Cumplimiento del GDPR en la recopilación de datos de WiFi para invitados
This guide provides IT managers, network architects, and Data Protection Officers with a comprehensive, actionable framework for achieving GDPR compliance across guest WiFi deployments in hospitality, retail, and public-sector venues. It covers the full spectrum of data collected by guest WiFi networks, the legal requirements for obtaining valid consent, best-practice data retention policies, and how to implement a defensible compliance architecture. Venue operators will learn how to transform their guest WiFi from a potential regulatory liability into a strategic asset that builds customer trust and drives measurable business intelligence.
🎧 Escucha esta guía
Ver transcripción
- Resumen ejecutivo
- Análisis técnico detallado
- Categorías de datos en el WiFi para invitados
- La base legal: Consentimiento vs. Interés legítimo
- Componentes arquitectónicos para el cumplimiento
- Guía de implementación
- Fase 1: Definición de políticas y requisitos (Semanas 1-2)
- Fase 2: Diseño de la solución técnica y selección de proveedores (Semanas 3-4)
- Fase 3: Implementación y pruebas (Semanas 5-6)
- Fase 4: Lanzamiento a producción y capacitación del personal (Semanas 7-8)
- Mejores prácticas
- Solución de problemas y mitigación de riesgos
- ROI e impacto comercial
Resumen ejecutivo
Esta guía proporciona a los gerentes de TI, arquitectos de redes y operadores de recintos un marco práctico y procesable para garantizar que sus servicios de WiFi para invitados cumplan plenamente con el Reglamento General de Protección de Datos (GDPR). Exploraremos los tipos específicos de datos recopilados a través del WiFi para invitados, los requisitos legales para el consentimiento y el manejo de datos, y las mejores prácticas neutrales en cuanto a proveedores para implementar una solución que cumpla con la normativa. Para el Director de Tecnología (CTO) y el Oficial de Protección de Datos (DPO), este documento describe cómo mitigar los riesgos legales y financieros asociados con el incumplimiento, que pueden incluir multas de hasta el 4 % de la facturación global anual. Para el Director de Operaciones, demuestra cómo una implementación de WiFi para invitados que cumpla con la normativa puede mejorar la confianza del cliente y proporcionar inteligencia empresarial valiosa y obtenida de forma ética. Cubriremos la arquitectura técnica de un sistema que cumpla con la normativa, desde el diseño del Captive Portal hasta la automatización de las políticas de retención de datos. La guía también incluye estudios de casos reales de los sectores de hotelería y comercio minorista, que demuestran el ROI tangible de una plataforma de WiFi para invitados bien diseñada y que cumpla con la normativa, como Purple. Al seguir los principios de esta guía, las organizaciones pueden transformar su WiFi para invitados de un posible riesgo de cumplimiento a un activo estratégico que impulse el crecimiento comercial mientras respeta la privacidad del usuario.

Análisis técnico detallado
Comprender el cumplimiento del GDPR para el WiFi para invitados comienza con una evaluación objetiva de los datos que se procesan. Según el reglamento, los "datos personales" se definen de manera amplia como cualquier información relacionada con una persona física identificada o identificable. En el contexto de una red WiFi para invitados, esto abarca una gama más amplia de puntos de datos de lo que muchas organizaciones suponen. No clasificar correctamente estos datos es un error fundamental en la estrategia de cumplimiento.
Categorías de datos en el WiFi para invitados
Los datos recopilados a través de una red WiFi para invitados se pueden segmentar en cuatro categorías principales. Cada una tiene distintas implicaciones para el cumplimiento del GDPR, en particular en lo que respecta a la base legal para el procesamiento y el período de retención requerido.
