WiFi Captive Portals: O Guia Definitivo para Configuração, Segurança e Personalização
This authoritative technical reference guide covers the full lifecycle of enterprise WiFi captive portal deployment, from network architecture and security hardening to GDPR and CCPA compliance and measurable business ROI. It is designed for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and public-sector organisations who need actionable, vendor-neutral guidance to implement, secure, and optimise guest WiFi infrastructure. The guide includes step-by-step configuration instructions, real-world case studies, security checklists, compliance frameworks, and a discussion of how captive portals drive first-party data acquisition and customer analytics at scale.
🎧 Listen to this Guide
View Transcript
Resumo Executivo
Para líderes de TI em empresas com múltiplas localidades, o WiFi para visitantes não é mais uma simples comodidade; é um componente crítico da experiência do cliente e uma rica fonte de dados primários. Um Captive Portal de WiFi bem arquitetado é a chave para desbloquear esse valor, servindo como o gateway estratégico para acesso seguro, conformidade legal e marketing personalizado. Este guia fornece uma referência técnica abrangente para a implantação de Captive Portals de nível corporativo, cobrindo a arquitetura essencial, os controles de segurança e os mandatos de conformidade necessários para mitigar riscos e maximizar o ROI. Vamos além da configuração básica para abordar os desafios específicos de escala, desde o gerenciamento centralizado e a segmentação de VLAN até o registro de consentimento da GDPR e a medição do impacto nos negócios. Para o CTO, este guia oferece uma estrutura para avaliar a postura de segurança e o retorno comercial do seu parque de WiFi para visitantes. Para o gerente de TI e o arquiteto de redes, ele fornece orientações acionáveis e neutras em relação a fornecedores para implementação imediata, garantindo que sua implantação seja segura, em conformidade e capaz de entregar resultados de negócios mensuráveis.
Análise Técnica Aprofundada
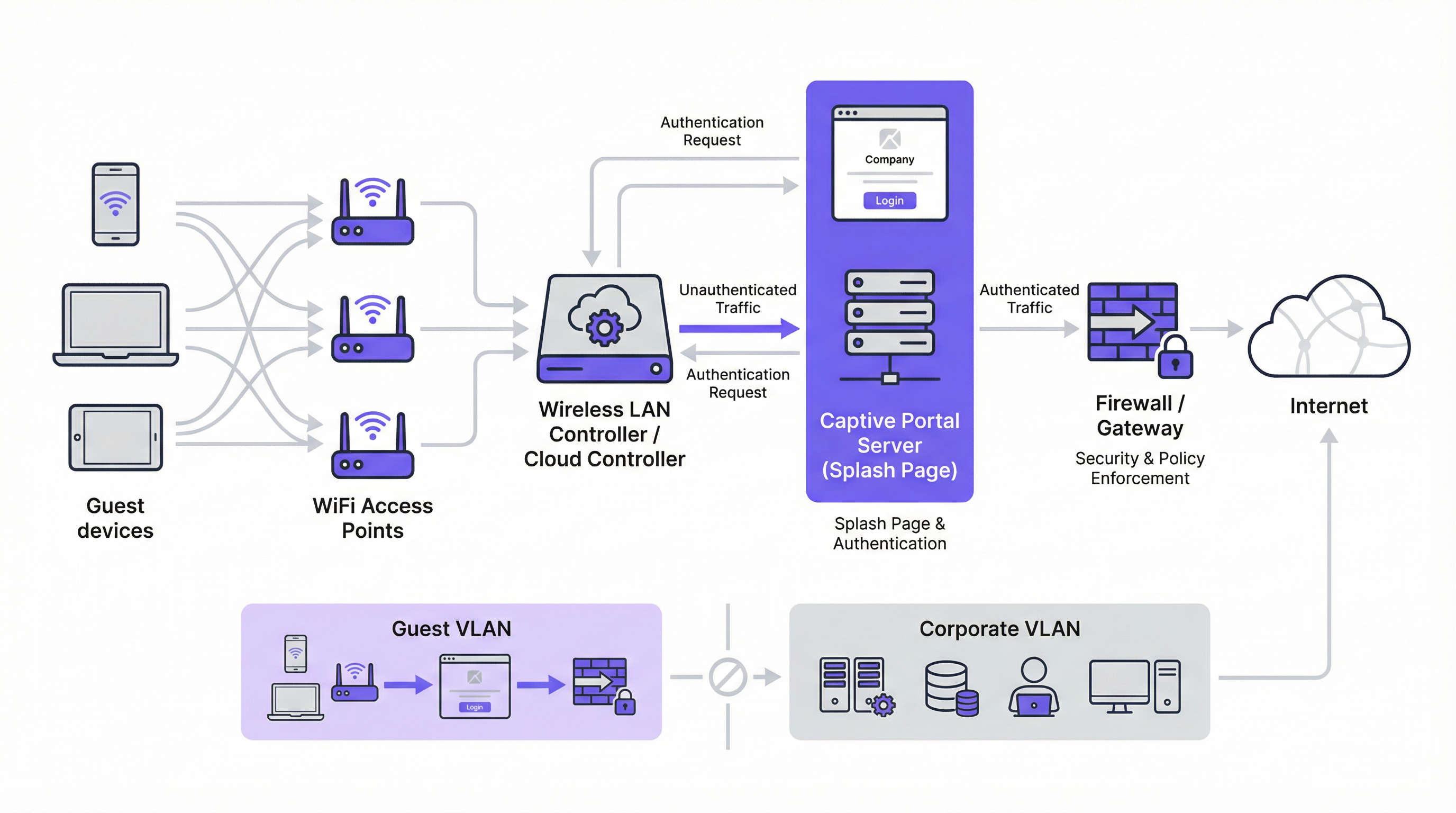
O Captive Portal moderno é um sistema sofisticado que equilibra a experiência do usuário, a segurança e os objetivos comerciais. Em sua essência, o portal intercepta a solicitação da web inicial de um usuário e o redireciona para uma splash page com a marca para autenticação ou consentimento. O mecanismo mais predominante é um redirecionamento HTTP 302. Quando um novo dispositivo se conecta ao SSID de visitantes, seu sistema operacional tenta entrar em contato com uma URL de detecção conhecida — a Apple usa captive.apple.com, o Google usa connectivitycheck.gstatic.com e a Microsoft usa www.msftconnecttest.com. O controlador sem fio da rede intercepta essa solicitação e retorna um código de status HTTP 302 (Found), direcionando o navegador do cliente para a URL do Captive Portal. Esse processo é contínuo em todos os principais sistemas operacionais e é a abordagem recomendada para implantações corporativas.
