WiFi Hotspot 2.0 (Passpoint): O Guia Definitivo para um Roaming WiFi Contínuo e Seguro
This guide provides a comprehensive technical overview of WiFi Hotspot 2.0 (Passpoint) for IT leaders. It details the technology, security benefits, and a step-by-step implementation framework for deploying seamless, secure WiFi roaming in enterprise environments like hotels, retail, and large venues, ultimately improving user experience and reducing operational overhead.
🎧 Listen to this Guide
View Transcript

Resumo Executivo
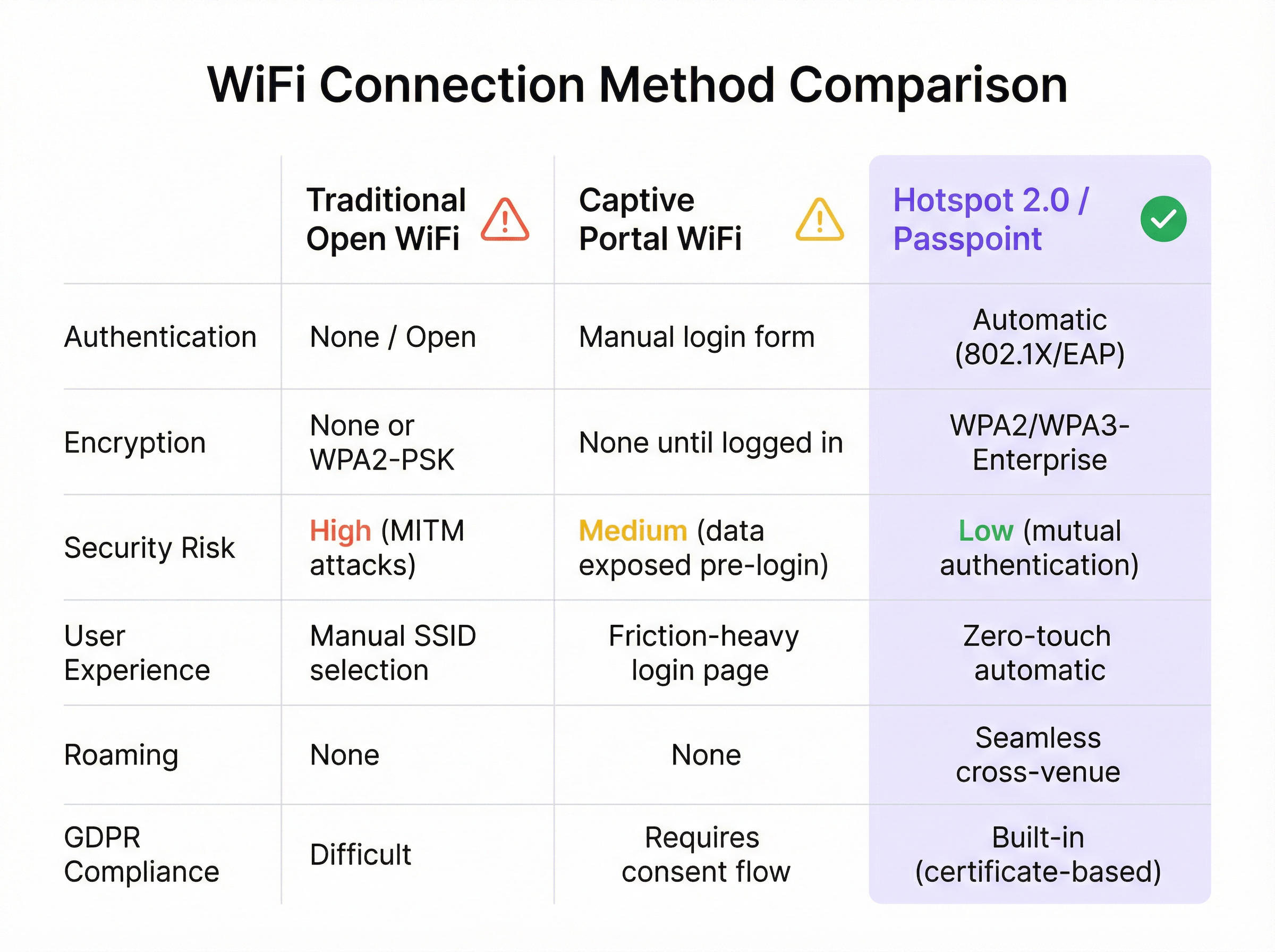
Para a empresa moderna, oferecer uma experiência WiFi contínua e segura já não é um luxo — é um requisito operacional central. O WiFi Hotspot 2.0, também conhecido como Passpoint, é uma framework padrão da indústria concebida para eliminar a fricção e os riscos de segurança associados ao WiFi público e de convidados tradicional. Permite que os dispositivos móveis descubram e se autentiquem automaticamente em redes WiFi com segurança WPA3 de nível empresarial, refletindo a experiência de roaming contínuo das redes móveis. Para um CTO ou Diretor de TI, isto traduz-se numa redução significativa dos problemas de ligação enfrentados pelos utilizadores, numa postura de segurança reforçada contra ataques WiFi comuns e num processo de autenticação otimizado que é simultaneamente compatível com o GDPR e imune aos desafios da aleatorização de endereços MAC. Ao substituir Captive Portals inseguros e de alta fricção por uma autenticação baseada em credenciais e sem intervenção (zero-touch), o Passpoint melhora a satisfação dos convidados, reduz a sobrecarga de suporte de TI e fornece uma base escalável para estratégias de roaming entre locais e descarregamento de dados (data offload). Este guia fornece os detalhes técnicos e a framework de implementação necessários para integrar o Passpoint na sua infraestrutura de rede, impulsionando melhorias tangíveis tanto na segurança como na experiência do utilizador.
