Conformità GDPR per la raccolta dati del Guest WiFi
This guide provides IT managers, network architects, and Data Protection Officers with a comprehensive, actionable framework for achieving GDPR compliance across guest WiFi deployments in hospitality, retail, and public-sector venues. It covers the full spectrum of data collected by guest WiFi networks, the legal requirements for obtaining valid consent, best-practice data retention policies, and how to implement a defensible compliance architecture. Venue operators will learn how to transform their guest WiFi from a potential regulatory liability into a strategic asset that builds customer trust and drives measurable business intelligence.
🎧 Ascolta questa guida
Visualizza trascrizione
- Riepilogo esecutivo
- Approfondimento tecnico
- Categorie di dati nel Guest WiFi
- La base giuridica: Consenso vs Interesse legittimo
- Componenti architetturali per la conformità
- Guida all'implementazione
- Fase 1: Definizione delle policy e dei requisiti (Settimane 1-2)
- Fase 2: Progettazione della soluzione tecnica e selezione del fornitore (Settimane 3-4)
- Fase 3: Implementazione e test (Settimane 5-6)
- Fase 4: Lancio in produzione e formazione del personale (Settimane 7-8)
- Best practice
- Risoluzione dei problemi e mitigazione dei rischi
- ROI e impatto aziendale
Riepilogo esecutivo
Questa guida fornisce a responsabili IT, architetti di rete e gestori di strutture un framework pratico e attuabile per garantire che i loro servizi di Guest WiFi siano pienamente conformi al Regolamento generale sulla protezione dei dati (GDPR). Esploreremo le tipologie specifiche di dati raccolti tramite il Guest WiFi, i requisiti legali per il consenso e la gestione dei dati, e le best practice indipendenti dal fornitore per implementare una soluzione conforme. Per il Chief Technology Officer e il Data Protection Officer, questo documento illustra come mitigare i rischi legali e finanziari associati alla non conformità, che possono includere sanzioni fino al 4% del fatturato globale annuo. Per l'Operations Director, dimostra come un'implementazione conforme del Guest WiFi possa rafforzare la fiducia dei clienti e fornire una business intelligence preziosa e di provenienza etica. Tratteremo l'architettura tecnica di un sistema conforme, dalla progettazione del Captive Portal all'automazione delle policy di conservazione dei dati. La guida include inoltre casi di studio reali nei settori dell'ospitalità e del retail, dimostrando il ROI tangibile di una piattaforma Guest WiFi ben strutturata e conforme come Purple. Seguendo i principi di questa guida, le organizzazioni possono trasformare il proprio Guest WiFi da potenziale rischio di conformità a risorsa strategica che promuove la crescita aziendale nel rispetto della privacy degli utenti.

Approfondimento tecnico
Comprendere la conformità GDPR per il Guest WiFi inizia con una valutazione lucida dei dati trattati. Secondo il regolamento, i 'dati personali' sono definiti in senso lato come qualsiasi informazione relativa a una persona fisica identificata o identificabile. Nel contesto di una rete Guest WiFi, ciò comprende una gamma di dati più ampia di quanto molte organizzazioni presumano. L'incapacità di classificare correttamente questi dati rappresenta un errore fondamentale nella strategia di conformità.
Categorie di dati nel Guest WiFi
I dati raccolti tramite una rete Guest WiFi possono essere suddivisi in quattro categorie principali. Ognuna ha implicazioni distinte per la conformità GDPR, in particolare per quanto riguarda la base giuridica del trattamento e il periodo di conservazione richiesto.
| Categoria di dati | Esempi | Base giuridica principale | Considerazioni chiave sulla conformità |
|---|---|---|---|
| Dati di registrazione | Nome, indirizzo email, numero di telefono, dati del profilo social | Consenso | Deve essere libero, specifico, informato e inequivocabile. I dati raccolti devono essere ridotti al minimo. |
| Dati del dispositivo e della sessione | Indirizzo MAC, indirizzo IP, tipo di dispositivo, browser, timestamp di connessione/disconnessione, utilizzo dei dati | Interesse legittimo / Consenso | La trasparenza è fondamentale. Gli utenti devono essere informati di questa raccolta. L'anonimizzazione dovrebbe essere utilizzata ove possibile. |
| Dati di localizzazione | Posizione del dispositivo in tempo reale, modelli di affluenza, tempi di permanenza, mappe di calore | Consenso esplicito | Trattamento ad alto rischio. Richiede un opt-in chiaro e specifico. Lo scopo deve essere chiaramente articolato (es. 'per migliorare il layout del negozio'). |
| Dati di utilizzo e navigazione | Siti web visitati, applicazioni utilizzate (meno comune) | Consenso esplicito | Rischio estremamente elevato e raramente giustificabile. Da evitare a meno che non vi sia uno scopo critico, esplicito e acconsentito. |
La base giuridica: Consenso vs Interesse legittimo
Sebbene l'Interesse legittimo possa essere invocato per il trattamento dei dati di sessione di base necessari per la sicurezza della rete e il monitoraggio delle prestazioni (es. come da considerando 49 del GDPR), l'ICO e le altre autorità dell'UE per la protezione dei dati hanno stabilito standard molto elevati. Per qualsiasi dato utilizzato per marketing, analisi o profilazione degli utenti, il Consenso è l'unica base giuridica appropriata.
