Okta and RADIUS: Extending Your Identity Provider to WiFi Authentication
This guide provides a comprehensive technical reference for IT administrators at Okta-centric organisations who want to extend their cloud identity provider to WiFi authentication using the Okta RADIUS agent. It covers the full authentication architecture, MFA enforcement trade-offs, dynamic VLAN assignment via RADIUS attribute mapping, and the critical decision between password-based EAP-TTLS and certificate-based EAP-TLS. Venue operators and enterprise IT teams will find actionable deployment guidance, real-world case studies from hospitality and retail, and a clear framework for integrating Okta RADIUS alongside dedicated guest WiFi solutions.
🎧 Listen to this Guide
View Transcript
Executive Summary
For enterprise IT teams managing distributed venues — from hotel chains to stadiums — unifying network access control with a cloud identity provider is a critical step toward Zero Trust. The Okta RADIUS agent bridges the gap between modern cloud identity and traditional 802.1X WiFi infrastructure, allowing organisations to deprecate legacy on-premises RADIUS servers and Active Directory infrastructure for network authentication.
This guide details how to deploy the Okta RADIUS agent for enterprise WiFi authentication, covering the proxy architecture, MFA enforcement mechanisms, and the trade-offs between password-based EAP-TTLS and certificate-based EAP-TLS. It also provides actionable guidance on mapping Okta group memberships to RADIUS attributes for dynamic VLAN assignment — a capability that directly supports PCI DSS network segmentation requirements. By integrating Okta for staff authentication alongside Guest WiFi solutions, venue operators can achieve a unified, secure, and compliant access layer without duplicating identity infrastructure.
Technical Deep-Dive
How the Okta RADIUS Agent Works
The Okta RADIUS agent is a lightweight system service that acts as a proxy between Network Access Servers (NAS) — such as wireless access points (WAPs) or wireless LAN controllers (WLCs) — and the Okta cloud. It is typically deployed on a Windows or Linux server on-premises or within a cloud VPC, and it is managed entirely from the Okta Admin Console after initial installation.
The authentication flow follows a standard 802.1X proxy model. A user's device (the supplicant) connects to an enterprise SSID and presents credentials. The WAP or WLC (the authenticator) forwards a RADIUS Access-Request to the Okta RADIUS agent over UDP port 1812. The agent securely tunnels this request to the Okta cloud via an HTTPS API call, where Okta's policy engine evaluates the credentials against its user directory and any configured sign-on policies. If authentication succeeds, the agent returns a RADIUS Access-Accept message to the authenticator, optionally including RADIUS attributes for authorisation such as VLAN assignment. If MFA is required, the agent sends a RADIUS Access-Challenge back to the client, prompting for a second factor before the final decision is returned.
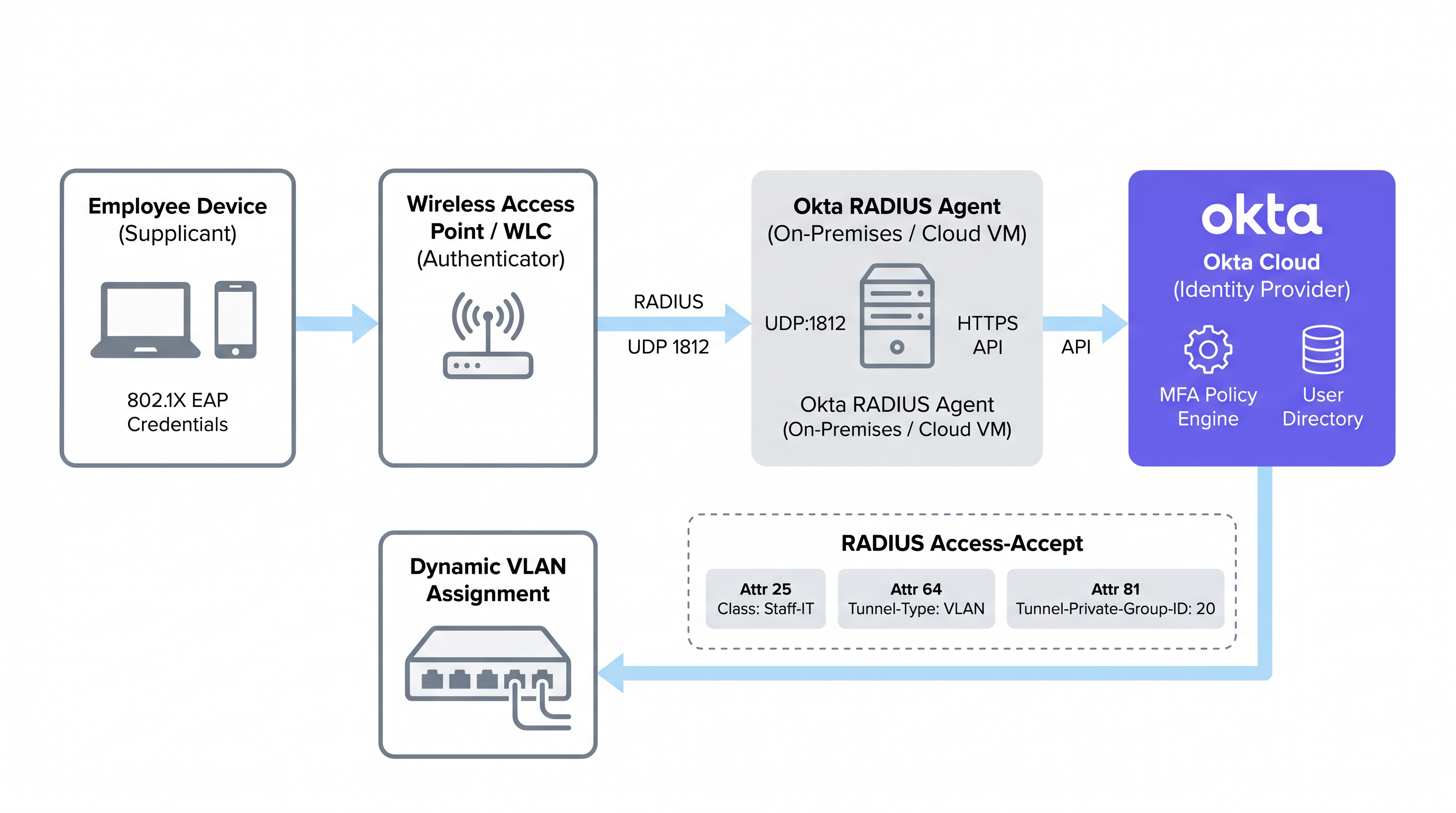