Análise Técnica Aprofundada
O Hotspot 2.0 e a sua certificação subjacente, o Passpoint, representam uma mudança arquitetónica fundamental na forma como as redes WiFi são descobertas e acedidas. A tecnologia baseia-se na emenda IEEE 802.11u, que permite a comunicação de pré-associação entre um dispositivo cliente e um ponto de acesso. Isto permite que um dispositivo recolha informações críticas sobre uma rede antes de se comprometer com uma ligação, passando de um modelo obsoleto de reconhecimento de SSID para um modelo mais inteligente de reconhecimento de credenciais.
Protocolos Principais: ANQP, GAS e 802.11u
O principal mecanismo que permite este diálogo de pré-associação é uma combinação do Generic Advertisement Service (GAS) e do Access Network Query Protocol (ANQP). Eis como interagem:
- Beaconing IEEE 802.11u: Um Ponto de Acesso (AP) com Passpoint ativado inclui um Interworking Element (IE) nas suas tramas de beacon. Este atua como um sinalizador, anunciando aos dispositivos próximos que suporta a descoberta avançada de rede.
- Troca GAS e ANQP: Um dispositivo cliente que detete este IE pode iniciar uma consulta GAS ao AP. Dentro desta consulta, utiliza o ANQP para fazer perguntas específicas sobre a identidade e as capacidades da rede. A consulta mais crítica é a dos Roaming Consortium Organizational Identifiers (RCOIs) suportados pela rede.
- Correspondência de Credenciais: O AP responde com a sua lista de RCOIs suportados. Se algum destes corresponder a um perfil de credenciais armazenado no dispositivo cliente (por exemplo, um perfil de uma operadora móvel, de uma marca de hotel ou de uma rede corporativa), o dispositivo sabe que se pode autenticar e avança para o passo seguinte. Se não for encontrada nenhuma correspondência, o dispositivo simplesmente ignora a rede, tudo sem qualquer interação do utilizador.
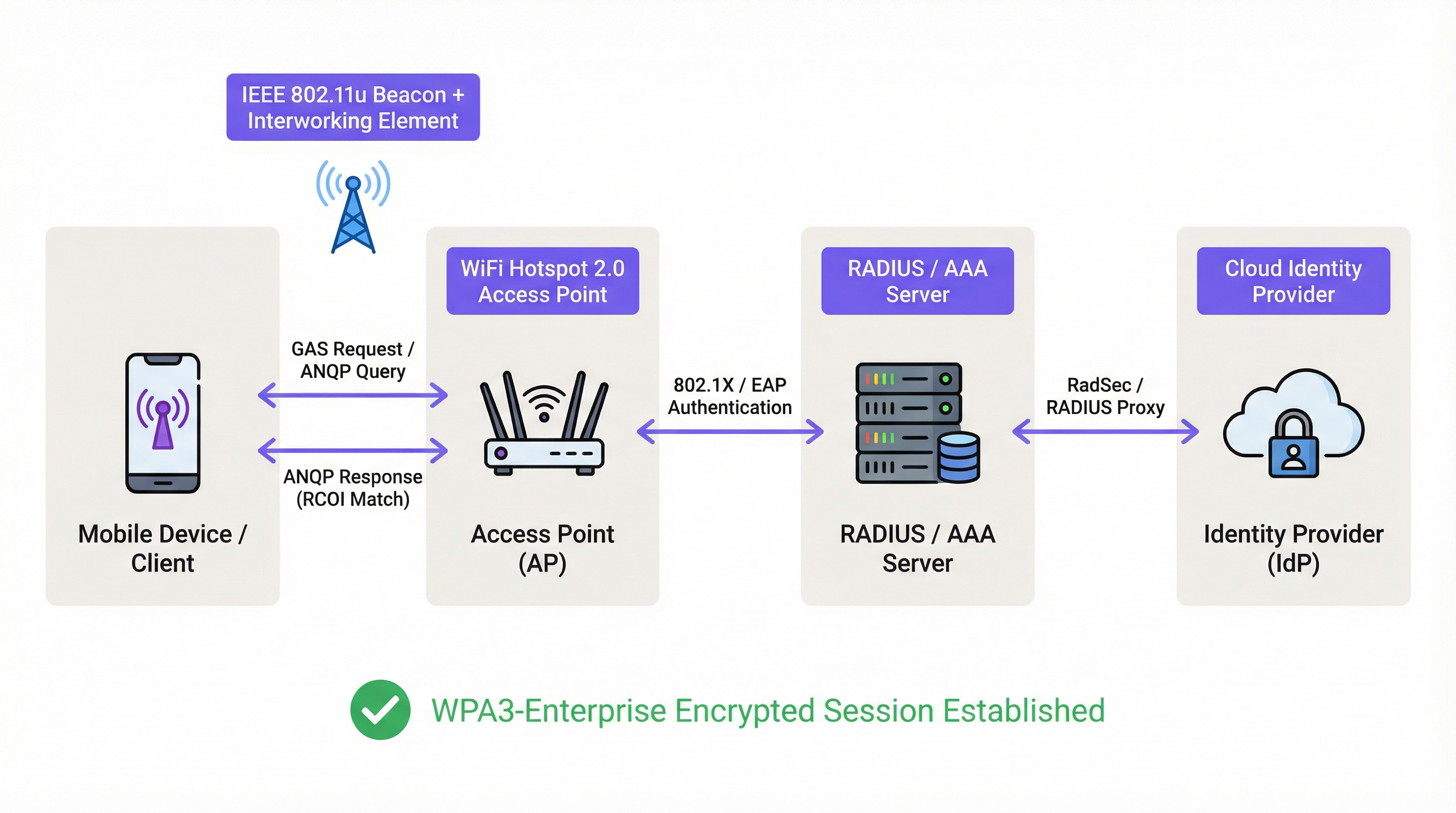
Framework de Autenticação e Segurança
