Solução de problemas de conectividade de internet no Windows 11 após atualização
This guide provides a definitive technical reference for IT leaders on resolving Windows 11 upgrade-related internet connectivity failures caused by the removal of 802.1X wired authentication settings. It delivers a step-by-step troubleshooting and remediation process, covering Group Policy, Microsoft Intune, and manual recovery methods, alongside preventative measures and ROI analysis to ensure stable, compliant network access across enterprise environments.
🎧 Listen to this Guide
View Transcript

Resumo Executivo
A transição para o Windows 11, embora ofereça melhorias significativas de segurança e produtividade, introduziu um problema operacional crítico para ambientes de rede corporativos: a exclusão silenciosa das configurações de autenticação com fio 802.1X durante atualizações in-place. Para gerentes de TI, arquitetos de rede e CTOs que supervisionam grandes parques de dispositivos em hotéis, redes de varejo, estádios, centros de conferências e organizações do setor público, isso se traduz diretamente em perda de produtividade, custos elevados de suporte e potencial exposição de conformidade. A causa raiz é a corrupção ou remoção completa de perfis de configuração XML essenciais para o serviço Configuração Automática de Rede com Fio (dot3svc), deixando os dispositivos incapazes de realizar o controle de acesso à rede baseado em porta, conforme definido pelo IEEE 802.1X. Este guia fornece uma metodologia oficial e passo a passo para diagnosticar, restaurar e prevenir esse problema. Abordamos os fundamentos técnicos da falha, os três principais caminhos de correção — Política de Grupo (Group Policy), Microsoft Intune e importação manual de perfil XML — e uma estrutura para criar resiliência em futuros ciclos de implantação de SO. Também analisamos o impacto nos negócios e o ROI de uma estratégia proativa de gerenciamento 802.1X, com referência às obrigações de conformidade do PCI DSS, ISO 27001 e GDPR.
Análise Técnica Aprofundada
O cerne do problema reside em como o processo de atualização in-place do Windows 11 lida com os perfis de configuração de rede. O serviço Configuração Automática de Rede com Fio (dot3svc) é o serviço do Windows responsável por gerenciar a autenticação IEEE 802.1X em interfaces Ethernet. Quando uma máquina se conecta a uma porta de switch, esse serviço lê um perfil XML armazenado para iniciar o handshake de autenticação, usando protocolos como EAP-TLS ou PEAP-MSCHAPv2. O processo de atualização — particularmente o ciclo de atualização de recursos da 23H2 para a 25H2 — pode corromper esse perfil ou redefinir totalmente as dependências do serviço, deixando efetivamente o dispositivo sem a configuração necessária para autenticar. O resultado é que a porta do switch, configurada para impor o 802.1X, nega o acesso, muitas vezes direcionando o dispositivo para uma VLAN de convidados restrita ou bloqueando o tráfego completamente.
Este não é um problema de driver ou de compatibilidade de hardware. É a perda do perfil de configuração específico que dita o método de autenticação, a confiança do servidor e a identidade do cliente. A distinção é importante porque muda completamente a abordagem de solução de problemas. Um administrador pode verificar o problema executando netsh lan show profiles em um prompt de comando elevado. Se o perfil esperado estiver ausente, a causa raiz é confirmada. Para uma análise mais profunda, o Visualizador de Eventos do Windows fornece dados de diagnóstico explícitos em Logs de Aplicativos e Serviços > Microsoft > Windows > Wired-AutoConfig > Operacional, onde as falhas de autenticação são registradas com códigos de erro e descrições específicas.
