Arquitectura WiFi Zero Trust: Aplicación de Zero Trust en redes de recintos
Una guía de referencia técnica integral que detalla cómo los operadores de recintos pueden aplicar los principios de Zero Trust a las redes WiFi empresariales. Abarca la verificación continua, la microsegmentación y la aplicación de la postura del dispositivo para proteger entornos de hotelería, retail y del sector público contra el movimiento lateral y los riesgos de cumplimiento.
🎧 Escucha esta guía
Ver transcripción
- Resumen ejecutivo
- Análisis técnico profundo: Los cuatro pilares de WiFi Zero Trust
- 1. Verificación continua
- 2. Acceso a la red de menor privilegio
- 3. Microsegmentación mediante VLAN dinámicas
- 4. Aplicación de la postura del dispositivo
- Guía de implementación: Arquitectura de la solución
- Tecnologías y estándares principales
- Fases de implementación paso a paso
- Mejores prácticas para redes de recintos
- Solución de problemas y mitigación de riesgos
- ROI e impacto empresarial

Resumen ejecutivo
El perímetro ha muerto. Para los operadores de recintos (hoteles, cadenas de retail, estadios y organizaciones del sector público), el modelo de seguridad tradicional de confiar en cualquier dispositivo que se autentique con éxito en la red WiFi ya no es viable. Una red de recinto moderna es un ecosistema complejo de laptops corporativas, smartphones BYOD, dispositivos de invitados no gestionados, sensores IoT e infraestructura crítica como terminales POS y sistemas de gestión de propiedades, todos compartiendo el mismo espacio físico.
La arquitectura WiFi Zero Trust es el imperativo estratégico para asegurar este entorno. Sustituye el modelo defectuoso de "confiar pero verificar" por la verificación continua, el acceso de menor privilegio y una microsegmentación estricta. Esta guía de referencia práctica proporciona a los líderes de TI el plan maestro para aplicar los principios de Zero Trust a las redes inalámbricas empresariales. Detallamos las tecnologías fundamentales (IEEE 802.1X, WPA3-Enterprise y la aplicación de políticas RADIUS) y proporcionamos orientación de implementación accionable para asegurar sus recintos sin comprometer la experiencia del usuario. Al implementar estos controles, las organizaciones pueden reducir drásticamente su superficie de ataque, garantizar el cumplimiento de PCI DSS y GDPR, y mitigar el riesgo de movimiento lateral en caso de una brecha.
Escuche nuestro informe ejecutivo sobre la arquitectura WiFi Zero Trust:
Análisis técnico profundo: Los cuatro pilares de WiFi Zero Trust
Zero Trust no es un producto único que se pueda comprar e instalar en un rack; es un marco arquitectónico. Cuando se aplica al borde inalámbrico, se basa en cuatro pilares fundamentales para trasladar la seguridad del perímetro de la red a los dispositivos y usuarios individuales.
1. Verificación continua
El modelo de seguridad WiFi tradicional se basa en un evento de autenticación único. Un usuario introduce una PSK o sus credenciales de Active Directory, el punto de acceso concede el acceso y se confía en el dispositivo durante la sesión. Zero Trust exige una verificación continua.
Esto significa que nunca se asume que la confianza sea permanente. Mediante configuraciones avanzadas de RADIUS y políticas de Control de Acceso a la Red (NAC), la red reevalúa continuamente el derecho del dispositivo a acceder a los recursos. Si el contexto de un dispositivo cambia (por ejemplo, si se desactiva su agente de protección de endpoints o si intenta acceder a recursos fuera de su perfil de comportamiento normal), sus privilegios de acceso pueden revocarse o restringirse dinámicamente a mitad de la sesión. Esto requiere configurar temporizadores de reautenticación de sesión e integrar su controlador inalámbrico con un proveedor de identidad robusto.
2. Acceso a la red de menor privilegio
¿Qué puede hacer un dispositivo una vez autenticado? En una red plana, la respuesta es "casi cualquier cosa". En una arquitectura Zero Trust, a cada dispositivo se le concede el acceso mínimo absoluto necesario para realizar su función.