Secondo l'ICO, "È necessario assicurarsi di poter dimostrare che il consenso è stato prestato liberamente, in modo specifico e informato, e che costituisce un'indicazione inequivocabile dei desideri dell'individuo."
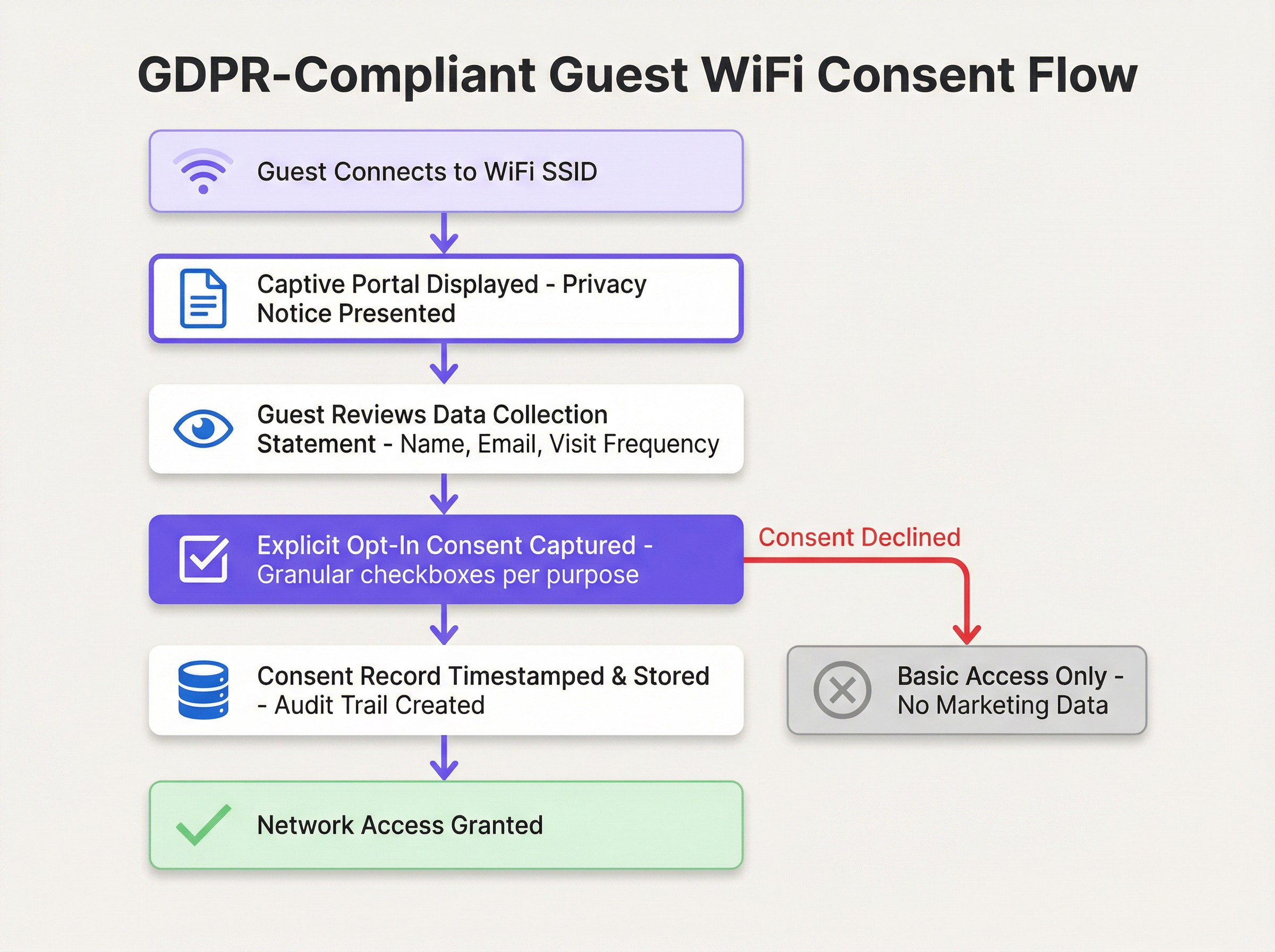
Ciò richiede il passaggio da un'accettazione passiva dei termini a un meccanismo di consenso attivo e granulare. L'architettura del vostro Captive Portal non è quindi solo una considerazione tecnica, ma anche legale.
