter Domains by Category: Add each domain from your audit systematically, working through each category. Use wildcards (
*.gstatic.com) where your controller supports them and where the risk profile is acceptable. For high-security environments, prefer explicit subdomains over broad wildcards. - Enable Dynamic DNS Resolution: Confirm that your controller is configured to periodically re-resolve whitelisted domains rather than caching a static IP list. Consult your vendor's documentation to verify this is active. Set a DNS TTL of 60 seconds or lower for walled garden entries.
- Configure Dual-Stack Rules: If your network supports IPv6 — and it should, given the depletion of IPv4 address space — ensure your walled garden ACLs apply to both IPv4 and IPv6 traffic. A guest device with an IPv6 address will bypass IPv4-only ACLs.
- Apply to Guest SSID: Associate the captive portal profile and its walled garden with the guest SSID only. Never apply guest-level walled garden policies to corporate SSIDs.

Step 3: Pre-Go-Live Testing Protocol
Testing is non-negotiable and must be conducted with real devices in a genuine pre-authentication state — not administrator accounts that may have elevated access, and not devices that have previously connected to the network and may have cached credentials.
For each device platform (iOS, Android, Windows, macOS), perform the following:
- Forget the network on the test device to ensure no cached state.
- Connect to the guest SSID and observe whether the captive portal launches automatically via the CNA mechanism.
- Attempt every login method offered on the portal — email registration, Google Sign-In, Facebook Login, Apple Sign In — and confirm each completes successfully.
- Test the payment flow if a paid tier is offered, using a test card number from your payment gateway's sandbox environment.
- Inspect the browser console on any failing test. The network tab will identify the exact domain being blocked, allowing you to add it to the whitelist with precision.
Document the results of this testing protocol in a configuration record that is retained for compliance purposes.
Best Practices
Principle of Least Privilege is the foundational rule for walled garden configuration. Whitelist only the domains that are demonstrably required for the authentication flow to function. Avoid broad wildcards such as *.google.com or *.facebook.com unless your controller's implementation requires them; prefer specific subdomains. Every additional whitelisted domain represents a potential attack surface in the pre-authentication zone.
Quarterly Review Cadence is essential for maintaining a functional walled garden over time. Social login providers and CDNs update their infrastructure regularly. Apple modified its Sign In domain structure in 2023. Google has added new subdomains to its OAuth flow on multiple occasions. A walled garden that was accurate at deployment will drift out of alignment within months without active maintenance. Build a quarterly review into your operational calendar, cross-referencing your whitelist against the current documentation from each provider.
Compliance Alignment requires that your walled garden configuration does not inadvertently violate the requirements of applicable standards. Under PCI DSS v4.0, any network that processes, stores, or transmits cardholder data must maintain strict access controls. If your guest WiFi includes a paid tier, the walled garden must permit TLS 1.2 or higher connections to your payment processor without interception. Under GDPR, the privacy notice must be accessible to guests before they provide any personal data — meaning the link to your privacy policy must be reachable from within the walled garden, even before authentication.
Change Management Documentation is a professional obligation for any production network change. Every modification to the walled garden — whether adding a new domain, removing a deprecated one, or updating a wildcard — should be logged with a timestamp, the reason for the change, and the engineer responsible. This audit trail is invaluable for troubleshooting intermittent failures and for demonstrating due diligence in a compliance audit.
Troubleshooting & Risk Mitigation
The following table maps the most common failure modes to their root causes and recommended mitigations:
| Symptom | Root Cause | Mitigation |
|---|---|---|
| Portal does not launch automatically on iOS/Android | OS captive portal probe domains are blocked. | Add captive.apple.com and connectivitycheck.gstatic.com to the walled garden. |
| Google Sign-In button is unresponsive | One or more Google OAuth or CDN domains are missing. | Add accounts.google.com, oauth2.googleapis.com, apis.google.com, and *.gstatic.com. |
| Facebook login fails with a CORS error | Facebook CDN subdomains (*.fbcdn.net) are not whitelisted. |
Add wildcard entries for *.fbcdn.net and *.facebook.com. |
| Login works initially but fails intermittently | Static IP whitelist; CDN IP addresses have rotated. | Enable dynamic DNS resolution on the controller. |
| Guests see TLS certificate warnings | Controller is intercepting HTTPS traffic to non-whitelisted domains. | Whitelist all required domains so HTTPS passes through uninterrupted. |
| Payment page fails to load | Payment gateway CDN or API domains are not whitelisted. | Add *.stripe.com or *.paypal.com as appropriate. |
| IPv6 users cannot access the portal | Walled garden ACLs are IPv4-only. | Extend all walled garden rules to cover IPv6 address ranges. |
Risk Mitigation: Over-Whitelisting is a real and underappreciated risk. When intermittent failures occur, the tempting response is to add progressively broader wildcard entries until the problem disappears. This approach can result in a walled garden that is effectively open, allowing unauthenticated guests to access large portions of the internet without completing the login flow. This defeats the purpose of the captive portal, undermines data collection for marketing purposes, and may create liability under GDPR if guests can access the network without consenting to terms and conditions. Always diagnose the specific blocked domain before adding entries.
