What is a Captive Portal and How Does It Work?
A comprehensive technical reference for IT managers and venue operators on the architecture, deployment, and business impact of captive portals. This guide provides actionable insights into device detection, the Captive Network Assistant (CNA), and best practices for implementation in enterprise environments.
🎧 Listen to this Guide
View Transcript

Executive Summary
A captive portal is the web page that intercepts a user's connection to a public or guest WiFi network, requiring them to perform an action—such as accepting terms, entering an email, or authenticating with a social media account—before granting full internet access. For IT managers, network architects, and venue operators, the captive portal is a critical control point for network security, legal compliance, and user engagement. Deployed correctly, it transforms a simple utility into a powerful asset for gathering business intelligence, driving marketing initiatives, and enhancing the visitor experience. This guide provides a technical deep-dive into the underlying architecture of captive portals, including the interception mechanisms (DNS hijacking and HTTP redirect), the role of the Captive Network Assistant (CNA) in modern operating systems, and the standards (RADIUS, WISPr) that govern authentication. It offers practical, vendor-neutral implementation guidance for enterprise environments like hotels, retail chains, and stadiums, focusing on security best practices, risk mitigation, and strategies for measuring return on investment (ROI). By understanding the technical nuances and strategic value of captive portals, IT leaders can ensure their guest WiFi deployments are secure, compliant, and aligned with broader business objectives.
Technical Deep-Dive
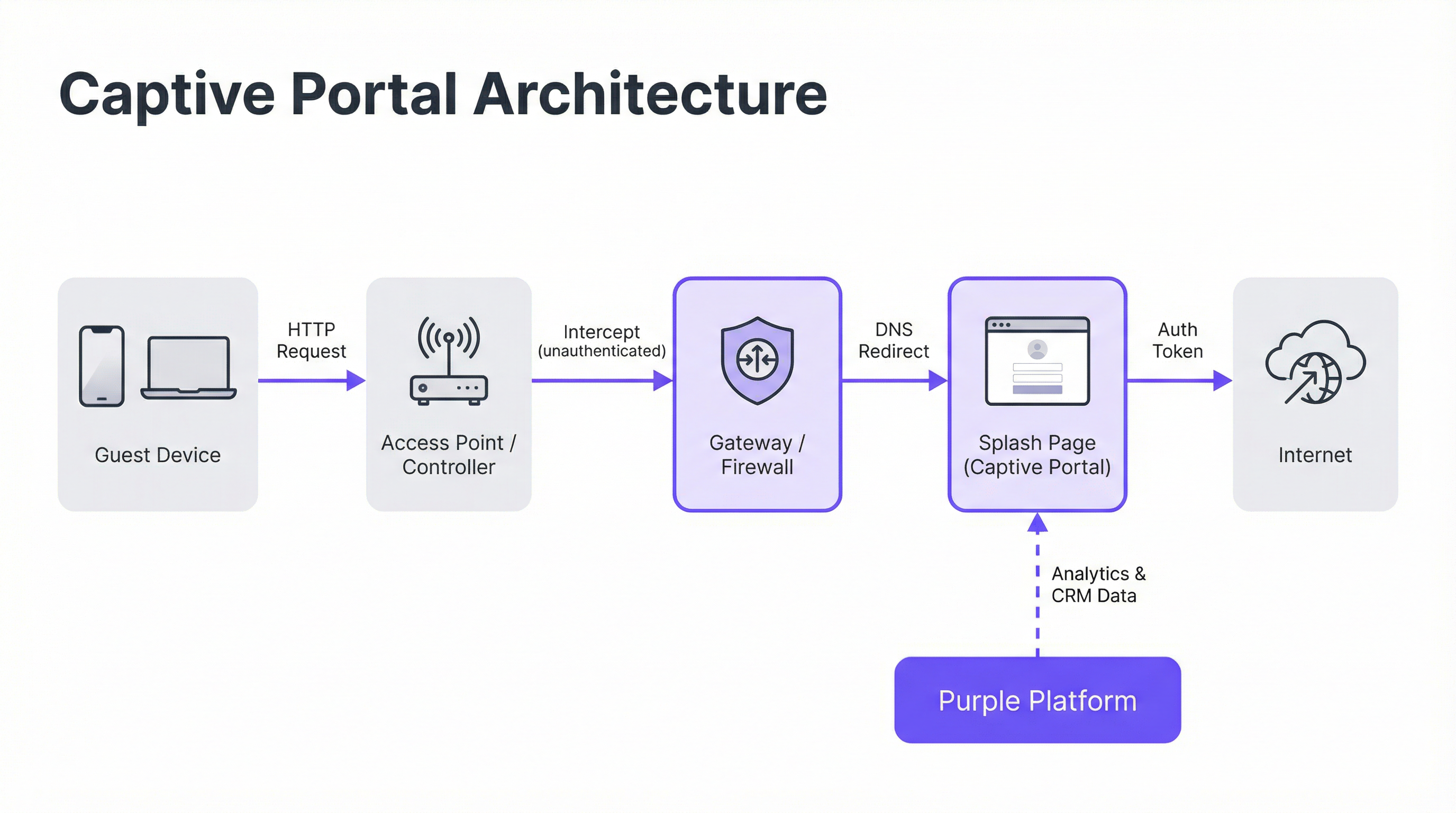
Core Architecture: The Walled Garden
