WiFi Roaming and Handoff: 802.11r and 802.11k Explained
This guide provides a senior-level technical deep-dive into WiFi roaming protocols — specifically 802.11r (Fast BSS Transition), 802.11k (Neighbor Reports), and 802.11v (BSS Transition Management) — and their combined role in delivering seamless connectivity across enterprise venues. It equips IT managers, network architects, and venue operations directors with the architectural understanding, implementation steps, and business-impact metrics needed to deploy and validate fast roaming in hospitality, retail, events, and public-sector environments. The guide also addresses the critical interaction between roaming and captive portals, a common deployment failure point in guest WiFi networks.
🎧 Listen to this Guide
View Transcript

Executive Summary
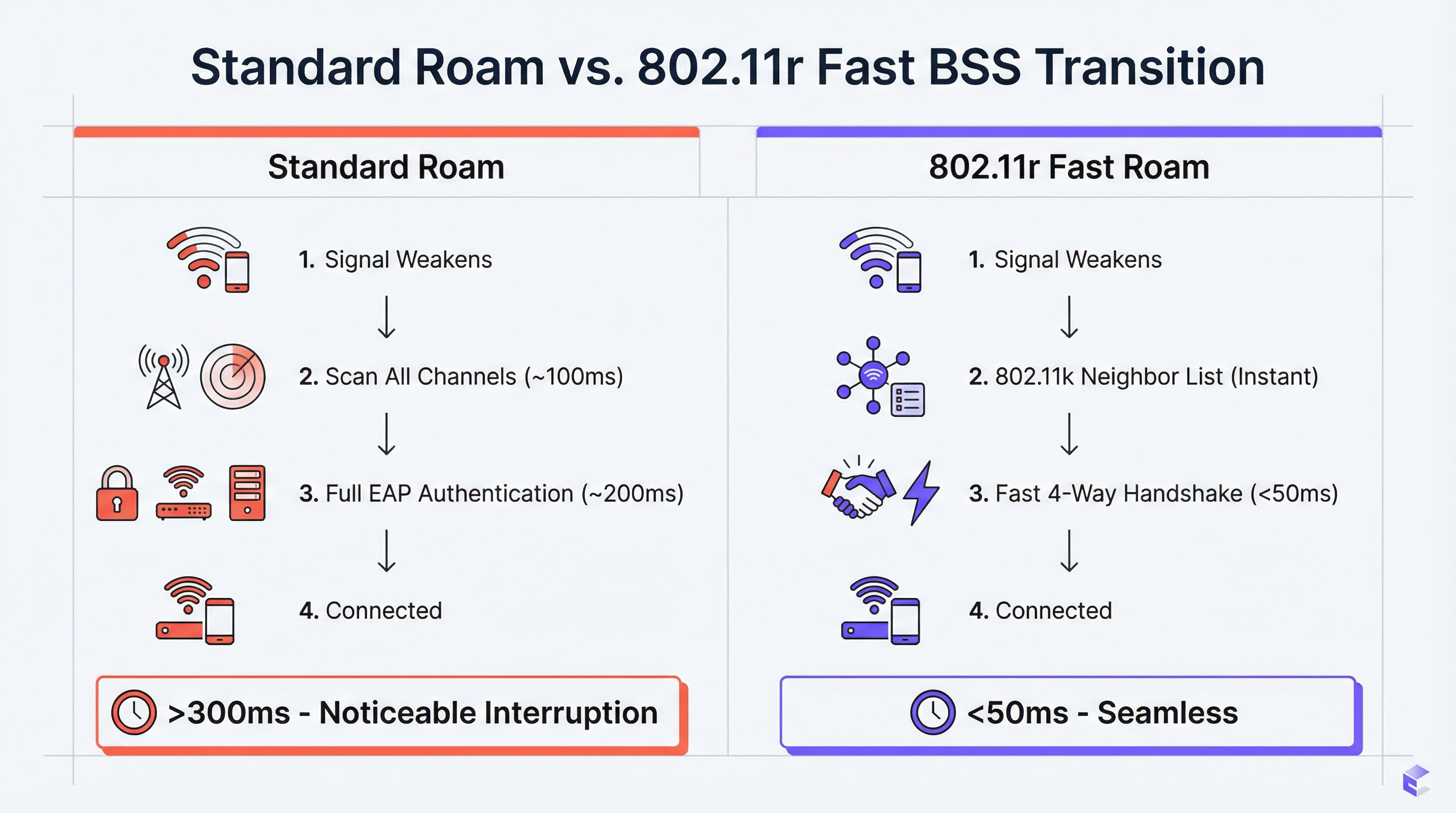
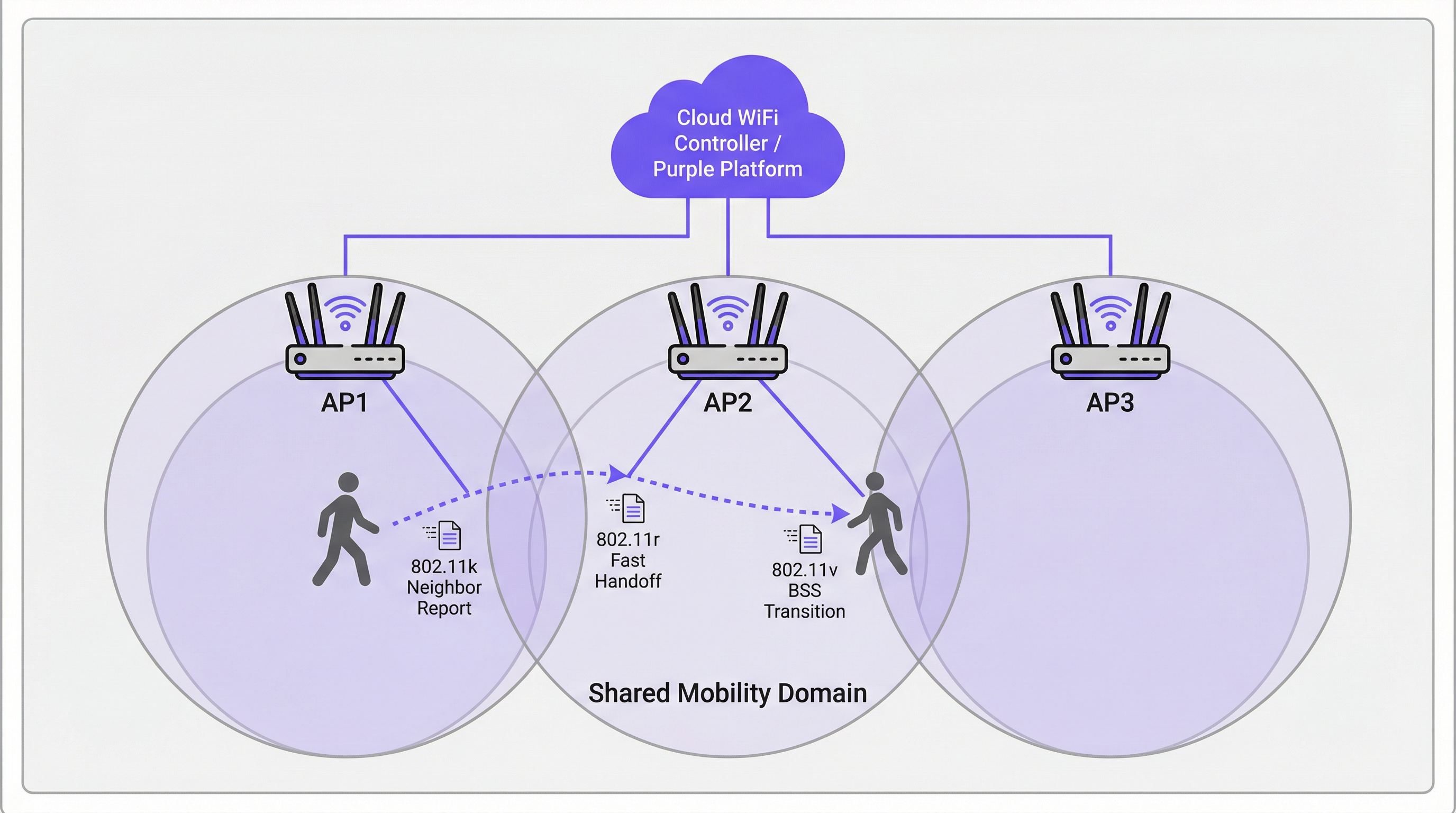
For enterprise venues — hotels, retail chains, stadiums, conference centres — seamless WiFi is a core operational requirement. As users move through a physical space, their devices must switch between access points (APs) without dropping a connection. Poor roaming performance leads to dropped VoIP calls, stalled video streams, and frustrated users, directly impacting guest satisfaction scores and staff productivity metrics. The solution lies in three complementary IEEE 802.11 amendments: 802.11k, 802.11v, and 802.11r. Together, they form a roaming assistance framework that gives client devices the intelligence to make faster, smarter handoff decisions and gives the network the tools to actively guide those decisions. 802.11k provides a curated list of candidate APs, eliminating time-consuming channel scans. 802.11r (Fast BSS Transition) compresses the re-authentication handshake from 200–300 ms to under 50 ms. 802.11v enables the network to proactively steer clients for load-balancing purposes. Implementing these standards correctly — alongside a properly architected guest WiFi platform — is the definitive path to a mobile, high-performance wireless experience that modern enterprise environments demand.