ROI & Business Impact
A correctly implemented walled garden delivers measurable business value across multiple dimensions. In the hospitality sector, a seamless guest WiFi login experience directly correlates with guest satisfaction scores. Research by J.D. Power consistently identifies WiFi performance as one of the top drivers of hotel guest satisfaction. A portal that fails to load — because the walled garden is misconfigured — creates a negative first impression that affects the entire stay experience.
For retail operators, the walled garden is the gateway to the loyalty programme. Every guest who successfully logs in via the captive portal provides a verified identity that can be linked to purchase behaviour, enabling personalised marketing campaigns with demonstrably higher conversion rates than anonymous advertising. A misconfigured walled garden that prevents login directly reduces the volume of first-party data captured, with a quantifiable impact on marketing ROI.
In the events sector — stadiums, conference centres, exhibition halls — the walled garden must be designed for scale. At peak load, tens of thousands of devices will attempt to authenticate simultaneously. A walled garden that relies on a slow or overloaded DNS resolver will create a bottleneck that manifests as a slow or unresponsive portal, even if the underlying network infrastructure is correctly sized. Deploying a local, caching DNS resolver that is authoritative for walled garden domains is a standard practice for high-density deployments.
For public sector organisations, the walled garden is also a compliance instrument. Under the UK's Network and Information Systems (NIS) Regulations and the broader GDPR framework, organisations must demonstrate that access to public-facing networks is controlled and auditable. A properly configured walled garden, combined with a compliant captive portal, provides the technical foundation for this audit trail.
The cost of getting the walled garden wrong is not merely technical. It is measured in helpdesk call volume, guest satisfaction scores, lost marketing data, and potential regulatory exposure. The investment in configuring and maintaining a robust walled garden is modest relative to these risks, and the return — in the form of higher portal adoption rates, richer first-party data, and reduced operational friction — is both measurable and significant.
Key Terms & Definitions
Walled Garden
A controlled set of pre-approved domains and IP address ranges that a guest device can access on a WiFi network before completing authentication. All traffic to domains outside this list is blocked or redirected to the captive portal.
This is the foundational mechanism that allows a captive portal to function. Without it, the portal itself — and all social login providers it depends on — would be unreachable by unauthenticated devices.
Captive Portal
A web page that intercepts the internet traffic of a newly connected WiFi user and requires them to complete an action — such as logging in, accepting terms, or making a payment — before granting full network access.
The captive portal is the primary point of interaction for guests. It is the mechanism through which operators collect first-party data, enforce terms of service, and manage paid access tiers.
OAuth 2.0
An open authorisation standard that allows users to grant a third-party application limited access to their account on another service, without sharing their password. It is the protocol underpinning 'Login with Google' and 'Login with Facebook'.
Every social login option on a captive portal relies on OAuth 2.0. Each provider's OAuth endpoints must be whitelisted in the walled garden for the login flow to complete successfully.
Dynamic DNS Resolution
A network controller feature that periodically re-resolves whitelisted domain names to their current IP addresses and updates the enforcement ACLs accordingly, rather than using a static IP list.
This is essential for walled garden reliability. Without it, the IP addresses cached at deployment time will become stale as CDNs rotate their infrastructure, causing intermittent and hard-to-diagnose login failures.
Content Delivery Network (CDN)
A geographically distributed network of servers that delivers web content to users from the nearest available location, improving performance and availability.
Captive portals and social login providers rely on CDNs to serve scripts, fonts, and images. CDN subdomains (e.g., *.gstatic.com for Google, *.fbcdn.net for Facebook) must be included in the walled garden.