Existem dois mecanismos de redirecionamento alternativos. O redirecionamento de DNS funciona configurando o firewall para garantir que clientes não autenticados só possam acessar o resolvedor de DNS designado da rede, que, por sua vez, resolve todos os hostnames para o endereço IP do portal. Embora eficaz, essa abordagem é arquitetonicamente equivalente ao sequestro de DNS (DNS hijacking) e deve ser implementada com cuidado. O redirecionamento ICMP opera na Camada 3 para instruir alterações de roteamento no nível do pacote; é menos comum em implantações modernas e carrega riscos de segurança inerentes que o tornam inadequado para a maioria dos ambientes corporativos.
Arquitetonicamente, a base de qualquer implantação corporativa segura é a segmentação de VLAN. O tráfego de visitantes deve ser isolado logicamente da rede corporativa em sua própria Rede Local Virtual (VLAN). Isso evita qualquer possibilidade de movimento lateral de um dispositivo de visitante potencialmente comprometido para sistemas internos sensíveis, como terminais de ponto de venda, bancos de dados de RH ou servidores de arquivos corporativos. A VLAN de visitantes deve ter seu próprio escopo DHCP e uma política de firewall restritiva que bloqueie explicitamente todo o acesso aos intervalos de endereços IP privados da RFC 1918, permitindo apenas o tráfego necessário para a autenticação no portal e o subsequente acesso à internet.
Antes da autenticação, um walled garden deve ser configurado para permitir o acesso a recursos externos específicos. Isso inclui o domínio de hospedagem do portal, os endpoints da CDN que fornecem os ativos do portal e os endpoints OAuth para quaisquer provedores de login social. Um walled garden minimamente permissivo — colocando em lista de permissões (whitelisting) endpoints específicos em vez de domínios inteiros — é um controle de segurança crítico que limita a superfície de ataque pré-autenticação.
Os métodos de autenticação abrangem um amplo espectro, desde o click-through sem atrito até a integração RADIUS de alta garantia:
| Método de Autenticação | Principal Caso de Uso | Consideração Principal |
|---|---|---|
| Click-Through (Termos de Serviço) | Espaços públicos, acesso de baixo atrito | Sem captura de dados; atrito mínimo para o usuário. |
| Login Social (OAuth) | Varejo, Hospitalidade | Captura rica de dados; requer walled garden para endpoints OAuth. |
| E-mail / Formulário | Geração de leads, fidelidade | Dados primários diretos; requer conformidade com GDPR/CCPA. |
| SMS OTP | Acesso de alto valor, programas de fidelidade | Verifica o número de telefone; adiciona camada de garantia de identidade. |
| Código de Voucher | Conferências, acesso pago | Acesso controlado e com tempo limitado por usuário. |
| RADIUS / IEEE 802.1X | Redes corporativas para visitantes | Integração de identidade corporativa; trilha de auditoria completa. |
Do ponto de vista dos padrões, o setor está migrando para o WPA3-Enterprise, que combina a robusta estrutura de autenticação IEEE 802.1X com um conjunto de segurança de 192 bits. Para redes abertas de visitantes, a Criptografia Sem Fio Oportunista (OWE) do WPA3 fornece um aprimoramento de segurança significativo ao criptografar o tráfego entre cada cliente e o ponto de acesso sem exigir uma chave pré-compartilhada, mitigando diretamente ataques de espionagem passiva que são endêmicos em redes WiFi abertas tradicionais.