Componenti architetturali per la conformità
Un'architettura Guest WiFi conforme al GDPR si basa sul principio della Privacy by Design e by Default. Ciò significa che la protezione dei dati non è un'aggiunta, ma un componente fondamentale della progettazione del sistema.
- Fondamenta di rete sicure (WPA3/802.1X): Prima di raccogliere qualsiasi dato, la rete stessa deve essere sicura. L'uso di WPA3 è l'attuale standard di settore e fornisce una solida protezione contro le intercettazioni. Per gli ambienti enterprise, lo standard IEEE 802.1X offre un controllo degli accessi di rete basato sulle porte, garantendo che solo i dispositivi autenticati e autorizzati possano connettersi.
- Il Captive Portal conforme: Questo è il componente rivolto all'utente più critico. Deve presentare un'informativa sulla privacy 'just-in-time' prima che l'utente inserisca qualsiasi informazione, includere un link a una privacy policy completa e accessibile, utilizzare caselle di controllo granulari non spuntate per ogni finalità di trattamento e funzionare su HTTPS per prevenire attacchi man-in-the-middle.
- Consent Management Platform (CMP): Dietro le quinte, è necessaria una solida CMP per registrare ogni azione di consenso con un audit trail immutabile, gestire il ciclo di vita del consenso inclusa la revoca, e integrarsi con un flusso di lavoro DSAR per facilitare la ricerca, l'esportazione o l'eliminazione dei dati di un utente specifico.
Guida all'implementazione
L'implementazione di una soluzione Guest WiFi conforme al GDPR richiede un approccio strutturato, passando dalla definizione delle policy alla configurazione tecnica.
Fase 1: Definizione delle policy e dei requisiti (Settimane 1-2)
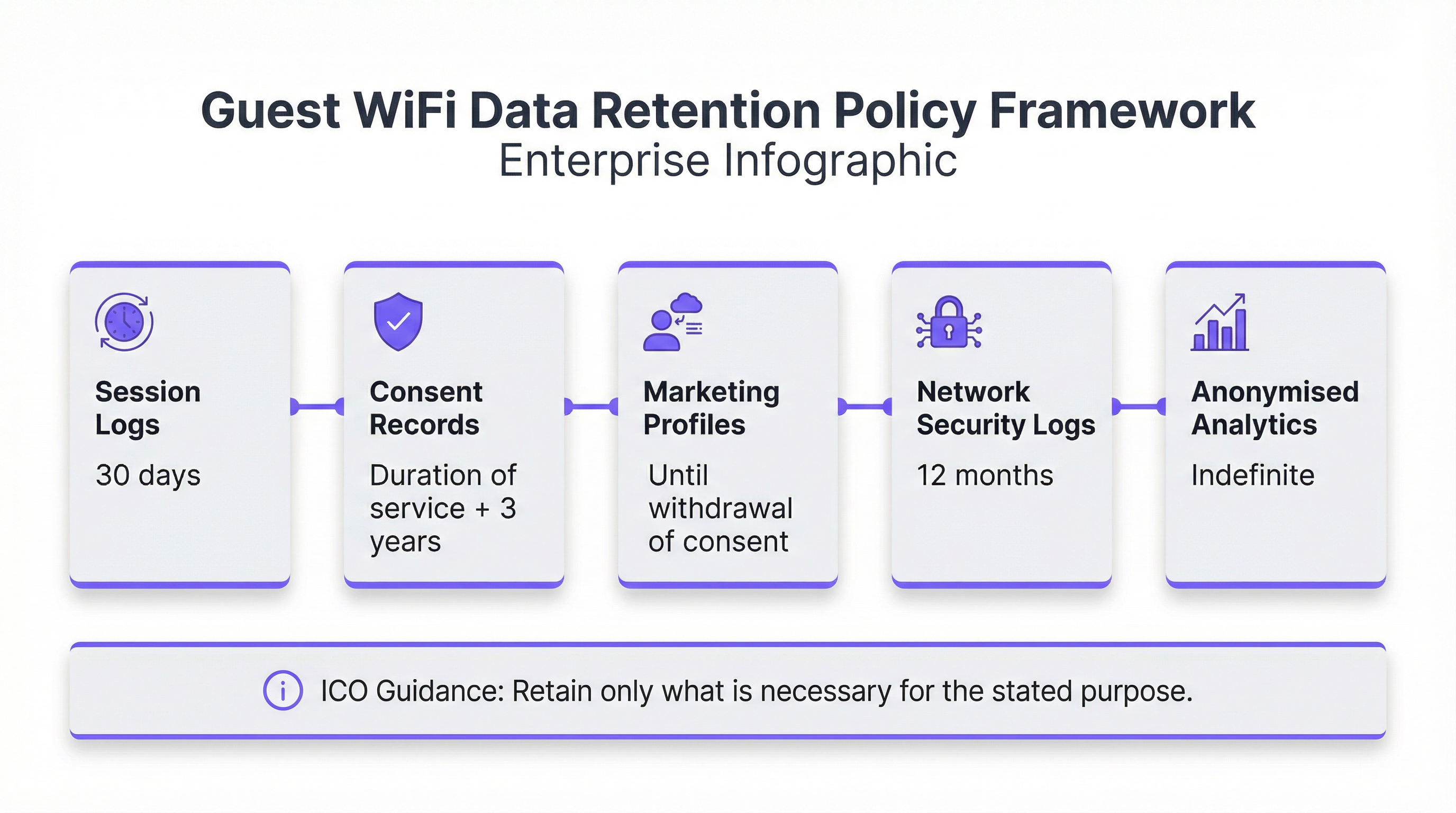
Prima di implementare qualsiasi hardware o software, l'organizzazione deve definire le proprie policy. Organizzate un workshop con gli stakeholder e i rappresentanti dei reparti IT, Legale, Marketing e Operations per concordare lo scopo del Guest WiFi. Conducete una valutazione sulla minimizzazione dei dati, documentando la specifica giustificazione aziendale per ogni dato richiesto. Definite e documentate il periodo di conservazione per ciascuna categoria di dati, e selezionate e documentate formalmente la base giuridica per ogni attività di trattamento.