Captive Network Assistant (CNA)
A built-in feature of modern operating systems (iOS, Android, Windows, macOS) that automatically detects the presence of a captive portal by probing a known HTTP endpoint after connecting to a new WiFi network.
The CNA is what causes the portal login window to pop up automatically on a guest's device. If the probe domain is blocked by the walled garden, the CNA cannot detect the portal and the guest sees no login prompt.
Pre-Authentication ACL
An Access Control List applied to a network session before the user has authenticated. It defines which traffic is permitted (the walled garden) and which is blocked or redirected.
This is the technical implementation of the walled garden on enterprise network controllers. IT teams configure Pre-Authentication ACLs in the captive portal settings of their wireless controllers.
PCI DSS
The Payment Card Industry Data Security Standard is a set of security standards designed to ensure that all companies that accept, process, store, or transmit credit card information maintain a secure environment.
Relevant to any guest WiFi deployment with a paid access tier. The walled garden must permit TLS 1.2+ connections to the payment gateway without interception, and the guest network must be segmented from any cardholder data environment.
HTTP Strict Transport Security (HSTS)
A web security policy mechanism that instructs browsers to only interact with a server using HTTPS, preventing protocol downgrade attacks and cookie hijacking.
HSTS causes HTTPS interception by a captive portal controller to fail outright for major domains, as the browser refuses to accept a certificate it does not trust. This reinforces the case for a correctly configured walled garden over an HTTPS interception approach.
Case Studies
A 500-room luxury hotel is deploying a new guest WiFi network using Cisco Meraki hardware and the Purple platform. They need to support Google and Facebook logins, and offer a paid premium-speed tier via Stripe. What is the minimum set of domains that must be whitelisted in the Meraki walled garden, and how should they be configured?
The following domains must be entered into the Meraki dashboard under Wireless > Configure > Splash Page > Walled Garden Ranges:
- Purple Platform: *.purple.ai (covers cdn, portal, and api subdomains)
- Google OAuth: accounts.google.com, oauth2.googleapis.com, apis.google.com, *.gstatic.com
- Facebook OAuth: www.facebook.com, graph.facebook.com, connect.facebook.net, *.fbcdn.net
- Stripe Payments: *.stripe.com
- OS Probes: captive.apple.com, connectivitycheck.gstatic.com, www.msftconnecttest.com
Cisco Meraki performs dynamic DNS resolution natively for walled garden entries, so no additional configuration is required for IP resolution. The hotel should also ensure their privacy policy URL is accessible from within the walled garden to comply with GDPR. Post-deployment, the IT team should test with a factory-reset iOS device and a factory-reset Android device to verify the full login flow for both social login methods.
A national retail chain with 200 stores is experiencing intermittent Google login failures on their guest WiFi. The failures are random — some stores are unaffected, others see failures on certain days or at certain times. The network uses Fortinet FortiGate controllers. What is the most likely root cause and how would you resolve it?
The most likely root cause is that the FortiGate walled garden is using a static IP list for Google's OAuth domains, and Google's CDN has rotated its IP addresses at some locations. The intermittent, location-specific nature of the failures is a classic indicator of CDN IP rotation — some stores' cached IP lists are still valid, others have become stale.
Resolution steps:
- Log into the FortiGate management console at an affected store and navigate to the captive portal walled garden configuration.
- Verify whether the Google OAuth domains are configured as domain names or as static IP addresses.
- If static IPs are present, replace them with domain-based entries: accounts.google.com, oauth2.googleapis.com, apis.google.com, *.gstatic.com.
- Enable the FortiGate's FQDN-based address objects with a short refresh interval (recommended: 60 seconds) to ensure dynamic DNS resolution is active.
- Roll this configuration change out to all 200 stores via FortiManager to ensure consistency.
- Monitor the affected stores for 48 hours post-change to confirm resolution.
Scenario Analysis
Q1. You are designing the guest WiFi for a new international airport terminal. The requirements include login via Google, Apple, and WeChat, plus a premium access tier sold via PayPal. What unique challenges does this scenario present for your walled garden configuration, and how would you address them?
💡 Hint:Consider the geographical and application-specific nature of WeChat's login flow, and the implications of a globally diverse user base for CDN IP resolution.
