O que é um Controlador WiFi e Precisa de Um?
This authoritative guide provides IT leaders and network architects with a practical overview of WiFi controllers, detailing their function, comparing on-premises and cloud-based models, and explaining how they integrate with WiFi intelligence platforms like Purple. It offers actionable insights for deploying scalable, secure, and high-performance wireless networks in enterprise environments such as hospitality, retail, and large venues. By the end, readers will have a clear framework for choosing the right controller architecture and understanding where a platform like Purple adds transformative business value.
🎧 Listen to this Guide
View Transcript
Resumo Executivo
Um Wireless LAN Controller (WLC), ou controlador WiFi, é um componente de rede centralizado que gere múltiplos pontos de acesso (APs) a partir de uma única interface, garantindo a aplicação consistente de políticas, uma administração simplificada e segurança reforçada em toda a rede sem fios empresarial. Para gestores de TI, arquitetos de redes e CTOs que supervisionam a conectividade em locais como hotéis, cadeias de retalho ou estádios, o controlador é o cérebro da operação. Automatiza funções críticas como a gestão de radiofrequência (RF), o roaming de clientes, a autenticação e o balanceamento de carga — funções que são simplesmente impossíveis de gerir em grande escala com APs isolados ou 'autónomos'.
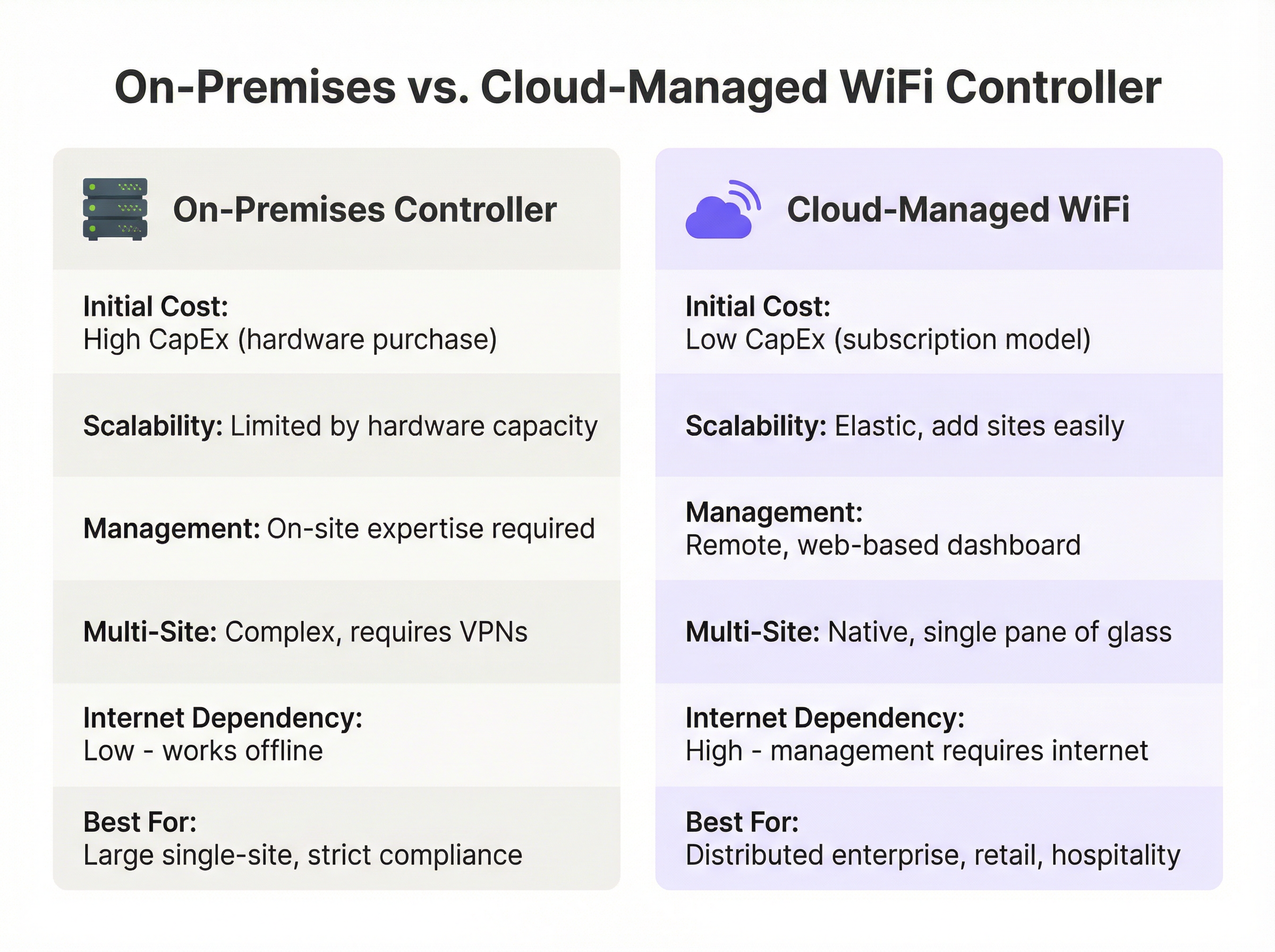
A principal decisão que as lideranças enfrentam hoje não é se devem usar um controlador, mas sim qual o modelo de implementação a adotar: um controlador de hardware tradicional no local (on-premises) ou uma solução moderna baseada na cloud. Os controladores on-premises oferecem um controlo granular e mantêm todo o processamento de dados local, um requisito fundamental para certos quadros de conformidade, mas exigem despesas de capital (CapEx) significativas e conhecimentos especializados no local. Por outro lado, o WiFi gerido na cloud transfere a gestão para um serviço baseado em subscrição, oferecendo uma escalabilidade superior, aprovisionamento zero-touch para implementações em vários locais e uma redução dos custos operacionais.