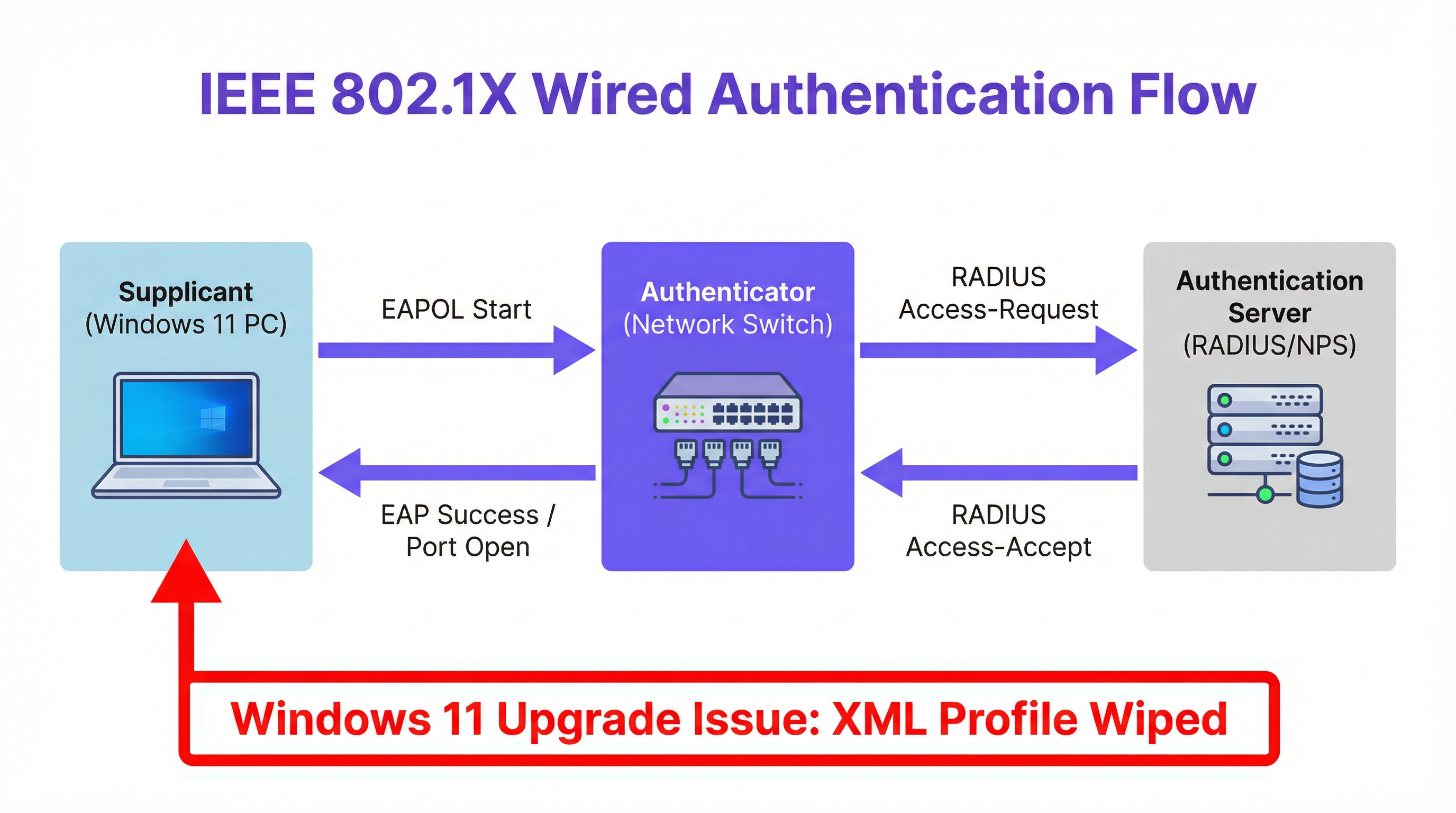
O fluxo de autenticação em si segue o modelo padrão 802.1X. O dispositivo Windows atua como o suplicante (supplicant), iniciando uma mensagem de início EAPOL (EAP over LAN) para o switch. O switch, atuando como o autenticador, encaminha a solicitação para um servidor RADIUS central (como Microsoft NPS ou Cisco ISE). O servidor RADIUS valida as credenciais — seja um certificado, nome de usuário e senha, ou identidade da máquina — e retorna uma resposta Access-Accept (Acesso Aceito) ou Access-Reject (Acesso Rejeitado). O switch então abre ou fecha a porta de acordo. Quando o perfil XML está ausente, o suplicante nunca inicia esse handshake, e a porta permanece em um estado não autorizado.
Guia de Implementação
A resolução da falha de autenticação 802.1X pós-atualização envolve três métodos principais, selecionados com base na infraestrutura de gerenciamento da organização.
