Zero Trust WiFi Architecture: Applying Zero Trust to Venue Networks
A comprehensive technical reference guide detailing how venue operators can apply Zero Trust principles to enterprise WiFi networks. It covers continuous verification, micro-segmentation, and device posture enforcement to secure hospitality, retail, and public-sector environments against lateral movement and compliance risks.
🎧 Listen to this Guide
View Transcript

Executive Summary
The perimeter is dead. For venue operators—hotels, retail chains, stadiums, and public-sector organisations—the traditional security model of trusting any device that successfully authenticates to the WiFi network is no longer viable. A modern venue network is a complex ecosystem of corporate laptops, BYOD smartphones, unmanaged guest devices, IoT sensors, and critical infrastructure like POS terminals and property management systems, all sharing the same physical airspace.
Zero Trust WiFi Architecture is the strategic imperative for securing this environment. It replaces the flawed "trust but verify" model with continuous verification, least-privilege access, and strict micro-segmentation. This practical reference guide provides IT leaders with the blueprint for applying Zero Trust principles to enterprise wireless networks. We detail the foundational technologies—IEEE 802.1X, WPA3-Enterprise, and RADIUS policy enforcement—and provide actionable deployment guidance to secure your venues without compromising the user experience. By implementing these controls, organisations can drastically reduce their attack surface, ensure compliance with PCI DSS and GDPR, and mitigate the risk of lateral movement in the event of a breach.
Listen to our executive briefing on Zero Trust WiFi Architecture:
Technical Deep-Dive: The Four Pillars of Zero Trust WiFi
Zero Trust is not a single product you can buy and rack in your server room; it is an architectural framework. When applied to the wireless edge, it relies on four foundational pillars to shift security from the network perimeter to individual devices and users.
1. Continuous Verification
The traditional WiFi security model relies on a one-time authentication event. A user enters a PSK or their Active Directory credentials, the access point grants access, and the device is trusted for the duration of the session. Zero Trust mandates continuous verification.
This means that trust is never assumed to be permanent. Using advanced RADIUS configurations and Network Access Control (NAC) policies, the network continuously reassesses the device's right to access resources. If a device's context changes—for instance, if its endpoint protection agent is disabled, or it attempts to access resources outside its normal behavioural profile—its access privileges can be dynamically revoked or restricted mid-session. This requires configuring session re-authentication timers and integrating your wireless controller with a robust identity provider.
2. Least-Privilege Network Access
Once a device is authenticated, what can it do? In a flat network, the answer is "almost anything." In a Zero Trust architecture, every device is granted the absolute minimum access required to perform its function.
A guest connecting via Guest WiFi requires outbound internet access and DNS resolution; they have no legitimate business communicating with the local subnet. A managed corporate laptop may require access to internal file shares and cloud applications. A smart thermostat requires communication only with its specific cloud controller. This principle is enforced at the network edge through dynamic role assignment, where the RADIUS server returns specific Vendor-Specific Attributes (VSAs) to the access point, placing the device into a tightly controlled role rather than a broad, permissive network segment.
3. Micro-Segmentation via Dynamic VLANs
Micro-segmentation is the mechanism by which least-privilege access is enforced at the network layer. Rather than maintaining a single large subnet for all wireless clients, the network is divided into discrete, logically isolated segments, typically using dynamic VLAN assignment.