A captive portal operates by creating a 'walled garden,' a restricted network state where a newly connected device has its internet access limited until it completes an authentication process. This is achieved through two primary interception techniques deployed at the network gateway or wireless controller level.
DNS Hijacking: When an unauthenticated device attempts to resolve a domain name (e.g.,
google.com), the network gateway intercepts the DNS query. Instead of returning the correct public IP address, it responds with the IP address of the captive portal server. The device's browser then initiates a connection to the portal, believing it to be the intended destination. This is the most common method as it effectively intercepts traffic regardless of protocol.HTTP Redirect: In this model, the gateway allows the DNS query to resolve correctly. However, when the device sends its initial HTTP request, the gateway intercepts it and responds with an HTTP 302 'Found' status code, redirecting the browser to the captive portal's URL. The primary limitation of this method is its ineffectiveness against HTTPS traffic, as the browser's security protocols will prevent the redirect and show a certificate warning. Modern systems use a hybrid approach, relying on DNS hijacking as the primary mechanism.
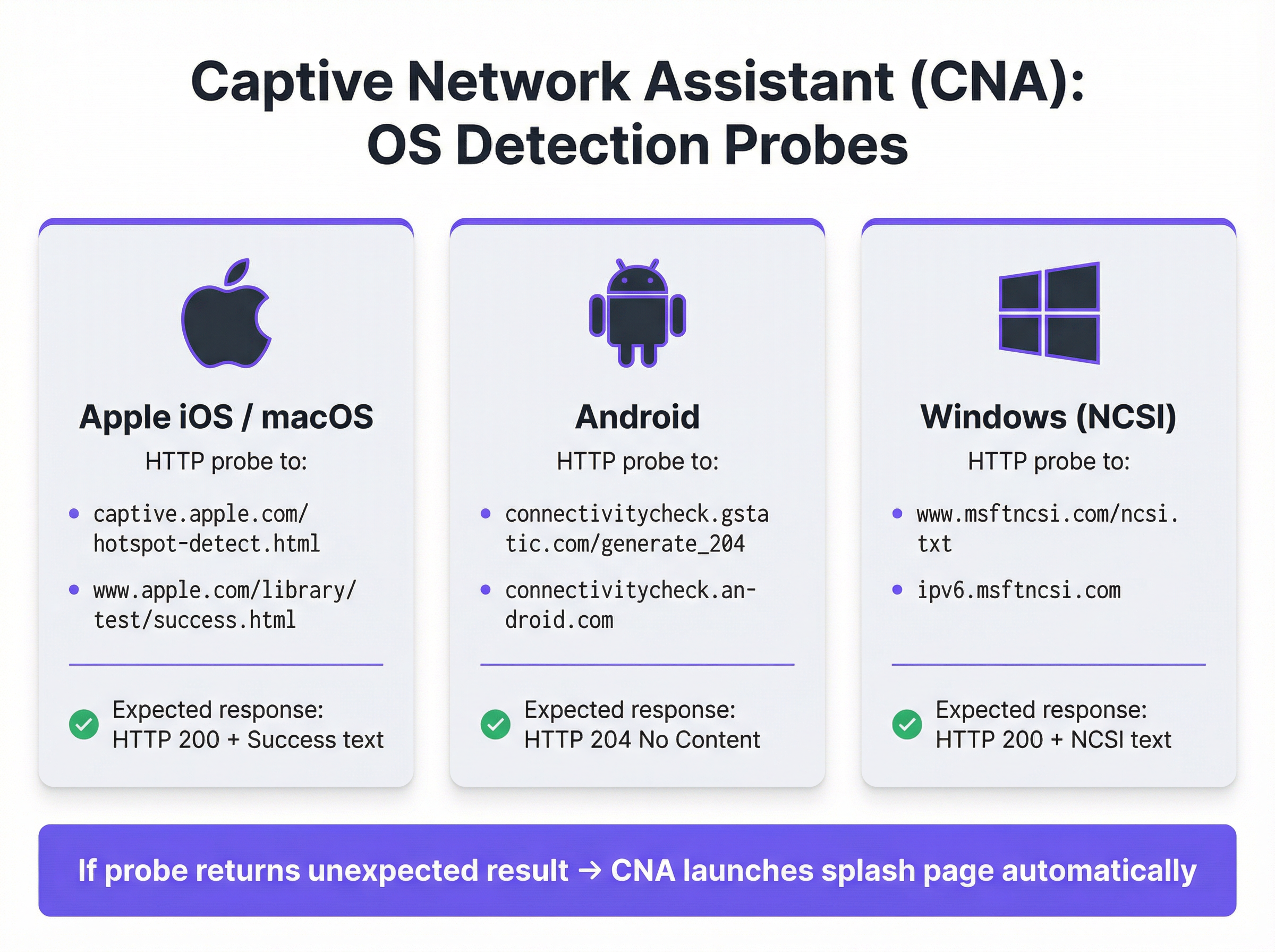
The Captive Network Assistant (CNA)
The seamless, automatic appearance of the splash page on modern devices is orchestrated by the Captive Network Assistant (CNA), a feature built into all major operating systems. The moment a device connects to a new WiFi network, the OS performs a 'liveness' test by sending an HTTP probe to a hardcoded endpoint.
- Apple (iOS & macOS): Probes
captive.apple.com/hotspot-detect.htmland expects an HTTP 200 response containing the word 'Success'. - Android: Probes
connectivitycheck.gstatic.com/generate_204and expects an HTTP 204 'No Content' response. - Windows (NCSI): The Network Connectivity Status Indicator probes
www.msftncsi.com/ncsi.txtand expects an HTTP 200 response with the text 'Microsoft NCSI'.