Guia de Implementação
A implantação de um Captive Portal em escala corporativa requer uma abordagem metódica. As etapas a seguir fornecem um roteiro neutro em relação a fornecedores para uma implementação segura e eficaz.
Etapa 1 — Fundação da Rede: Crie um SSID dedicado para visitantes e associe-o a uma nova VLAN isolada (por exemplo, VLAN 100). Defina um escopo DHCP grande o suficiente para acomodar sua contagem de usuários simultâneos no pico. Para um hotel de 200 quartos, uma sub-rede /22 (1.022 endereços utilizáveis) é um ponto de partida seguro; para um estádio com capacidade para 20.000 pessoas, uma /19 ou maior é apropriada.
Etapa 2 — Firewall e Política de Segurança: Em seu firewall principal, crie uma política para a VLAN de visitantes com uma postura padrão de deny all (negar tudo). Adicione regras explícitas de allow (permitir) para DNS (porta UDP/TCP 53) e DHCP (portas UDP 67–68). Crie uma regra de pré-autenticação permitindo acesso HTTP e HTTPS apenas aos endereços IP listados em seu walled garden. Bloqueie todo o tráfego destinado ao espaço de endereço da RFC 1918 (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16).
Etapa 3 — Configuração do Controlador: Em seu controlador de LAN sem fio — seja Cisco Meraki, Aruba ClearPass, Ruckus SmartZone ou uma plataforma gerenciada na nuvem — configure o SSID de visitantes para usar a autenticação externa do Captive Portal, apontando para a URL do servidor do seu portal. Defina o tempo limite da sessão (8 horas para hospitalidade, 2 a 4 horas para varejo, 1 hora para eventos). Defina limites de largura de banda por cliente (por exemplo, 5 Mbps de download, 2 Mbps de upload) para garantir o uso justo e evitar abusos na rede.
Etapa 4 — Design do Portal e Conformidade: Projete sua splash page para velocidade e clareza. A página deve ser servida via HTTPS com um certificado TLS válido de uma Autoridade de Certificação confiável. Para conformidade com a GDPR, inclua um link para sua política de privacidade e uma caixa de seleção desmarcada para consentimento de marketing, apresentada separadamente do acordo principal dos termos de serviço. Para a CCPA, inclua um link claramente rotulado "Não Venda Minhas Informações Pessoais". Todas as ações de consentimento devem ser registradas com um carimbo de data/hora e o endereço IP do usuário para fins de auditoria regulatória.
Etapa 5 — Autenticação e Walled Garden: Configure seu(s) método(s) de autenticação escolhido(s) e as regras correspondentes do walled garden. Se estiver usando login social, coloque na lista de permissões (whitelist) os endpoints OAuth específicos para cada provedor. Teste o fluxo de autenticação completo em dispositivos iOS, Android, Windows e macOS antes do lançamento (go-live).
Etapa 6 — Registro e Monitoramento: Habilite o accounting RADIUS em seu controlador para enviar dados detalhados da sessão — endereço MAC, endereço IP, horários de início e término da sessão, volume de dados transferidos — para um servidor de registro centralizado ou SIEM. Retenha os metadados de conexão de acordo com os requisitos da sua jurisdição (normalmente 12 meses no Reino Unido e em muitos estados-membros da UE). Implemente o monitoramento da taxa de consulta DNS para detectar possíveis tentativas de desvio por tunelamento (tunnelling bypass).
Melhores Práticas
A adesão às melhores práticas do setor é essencial para mitigar riscos e garantir uma experiência de usuário de alta qualidade. Essas recomendações são fundamentadas em estruturas de segurança estabelecidas, incluindo PCI DSS, GDPR e orientações de segurança sem fio neutras em relação a fornecedores.