Método 1: Correção via Política de Grupo (GPO). Para dispositivos ingressados no domínio em um ambiente tradicional do Active Directory, a solução mais escalável é impor as configurações 802.1X via GPO. Navegue até Configuração do Computador > Políticas > Configurações do Windows > Configurações de Segurança > Políticas de Rede com Fio (IEEE 802.3). Crie uma nova política, especificando o tipo de EAP — por exemplo, Microsoft: Protected EAP (PEAP) — e defina suas propriedades, incluindo autoridades de certificação raiz confiáveis e o método de autenticação interno (por exemplo, EAP-MSCHAP v2). Essa política reaplicará automaticamente as configurações corretas a todas as máquinas de destino no próximo ciclo de atualização da Política de Grupo, normalmente em 90 minutos ou no próximo logon. A etapa crítica de verificação é executar gpresult /r em uma máquina de destino para confirmar se a política está sendo aplicada corretamente.
Método 2: Implantação via Microsoft Intune. Para endpoints modernos gerenciados na nuvem, crie um Perfil de Configuração no centro de administração do Intune para Windows 10 e posterior, selecionando o modelo Rede com fio (Wired network). A abordagem mais eficiente é primeiro exportar o perfil 802.1X funcional de uma máquina de referência configurada corretamente usando netsh lan export profile folder=. interface="Ethernet". Isso gera um arquivo XML que pode ser importado diretamente para o campo EAP XML do perfil do Intune. Atribua o perfil ao grupo de dispositivos relevante do Azure AD. O Intune enviará a configuração na próxima sincronização do dispositivo, restaurando as configurações de autenticação sem nenhuma intervenção manual no endpoint.
Método 3: Importação Manual de Perfil XML. Para dispositivos autônomos ou correções urgentes e pontuais, a configuração pode ser restaurada manualmente. Em uma máquina funcional, exporte o perfil 802.1X em funcionamento: netsh lan export profile folder=C:\temp interface="Ethernet". Transfira o arquivo XML resultante para a máquina afetada e importe-o: netsh lan add profile filename="C:\temp\SeuPerfil.xml" interface="Ethernet". Reconecte o cabo de rede para acionar o processo de autenticação. Este método fornece uma correção imediata, mas não é escalável e deve ser tratado apenas como uma medida tática.
Melhores Práticas
Para gerenciar e mitigar proativamente o risco de perda de configuração 802.1X, as equipes de TI devem adotar uma estratégia em várias camadas baseada nas melhores práticas de gerenciamento de configuração.
Incorpore a Configuração 802.1X à Build Padrão. Seja usando MDT, SCCM ou Windows Autopilot, a imagem de linha de base ou o processo de provisionamento deve incluir a implantação do perfil de rede com fio. Isso estabelece o estado correto desde o provisionamento inicial, reduzindo a superfície para falhas relacionadas a atualizações.
Aproveite o Gerenciamento Centralizado para Imposição. Não dependa de endpoints configurados manualmente. Use GPOs ou perfis do Intune como a única fonte de verdade para as configurações de rede. Isso garante que, mesmo que uma atualização remova a configuração local, ela seja restaurada automaticamente no próximo ciclo de atualização da política. Isso está alinhado com os princípios de gerenciamento de configuração da ITIL e com o controle A.12.1.2 do Anexo A da ISO 27001 (Gerenciamento de Mudanças).
Implemente Verificações Pré e Pós-Atualização em Sequências de Tarefas. Antes de iniciar uma grande atualização de SO via SCCM ou MDT, inclua uma etapa de script para exportar e fazer backup do perfil 802.1X atual para um compartilhamento de rede. A fase pós-atualização da sequência de tarefas deve incluir uma etapa de verificação que checa a presença do perfil e, se ausente, o restaura a partir do backup. Essa abordagem de dupla segurança fornece uma rede de proteção independente da política de gerenciamento central.
Mantenha um Repositório de Perfis com Controle de Versão. Mantenha um repositório centralizado e com controle de versão de perfis XML 802.1X mestres para diferentes sites, níveis de segurança e ambientes de rede. Isso é inestimável para uma rápida recuperação de desastres e garante a consistência em todo o parque, um requisito fundamental para a conformidade com o PCI DSS e as obrigações de segurança de dados do GDPR.