Uma vez confirmada a correspondência de credenciais, o Passpoint tira partido da segurança robusta do IEEE 802.1X para autenticação, tipicamente com encriptação WPA2-Enterprise ou a mais segura WPA3-Enterprise. Este é o mesmo padrão de controlo de acesso à rede baseado em portas em que se confia nas redes empresariais com fios seguras. A autenticação é gerida através de um método Extensible Authentication Protocol (EAP), tal como:
- EAP-TLS: Autenticação baseada em certificados, considerada o padrão de excelência em segurança. Tanto o cliente como o servidor apresentam certificados para provar a sua identidade.
- EAP-TTLS/PEAP: Encapsula um método de autenticação legado (como nome de utilizador/palavra-passe) dentro de um túnel TLS seguro.
- EAP-SIM/AKA/AKA': Autenticação baseada em SIM, permitindo que os operadores de redes móveis façam o roaming contínuo dos seus subscritores para redes WiFi de confiança.
Este processo garante a autenticação mútua: o cliente valida que a rede é legítima (prevenindo ataques de AP 'Evil Twin') e a rede valida que o cliente está autorizado. Todo o tráfego subsequente é encriptado, mitigando o risco de ataques man-in-the-middle (MITM) comuns em redes abertas ou baseadas em PSK.
Passpoint vs. OpenRoaming
É crucial distinguir entre Passpoint e OpenRoaming:
O Passpoint é o veículo; o OpenRoaming é o sistema de autoestradas.
- O Passpoint é o padrão técnico (802.11u, ANQP/GAS, 802.1X) que permite a um dispositivo descobrir e autenticar-se automaticamente numa única rede ou num grupo de redes sob o mesmo controlo administrativo.
- O WBA OpenRoaming é uma framework de federação global gerida pela Wireless Broadband Alliance. Cria um ecossistema de confiança entre milhares de Fornecedores de Identidade (IdPs), como operadoras móveis, e Fornecedores de Redes de Acesso (ANPs), como hotéis, aeroportos e cadeias de retalho. Isto permite que um utilizador com uma credencial de qualquer IdP membro se ligue automaticamente em qualquer local de um ANP membro, sem necessitar de acordos de roaming bilaterais complexos.