This proxy model means the Okta RADIUS agent does not need to store user credentials locally. All authentication logic, policy evaluation, and audit logging occur in the Okta cloud, giving administrators a single pane of glass for identity governance across both cloud applications and network access.
Supported EAP Protocols and Critical Limitations
A fundamental architectural constraint of the Okta RADIUS agent is its reliance on the Password Authentication Protocol (PAP) for primary authentication. While PAP transmits passwords in plaintext at the inner layer, this is encapsulated and protected by the outer TLS tunnel of the Extensible Authentication Protocol (EAP). The supported outer protocols are EAP-TTLS (with PAP as the inner method) and EAP-GTC. For a deeper comparison of EAP methods, see the Comparativa de métodos EAP: PEAP, EAP-TLS, EAP-TTLS y EAP-FAST reference guide.
Critically, PEAP-MSCHAPv2 is not supported. This is the default 802.1X protocol for Windows clients and many legacy enterprise environments. Organisations migrating from a traditional NPS/Active Directory RADIUS setup must reconfigure their client supplicants to use EAP-TTLS with PAP — a change that typically requires a wireless profile pushed via MDM or Group Policy. Failing to account for this is the most common cause of failed Okta RADIUS deployments.
EAP-TLS, which relies entirely on mutual certificate-based authentication, is also not natively supported by the Okta RADIUS agent. Organisations requiring EAP-TLS must deploy a dedicated PKI or cloud RADIUS solution that integrates with Okta as the IdP via SAML or OIDC, rather than using the Okta RADIUS agent directly.
Enforcing MFA on WiFi Connections
The Okta RADIUS agent supports MFA for WiFi access, but it introduces user experience challenges that must be carefully considered before deployment. When an MFA policy is triggered, the agent sends a RADIUS Access-Challenge to the client. Okta supports several factors for RADIUS applications:
| MFA Factor | PAP | EAP-TTLS | Notes |
|---|---|---|---|
| Okta Verify Push | Supported | Supported | Sent out-of-band; user taps Approve on mobile |
| TOTP (Okta Verify / Google Auth) | Supported | Supported | User appends OTP to password (e.g., Pass123,456789) |
| SMS / Email / Voice | Supported | Supported | User sends trigger string (SMS, EMAIL, CALL) first |
| Duo Push / SMS / Passcode | Supported | Supported | Duo passcode only for EAP-TTLS |
| YubiKey / U2F / Windows Hello | Not Supported | Not Supported | Hardware tokens incompatible with RADIUS protocol |
The practical constraint is roaming. In Hospitality environments, a housekeeper's tablet may roam between access points dozens of times per shift, triggering re-authentication each time. Requiring a push notification approval on every roam is operationally untenable. For general staff WiFi, strong password policies combined with Okta's device trust and network zone policies are typically preferred over active MFA prompts. MFA on WiFi should be reserved for administrative SSIDs or high-privilege access scenarios.