If the gateway intercepts this probe and returns anything other than the expected response, the OS concludes it is behind a captive portal and automatically launches the CNA—a sandboxed, lightweight 'mini-browser'—to display the splash page. This process removes the need for users to manually open their browser, significantly improving the user experience.
Authentication and Access Grant
Once the user interacts with the splash page (e.g., by submitting a form), the portal server communicates with the network gateway to authorise the device. This is typically handled via one of three protocols:
- RADIUS (Remote Authentication Dial-In User Service): The most common standard (RFC 2865), where the portal acts as a RADIUS client, sending an authentication request with the device's MAC address to the gateway (acting as the RADIUS server).
- WISPr (Wireless Internet Service Provider roaming): An XML-based protocol for hotspot authentication, though its adoption is less widespread than RADIUS.
- Proprietary APIs: Many modern network hardware vendors (like Cisco Meraki, Aruba, and Ruckus) provide RESTful APIs that allow for more flexible and granular control over device authorisation, which is the integration method used by Purple.
Upon successful authentication, the gateway moves the device's MAC address from the 'unauthenticated' to the 'authenticated' state, removes the walled garden restrictions, and grants full internet access for a predefined session duration.
Implementation Guide
Deploying an enterprise-grade captive portal requires careful planning that extends beyond the splash page design. Follow these vendor-neutral steps for a successful implementation.
Define Access Policies: Determine authentication methods (e.g., social login, email/SMS verification, voucher codes), session duration, idle timeouts, and bandwidth limits. For a hotel, a 24-hour session with a 10 Mbps cap might be appropriate. For a high-density stadium, a 4-hour session with a 2 Mbps cap and aggressive traffic shaping is more realistic.