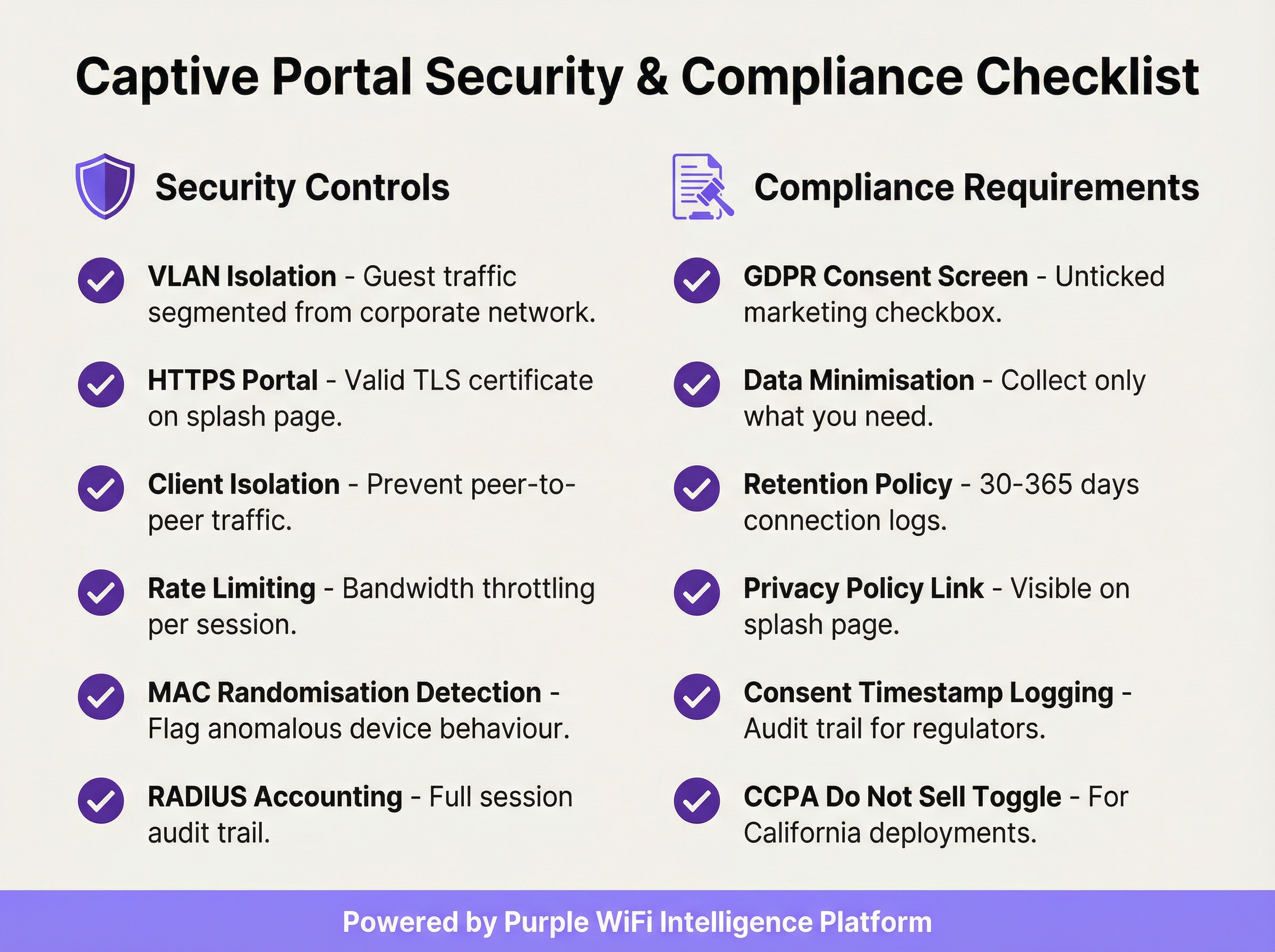
Imponha o Isolamento de Clientes: Essa configuração do controlador sem fio impede que dispositivos de visitantes no mesmo segmento de rede se comuniquem diretamente entre si, reduzindo significativamente o risco de ataques peer-to-peer e movimento lateral entre dispositivos de visitantes.
Valide Seu Certificado TLS: Toda a comunicação com o Captive Portal deve ser criptografada com um certificado TLS válido e confiável. Um certificado expirado ou autoassinado acionará avisos de segurança no navegador, degradando a experiência do usuário e minando a confiança em sua marca.
Implemente a Minimização de Dados: Colete apenas os dados necessários para o serviço específico que você está fornecendo. Se o seu caso de uso exigir apenas um endereço de e-mail para marketing, não solicite um número de telefone ou data de nascimento. Este é um princípio fundamental do Artigo 5(1)(c) da GDPR e reduz sua exposição regulatória.
Mantenha uma Política de Retenção de Dados Documentada: Estabeleça e documente cronogramas de retenção separados para logs de conexão (normalmente de 30 a 365 dias, dependendo da jurisdição) e dados de marketing (elimine contatos inativos e mantenha evidências de consentimento durante todo o período de retenção). As penalidades por não conformidade com a GDPR podem chegar a € 20 milhões ou 4% do faturamento anual global.
Audite Seu Walled Garden Trimestralmente: Com o tempo, os walled gardens acumulam entradas desnecessárias. Uma auditoria trimestral garante que todos os domínios na lista de permissões ainda sejam necessários e que as entradas sejam as mais específicas possíveis, minimizando a superfície de ataque pré-autenticação.
Planeje o Escopo do PCI DSS: Se o seu local processa pagamentos com cartão, certifique-se de que sua rede WiFi para visitantes esteja completamente isolada de qualquer infraestrutura de cartão de pagamento. Um Assessor de Segurança Qualificado (QSA) deve revisar a segmentação da rede se houver alguma ambiguidade sobre o escopo.