Technical Deep-Dive
The Challenge: Slow Roaming and the Sticky Client Problem
In a standard WiFi deployment without roaming assistance, the client device is solely responsible for deciding when to roam. The typical outcome is that devices hold on to their current AP far longer than is optimal, even when a significantly stronger signal is available from a nearby AP. This is the sticky client problem, and it is endemic in enterprise environments where a mix of device types — smartphones, laptops, IoT sensors, handheld scanners — each implement their own roaming algorithms with varying degrees of sophistication.
When the client finally decides to roam, it must complete a full re-authentication cycle with the new AP. In a WPA2-Enterprise or WPA3-Enterprise network, this involves multiple EAP (Extensible Authentication Protocol) round trips between the client, the AP, and a back-end RADIUS server. This process can consume 200–400 milliseconds. For real-time applications — VoIP, video conferencing, mobile point-of-sale — this latency is unacceptable. The result is dropped calls, frozen video frames, and failed transactions.
802.11k: Radio Resource Management and Neighbor Reports
The 802.11k amendment introduces Radio Resource Management (RRM), a framework that allows APs and clients to exchange information about the RF environment. The most operationally significant feature is the Neighbor Report. An 802.11k-capable AP can respond to a client's request with a structured list of neighboring APs, including their BSSIDs, operating channels, and signal characteristics. This eliminates the need for the client to perform a passive or active scan across all available channels — a process that can itself take 100 ms or more on a multi-band network.
The practical effect is that a client approaching the edge of an AP's coverage zone already has a ranked list of handoff candidates before it needs to roam. The decision is made with full information, not through a slow, blind search.
802.11r: Fast BSS Transition (FT)
802.11r is the cornerstone of fast roaming. Its primary innovation is the pre-distribution of key material across APs within a defined Mobility Domain. When a client first authenticates to an 802.11r-enabled network, it establishes a Pairwise Master Key (PMK) through the standard EAP process. With FT enabled, a derivative of this key — the PMK-R1 — is pre-distributed to all APs in the Mobility Domain via the controller or distribution system.
When the client roams to a new AP, instead of initiating a full EAP exchange, it performs a compressed 4-way handshake using the pre-shared PMK-R1. This reduces the handoff authentication time to under 50 milliseconds — the critical threshold below which a roam is imperceptible to the end user during a voice or video session.
802.11r supports two operational modes. FT over-the-Air has the client communicate directly with the target AP during the handoff, which is simpler and the recommended approach for most deployments. FT over-the-DS (Distribution System) routes the FT frames through the wired network via the current AP, which can be useful in specific controller architectures but adds complexity.
802.11v: BSS Transition Management
Where 802.11k is reactive (providing information when the client asks) and 802.11r is transactional (speeding up the handoff), 802.11v is proactive. It allows the network to send BSS Transition Management Requests to client devices, suggesting or directing them to roam to a specific AP. This is the network's primary tool for load balancing. If an AP is approaching capacity, the controller can identify connected clients with a strong signal to a nearby, less-loaded AP and send them a transition request. The client is not obligated to comply, but well-implemented clients (modern iOS, Android, and Windows devices) will generally honour the request.