Fase 2: Progettazione della soluzione tecnica e selezione del fornitore (Settimane 3-4)
Con una policy chiara in atto, valutate la vostra attuale infrastruttura di rete per le funzionalità WPA3 e di segmentazione VLAN. Valutate i fornitori di Captive Portal e CMP in base a criteri che includono il design personalizzabile del portale, log di audit del consenso solidi e ricercabili, strumenti di automazione DSAR, regole automatizzate di conservazione dei dati e capacità di integrazione CRM.

Fase 3: Implementazione e test (Settimane 5-6)
Implementate prima la soluzione in un ambiente di staging. Configurate il Captive Portal con il testo definitivo e le caselle di consenso non spuntate, impostate le regole di conservazione dei dati e implementate il controllo degli accessi basato sui ruoli. Eseguite test end-to-end dell'intero percorso dell'utente, inclusa l'accettazione del consenso, il rifiuto del consenso, l'invio di richieste DSAR e l'eliminazione automatizzata dei dati.
Fase 4: Lancio in produzione e formazione del personale (Settimane 7-8)
Distribuite la soluzione in modo graduale nelle varie sedi. Formate l'helpdesk IT e il personale di front-office per rispondere alle domande di base degli utenti e inoltrare le richieste specifiche sulla privacy al Data Protection Officer. Assicuratevi che tutte le configurazioni e i processi siano accuratamente documentati.
Best practice
Oltre all'implementazione tecnica, l'adesione alle best practice standard del settore è fondamentale per mantenere la conformità GDPR a lungo termine e creare fiducia con i vostri utenti.
Principio del privilegio minimo: Concedete l'accesso ai dati personali in base alla stretta necessità di sapere, utilizzando il controllo degli accessi basato sui ruoli (RBAC). I team di marketing non dovrebbero avere accesso ai log di sicurezza della rete e viceversa.