Show Recommended Approach
Three unique challenges arise. First, WeChat login: unlike standard web-based OAuth, WeChat's login flow on mobile devices often attempts to open the native WeChat app via a deep link rather than completing the flow in a web browser. This can break the captive portal flow entirely. The solution is to configure the portal to force a web-based QR code flow and whitelist the specific Tencent domains that serve the QR code and handle the authentication handshake (e.g., open.weixin.qq.com, wx.qq.com). Second, global CDN resolution: an international airport serves users from every region. Dynamic DNS resolution is critical, as Google, Apple, and PayPal serve their content from geographically distributed CDN nodes. The controller must re-resolve walled garden domains frequently to ensure the correct regional IP addresses are whitelisted. Third, PayPal localisation: PayPal uses country-specific domains and CDNs for localised payment experiences. In addition to *.paypal.com, you may need to whitelist *.paypalobjects.com and regional variants. A thorough audit of the PayPal checkout flow from multiple device locales is recommended before go-live.
Q2. A 60,000-seat stadium is experiencing widespread portal login failures during the first 15 minutes of every event, after which performance normalises. The infrastructure is correctly sized for the user load. What is the likely bottleneck and how would you resolve it?
💡 Hint:Think about what happens when 60,000 devices all attempt to connect and resolve the same domains simultaneously.
Show Recommended Approach
The bottleneck is almost certainly DNS resolution. When 60,000 devices connect simultaneously, they all attempt to resolve the same walled garden domains (portal CDN, Google OAuth, Apple Sign In, etc.) at the same time. If the upstream DNS resolver — typically the ISP's recursive resolver or a cloud DNS service — cannot handle this burst of queries, resolution latency spikes, causing the portal to appear slow or unresponsive even though the network itself is performing correctly. The performance normalises after the initial rush because the resolver's cache warms up and subsequent queries are served from cache. The solution is to deploy a local, caching DNS resolver (e.g., Unbound or a dedicated appliance) within the stadium's network infrastructure. This resolver should be pre-seeded with the walled garden domains before the event begins, so that all DNS queries for those domains are answered from local cache with sub-millisecond latency. The controller's DHCP configuration should point guest devices to this local resolver.
Q3. Your company is acquiring a chain of boutique hotels that uses a competitor's captive portal platform. You are tasked with migrating them to Purple. The existing IT team has no documentation of their current walled garden configuration. How would you approach the migration to ensure no guest-facing disruption?
💡 Hint:Before you build the new, you must understand the old. Consider both technical discovery and business requirements.
Show Recommended Approach
The migration should proceed in four stages. Stage 1 — Discovery: Connect a laptop to the existing guest WiFi in an unauthenticated state and use a packet capture tool (Wireshark) to record all DNS queries and HTTP/HTTPS requests made during the authentication flow. This produces a definitive list of every domain the existing portal depends on, regardless of what is or is not documented. Stage 2 — Categorisation: Map the discovered domains to the standard categories (portal platform, OAuth, CDN, OS probes, payments). Identify any non-standard domains — these may indicate custom integrations (e.g., a loyalty programme API, a local marketing platform) that must be preserved in the new configuration. Stage 3 — Parallel Deployment: Configure the Purple platform with the discovered domain list and deploy it on a test SSID alongside the existing portal. Run the full test protocol on both SSIDs simultaneously to validate that the Purple configuration is functionally equivalent. Stage 4 — Cutover: Once validated, migrate the production SSID to Purple during a low-traffic period (e.g., 3am on a weeknight). Monitor portal adoption rates and helpdesk tickets for the following 48 hours to confirm a clean cutover.
Key Takeaways
- ✓A walled garden is the whitelist of domains accessible before guest WiFi authentication — it is the mechanism that allows the captive portal itself to function.
- ✓Incorrect walled garden configuration is the leading cause of guest login failures; the most common omission is OS captive portal probe domains (captive.apple.com, connectivitycheck.gstatic.com).
- ✓Every social login method (Google, Facebook, Apple) requires its own set of OAuth and CDN domains to be whitelisted — missing even one will cause silent failures.
- ✓Always use dynamic DNS resolution for walled garden domains; static IP lists will degrade over time as CDN providers rotate their infrastructure.
- ✓Test every login path with real, factory-reset devices before go-live — administrator accounts and previously connected devices will not reveal misconfiguration.
- ✓Schedule a quarterly review of your walled garden whitelist; OAuth providers and CDNs change their domain structures regularly without notice.
- ✓A correctly configured walled garden directly increases portal adoption rates, first-party data capture, and guest satisfaction — making it a measurable driver of marketing and operational ROI.



