Compreender e Fortalecer o RADIUS Contra Ataques de Colisão MD5
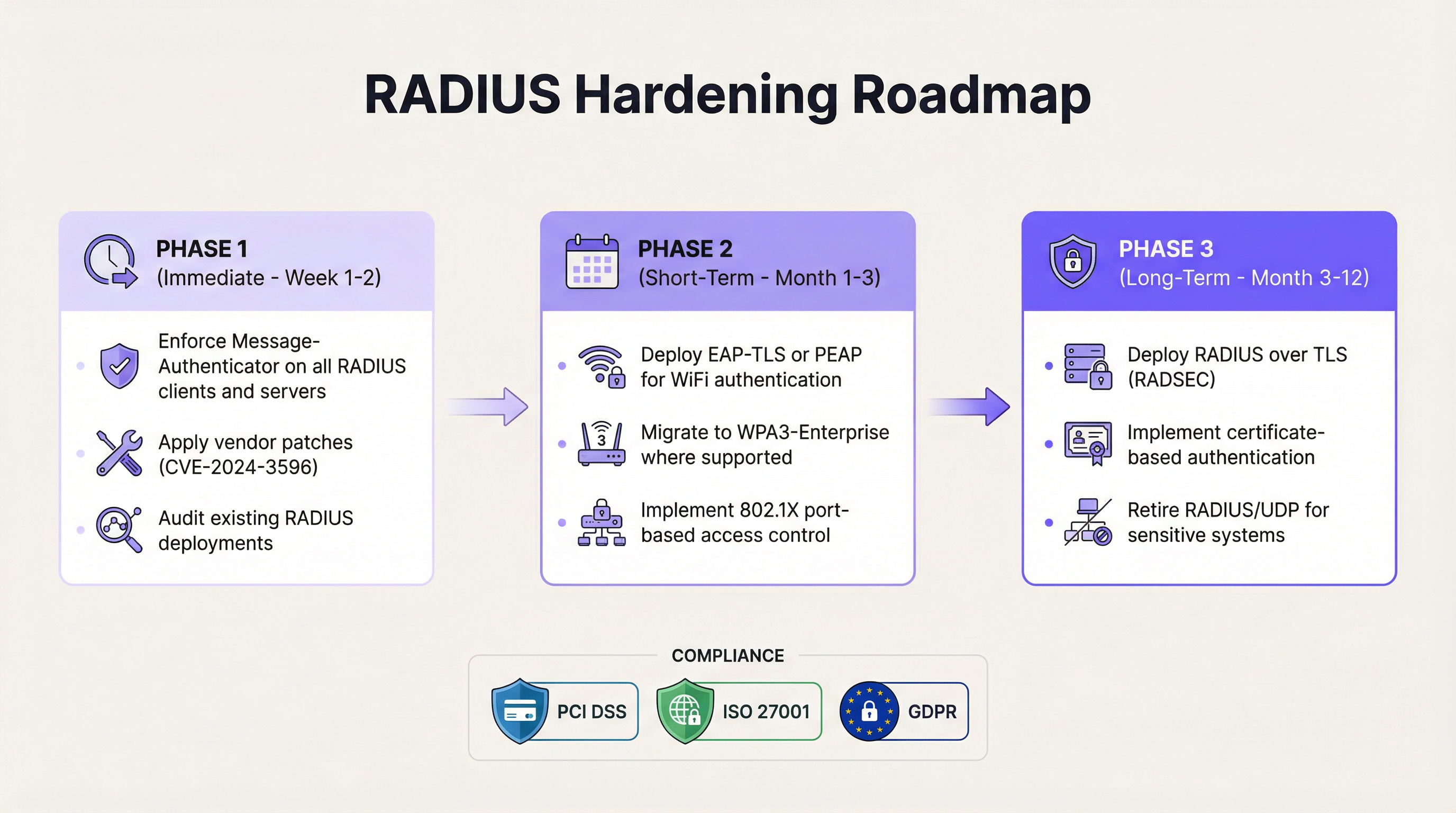
This guide provides a comprehensive technical reference on the RADIUS MD5 collision vulnerability (CVE-2024-3596, 'Blast-RADIUS'), explaining how man-in-the-middle attackers can exploit weaknesses in the MD5-based Response Authenticator to forge authentication approvals without knowing user credentials. It is essential reading for IT managers, network architects, and CTOs operating enterprise WiFi in hospitality, retail, events, and public-sector environments who need to assess their exposure, apply immediate mitigations, and plan a strategic migration to modern authentication standards. The guide covers the full attack lifecycle, a phased hardening roadmap, real-world deployment scenarios, and compliance implications under PCI DSS, GDPR, and ISO 27001.