Configure the Walled Garden: Create a comprehensive whitelist of all domains and IP addresses that an unauthenticated device must be able to access. This includes the portal server itself, its CDN for assets (images, CSS), and the endpoints for any third-party authentication providers (e.g., Google's and Facebook's OAuth domains). An incomplete walled garden is the leading cause of failed portal deployments.
Design a CNA-Optimised Splash Page: The splash page must be lightweight and responsive. It should load in under 3 seconds on a mobile connection and avoid complex JavaScript or large frameworks that may fail within the sandboxed CNA environment. All user actions should be achievable within a single page view to prevent issues with the CNA closing prematurely.
Integrate with Network Hardware: Configure your wireless controller or gateway to point to your captive portal server. This involves setting the portal URL, defining the RADIUS or API authentication parameters, and specifying the redirect behaviour. Purple provides pre-built integrations that automate this process for all major hardware vendors.
Ensure Data Compliance: If collecting personal data, your portal flow must incorporate explicit, granular consent mechanisms that comply with regulations like GDPR and CCPA. Consent for marketing must be separate from the acceptance of terms of service. The Purple platform includes a fully compliant consent management framework with auditable logs.

Best Practices
- Prioritise Security with WPA2/WPA3: Always run your guest SSID with, at minimum, WPA2-Personal encryption. A captive portal is an application-layer control and does not encrypt over-the-air traffic. Combining encryption with a portal provides layered security.
- Implement Network Segmentation: Use VLANs to strictly segregate guest traffic from your internal corporate network. A captive portal provides logical separation, but physical or virtual segmentation is required to meet standards like PCI DSS.
- Address MAC Address Randomisation: Modern mobile operating systems randomise MAC addresses by default to prevent tracking. Relying solely on MAC addresses for returning visitor recognition is no longer viable. Leverage platforms like Purple that use more advanced device fingerprinting and profile-based authentication to identify returning users.
- Monitor and Test Regularly: OS updates, especially from Apple, can change CNA behaviour without warning. Establish a quarterly testing protocol to validate your portal's functionality on the latest versions of iOS, Android, and Windows.
Troubleshooting & Risk Mitigation
| Common Failure Mode | Root Cause | Mitigation Strategy |
|---|---|---|
| Splash Page Not Loading | Incomplete walled garden blocking access to portal assets (CSS, JS, images) or DNS resolution failure. | Thoroughly test and validate all required domains for the walled garden. Ensure DNS is correctly configured on the guest VLAN. |
| Social Logins Failing | OAuth provider domains (e.g., accounts.google.com) are not included in the walled garden. |
Add all required third-party authentication domains to the walled garden. Use browser developer tools to trace network requests during the login flow. |
| CNA Window Closes Unexpectedly | The splash page attempts a complex redirect or tries to open a new tab, which is unsupported in the CNA. | Design a single-page authentication flow. Ensure all interactions happen within the initial portal page. |
| Users Not Redirected (HTTPS) | The gateway is attempting an HTTP redirect on an HTTPS site, causing a browser security error. | Ensure the gateway is configured for DNS hijacking, which is effective for both HTTP and HTTPS traffic. |
| Poor Performance / Slow Login | The splash page is too large (high-resolution images, heavy JavaScript frameworks). | Optimise all assets and aim for a total page weight under 500KB. Defer loading of non-essential scripts. |
ROI & Business Impact
The business value of a captive portal extends far beyond providing internet access. The ROI is measured through its ability to convert anonymous visitors into known customers and drive tangible business outcomes.
- Data Acquisition: By capturing email addresses, social profiles, or survey responses at the point of login, venues can build rich CRM profiles. A retail chain can attribute a physical store visit to a specific customer in their marketing database, bridging the online-offline gap.
- Increased Engagement: The splash page is a high-visibility digital billboard. Hotels can promote spa services or restaurant bookings. Conference centres can display event schedules and sponsor messages. This direct communication channel can drive incremental revenue.
- Operational Intelligence: WiFi analytics platforms like Purple use authentication data to provide deep insights into visitor behaviour. Heatmaps reveal footfall patterns, dwell time analysis shows engagement levels, and repeat visitor metrics help measure loyalty. A stadium can use this data to optimise concession stand staffing, while a museum can analyse exhibit popularity.