This proactive steering capability transforms the network from a passive infrastructure into an active participant in optimising the user experience across the entire venue.
How Captive Portals Interact with Roaming
A critical and frequently overlooked failure point in guest WiFi deployments is the interaction between roaming and captive portal authentication. If a guest authenticates through a captive portal on AP1 and then roams to AP2, a naive implementation will present the captive portal again, forcing re-authentication. This is a fundamental UX failure.
The correct architectural approach is to centralise session state management on the guest WiFi platform (such as Purple). Once a user authenticates, their MAC address and session token are stored centrally. When they roam, the new AP queries the central platform, which confirms the active session and bypasses the captive portal automatically. This requires the guest WiFi platform to be tightly integrated with the wireless infrastructure — a key consideration when evaluating vendor solutions.
Implementation Guide
The following steps represent a vendor-neutral deployment framework applicable to any enterprise-grade wireless infrastructure.
Step 1 — Hardware and Software Audit. Verify that your APs, wireless LAN controller (WLC) or cloud management platform, and target client devices all support 802.11k, 802.11v, and 802.11r. AP and controller support is near-universal on modern enterprise hardware (Cisco Catalyst, Aruba, Juniper Mist, Ruckus). Client support varies — verify against device specification sheets, particularly for specialist hardware like barcode scanners, medical devices, or IoT sensors.
Step 2 — Enable the Standards on the Target SSID. In your WLC or cloud dashboard, navigate to the SSID configuration and enable 802.11k (Neighbor Reports), 802.11v (BSS Transition Management), and 802.11r (Fast BSS Transition). For 802.11r, select FT over-the-Air as the default mode unless your architecture specifically requires over-the-DS.
Step 3 — Configure the Mobility Domain. Ensure all APs within the same physical roaming area are assigned to the same Mobility Domain. This is the prerequisite for FT key sharing. Verify that the management network has full connectivity between all APs in the domain.
Step 4 — Security Configuration. 802.11r delivers the greatest benefit with WPA2/WPA3-Enterprise authentication, as it is the complex EAP process that FT is designed to accelerate. For staff and corporate networks, this is non-negotiable from both a performance and a PCI DSS compliance perspective. For guest networks using a captive portal with a Pre-Shared Key (PSK), 802.11r still provides benefit but the gains are less dramatic.
Step 5 — Validate with Packet Capture. Use a WiFi analysis tool (Wireshark with a compatible 802.11 adapter, or a commercial tool like Ekahau or AirMagnet) to capture roaming events. Confirm the presence of 802.11k Neighbor Report exchanges, 802.11v BSS Transition Management frames, and the abbreviated 802.11r FT authentication sequence. Measure the time from the last data frame on the old AP to the first data frame on the new AP. Your target is consistently under 50 ms.
Step 6 — Phased Production Rollout. Once validated on a test SSID, roll out the configuration to production SSIDs in phases, starting with a single floor or zone. Monitor for client compatibility issues and escalate any anomalies before expanding to the full venue.
Best Practices
The following recommendations reflect industry-standard guidance and are applicable across vendor platforms.
Design for the Mobility Domain, not the VLAN. A common misconfiguration is defining the Mobility Domain along VLAN boundaries rather than physical roaming boundaries. A user walking between two floors should be in the same Mobility Domain even if they cross a VLAN boundary. Ensure your controller architecture supports this.
Maintain a Legacy SSID for Non-Compliant Devices. Some devices have buggy or absent 802.11r implementations. Rather than disabling FT network-wide to accommodate them, maintain a secondary SSID without FT for legacy devices. This prevents a 'race to the bottom' where the entire network's capabilities are constrained by the oldest device.
Align with Security Standards. For retail environments, ensure your wireless security configuration aligns with PCI DSS 4.0 requirements, particularly around network segmentation and encryption. For public-sector and hospitality deployments handling personal data, ensure your guest WiFi data practices comply with GDPR and relevant national data protection legislation. WPA3-Enterprise, where supported, provides the strongest security posture.
Document Your Mobility Domain Topology. Maintain an up-to-date record of which APs belong to which Mobility Domain. This is essential for troubleshooting and for onboarding new APs during infrastructure expansion.