🎧 Listen to this Guide
View Transcript

Resumo Executivo
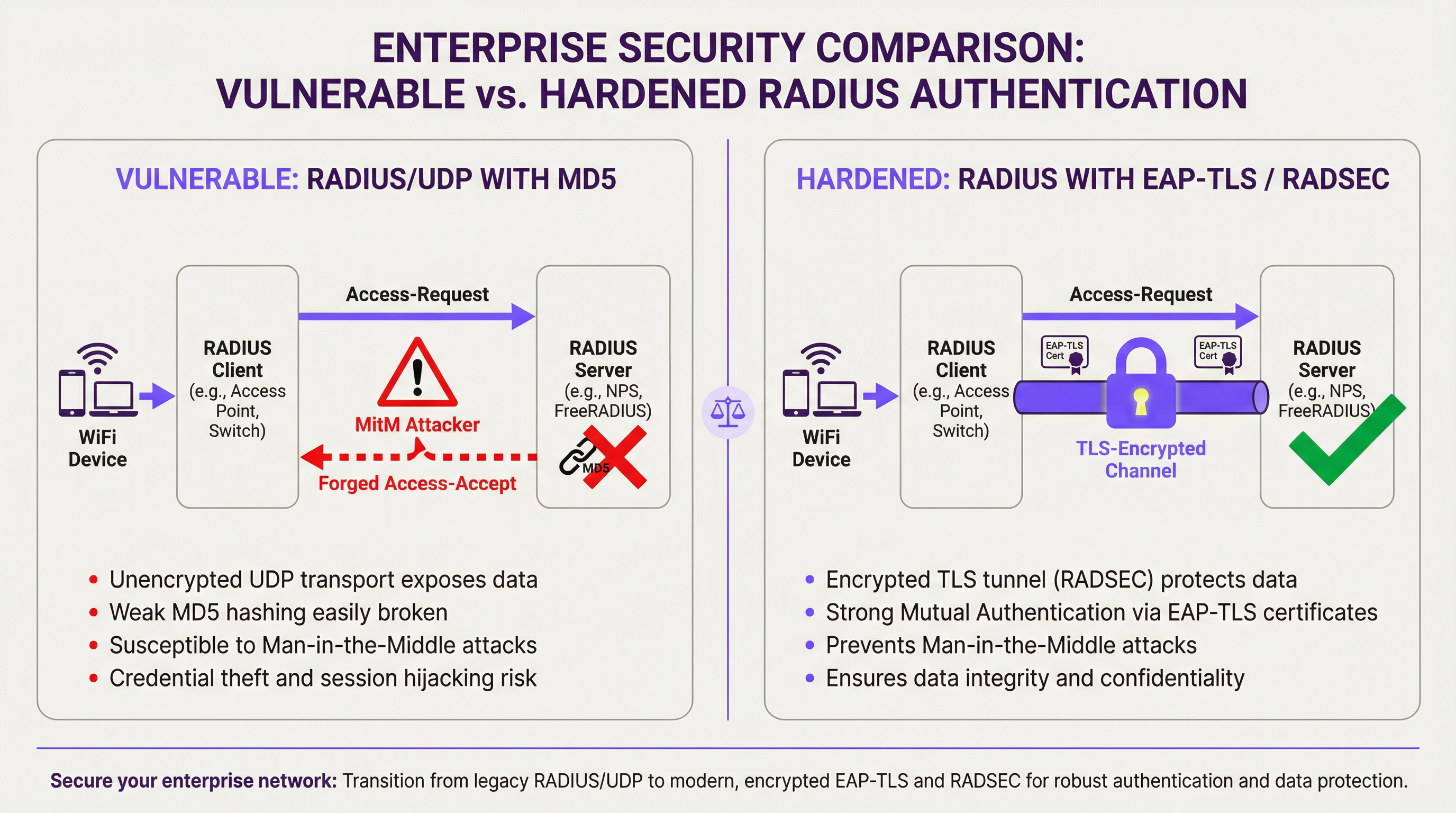
O protocolo RADIUS, um pilar da autenticação de redes empresariais desde 1991, apresenta uma vulnerabilidade crítica e agora praticamente explorável. Divulgada em julho de 2024 sob o CVE-2024-3596 e apelidada de 'Blast-RADIUS', esta falha permite que um atacante man-in-the-middle (MitM) posicionado entre um cliente e um servidor RADIUS forje uma aprovação de autenticação válida — convertendo um 'Access-Reject' legítimo num 'Access-Accept' — sem nunca conhecer a palavra-passe de um utilizador ou o segredo partilhado do RADIUS. O ataque explora técnicas de colisão de prefixo escolhido MD5 que, com hardware moderno, podem ser executadas em minutos.
Para operadores de recintos e equipas de TI empresariais, o risco de negócio é direto: um atacante que obtenha acesso não autorizado à rede pode mover-se lateralmente pela infraestrutura, aceder a sistemas de ponto de venda, exfiltrar dados de convidados e desencadear violações de conformidade ao abrigo do PCI DSS e do GDPR. Qualquer organização que execute RADIUS/UDP com modos de autenticação PAP, CHAP ou MS-CHAP está exposta até que as correções sejam aplicadas e as alterações arquitetónicas planeadas. A mitigação imediata — impor o atributo Message-Authenticator em todo o tráfego RADIUS — é uma alteração de configuração de baixo impacto disponível em todos os principais fornecedores. A resposta estratégica é uma migração faseada para EAP-TLS e RADIUS sobre TLS (RADSEC).