Password-Based vs Certificate-Based Authentication
The choice between password-based RADIUS (via the Okta RADIUS agent) and certificate-based EAP-TLS is one of the most consequential decisions in an enterprise WiFi deployment. The trade-offs are not simply about security; they involve deployment complexity, device management maturity, and operational overhead.
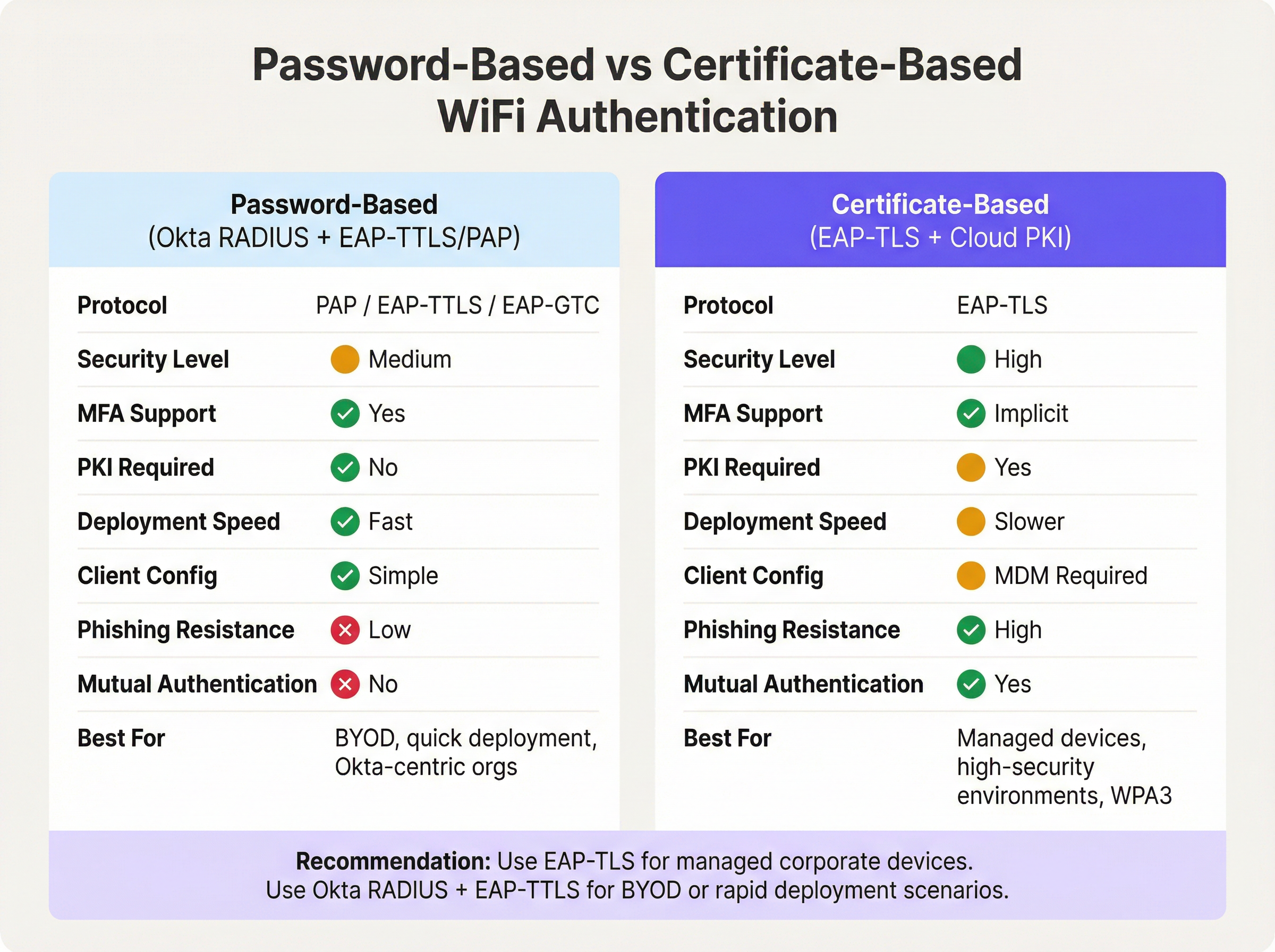
Password-based authentication via the Okta RADIUS agent offers a rapid path to unified identity. If your organisation already manages users in Okta, deployment can be completed in hours rather than weeks. There is no PKI to build, no certificates to distribute, and no MDM dependency. The trade-off is that passwords remain the primary credential, and the absence of mutual authentication means the client cannot cryptographically verify the network's identity — a vector for evil twin attacks in high-risk environments.