Solução de Problemas e Mitigação de Riscos
Quando um endpoint falha ao se conectar após uma atualização do Windows 11, o processo de solução de problemas deve ser sistemático e baseado em evidências.
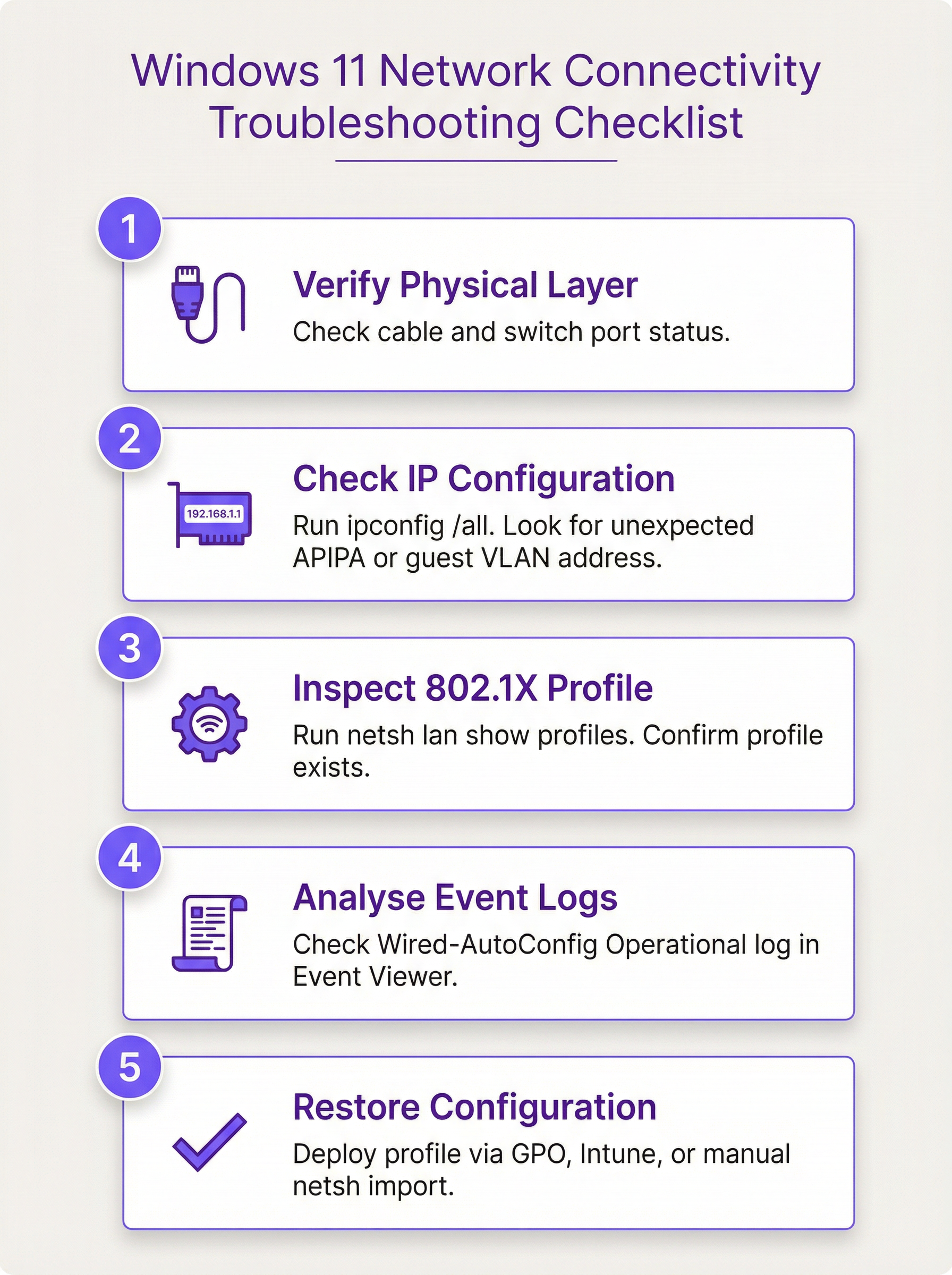
Passo 1 — Verifique a Camada Física. Confirme se o cabo Ethernet está conectado e se a porta do switch está ativa. Verifique as luzes de link da placa de rede (NIC).
