IoT Device Segmentation on WiFi: Isolating Non-Standard Devices
This guide provides practical, enterprise-grade strategies for securely segmenting non-standard IoT devices on venue WiFi networks. Learn how to implement VLAN isolation, MAC-based authentication, and strict firewall policies to protect your core infrastructure from vulnerable smart devices.
🎧 Listen to this Guide
View Transcript

Executive Summary
For IT managers and network architects in hospitality, retail, and large public venues, the proliferation of Internet of Things (IoT) devices presents a critical security challenge. Smart TVs, payment terminals, wireless printers, and building management systems (BMS) are essential for modern venue operations, but they rarely support enterprise-grade 802.1X authentication.
Placing these "dumb" devices on a flat corporate network or a public Guest WiFi network introduces severe vulnerabilities. A compromised smart thermostat can become a pivot point for attackers to access sensitive corporate data or payment systems, violating PCI DSS and GDPR compliance.
This technical reference guide outlines the definitive strategy for IoT device segmentation on WiFi. By implementing dedicated IoT VLANs, leveraging Identity Pre-Shared Keys (iPSK) or MAC Authentication Bypass (MAB), and enforcing Zero Trust firewall policies, venue IT teams can securely onboard non-standard devices. This approach ensures robust WiFi Analytics visibility while mitigating the inherent risks of a mixed-device environment.
Technical Deep-Dive
The fundamental principle of IoT device segmentation on WiFi is logical isolation. Devices that cannot authenticate securely must be quarantined in a restricted network segment.