Para máxima compatibilidade num ambiente OpenRoaming, os arquitetos de rede devem transmitir tanto o RCOI standard isento de liquidação (5A-03-BA) como o RCOI legado da Cisco (00-40-96).
Guia de Implementação
A implementação do Passpoint é um processo estruturado que vai desde a auditoria da sua infraestrutura existente até a um lançamento faseado e otimização. Seguir este roteiro garantirá uma transição suave e mitigará as armadilhas comuns de implementação.
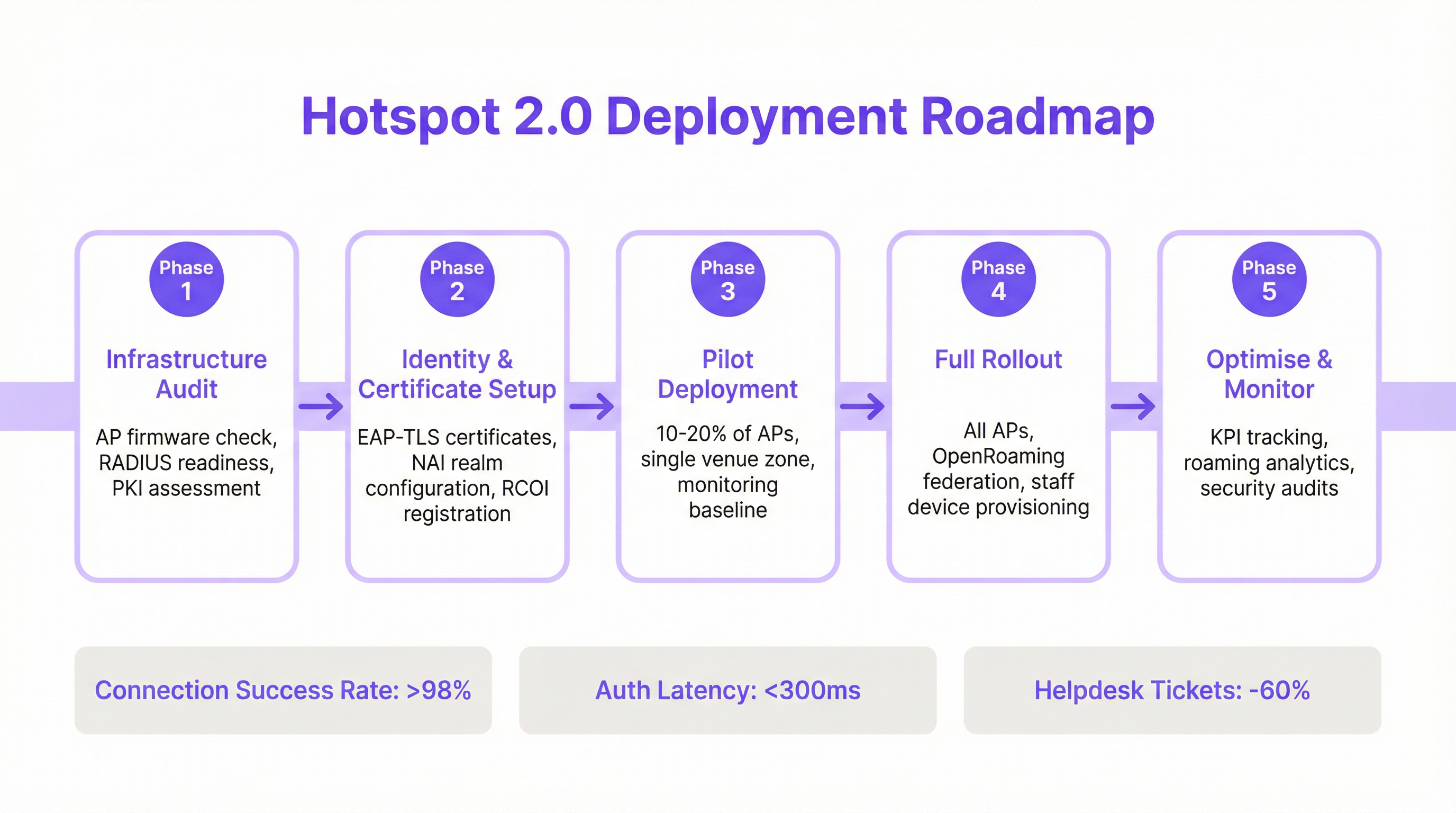
Fase 1: Auditoria da Infraestrutura
Antes de começar, avalie o hardware e software da sua rede atual. Os principais pontos de auditoria incluem:
- Compatibilidade dos Pontos de Acesso: Verifique se os seus APs suportam IEEE 802.11u. A maioria dos APs de nível empresarial fabricados após 2015 (de fornecedores como Cisco, HPE Aruba, Juniper Mist, Ruckus) possui o hardware necessário, mas pode exigir uma atualização de firmware.