Passo 2 — Verifique a Configuração de IP. Execute ipconfig /all. Determine se o dispositivo está recebendo um endereço IP da VLAN esperada. Um endereço APIPA (169.254.x.x) indica uma falha completa na obtenção de um IP, sugerindo que a porta está totalmente bloqueada. Um IP de uma sub-rede inesperada pode indicar que o dispositivo foi colocado em uma VLAN de convidados devido a uma falha de autenticação.
Passo 3 — Inspecione o Perfil 802.1X. Execute netsh lan show profiles. Se o perfil esperado estiver ausente, a atualização o removeu. Se estiver presente, mas a autenticação ainda estiver falhando, o perfil pode estar corrompido ou a cadeia de certificados pode estar quebrada.
Passo 4 — Analise os Logs de Eventos. Abra o Visualizador de Eventos e navegue até Logs de Aplicativos e Serviços > Microsoft > Windows > Wired-AutoConfig > Operacional. Procure por eventos de erro no momento da tentativa de conexão. Esses logs fornecem motivos explícitos de falha, como "A identidade do servidor de autenticação não pôde ser verificada" (indicando um problema de confiança de certificado) ou "A autenticação EAP falhou" (indicando uma incompatibilidade de credencial ou método).
Passo 5 — Restaure a Configuração. Com base no diagnóstico, aplique o método de correção apropriado: GPO, Intune ou importação manual de XML.
Do ponto de vista da mitigação de riscos, a chave é a automação e a imposição. Um perfil 802.1X configurado manualmente é um ponto único de falha. Uma política imposta centralmente é um controle de autocorreção. O risco operacional de depender de configurações manuais é agravado em grandes parques onde centenas de dispositivos podem ser atualizados simultaneamente. Um único GPO ou perfil do Intune, configurado e testado corretamente, elimina esse risco em escala.
ROI e Impacto nos Negócios
O impacto nos negócios de uma perda generalizada de conectividade após uma atualização do Windows 11 pode ser severo, variando desde a perda de produtividade da equipe até a perda direta de receita em ambientes onde o acesso à rede é operacionalmente crítico. O ROI da implementação de uma estratégia centralizada de gerenciamento 802.1X é medido em três dimensões: redução de custos de suporte, mitigação de riscos de conformidade e melhoria da resiliência operacional.
Redução de Custos de Suporte. Considere um parque corporativo de 1.000 dispositivos onde 15% dos dispositivos perdem a conectividade após um ciclo de atualização noturno. Cada incidente requer 30 minutos de tempo de suporte de TI para ser resolvido manualmente. A um custo de £ 60 por hora para um técnico de Nível 2, este único evento custa à organização £ 4.500 em suporte reativo. Em contraste, criar e implantar um GPO ou perfil do Intune requer aproximadamente 4 horas de tempo de um arquiteto (£ 240). O ROI é percebido integralmente durante o primeiro incidente evitado, com cada ciclo de atualização subsequente entregando a mesma economia.
Mitigação de Riscos de Conformidade. O Requisito 1.2.1 do PCI DSS exige a restrição do tráfego entre o ambiente de dados do titular do cartão e outras redes. O 802.1X é um controle primário para impor essa segmentação de rede. Se os dispositivos perderem sua configuração de autenticação e caírem em uma rede não segmentada, a organização pode violar esse requisito, expondo-se a multas, constatações de auditoria e danos à reputação. Uma estratégia de gerenciamento 802.1X centralizada e resiliente mitiga diretamente esse risco. Da mesma forma, o Artigo 32 do GDPR exige medidas técnicas apropriadas para garantir a segurança da rede; uma política de autenticação de autocorreção é um controle demonstrável.