A Purple atua como uma poderosa camada de inteligência, integrando-se com a infraestrutura de controladores existente de fornecedores como a Cisco, Aruba e Ruckus para fornecer serviços avançados de WiFi para convidados, análises e capacidades de marketing sem alterar a estrutura central da rede. Este guia fornece uma análise técnica aprofundada destas arquiteturas para o ajudar a determinar a estratégia certa para a sua organização.
Análise Técnica Aprofundada
Na sua essência, um controlador WiFi resolve o problema da escala. Um único ponto de acesso é simples de configurar, mas gerir dez, cem ou mil APs individualmente é insustentável. A arquitetura WLC centraliza esta gestão, criando um sistema unificado e inteligente. Isto é normalmente alcançado utilizando o protocolo Control and Provisioning of Wireless Access Points (CAPWAP), uma norma IETF definida no RFC 5415. O CAPWAP cria um túnel seguro entre cada AP e o controlador, separando as funções de gestão e controlo (o 'control plane') do tráfego de dados do utilizador final (o 'data plane').
As Principais Funções do Controlador abrangem todo o ciclo de vida da gestão de redes sem fios. A Gestão Centralizada de APs é o papel mais fundamental: a partir do controlador, os administradores podem enviar atualizações de firmware, configurar SSIDs, definir políticas de segurança como o WPA3-Enterprise e definir VLANs para todos os APs ligados em simultâneo. A Gestão Dinâmica de RF permite que o controlador monitorize continuamente o espetro de radiofrequência, ajustando automaticamente as atribuições de canais dos APs e os níveis de potência para mitigar interferências e otimizar a cobertura. O Roaming de Clientes Contínuo é facilitado pelo controlador, que gere as chaves de segurança e o estado da sessão à medida que os utilizadores se movem entre APs, tirando partido das normas 802.11k/v/r para transições rápidas. A Autenticação e Aplicação de Políticas permite que o WLC atue como um guardião central, integrando-se com um servidor RADIUS e o IEEE 802.1X para conceder acesso à rede com base na identidade do utilizador e na postura do dispositivo, permitindo um controlo de acesso robusto baseado em funções.