- Prontidão do Servidor RADIUS: Precisará de um servidor RADIUS (ou AAA) capaz de lidar com a autenticação 802.1X EAP. Pode ser uma solução local (on-premise) como o Cisco ISE ou um serviço baseado na cloud como o SecureW2, Foxpass ou Google Cloud Identity.
- Avaliação de PKI: Para implementações EAP-TLS, é necessária uma Infraestrutura de Chave Pública (PKI) para emitir e gerir certificados digitais para dispositivos clientes e servidores.
Fase 2: Configuração de Identidade e Certificados
Esta fase envolve a configuração dos componentes centrais de autenticação:
- Configuração do Realm NAI: Defina os seus realms de Network Access Identifier (NAI), que identificam o seu domínio de autenticação (por exemplo,
@suaempresa.com). - Registo de RCOI: Se participar num consórcio de roaming como o OpenRoaming, registe os seus RCOIs junto da WBA.
- Geração de Certificados: Para EAP-TLS, gere e implemente certificados de cliente nos seus dispositivos geridos através de uma solução de Mobile Device Management (MDM). Para acesso de convidados, precisará de um mecanismo para aprovisionar um perfil com a cadeia de confiança de certificados necessária.
Fase 3: Implementação Piloto
Comece com um piloto controlado numa área limitada, como um único piso ou uma zona específica do local, cobrindo 10 a 20% dos seus APs. Os objetivos do piloto são:
- Estabelecer uma Linha de Base: Meça as atuais taxas de sucesso de ligação, a latência de autenticação e o volume de tickets de helpdesk relacionados com o WiFi.
- Testar a Matriz de Dispositivos: Teste a experiência de integração (onboarding) e ligação numa vasta gama de dispositivos (iOS, vários fabricantes Android como Samsung e Google Pixel, Windows, macOS).
- Refinar o Onboarding: Otimize o processo de instalação do perfil Passpoint em dispositivos de convidados não geridos.
Fase 4: Lançamento Completo
Assim que o piloto atingir os seus critérios de sucesso (por exemplo, >98% de sucesso de ligação, latência de autenticação <300ms), avance para um lançamento completo em todos os APs e locais. Esta fase inclui:
- Configuração Completa dos APs: Envie a configuração WLAN Passpoint padronizada para todos os pontos de acesso.
- Aprovisionamento de Dispositivos Corporativos e de Funcionários: Garanta que todos os dispositivos propriedade da empresa são aprovisionados com o perfil Passpoint via MDM.
- Ativar a Federação OpenRoaming: Se aplicável, ative as regras de proxy RADIUS para participar na federação OpenRoaming.
Fase 5: Otimizar e Monitorizar
Após o lançamento, monitorize continuamente o desempenho e a segurança da rede:
- Acompanhamento de KPIs: Acompanhe os principais indicadores de desempenho, comparando-os com a linha de base do piloto. As principais métricas incluem a taxa de sucesso de ligação, a latência de autenticação, o sucesso de roaming e o débito de dados (throughput).
- Análise de Roaming: Utilize análises para compreender os padrões de roaming entre os seus locais e com parceiros de roaming.
- Auditorias de Segurança: Realize auditorias de segurança regulares para garantir a integridade da sua infraestrutura RADIUS e PKI.
Melhores Práticas
Para maximizar o sucesso e a segurança da sua implementação Passpoint, adira às seguintes melhores práticas padrão da indústria.