Un invitado que se conecta a través de Guest WiFi requiere acceso a internet de salida y resolución DNS; no tiene ninguna razón legítima para comunicarse con la subred local. Una laptop corporativa gestionada puede requerir acceso a archivos compartidos internos y aplicaciones en la nube. Un termostato inteligente requiere comunicación únicamente con su controlador en la nube específico. Este principio se aplica en el borde de la red mediante la asignación dinámica de roles, donde el servidor RADIUS devuelve atributos específicos del proveedor (VSAs) al punto de acceso, situando al dispositivo en un rol estrictamente controlado en lugar de en un segmento de red amplio y permisivo.
3. Microsegmentación mediante VLAN dinámicas
La microsegmentación es el mecanismo mediante el cual se aplica el acceso de menor privilegio en la capa de red. En lugar de mantener una única subred grande para todos los clientes inalámbricos, la red se divide en segmentos discretos y lógicamente aislados, normalmente mediante la asignación dinámica de VLAN.
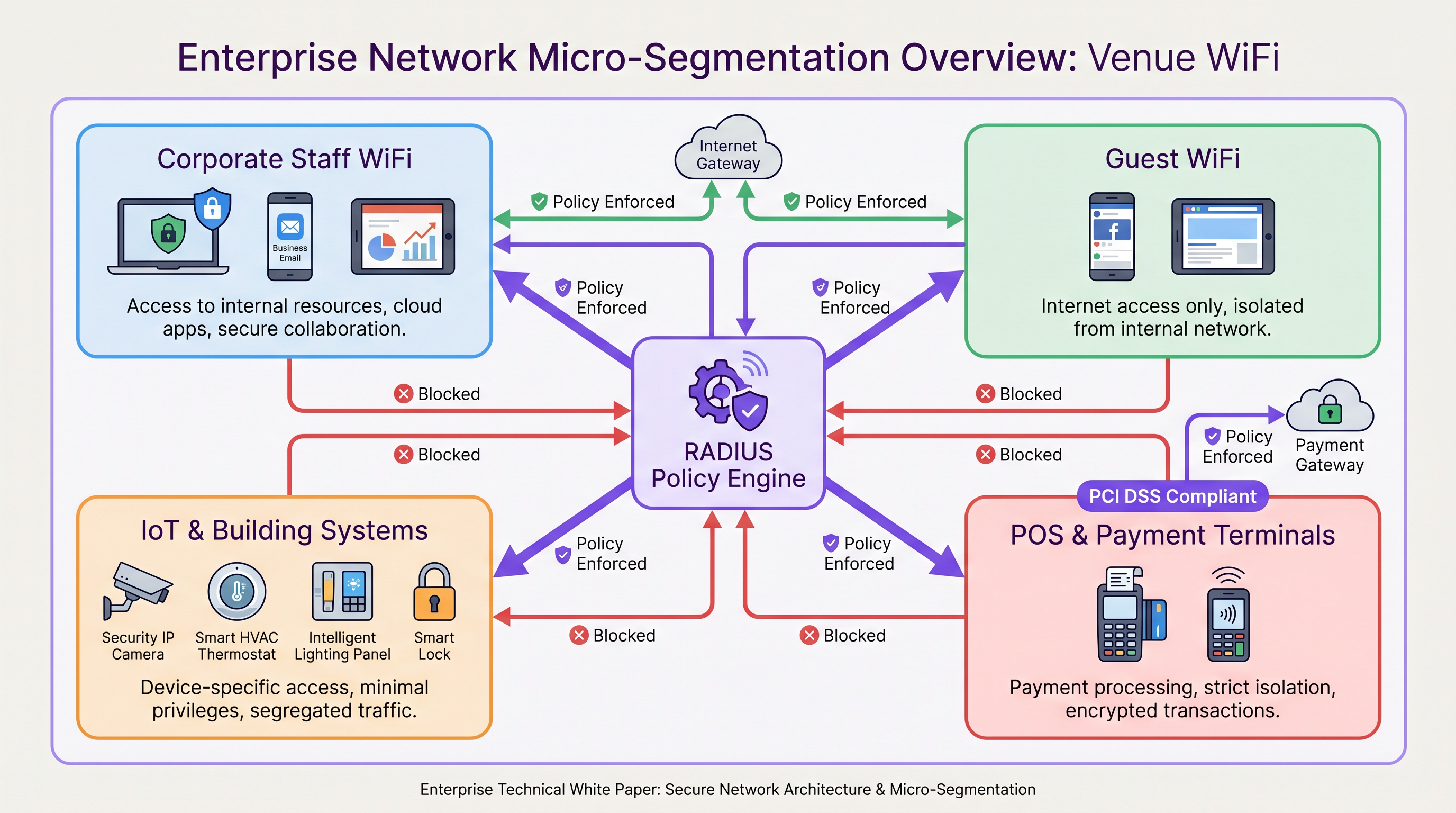
Cuando un dispositivo se autentica mediante 802.1X, el motor de políticas RADIUS evalúa la identidad del usuario, el tipo de dispositivo y la ubicación, y asigna el dispositivo a la VLAN adecuada. Los firewalls y las listas de control de acceso (ACL) rigen entonces el flujo de tráfico entre estos microsegmentos. Por ejemplo, en entornos de Retail , el cumplimiento de PCI DSS exige el aislamiento estricto del entorno de datos de los titulares de tarjetas. La microsegmentación garantiza que un dispositivo comprometido en la red de invitados no pueda pivotar y comunicarse con las terminales POS.