Certificate-based EAP-TLS eliminates passwords from the WiFi authentication equation entirely. The client presents a device certificate, and the RADIUS server presents a server certificate, providing mutual authentication. This is the recommended approach for IEEE 802.1X on WPA3-Enterprise networks, particularly in environments subject to PCI DSS or NCSC Cyber Essentials Plus. The prerequisite is a functioning PKI — either an on-premises Microsoft ADCS deployment or a cloud PKI service — and an MDM platform capable of distributing certificates to all managed endpoints. For Retail environments with hundreds of managed point-of-sale devices, this investment is well justified. For BYOD-heavy environments or rapid deployments, Okta RADIUS with EAP-TTLS is the pragmatic choice.
RADIUS Attribute Mapping for Dynamic VLAN Assignment
Dynamic VLAN assignment is where the Okta RADIUS integration delivers its most tangible operational value. By mapping Okta group membership to RADIUS attributes, network administrators can enforce role-based network segmentation without maintaining separate VLAN policies per device or per location.
Okta passes group membership data in the RADIUS Access-Accept message using one of three attributes, configurable in the Advanced RADIUS Settings of the Okta application:
- Attribute 11 (Filter-Id): A string attribute containing the group name. Widely supported across vendors.
- Attribute 25 (Class): An opaque attribute used for authorisation. Supported by Cisco ISE, Aruba ClearPass, and Fortinet.
- Attribute 26 (Vendor-Specific): Allows vendor-specific sub-attributes for more granular control.
The network controller (WLC, NAC appliance) receives the Okta group name in the chosen attribute and maps it to the standard RADIUS tunnel attributes required for VLAN assignment:
| RADIUS Attribute | Value | Purpose |
|---|---|---|
| 64 (Tunnel-Type) | 13 (VLAN) | Specifies VLAN tunnelling |
| 65 (Tunnel-Medium-Type) | 6 (802) | Specifies IEEE 802 medium |
| 81 (Tunnel-Private-Group-ID) | e.g., 40 |
The target VLAN ID |
For example, a user in the Okta group Retail-POS-Staff would have Class: Retail-POS-Staff returned in the Access-Accept. The WLC policy would map this to Tunnel-Private-Group-ID: 40, placing the device on VLAN 40 — the isolated POS network. A user in Store-Management would be placed on VLAN 50. This logic is enforced at the network edge, not in Okta, but it is driven entirely by Okta group membership.
Implementation Guide
Step 1: Deploy the Okta RADIUS Agent (High Availability)
Deploy the Okta RADIUS agent on a minimum of two servers — either on-premises or in a cloud VPC — to ensure high availability. Single-agent deployments are a critical risk: if the server is unavailable for patching or experiences a failure, all 802.1X WiFi authentication will fail across the estate. Configure your WLC or NAC appliance to load balance RADIUS requests between both agents.
During installation, the agent will prompt for an Okta administrator login to authorise the agent and link it to the Okta tenant. Once authorised, the agent appears in the Okta Admin Console under Settings > Downloads > RADIUS Agent Status, where health and connectivity can be monitored.
Step 2: Configure the RADIUS Application in Okta
- In the Okta Admin Console, navigate to Applications > Applications and search the app catalogue for RADIUS Application.
- Add the application, assign it a descriptive name (e.g.,
Corporate-WiFi-Staff), and click Next. - Under the Sign On tab, configure the RADIUS Port (default 1812) and generate a strong, randomly generated Shared Secret of at least 32 characters.
- Under Advanced RADIUS Settings, enable Accept password and security token in the same login request if you intend to support TOTP appended to passwords.
- Optionally enable Permit Automatic Push for Okta Verify Enrolled Users for seamless push-based MFA.
- Assign the application to the relevant Okta groups representing your staff.
Step 3: Configure Group-Based VLAN Assignment
- In the RADIUS application's Sign On settings, click Edit in the Advanced RADIUS Settings section.
- Check Include groups in RADIUS response.
- Select the RADIUS attribute: 25 Class is recommended for Aruba and Cisco environments; 11 Filter-Id for Fortinet and others.
- Add the specific Okta group names to include (e.g.,
Retail-POS-Staff,Store-Management,IT-Admins). - On your WLC or NAC appliance, create enforcement policies that map each group name to the corresponding VLAN tunnel attributes.
Step 4: Configure Client Supplicants
Because PEAP-MSCHAPv2 is unsupported, client devices must be configured to use EAP-TTLS with PAP as the inner method. Deploy a wireless network profile via your MDM platform (e.g., Microsoft Intune, Jamf Pro) or via Group Policy Objects (GPO) for Windows domain-joined devices. The profile should specify:
- SSID: Your enterprise SSID name
- Security: WPA2-Enterprise or WPA3-Enterprise
- EAP Method: EAP-TTLS
- Inner Authentication: PAP
- Server Certificate Validation: Enabled (pin to your RADIUS agent's server certificate CN)
Step 5: Set RADIUS Timeouts
Increase the RADIUS timeout on your WLC from the default 3-5 seconds to 30-60 seconds. This is critical if MFA push notifications are in use, as the user must have sufficient time to approve the notification on their device before the WLC abandons the authentication attempt.