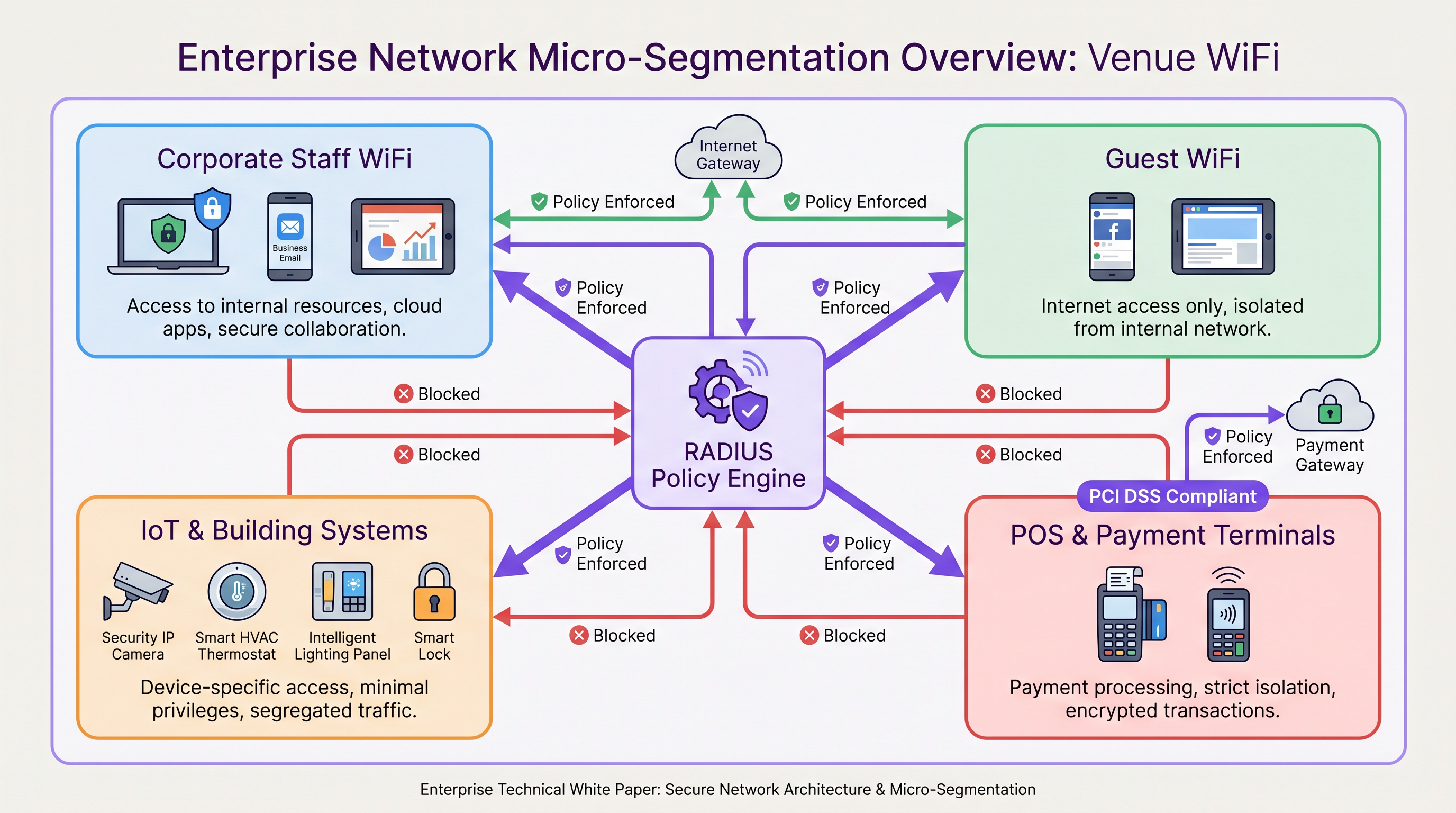
When a device authenticates via 802.1X, the RADIUS policy engine evaluates the user's identity, device type, and location, and assigns the device to the appropriate VLAN. Firewalls and Access Control Lists (ACLs) then govern the traffic flow between these micro-segments. For example, in Retail environments, PCI DSS compliance mandates strict isolation of the cardholder data environment. Micro-segmentation ensures that a compromised device on the guest network cannot pivot and communicate with POS terminals.
4. Device Posture Enforcement
Identity alone is insufficient for establishing trust; the health and compliance of the device must also be verified. Device posture enforcement checks the state of the endpoint before granting access.