The Architecture of Isolation
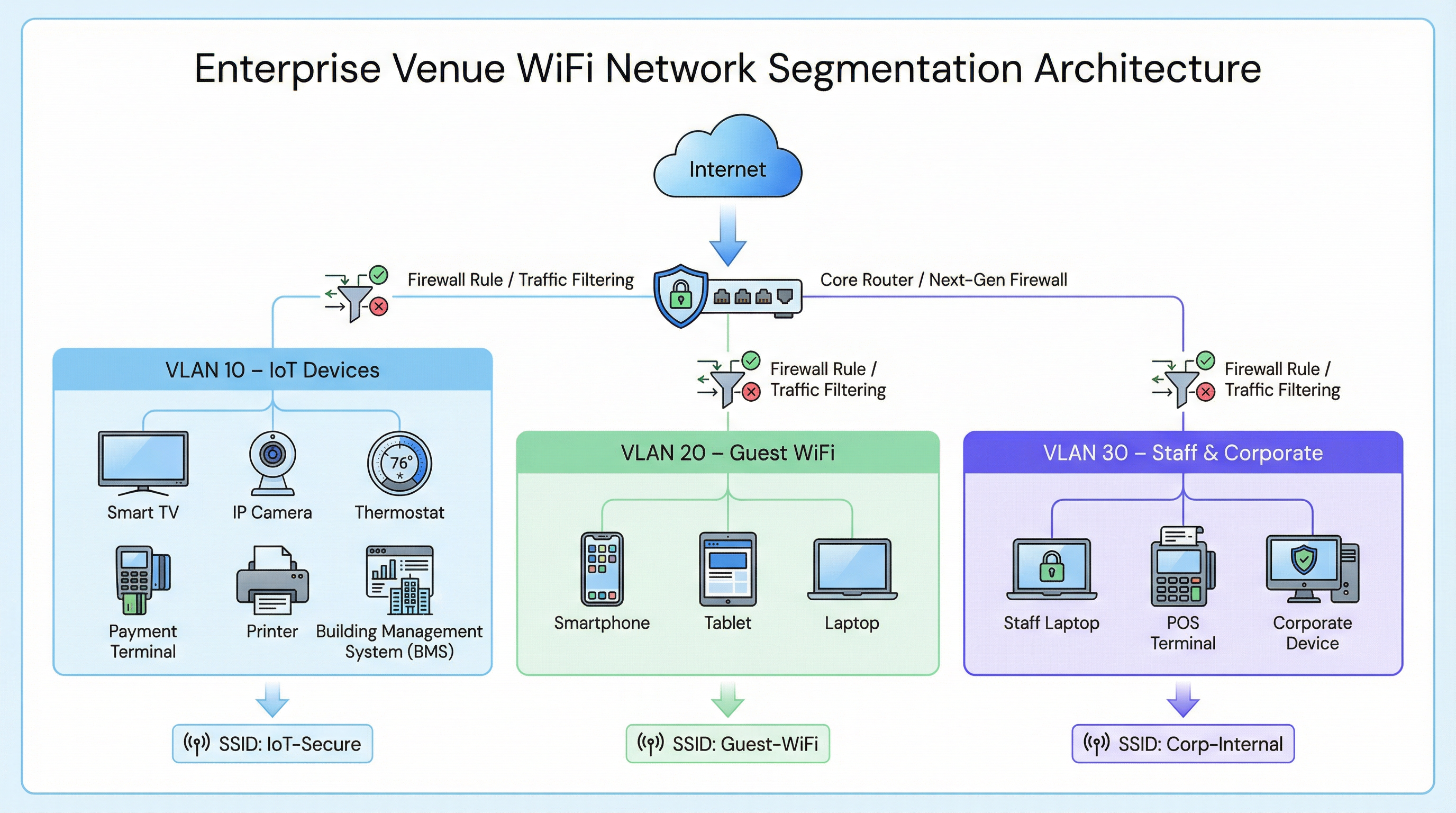
In a typical enterprise deployment, such as a Retail chain or a Hospitality venue, network traffic is divided into distinct Virtual Local Area Networks (VLANs).
- Corporate VLAN (e.g., VLAN 30): Secured via 802.1X (WPA2/WPA3-Enterprise) for staff laptops and POS terminals.
- Guest VLAN (e.g., VLAN 20): An open network utilizing a captive portal for terms of service acceptance and analytics capture.
- IoT VLAN (e.g., VLAN 10): A dedicated segment for non-standard devices.
Authentication Fallbacks for Non-Standard Devices
Since IoT devices typically lack the supplicants required for 802.1X, IT teams must rely on alternative authentication methods to assign them to the IoT VLAN.
1. Identity Pre-Shared Keys (iPSK) / Multiple PSK
Rather than using a single, global password (WPA2-Personal) for an entire IoT SSID, modern wireless controllers support iPSK. This allows administrators to generate unique pre-shared keys for individual devices or groups of devices (e.g., all smart TVs in a specific hotel wing) while broadcasting a single SSID.
- Advantage: If a specific key is compromised, it can be revoked without disrupting the entire IoT network.
- Deployment: Highly recommended for modern smart building deployments.
2. MAC Authentication Bypass (MAB)
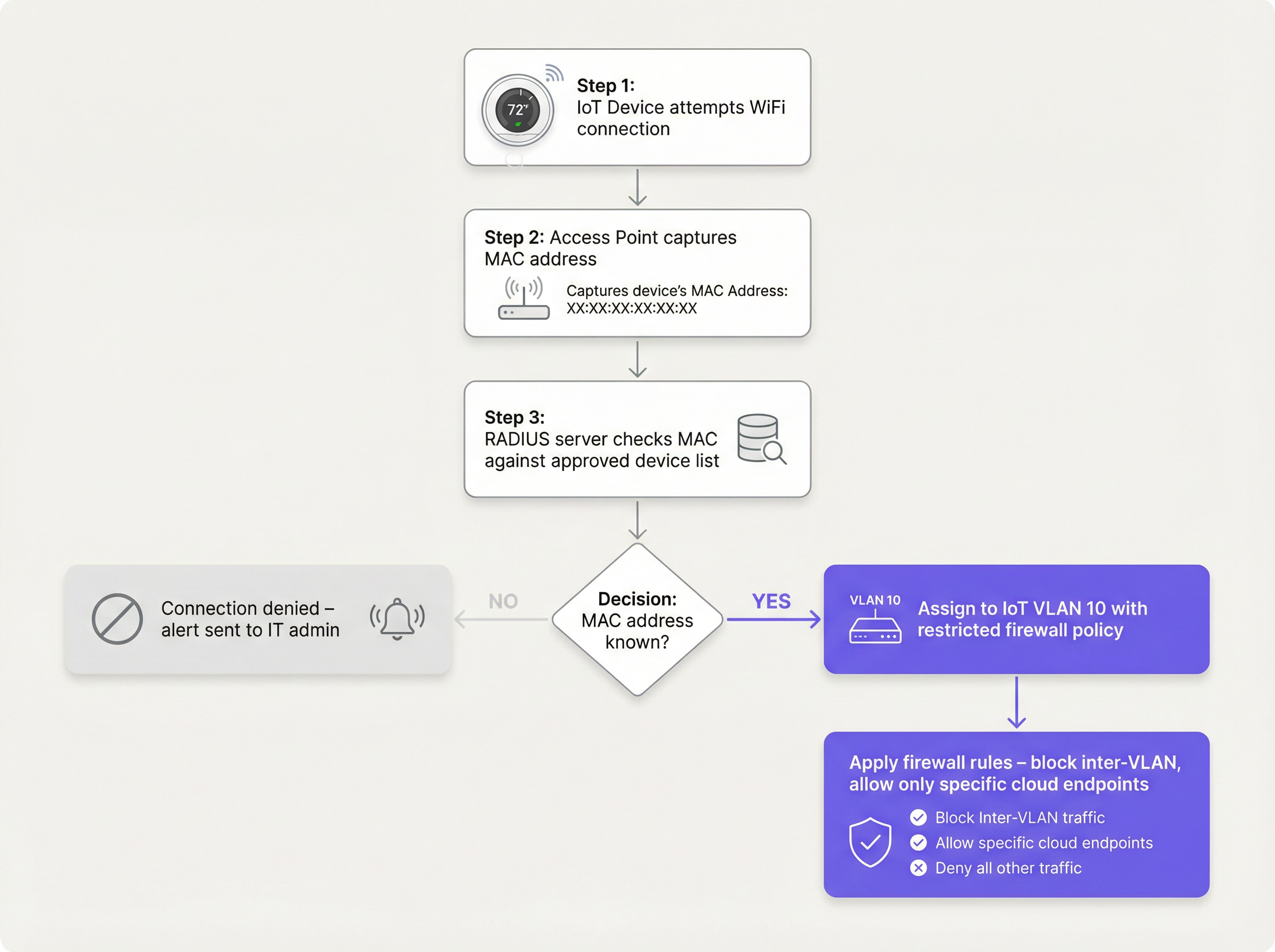
For legacy devices that struggle even with complex PSKs, MAB serves as a fallback. The wireless access point captures the device's MAC address and queries a RADIUS server. If the MAC address is registered in the approved database, the RADIUS server authorizes the connection and dynamically assigns the device to the IoT VLAN.