Best Practices
Deploying Okta RADIUS for WiFi authentication is straightforward, but several operational best practices separate a resilient production deployment from a fragile proof-of-concept.
Segment guest and staff traffic at the SSID level. Okta RADIUS is a workforce identity tool. For visitor and guest access, deploy a dedicated captive portal solution. This prevents Okta licence costs from scaling with guest volumes and ensures clean separation of concerns. Purple enterprise customers can deploy Guest WiFi on a separate SSID while using Okta RADIUS for staff authentication on the same physical infrastructure.
Use a NAC appliance for complex policy environments. If your environment requires conditional access based on device posture, MAC address filtering, or certificate status alongside user identity, deploy an intermediate NAC appliance (Aruba ClearPass, Cisco ISE, or Portnox) to proxy requests to the Okta RADIUS agent. The NAC appliance can enrich the RADIUS response with additional tunnel attributes that the Okta agent alone cannot generate.
Monitor via the Okta System Log. Every authentication event — success, failure, MFA challenge, and factor type — is recorded in the Okta System Log. Configure log streaming to your SIEM for real-time alerting on authentication anomalies. This is particularly valuable for Healthcare and public-sector organisations subject to audit requirements.
Rotate shared secrets on a schedule. The shared secret between the Okta RADIUS application and your NAS is a critical security credential. Implement a rotation schedule (quarterly is recommended) and update both the Okta application and the WLC/NAC configuration simultaneously.
Restrict RADIUS service addresses. In the Okta RADIUS agent configuration, restrict which IP addresses are permitted to send RADIUS requests. This prevents unauthorised NAS devices from attempting authentication against your Okta tenant.
For guidance on the broader network architecture context, see The Core SD WAN Benefits for Modern Businesses and Wireless Access Points Definition Your Ultimate 2026 Guide.
Troubleshooting & Risk Mitigation
The following table summarises the most common failure modes encountered in Okta RADIUS WiFi deployments and their recommended mitigations.
| Failure Mode | Root Cause | Mitigation |
|---|---|---|
| Authentication Timeouts | WLC RADIUS timeout too short for Okta API or MFA response | Increase WLC RADIUS timeout to 30-60 seconds |
| Windows Clients Rejected | Windows defaults to PEAP-MSCHAPv2, which Okta RADIUS rejects | Push EAP-TTLS/PAP wireless profile via MDM or GPO |
| Users in Wrong VLAN | Okta group name mismatch or missing tunnel attributes on WLC | Verify WLC maps Class/Filter-Id to Tunnel-Private-Group-ID; check Okta System Log |
| Agent Unreachable | Server offline, API token expired, or firewall blocking HTTPS to Okta | Deploy redundant agents; monitor agent status in Okta Admin Console; verify outbound HTTPS |
| MFA Push Not Delivered | User not enrolled in Okta Verify, or mobile device offline | Enforce Okta Verify enrolment policy; consider TOTP as fallback |
| Certificate Validation Errors | Client cannot validate RADIUS server certificate | Pin server certificate CN in client wireless profile; ensure CA chain is trusted |
| VLAN Attributes Not Sent | Okta group not included in RADIUS response configuration | Verify group is listed in Advanced RADIUS Settings; confirm user is a member of the group in Okta |
For Transport and public-sector environments where network uptime is mission-critical, implement synthetic monitoring that periodically tests RADIUS authentication end-to-end and alerts on failure before users are impacted.
ROI & Business Impact
The business case for Okta RADIUS WiFi authentication rests on three pillars: operational efficiency, security posture improvement, and compliance readiness.
Operational Efficiency. Consolidating WiFi authentication into Okta eliminates the need to maintain separate on-premises RADIUS infrastructure (NPS servers, local AD) at each venue or site. For a hotel chain with 50 properties, this can represent a significant reduction in per-site infrastructure costs and IT support overhead. User provisioning and deprovisioning become atomic: adding a user to the correct Okta group grants both application access and the appropriate WiFi VLAN access simultaneously. When an employee leaves, deactivating their Okta account immediately revokes WiFi access across all sites.
Security Posture. Replacing shared PSK WiFi passwords with per-user 802.1X authentication eliminates credential sharing, a common vector for insider threat and unauthorised access. Combined with dynamic VLAN assignment, this enforces the principle of least privilege at the network layer. The Okta System Log provides a complete, tamper-evident audit trail of every WiFi authentication event, which is essential for incident response.