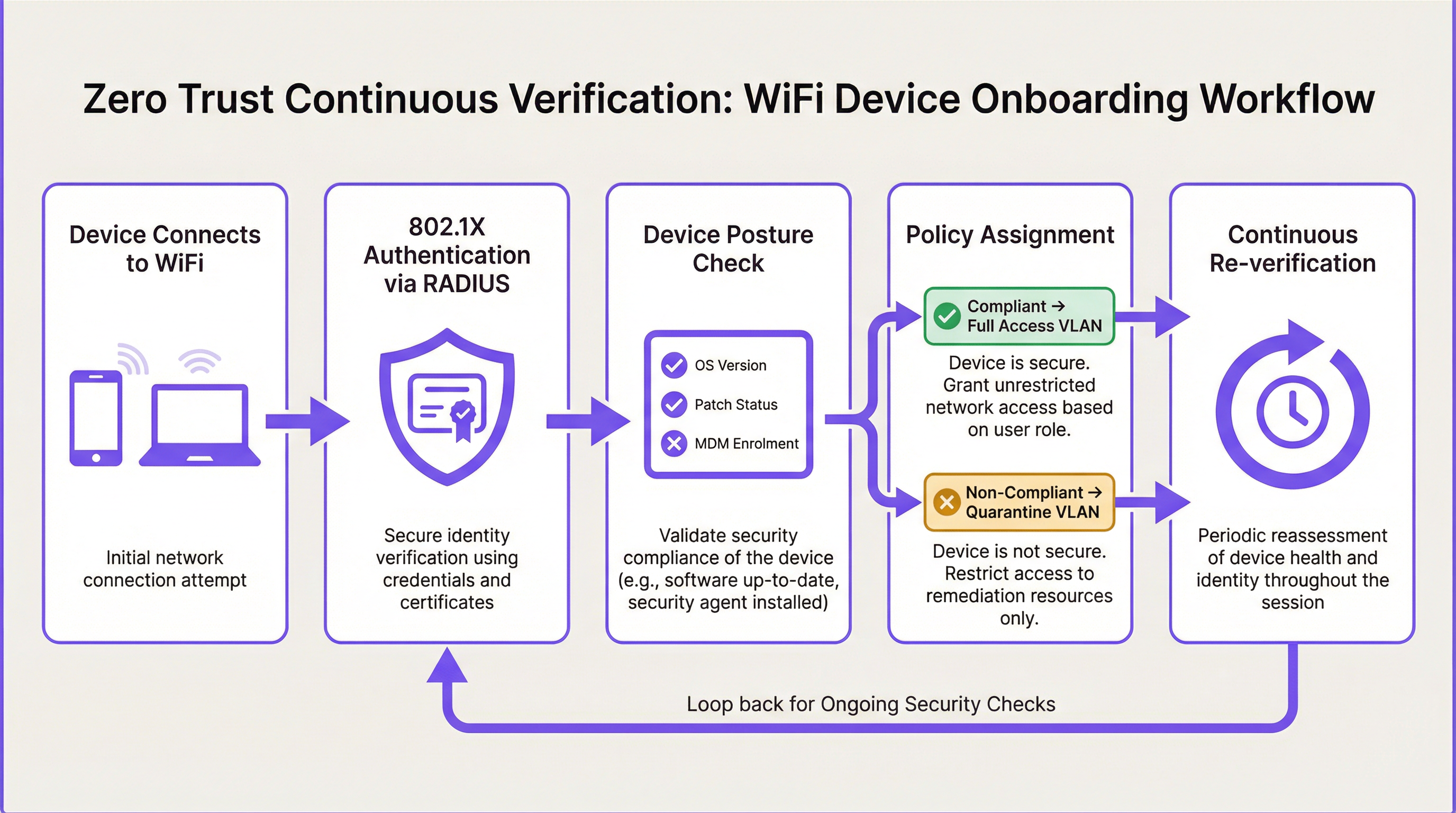
Is the device running a supported, patched operating system? Is it enrolled in the corporate Mobile Device Management (MDM) platform? Is the antivirus software active and up to date? If a device fails these posture checks, it is not simply disconnected; it is placed into a remediation VLAN with limited access to patch servers or IT support portals, allowing the user to resolve the compliance issue without requiring manual IT intervention.
Implementation Guide: Architecting the Solution
Deploying Zero Trust WiFi requires a coordinated approach across the wireless LAN, the authentication infrastructure, and the network security stack.
Core Technologies and Standards
- IEEE 802.1X: The foundation of secure network access. 802.1X provides port-based access control, ensuring that devices cannot pass traffic (other than EAP authentication frames) until they have been explicitly authenticated and authorised by the RADIUS server.
- EAP-TLS (Extensible Authentication Protocol - Transport Layer Security): The gold standard for device authentication. EAP-TLS uses client-side and server-side digital certificates for mutual authentication, entirely eliminating the risk of credential theft via phishing or Man-in-the-Middle (MitM) attacks. For a deeper dive into authentication protocols, review our guide: Comparativa de métodos EAP: PEAP, EAP-TLS, EAP-TTLS y EAP-FAST.