Resiliência Operacional. Para operadores de locais — hotéis, centros de conferências, estádios — a conectividade de rede está diretamente ligada às operações que geram receita. O sistema de gerenciamento de propriedades de um hotel, a infraestrutura audiovisual de um centro de conferências e os sistemas de bilheteria e ponto de venda de um estádio dependem de um acesso à rede confiável e autenticado. O custo do tempo de inatividade nesses ambientes excede em muito o custo de implementação de uma estratégia de gerenciamento robusta. O gerenciamento proativo do 802.1X é, neste contexto, um investimento direto na continuidade operacional.
Key Terms & Definitions
IEEE 802.1X
An IEEE standard for Port-Based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, ensuring that only authorised devices can access network resources.
When IT teams need to prevent unauthorised devices from connecting to wired or wireless networks, they implement 802.1X. It is the primary gatekeeper for corporate network access and is a key control for PCI DSS network segmentation requirements.
Wired AutoConfig (dot3svc)
The Microsoft Windows service responsible for performing IEEE 802.1X authentication on Ethernet interfaces. It reads from a stored XML profile to initiate and manage the authentication handshake with the network switch.
This is the specific service that is disrupted during the Windows 11 upgrade. If this service is not running or its XML profile is missing, wired 802.1X authentication will fail silently. It is the primary focus of troubleshooting for this issue.
EAP (Extensible Authentication Protocol)
An authentication framework that provides a common set of functions and a negotiation mechanism for authentication methods, known as EAP methods. It is used within 802.1X to define how clients and servers exchange credentials.
When configuring 802.1X, IT teams must choose an EAP method. The choice determines the security level and infrastructure requirements: EAP-TLS requires a certificate infrastructure (PKI), while PEAP-MSCHAPv2 uses username and password credentials.
PEAP-MSCHAPv2
Protected Extensible Authentication Protocol with Microsoft Challenge-Handshake Authentication Protocol version 2. A widely deployed EAP method that creates a TLS tunnel to protect the authentication exchange and then authenticates the client using a username and password.
This is one of the most common authentication methods for 802.1X in enterprise environments. It is simpler to deploy than certificate-based EAP-TLS as it does not require client certificates. The Windows 11 upgrade issue affects all EAP types, including PEAP-MSCHAPv2.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users and devices connecting to a network. In an 802.1X deployment, the network switch forwards authentication requests to the RADIUS server.
The RADIUS server is the central authority that validates credentials and grants or denies access. Common implementations include Microsoft NPS (Network Policy Server) and Cisco ISE. When the 802.1X profile is missing, the RADIUS server is never even contacted.
Group Policy (GPO)
A feature of Microsoft Windows that provides centralised management and configuration of operating systems, applications, and user settings in an Active Directory environment.
For on-premises, domain-joined Windows devices, GPOs are the standard method for deploying and enforcing security settings, including 802.1X configurations. A correctly configured Wired Network GPO will re-apply the 802.1X profile even if an upgrade removes it locally.
Microsoft Intune
A Microsoft cloud-based unified endpoint management (UEM) platform for managing mobile devices, desktop operating systems, and applications.
For modern, cloud-managed, or hybrid Azure AD-joined environments, Intune is the preferred method for deploying 802.1X profiles. It replaces the need for traditional GPOs and is essential for managing distributed, modern device estates.
VLAN (Virtual Local Area Network)
A logical overlay network that groups together a set of devices from different physical LAN segments, creating an isolated broadcast domain independent of physical location.
802.1X is frequently used to dynamically assign devices to specific VLANs based on their authenticated identity. When the 802.1X configuration is wiped, this dynamic assignment fails, and the device may be placed in a restricted guest VLAN or denied access entirely, which is the symptom most commonly reported by end users.
EAPOL (EAP over LAN)
An encapsulation protocol defined in IEEE 802.1X that carries EAP messages over an IEEE 802 network, such as Ethernet or Wi-Fi.
EAPOL is the mechanism by which the supplicant (the Windows device) initiates the 802.1X authentication process with the switch. The first message sent is an EAPOL-Start frame. When the dot3svc XML profile is missing, this initial frame is never sent.