4. Aplicación de la postura del dispositivo
La identidad por sí sola es insuficiente para establecer la confianza; también debe verificarse el estado y el cumplimiento del dispositivo. La aplicación de la postura del dispositivo comprueba el estado del endpoint antes de conceder el acceso.
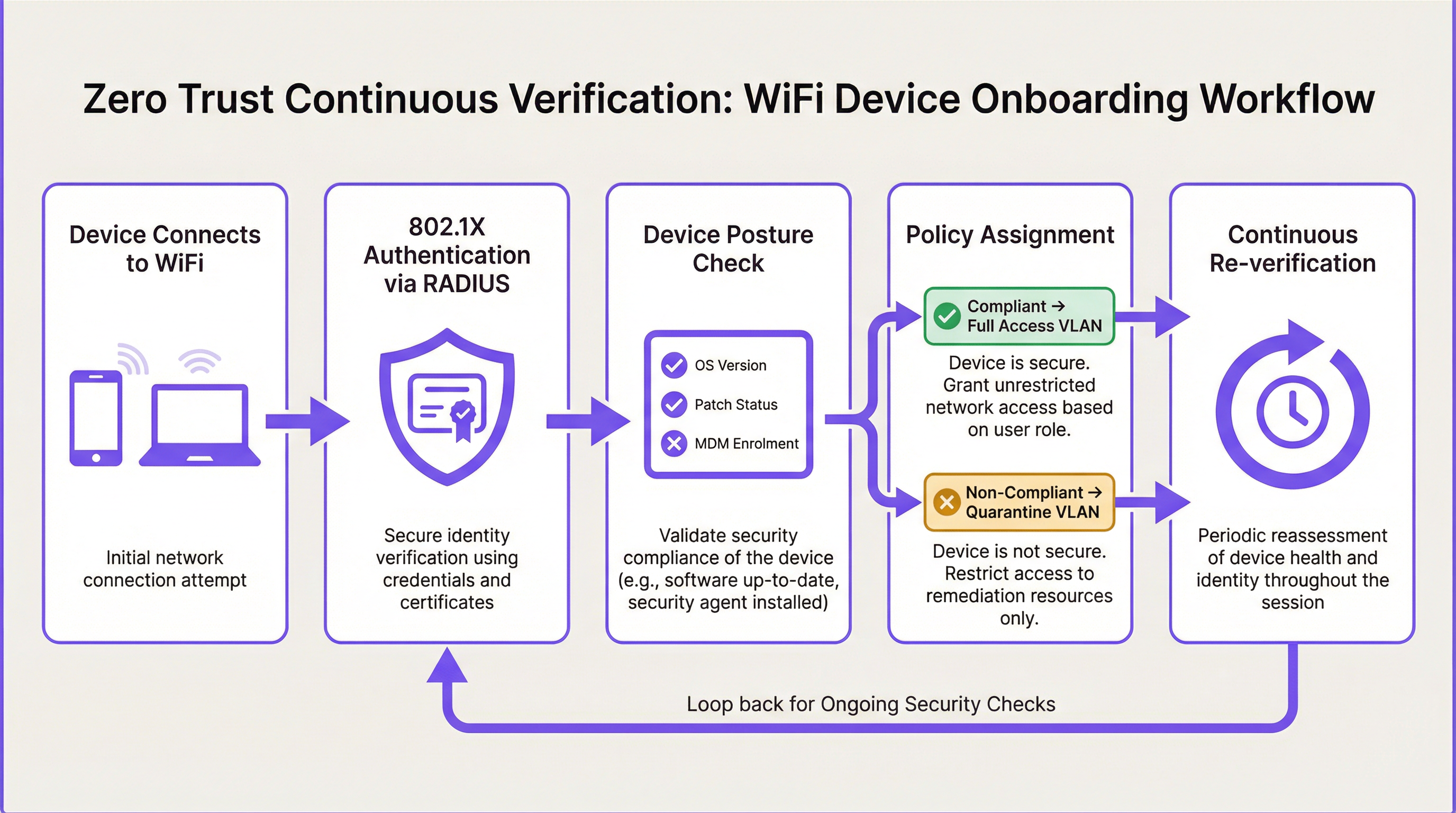
¿El dispositivo ejecuta un sistema operativo compatible y con parches? ¿Está inscrito en la plataforma corporativa de gestión de dispositivos móviles (MDM)? ¿El software antivirus está activo y actualizado? Si un dispositivo falla estas comprobaciones de postura, no se desconecta simplemente; se coloca en una VLAN de remediación con acceso limitado a servidores de parches o portales de soporte de TI, lo que permite al usuario resolver el problema de cumplimiento sin necesidad de intervención manual de TI.
Guía de implementación: Arquitectura de la solución
La implementación de WiFi Zero Trust requiere un enfoque coordinado en toda la LAN inalámbrica, la infraestructura de autenticación y el stack de seguridad de red.
Tecnologías y estándares principales
- IEEE 802.1X: La base del acceso seguro a la red. 802.1X proporciona control de acceso basado en puertos, garantizando que los dispositivos no puedan transmitir tráfico (que no sean tramas de autenticación EAP) hasta que hayan sido autenticados y autorizados explícitamente por el servidor RADIUS.
- EAP-TLS (Extensible Authentication Protocol - Transport Layer Security): El estándar de oro para la autenticación de dispositivos. EAP-TLS utiliza certificados digitales del lado del cliente y del servidor para la autenticación mutua, eliminando por completo el riesgo de robo de credenciales mediante phishing o ataques Man-in-the-Middle (MitM). Para profundizar en los protocolos de autenticación, revise nuestra guía: Comparativa de métodos EAP: PEAP, EAP-TLS, EAP-TTLS y EAP-FAST .