| Categoría de datos | Ejemplos | Base legal principal | Consideración clave de cumplimiento |
|---|---|---|---|
| Datos de registro | Nombre, dirección de correo electrónico, número de teléfono, datos de perfil de redes sociales | Consentimiento | Debe otorgarse de forma libre, específica, informada e inequívoca. Los datos recopilados deben minimizarse. |
| Datos de dispositivo y sesión | Dirección MAC, dirección IP, tipo de dispositivo, navegador, marcas de tiempo de conexión/desconexión, uso de datos | Interés legítimo / Consentimiento | La transparencia es clave. Se debe informar a los usuarios sobre esta recopilación. Se debe utilizar la anonimización siempre que sea posible. |
| Datos de ubicación | Ubicación del dispositivo en tiempo real, patrones de afluencia, tiempos de permanencia, mapas de calor | Consentimiento explícito | Procesamiento de alto riesgo. Requiere una aceptación (opt-in) clara y específica. El propósito debe articularse claramente (por ejemplo, "para mejorar el diseño de la tienda"). |
| Datos de uso y navegación | Sitios web visitados, aplicaciones utilizadas (menos común) | Consentimiento explícito | Riesgo extremadamente alto y rara vez justificable. Debe evitarse a menos que exista un propósito crítico, explícito y consentido. |
La base legal: Consentimiento vs. Interés legítimo
Si bien se puede argumentar el Interés legítimo para procesar datos básicos de sesión requeridos para la seguridad de la red y el monitoreo del rendimiento (por ejemplo, según el considerando 49 del GDPR), la ICO y otras autoridades de protección de datos de la UE han establecido un estándar alto. Para cualquier dato utilizado para marketing, análisis o creación de perfiles de usuario, el Consentimiento es la única base legal adecuada.
Según la ICO, "Debe asegurarse de poder demostrar que el consentimiento se otorgó de forma libre, específica e informada, y que fue una indicación inequívoca de los deseos del individuo".
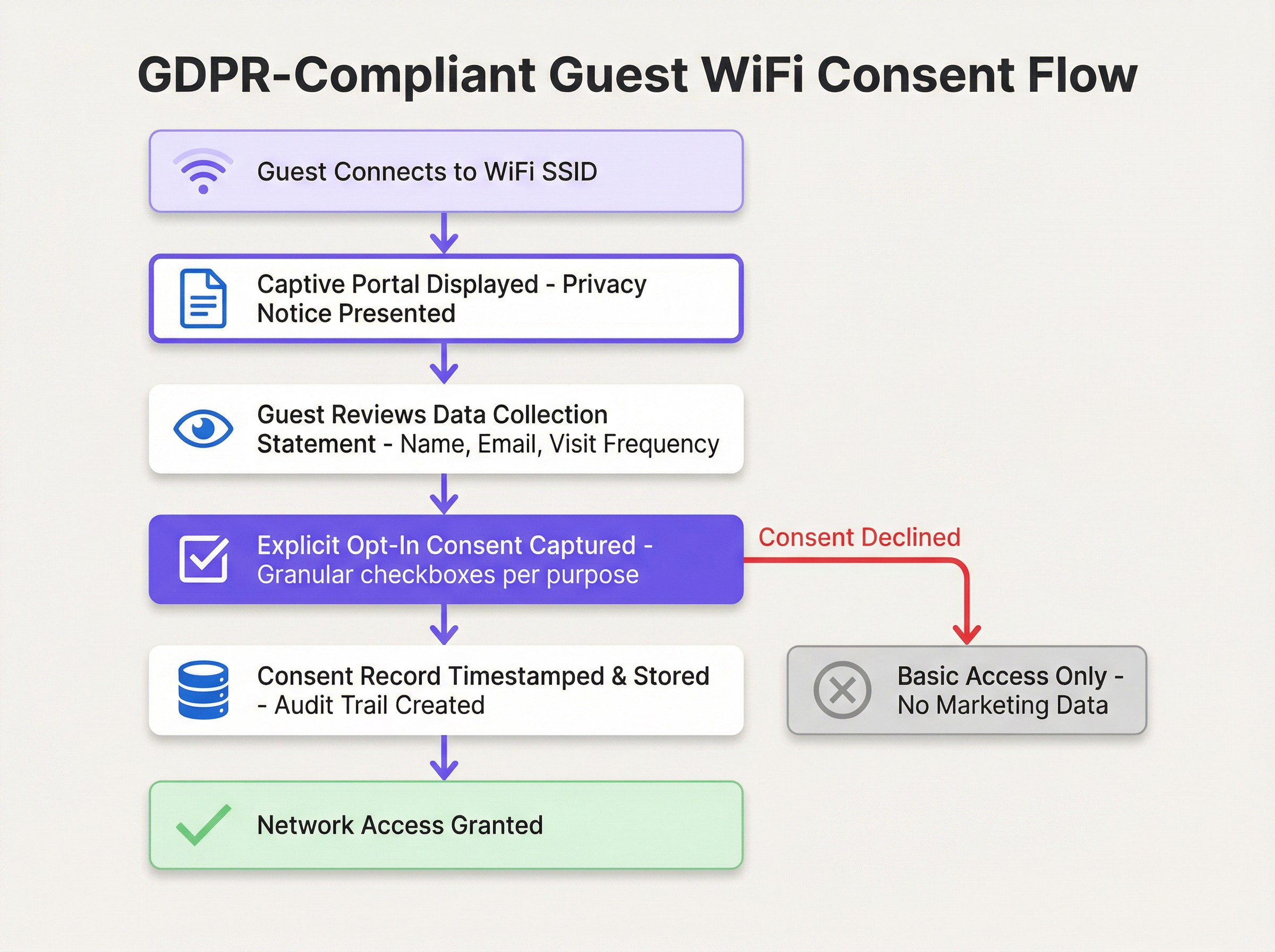
Esto requiere pasar de una aceptación pasiva de los términos a un mecanismo de consentimiento activo y granular. Por lo tanto, la arquitectura de su Captive Portal no es solo una consideración técnica, sino legal.