Troubleshooting and Risk Mitigation
| Symptom | Likely Cause | Recommended Action |
|---|---|---|
| Device cannot connect after enabling 802.11r | Client has a buggy FT implementation | Disable FT on the SSID or create a legacy SSID without FT for the affected device |
| Roam times are still >100 ms despite 802.11r | APs are not in the same Mobility Domain | Verify Mobility Domain configuration on the controller; check management network connectivity between APs |
| Guest hits captive portal after every roam | Session state is not centralised | Ensure the guest WiFi platform is tracking MAC addresses and session tokens centrally across all APs |
| Sticky clients not responding to 802.11v steering | Client does not support or ignores 802.11v | Adjust AP transmit power to reduce coverage overlap, forcing the client to roam at a stronger RSSI threshold |
| Intermittent disconnections in high-density areas | Roaming loop between two APs | Adjust 802.11v transition thresholds; ensure AP placement minimises excessive coverage overlap |
ROI and Business Impact
The business case for investing in a properly configured roaming network is straightforward. In hospitality, seamless WiFi directly correlates with guest satisfaction scores. A guest whose Teams call drops in the corridor will rate the hotel's WiFi poorly, regardless of the headline speeds on the in-room connection. For retail, reliable handheld scanner connectivity translates directly to inventory accuracy and staff efficiency — a 200-store chain that eliminates scanner disconnections can recover significant labour hours annually. For conference and events, the reputational cost of a poor connectivity experience during a flagship event can far outweigh the cost of the infrastructure investment.
The measurable KPIs for a successful roaming deployment are: average roaming event duration (target: <50 ms), number of VoIP call drops per hour (target: zero), and guest WiFi satisfaction scores (tracked via post-visit surveys). A well-configured network with 802.11k, 802.11v, and 802.11r should deliver measurable improvements across all three metrics within the first month of deployment.
Key Terms & Definitions
BSS (Basic Service Set)
A fundamental building block of a WiFi network, consisting of one Access Point and all the client devices associated with it. Each BSS is identified by a unique BSSID (the AP's MAC address).
When discussing roaming, a client transitions from the BSS of its current AP to the BSS of a new AP. 'Fast BSS Transition' (802.11r) is literally a faster mechanism for executing this switch.
SSID (Service Set Identifier)
The human-readable name of a WiFi network — the name users see and select on their devices. An SSID can be broadcast by multiple APs simultaneously to create a single logical network across a large area.
For roaming to function, all APs in the roaming area must broadcast the same SSID. Users should experience a single, continuous network, not a series of separate networks named 'Hotel_WiFi_Floor1', 'Hotel_WiFi_Floor2', etc.
WPA2/WPA3-Enterprise
A WiFi security standard that authenticates each user or device individually using a RADIUS server and the EAP protocol, rather than a shared password. It is the required security method for corporate and PCI DSS-compliant networks.
802.11r provides the greatest performance benefit in Enterprise networks, as it is the complex, multi-step EAP authentication process that FT is specifically designed to accelerate.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) for network access. In a WiFi context, the AP acts as a RADIUS client, forwarding user credentials to the RADIUS server for validation.
In a standard WPA2-Enterprise roam, the client must complete a full EAP exchange with the RADIUS server for every new AP. 802.11r eliminates this requirement by pre-distributing key material, so the RADIUS server is only consulted during the initial authentication.
Pairwise Master Key (PMK)
The top-level cryptographic key in the WPA2/WPA3 security hierarchy, derived during the initial EAP authentication process between the client and the RADIUS server.
802.11r works by deriving a hierarchy of keys from the PMK. A derivative key (PMK-R1) is pre-distributed to APs in the Mobility Domain, allowing a roaming client to perform a fast handshake without re-deriving the PMK from scratch.
Mobility Domain
A set of APs, managed by the same controller or cloud platform, that are configured to share Fast Transition key material and allow seamless 802.11r roaming between them.
This is the foundational configuration element for 802.11r. If two APs are not in the same Mobility Domain, a client roaming between them will fall back to a full, slow re-authentication. Correctly defining Mobility Domain boundaries is the most critical implementation step.
Sticky Client
A wireless client device that fails to roam to a nearby AP with a significantly stronger signal, instead maintaining its association with a distant AP with a weak signal, resulting in degraded throughput and increased latency.