Audit regolari e Penetration Test: Pianificate audit annuali che coprano la revisione dei log di consenso, la verifica delle policy di conservazione e i test del processo DSAR. Incaricate una terza parte per i penetration test del Captive Portal e dell'infrastruttura WiFi.
Trasparenza verso l'utente: Implementate un'informativa sulla privacy a più livelli sul Captive Portal, fornite un centro preferenze self-service affinché gli utenti possano gestire i propri dati e integrate le iniziative digitali con una chiara segnaletica in loco nella vostra struttura.
Anonimizzazione e pseudonimizzazione dei dati: Impiegate tecniche di anonimizzazione o pseudonimizzazione il prima possibile nel ciclo di vita dei dati. Per le analisi, archiviate un hash unidirezionale dell'indirizzo MAC anziché l'identificatore grezzo e utilizzate identificatori pseudonimizzati nel vostro database di analisi per ridurre l'ambito di conformità.
Risoluzione dei problemi e mitigazione dei rischi
Anche con un sistema ben progettato, possono sorgere problemi operativi e rischi di conformità. Identificare e pianificare in modo proattivo questi scenari è il segno distintivo di un programma di data governance maturo.
| Modalità di guasto | Impatto | Mitigazione e soluzione |
|---|---|---|
| Mancata corrispondenza dei record di consenso | Alto. L'incapacità di dimostrare il consenso può portare a sanzioni normative. | Implementare una CMP con un log di audit immutabile e con timestamp. Rimuovere immediatamente l'utente dalle liste di marketing in caso di contestazione. |
| Errore di conservazione dei dati | Da medio ad alto. Violazione tecnica della policy, critica se si riceve una richiesta DSAR di cancellazione. | Implementare un monitoraggio e avvisi solidi per tutti i processi di eliminazione dei dati. Attivare manualmente l'eliminazione e condurre un'analisi post-mortem. |
| Bypass del Captive Portal | Da basso a medio. Rischio di accesso non autorizzato alla rete. | Implementare rigide regole firewall che blocchino tutto il traffico dai dispositivi non autenticati, ad eccezione di DHCP e DNS verso il portale. |
| Interruzione del processo DSAR | Alto. La mancata risposta entro un mese viola l'Articolo 15 del GDPR. | Creare un alias email dedicato e monitorato per la privacy. Condurre una formazione annuale obbligatoria del personale sull'identificazione e l'escalation delle richieste DSAR. |
Per una mitigazione proattiva dei rischi, conducete una Valutazione d'impatto sulla protezione dei dati (DPIA) prima di implementare o modificare in modo significativo un sistema Guest WiFi. Eseguite un'accurata due diligence sui fornitori, esaminando le certificazioni di sicurezza (ISO 27001, SOC 2) e assicurandovi che sia in atto un solido Data Processing Addendum. Mantenete un piano di risposta agli incidenti documentato che copra il requisito di notifica delle violazioni entro 72 ore.
ROI e impatto aziendale
Una soluzione Guest WiFi conforme al GDPR non dovrebbe essere considerata un centro di costo. Se implementata correttamente, è un fattore abilitante strategico che offre un ROI misurabile attraverso la mitigazione dei rischi, una maggiore fiducia dei clienti e una business intelligence etica.
Le sanzioni GDPR possono raggiungere i 20 milioni di euro o il 4% del fatturato globale annuo. Una piattaforma conforme che costa 50.000 € all'anno rappresenta una frazione di questa potenziale responsabilità. Oltre alla mitigazione dei rischi, i dati anonimizzati e aggregati raccolti con il consenso dell'utente forniscono preziose informazioni su affluenza, tempi di permanenza, frequenza delle visite e modelli demografici. Una catena di negozi con un fatturato annuo di 50 milioni di euro che evita una multa di 2 milioni di euro e fa crescere il proprio database di marketing acconsentito di 10.000 utenti (con un valore medio per lead di 10 €) ottiene un ROI convincente e multidimensionale.
Inquadrando la discussione attorno alla mitigazione dei rischi, alla fiducia dei clienti e al processo decisionale etico basato sui dati, i leader IT possono dimostrare che una soluzione Guest WiFi conforme al GDPR non è solo una necessità legale, ma un potente motore per la crescita aziendale.
Termini chiave e definizioni
GDPR (General Data Protection Regulation)
The EU's primary data protection law, which came into force on 25 May 2018 and was retained in UK law post-Brexit as the UK GDPR. It governs how organizations collect, process, store, and share personal data of individuals in the UK and EU. Non-compliance can result in fines of up to €20 million or 4% of annual global turnover.