- WPA3-Enterprise: The current standard for wireless encryption. WPA3-Enterprise, particularly when deployed in 192-bit mode, provides the cryptographic strength required for highly sensitive environments, replacing the vulnerable WPA2 standard.
- RADIUS Policy Engine: The central brain of the architecture. The RADIUS server evaluates authentication requests against defined policies and returns dynamic attributes (VLAN IDs, ACLs, bandwidth limits) to the access point.
Step-by-Step Deployment Phasing
- Discovery and Profiling: You cannot secure what you cannot see. Begin by profiling all devices currently on the network. Use DHCP fingerprinting, MAC OUI analysis, and HTTP user-agent parsing to categorise devices into logical groups (e.g., Corporate IT, BYOD, Guest, IoT, POS).
- Define Micro-Segments: Based on the discovery phase, define your target VLAN architecture. A typical Hospitality deployment might require segments for Guest Internet, Staff Operations, Property Management Systems (PMS), and Building IoT.
- Deploy High-Availability RADIUS: Implement a robust RADIUS infrastructure capable of handling the authentication load and policy evaluation. Ensure active-active or active-passive redundancy to prevent a single point of failure.
- Implement 802.1X for Managed Devices: Begin the migration by transitioning corporate-managed laptops and tablets to 802.1X with EAP-TLS. Push the required certificates and wireless profiles via your MDM solution to ensure a seamless user experience.
- Address IoT via MAC Authentication Bypass (MAB) and Profiling: Many legacy IoT devices (printers, smart TVs, Sensors) do not support 802.1X supplicants. For these devices, implement MAB combined with strict device profiling. The RADIUS server authenticates the device based on its MAC address but applies a highly restrictive ACL that only permits communication with required servers.
- Integrate with SD-WAN: Ensure your wireless micro-segmentation aligns with your broader network architecture. As discussed in The Core SD WAN Benefits for Modern Businesses, SD-WAN can extend these segmented policies across the WAN, ensuring end-to-end Zero Trust enforcement.
Best Practices for Venue Networks
- Never Rely on PSKs for Corporate Access: Pre-Shared Keys (PSKs) provide encryption but zero identity verification. Anyone with the password has access. PSKs should be relegated exclusively to legacy IoT networks (ideally using unique PSKs per device via technologies like MPSK/DPSK) or open guest networks.
- Automate Device Onboarding: The transition to 802.1X and certificate-based authentication must be frictionless for the end-user. Utilise onboarding portals that automatically provision BYOD devices with the correct certificates and network profiles without requiring IT helpdesk tickets.
- Monitor and Baseline Behaviour: Zero Trust requires visibility. Leverage WiFi Analytics to establish baselines for normal network behaviour. If an IP camera suddenly begins attempting to initiate SSH connections to internal servers, the policy engine must detect this anomaly and automatically quarantine the device.
- Align with Modern Hardware: Ensure your infrastructure supports the required standards. Review our guide on Wireless Access Points Definition Your Ultimate 2026 Guide to understand the capabilities required for WPA3 and dynamic policy enforcement.
Troubleshooting & Risk Mitigation
Implementing Zero Trust on a live venue network carries operational risks. The most common failure modes involve blocking legitimate traffic or creating authentication loops.