Solução de Problemas e Mitigação de Riscos
Os modos de falha mais comuns em implantações de Captive Portal geralmente estão relacionados à compatibilidade de dispositivos, problemas de certificado ou configuração incorreta da rede.
A página do portal não carrega automaticamente: A causa mais frequente é a falha no acionamento do Captive Network Assistant (CNA) do dispositivo. Isso pode ocorrer se o firewall estiver bloqueando o acesso às URLs de detecção específicas do sistema operacional ou se o portal tiver um certificado TLS inválido. Verifique se suas regras de pré-autenticação permitem acesso a captive.apple.com, connectivitycheck.gstatic.com e www.msftconnecttest.com. Certifique-se de que o certificado do portal seja válido e confiável.
Os usuários recebem um aviso de segurança do navegador: Isso quase sempre indica um problema de certificado TLS — expirado, autoassinado ou domínio incompatível. Use um certificado de uma CA confiável e garanta que a URL do portal corresponda exatamente ao Nome Alternativo do Sujeito (SAN) do certificado. Automatize a renovação do certificado usando o Let's Encrypt ou um serviço semelhante para evitar interrupções relacionadas à expiração.
Desvio por tunelamento DNS: Alguns usuários tecnicamente sofisticados podem tentar contornar o portal codificando o tráfego em consultas DNS. Mitigue isso bloqueando todo o tráfego DNS de saída de clientes não autenticados, exceto para o seu resolvedor interno designado, e implementando a limitação da taxa de consulta DNS — sinalizando qualquer cliente que gere mais do que um limite definido de consultas por segundo antes da autenticação.
Falsificação de endereço MAC (MAC spoofing): Um invasor pode clonar o endereço MAC de um dispositivo autenticado para contornar o portal. Mitigue isso por meio do accounting RADIUS com vinculação de sessão tanto ao endereço MAC quanto ao endereço IP, e monitorando entradas duplicadas de endereço MAC em sua tabela de concessão DHCP. O isolamento de clientes também reduz o risco ao impedir que o invasor observe os endereços MAC de outros clientes.
Altos tempos de carregamento do portal degradando as taxas de opt-in: Cada segundo adicional de tempo de carregamento do portal reduz as taxas de conclusão da autenticação. Hospede os ativos do portal em uma CDN, otimize as imagens e minimize as dependências de scripts de terceiros. Tenha como meta um Tempo até a Interatividade (TTI) inferior a 2 segundos em uma conexão móvel 4G.
ROI e Impacto nos Negócios
A implantação de um Captive Portal corporativo deve ser vista como um investimento estratégico. O retorno é realizado por meio de três canais principais: aquisição de dados primários, análise de clientes e localização, e geração direta de receita ou valor de marca.
Aquisição de Dados Primários: Em um cenário de desaparecimento de cookies de terceiros e aumento da perda de sinal devido a atualizações de navegadores focadas em privacidade, um Captive Portal é uma das ferramentas mais eficazes para construir um banco de dados de marketing rico e baseado em consentimento. Um portal bem projetado em um local de varejo ou hospitalidade de alto tráfego pode capturar de centenas a milhares de novos endereços de e-mail com opt-in por mês, fornecendo um canal direto para marketing personalizado, inscrição em programas de fidelidade e engajamento pós-visita.
Análise de Clientes e Localização: Ao analisar os dados de conexão — visitantes únicos, tempo de permanência, frequência de visitas, períodos de pico de tráfego — os locais obtêm inteligência acionável para otimização operacional. Os varejistas podem medir o impacto na loja das campanhas de marketing, identificar seus clientes recorrentes mais fiéis e otimizar os níveis de equipe com base em dados de fluxo de pessoas em tempo real. Os operadores de hospitalidade podem correlacionar os padrões de conexão WiFi com os gastos em Alimentos e Bebidas (F&B) ou reservas de spa para identificar oportunidades de upsell.

Receita Direta e Reforço de Marca: Em aeroportos, centros de conferências e centros de transporte, o WiFi pode ser monetizado diretamente por meio de planos de acesso em níveis. No varejo e na hospitalidade, o portal serve como um poderoso ponto de contato da marca no momento da conexão, permitindo a promoção de ofertas especiais, esquemas de fidelidade e marcas parceiras. Uma experiência de boas-vindas consistente e com a marca em centenas de locais reforça a identidade da marca e demonstra profissionalismo operacional.
Um cálculo típico de ROI pondera a plataforma e os custos operacionais em relação ao valor do ciclo de vida (LTV) dos contatos de marketing adquiridos, às eficiências operacionais obtidas com a análise de fluxo de pessoas e a qualquer receita direta gerada a partir de acesso pago ou parcerias de marketing. Para a maioria das implantações corporativas, o valor do ativo de dados primários por si só — particularmente no contexto de marketing baseado em consentimento e em conformidade com a GDPR — fornece um caso de negócios convincente e defensável.