Componentes arquitectónicos para el cumplimiento
Una arquitectura de WiFi para invitados que cumpla con el GDPR se basa en el principio de Privacidad desde el diseño y por defecto. Esto significa que la protección de datos no es un complemento, sino un componente central del diseño del sistema.
- Base de red segura (WPA3/802.1X): Antes de recopilar cualquier dato, la red en sí debe ser segura. El uso de WPA3 es el estándar actual de la industria, proporcionando una protección sólida contra la interceptación. Para entornos empresariales, IEEE 802.1X ofrece control de acceso a la red basado en puertos, garantizando que solo los dispositivos autenticados y autorizados puedan conectarse.
- El Captive Portal que cumple con la normativa: Este es el componente más crítico de cara al usuario. Debe presentar un aviso de privacidad "justo a tiempo" antes de que el usuario ingrese cualquier información, enlazar a una política de privacidad completa y accesible, utilizar casillas de verificación granulares sin marcar para cada propósito de procesamiento y ejecutarse sobre HTTPS para evitar ataques de intermediario (man-in-the-middle).
- Plataforma de gestión del consentimiento (CMP): En segundo plano, se requiere una CMP robusta para registrar cada acción de consentimiento con una pista de auditoría inmutable, gestionar el ciclo de vida del consentimiento, incluida su revocación, e integrarse con un flujo de trabajo de DSAR (Solicitud de Acceso de los Interesados) para facilitar la búsqueda, exportación o eliminación sencilla de los datos de un usuario específico.
Guía de implementación
Implementar una solución de WiFi para invitados que cumpla con el GDPR requiere un enfoque estructurado, pasando de la definición de políticas a la configuración técnica.
Fase 1: Definición de políticas y requisitos (Semanas 1-2)
Antes de implementar cualquier hardware o software, su organización debe definir sus políticas. Convoque un taller con las partes interesadas, con representantes de TI, Legal, Marketing y Operaciones, para acordar el propósito del WiFi para invitados. Realice una Evaluación de minimización de datos, documentando la justificación comercial específica para cada punto de datos solicitado. Defina y documente el período de retención para cada categoría de datos, y seleccione y documente formalmente la base legal para cada actividad de procesamiento.
Fase 2: Diseño de la solución técnica y selección de proveedores (Semanas 3-4)
Con una política clara en vigor, evalúe su infraestructura de red actual en cuanto a la capacidad de WPA3 y segmentación de VLAN. Evalúe a los proveedores de Captive Portal y CMP según criterios que incluyan diseño de portal personalizable, registros de auditoría de consentimiento robustos y con capacidad de búsqueda, herramientas de automatización de DSAR, reglas automatizadas de retención de datos y capacidades de integración con CRM.

Fase 3: Implementación y pruebas (Semanas 5-6)
Implemente primero la solución en un entorno de prueba (staging). Configure el Captive Portal con el texto finalizado y las casillas de consentimiento sin marcar, establezca reglas de retención de datos e implemente el control de acceso basado en roles. Realice pruebas de extremo a extremo de todo el recorrido del usuario, incluida la aceptación del consentimiento, el rechazo del consentimiento, el envío de DSAR y la eliminación automatizada de datos.
Fase 4: Lanzamiento a producción y capacitación del personal (Semanas 7-8)
Lance la solución de manera gradual en todos los recintos. Capacite al personal de la mesa de ayuda de TI y de atención al público para responder preguntas básicas de los usuarios y derivar las consultas específicas de privacidad al Oficial de Protección de Datos. Asegúrese de que todas las configuraciones y procesos estén completamente documentados.