- WPA3-Enterprise: El estándar actual para el cifrado inalámbrico. WPA3-Enterprise, especialmente cuando se despliega en modo de 192 bits, proporciona la fuerza criptográfica necesaria para entornos altamente sensibles, sustituyendo al vulnerable estándar WPA2.
- Motor de políticas RADIUS: El cerebro central de la arquitectura. El servidor RADIUS evalúa las solicitudes de autenticación frente a las políticas definidas y devuelve atributos dinámicos (IDs de VLAN, ACLs, límites de ancho de banda) al punto de acceso.
Fases de implementación paso a paso
- Descubrimiento y perfilado: No se puede asegurar lo que no se puede ver. Comience por perfilar todos los dispositivos que se encuentran actualmente en la red. Utilice el fingerprinting de DHCP, el análisis de MAC OUI y el análisis de user-agent de HTTP para categorizar los dispositivos en grupos lógicos (por ejemplo, TI corporativa, BYOD, Invitado, IoT, POS).
- Definir microsegmentos: Basándose en la fase de descubrimiento, defina su arquitectura de VLAN objetivo. Un despliegue típico de Hospitality podría requerir segmentos para internet de invitados, operaciones del personal, sistemas de gestión de propiedades (PMS) e IoT del edificio.
- Desplegar RADIUS de alta disponibilidad: Implemente una infraestructura RADIUS robusta capaz de manejar la carga de autenticación y la evaluación de políticas. Garantice la redundancia activo-activo o activo-pasivo para evitar un punto único de falla.
- Implementar 802.1X para dispositivos gestionados: Comience la migración transicionando las laptops y tablets gestionadas por la empresa a 802.1X con EAP-TLS. Envíe los certificados y perfiles inalámbricos necesarios a través de su solución MDM para garantizar una experiencia de usuario fluida.