Compliance Readiness. PCI DSS 4.0 Requirement 8.3 mandates MFA for all non-console administrative access. Requirement 1.3 requires network segmentation between the cardholder data environment and other networks. Okta RADIUS with group-based VLAN assignment directly addresses both requirements. For GDPR compliance, the Okta System Log provides the access records required to demonstrate appropriate technical controls over personal data processing systems. For venues deploying Modern Hospitality WiFi Solutions, this unified approach to identity and network access is increasingly a prerequisite for enterprise procurement.
Organisations that have completed this integration typically report a reduction in WiFi-related IT support tickets (fewer password reset requests, fewer VLAN misconfiguration incidents) and a measurable improvement in security audit scores. The investment in deploying and configuring the Okta RADIUS agent — typically measured in days rather than weeks for a single-site deployment — delivers ongoing operational savings that compound across a distributed estate.
Key Terms & Definitions
Okta RADIUS Agent
A lightweight on-premises or cloud-hosted proxy service that translates RADIUS authentication requests from network infrastructure (access points, WLCs) into Okta API calls, enabling the Okta cloud to serve as the authentication backend for 802.1X WiFi.
IT teams encounter this when deploying enterprise WiFi authentication backed by Okta. It is the critical bridge component between legacy RADIUS-based network infrastructure and modern cloud identity.
802.1X
An IEEE standard for port-based Network Access Control (NAC) that defines an authentication framework for wired and wireless networks. It uses the Extensible Authentication Protocol (EAP) to carry authentication credentials between the supplicant (device), authenticator (AP/switch), and authentication server (RADIUS).
802.1X is the foundation of enterprise WiFi security. Any deployment using WPA2-Enterprise or WPA3-Enterprise is using 802.1X. IT teams must understand the three-party model (supplicant, authenticator, authentication server) to troubleshoot connectivity issues.
EAP-TTLS (Extensible Authentication Protocol - Tunnelled Transport Layer Security)
An EAP method that establishes a TLS tunnel using only a server-side certificate, then carries a simpler inner authentication protocol (such as PAP) inside the tunnel. This protects the inner credentials from eavesdropping while requiring only server-side certificate infrastructure.
EAP-TTLS with PAP is the recommended protocol for Okta RADIUS WiFi authentication. It is more secure than bare PAP but does not require client-side certificates, making it practical for BYOD and mixed-device environments.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An EAP method that uses mutual certificate-based authentication — both the client and the server present digital certificates. It is the most secure 802.1X method, providing phishing-resistant, password-free authentication.
EAP-TLS is the gold standard for managed corporate device environments. It requires a PKI infrastructure and MDM for certificate distribution. The Okta RADIUS agent does not natively support EAP-TLS; a dedicated cloud PKI or RADIUS service is required.
PAP (Password Authentication Protocol)
A simple authentication protocol that transmits usernames and passwords in plaintext. In the context of 802.1X, PAP is used as the inner authentication method inside an EAP-TTLS tunnel, where the outer TLS layer provides encryption.
PAP is the primary authentication mechanism supported by the Okta RADIUS agent. IT teams must understand that PAP alone is insecure, but PAP inside EAP-TTLS is acceptable for enterprise WiFi when the server certificate is properly validated.
Dynamic VLAN Assignment
A network access control technique where a RADIUS server returns VLAN assignment attributes in the Access-Accept message, causing the wireless controller or switch to place the authenticated client on a specific VLAN based on their identity or group membership, rather than a static per-SSID VLAN.
Dynamic VLAN assignment is essential for network segmentation in multi-role environments (e.g., separating POS terminals from general staff devices). It is configured by returning RADIUS attributes 64, 65, and 81 in the Access-Accept message.
RADIUS Attribute 25 (Class)
A standard RADIUS attribute used to pass arbitrary authorisation data from the authentication server to the NAS. Okta uses this attribute to return Okta group membership information to the wireless controller, which can then use it for VLAN assignment or access policy decisions.
IT teams configuring Okta group-based VLAN assignment will configure the WLC to read the Class attribute value and map it to a VLAN ID. The exact attribute to use (11, 25, or 26) depends on the WLC vendor's documentation.
NAS (Network Access Server)
In RADIUS terminology, the NAS is the network device that receives the user's connection request and forwards it to the RADIUS server for authentication. In WiFi deployments, the NAS is typically the wireless access point or wireless LAN controller.
The NAS is the authenticator in the 802.1X model. IT teams must configure the NAS with the RADIUS server IP address, port, and shared secret. The NAS IP address should be whitelisted in the Okta RADIUS agent's service address filtering configuration.
Shared Secret
A pre-shared password used to authenticate RADIUS messages between the NAS (WLC/AP) and the RADIUS server (Okta RADIUS agent). It is used to compute a Message-Authenticator hash that verifies the integrity of RADIUS packets.
The shared secret must be identical on both the Okta RADIUS application configuration and the WLC/NAC RADIUS server entry. It should be at least 32 characters, randomly generated, and rotated on a regular schedule. A mismatch is a common cause of RADIUS authentication failures.