- Limitation: MAC addresses can be spoofed. MAB is not strong security; it is an operational workaround that must be paired with aggressive firewall policies.
- Decision Point: When evaluating RADIUS infrastructure to support MAB, consult the Cloud RADIUS vs On-Premise RADIUS: Decision Guide for IT Teams.
Implementation Guide
Deploying a secure IoT segment requires a coordinated approach across the wireless controller, RADIUS server, and core firewall.
Step 1: Define the IoT VLAN and SSID Strategy
Create a dedicated VLAN (e.g., VLAN 10) for IoT devices. Decide whether to use a dedicated SSID (e.g., Venue-IoT) or utilize dynamic VLAN assignment on a shared SSID. For maximum compatibility with cheap IoT radios, a dedicated SSID operating exclusively on the 2.4GHz band is often necessary, as many legacy sensors do not support 5GHz.
Step 2: Configure Authentication (iPSK or MAB)
If using iPSK, configure the wireless controller to map specific keys to the IoT VLAN. If using MAB, populate your RADIUS server with the MAC addresses of approved IoT devices. Ensure a strict lifecycle management process is in place—when a device is retired, its MAC address must be immediately purged from the database.
Step 3: Enforce Zero Trust Firewall Policies
This is the most critical step. The IoT VLAN must be treated as untrusted.
- Block Inter-VLAN Routing: The IoT VLAN must not be able to initiate connections to the Corporate VLAN or the Guest VLAN.
- Implement Client Isolation (L2 Isolation): Devices on the same IoT SSID should not be able to communicate with each other. A smart TV in Room 101 does not need to ping the smart TV in Room 102.