Mejores prácticas
Más allá de la implementación técnica, adherirse a las mejores prácticas estándar de la industria es crucial para mantener el cumplimiento del GDPR a largo plazo y generar confianza con sus usuarios.
Principio de privilegio mínimo: Otorgue acceso a los datos personales estrictamente según la necesidad de conocerlos, utilizando el control de acceso basado en roles (RBAC). Los equipos de marketing no deben tener acceso a los registros de seguridad de la red, y viceversa.
Auditorías periódicas y pruebas de penetración: Programe auditorías anuales que cubran la revisión del registro de consentimiento, la verificación de la política de retención y las pruebas del proceso de DSAR. Contrate a un tercero para realizar pruebas de penetración del Captive Portal y la infraestructura de WiFi.
Transparencia de cara al usuario: Implemente un aviso de privacidad en capas en el Captive Portal, proporcione un centro de preferencias de autoservicio para que los usuarios administren sus datos y complemente los esfuerzos digitales con señalización clara en el lugar de su recinto.
Anonimización y seudonimización de datos: Emplee técnicas de anonimización o seudonimización lo antes posible en el ciclo de vida de los datos. Para el análisis, almacene un hash unidireccional de la dirección MAC en lugar del identificador sin procesar, y utilice identificadores seudonimizados en su base de datos de análisis para reducir el alcance del cumplimiento.
Solución de problemas y mitigación de riesgos
Incluso con un sistema bien diseñado, pueden surgir problemas operativos y riesgos de cumplimiento. Identificar y planificar proactivamente estos escenarios es un sello distintivo de un programa maduro de gobernanza de datos.
| Modo de fallo | Impacto | Mitigación y solución |
|---|---|---|
| Discrepancia en el registro de consentimiento | Alto. La incapacidad de demostrar el consentimiento puede dar lugar a multas regulatorias. | Implemente una CMP con un registro de auditoría inmutable y con marca de tiempo. Elimine inmediatamente al usuario de las listas de marketing en caso de disputa. |
| Fallo en la retención de datos | Medio a Alto. Incumplimiento técnico de la política, crítico si se recibe un DSAR de eliminación. | Implemente un monitoreo y alertas robustos para todos los trabajos de purga de datos. Active manualmente la purga y realice un análisis posterior (post-mortem). |
| Evasión del Captive Portal | Bajo a Medio. Riesgo de acceso no autorizado a la red. | Implemente reglas estrictas de firewall que bloqueen todo el tráfico de dispositivos no autenticados, excepto DHCP y DNS hacia el portal. |
| Interrupción del proceso de DSAR | Alto. No responder en el plazo de un mes infringe el Artículo 15 del GDPR. | Cree un alias de correo electrónico de privacidad dedicado y monitoreado. Realice una capacitación anual obligatoria para el personal sobre la identificación y derivación de DSAR. |
Para la mitigación proactiva de riesgos, realice una Evaluación de Impacto en la Protección de Datos (DPIA) antes de implementar o modificar significativamente un sistema de WiFi para invitados. Lleve a cabo una debida diligencia exhaustiva de los proveedores, revisando las certificaciones de seguridad (ISO 27001, SOC 2) y asegurándose de que exista un Anexo de Procesamiento de Datos robusto. Mantenga un plan de respuesta a incidentes documentado que cubra el requisito de notificación de brechas de 72 horas.
ROI e impacto comercial
Una solución de WiFi para invitados que cumpla con el GDPR no debe verse como un centro de costos. Cuando se implementa correctamente, es un habilitador estratégico que ofrece un ROI medible a través de la mitigación de riesgos, una mayor confianza del cliente y una inteligencia empresarial ética.
Las multas del GDPR pueden alcanzar los 20 millones de euros o el 4 % de la facturación global anual. Una plataforma que cumpla con la normativa y cueste 50 000 € anuales representa una fracción de esta posible responsabilidad. Más allá de la mitigación de riesgos, los datos anonimizados y agregados recopilados con el consentimiento del usuario proporcionan información valiosa sobre la afluencia, los tiempos de permanencia, la frecuencia de las visitas y los patrones demográficos. Una cadena minorista con una facturación anual de 50 millones de euros que evita una multa de 2 millones de euros y aumenta su base de datos de marketing con consentimiento en 10 000 usuarios (con un valor promedio por cliente potencial de 10 €) logra un ROI convincente y multidimensional.