On-Premises vs. Gerido na Cloud: O Compromisso Arquitetónico
A escolha estratégica entre um WLC on-premises e um gerido na cloud tem implicações significativas a nível de custos, escalabilidade e operações. A tabela abaixo resume os principais compromissos.
| Funcionalidade | Controlador On-Premises | WiFi Gerido na Cloud |
|---|---|---|
| Modelo de Implementação | Appliance física ou virtual num data center local | Plano de gestão alojado por um fornecedor externo |
| Custo Inicial (CapEx) | Elevado — appliances de hardware com limites de capacidade específicos | Baixo — não requer hardware de controlador no local |
| Custo Operacional (OpEx) | Custos recorrentes mais baixos, mas inclui energia e manutenção | Custos recorrentes mais elevados através de licença de subscrição anual |
| Escalabilidade | Limitada pela capacidade do hardware; as atualizações exigem novo hardware | Altamente elástica; novos APs e locais adicionados com um ajuste de licença |
| Gestão Multi-Local | Complexa; requer frequentemente VPNs ou controladores dedicados por local | Simples; um único dashboard web fornece uma visão global unificada |
| Dependência da Internet | Baixa; o WiFi principal continua a funcionar se a internet falhar | Elevada; internet necessária para gestão e configuração |
| Conformidade e Dados | Ideal para requisitos rigorosos de soberania de dados | Requer due diligence do fornecedor para conformidade com o GDPR e PCI DSS |
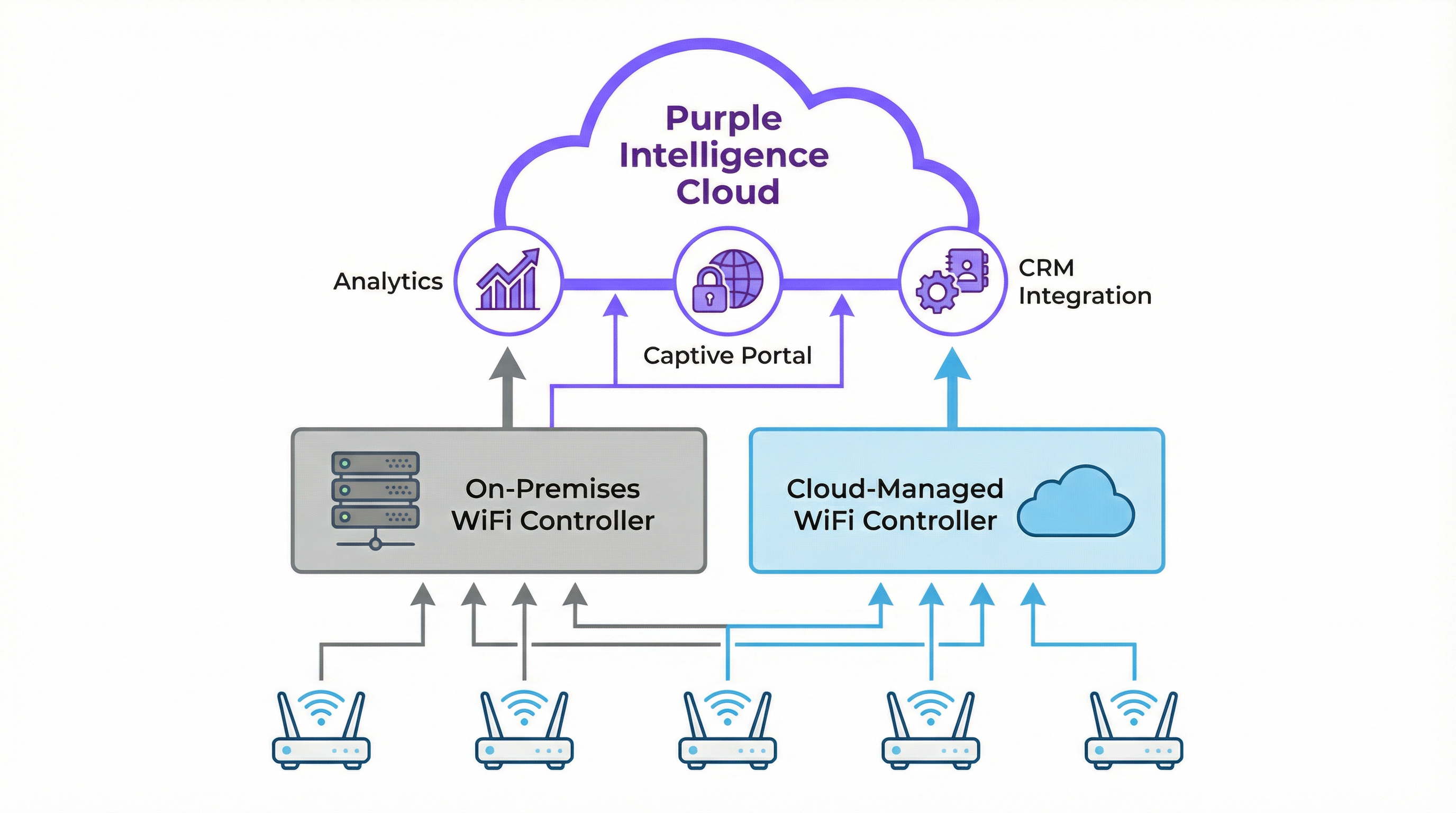
Como a Purple se Integra com o seu Controlador
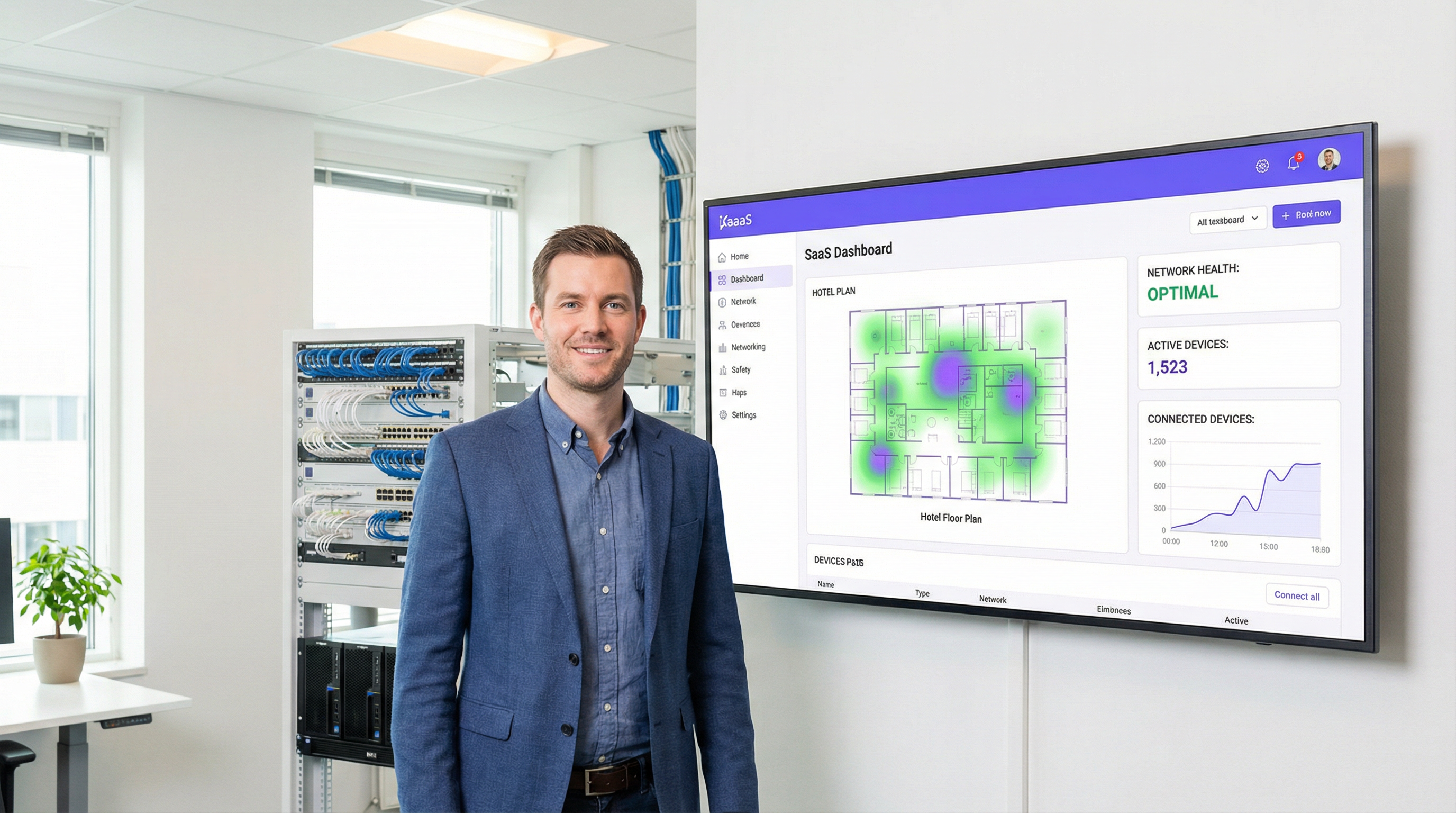
A Purple é uma plataforma de inteligência WiFi baseada na cloud que funciona como uma camada sofisticada, melhorando as capacidades da sua infraestrutura de rede existente em vez de a substituir. Integra-se perfeitamente com arquiteturas de controladores on-premises e geridos na cloud de mais de 200 fornecedores de hardware.