MFA Challenge (RADIUS Access-Challenge)
A RADIUS message type sent by the authentication server to the NAS when additional authentication factors are required. The NAS relays the challenge to the client, which must respond with the appropriate factor (e.g., OTP, push approval) before authentication can complete.
The Access-Challenge mechanism is how Okta enforces MFA over RADIUS. IT teams must ensure the WLC supports the challenge-response exchange and that the RADIUS timeout is long enough for the user to complete the MFA step.
Case Studies
A 150-property hotel chain currently uses on-premises NPS servers at each property for 802.1X staff WiFi authentication. Each NPS server is joined to a local Active Directory domain. The IT team wants to centralise identity management in Okta and eliminate the per-property NPS infrastructure. How should they approach the migration?
The recommended approach is a phased migration using the Okta RADIUS agent deployed in a centralised cloud VPC rather than at each property. Phase 1: Deploy two Okta RADIUS agent instances in a cloud VPC (e.g., AWS or Azure) in the same region as the majority of properties. Configure the agents to listen on UDP 1812. Phase 2: For each property, add the Okta RADIUS agent IPs as secondary RADIUS servers on the WLC, keeping the existing NPS as primary. This allows parallel operation and testing without disrupting live authentication. Phase 3: Migrate users from local AD to Okta. Use Okta's AD agent to sync existing accounts initially, then progressively move to Okta as the authoritative source. Phase 4: For each property, configure the WLC to use EAP-TTLS/PAP and push the new wireless profile to staff devices via MDM. Phase 5: Once all devices are confirmed on EAP-TTLS, switch the WLC RADIUS priority to the Okta agents as primary and decommission the NPS servers. Configure Okta groups (Front-Desk, Housekeeping, F&B, Management, IT-Admins) and enable group-based VLAN assignment using Attribute 25 (Class). Map each group to the appropriate VLAN on the WLC. Increase WLC RADIUS timeout to 45 seconds to accommodate Okta API latency.
A national retail chain with 320 stores needs to achieve PCI DSS 4.0 compliance for its staff WiFi. Store associates use handheld devices for inventory management, and a separate set of devices handles point-of-sale transactions. The chain uses Okta for all workforce identity. How do they implement VLAN segmentation using Okta RADIUS to satisfy PCI DSS network segmentation requirements?
Create three Okta groups: POS-Staff (for employees who operate POS terminals), Inventory-Staff (for warehouse and shop floor associates), and Store-Management. In the Okta RADIUS application, enable 'Include groups in RADIUS response' and select Attribute 25 (Class). Add all three groups to the response configuration. On the wireless controller at each store (or centrally via a cloud WLC), create three enforcement policies: (1) If Class = POS-Staff, assign Tunnel-Private-Group-ID = 40 (the POS VLAN, which is in scope for PCI DSS and has firewall rules restricting access to only the payment processor). (2) If Class = Inventory-Staff, assign Tunnel-Private-Group-ID = 50 (the inventory VLAN, out of PCI scope). (3) If Class = Store-Management, assign Tunnel-Private-Group-ID = 60 (the management VLAN with access to store management systems). Devices connecting with credentials of a user in the POS-Staff group are automatically placed on VLAN 40. If a store associate's role changes, updating their Okta group membership immediately changes their VLAN assignment on next connection — no WLC reconfiguration required. Document the Okta group-to-VLAN mapping in the network segmentation diagram for the PCI DSS QSA audit.
Scenario Analysis
Q1. A mid-size conference centre uses Okta for all staff identity management. They want to deploy 802.1X WiFi for staff using their existing Cisco Meraki access points. Their Windows laptops are managed via Microsoft Intune. The IT manager wants to enforce Okta Verify push MFA for all WiFi connections. What are the three most critical configuration steps they must complete, and what is the most likely failure mode if they skip any of them?
💡 Hint:Consider the EAP protocol compatibility between Okta RADIUS and Windows defaults, the RADIUS timeout setting, and the client wireless profile configuration.
Show Recommended Approach
The three critical steps are: (1) Deploy a wireless profile via Intune that configures Windows clients to use EAP-TTLS with PAP as the inner method — Windows defaults to PEAP-MSCHAPv2, which the Okta RADIUS agent does not support, causing all authentication attempts to be rejected. (2) Increase the Cisco Meraki RADIUS timeout from the default 5 seconds to at least 45-60 seconds — without this, the authentication request will time out before the user can approve the Okta Verify push notification. (3) Enable 'Permit Automatic Push for Okta Verify Enrolled Users' in the Okta RADIUS application's Advanced RADIUS Settings — without this, users may be prompted to manually select their MFA factor rather than receiving an automatic push. The most likely failure mode if step 1 is skipped is a complete authentication failure for all Windows devices. If step 2 is skipped, authentication will intermittently fail for users who take more than 5 seconds to approve the push. If step 3 is skipped, users will experience a confusing challenge prompt rather than a seamless push notification.