| Categoria | Melhor Prática | Justificação |
|---|---|---|
| Segurança | Exigir WPA3-Enterprise | O WPA3 fornece o mais alto nível de segurança, com força criptográfica de 192 bits e Protected Management Frames (PMF) para prevenir ataques de desautenticação. |
| Segurança | Utilizar EAP-TLS para Dispositivos Corporativos | A autenticação baseada em certificados é mais segura do que os métodos baseados em palavras-passe e é imune a phishing e roubo de credenciais. |
| Compatibilidade | Transmitir Múltiplos RCOIs | Para garantir um amplo suporte de dispositivos, transmita tanto o RCOI OpenRoaming moderno (5A-03-BA) como o RCOI legado da Cisco (00-40-96). |
| Experiência do Utilizador | Otimizar o Onboarding de Perfis | O onboarding inicial é o único ponto de fricção. Utilize um Captive Portal simples e de utilização única ou uma aplicação leve para tornar a instalação do perfil o mais fácil possível. |
| Design de Rede | Segmentar Dispositivos IoT | A maioria dos dispositivos IoT não suporta 802.1X. Devem ser segmentados num SSID separado e devidamente seguro (por exemplo, utilizando autenticação MPSK ou MAC) e não misturados com o tráfego Passpoint. |
| Operações | Integrar com Análises | Para manter a visibilidade sobre o comportamento dos convidados na ausência de um Captive Portal, integre os seus registos de autenticação Passpoint com uma plataforma de análise WiFi como a Purple. |
Resolução de Problemas e Mitigação de Riscos
Mesmo as implementações bem planeadas podem encontrar problemas. Eis os modos de falha comuns e como mitigá-los.
| Sintoma | Causa Potencial | Estratégia de Mitigação |
|---|---|---|
| Dispositivos não tentam ligar-se | Incompatibilidade de RCOI ou RCOI em Falta | Verifique se os seus APs estão a transmitir os RCOIs corretos, incluindo o OI legado 00-40-96. Utilize uma ferramenta de análise WiFi para inspecionar as tramas de beacon. |
| Falhas de autenticação (EAP) | Má Configuração do Servidor RADIUS / Problemas de Certificados | Verifique os registos RADIUS para obter códigos de erro detalhados. Certifique-se de que os certificados de cliente são válidos e que o servidor confia na CA emissora do cliente. Verifique se o certificado do servidor é válido e se os clientes confiam nele. |
| Alta latência de autenticação | Resposta lenta do RADIUS / Problemas no Caminho de Rede | Garanta uma baixa latência entre os APs e o servidor RADIUS. Se utilizar um RADIUS na cloud, verifique se há congestionamento de rede ou problemas de encaminhamento. Aponte para um tempo de resposta inferior a 300ms. |
| Comportamento inconsistente no Android | Implementação ANQP/GAS específica do OEM | Teste exaustivamente numa gama de dispositivos Android durante a fase piloto. Algumas versões Android mais antigas ou menos comuns podem ter implementações 802.11u com falhas. |
| Falhas de roaming entre locais | Configuração WLAN Inconsistente | Certifique-se de que o perfil WLAN Passpoint (SSID, definições de segurança, RCOIs) é absolutamente idêntico em todos os locais destinados a um roaming contínuo. |
ROI e Impacto no Negócio
Embora o Passpoint seja uma solução técnica, o seu impacto mede-se em resultados de negócio. O retorno do investimento é impulsionado por melhorias na eficiência operacional, na experiência do utilizador e na postura de segurança.
Análise Custo-Benefício
Custos de Investimento:
- Hardware: Potenciais atualizações de APs se o hardware existente não for compatível com 802.11u.
- Software/Licenciamento: Custos de licenças de servidor RADIUS (por exemplo, Cisco ISE) ou serviços AAA na cloud.
- Taxas de Federação: Quotas anuais de adesão para participar no WBA OpenRoaming.
- Implementação: Serviços profissionais ou tempo da equipa interna para configuração, testes e lançamento.
Retornos e Benefícios Esperados:
- Redução da Sobrecarga de TI: Uma redução significativa nos tickets de helpdesk relacionados com o WiFi. Um resultado comum é uma diminuição de 40 a 60% nos tickets relacionados com problemas de conectividade WiFi.
- Aumento da Satisfação dos Convidados: A remoção da fricção no login leva a Net Promoter Scores (NPS) mais elevados e a melhores avaliações, particularmente na hotelaria.
- Segurança e Conformidade Melhoradas: Mitiga o risco de violações de dados resultantes de ataques baseados em WiFi, apoiando a conformidade com o PCI DSS e o GDPR e reduzindo potenciais penalizações financeiras.
- Melhoria no Descarregamento de Dados (Data Offload): Para os operadores móveis e os seus parceiros de locais, o Passpoint permite o descarregamento automático e seguro de dados móveis para WiFi, reduzindo a sobrecarga na rede móvel.
- Aumento do Envolvimento: Uma ligação contínua incentiva os utilizadores a permanecerem mais tempo no local e a envolverem-se mais com os serviços digitais, impulsionando as receitas em ambientes de retalho e hotelaria.
Ao medir KPIs como o volume de tickets de helpdesk, as pontuações de satisfação dos convidados e as taxas de sucesso de ligação antes e depois da implementação, as equipas de TI podem construir um business case convincente que demonstre um ROI claro e mensurável.