Análise Técnica Aprofundada
O Protocolo RADIUS e a sua Herança Criptográfica
O RADIUS (Remote Authentication Dial-In User Service), padronizado no RFC 2865, foi concebido numa época em que os requisitos de segurança de rede eram fundamentalmente diferentes. O protocolo opera sobre UDP e utiliza um segredo partilhado entre o cliente RADIUS (normalmente um ponto de acesso ou servidor de acesso à rede) e o servidor RADIUS para fornecer um grau de integridade da mensagem. Especificamente, as respostas do servidor são 'autenticadas' utilizando uma construção chamada Response Authenticator, calculada como:
MD5(Code || ID || Length || RequestAuthenticator || Attributes || SharedSecret)
Esta construção nunca foi um verdadeiro código de autenticação de mensagem (MAC). É anterior ao HMAC, que foi padronizado em 1997 precisamente para colmatar as fraquezas dos MACs baseados em hash simples. A especificação RADIUS não foi atualizada quando o HMAC foi introduzido, nem quando as colisões MD5 foram demonstradas pela primeira vez em 2004. Esta dívida arquitetónica tornou-se agora uma vulnerabilidade crítica.
A Mecânica do Ataque Blast-RADIUS
O ataque Blast-RADIUS (CVE-2024-3596) combina três elementos: uma vulnerabilidade ao nível do protocolo na forma como o RADIUS constrói o seu Response Authenticator, uma técnica de colisão de prefixo escolhido MD5 e melhorias significativas na velocidade de cálculo da colisão que tornam o ataque prático num cenário de interceção de rede em tempo real.
O ataque decorre da seguinte forma. Um atacante MitM interceta um pacote Access-Request enviado do cliente RADIUS para o servidor. O atacante injeta um atributo malicioso neste pedido — um payload cuidadosamente elaborado que causará uma colisão entre o hash MD5 da resposta legítima do servidor e o hash MD5 da resposta forjada desejada pelo atacante. Quando o servidor devolve um Access-Reject (uma autenticação falhada), o atacante utiliza a colisão pré-calculada para forjar um pacote Access-Accept válido, completo com um Response Authenticator que o cliente RADIUS aceitará como genuíno. O atacante não precisa de conhecer o segredo partilhado ou as credenciais do utilizador.
Investigadores da Universidade de Boston, UC San Diego, CWI Amsterdam e Microsoft demonstraram que, com algoritmos otimizados, a colisão de prefixo escolhido MD5 necessária para este ataque pode ser calculada em menos de cinco minutos em hardware comum. Isto torna o ataque operacionalmente viável para um adversário determinado com acesso ao caminho de rede entre o cliente e o servidor RADIUS.
Modos de Autenticação Afetados
A vulnerabilidade afeta todas as implementações RADIUS/UDP que utilizam métodos de autenticação não-EAP. A tabela abaixo resume a exposição por modo de autenticação:
| Modo de Autenticação | Protocolo | Vulnerável ao Blast-RADIUS? | Notas |
|---|---|---|---|
| PAP | Password Authentication Protocol | Sim | Mais comum em implementações legadas |
| CHAP | Challenge Handshake Authentication Protocol | Sim | Ligeiramente mais forte que o PAP, mas ainda exposto |
| MS-CHAP / MS-CHAPv2 | Microsoft CHAP | Sim | Comum em ambientes Windows |
| EAP-MD5 | EAP com MD5 | Sim | Obsoleto; evitar totalmente |
| PEAP (MSCHAPv2 interno) | Protected EAP | Não (túnel EAP protege) | Requer validação correta do certificado do servidor |
| EAP-TLS | EAP com TLS | Não | Padrão de excelência recomendado |
| EAP-TTLS | EAP Tunnelled TLS | Não | Alternativa aceitável |
A distinção crítica é que os métodos baseados em EAP estabelecem o seu próprio túnel criptográfico para autenticação, que não depende do Response Authenticator MD5. Isto torna-os imunes ao vetor de ataque específico do Blast-RADIUS.
Por Que a Segmentação de VLAN Não é Suficiente
Um equívoco comum é que isolar o tráfego RADIUS numa VLAN de gestão dedicada fornece proteção adequada. Embora a segmentação de rede seja uma prática de segurança sólida, não elimina o risco do Blast-RADIUS. Um atacante que já tenha comprometido um dispositivo na rede de gestão — através de um ataque de phishing, um comprometimento da cadeia de abastecimento ou a exploração de outra vulnerabilidade — pode posicionar-se como um MitM no caminho do tráfego RADIUS. O ataque requer apenas acesso ao caminho de rede, não acesso externo à Internet. A segmentação reduz a superfície de ataque, mas não elimina a fraqueza criptográfica subjacente.