Key Terms & Definitions
Captive Portal
A network gateway mechanism that intercepts a connecting device's initial HTTP request and redirects it to a web page requiring user interaction — such as authentication, terms of service acceptance, or payment — before granting full internet access. Technically implemented via HTTP 302 redirect, DNS redirect, or ICMP redirect.
IT teams encounter this as the core technology underpinning guest WiFi access control in any public or semi-public venue. The design and configuration of the captive portal directly determines the security posture, compliance status, and commercial value of the guest WiFi deployment.
VLAN (Virtual Local Area Network)
A logical network segment created within a physical network infrastructure that isolates traffic between different groups of devices. In captive portal deployments, a dedicated guest VLAN ensures that guest device traffic is completely separated from corporate network infrastructure, preventing lateral movement and limiting the blast radius of any security incident on the guest network.
Network architects must configure a dedicated guest VLAN as the foundational security control for any captive portal deployment. Without VLAN isolation, a compromised guest device could potentially access corporate systems, creating significant security and compliance risk.
Walled Garden
A pre-authentication whitelist of network resources (IP addresses, hostnames, or domains) that an unauthenticated guest device is permitted to access before completing the captive portal process. Typically includes the portal server itself, CDN endpoints, and OAuth endpoints for social login providers.
IT teams must configure and maintain the walled garden carefully. An overly permissive walled garden expands the pre-authentication attack surface; an overly restrictive one breaks social login functionality or prevents the portal page from loading correctly.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication framework for devices wishing to connect to a LAN or WLAN. It defines the Extensible Authentication Protocol (EAP) transport mechanism and requires a supplicant (client), authenticator (switch or AP), and authentication server (typically RADIUS) to complete the authentication exchange.
Network architects deploying captive portals for corporate guest environments should consider 802.1X integration for the highest level of identity assurance. It provides mutual authentication and a full audit trail, and is the authentication framework underpinning WPA2-Enterprise and WPA3-Enterprise.
WPA3-OWE (Opportunistic Wireless Encryption)
A WPA3 security mode defined in IEEE 802.11i that provides over-the-air encryption on open (no-password) WiFi networks without requiring user authentication. Each client-to-AP connection is encrypted with a unique key, preventing passive eavesdropping by other devices on the same network, even though no password is required to connect.
IT architects planning new captive portal deployments should evaluate OWE as a security enhancement for open guest SSIDs. It addresses the fundamental vulnerability of traditional open WiFi — unencrypted over-the-air traffic — while maintaining the zero-friction connection experience that guests expect.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect to a network service. In captive portal deployments, RADIUS accounting records detailed session information — including MAC address, IP address, session duration, and data volume — to a central server.
RADIUS accounting is the mechanism by which IT teams maintain a comprehensive audit trail of guest WiFi sessions. This audit trail is essential for regulatory compliance (data retention laws), security investigations, and the analytics that underpin ROI measurement.
DNS Tunnelling
A network bypass technique in which a client encodes arbitrary internet traffic (e.g., HTTP requests) within DNS query packets, which are typically permitted through firewalls even for unauthenticated clients. An attacker or technically sophisticated user can use a DNS tunnelling tool to bypass a captive portal and access the internet without authenticating.
Network security teams should implement DNS query rate monitoring and anomaly detection to identify potential tunnelling activity. Blocking outbound DNS traffic from unauthenticated clients to all servers except the designated internal resolver is the primary mitigation.
MAC Address Spoofing
A technique in which a device's network interface is configured to broadcast a different MAC (Media Access Control) address than the one burned into the hardware. In captive portal environments, an attacker can clone the MAC address of an already-authenticated device to bypass the portal's access control, as many portals use MAC address as the primary session identifier.
IT security teams should be aware that MAC-based authentication alone is not sufficient for high-security environments. RADIUS accounting with session binding to both MAC address and IP address, combined with client isolation to prevent MAC address observation, provides a more robust defence.
Splash Page
The branded web page presented to a user by a captive portal before internet access is granted. The splash page typically contains the venue's branding, a login or consent form, a link to the privacy policy, and terms of service. It is the primary user-facing element of the captive portal system and the key touchpoint for data capture and brand communication.
Marketing and IT teams must collaborate on splash page design. From an IT perspective, the page must be served over HTTPS, load in under 2 seconds, and contain all legally required consent elements. From a marketing perspective, it must be on-brand, clear, and designed to maximise opt-in rates.
GDPR (General Data Protection Regulation)
The European Union's primary data protection regulation (Regulation 2016/679), which governs the collection, processing, storage, and transfer of personal data relating to EU residents. For captive portal deployments, GDPR mandates freely given, specific, and unambiguous consent for data collection; data minimisation; documented retention policies; and the ability to demonstrate compliance through audit trails.
Any captive portal that collects personal data (email addresses, names, phone numbers) from EU or UK residents must comply with GDPR. Non-compliance penalties can reach €20 million or 4% of global annual turnover. IT and legal teams must collaborate to ensure the portal's consent mechanism, data storage, and retention policies meet the regulation's requirements.