By leveraging a platform like Purple, the captive portal becomes the foundation of a venue's location intelligence strategy, delivering measurable returns in marketing effectiveness, operational efficiency, and customer satisfaction.
Key Terms & Definitions
Captive Portal
A web page that intercepts a newly connected user's browser, requiring them to perform a specific action before being granted full internet access.
This is the primary mechanism IT teams use to control access to guest and public WiFi networks, serving as a gateway for authentication, compliance, and user engagement.
Splash Page
The specific web page or user interface that is displayed to the user by the captive portal for authentication.
This is the main user-facing component. Its design and performance are critical for user experience and for achieving business goals like data capture or marketing.
Captive Network Assistant (CNA)
A built-in operating system feature (also known as a 'mini-browser') that automatically detects a captive portal and displays the splash page.
IT teams must design splash pages specifically for the CNA's limited, sandboxed environment, as it behaves differently from a standard web browser and is a common point of failure.
Walled Garden
The list of whitelisted IP addresses and domain names that an unauthenticated user is allowed to access before completing the captive portal authentication.
A misconfigured walled garden is the most common reason for portal failures. Network architects must ensure it includes all necessary endpoints for the portal and any third-party login providers.
DNS Hijacking
An interception technique where a network gateway provides a false IP address (that of the portal server) in response to a DNS query from an unauthenticated device.
This is the core mechanism that makes captive portals work, allowing the network to redirect users to the splash page regardless of the website they are trying to visit.
RADIUS (RFC 2865)
A standard networking protocol for centralized Authentication, Authorization, and Accounting (AAA) management.
In a captive portal context, it's a common way for the portal server to tell the network gateway that a user has been authenticated and should be granted internet access.
MAC Address Randomization
An OS-level privacy feature where a device uses a different, randomly generated MAC address for each WiFi network it connects to.
This feature makes it difficult for IT teams to track unique devices over time using traditional methods. It necessitates a shift towards profile-based authentication for accurate visitor analytics.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides authenticated network access to Ethernet networks and WLANs.
This is the enterprise-grade alternative to captive portals, often used for corporate devices. It offers higher security but requires client-side configuration, making it unsuitable for guest access scenarios where simplicity is key.
Case Studies
A 200-room luxury hotel needs to replace its outdated guest WiFi system. The goal is to provide a seamless, branded login experience, offer tiered bandwidth (free for basic access, paid for premium streaming), and promote hotel amenities like the spa and restaurant directly on the splash page. The hotel uses Cisco Meraki access points.
- Deployment with Purple & Meraki: Leverage Purple's native API integration with the Cisco Meraki dashboard. Create a new SSID for guest access (e.g., 'Hotel_Guest_WiFi') and configure it with WPA2-Personal encryption. In the Meraki dashboard, set the 'Splash Page' option to 'Sign-on with' and select 'Purple'.
- Tiered Access Configuration: Within the Purple platform, create two access tiers. The 'Free' tier is configured with a 5 Mbps bandwidth cap and a 24-hour session time. The 'Premium' tier is set to 25 Mbps with no cap and requires payment via an integrated Stripe gateway.
- Splash Page Design: Use Purple's drag-and-drop editor to design the splash page. The initial view presents the 'Free' option (login with email or social media) and a prominent 'Upgrade to Premium' button. Upon successful free login, the user is redirected to a welcome page featuring a carousel of promotions for the hotel's restaurant and spa, with direct links to the booking engine.
- Compliance: Enable Purple's GDPR/CCPA consent module, ensuring separate checkboxes for 'Terms of Service' and 'Marketing Communications'.
A national retail chain with 500 stores wants to offer free guest WiFi to understand in-store customer behavior and build its marketing database. They need a scalable solution that provides centralized management and delivers analytics on footfall, dwell time, and repeat visits. The existing hardware is a mix of Aruba and Ruckus.
- Centralized Management: Deploy Purple across all 500 stores. The platform's hardware-agnostic nature allows for consistent configuration across both Aruba and Ruckus controllers from a single cloud dashboard.