Al enmarcar la discusión en torno a la mitigación de riesgos, la confianza del cliente y la toma de decisiones ética basada en datos, los líderes de TI pueden demostrar que una solución de WiFi para invitados que cumpla con el GDPR no es solo una necesidad legal, sino un poderoso motor para el crecimiento comercial.
Términos clave y definiciones
GDPR (General Data Protection Regulation)
The EU's primary data protection law, which came into force on 25 May 2018 and was retained in UK law post-Brexit as the UK GDPR. It governs how organizations collect, process, store, and share personal data of individuals in the UK and EU. Non-compliance can result in fines of up to €20 million or 4% of annual global turnover.
IT teams encounter GDPR as the overarching legal framework governing every aspect of their guest WiFi data collection. It is the source of all consent, retention, and transparency requirements discussed in this guide.
Captive Portal
A web page presented to a user when they first connect to a guest WiFi network, before they are granted full internet access. It is the primary mechanism for presenting privacy notices, capturing consent, and collecting registration data (e.g., name, email). Under GDPR, the design of the captive portal is a critical compliance control.
Network architects and IT managers configure captive portals as part of the guest WiFi deployment. The portal's design — specifically the consent checkboxes and privacy notice — directly determines the organization's GDPR compliance posture.
Data Controller
The organization that determines the purposes and means of processing personal data. When a hotel, retailer, or venue operator deploys guest WiFi and decides what data to collect and why, they become the Data Controller and bear primary responsibility for GDPR compliance.
Venue operators are often surprised to learn they are the Data Controller for their guest WiFi, not their technology vendor. This distinction is critical because it means the legal obligations and potential fines fall on the venue operator, not the platform provider.
Data Processor
An organization that processes personal data on behalf of a Data Controller. A guest WiFi platform provider like Purple acts as a Data Processor. The relationship must be governed by a formal Data Processing Addendum (DPA) that defines the processor's obligations and restrictions.
IT managers must ensure that a DPA is in place with every technology vendor that handles personal data collected via the guest WiFi. Without a DPA, the organization is in breach of GDPR Article 28.
Consent Management Platform (CMP)
A software system that manages the collection, storage, and lifecycle of user consent. In a guest WiFi context, a CMP records every consent event with a timestamp, the specific purposes consented to, and the version of the privacy notice presented. It also manages consent withdrawal and integrates with DSAR workflows.
A CMP is the technical backbone of GDPR compliance for guest WiFi. IT managers should evaluate any guest WiFi platform on the robustness of its CMP capabilities, particularly the immutability and searchability of its consent audit log.
Data Subject Access Request (DSAR)
A formal request from an individual (the 'data subject') to an organization, asking for a copy of all personal data held about them, or requesting that their data be corrected or deleted. Under GDPR, organizations must respond to DSARs within one calendar month.
IT managers and DPOs must have a documented, tested process for handling DSARs. Guest WiFi platforms should provide tools to quickly search for and export or delete a specific user's data, reducing the operational burden of fulfilling these requests.
Data Minimisation
A core GDPR principle (Article 5(1)(c)) requiring that personal data collected must be 'adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed.' In practice, this means only collecting the data you genuinely need for a specific, stated purpose.
Data minimisation is the most commonly violated principle in guest WiFi deployments. IT managers should challenge every data field on the captive portal with the question: 'What specific business purpose does this serve, and can we achieve that purpose without this data?'
Data Protection Impact Assessment (DPIA)
A formal process for identifying and minimizing the data protection risks of a project or system. Under GDPR Article 35, a DPIA is legally mandatory before undertaking any processing that is 'likely to result in a high risk' to individuals' rights and freedoms. This includes large-scale location tracking and systematic behavioural profiling.
IT managers and DPOs must conduct a DPIA before deploying guest WiFi systems that include footfall analytics, real-time location tracking, or marketing profiling. Failure to conduct a required DPIA is itself a GDPR violation.
Pseudonymisation
A data processing technique that replaces directly identifying information (e.g., a name or email address) with an artificial identifier, such that the data can no longer be attributed to a specific individual without the use of additional information kept separately. Unlike anonymisation, pseudonymisation is reversible.
IT architects use pseudonymisation in guest WiFi analytics databases to reduce the risk associated with a data breach. If the analytics database is compromised, the attacker cannot directly identify individuals. The 'key' linking the pseudonym to the real identity is stored separately with stronger access controls.