- Restrict Outbound Internet Access (Egress Filtering): Apply a default-deny policy for outbound traffic. Only allow traffic to specific, required IP addresses or domains (e.g., the manufacturer's cloud endpoint over port 443). Block all generic outbound DNS, HTTP, and NTP requests, forcing devices to use internal, monitored services.
Best Practices
- Do Not Hide the SSID: Disabling SSID broadcast provides negligible security benefits and often causes connection instability for poorly coded IoT network stacks. Leave the SSID visible but secure it properly.
- Monitor Device Behavior: Utilize WiFi Analytics to establish a baseline of normal behavior for IoT devices. If a temperature sensor suddenly begins transferring gigabytes of data, the system should trigger an immediate alert.
- Segment by Device Type: In complex environments, such as Healthcare facilities, consider creating multiple micro-segments (e.g., VLAN 11 for medical IoT, VLAN 12 for facility HVAC) to further reduce the blast radius of a compromise.
Troubleshooting & Risk Mitigation
Common Failure Mode: The "Flat Network" Compromise
The most frequent cause of IoT-related breaches is deploying smart devices on the main corporate network for convenience. This bypasses all segmentation controls.
- Mitigation: Enforce strict change control policies. No device connects to the network without an approved MAC address or iPSK assignment.
Common Failure Mode: Stale MAC Addresses
When a device breaks and is replaced, the old MAC address often remains in the RADIUS database, creating a permanent backdoor if an attacker spoofs that specific address.
- Mitigation: Implement automated lifecycle management. Require periodic re-validation of all devices in the MAB database.
ROI & Business Impact
Implementing proper IoT device segmentation on WiFi requires upfront configuration effort, but the return on investment is substantial:
- Risk Mitigation: Drastically reduces the probability of a catastrophic data breach originating from a vulnerable smart device, protecting brand reputation and avoiding regulatory fines (GDPR, PCI DSS).
- Operational Stability: Isolating noisy IoT traffic prevents broadcast storms from degrading the performance of critical corporate applications or the Guest WiFi experience.
- Future-Proofing: A segmented architecture allows venues to confidently deploy new smart building technologies, such as advanced Sensors and Wayfinding solutions, without compromising core network security.
Key Terms & Definitions
VLAN (Virtual Local Area Network)
A logical grouping of network devices that behave as if they are on an independent network, regardless of their physical location.
Used to isolate IoT devices from corporate and guest traffic, preventing lateral movement during a security breach.
MAC Authentication Bypass (MAB)
A network access control technique that uses a device's MAC address to authorize connection to the network when standard 802.1X authentication is not supported.
The primary fallback method for onboarding 'dumb' IoT devices, requiring a RADIUS server to validate the MAC address.
Identity Pre-Shared Key (iPSK)
A feature that allows multiple unique pre-shared keys to be used on a single SSID, with each key assigning the device to a specific VLAN or policy.
A more secure alternative to a single shared password for IoT networks, allowing IT teams to revoke individual compromised devices.
Client Isolation (L2 Isolation)
A wireless network setting that prevents devices connected to the same access point or SSID from communicating directly with each other.
Essential for guest networks and IoT networks to prevent infected devices from spreading malware to adjacent devices.
802.1X
An IEEE standard for port-based network access control, providing secure, enterprise-grade authentication using a RADIUS server.
The gold standard for corporate devices, but rarely supported by the IoT devices discussed in this guide.
Zero Trust
A security framework requiring all users and devices to be authenticated, authorized, and continuously validated before being granted access to applications and data.
The guiding principle for configuring firewall rules for the IoT VLAN—assume the device is compromised and restrict access accordingly.
Egress Filtering
The practice of monitoring and potentially restricting the flow of information outbound from one network to another, typically the internet.
Crucial for IoT devices to ensure they only communicate with authorized vendor cloud services and cannot be used in DDoS attacks.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
Used for Guest WiFi, but unusable by headless IoT devices, necessitating MAB or iPSK for IoT onboarding.
Case Studies
A 300-room hotel is deploying new smart TVs in every guest room. The TVs require internet access to stream content from vendor-approved cloud services, but they do not support 802.1X. The hotel also needs to ensure guests cannot cast content to TVs in adjacent rooms.