IT teams encounter GDPR as the overarching legal framework governing every aspect of their guest WiFi data collection. It is the source of all consent, retention, and transparency requirements discussed in this guide.
Captive Portal
A web page presented to a user when they first connect to a guest WiFi network, before they are granted full internet access. It is the primary mechanism for presenting privacy notices, capturing consent, and collecting registration data (e.g., name, email). Under GDPR, the design of the captive portal is a critical compliance control.
Network architects and IT managers configure captive portals as part of the guest WiFi deployment. The portal's design — specifically the consent checkboxes and privacy notice — directly determines the organization's GDPR compliance posture.
Data Controller
The organization that determines the purposes and means of processing personal data. When a hotel, retailer, or venue operator deploys guest WiFi and decides what data to collect and why, they become the Data Controller and bear primary responsibility for GDPR compliance.
Venue operators are often surprised to learn they are the Data Controller for their guest WiFi, not their technology vendor. This distinction is critical because it means the legal obligations and potential fines fall on the venue operator, not the platform provider.
Data Processor
An organization that processes personal data on behalf of a Data Controller. A guest WiFi platform provider like Purple acts as a Data Processor. The relationship must be governed by a formal Data Processing Addendum (DPA) that defines the processor's obligations and restrictions.
IT managers must ensure that a DPA is in place with every technology vendor that handles personal data collected via the guest WiFi. Without a DPA, the organization is in breach of GDPR Article 28.
Consent Management Platform (CMP)
A software system that manages the collection, storage, and lifecycle of user consent. In a guest WiFi context, a CMP records every consent event with a timestamp, the specific purposes consented to, and the version of the privacy notice presented. It also manages consent withdrawal and integrates with DSAR workflows.
A CMP is the technical backbone of GDPR compliance for guest WiFi. IT managers should evaluate any guest WiFi platform on the robustness of its CMP capabilities, particularly the immutability and searchability of its consent audit log.
Data Subject Access Request (DSAR)
A formal request from an individual (the 'data subject') to an organization, asking for a copy of all personal data held about them, or requesting that their data be corrected or deleted. Under GDPR, organizations must respond to DSARs within one calendar month.
IT managers and DPOs must have a documented, tested process for handling DSARs. Guest WiFi platforms should provide tools to quickly search for and export or delete a specific user's data, reducing the operational burden of fulfilling these requests.
Data Minimisation
A core GDPR principle (Article 5(1)(c)) requiring that personal data collected must be 'adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed.' In practice, this means only collecting the data you genuinely need for a specific, stated purpose.
Data minimisation is the most commonly violated principle in guest WiFi deployments. IT managers should challenge every data field on the captive portal with the question: 'What specific business purpose does this serve, and can we achieve that purpose without this data?'
Data Protection Impact Assessment (DPIA)
A formal process for identifying and minimizing the data protection risks of a project or system. Under GDPR Article 35, a DPIA is legally mandatory before undertaking any processing that is 'likely to result in a high risk' to individuals' rights and freedoms. This includes large-scale location tracking and systematic behavioural profiling.
IT managers and DPOs must conduct a DPIA before deploying guest WiFi systems that include footfall analytics, real-time location tracking, or marketing profiling. Failure to conduct a required DPIA is itself a GDPR violation.
Pseudonymisation
A data processing technique that replaces directly identifying information (e.g., a name or email address) with an artificial identifier, such that the data can no longer be attributed to a specific individual without the use of additional information kept separately. Unlike anonymisation, pseudonymisation is reversible.
IT architects use pseudonymisation in guest WiFi analytics databases to reduce the risk associated with a data breach. If the analytics database is compromised, the attacker cannot directly identify individuals. The 'key' linking the pseudonym to the real identity is stored separately with stronger access controls.
ICO (Information Commissioner's Office)
The UK's independent authority set up to uphold information rights in the public interest, promoting openness by public bodies and data privacy for individuals. The ICO is the primary supervisory authority for GDPR compliance in the UK. It has the power to issue fines, conduct audits, and publish enforcement actions.
UK-based venue operators must comply with UK GDPR as enforced by the ICO. IT managers should monitor ICO guidance and enforcement notices, as these provide practical interpretation of how the law applies to specific scenarios, including guest WiFi.