ICO (Information Commissioner's Office)
The UK's independent authority set up to uphold information rights in the public interest, promoting openness by public bodies and data privacy for individuals. The ICO is the primary supervisory authority for GDPR compliance in the UK. It has the power to issue fines, conduct audits, and publish enforcement actions.
UK-based venue operators must comply with UK GDPR as enforced by the ICO. IT managers should monitor ICO guidance and enforcement notices, as these provide practical interpretation of how the law applies to specific scenarios, including guest WiFi.
Casos de éxito
A 250-room, four-star hotel group with 12 properties across the UK wants to deploy guest WiFi across all sites. Their primary goals are to provide a seamless connectivity experience for guests, build a consented marketing database for their loyalty programme, and gain footfall analytics to optimise lobby and restaurant layouts. Their current setup is a basic, unmanaged open WiFi network with no captive portal. How should they approach a GDPR-compliant deployment?
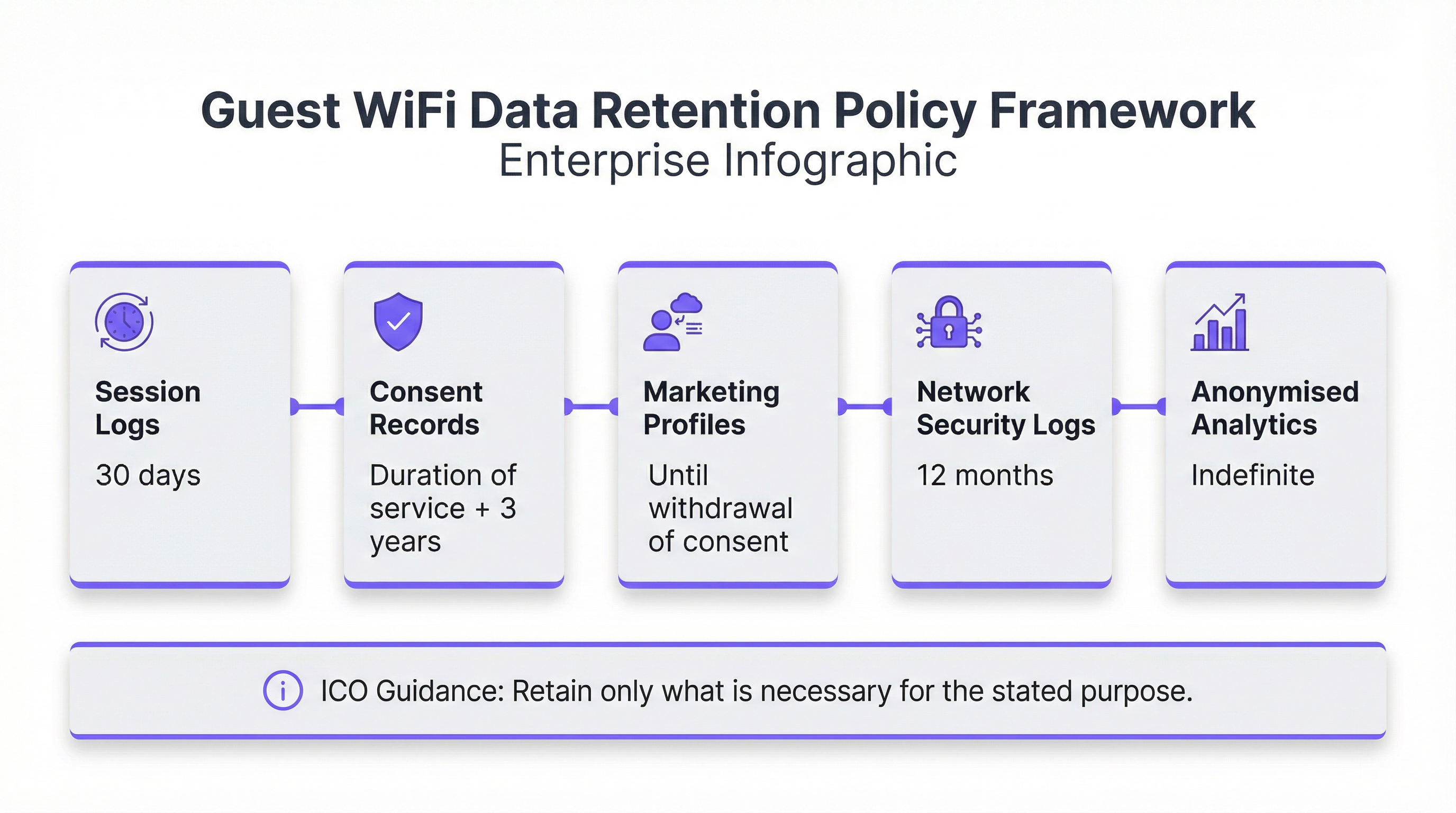
The deployment should follow a four-phase approach. In Phase 1 (Policy), the hotel group must convene a workshop with IT, Marketing, Legal, and the DPO. They need to define three distinct processing purposes: (1) providing network access, (2) marketing communications for the loyalty programme, and (3) footfall analytics. Each purpose requires a separate legal basis and consent mechanism. In Phase 2 (Design), they should select a managed guest WiFi platform such as Purple, which provides a customizable captive portal, a consent management platform, and integrated analytics. The captive portal should be designed with a clear, two-step flow: first, a mandatory acceptance of terms for network access (which can use Legitimate Interest for basic session data); second, two separate, optional, unticked checkboxes — one for 'Loyalty Programme Marketing' and one for 'Anonymous Footfall Analytics'. The privacy notice must be concise and clearly explain each purpose. In Phase 3 (Deployment), the solution should be staged at a single property first. The team must configure automated data retention rules: session logs purged after 30 days, marketing profiles retained until consent is withdrawn, and footfall analytics data anonymised at the point of collection and retained indefinitely. In Phase 4 (Rollout), the solution is deployed to all 12 properties with a phased rollout over 8 weeks. Front desk staff are trained to direct guests to the WiFi and to escalate any data queries to the DPO.
A national retail chain with 85 stores wants to use their guest WiFi to run footfall heatmaps and measure the effectiveness of in-store promotional displays. Their marketing team wants to use the WiFi to send push notifications to customers who are currently in-store. Their IT team is concerned about GDPR compliance, particularly around the use of MAC addresses for tracking. How should the IT manager advise the business?