| Risk/Failure Mode | Cause | Mitigation Strategy |
|---|---|---|
| 802.1X Authentication Timeouts | Supplicant misconfiguration or RADIUS server latency. | Ensure RADIUS servers are geographically proximate to the venues. Verify certificate trust chains on client devices. Use EAP-TLS to avoid user credential prompts. |
| IoT Devices Dropping Offline | Devices failing MAC Authentication Bypass or failing posture checks. | Implement a 'monitor mode' phase before enforcing block policies. Log all MAB failures and refine device profiling rules before switching to enforcement mode. |
| Over-Segmentation Complexity | Creating too many VLANs, leading to routing complexity and broken applications (e.g., multicast discovery failures like Bonjour/mDNS). | Start with broad functional segments (Guest, Staff, IoT, Secure). Only introduce further segmentation when a specific risk or compliance mandate (e.g., PCI DSS) requires it. Use Bonjour gateways if cross-VLAN discovery is necessary. |
| Captive Portal Bypasses | Advanced users spoofing MAC addresses to bypass guest portal authentication. | MAC addresses are easily spoofed. Combine MAC tracking with browser fingerprinting and enforce session timeouts to mitigate the impact of MAC spoofing. |
ROI & Business Impact
The transition to a Zero Trust WiFi architecture requires investment in engineering time, RADIUS infrastructure, and potentially NAC licensing. However, the return on investment for enterprise venues is substantial and measurable:
- Reduced Breach Impact (Blast Radius Reduction): By micro-segmenting the network, a compromised guest device or vulnerable IoT sensor cannot be used as a pivot point to attack critical infrastructure. This limits the "blast radius" of an incident, drastically reducing the potential financial and reputational damage of a breach.
- Streamlined Compliance Audits: For retail and hospitality venues, PCI DSS and GDPR compliance are significant operational burdens. Micro-segmentation clearly defines and isolates the Cardholder Data Environment (CDE) and systems processing Personally Identifiable Information (PII). This reduces the scope of compliance audits, saving significant time and consulting fees.
- Operational Efficiency: Moving away from PSK management and manual VLAN assignments to dynamic, policy-driven access reduces the IT helpdesk burden. Automated onboarding and self-service remediation workflows free up senior engineers to focus on strategic initiatives rather than resetting WiFi passwords.
- Future-Proofing the Venue: As venues deploy more advanced technologies—from Wayfinding systems to automated check-in kiosks—the attack surface expands. A Zero Trust foundation ensures that new technologies can be securely integrated without compromising the core network. As highlighted in Modern Hospitality WiFi Solutions Your Guests Deserve, security is the invisible bedrock of the modern guest experience.
Key Terms & Definitions
Zero Trust Network Access (ZTNA)
A security framework that requires all users and devices, whether inside or outside the organisation's network, to be authenticated, authorised, and continuously validated before being granted access to applications and data.
The overarching philosophy that drives the shift from perimeter-based security to identity- and context-based security on venue WiFi networks.
Micro-Segmentation
The practice of dividing a network into distinct security segments down to the individual workload or device level, applying strict access controls to dictate how these segments communicate.
Essential for limiting the 'blast radius' of a breach; ensures a compromised guest device cannot access corporate servers or POS terminals.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enforcing Zero Trust at the wireless edge, acting as the gatekeeper before any network traffic is permitted.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The policy engine in a Zero Trust WiFi architecture that evaluates credentials and dynamically assigns VLANs and access policies.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An EAP method that uses public key infrastructure (PKI) and digital certificates for mutual authentication between the client and the authentication server.
The most secure authentication method for managed devices, eliminating reliance on passwords and protecting against credential theft.
Dynamic VLAN Assignment
A network configuration where a RADIUS server assigns a device to a specific Virtual Local Area Network (VLAN) based on its authenticated identity or profile, rather than the SSID it connected to.
The primary mechanism for enforcing micro-segmentation and least-privilege access on enterprise wireless networks.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X supplicants (like many IoT devices) by using their MAC address as the identity credential.
A pragmatic workaround for legacy devices, which must be paired with strict profiling and restricted VLAN assignment due to the ease of MAC spoofing.
Device Posture
The security state of an endpoint device, including factors such as OS patch level, antivirus status, firewall configuration, and MDM enrolment.
A critical component of continuous verification; devices failing posture checks are quarantined regardless of valid user credentials.
Case Studies
A 350-room hotel group needs to secure its flat network architecture where guest devices, staff laptops, IP cameras, and the Property Management System (PMS) currently share the same VLAN, creating significant GDPR and lateral movement risks.
Deploy a micro-segmented architecture using dynamic VLAN assignment via RADIUS. Create four distinct segments: Guest Internet, Staff Corporate, IoT/Building Systems, and PMS Access. Implement 802.1X with EAP-TLS certificate authentication for staff devices via MDM. Use MAC Authentication Bypass (MAB) with strict profiling for IoT devices, placing them in an isolated VLAN with restrictive ACLs. Guest devices authenticate via a captive portal, receiving internet-only access.