This is the primary user-experience problem that 802.11k and 802.11v are designed to address. 802.11k gives the client better information; 802.11v gives the network the ability to actively encourage the client to move.
Captive Portal
A web page that intercepts a user's initial HTTP request and redirects them to an authentication or registration page before granting full network access. Widely used in hospitality, retail, and public WiFi deployments.
A poorly architected captive portal will re-present itself every time a user roams to a new AP, breaking the seamless experience. The solution is centralised session management on the guest WiFi platform, which recognises authenticated users by their MAC address across all APs.
EAP (Extensible Authentication Protocol)
An authentication framework used in WPA2/WPA3-Enterprise networks. It supports multiple authentication methods (EAP-TLS, PEAP, EAP-TTLS) and involves a multi-step exchange between the client, the AP, and a RADIUS server.
The EAP exchange is the primary source of latency in a standard WiFi roam. 802.11r is specifically designed to bypass the need to repeat this exchange on every roam, replacing it with a much faster 4-way handshake.
Case Studies
A 500-room luxury hotel is experiencing guest complaints of dropped WiFi calls and poor connectivity in hallways and common areas. Their infrastructure consists of enterprise-grade APs from a major vendor, but roaming assistance is not configured. How would you design and implement a solution?
Phase 1 — Baseline Assessment. Conduct a site survey to confirm RF coverage and identify roaming boundaries. Use a WiFi analyser to benchmark current roaming performance. Capture packet traces in the problem corridors to measure actual handoff times. Expect to find values of 200–400 ms, confirming the slow re-authentication hypothesis.
Phase 2 — Pilot Configuration. On the hotel's Wireless LAN Controller, create a test SSID (e.g., 'HotelGuest_FT_Test'). Enable 802.11k (Neighbor Reports), 802.11v (BSS Transition Management), and 802.11r (Fast BSS Transition, over-the-Air mode) on this SSID. Set security to WPA2-Enterprise, integrating with the hotel's existing RADIUS infrastructure. Assign all APs in the pilot zone to the same Mobility Domain.
Phase 3 — Validation. Using a modern smartphone (iOS 14+ or Android 10+), connect to the test SSID and initiate a VoIP call. Walk through the previously identified problem areas. The call should remain clear and uninterrupted. Capture packets to confirm handoff times are now consistently below 50 ms.
Phase 4 — Production Rollout. Apply the configuration to the primary guest and staff SSIDs in a phased rollout, floor by floor. Monitor for client compatibility issues. Communicate the changes to the IT team and set up alerting on the management platform for any roaming anomalies.
A large retail chain wants to deploy handheld inventory scanners across its 200 stores. The scanners must maintain a persistent, low-latency connection to the central inventory management system as employees move throughout stockrooms and sales floors. What are the critical WiFi configuration requirements, and what are the key risks?
Step 1 — Device Procurement Requirement. The absolute first step is to mandate 802.11r, 802.11k, and 802.11v support as a non-negotiable requirement in the scanner procurement specification. This must be confirmed against the manufacturer's data sheet, not assumed. Failure to do this at the procurement stage is the single most common cause of project failure in IoT and specialist device deployments.
Step 2 — Dedicated SSID Architecture. Create a dedicated, hidden SSID for the scanners. This network should be configured for WPA2/WPA3-Enterprise with certificate-based authentication (EAP-TLS) using device certificates provisioned during the scanner build process. This eliminates password management overhead and provides a strong, auditable security posture aligned with PCI DSS requirements for retail networks.
Step 3 — Enable Fast Roaming. On the dedicated SSID, enable 802.11k, 802.11v, and 802.11r. Define a Mobility Domain that encompasses all APs in each store.
Step 4 — QoS Configuration. Implement Quality of Service (QoS) policies to prioritise scanner traffic (DSCP marking) over less critical traffic such as the guest WiFi network. This ensures inventory data is always given network precedence during periods of congestion.
Step 5 — Centralised Management and Monitoring. Deploy a cloud management platform that provides a single-pane-of-glass view across all 200 stores. Configure alerting for roaming failures and AP health events. This allows the central IT team to identify and remediate issues without dispatching on-site engineers.