Case Studies
A multi-site retail chain with 500 stores is preparing to upgrade its POS terminals and back-office PCs to Windows 11. Each store uses 802.1X with PEAP-MSCHAPv2 to secure wired access and segment payment processing traffic from general corporate traffic, as required by PCI DSS. How can the IT Director prevent mass connectivity outages during the phased rollout?
The IT Director should leverage Microsoft Intune for centralised management across the distributed estate. Step 1: Create a Master Configuration Profile. On a reference Windows 11 device, manually configure and test the 802.1X settings for a store environment. Export this configuration to an XML file using netsh lan export profile folder=C:\temp interface="Ethernet". Step 2: Build an Intune Profile. In the Intune admin centre, create a new Configuration Profile for Windows 10 and later, using the 'Wired network' template. Import the XML file from Step 1 into the EAP XML field of this profile. Step 3: Define Dynamic Device Groups. Create Azure AD dynamic device groups that automatically populate based on device properties, such as a naming convention specific to POS terminals (e.g., devices with names matching 'POS-*'). This enables targeted, role-based policy application. Step 4: Phased Deployment. Assign the Intune profile to a pilot group of non-critical back-office devices in a single region first. Monitor their upgrade process and connectivity status via Intune's endpoint analytics and device compliance reports. Once validated over a 48-hour observation window, expand the assignment to POS terminals and then to the broader estate in a region-by-region rollout. This ensures that even if the upgrade process removes the local profile, Intune will enforce its re-application on the next sync, guaranteeing seamless connectivity and maintaining PCI DSS network segmentation controls.
A large conference centre hosts multiple concurrent events, each requiring a secure, isolated network for organisers and exhibitors. The on-site IT team uses dynamic VLAN assignment via 802.1X based on user credentials managed in Microsoft NPS. After a Windows 11 feature update deployed overnight, an event organiser's laptop can no longer access the organiser network or the shared file server. The event begins in two hours. How should the on-site technician resolve this?
For an immediate, tactical fix in a time-sensitive business environment, the technician should use the manual XML profile import method. Step 1: Obtain a Working Profile. The technician should use their own correctly configured laptop or a reference device to export the 802.1X profile for the organiser network. Command: netsh lan export profile folder=C:\temp interface="Ethernet". This creates an XML file containing the full authentication configuration. Step 2: Transfer the Profile. The XML file should be transferred to the organiser's laptop via a USB drive, as the organiser's device currently has no access to network shares. Step 3: Import the Profile. On the organiser's laptop, open an administrative Command Prompt and run: netsh lan add profile filename="C:\temp\Wired_Organiser_Profile.xml" interface="Ethernet". Step 4: Verify Connectivity. Disconnect and reconnect the Ethernet cable to trigger the 802.1X authentication process. The device should authenticate successfully and be placed in the correct VLAN, restoring access to the file server. Step 5: Document and Escalate. The technician must document this one-off fix in the IT service management system and raise a change request for the central IT architecture team to deploy a permanent Intune or GPO-based solution, preventing recurrence for other users and future events.
Scenario Analysis
Q1. You are the CTO of a large hotel group with 3,000 staff devices across 45 properties. A scheduled overnight Windows 11 feature update has been deployed to all devices. The following morning, your helpdesk receives 200 tickets reporting that back-office PCs cannot access the property management system or internal file shares. All devices are domain-joined and managed via SCCM. What is your immediate response plan and your long-term remediation strategy?
💡 Hint:Consider both the immediate operational impact — getting the hotel properties functional — and the root cause, which is a systemic configuration management gap. Your response must address both.
Show Recommended Approach
Immediate response: Declare a P1 incident and convene a bridge call with the network architecture and endpoint management teams. The priority is to identify the fastest path to restoring connectivity at scale. Given that devices are domain-joined and managed via SCCM, the fastest scalable fix is to create a Wired Network GPO immediately, deploying the correct 802.1X settings to all affected OUs. Force a Group Policy update on affected machines remotely using Invoke-GPUpdate via SCCM. For properties where this does not resolve the issue quickly enough, dispatch IT staff with USB drives containing the XML profile for manual import on the most critical devices (e.g., front desk and revenue management PCs). Long-term strategy: Conduct a post-incident review to understand why the 802.1X settings were not already enforced via GPO. Build the Wired Network GPO as a permanent, enforced policy. Add a post-upgrade verification step to the SCCM task sequence that checks for the profile's presence and restores it if absent. Document the master XML profiles in a version-controlled repository. Review the change management process to ensure that upgrade deployments include a validation step before full rollout.