A integração segue uma sequência clara. Primeiro, o controlador WiFi é configurado para redirecionar todos os novos dispositivos de convidados não autenticados para o Captive Portal da Purple. O utilizador autentica-se então através de uma página de splash personalizada, utilizando logins sociais, a submissão de um formulário ou perfis Passpoint/OpenRoaming contínuos — um processo totalmente em conformidade com o GDPR e o CCPA. Após uma autenticação bem-sucedida, a Purple captura dados demográficos e comportamentais valiosos (opt-in), que alimentam o motor de análise e podem ser integrados com o seu CRM. Por fim, a Purple sinaliza o controlador para conceder acesso à internet ao dispositivo, aplicando quaisquer políticas predefinidas, como limites de largura de banda, duração da sessão ou filtragem de conteúdos através do Purple Shield.
Este modelo permite que as organizações retenham o seu investimento em hardware robusto de nível empresarial, ao mesmo tempo que adicionam ferramentas poderosas de análise e envolvimento de convidados que impulsionam o valor do negócio.
Guia de Implementação
A implementação ou atualização da arquitetura do seu controlador WiFi requer uma abordagem estruturada. Este guia, neutro em relação a fornecedores, descreve as principais fases para uma implementação bem-sucedida.
Fase 1: Descoberta e Levantamento de Requisitos. Realize um estudo de RF físico ou preditivo para determinar o número e a localização ideais dos pontos de acesso, tendo em conta os materiais de construção, a densidade de utilizadores e os requisitos de débito das aplicações. Documente os principais casos de uso — acesso de convidados, pessoal interno, sistemas de ponto de venda, dispositivos IoT — uma vez que estes ditarão as políticas de segmentação e segurança. Catalogue a sua infraestrutura de rede atual e identifique todos os requisitos regulamentares, incluindo o PCI DSS para o retalho e o GDPR para o tratamento de dados de cidadãos da UE.
Fase 2: Seleção da Arquitetura. Utilize a tabela de comparação e o diagrama de fluxo de decisão deste guia para escolher entre soluções on-premises e geridas na cloud. Para a maioria das empresas com vários locais nos setores do retalho, hotelaria e similares, a eficiência operacional e a escalabilidade de uma arquitetura gerida na cloud apresentam um business case muito atrativo.
Fase 3: Implementação e Configuração. Configure VLANs separadas para cada grupo de utilizadores (Convidados, Pessoal, Corporativo, IoT) — esta é uma medida de segurança crítica. Para sistemas geridos na cloud, pré-registe os APs no dashboard para permitir o aprovisionamento zero-touch. Implemente o WPA3-Enterprise com o IEEE 802.1X para todas as redes seguras. Para a rede de convidados, configure um SSID aberto com o isolamento de clientes ativado, forçando todo o tráfego através do Captive Portal da Purple. Configure o URL do Captive Portal da Purple como a fonte de autenticação externa nas definições do seu controlador e adicione os endereços IP necessários às suas listas de controlo de acesso de pré-autenticação.
Fase 4: Testes e Validação. Realize um estudo de RF pós-implementação para verificar a cobertura. Teste o processo de integração (onboarding) para cada grupo de utilizadores. Efetue testes de débito utilizando ferramentas como o iPerf para garantir que a rede cumpre os padrões de desempenho.