Case Studies
A 250-room luxury hotel group with 12 properties needs to deploy a unified captive portal solution that captures guest email addresses for their loyalty programme, complies with GDPR across all EU properties, and provides the IT team with centralised management. The properties use a mix of Cisco Meraki and Aruba access points. What architecture and implementation approach should they adopt?
The recommended approach is a cloud-managed, hardware-agnostic captive portal platform (such as Purple) that integrates with both Meraki and Aruba controllers via external portal redirect. The implementation proceeds as follows:
VLAN Architecture: Configure a dedicated guest VLAN (e.g., VLAN 200) on all properties, with a consistent IP addressing scheme (e.g., 10.200.x.0/22 per property) to simplify firewall policy management across the estate.
Controller Configuration: On Meraki, navigate to Wireless > SSIDs > [Guest SSID] > Splash page and select 'Click-through' or 'Sign-on splash page', entering the external portal URL. On Aruba, configure a Captive Portal profile in ClearPass Policy Manager pointing to the same external portal URL. Set session timeout to 8 hours and per-client bandwidth to 10 Mbps down / 5 Mbps up.
Portal Design: Build a single portal template with the group's master brand. Use location-specific branding overrides (logo, colour scheme) for each property. The form captures first name, last name, and email. The GDPR consent screen presents two separate, unticked checkboxes: one for the terms of service (required for access) and one for marketing communications (optional). The privacy policy link is prominently displayed.
Compliance Configuration: Enable consent timestamp logging for every session. Configure a data retention policy: connection logs retained for 12 months (UK GDPR requirement), marketing contacts purged after 24 months of inactivity. Export audit logs monthly to the group's central compliance repository.
Loyalty Integration: Connect the portal's API to the hotel group's CRM/loyalty platform. On successful email capture with marketing consent, automatically enrol the guest in the loyalty programme and trigger a welcome email within 15 minutes.
Testing and Rollout: Pilot at one property for 30 days, measuring email capture rate (target: >60% of connecting guests), portal load time (target: <2 seconds), and authentication error rate (target: <1%). Roll out to remaining properties in batches of three.
A national retail chain with 80 stores wants to use their guest WiFi captive portal to measure the effectiveness of their in-store marketing campaigns, specifically whether customers who receive a promotional email visit the store within 14 days. The IT team is concerned about PCI DSS compliance, as the stores also process card payments. How should this be architected?
This deployment requires careful attention to both the analytics use case and PCI DSS network segmentation requirements.
PCI DSS Segmentation: The guest WiFi network must be completely isolated from the payment card environment (PCE). Implement a three-VLAN architecture: VLAN 10 for POS/payment systems, VLAN 20 for corporate/staff systems, VLAN 30 for guest WiFi. The firewall must have explicit
denyrules preventing any traffic between VLAN 30 and VLANs 10 and 20. Engage a QSA to validate the segmentation before go-live.Guest SSID and Portal: Deploy the guest SSID on VLAN 30 with an email-capture portal. The form collects email address and optionally a loyalty card number. GDPR-compliant marketing consent checkbox is included.
Campaign Attribution Architecture: The portal platform assigns each authenticated session a unique session ID linked to the guest's email address and the store location (identified by the access point's location tag). When a promotional email is sent, it contains a unique tracking pixel and a store-specific UTM parameter on the call-to-action link.
Visit Attribution: When a customer who received the promotional email returns to a store and connects to WiFi within 14 days, the portal platform matches their email address to the campaign cohort and records the return visit. This creates a closed-loop attribution model: email sent → store visit detected via WiFi connection → conversion recorded.
Analytics Dashboard: The central analytics platform aggregates data across all 80 stores, providing campaign attribution reports showing email-to-visit conversion rates by store, region, and campaign. Typical metrics: unique visitors per store per day, email capture rate, 14-day return visit rate for campaign cohort vs. control group.
Data Governance: All guest data is stored in a GDPR-compliant data warehouse with role-based access control. Marketing data is retained for 24 months from last interaction. Connection logs are retained for 12 months.
Scenario Analysis
Q1. A conference centre hosts 50 events per year, ranging from 200-person seminars to 5,000-person trade shows. They want to deploy a captive portal that provides event-specific branding for each event, captures attendee email addresses for post-event marketing, and can scale from 200 to 5,000 concurrent connections. The venue's IT team has limited capacity for per-event configuration. What platform architecture and configuration approach would you recommend?
💡 Hint:Consider the operational overhead of per-event portal customisation, the DHCP scope sizing requirements for peak concurrent users, and the GDPR implications of sharing attendee data with event organisers.