A major retail chain with 200 stores must achieve PCI DSS compliance by isolating its Point of Sale (POS) terminals from the customer WiFi and staff productivity networks, all of which currently operate on the same physical wireless infrastructure.
Implement role-based access control and micro-segmentation. Configure the RADIUS policy engine to assign devices to three isolated VLANs: Customer Guest WiFi (internet only), Staff WiFi (role-based access for managers vs. associates), and a dedicated POS segment. Secure the POS segment using WPA3-Enterprise and EAP-TLS, enforcing strict firewall rules that only permit traffic to the payment gateway. Integrate RADIUS accounting logs into the SIEM for audit trails.
A stadium venue needs to deploy a new fleet of smart turnstiles. These devices support basic WPA2-Personal but do not have an 802.1X supplicant. How should the network architect integrate them into the Zero Trust WiFi environment?
The architect should utilise MAC Authentication Bypass (MAB) configured on the RADIUS server. The turnstiles' MAC addresses should be profiled, and upon connection, the RADIUS server should dynamically assign them to a dedicated, highly restricted 'Turnstile IoT' VLAN. The firewall rules for this VLAN must enforce least-privilege, permitting outbound communication only to the specific ticketing gateway IP addresses on the required ports, blocking all lateral movement to other network segments.
Scenario Analysis
Q1. During a network audit, you discover that the 'Staff Corporate' SSID uses a single Pre-Shared Key (PSK) shared among 50 employees. What are the primary security risks of this configuration in a Zero Trust context, and what is the recommended remediation?
💡 Hint:Focus on identity verification and the impact of employee turnover.
Show Recommended Approach
The primary risks are the lack of individual identity verification (anyone with the PSK is trusted) and the inability to revoke access for a single user without changing the password for everyone (e.g., when an employee leaves). The recommended remediation is to migrate the 'Staff Corporate' SSID to WPA3-Enterprise using 802.1X. Ideally, deploy EAP-TLS with certificates pushed via MDM for seamless, highly secure authentication, allowing individual device access to be revoked instantly.
Q2. A managed corporate laptop successfully authenticates via EAP-TLS and is assigned to the 'Corporate Access' VLAN. However, the user subsequently disables their endpoint detection and response (EDR) agent. How should a Zero Trust architecture handle this event?
💡 Hint:Think about the 'continuous verification' and 'device posture' pillars of Zero Trust.
Show Recommended Approach
A Zero Trust architecture must enforce continuous verification. The Network Access Control (NAC) solution, integrated with the EDR platform, should detect the posture change (EDR disabled). The NAC should then issue a Change of Authorization (CoA) to the wireless controller, dynamically revoking the laptop's 'Corporate Access' privileges mid-session and reassigning it to a 'Quarantine' VLAN until the EDR agent is re-enabled.
Q3. A hotel guest connects to the open 'Guest WiFi' SSID and authenticates via the captive portal. However, the network administrator notices that the guest device is attempting to scan IP addresses within the 10.0.0.0/8 range, which is used for internal hotel systems. What Zero Trust principle is failing, and how should it be corrected?
💡 Hint:Consider the principles of micro-segmentation and least-privilege access.
Show Recommended Approach
The principle of least-privilege access (and micro-segmentation) is failing. A guest device should only have outbound internet access and should not be able to route traffic to internal subnets. This should be corrected by ensuring the Guest VLAN has strict Access Control Lists (ACLs) applied at the firewall or gateway that explicitly drop any traffic destined for RFC 1918 private IP ranges, permitting only traffic destined for the public internet.
Key Takeaways
- ✓Zero Trust WiFi assumes no device is inherently safe, replacing perimeter security with continuous verification.
- ✓Least-privilege access ensures devices only reach the specific network resources required for their function.
- ✓Micro-segmentation via dynamic VLAN assignment isolates critical systems (like POS) from guest and IoT traffic.
- ✓Device posture enforcement validates OS patching and security agents before granting network access.
- ✓IEEE 802.1X and WPA3-Enterprise form the technical foundation for secure, policy-driven wireless authentication.
- ✓EAP-TLS certificate-based authentication is the gold standard for securing managed corporate devices.
- ✓Implementing Zero Trust reduces the 'blast radius' of breaches and streamlines compliance for PCI DSS and GDPR.