Casi di studio
A 250-room, four-star hotel group with 12 properties across the UK wants to deploy guest WiFi across all sites. Their primary goals are to provide a seamless connectivity experience for guests, build a consented marketing database for their loyalty programme, and gain footfall analytics to optimise lobby and restaurant layouts. Their current setup is a basic, unmanaged open WiFi network with no captive portal. How should they approach a GDPR-compliant deployment?
The deployment should follow a four-phase approach. In Phase 1 (Policy), the hotel group must convene a workshop with IT, Marketing, Legal, and the DPO. They need to define three distinct processing purposes: (1) providing network access, (2) marketing communications for the loyalty programme, and (3) footfall analytics. Each purpose requires a separate legal basis and consent mechanism. In Phase 2 (Design), they should select a managed guest WiFi platform such as Purple, which provides a customizable captive portal, a consent management platform, and integrated analytics. The captive portal should be designed with a clear, two-step flow: first, a mandatory acceptance of terms for network access (which can use Legitimate Interest for basic session data); second, two separate, optional, unticked checkboxes — one for 'Loyalty Programme Marketing' and one for 'Anonymous Footfall Analytics'. The privacy notice must be concise and clearly explain each purpose. In Phase 3 (Deployment), the solution should be staged at a single property first. The team must configure automated data retention rules: session logs purged after 30 days, marketing profiles retained until consent is withdrawn, and footfall analytics data anonymised at the point of collection and retained indefinitely. In Phase 4 (Rollout), the solution is deployed to all 12 properties with a phased rollout over 8 weeks. Front desk staff are trained to direct guests to the WiFi and to escalate any data queries to the DPO.
A national retail chain with 85 stores wants to use their guest WiFi to run footfall heatmaps and measure the effectiveness of in-store promotional displays. Their marketing team wants to use the WiFi to send push notifications to customers who are currently in-store. Their IT team is concerned about GDPR compliance, particularly around the use of MAC addresses for tracking. How should the IT manager advise the business?
The IT manager should advise the business that this use case is achievable but requires careful architectural decisions. First, regarding MAC address tracking: modern mobile devices (iOS 14+ and Android 10+) use MAC address randomization by default, which means that a MAC address is not a stable, persistent identifier for a specific device. However, it is still considered personal data when collected, as it can be combined with other data to identify an individual. The IT manager should recommend that the analytics platform anonymise the MAC address immediately upon collection (using a one-way hash), and that the analytics dashboard only ever display aggregated, anonymised data. This significantly reduces the GDPR risk. Second, regarding in-store push notifications: this is a high-risk processing activity that requires explicit, specific consent. The captive portal must include a specific, unticked checkbox that reads: 'I consent to receiving personalised offers and notifications while I am connected to the store WiFi.' The purpose must be clearly explained. Third, the IT manager should recommend conducting a DPIA before deploying the push notification feature, as it involves real-time location-based processing of personal data. The DPIA should assess the risk to user privacy and document the mitigations in place. A platform like Purple can support this use case with its consent management, analytics, and marketing automation capabilities, while providing the audit trail needed to demonstrate compliance.
Analisi degli scenari
Q1. You are the IT Manager for a 50-store retail chain. Your Marketing Director wants to deploy guest WiFi and use it to send in-store push notifications to customers who have previously visited any of your stores. The notifications would be triggered when a known device (identified by MAC address) reconnects to any store's WiFi. Your DPO has flagged this as high-risk. What steps must you take before this feature can be deployed, and what technical safeguards are required?
💡 Suggerimento:Consider the DPIA trigger checklist, the specific consent required for cross-store device tracking, and the technical challenges of MAC address randomization on modern devices.
Mostra l'approccio consigliato
Before deploying this feature, you must: (1) Conduct a mandatory Data Protection Impact Assessment (DPIA), as this involves systematic monitoring of individuals across multiple locations using device identifiers — a clear GDPR Article 35 trigger. The DPIA must document the risks and the mitigations. (2) Redesign the captive portal to include a specific, unticked consent checkbox that clearly explains cross-store device recognition and targeted notifications. The language must be explicit: 'I consent to [Brand] recognising my device across all stores and sending me personalised offers when I connect.' (3) Address the MAC randomization challenge: since modern iOS and Android devices randomize MAC addresses, you cannot reliably use raw MAC addresses for cross-store recognition. You must instead require users to authenticate via a persistent identifier such as an email address or social login, which then becomes the cross-store tracking key. (4) Implement a Data Processing Addendum with your push notification provider. (5) Provide a clear, accessible opt-out mechanism in every push notification and in a self-service preference center. Only after completing these steps and obtaining sign-off from the DPO should the feature be deployed.