Guia de Implementação
Fase 1: Fortalecimento Imediato (Semanas 1–2)
A primeira prioridade é aplicar as correções dos fornecedores para o CVE-2024-3596 em toda a infraestrutura RADIUS. Todos os principais fornecedores — incluindo Cisco ISE, Microsoft NPS, FreeRADIUS, Juniper, Aruba e Ruckus — lançaram atualizações. Paralelamente à aplicação de correções, a alteração de configuração crítica é impor o atributo Message-Authenticator em todos os clientes e servidores RADIUS.
O atributo Message-Authenticator (definido no RFC 2869) fornece uma verificação de integridade HMAC-MD5 sobre todo o pacote RADIUS. Ao contrário do Response Authenticator, esta construção não é vulnerável ao ataque de colisão de prefixo escolhido porque a construção HMAC vincula o hash ao segredo partilhado de uma forma que impede o atacante de criar uma falsificação válida. Configurar clientes e servidores para exigirem este atributo — e rejeitarem qualquer mensagem que não o inclua — fecha o vetor de ataque imediato.
Para o FreeRADIUS, isto envolve definir require_message_authenticator = yes no ficheiro clients.conf. Para o Microsoft NPS, a política equivalente é imposta através das definições de Política de Rede. Para o Cisco ISE, a definição está disponível na configuração do cliente RADIUS, na política de autenticação. Consulte o aviso específico do seu fornecedor para o CVE-2024-3596 para obter os passos exatos de configuração.
Fase 2: Modernização da Autenticação (Meses 1–3)
O objetivo a médio prazo é migrar a autenticação WiFi dos modos legados PAP/CHAP para métodos baseados em EAP. Para ambientes WiFi empresariais, o caminho recomendado é o WPA3-Enterprise com EAP-TLS. Isto requer a implementação de uma Infraestrutura de Chave Pública (PKI) para emitir certificados de dispositivos e/ou utilizadores, a configuração do seu servidor RADIUS para validar estes certificados e o aprovisionamento dos dispositivos clientes com os certificados apropriados e as âncoras de confiança do servidor RADIUS.
Para ambientes onde a implementação de certificados é complexa — como recintos com elevada rotatividade de dispositivos ou políticas BYOD — o PEAP com MSCHAPv2 fornece um passo intermédio aceitável, desde que os clientes estejam configurados para validar o certificado do servidor RADIUS. Sem a validação do certificado do servidor, o PEAP é vulnerável a ataques de pontos de acesso não autorizados (rogue access points). O controlo de acesso baseado em portas IEEE 802.1X deve ser implementado simultaneamente na infraestrutura com fios para garantir uma política de autenticação consistente em toda a rede.
Fase 3: Segurança da Camada de Transporte (Meses 3–12)
O objetivo arquitetónico a longo prazo é encapsular todo o tráfego RADIUS dentro de um túnel TLS utilizando o RADIUS sobre TLS (RADSEC), padronizado no RFC 6614. O RADSEC substitui o UDP pelo TCP e envolve toda a sessão RADIUS numa ligação TLS mutuamente autenticada. Isto fornece confidencialidade, integridade e proteção contra repetição para todo o tráfego de autenticação, tornando o Response Authenticator MD5 irrelevante, uma vez que a própria camada de transporte é criptograficamente segura.
O RADSEC é particularmente valioso em implementações distribuídas — como cadeias de hotéis, redes de retalho ou ambientes de estádios — onde o tráfego RADIUS pode atravessar segmentos de rede intermédios. A IETF está atualmente a progredir o RADIUS sobre TLS e DTLS para o estatuto de padrão, refletindo o consenso da indústria de que o RADIUS/UDP deve ser descontinuado para implementações sensíveis.
Melhores Práticas
As seguintes melhores práticas, independentes de fornecedores, refletem os padrões atuais da indústria e as orientações regulamentares para a segurança da autenticação WiFi empresarial.
Impor o Message-Authenticator universalmente. Todos os clientes e servidores RADIUS no seu parque informático devem ser configurados para enviar e exigir o atributo Message-Authenticator. Esta é a ação de maior impacto e menor disrupção disponível atualmente. De acordo com as orientações da equipa de investigação do Blast-RADIUS, este atributo deve aparecer como o primeiro atributo nas respostas Access-Accept e Access-Reject.
Adotar o EAP-TLS como padrão de autenticação. O IEEE 802.1X com EAP-TLS fornece autenticação mútua baseada em certificados que é imune à classe de ataques Blast-RADIUS e alinha-se com as recomendações do NIST SP 800-120 para métodos EAP no acesso a redes sem fios. O WPA3-Enterprise exige o modo de segurança de 192 bits com EAP-TLS para o nível de segurança mais elevado.
Rodar os segredos partilhados do RADIUS regularmente. Embora o ataque Blast-RADIUS não exija o conhecimento do segredo partilhado, segredos partilhados fortes e únicos (mínimo de 32 caracteres, gerados aleatoriamente) reduzem o risco de outras classes de ataques. Os segredos devem ser rodados pelo menos anualmente e imediatamente após qualquer suspeita de comprometimento.