Melhores Práticas
Priorizar a segurança através da segmentação da rede não é negociável. O tráfego de convidados nunca deve partilhar uma VLAN com o tráfego corporativo ou em conformidade com o PCI. A ativação do isolamento de clientes nas redes de convidados é uma funcionalidade crítica do WLC que impede que os clientes sem fios comuniquem entre si, mitigando os riscos de ataques peer-to-peer. A centralização da autenticação com um servidor RADIUS em conjunto com o WLC fornece uma base de dados única e auditável de utilizadores e políticas. As atualizações regulares de firmware, tanto para o controlador como para os APs, são essenciais, uma vez que se tratam de ativos de segurança críticos. As soluções geridas na cloud automatizam normalmente este processo, o que constitui uma vantagem operacional significativa. Por fim, a monitorização contínua através do dashboard do controlador e das análises da Purple permite às equipas de TI identificar proativamente problemas de desempenho, APs não autorizados (rogue APs) e anomalias de segurança antes que afetem os utilizadores.
Resolução de Problemas e Mitigação de Riscos
Quando os clientes não se conseguem ligar, o primeiro passo de diagnóstico é verificar o controlador quanto a erros de autenticação: verifique se o servidor RADIUS está acessível, se as credenciais do cliente estão corretas e se os endereços IP do portal da Purple estão corretamente na whitelist das ACLs de pré-autenticação do controlador. O fraco desempenho da rede sem fios aponta normalmente para interferências de RF ou canais sobrecarregados, o que pode ser diagnosticado através do dashboard de gestão de RF do controlador. Áreas de alta densidade podem exigir APs adicionais ou uma reavaliação das atribuições de canais.
Para implementações on-premises, o principal risco é a falha do hardware do controlador. Isto é mitigado através da implementação de controladores num par de alta disponibilidade (HA) — uma configuração ativo/passivo — e da manutenção de backups regulares da configuração do controlador. Para redes geridas na cloud, o risco é a perda de conectividade à internet. Os APs devem ser configurados para continuar a fornecer acesso à rede local durante as falhas, e os serviços operacionais críticos não devem depender da ligação de gestão na cloud.
ROI e Impacto no Negócio
Uma rede sem fios devidamente arquitetada não é um centro de custos; é um facilitador de negócios. O ROI vai muito além do fornecimento de uma simples ligação à internet. A gestão centralizada reduz drasticamente os custos indiretos de TI, tal como demonstrado pela McDonald's, onde as análises e as capacidades de gestão remota da Purple levaram a uma redução de 90% nas visitas de engenheiros de TI aos locais, com 4 milhões de logins WiFi por restaurante por ano e 2,5 milhões de utilizadores únicos capturados no CRM.
Um WiFi rápido, fiável e de fácil acesso é agora uma expetativa básica na hotelaria e no retalho. Uma experiência contínua, facilitada pelo roaming gerido pelo controlador e por uma integração simples através do portal da Purple, tem um impacto direto na satisfação e fidelização dos clientes. Ao integrar a Purple, a rede WiFi transforma-se numa rica fonte de dados first-party, permitindo aos operadores dos locais medir o tráfego de pessoas (footfall), os tempos de permanência e a frequência dos visitantes. Estes dados proporcionam um ROI tangível, com os clientes da Purple a registarem um ROI médio de 873%. Para locais como centros de conferências ou hotéis, o acesso WiFi premium por níveis também se pode tornar num fluxo de receitas direto, facilmente gerido e automatizado através do controlador e da plataforma Purple.
Key Terms & Definitions
Wireless LAN Controller (WLC)
A centralized network appliance or cloud service that configures, manages, and monitors wireless access points at scale, handling functions such as RF management, roaming, authentication, and security policy enforcement.
This is the core component for any enterprise-grade WiFi deployment. IT teams use the WLC to avoid having to configure hundreds of APs individually and to ensure a consistent, secure experience across the entire network.
Access Point (AP)
A hardware device that creates a wireless local area network (WLAN) by transmitting and receiving radio signals. In a controller-based architecture, APs are 'lightweight' devices whose intelligence is provided by the central WLC.