Q2. Your organization has received a Data Subject Access Request from a former hotel guest who stayed 18 months ago. They are requesting a copy of all personal data you hold about them, including their WiFi session history. Your current guest WiFi platform stores session logs indefinitely. What are your immediate obligations, and what systemic changes should you make?
💡 Suggerimento:Consider the one-month response deadline, the data minimisation principle, and the need for a documented retention policy.
Mostra l'approccio consigliato
Your immediate obligations are: (1) Acknowledge the DSAR in writing within 5 working days, confirming you have received it and will respond within one calendar month. (2) Search all systems — your guest WiFi CMP, CRM, and any email marketing platforms — for all personal data associated with this individual. (3) Compile and provide a copy of all data found, in a commonly used electronic format, within one calendar month of receipt. This includes session logs, consent records, and any marketing profile data. The systemic change required is urgent: storing session logs indefinitely is a clear violation of the GDPR data minimisation and storage limitation principles. You must immediately define and implement a data retention policy. Session logs should be purged after 30-90 days. You must configure automated retention rules in your guest WiFi platform to enforce this policy going forward. Additionally, you should implement a formal DSAR intake process — a dedicated privacy email alias, a trained point of contact, and a documented workflow — to ensure future requests are handled efficiently and within the statutory deadline.
Q3. A conference centre is deploying guest WiFi for a major three-day event with 5,000 attendees. The event organiser wants to use the WiFi analytics to provide sponsors with data on how many unique visitors attended each sponsor's exhibition stand. The data would be presented as a report showing stand visit counts and average dwell times per stand. Is this use case GDPR-compliant as described, and what conditions must be met for it to proceed?
💡 Suggerimento:Consider the distinction between anonymised aggregate data and personal data, and the specific consent required for location-based analytics.
Mostra l'approccio consigliato
The use case as described is potentially compliant, but only under specific conditions. The key question is whether the data provided to sponsors is truly anonymised and aggregated, or whether it could be used to identify individuals. If the report shows only aggregate counts (e.g., 'Stand A received 342 unique device visits with an average dwell time of 4.2 minutes'), and if the underlying device-level data has been irreversibly anonymised before any analysis, then this data is no longer personal data and can be shared with sponsors without restriction. However, to get to this point, the following conditions must be met: (1) The captive portal for the event WiFi must include a specific, unticked consent checkbox for 'Anonymous footfall analytics to measure event attendance and stand popularity.' The purpose and the fact that aggregated data will be shared with event sponsors must be clearly disclosed. (2) The analytics platform must anonymise device identifiers (e.g., hash the MAC address) at the point of collection, before any analysis is performed. (3) The reports shared with sponsors must contain only aggregated data with no possibility of re-identification. If any stand had very few visitors, the data for that stand should be suppressed to prevent re-identification. (4) A DPIA should be conducted given the large scale of the data collection. If these conditions are met, the use case is compliant and represents a legitimate and valuable application of guest WiFi analytics.
Punti chiave
- ✓Guest WiFi networks collect four categories of personal data under GDPR: registration data, device and session data, location data, and usage data. Each requires a distinct legal basis and compliance approach.
- ✓Consent for marketing and analytics must be freely given, specific, informed, and unambiguous. This means separate, unticked checkboxes for each purpose on the captive portal — never bundled with the terms of service for network access.
- ✓A robust data retention policy is non-negotiable. Session logs should be purged after 30 days, consent records retained for 2 years post-last-interaction, and marketing profiles deleted upon consent withdrawal. Automate these rules in your CMP.
- ✓A Data Protection Impact Assessment (DPIA) is legally mandatory before deploying guest WiFi systems that involve large-scale location tracking, behavioural profiling, or processing data from vulnerable groups.
- ✓Your guest WiFi vendor is a Data Processor. A formal Data Processing Addendum (DPA) must be in place before any personal data is shared with them. Evaluate vendors on their security certifications (ISO 27001, SOC 2) and GDPR compliance documentation.
- ✓GDPR compliance for guest WiFi is not just a cost — it is a strategic enabler. A compliant platform mitigates fines of up to 4% of global turnover, builds customer trust, and provides ethically sourced business intelligence that drives operational and marketing ROI.
- ✓In the event of a personal data breach, the 72-hour notification clock starts the moment you become aware of it. Build this timeline into your incident response plan and ensure your team knows to notify before the investigation is complete.