The IT manager should advise the business that this use case is achievable but requires careful architectural decisions. First, regarding MAC address tracking: modern mobile devices (iOS 14+ and Android 10+) use MAC address randomization by default, which means that a MAC address is not a stable, persistent identifier for a specific device. However, it is still considered personal data when collected, as it can be combined with other data to identify an individual. The IT manager should recommend that the analytics platform anonymise the MAC address immediately upon collection (using a one-way hash), and that the analytics dashboard only ever display aggregated, anonymised data. This significantly reduces the GDPR risk. Second, regarding in-store push notifications: this is a high-risk processing activity that requires explicit, specific consent. The captive portal must include a specific, unticked checkbox that reads: 'I consent to receiving personalised offers and notifications while I am connected to the store WiFi.' The purpose must be clearly explained. Third, the IT manager should recommend conducting a DPIA before deploying the push notification feature, as it involves real-time location-based processing of personal data. The DPIA should assess the risk to user privacy and document the mitigations in place. A platform like Purple can support this use case with its consent management, analytics, and marketing automation capabilities, while providing the audit trail needed to demonstrate compliance.
Análisis de escenarios
Q1. You are the IT Manager for a 50-store retail chain. Your Marketing Director wants to deploy guest WiFi and use it to send in-store push notifications to customers who have previously visited any of your stores. The notifications would be triggered when a known device (identified by MAC address) reconnects to any store's WiFi. Your DPO has flagged this as high-risk. What steps must you take before this feature can be deployed, and what technical safeguards are required?
💡 Sugerencia:Consider the DPIA trigger checklist, the specific consent required for cross-store device tracking, and the technical challenges of MAC address randomization on modern devices.
Mostrar enfoque recomendado
Before deploying this feature, you must: (1) Conduct a mandatory Data Protection Impact Assessment (DPIA), as this involves systematic monitoring of individuals across multiple locations using device identifiers — a clear GDPR Article 35 trigger. The DPIA must document the risks and the mitigations. (2) Redesign the captive portal to include a specific, unticked consent checkbox that clearly explains cross-store device recognition and targeted notifications. The language must be explicit: 'I consent to [Brand] recognising my device across all stores and sending me personalised offers when I connect.' (3) Address the MAC randomization challenge: since modern iOS and Android devices randomize MAC addresses, you cannot reliably use raw MAC addresses for cross-store recognition. You must instead require users to authenticate via a persistent identifier such as an email address or social login, which then becomes the cross-store tracking key. (4) Implement a Data Processing Addendum with your push notification provider. (5) Provide a clear, accessible opt-out mechanism in every push notification and in a self-service preference center. Only after completing these steps and obtaining sign-off from the DPO should the feature be deployed.