Implementar a contabilização (accounting) do RADIUS e a monitorização de anomalias. Os registos de contabilização do RADIUS fornecem um rasto de auditoria dos eventos de autenticação. A monitorização de padrões anómalos — como autenticações bem-sucedidas de tipos de dispositivos inesperados, endereços MAC ou em horários invulgares — pode fornecer um aviso prévio de exploração. Integre a contabilização do RADIUS com o seu SIEM para alertas automatizados.
Segmentar o tráfego RADIUS. Embora não seja uma mitigação completa, colocar o tráfego RADIUS numa VLAN de gestão dedicada com ACLs rigorosas reduz a população de dispositivos que poderiam ser utilizados como ponto de articulação MitM. Combine com o controlo de acesso à rede para garantir que apenas dispositivos autorizados podem aceder ao servidor RADIUS.
Alinhar com os requisitos do PCI DSS. O Requisito 8.6 do PCI DSS v4.0 exige autenticação forte para todas as contas. O Requisito 1.3 exige controlos de segmentação de rede. As organizações que processam dados de cartões de pagamento devem garantir que a sua arquitetura de autenticação WiFi cumpre estes requisitos, e a vulnerabilidade Blast-RADIUS afeta diretamente a postura de conformidade de qualquer segmento de rede abrangido.
Resolução de Problemas e Mitigação de Riscos
Modos de Falha Comuns Durante o Fortalecimento
O problema mais frequente encontrado ao impor o Message-Authenticator é a incompatibilidade de dispositivos legados. Pontos de acesso, switches ou concentradores VPN mais antigos podem não suportar o atributo, causando falhas de autenticação após o servidor ser configurado para o exigir. A abordagem recomendada é auditar todos os clientes RADIUS antes de impor o requisito do lado do servidor e manter uma lista de dispositivos que requerem atualizações de firmware ou substituição.
Um segundo problema comum são as falhas de validação de certificados durante a migração para EAP-TLS. Se os dispositivos clientes não forem aprovisionados com a âncora de confiança correta do certificado do servidor RADIUS, rejeitarão o certificado do servidor e falharão a autenticação. Isto é particularmente prevalente em ambientes BYOD. A implementação de uma solução de Gestão de Dispositivos Móveis (MDM) para distribuir perfis de certificados é a resolução padrão.
Incompatibilidades de segredos partilhados podem ocorrer durante a migração para RADSEC se o Nome Comum (Common Name) do certificado TLS não corresponder ao identificador de cliente esperado. Certifique-se de que os nomes de sujeito dos certificados são consistentes com os endereços IP ou nomes de anfitrião dos clientes RADIUS configurados no servidor.
Mitigação de Riscos para Ambientes Que Não Podem Aplicar Correções Imediatamente
Para ambientes onde a aplicação imediata de correções não é viável — como sistemas de controlo industrial legados ou dispositivos de rede incorporados — o risco pode ser parcialmente mitigado através da implementação de controlos rigorosos de acesso à rede que limitam quais os anfitriões que podem comunicar com o servidor RADIUS, reduzindo a oportunidade de um atacante MitM intercetar o tráfego. Esta é apenas uma medida temporária; deve ser estabelecido um roteiro de correção e substituição.
ROI e Impacto no Negócio
Quantificar o Risco
O caso de negócio para o fortalecimento do RADIUS é simples quando enquadrado em termos de custos de violação e responsabilidade de conformidade. Uma exploração bem-sucedida do Blast-RADIUS num ambiente de hotelaria ou retalho poderia fornecer a um atacante acesso à rede corporativa, alcançando potencialmente sistemas de ponto de venda, repositórios de dados de convidados e infraestrutura de back-office. O custo médio de uma violação de dados no setor da hotelaria excede os 3 milhões de libras, de acordo com as referências da indústria, com as multas regulamentares ao abrigo do GDPR a poderem somar até 4% do volume de negócios anual global.
Para organizações abrangidas pelo PCI DSS, uma falha de autenticação de rede que resulte na exposição de dados de titulares de cartões pode desencadear investigações forenses obrigatórias, multas das marcas de cartões e a potencial perda de privilégios de processamento de cartões — custos que excedem largamente o investimento necessário para implementar o EAP-TLS e o RADSEC.
Referências de Custos de Implementação
A tabela seguinte fornece estimativas indicativas de custos e esforço para o roteiro de fortalecimento em três fases em ambientes de recintos típicos:
| Fase | Ação | Esforço Estimado | Custo Estimado | Redução de Risco |
|---|---|---|---|---|
| Fase 1 | Corrigir + impor Message-Authenticator | 1–3 dias (equipa de TI) | Apenas tempo da equipa | Elevada (fecha o CVE imediato) |
| Fase 2 | Migração para EAP-TLS / WPA3-Enterprise | 2–6 semanas | Licenciamento PKI + MDM | Muito Elevada |
| Fase 3 | Implementação de RADSEC | 4–12 semanas | Atualizações de infraestrutura | Abrangente |
Benefícios Operacionais Além da Segurança
A migração para EAP-TLS e RADSEC proporciona benefícios operacionais além do fortalecimento da segurança. A autenticação baseada em certificados elimina a sobrecarga operacional de gerir e rodar palavras-passe partilhadas em grandes frotas de dispositivos. O WPA3-Enterprise melhora a fiabilidade da ligação em ambientes densos — um benefício mensurável para estádios e centros de conferências onde centenas de dispositivos competem pela autenticação. O transporte TCP do RADSEC também fornece melhor fiabilidade do que o UDP em condições de rede com elevada latência ou perda de pacotes, melhorando a experiência de autenticação para os utilizadores finais.