- Abordar el IoT mediante MAC Authentication Bypass (MAB) y perfilado: Muchos dispositivos IoT heredados (impresoras, smart TVs, Sensors ) no admiten suplicantes 802.1X. Para estos dispositivos, implemente MAB combinado con un perfilado estricto de dispositivos. El servidor RADIUS autentica el dispositivo basándose en su dirección MAC, pero aplica una ACL altamente restrictiva que solo permite la comunicación con los servidores requeridos.
- Integrar con SD-WAN: Asegúrese de que su microsegmentación inalámbrica se alinee con su arquitectura de red más amplia. Como se analiza en The Core SD WAN Benefits for Modern Businesses , SD-WAN puede extender estas políticas segmentadas a través de la WAN, garantizando la aplicación de Zero Trust de extremo a extremo.
Mejores prácticas para redes de recintos
- Nunca confíe en las PSK para el acceso corporativo: Las claves precompartidas (PSK) proporcionan cifrado pero ninguna verificación de identidad. Cualquier persona con la contraseña tiene acceso. Las PSK deben relegarse exclusivamente a las redes IoT heredadas (idealmente utilizando PSK únicas por dispositivo mediante tecnologías como MPSK/DPSK) o a las redes de invitados abiertas.
- Automatizar el onboarding de dispositivos: La transición a 802.1X y a la autenticación basada en certificados debe ser fluida para el usuario final. Utilice portales de onboarding que aprovisionen automáticamente los dispositivos BYOD con los certificados y perfiles de red correctos sin necesidad de tickets de soporte de TI.
- Monitorear y establecer líneas base de comportamiento: Zero Trust requiere visibilidad. Aproveche WiFi Analytics para establecer líneas base del comportamiento normal de la red. Si una cámara IP comienza repentinamente a intentar iniciar conexiones SSH a servidores internos, el motor de políticas debe detectar esta anomalía y poner el dispositivo en cuarentena automáticamente.
- Alinear con el hardware moderno: Asegúrese de que su infraestructura admita los estándares requeridos. Revise nuestra guía sobre Wireless Access Points Definition Your Ultimate 2026 Guide para comprender las capacidades necesarias para WPA3 y la aplicación de políticas dinámicas.
Solución de problemas y mitigación de riesgos
La implementación de Zero Trust en una red de recinto activa conlleva riesgos operativos. Los modos de falla más comunes implican el bloqueo de tráfico legítimo o la creación de bucles de autenticación.
| Riesgo/Modo de falla | Causa | Estrategia de mitigación |
|---|---|---|
| Tiempos de espera de autenticación 802.1X | Mala configuración del suplicante o latencia del servidor RADIUS. | Asegúrese de que los servidores RADIUS estén geográficamente cerca de los recintos. Verifique las cadenas de confianza de los certificados en los dispositivos cliente. Utilice EAP-TLS para evitar las solicitudes de credenciales de usuario. |
| Dispositivos IoT que se desconectan | Dispositivos que fallan el MAC Authentication Bypass o las comprobaciones de postura. | Implemente una fase de "modo de monitoreo" antes de aplicar las políticas de bloqueo. Registre todas las fallas de MAB y perfeccione las reglas de perfilado de dispositivos antes de cambiar al modo de aplicación. |
| Complejidad por sobresegmentación | Creación de demasiadas VLAN, lo que genera complejidad de enrutamiento y fallas en las aplicaciones (por ejemplo, fallas en el descubrimiento de multidifusión como Bonjour/mDNS). | Comience con segmentos funcionales amplios (Invitado, Personal, IoT, Seguro). Solo introduzca una mayor segmentación cuando un riesgo específico o un mandato de cumplimiento (por ejemplo, PCI DSS) lo requiera. Utilice gateways de Bonjour si es necesario el descubrimiento entre VLAN. |
| Evasiones de Captive Portal | Usuarios avanzados que suplantan direcciones MAC para evadir la autenticación del portal de invitados. | Las direcciones MAC se suplantan fácilmente. Combine el seguimiento de MAC con el fingerprinting del navegador y aplique tiempos de espera de sesión para mitigar el impacto de la suplantación de MAC. |
ROI e impacto empresarial
La transición a una arquitectura WiFi Zero Trust requiere inversión en tiempo de ingeniería, infraestructura RADIUS y, potencialmente, licencias NAC. Sin embargo, el retorno de la inversión para los recintos empresariales es sustancial y medible:
- Reducción del impacto de las brechas (reducción del radio de explosión): Al microsegmentar la red, un dispositivo de invitado comprometido o un sensor IoT vulnerable no puede utilizarse como punto de pivote para atacar la infraestructura crítica. Esto limita el "radio de explosión" de un incidente, reduciendo drásticamente el daño financiero y reputacional potencial de una brecha.