Q2. Your organization has received a Data Subject Access Request from a former hotel guest who stayed 18 months ago. They are requesting a copy of all personal data you hold about them, including their WiFi session history. Your current guest WiFi platform stores session logs indefinitely. What are your immediate obligations, and what systemic changes should you make?
💡 Sugerencia:Consider the one-month response deadline, the data minimisation principle, and the need for a documented retention policy.
Mostrar enfoque recomendado
Your immediate obligations are: (1) Acknowledge the DSAR in writing within 5 working days, confirming you have received it and will respond within one calendar month. (2) Search all systems — your guest WiFi CMP, CRM, and any email marketing platforms — for all personal data associated with this individual. (3) Compile and provide a copy of all data found, in a commonly used electronic format, within one calendar month of receipt. This includes session logs, consent records, and any marketing profile data. The systemic change required is urgent: storing session logs indefinitely is a clear violation of the GDPR data minimisation and storage limitation principles. You must immediately define and implement a data retention policy. Session logs should be purged after 30-90 days. You must configure automated retention rules in your guest WiFi platform to enforce this policy going forward. Additionally, you should implement a formal DSAR intake process — a dedicated privacy email alias, a trained point of contact, and a documented workflow — to ensure future requests are handled efficiently and within the statutory deadline.
Q3. A conference centre is deploying guest WiFi for a major three-day event with 5,000 attendees. The event organiser wants to use the WiFi analytics to provide sponsors with data on how many unique visitors attended each sponsor's exhibition stand. The data would be presented as a report showing stand visit counts and average dwell times per stand. Is this use case GDPR-compliant as described, and what conditions must be met for it to proceed?
💡 Sugerencia:Consider the distinction between anonymised aggregate data and personal data, and the specific consent required for location-based analytics.
Mostrar enfoque recomendado
The use case as described is potentially compliant, but only under specific conditions. The key question is whether the data provided to sponsors is truly anonymised and aggregated, or whether it could be used to identify individuals. If the report shows only aggregate counts (e.g., 'Stand A received 342 unique device visits with an average dwell time of 4.2 minutes'), and if the underlying device-level data has been irreversibly anonymised before any analysis, then this data is no longer personal data and can be shared with sponsors without restriction. However, to get to this point, the following conditions must be met: (1) The captive portal for the event WiFi must include a specific, unticked consent checkbox for 'Anonymous footfall analytics to measure event attendance and stand popularity.' The purpose and the fact that aggregated data will be shared with event sponsors must be clearly disclosed. (2) The analytics platform must anonymise device identifiers (e.g., hash the MAC address) at the point of collection, before any analysis is performed. (3) The reports shared with sponsors must contain only aggregated data with no possibility of re-identification. If any stand had very few visitors, the data for that stand should be suppressed to prevent re-identification. (4) A DPIA should be conducted given the large scale of the data collection. If these conditions are met, the use case is compliant and represents a legitimate and valuable application of guest WiFi analytics.
Conclusiones clave
- ✓Guest WiFi networks collect four categories of personal data under GDPR: registration data, device and session data, location data, and usage data. Each requires a distinct legal basis and compliance approach.
- ✓Consent for marketing and analytics must be freely given, specific, informed, and unambiguous. This means separate, unticked checkboxes for each purpose on the captive portal — never bundled with the terms of service for network access.
- ✓A robust data retention policy is non-negotiable. Session logs should be purged after 30 days, consent records retained for 2 years post-last-interaction, and marketing profiles deleted upon consent withdrawal. Automate these rules in your CMP.
- ✓A Data Protection Impact Assessment (DPIA) is legally mandatory before deploying guest WiFi systems that involve large-scale location tracking, behavioural profiling, or processing data from vulnerable groups.
- ✓Your guest WiFi vendor is a Data Processor. A formal Data Processing Addendum (DPA) must be in place before any personal data is shared with them. Evaluate vendors on their security certifications (ISO 27001, SOC 2) and GDPR compliance documentation.
- ✓GDPR compliance for guest WiFi is not just a cost — it is a strategic enabler. A compliant platform mitigates fines of up to 4% of global turnover, builds customer trust, and provides ethically sourced business intelligence that drives operational and marketing ROI.
- ✓In the event of a personal data breach, the 72-hour notification clock starts the moment you become aware of it. Build this timeline into your incident response plan and ensure your team knows to notify before the investigation is complete.