Key Terms & Definitions
RADIUS (Remote Authentication Dial-In User Service)
A client-server networking protocol (RFC 2865) that provides centralised authentication, authorisation, and accounting (AAA) for users connecting to a network. RADIUS clients (access points, switches, VPN concentrators) forward authentication requests to a central RADIUS server, which validates credentials and returns an Access-Accept or Access-Reject response.
IT teams encounter RADIUS as the authentication backbone for enterprise WiFi (802.1X), VPN access, and network device administration. Its age and architectural limitations are now a direct security liability under CVE-2024-3596.
MD5 Chosen-Prefix Collision Attack
A cryptographic attack against the MD5 hash function in which an attacker constructs two different messages with the same MD5 hash, where both messages begin with attacker-chosen prefixes. This is more powerful than a standard collision attack because the attacker can control the meaningful content of both colliding messages.
This is the specific attack technique used in Blast-RADIUS. The attacker uses it to forge a RADIUS Response Authenticator that the client will accept as genuine, even though the response content has been modified from Access-Reject to Access-Accept.
Response Authenticator
A 16-byte field in RADIUS response packets (Access-Accept, Access-Reject, Access-Challenge) computed as MD5(Code || ID || Length || RequestAuthenticator || Attributes || SharedSecret). It is intended to verify the integrity of the server response but is not a proper cryptographic MAC and is vulnerable to the Blast-RADIUS attack.
Network architects need to understand that the Response Authenticator is the specific field being forged in a Blast-RADIUS attack. Enforcing the Message-Authenticator attribute provides a stronger integrity check that is not vulnerable to the same collision technique.
Message-Authenticator Attribute
A RADIUS attribute (Attribute 80, defined in RFC 2869) that provides an HMAC-MD5 integrity check over the entire RADIUS packet, including all attributes. Unlike the Response Authenticator, the HMAC construction binds the integrity check to the shared secret in a way that prevents chosen-prefix collision forgery.
Enforcing the Message-Authenticator attribute on all RADIUS clients and servers is the primary short-term mitigation for CVE-2024-3596. IT teams should verify that all RADIUS infrastructure is patched and configured to require this attribute before accepting any response.
EAP-TLS (Extensible Authentication Protocol – Transport Layer Security)
An EAP method (RFC 5216) that uses TLS for mutual certificate-based authentication between the client and the RADIUS server. Both parties must present valid digital certificates from a trusted Certificate Authority. It is immune to the Blast-RADIUS attack and is the recommended gold standard for enterprise WiFi authentication.
CTOs and network architects should treat EAP-TLS as the target state for all enterprise WiFi authentication. It requires a PKI infrastructure but eliminates shared secrets, password-based attacks, and the MD5 vulnerability class entirely.
RADSEC (RADIUS over TLS)
A protocol extension (RFC 6614) that encapsulates RADIUS messages within a mutually authenticated TLS session over TCP, replacing the traditional UDP transport. RADSEC provides confidentiality, integrity, and replay protection for all RADIUS traffic, making transport-layer attacks such as Blast-RADIUS impossible.
RADSEC is the long-term architectural solution for RADIUS security. It is particularly valuable in distributed deployments (hotel chains, retail networks) where RADIUS traffic traverses multiple network segments. Vendors including Cisco, Juniper, Aruba, and FreeRADIUS support RADSEC.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism for devices wishing to connect to a LAN or WLAN. It uses EAP as the authentication framework and RADIUS as the backend authentication server. 802.1X ensures that only authenticated devices can access network resources.
802.1X is the framework within which RADIUS and EAP operate for enterprise WiFi. IT managers implementing WPA2/WPA3-Enterprise are deploying 802.1X. Understanding this relationship is essential for configuring authentication policies and troubleshooting access issues.
WPA3-Enterprise
The enterprise variant of the Wi-Fi Protected Access 3 (WPA3) security standard, which mandates 802.1X authentication and, in its highest security mode (192-bit), requires EAP-TLS with a 384-bit elliptic curve cipher suite. WPA3-Enterprise provides significantly stronger security guarantees than WPA2-Enterprise and is immune to the Blast-RADIUS attack when correctly configured.
Network architects planning new WiFi deployments or major infrastructure refreshes should specify WPA3-Enterprise as the minimum security standard. It is supported by all modern access points and client devices manufactured after 2020.