- Auditorías de cumplimiento simplificadas: Para los recintos de retail y hotelería, el cumplimiento de PCI DSS y GDPR representa una carga operativa significativa. La microsegmentación define y aísla claramente el Entorno de Datos de los Titulares de Tarjetas (CDE) y los sistemas que procesan Información de Identificación Personal (PII). Esto reduce el alcance de las auditorías de cumplimiento, ahorrando tiempo y gastos de consultoría significativos.
- Eficiencia operativa: Pasar de la gestión de PSK y las asignaciones manuales de VLAN a un acceso dinámico basado en políticas reduce la carga del soporte de TI. El onboarding automatizado y los flujos de trabajo de remediación de autoservicio liberan a los ingenieros senior para que se centren en iniciativas estratégicas en lugar de restablecer contraseñas de WiFi.
- Preparar el recinto para el futuro: A medida que los recintos despliegan tecnologías más avanzadas (desde sistemas de Wayfinding hasta quioscos de check-in automatizados), la superficie de ataque se expande. Una base Zero Trust garantiza que las nuevas tecnologías puedan integrarse de forma segura sin comprometer la red principal. Como se destaca en Modern Hospitality WiFi Solutions Your Guests Deserve , la seguridad es la base invisible de la experiencia moderna del invitado.
Términos clave y definiciones
Zero Trust Network Access (ZTNA)
A security framework that requires all users and devices, whether inside or outside the organisation's network, to be authenticated, authorised, and continuously validated before being granted access to applications and data.
The overarching philosophy that drives the shift from perimeter-based security to identity- and context-based security on venue WiFi networks.
Micro-Segmentation
The practice of dividing a network into distinct security segments down to the individual workload or device level, applying strict access controls to dictate how these segments communicate.
Essential for limiting the 'blast radius' of a breach; ensures a compromised guest device cannot access corporate servers or POS terminals.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enforcing Zero Trust at the wireless edge, acting as the gatekeeper before any network traffic is permitted.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The policy engine in a Zero Trust WiFi architecture that evaluates credentials and dynamically assigns VLANs and access policies.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An EAP method that uses public key infrastructure (PKI) and digital certificates for mutual authentication between the client and the authentication server.
The most secure authentication method for managed devices, eliminating reliance on passwords and protecting against credential theft.
Dynamic VLAN Assignment
A network configuration where a RADIUS server assigns a device to a specific Virtual Local Area Network (VLAN) based on its authenticated identity or profile, rather than the SSID it connected to.
The primary mechanism for enforcing micro-segmentation and least-privilege access on enterprise wireless networks.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X supplicants (like many IoT devices) by using their MAC address as the identity credential.
A pragmatic workaround for legacy devices, which must be paired with strict profiling and restricted VLAN assignment due to the ease of MAC spoofing.
Device Posture
The security state of an endpoint device, including factors such as OS patch level, antivirus status, firewall configuration, and MDM enrolment.
A critical component of continuous verification; devices failing posture checks are quarantined regardless of valid user credentials.
Casos de éxito
A 350-room hotel group needs to secure its flat network architecture where guest devices, staff laptops, IP cameras, and the Property Management System (PMS) currently share the same VLAN, creating significant GDPR and lateral movement risks.
Deploy a micro-segmented architecture using dynamic VLAN assignment via RADIUS. Create four distinct segments: Guest Internet, Staff Corporate, IoT/Building Systems, and PMS Access. Implement 802.1X with EAP-TLS certificate authentication for staff devices via MDM. Use MAC Authentication Bypass (MAB) with strict profiling for IoT devices, placing them in an isolated VLAN with restrictive ACLs. Guest devices authenticate via a captive portal, receiving internet-only access.