Show Recommended Approach
The recommended architecture uses a cloud-managed captive portal platform with a self-service portal builder. The venue's IT team creates a master portal template with the venue's base branding and GDPR consent framework. For each event, the organiser is given access to a restricted portal customisation interface where they can upload their logo, set brand colours, and add event-specific messaging — without touching any network configuration. The DHCP scope for the guest VLAN should be sized for the maximum expected concurrent connections (5,000), using a /19 subnet (8,190 usable addresses) to provide headroom. The wireless controller should be configured with dynamic bandwidth management to automatically adjust per-client limits based on current network load. For GDPR, the data controller relationship must be clearly defined: if attendee data is shared with event organisers, a Data Processing Agreement (DPA) is required, and the privacy policy must disclose this sharing. Attendees should be able to opt out of data sharing with the event organiser while still accepting the venue's terms of service for WiFi access.
Q2. A hospital trust wants to deploy guest WiFi with a captive portal across 5 sites. Clinical staff have raised concerns that the guest WiFi could be used to access patient records if the network segmentation is not correctly implemented. The IT security team also needs to ensure the deployment does not bring any clinical systems into scope for additional regulatory review. How do you address these concerns?
💡 Hint:Consider the network segmentation requirements, the specific clinical systems that must be protected, and the regulatory frameworks (NHS Data Security and Protection Toolkit, Cyber Essentials) that apply in addition to GDPR.
Show Recommended Approach
The deployment requires a minimum three-tier network architecture: a clinical VLAN for patient records systems (EPR, PACS, clinical workstations), a staff VLAN for administrative systems, and a guest VLAN for patient and visitor WiFi. The firewall policy must include explicit deny rules preventing any traffic from the guest VLAN to the clinical and staff VLANs, with the default stance being deny-all for inter-VLAN traffic. The guest SSID should be on a completely separate DHCP scope with no route to RFC 1918 clinical address space. The captive portal itself should be hosted externally (cloud-based) or on a dedicated DMZ server, not on any system within the clinical network. For regulatory compliance, the IT security team should document the network segmentation design and have it reviewed by an independent assessor as part of the NHS Data Security and Protection Toolkit submission. The guest WiFi network should be explicitly scoped out of any clinical system security assessments. GDPR compliance for the portal requires a healthcare-specific privacy notice that discloses the limited data collected (connection metadata, optional email) and the retention period.
Q3. Your organisation's captive portal has been in production for 18 months. A security audit has identified three issues: (1) the portal TLS certificate expired 3 weeks ago and users are receiving browser warnings, (2) the walled garden contains 47 entries, many of which appear to be from a social login provider that was removed 12 months ago, and (3) RADIUS accounting logs show that 15% of guest sessions have a duration of over 30 days, suggesting that session timeouts are not being enforced. Prioritise and address these issues.
💡 Hint:Consider the security and user experience impact of each issue, the speed of remediation required, and the root cause of the session timeout failure.
Show Recommended Approach
Prioritise in order of security and user experience impact. Issue 1 (expired TLS certificate) is the most urgent: it is actively degrading the user experience (browser security warnings) and represents a security risk (users may be trained to click through certificate warnings, making them vulnerable to genuine MITM attacks). Immediate action: renew the certificate from a trusted CA and deploy it to the portal server. Implement automated certificate renewal (e.g., using Let's Encrypt with auto-renewal) to prevent recurrence. Issue 3 (30-day sessions) is the second priority: sessions lasting 30 days represent a significant security risk, as a device that was authenticated 30 days ago may no longer be in the possession of the original user. Investigate the root cause — likely a misconfigured session timeout value on the wireless controller or a controller firmware bug. Set the session timeout to 8 hours (or appropriate for the venue type) and force-terminate all existing sessions over 24 hours old. Issue 2 (walled garden hygiene) is the third priority: while a security concern, stale walled garden entries from a removed provider are lower risk than the first two issues. Audit all 47 entries, remove those associated with the deprecated social login provider, and document the purpose of each remaining entry. Implement a quarterly walled garden review process to prevent recurrence.
Key Takeaways
- ✓VLAN segmentation is the non-negotiable foundation of any enterprise captive portal deployment — guest traffic must be completely isolated from corporate infrastructure before any portal configuration begins.
- ✓The captive portal must be served over HTTPS with a valid TLS certificate from a trusted Certificate Authority; HTTP-only portals are a security liability and will be deprecated by modern browsers.
- ✓GDPR compliance requires a separate, unticked marketing consent checkbox distinct from the terms of service acceptance, with all consent states and timestamps logged for regulatory audit purposes.
- ✓The walled garden should whitelist specific endpoints rather than entire domains, and should be audited quarterly to remove unnecessary entries that expand the pre-authentication attack surface.
- ✓WPA3's Opportunistic Wireless Encryption (OWE) mode should be evaluated for all new deployments, as it provides over-the-air encryption on open networks without requiring a password, directly mitigating passive eavesdropping.
- ✓Portal load time directly impacts opt-in rates — target a Time to Interactive of under 2 seconds by hosting assets on a CDN and minimising third-party script dependencies.
- ✓The commercial ROI of a captive portal is realised through three channels: first-party data acquisition for marketing, customer and location analytics for operational intelligence, and direct revenue or brand value from the connection experience — all of which should be quantified in the business case.