Key Terms & Definitions
IEEE 802.11u
An amendment to the IEEE 802.11 standard that enables 'interworking with external networks'. It allows client devices to exchange information with an access point before establishing a connection.
This is the foundational protocol that makes Hotspot 2.0 possible. When an IT team sees that an AP is '802.11u capable', it means it can support the discovery mechanisms required for Passpoint.
ANQP (Access Network Query Protocol)
The specific protocol used by a client device to query an access point about its capabilities, such as roaming partners, venue type, and authentication methods.
Network architects will configure ANQP elements on their wireless controllers to advertise network services. Troubleshooting often involves analyzing ANQP frames to see what information the AP is providing to clients.
GAS (Generic Advertisement Service)
The transport mechanism defined in 802.11u that carries ANQP frames between the client and the access point before an association is formed.
GAS and ANQP work together. GAS is the 'envelope' and ANQP is the 'letter' inside. When troubleshooting, packet captures will show GAS frames containing the ANQP queries and responses.
RCOI (Roaming Consortium Organizational Identifier)
A unique identifier that represents a group of network providers who have a roaming agreement. It's the primary piece of information a device looks for to decide if it can automatically connect.
This is a critical configuration item. An IT manager must ensure their APs are broadcasting the correct RCOIs for their own organization and any roaming partners like OpenRoaming. A missing or incorrect RCOI is a common cause of connection failures.
WPA3-Enterprise
The highest level of WiFi security, which uses 192-bit encryption and requires 802.1X authentication. It provides robust protection against eavesdropping and other sophisticated attacks.
For any organization concerned with security and compliance (PCI DSS, GDPR), deploying WPA3-Enterprise is a non-negotiable best practice. Passpoint is the most user-friendly way to implement it at scale.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An EAP method that uses client-side and server-side digital certificates for mutual authentication. It is considered the most secure EAP method.
This is the recommended method for securing corporate-owned devices. IT teams will use an MDM to push certificates to devices, enabling zero-touch, highly secure network access.
RadSec (RADIUS over TLS)
A protocol that secures RADIUS authentication traffic by tunneling it through a TLS-encrypted connection (typically over TCP port 2083).
When setting up roaming with OpenRoaming or other external partners, network architects will use RadSec to ensure that authentication requests traversing the public internet are fully encrypted and secure.
NAI (Network Access Identifier)
A standardized way of identifying a user in an 802.1X authentication request, typically formatted like an email address (e.g., 'user@realm'). The realm portion is used to route the request to the correct home RADIUS server.
IT teams configure NAI realms to define their authentication domains. In a roaming scenario, the realm of the user's NAI determines which Identity Provider's RADIUS server needs to process the authentication request.
Case Studies
A 500-room luxury hotel with multiple conference wings wants to eliminate its cumbersome captive portal. Corporate guests frequently complain about having to re-authenticate multiple times per day as they move between their room, the conference centre, and the restaurant. The hotel needs to maintain PCI DSS compliance for its payment systems.
The recommended solution is a phased Passpoint deployment integrated with WBA OpenRoaming. Phase 1 (Pilot): Deploy Passpoint in the main conference wing and on one floor of guest rooms. Configure the WLAN to broadcast the hotel's own RCOI and the OpenRoaming RCOI. Use EAP-TLS for corporate-managed devices (provisioned via MDM by their employers) and provide a simple, one-time onboarding portal for guests to install a Passpoint profile with an EAP-TTLS credential. Phase 2 (Rollout): After a successful pilot, extend the Passpoint WLAN to all guest rooms, public areas, and restaurants. Decommission the legacy captive portal SSID, but keep a single, hidden SSID for specific back-of-house devices that do not support 802.1X. Security: The use of WPA3-Enterprise and 802.1X provides traffic encryption and mutual authentication, satisfying key PCI DSS requirements for securing wireless environments.
A large retail chain with 200 stores across the country wants to offer seamless WiFi to its loyalty program members. They also want to offload traffic from their in-store staff's cellular devices to the corporate WiFi to ensure reliable access to inventory and POS applications. The existing infrastructure is a mix of Cisco Meraki and Aruba hardware.