A major retail chain with 200 stores must achieve PCI DSS compliance by isolating its Point of Sale (POS) terminals from the customer WiFi and staff productivity networks, all of which currently operate on the same physical wireless infrastructure.
Implement role-based access control and micro-segmentation. Configure the RADIUS policy engine to assign devices to three isolated VLANs: Customer Guest WiFi (internet only), Staff WiFi (role-based access for managers vs. associates), and a dedicated POS segment. Secure the POS segment using WPA3-Enterprise and EAP-TLS, enforcing strict firewall rules that only permit traffic to the payment gateway. Integrate RADIUS accounting logs into the SIEM for audit trails.
A stadium venue needs to deploy a new fleet of smart turnstiles. These devices support basic WPA2-Personal but do not have an 802.1X supplicant. How should the network architect integrate them into the Zero Trust WiFi environment?
The architect should utilise MAC Authentication Bypass (MAB) configured on the RADIUS server. The turnstiles' MAC addresses should be profiled, and upon connection, the RADIUS server should dynamically assign them to a dedicated, highly restricted 'Turnstile IoT' VLAN. The firewall rules for this VLAN must enforce least-privilege, permitting outbound communication only to the specific ticketing gateway IP addresses on the required ports, blocking all lateral movement to other network segments.
Análisis de escenarios
Q1. During a network audit, you discover that the 'Staff Corporate' SSID uses a single Pre-Shared Key (PSK) shared among 50 employees. What are the primary security risks of this configuration in a Zero Trust context, and what is the recommended remediation?
💡 Sugerencia:Focus on identity verification and the impact of employee turnover.
Mostrar enfoque recomendado
The primary risks are the lack of individual identity verification (anyone with the PSK is trusted) and the inability to revoke access for a single user without changing the password for everyone (e.g., when an employee leaves). The recommended remediation is to migrate the 'Staff Corporate' SSID to WPA3-Enterprise using 802.1X. Ideally, deploy EAP-TLS with certificates pushed via MDM for seamless, highly secure authentication, allowing individual device access to be revoked instantly.
Q2. A managed corporate laptop successfully authenticates via EAP-TLS and is assigned to the 'Corporate Access' VLAN. However, the user subsequently disables their endpoint detection and response (EDR) agent. How should a Zero Trust architecture handle this event?
💡 Sugerencia:Think about the 'continuous verification' and 'device posture' pillars of Zero Trust.
Mostrar enfoque recomendado
A Zero Trust architecture must enforce continuous verification. The Network Access Control (NAC) solution, integrated with the EDR platform, should detect the posture change (EDR disabled). The NAC should then issue a Change of Authorization (CoA) to the wireless controller, dynamically revoking the laptop's 'Corporate Access' privileges mid-session and reassigning it to a 'Quarantine' VLAN until the EDR agent is re-enabled.
Q3. A hotel guest connects to the open 'Guest WiFi' SSID and authenticates via the captive portal. However, the network administrator notices that the guest device is attempting to scan IP addresses within the 10.0.0.0/8 range, which is used for internal hotel systems. What Zero Trust principle is failing, and how should it be corrected?
💡 Sugerencia:Consider the principles of micro-segmentation and least-privilege access.
Mostrar enfoque recomendado
The principle of least-privilege access (and micro-segmentation) is failing. A guest device should only have outbound internet access and should not be able to route traffic to internal subnets. This should be corrected by ensuring the Guest VLAN has strict Access Control Lists (ACLs) applied at the firewall or gateway that explicitly drop any traffic destined for RFC 1918 private IP ranges, permitting only traffic destined for the public internet.
Conclusiones clave
- ✓Zero Trust WiFi assumes no device is inherently safe, replacing perimeter security with continuous verification.
- ✓Least-privilege access ensures devices only reach the specific network resources required for their function.
- ✓Micro-segmentation via dynamic VLAN assignment isolates critical systems (like POS) from guest and IoT traffic.
- ✓Device posture enforcement validates OS patching and security agents before granting network access.
- ✓IEEE 802.1X and WPA3-Enterprise form the technical foundation for secure, policy-driven wireless authentication.
- ✓EAP-TLS certificate-based authentication is the gold standard for securing managed corporate devices.
- ✓Implementing Zero Trust reduces the 'blast radius' of breaches and streamlines compliance for PCI DSS and GDPR.