The IT team should create a dedicated IoT VLAN (e.g., VLAN 40) and a hidden or visible dedicated SSID (e.g., Hotel-Media). They implement Identity PSK (iPSK), assigning a unique pre-shared key to each room's TV. At the access point level, Client Isolation (Layer 2 isolation) is enabled to prevent TVs from communicating with each other. At the core firewall, inter-VLAN routing is blocked, ensuring the TVs cannot access the corporate network or the guest network. Finally, egress filtering is applied to VLAN 40, allowing outbound traffic only to the specific IP ranges required by the streaming services.
A large retail chain needs to connect hundreds of wireless barcode scanners and receipt printers. These legacy devices only support basic WPA2-PSK and cannot handle complex passwords or iPSK. How should they be secured?
The network architect should deploy a dedicated SSID specifically for these legacy devices, operating on the 2.4GHz band for maximum compatibility. Because the devices cannot support iPSK, the team must use MAC Authentication Bypass (MAB). The MAC addresses of all authorized scanners and printers are loaded into the central RADIUS server. When a device connects, the RADIUS server authenticates the MAC and assigns it to a highly restricted Retail-IoT VLAN. The firewall policy for this VLAN strictly limits outbound traffic to the specific internal inventory servers and payment gateways required for operation.
Scenario Analysis
Q1. A stadium IT director wants to deploy 50 new wireless digital signage displays. The vendor states the displays only support WPA2-Personal (a single shared password). The director wants to put them on the Guest WiFi network to avoid managing a new SSID. What is your recommendation?
💡 Hint:Consider the impact of client isolation and the security implications of mixing trusted and untrusted devices.
Show Recommended Approach
Do not place the displays on the Guest WiFi. The Guest network uses a captive portal, which the headless displays cannot navigate. Furthermore, Guest networks typically have client isolation enabled, which might interfere with the management system trying to update the displays. Recommendation: Create a dedicated IoT SSID. Since the devices only support WPA2-Personal, use MAC Authentication Bypass (MAB) to assign them to a dedicated Digital Signage VLAN. Apply strict firewall rules to this VLAN, allowing outbound traffic only to the specific content management cloud server.
Q2. During a network audit at a retail chain, you discover that all wireless receipt printers are connected to the Corporate VLAN using MAB. The firewall allows the Corporate VLAN full outbound internet access. What is the primary risk, and how should it be remediated?
💡 Hint:Think about what happens if an attacker unplugs a printer and connects their own device.
Show Recommended Approach
The primary risk is MAC spoofing. An attacker could spoof a printer's MAC address and gain full access to the Corporate VLAN, including unrestricted outbound internet access, allowing them to exfiltrate sensitive data or establish a command-and-control connection. Remediation: Move the printers to a dedicated IoT VLAN. Enforce strict egress filtering on the IoT VLAN, blocking all outbound internet access and only allowing internal communication to the specific print servers required for operation.
Q3. A hospital is deploying new smart thermostats that support Identity PSK (iPSK). The IT team plans to use a single iPSK for all thermostats across the entire campus to simplify management. Is this the optimal approach?
💡 Hint:Consider the blast radius if that single iPSK is compromised.
Show Recommended Approach
While better than a standard shared password, using a single iPSK for all devices defeats the primary benefit of the technology. If that single key is compromised, all thermostats are vulnerable, and changing the key requires reconfiguring every device on campus. Recommendation: Group the thermostats logically (e.g., by floor, wing, or department) and assign a unique iPSK to each group. This minimizes the blast radius of a compromised key and simplifies revocation.
Key Takeaways
- ✓IoT devices rarely support 802.1X and must be logically isolated on dedicated VLANs.
- ✓Never place IoT devices on corporate or guest networks.
- ✓Use Identity PSK (iPSK) to assign unique keys to devices on a shared SSID.
- ✓Use MAC Authentication Bypass (MAB) as a fallback for legacy devices that cannot support iPSK.
- ✓MAB is not strong security; it must be paired with aggressive Zero Trust firewall policies.
- ✓Implement client isolation on IoT SSIDs to prevent lateral movement between devices.
- ✓Enforce default-deny egress filtering, allowing IoT devices to communicate only with required vendor endpoints.