Man-in-the-Middle (MitM) Attack
An attack in which the adversary secretly intercepts and potentially alters communications between two parties who believe they are communicating directly with each other. In the context of Blast-RADIUS, the MitM is positioned between the RADIUS client (access point) and the RADIUS server, enabling them to intercept and forge authentication responses.
The Blast-RADIUS attack requires MitM positioning. This is achievable through ARP spoofing on a shared network segment, compromise of an intermediate network device, or physical access to network infrastructure. Understanding this threat model helps IT teams prioritise network segmentation and device hardening alongside RADIUS-specific mitigations.
Case Studies
A 350-room luxury hotel chain with 12 properties is running Cisco Meraki access points with Microsoft NPS as the RADIUS server for staff WiFi. Authentication is via MSCHAPv2. The IT director has been alerted to CVE-2024-3596 and needs to assess exposure and implement mitigations without disrupting the 24/7 hotel operations.
The immediate priority is to confirm that Microsoft NPS has been updated to include the Message-Authenticator enforcement patch (released July 2024). In NPS, navigate to the RADIUS Clients and Servers configuration and enable the 'Require Message-Authenticator' setting for all configured RADIUS clients. On the Meraki side, confirm that the firmware version supports sending the Message-Authenticator attribute in Access-Request packets — Meraki released a firmware update addressing CVE-2024-3596 in Q3 2024. This configuration change can be deployed during a low-traffic window (typically 03:00–05:00 local time) with minimal guest impact, as it affects only staff authentication. Once Phase 1 is stable, plan the migration from MSCHAPv2 to EAP-TLS. Deploy a Microsoft Active Directory Certificate Services (ADCS) PKI to issue computer certificates to all staff devices via Group Policy. Configure NPS with an EAP-TLS network policy and update the Meraki SSID security settings to WPA2/WPA3-Enterprise with EAP-TLS. Use Meraki's Systems Manager MDM to push the NPS server certificate trust anchor to all managed devices. Roll out property-by-property to manage risk, starting with the lowest-occupancy property.
A national retail chain with 200 stores uses a centralised FreeRADIUS server for 802.1X authentication on its store network infrastructure. Each store has a mix of managed corporate devices (Windows laptops, handheld scanners) and unmanaged IoT devices (digital signage, payment terminals). The network team needs to harden against Blast-RADIUS while maintaining PCI DSS compliance for the payment card environment.
Begin with a network segmentation audit to confirm that RADIUS traffic between store access points and the central FreeRADIUS server is isolated from the payment card data environment (CDE). If RADIUS traffic traverses any segment that is in PCI DSS scope, this must be addressed as a priority. Update FreeRADIUS to version 3.2.3 or later, which includes the Message-Authenticator enforcement fix. In the FreeRADIUS clients.conf file, add 'require_message_authenticator = yes' for all store RADIUS clients. For the managed device fleet, deploy EAP-TLS using an existing PKI or a cloud certificate authority. For unmanaged IoT devices that cannot support 802.1X, implement MAC Authentication Bypass (MAB) on a separate, isolated VLAN with strict firewall rules preventing lateral movement to the CDE. This ensures that even if an IoT device's MAC address is spoofed, the attacker gains access only to the IoT VLAN, not the corporate or payment network. For the RADSEC migration, deploy a RADSEC proxy at each store that terminates the local UDP RADIUS traffic and forwards it over TLS to the central FreeRADIUS server, avoiding the need to upgrade every store's network device firmware simultaneously.
Scenario Analysis
Q1. Your organisation operates a 500-seat conference centre that hosts corporate events. The venue WiFi uses WPA2-Enterprise with PEAP/MSCHAPv2 and a FreeRADIUS server. A security consultant has flagged CVE-2024-3596 in their report. The venue director wants to know: (a) Are you currently vulnerable? (b) What is the minimum action required to close the immediate risk? (c) What is the recommended long-term architecture?
💡 Hint:Consider whether PEAP provides immunity to Blast-RADIUS, and what conditions must be met for that immunity to hold. Also consider the operational constraints of a 24/7 venue environment when planning the remediation timeline.
Show Recommended Approach
(a) PEAP with MSCHAPv2 uses an EAP tunnel that protects the inner authentication from the Blast-RADIUS attack, so you are not directly vulnerable to CVE-2024-3596 — provided that clients are correctly configured to validate the FreeRADIUS server certificate. If certificate validation is not enforced, you are vulnerable to rogue access point attacks, which is a separate but equally serious risk. You should still update FreeRADIUS to the patched version and enforce Message-Authenticator as a defence-in-depth measure. (b) The minimum immediate action is to update FreeRADIUS to version 3.2.3 or later and enforce Message-Authenticator in clients.conf. Simultaneously, audit all client devices to confirm server certificate validation is enabled. (c) The recommended long-term architecture is WPA3-Enterprise with EAP-TLS, backed by a PKI for certificate issuance. For a conference centre with high device turnover and BYOD, consider a cloud-based certificate authority with automated provisioning to reduce the operational burden of certificate management.