- Authentication & Data Capture: Configure the splash page to require social login (Facebook or Google) or email address submission. This captures valuable demographic data and a marketing contact for every user who connects.
- Analytics & Integration: Leverage Purple's WiFi analytics suite. The platform will automatically generate dashboards for each store and at the corporate level, showing metrics like unique visitors, dwell times by zone (if location services are enabled), and repeat visitor rates. Set up a daily data export via API to feed the captured email addresses and visitor metrics directly into the company's master CRM (e.g., Salesforce).
- Scalable Deployment: Create a single splash page template and apply it to all locations. Any updates to branding or promotions can be pushed to all 500 stores simultaneously from the central dashboard.
Scenario Analysis
Q1. You are deploying a new guest WiFi network in a conference center. A key requirement is that attendees can log in using their LinkedIn profile to facilitate networking. During testing, the LinkedIn login button on the splash page does nothing when clicked on an iPhone. What is the most likely cause and how would you troubleshoot it?
💡 Hint:Consider the sandboxed environment of the CNA and its network restrictions.
Show Recommended Approach
The most likely cause is an incomplete walled garden. The LinkedIn OAuth flow requires the device to access several domains (e.g., linkedin.com, static-exp1.licdn.com) to load its authentication scripts and display the login pop-up. Because the iPhone is in an unauthenticated state, the CNA is blocking these requests. To troubleshoot, I would connect a laptop to the guest SSID, open the browser's developer tools, and monitor the 'Network' tab while attempting to log in. This will reveal all the blocked domains, which must then be added to the gateway's walled garden whitelist.
Q2. A retail client wants to measure the loyalty of their in-store shoppers by tracking how many of them are repeat visitors. Their current captive portal only identifies devices by MAC address. Why is this approach flawed and what alternative strategy should you propose?
💡 Hint:Think about modern mobile OS privacy features.
Show Recommended Approach
This approach is flawed due to MAC address randomization, a default privacy feature in iOS, Android, and Windows that assigns a different MAC address for each WiFi network. A returning customer's phone will appear as a new device on each visit, making MAC-based loyalty tracking highly inaccurate. I would propose a shift to a profile-based authentication strategy using Purple. By requiring a social login or an email/phone number verification, we can create a persistent user profile that is independent of the device's MAC address. This allows for accurate tracking of repeat visits and builds a much richer CRM profile for the client.
Q3. A hotel is receiving complaints that its premium paid WiFi tier, which is supposed to be faster, feels no different from the free tier. The network is configured with a 5 Mbps cap on the 'Free' user profile and a 50 Mbps cap on the 'Premium' profile. Where in the network architecture would you investigate to diagnose this issue?
💡 Hint:Consider the entire data path from the access point to the internet egress.
Show Recommended Approach
The issue is likely not with the captive portal profiles themselves, but with a bottleneck further up the network chain. I would investigate in this order: 1. Wireless Controller/Gateway: Verify that the bandwidth shaping or Quality of Service (QoS) policies are being correctly applied to the user roles associated with the 'Free' and 'Premium' profiles. 2. Firewall: Check the firewall for any global traffic shaping policies that might be overriding the per-user rules from the controller. 3. Internet Circuit: Run a speed test from the gateway's LAN interface to confirm the total available internet bandwidth. It's possible the entire property's internet connection is saturated or performing below its subscribed speed, making the per-user caps irrelevant. 4. Access Point Saturation: In high-density areas, check the client load and channel utilization on the specific APs the complaining users are connected to. RF interference or an overloaded AP can also be a bottleneck.
Key Takeaways
- ✓A captive portal is a web page that intercepts user traffic on a guest WiFi network to enforce authentication and policy.
- ✓The automatic pop-up is handled by the Captive Network Assistant (CNA), a mini-browser in all major operating systems.
- ✓Core interception works via DNS hijacking or HTTP redirect at the network gateway.
- ✓Splash pages must be designed to be lightweight and functional within the limited, sandboxed CNA environment.
- ✓A correctly configured 'walled garden' is critical for ensuring third-party social logins work correctly.
- ✓Modern OS privacy features like MAC address randomization make profile-based authentication essential for accurate visitor analytics.
- ✓A captive portal platform like Purple transforms a network access tool into a powerful asset for business intelligence, marketing, and compliance.