Q2. A large retail chain's security team has flagged that their current Okta RADIUS WiFi deployment uses a single RADIUS agent server. During a recent patching window, the server was offline for 45 minutes, causing WiFi authentication to fail across all 80 stores. What architectural changes should the IT team implement to prevent this, and what are the two deployment options for the agents?
💡 Hint:Consider both the agent deployment topology and the WLC configuration required to support redundancy.
Show Recommended Approach
The IT team should deploy a minimum of two Okta RADIUS agent instances and configure the WLC at each store to use both agents. There are two deployment options: Option A (Centralised Cloud VMs) — deploy both agents in a cloud VPC (e.g., AWS or Azure), ideally in different availability zones. The WLC at each store points to both cloud IPs, with one as primary and one as secondary (or with load balancing enabled). This minimises per-site infrastructure but introduces WAN dependency. Option B (On-Premises Redundant Pair) — deploy two agent servers at a central data centre or co-location facility, with the WLC using RADIUS failover. On the WLC, configure the primary RADIUS server as Agent 1 and the secondary as Agent 2, with a failover timeout of 3-5 seconds. Enable 'Dead Server Detection' if supported by the WLC vendor. Additionally, the IT team should configure health monitoring in the Okta Admin Console and set up alerting if an agent goes offline. For stores with local servers, a local agent can serve as a tertiary fallback for resilience against WAN outages.
Q3. An enterprise organisation is evaluating whether to use the Okta RADIUS agent with EAP-TTLS/PAP or to invest in a cloud PKI solution for EAP-TLS for their corporate WiFi. They have 2,000 managed Windows and macOS devices enrolled in Microsoft Intune, and they are subject to PCI DSS 4.0. What is the recommended approach and what is the primary security justification?
💡 Hint:Consider the PCI DSS requirements, the device management maturity (all devices are MDM-enrolled), and the security properties of each authentication method.
Show Recommended Approach
The recommended approach is to invest in EAP-TLS with a cloud PKI solution. The primary security justification is mutual authentication: EAP-TLS requires both the client and the RADIUS server to present digital certificates, meaning the device cryptographically proves its identity to the network and the network proves its identity to the device. This eliminates the risk of evil twin attacks (where a rogue AP impersonates the corporate SSID) and removes passwords from the WiFi authentication equation entirely, eliminating credential theft and phishing as attack vectors. For PCI DSS 4.0, EAP-TLS satisfies Requirement 8.3 (MFA for non-console admin access) implicitly through certificate-based authentication, and it supports WPA3-Enterprise 192-bit mode (Requirement 4.2.1 for strong cryptography). The prerequisite — all 2,000 devices enrolled in Intune — is already met, making certificate distribution via Intune SCEP profiles straightforward. The Okta RADIUS agent with EAP-TTLS/PAP would be an acceptable interim solution during the PKI build-out, but given the PCI DSS scope and the fully managed device estate, EAP-TLS is the correct long-term architecture. The additional investment in a cloud PKI service (typically $3-8 per device per year) is justified by the security uplift and reduced credential management overhead.
Key Takeaways
- ✓The Okta RADIUS agent proxies 802.1X WiFi authentication requests from network infrastructure to the Okta cloud via HTTPS, enabling cloud identity to govern network access without on-premises directory servers.
- ✓The agent supports EAP-TTLS with PAP and EAP-GTC, but does NOT support PEAP-MSCHAPv2 (the Windows default) or EAP-TLS — client supplicants must be reconfigured via MDM or GPO before deployment.
- ✓MFA on WiFi is technically supported (Okta Verify push, TOTP, SMS) but requires increasing the WLC RADIUS timeout to 30-60 seconds; it is best reserved for administrative SSIDs rather than general staff WiFi due to roaming friction.
- ✓Dynamic VLAN assignment is achieved by enabling 'Include groups in RADIUS response' in Okta and mapping the returned Class (Attribute 25) or Filter-Id (Attribute 11) to VLAN tunnel attributes (64, 65, 81) on the WLC or NAC appliance.
- ✓Always deploy a minimum of two Okta RADIUS agent instances for high availability — a single agent is a critical single point of failure for all WiFi authentication across the estate.
- ✓For fully managed device environments subject to PCI DSS or high-security requirements, EAP-TLS with a cloud PKI is the superior long-term architecture; Okta RADIUS with EAP-TTLS/PAP is the pragmatic choice for BYOD or rapid deployment scenarios.
- ✓Okta RADIUS is a workforce identity tool — deploy a dedicated guest WiFi captive portal solution for visitor access to avoid Okta licence scaling costs and maintain clean separation between staff and guest network access.