These are the physical devices installed in ceilings and walls throughout a venue. In enterprise settings, they are often referred to as 'thin' or 'lightweight' APs because the controller provides their configuration and management logic.
Cloud-Managed WiFi
An architecture where the WLC functionality is hosted in the cloud as a subscription service, allowing for centralized management of geographically distributed APs via a web-based dashboard without any on-site controller hardware.
This is the dominant model for retail, hospitality, and distributed enterprises due to its scalability and operational simplicity. Purple is a cloud-native platform that integrates perfectly with this model.
CAPWAP (Control and Provisioning of Wireless Access Points)
An IETF standard protocol (RFC 5415) that enables a WLC to manage a collection of access points by establishing a secure, encrypted tunnel for control traffic and, optionally, data traffic.
This is the technical underpinning of how controllers and APs communicate. Understanding CAPWAP is essential for troubleshooting connectivity issues between the controller and its managed APs, particularly in complex network topologies.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication framework requiring devices to present valid credentials before being granted access to a LAN or WLAN.
This is the gold standard for securing corporate wireless networks. It requires users to authenticate with unique credentials before being granted access, managed by the WLC in conjunction with a RADIUS server. It is a key requirement for PCI DSS and ISO 27001 compliance.
Captive Portal
A web page displayed to newly connected users of a WiFi network before they are granted broader internet access, typically used for authentication, terms-of-service acceptance, or data capture.
This is Purple's core entry point for guest users. The WLC is configured to redirect all unauthenticated guest devices to the Purple captive portal, which then handles the entire user onboarding journey, from authentication to data capture.
Network Segmentation
The practice of dividing a computer network into distinct subnetworks (VLANs) to improve security, performance, and compliance by preventing unauthorized traffic between segments.
This is a non-negotiable best practice enforced via the WLC. Separating guest traffic from corporate and POS systems is a fundamental security requirement and a compliance obligation under PCI DSS for any organization processing card payments.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards mandating that all companies that accept, process, store, or transmit credit card information maintain a secure environment, including strict network segmentation requirements.
For any retail or hospitality client, the WLC and network architecture must be configured to meet PCI DSS requirements. Failure to comply can result in significant fines and the revocation of the ability to process card payments.
Case Studies
A 250-room luxury hotel needs to upgrade its legacy WiFi network to provide seamless, high-performance coverage for guests and staff while enabling marketing to capture guest data for loyalty programs. The hotel has a central server room and a dedicated IT team.
1. Architecture Choice: A hybrid approach is recommended. Deploy on-premises controllers in a high-availability (HA) pair to manage all on-site access points. This ensures maximum performance and resilience for in-room streaming and staff operational systems. 2. Network Segmentation: Create distinct VLANs and SSIDs: 'HotelGuest' (open, with captive portal), 'Staff_Secure' (WPA3-Enterprise with 802.1X), and 'POS_Systems' (WPA3-Enterprise, highly restricted, firewalled from guest VLAN). 3. Purple Integration: Configure the controllers to redirect the 'HotelGuest' SSID to the Purple cloud-based captive portal. The portal handles guest authentication via room number and last name, or social login, and captures opt-in marketing consent. 4. Policy Enforcement: The controller enforces a bandwidth limit of 25 Mbps per guest device, while the Purple platform manages session duration and feeds data directly into the hotel's Salesforce CRM, enabling targeted loyalty campaigns.
A retail chain with 80 stores across the country wants to standardize its in-store guest WiFi experience, centrally manage all networks, and use WiFi analytics to understand customer footfall patterns. Each store has limited on-site technical staff.
1. Architecture Choice: A fully cloud-managed WiFi solution is the clear choice. Equip each store with cloud-managed access points from a single vendor. There is no need for an on-premises controller in any store. 2. Zero-Touch Provisioning: APs are pre-configured in the central cloud dashboard and shipped to each store. The local store manager simply plugs them in — the AP automatically downloads its configuration. 3. Centralized Management: From corporate headquarters, the IT team uses a single web dashboard to monitor all 80 stores, push configuration updates, and manage security policies simultaneously. 4. Purple Integration: The cloud controller is configured globally to use Purple for guest authentication across all stores, ensuring a consistent branded experience. Purple's analytics dashboard provides footfall, dwell time, and loyalty metrics for every store, enabling direct comparison of performance across the estate.