Q2. A university campus network uses 802.1X to control access to different network segments for students, faculty, and staff. After the latest Windows 11 feature update, a professor reports they can no longer access the faculty research drive from their office. They can, however, access the public internet. What is the most likely cause, and what single command would you run first on their machine to begin your diagnosis?
💡 Hint:The user has partial connectivity — they can reach the internet but not internal resources. This is a specific pattern that points to a particular type of failure. Think about what controls access to different network segments.
Show Recommended Approach
The most likely cause is that the 802.1X authentication is failing, and the switch port is defaulting the professor's device into a restricted VLAN that has internet access but no access to internal resources such as the faculty research drive. This is a common network design pattern where the 'fail-open' state provides internet access but not internal network access. The Windows 11 update has likely wiped the specific 802.1X profile for the faculty network, so the device is not authenticating and is therefore not being placed in the faculty VLAN. The first command to run on their machine is netsh lan show profiles. If the faculty network profile is absent from the output, the root cause is confirmed. The fix is to restore the profile via the appropriate method — in a university environment, this is likely a GPO or Intune profile, or a manual import as an immediate fix.
Q3. Your organisation is migrating from a traditional on-premises Active Directory environment to a fully cloud-native Azure AD and Intune deployment. Your existing 802.1X settings are currently managed via GPO. A new regional office is being set up with Azure AD-joined devices only. How do you adapt your 802.1X deployment strategy for this new office, and what is the specific step that bridges the gap between your existing GPO configuration and the new Intune-based approach?
💡 Hint:GPOs do not apply to Azure AD-joined devices. You need to replicate the GPO's intent using a different tool. Think about what the GPO contains and how that information can be transferred.
Show Recommended Approach
The existing GPO-based strategy cannot be applied to Azure AD-joined devices, as Group Policy requires a connection to an on-premises domain controller. The correct approach is to replicate the GPO settings in Microsoft Intune. The bridging step is to export the 802.1X XML profile from an existing GPO-managed machine using netsh lan export profile folder=C:\temp interface="Ethernet". This XML file contains the exact same configuration that the GPO was deploying. In Intune, create a new Configuration Profile for Windows 10 and later, select the 'Wired network' template, and import this XML into the EAP XML field. Assign this profile to an Azure AD device group containing the machines in the new regional office. This effectively translates the on-premises GPO logic into a cloud-native Intune policy, ensuring the same level of security and configuration enforcement for the modern-managed devices. This approach also provides a clear migration path: as more sites move to Azure AD-joined devices, the same Intune profile can be extended to them, eventually replacing the GPO entirely.
Key Takeaways
- ✓Windows 11 in-place upgrades — particularly the 23H2 to 25H2 feature update cycle — can silently wipe the XML configuration profiles used by the Wired AutoConfig (dot3svc) service, causing immediate 802.1X authentication failures on wired networks.
- ✓The failure manifests as devices being placed on a restricted guest VLAN or having their switch port blocked entirely, resulting in loss of access to internal resources while potentially retaining internet access.
- ✓Diagnose the issue by running `netsh lan show profiles` (to check for the missing profile) and reviewing the Wired-AutoConfig Operational log in Windows Event Viewer (for explicit error codes).
- ✓Restore connectivity at scale using a Group Policy Wired Network policy (for domain-joined devices) or a Microsoft Intune Configuration Profile (for Azure AD-joined or hybrid devices), both of which enforce the correct settings persistently.
- ✓For urgent, one-off fixes, export the working profile from a functional machine (`netsh lan export`) and import it on the affected device (`netsh lan add profile`).
- ✓Prevent future occurrences by making 802.1X configuration part of the standard device build and enforcing it via a central policy — never rely on manually applied configurations surviving an OS upgrade.
- ✓This issue has direct compliance implications for PCI DSS (network segmentation) and ISO 27001 (configuration management); a centralised, resilient 802.1X strategy is both an operational and a compliance imperative.