The solution is to create a unified Passpoint strategy across the mixed-vendor environment. Step 1 (Onboarding): Integrate Passpoint profile generation into the loyalty program's mobile app. When a user signs into the app, it automatically installs the Passpoint profile with a unique EAP-TTLS credential. Step 2 (Staff Provisioning): Use the company's MDM to push a separate Passpoint profile to all corporate-owned staff devices, configured for EAP-TLS using device certificates for zero-touch authentication. Step 3 (Network Configuration): In both Cisco Meraki and Aruba Central dashboards, create a new WLAN profile for Passpoint. Enable Hotspot 2.0, set security to WPA3-Enterprise, and add the company's RCOI and the OpenRoaming RCOI. Point authentication to a central cloud RADIUS server to ensure consistent policy enforcement across all stores. Step 4 (Analytics): Ingest RADIUS authentication logs into the Purple analytics platform to correlate WiFi connections with loyalty member IDs, tracking visit frequency and dwell time without a captive portal.
Scenario Analysis
Q1. You are the network architect for a large international airport. You want to implement Passpoint to provide seamless roaming for travelers from major cellular carriers. During your pilot, you notice that a large number of Android devices are not automatically connecting, while iOS devices are connecting successfully. What is the most likely cause and your first troubleshooting step?
💡 Hint:Consider the differences in how various device manufacturers implement the 802.11u standard and what specific information they look for during discovery.
Show Recommended Approach
The most likely cause is a misconfiguration of the Roaming Consortium Organizational Identifiers (RCOIs). Many Android devices, particularly older models or those with manufacturer-customized operating systems, rely on the legacy Cisco RCOI (00-40-96) to initiate an ANQP query. If only the modern OpenRoaming RCOI (5A-03-BA) is being broadcast, these devices will not attempt to connect. The first troubleshooting step is to use a WiFi analysis tool to inspect the beacon frames from the pilot APs and verify that both the OpenRoaming and the legacy Cisco RCOIs are being broadcast.
Q2. A retail chain has successfully deployed Passpoint with OpenRoaming in all its stores. The marketing team now wants to know if they can still gather customer analytics, such as visit frequency and dwell time, which they previously collected via the captive portal. What is your recommendation?
💡 Hint:Where in the new authentication flow can user identity be correlated with a connection event? Can this be done while respecting privacy and the principles of the OpenRoaming federation?
Show Recommended Approach
While Passpoint eliminates the captive portal, it is still possible to gather valuable analytics. The recommended approach is to leverage the RADIUS authentication logs. Each time a user connects, an authentication request is sent to the RADIUS server, which contains the user's Network Access Identifier (NAI). By integrating the RADIUS server with an analytics platform like Purple, the NAI can be used as a persistent anonymous identifier to track visit frequency and dwell time. This provides the marketing team with the data they need without reintroducing login friction for the user. It's important to ensure this process is compliant with privacy policies and the terms of the roaming federation.
Q3. A conference centre is setting up a Passpoint network. They plan to use EAP-TLS for staff and event organizers, but need a solution for thousands of temporary attendees. They are considering using EAP-TTLS with usernames and passwords distributed at registration. What is a significant security risk of this approach and what is a better alternative?
💡 Hint:Think about the lifecycle of shared credentials and the security of the 'inner' authentication method in EAP-TTLS.
Show Recommended Approach
The significant risk of using shared EAP-TTLS credentials (username/password) is the lack of revocation and accountability. If a credential pair is compromised, it can be used by an unauthorized party until it expires, and it's difficult to trace activity back to a specific individual. A better and more secure alternative is to use an onboarding portal that generates a unique Passpoint profile for each attendee. This can be done by having the attendee scan a QR code or visit a one-time URL. The portal generates a profile containing a unique, short-lived digital certificate (for EAP-TLS) or a unique EAP-TTLS credential. This ensures that each user has a distinct identity, and access can be revoked on a per-user basis if necessary, providing much stronger security and accountability.
Key Takeaways
- ✓WiFi Hotspot 2.0 (Passpoint) enables seamless, zero-touch roaming for users by automatically authenticating devices to trusted WiFi networks.
- ✓It replaces insecure, high-friction captive portals with credential-based authentication using the enterprise-grade WPA3-Enterprise security standard.
- ✓The core technology relies on the IEEE 802.11u standard, which allows devices to query network information (via ANQP/GAS) before connecting.
- ✓Mutual authentication (802.1X) is a key security benefit, protecting against 'Evil Twin' and Man-in-the-Middle (MITM) attacks.
- ✓OpenRoaming is a global federation that works with Passpoint to allow seamless roaming across thousands of different network providers.
- ✓A successful deployment requires a phased approach: audit your infrastructure, run a pilot to test across all device types, and then perform a full rollout.
- ✓Key business benefits include reduced IT helpdesk costs, improved guest satisfaction, enhanced security compliance (PCI DSS, GDPR), and new opportunities for data offload and analytics.