Q2. A retail chain's security team has completed a RADIUS audit and identified three categories of devices on their store networks: (1) managed Windows laptops using MS-CHAP, (2) Android handheld scanners using PAP, (3) IoT digital signage devices that do not support 802.1X at all. Prioritise the remediation actions and explain the rationale for each device category.
💡 Hint:Consider the relative vulnerability of each authentication mode, the feasibility of migrating each device category to EAP, and the appropriate network architecture for devices that cannot support 802.1X.
Show Recommended Approach
All three categories require action, but the approach differs. Category 1 (Windows laptops, MS-CHAP): Highest priority for EAP-TLS migration because MS-CHAP is directly vulnerable to Blast-RADIUS. Deploy computer certificates via Group Policy and migrate to EAP-TLS within 30–60 days. Enforce Message-Authenticator immediately as an interim measure. Category 2 (Android scanners, PAP): Also directly vulnerable. PAP transmits credentials in a form that is trivially readable if the RADIUS traffic is intercepted, making this the highest-risk category from a credential exposure perspective as well. Migrate to PEAP or EAP-TLS using Android's built-in 802.1X support. If the scanner firmware does not support EAP, prioritise firmware updates or device replacement. Category 3 (IoT signage, no 802.1X): Cannot be migrated to EAP. Implement MAC Authentication Bypass (MAB) on a dedicated IoT VLAN with strict firewall rules preventing access to the corporate network or CDE. Accept that MAB provides weaker authentication (MAC addresses can be spoofed) and compensate with network monitoring and anomaly detection.
Q3. A CTO at a 50-property hotel chain asks you to present the business case for a full RADIUS modernisation programme (EAP-TLS + RADSEC) with an estimated budget of £180,000 over 12 months. She wants to understand: the risk being mitigated, the compliance benefits, and the operational ROI beyond security. How do you structure the business case?
💡 Hint:Frame the business case around three pillars: risk quantification (what is the cost of a breach?), compliance value (what fines or audit costs does this avoid?), and operational efficiency (what does this enable beyond security?). Use the 350-room hotel scenario as a reference point.
Show Recommended Approach
Structure the business case around three pillars. Risk Quantification: A successful Blast-RADIUS exploit at a single property could provide network access to guest PII, payment systems, and back-office infrastructure. The average hospitality data breach costs £3M+ in remediation, notification, and reputational damage. At 50 properties, the aggregate risk is significant. The £180,000 investment represents less than 6% of a single breach cost. Compliance Value: PCI DSS v4.0 requires strong authentication for all systems in scope. EAP-TLS and RADSEC directly satisfy Requirements 8.6 (authentication management) and 1.3 (network segmentation). Avoiding a PCI DSS Level 1 forensic investigation (typically £50,000–£150,000) and potential card brand fines justifies the programme cost. GDPR Article 32 requires 'appropriate technical measures' — a documented modernisation programme demonstrates compliance due diligence. Operational ROI: Certificate-based authentication eliminates the overhead of managing shared WiFi passwords across 50 properties (estimated 2–4 hours per property per year for rotation and distribution). WPA3-Enterprise improves connection reliability in high-density environments, directly improving guest satisfaction scores. RADSEC's TCP transport reduces authentication failures in properties with high-latency WAN connections. Combined, these operational benefits represent an estimated 200–300 IT hours per year in saved administration time.
Key Takeaways
- ✓CVE-2024-3596 ('Blast-RADIUS') is a practically exploitable vulnerability in RADIUS/UDP that allows a man-in-the-middle attacker to forge authentication approvals without knowing user credentials, affecting all PAP, CHAP, and MS-CHAP deployments.
- ✓The attack exploits the MD5-based Response Authenticator field in RADIUS responses using a chosen-prefix collision technique that can be executed in minutes on modern hardware — making this a real operational threat, not a theoretical one.
- ✓The immediate mitigation is to apply vendor patches for CVE-2024-3596 and enforce the Message-Authenticator attribute on all RADIUS clients and servers — a low-disruption configuration change available from all major vendors including Cisco, Microsoft NPS, FreeRADIUS, Aruba, and Ruckus.
- ✓EAP-based authentication methods (EAP-TLS, PEAP, EAP-TTLS) are immune to the Blast-RADIUS attack, making migration to WPA3-Enterprise with EAP-TLS the recommended medium-term strategic response.
- ✓RADIUS over TLS (RADSEC, RFC 6614) is the long-term architectural solution, encapsulating all RADIUS traffic in a mutually authenticated TLS tunnel and eliminating the transport-layer vulnerability entirely.
- ✓For hospitality, retail, and venue operators, the compliance implications are direct: a successful exploit can trigger PCI DSS violations, GDPR data breach notifications, and significant financial and reputational damage that far exceeds the cost of remediation.
- ✓Network segmentation (dedicated RADIUS VLANs) reduces the attack surface but does not eliminate the vulnerability — it must be combined with Message-Authenticator enforcement and EAP migration to provide genuine protection.