Scenario Analysis
Q1. You are designing the WiFi for a new conference centre. The main auditorium will host 2,000 concurrent users during keynote sessions, while 20 breakout rooms need reliable connectivity for video conferencing. The AV team will be using wireless microphone systems and tablet-based presentation controllers. Which roaming standard is the single most critical to enable on the AV and staff SSID, and why?
💡 Hint:Consider the latency tolerance of the applications being used by the AV team and presenters.
Show Recommended Approach
802.11r (Fast BSS Transition) is the most critical standard for the AV and staff SSID. The AV team and presenters are running latency-sensitive, real-time applications — wireless microphone control, tablet presentation software, and video feeds — where any interruption is immediately visible to the audience. 802.11k and 802.11v are important supporting standards that help the client make better roaming decisions, but the raw speed of the handoff (the domain of 802.11r) is the primary determinant of whether a roam is noticeable. The target is consistently under 50 ms. For the general attendee SSID, all three standards should be enabled, but 802.11v's load-balancing capability becomes particularly valuable for managing 2,000 concurrent users across the auditorium's AP array.
Q2. A hotel guest complains that their WiFi is slow in their room, despite showing full signal bars on their device. A quick check on the controller shows the guest is connected to an AP two floors below them at a high RSSI, rather than the AP directly above their room. What is the technical term for this condition, and which standard is designed to address it?
💡 Hint:The problem is not signal strength — the device has a strong signal. The problem is which AP it has chosen to associate with.
Show Recommended Approach
This is the classic sticky client problem. The guest's device has associated with a distant AP that happens to have a strong signal (perhaps due to building geometry or AP placement) and is refusing to roam to the closer, more appropriate AP. The standard designed to address this is 802.11v (BSS Transition Management). With 802.11v enabled, the network controller can detect this suboptimal association — the guest is connected to an AP two floors away when a perfectly capable AP is directly above them — and send a BSS Transition Management Request to the client, suggesting it roam to the more appropriate AP. A well-implemented client (modern iOS, Android, Windows) will honour this request.
Q3. An IT administrator enables 802.11r on a hospital's staff WiFi network. Within hours, the helpdesk receives calls from nurses whose older mobile clinical workstations can no longer connect to the network at all. The workstations are running a legacy operating system and were purchased five years ago. What is the most likely cause, and what is the safest remediation strategy that does not require disabling 802.11r for all users?
💡 Hint:The problem is specific to the older devices. The solution should be targeted at those devices, not the entire network.
Show Recommended Approach
The most likely cause is that the legacy clinical workstations have a buggy or absent implementation of 802.11r. Some older devices fail to correctly negotiate the FT capability during the association process, resulting in a connection failure rather than a graceful fallback to standard authentication. The safest remediation strategy is SSID segmentation. Create a secondary staff SSID (e.g., 'ClinicalStaff_Legacy') with 802.11r disabled but 802.11k and 802.11v still enabled. Configure the legacy workstations to connect to this SSID. The primary staff SSID retains 802.11r for all modern devices. This approach avoids a 'race to the bottom' where the entire network's capabilities are constrained by the oldest device, while ensuring the legacy workstations remain operational. The long-term recommendation is to include 802.11r support as a mandatory requirement in the next device refresh cycle.
Key Takeaways
- ✓Seamless WiFi roaming is a critical operational requirement for enterprise venues — poor handoff performance directly impacts guest satisfaction and staff productivity.
- ✓802.11k eliminates slow channel scanning by providing client devices with a curated Neighbor Report of candidate APs before they need to roam.
- ✓802.11r (Fast BSS Transition) is the most impactful standard, reducing AP handoff authentication time from 200–400 ms to under 50 ms by pre-distributing cryptographic key material across the Mobility Domain.
- ✓802.11v enables the network to proactively steer sticky clients to better APs for load balancing, transforming the network from a passive infrastructure into an active participant in optimising user experience.
- ✓Client device compatibility is the most common deployment risk — always verify 802.11r/k/v support against device specification sheets at the procurement stage, not after purchase.
- ✓Captive portals must be backed by centralised session management to prevent re-authentication on every roam — this is a platform architecture requirement, not just a configuration setting.
- ✓Validate every deployment with packet captures measuring actual handoff duration; the target benchmark is consistently under 50 milliseconds.