Scenario Analysis
Q1. A large conference center is preparing for a major tech summit expecting 10,000 concurrent users, all requiring high-throughput video streaming. They have a large, expert IT team on-site and a dedicated server room. Which controller architecture should they primarily rely on and why?
💡 Hint:Consider the requirements for latency, throughput, and the value of on-site expertise in a single-location, high-density scenario.
Show Recommended Approach
They should deploy a high-capacity, on-premises controller cluster in a high-availability (active/standby) configuration. For a high-density, single-site event, minimizing latency and maximizing throughput is critical. Routing all traffic through a powerful on-site controller avoids the latency of cloud-based data paths and provides the advanced RF management needed to handle 10,000 concurrent users. The presence of an expert on-site IT team mitigates the management overhead of an on-premises solution. Purple would be integrated as an overlay for guest authentication and analytics.
Q2. A fast-growing coffee shop chain plans to expand from 10 to 50 locations in the next year. They want to offer a consistent, branded guest WiFi experience at all stores and use the data for marketing campaigns. Their corporate IT team consists of just two people. What is the single most critical feature they should look for in a WiFi solution?
💡 Hint:Think about the operational challenge of deploying and managing 50 separate locations with a two-person IT team.
Show Recommended Approach
The most critical feature is zero-touch provisioning via a cloud-based management dashboard. This will allow their small IT team to pre-configure access points in the cloud dashboard and ship them to new stores. The local store manager simply plugs in the AP, and it automatically downloads its configuration — no specialist IT visit required. A cloud architecture is essential for them to scale rapidly and manage all 50 locations from a single interface, ensuring a consistent guest experience and centralized data collection via Purple.
Q3. A hospital needs to provide guest WiFi for patients and visitors while ensuring that patient health records, stored on a separate internal clinical network, remain completely isolated and secure. How should the IT team use a WLC to achieve this, and what specific configuration steps are required?
💡 Hint:Focus on the security and traffic separation capabilities of the WLC, and consider both the technical and compliance dimensions.
Show Recommended Approach
The IT team must use the WLC to implement strict network segmentation. The specific steps are: (1) Create a dedicated 'Guest' SSID on a separate VLAN (e.g., VLAN 100) that is completely firewalled from all internal clinical VLANs. (2) Configure an Access Control List (ACL) on the controller that explicitly denies any traffic originating from VLAN 100 from reaching the internal network segments. (3) Enable 'client isolation' on the guest SSID to prevent guest devices from communicating with each other. (4) Configure the guest SSID to redirect unauthenticated clients to the Purple captive portal for terms-of-service acceptance. This architecture ensures compliance with healthcare data regulations and protects patient data from both external and internal threats.
Key Takeaways
- ✓A WiFi Controller (WLC) centralizes the management of multiple access points, providing the consistency, security, and scalability that enterprise wireless networks demand.
- ✓The primary architectural choice is between on-premises controllers (high control, high CapEx, ideal for single-site or strict compliance environments) and cloud-managed controllers (high scalability, subscription-based, ideal for distributed enterprises).
- ✓Cloud-managed WiFi is the dominant choice for distributed enterprises in retail and hospitality due to zero-touch provisioning, single-pane-of-glass management, and elastic scalability.
- ✓Purple is a cloud-based intelligence platform that acts as an overlay on existing WiFi infrastructure — it does not replace the controller, but enhances it with guest authentication, analytics, and CRM integration.
- ✓Security is non-negotiable: use the WLC to enforce network segmentation (separate VLANs for guests, staff, and POS), enable client isolation on guest networks, and implement WPA3-Enterprise with IEEE 802.1X for secure access.
- ✓The ROI of a modern WiFi architecture is driven by operational efficiency, enhanced customer experience, and the business intelligence derived from WiFi analytics — Purple customers see an average ROI of 873%.
- ✓The core framework: your controller manages the APs; a platform like Purple manages the users — turning connectivity from a cost centre into a source of measurable business value.



