Alta Disponibilidade de Servidor RADIUS: Ativo-Ativo vs Ativo-Passivo
Um guia de referência técnica definitivo para gerentes de TI e arquitetos de rede que avaliam arquiteturas de alta disponibilidade RADIUS. Ele contrasta implantações Ativo-Ativo e Ativo-Passivo, detalha os requisitos de replicação de banco de dados e explica como o Cloud RADIUS mitiga a latência de failover para locais corporativos.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Aprofundamento Técnico: Entendendo a Arquitetura RADIUS
- Arquitetura Ativo-Passivo
- Arquitetura Ativo-Ativo
- O Desafio da Replicação de Banco de Dados
- Guia de Implementação: Nuvem vs On-Premise
- Cloud RADIUS Platforms
- Considerações de Implantação On-Premise
- Melhores Práticas para Alta Disponibilidade RADIUS
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
Resumo Executivo
Para redes corporativas, a autenticação é binária: ou funciona perfeitamente, ou as operações comerciais param inteiramente. O RADIUS (Remote Authentication Dial-In User Service) serve como o guardião crítico para implantações de IEEE 802.1X, WPA3 enterprise e Guest WiFi em locais modernos. Ao contrário dos serviços de aplicação que degradam gradualmente sob carga, uma falha no RADIUS bloqueia imediatamente o acesso à rede de usuários, terminais de ponto de venda e dispositivos operacionais.
Este guia de referência técnica avalia os modelos arquitetônicos para a implantação de infraestrutura RADIUS de alta disponibilidade. Especificamente, ele contrasta as configurações tradicionais Ativo-Passivo com os clusters Ativo-Ativo modernos. Para gerentes de TI, arquitetos de rede e diretores de operações de locais que gerenciam ambientes de alta densidade como Varejo , Hospitalidade e estádios, entender essas estratégias de failover, mecânicas de balanceamento de carga e requisitos de replicação de banco de dados é essencial.
Além disso, este guia examina como as plataformas Cloud RADIUS abstraem a complexidade da alta disponibilidade, fornecendo failover automático e escalabilidade elástica sem o ônus operacional de manter infraestrutura on-premise redundante. Ao aplicar essas melhores práticas neutras em relação a fornecedores, as equipes de engenharia podem projetar arquiteturas de autenticação que eliminam pontos únicos de falha e atendem a rigorosos Acordos de Nível de Serviço (SLAs) de tempo de atividade.
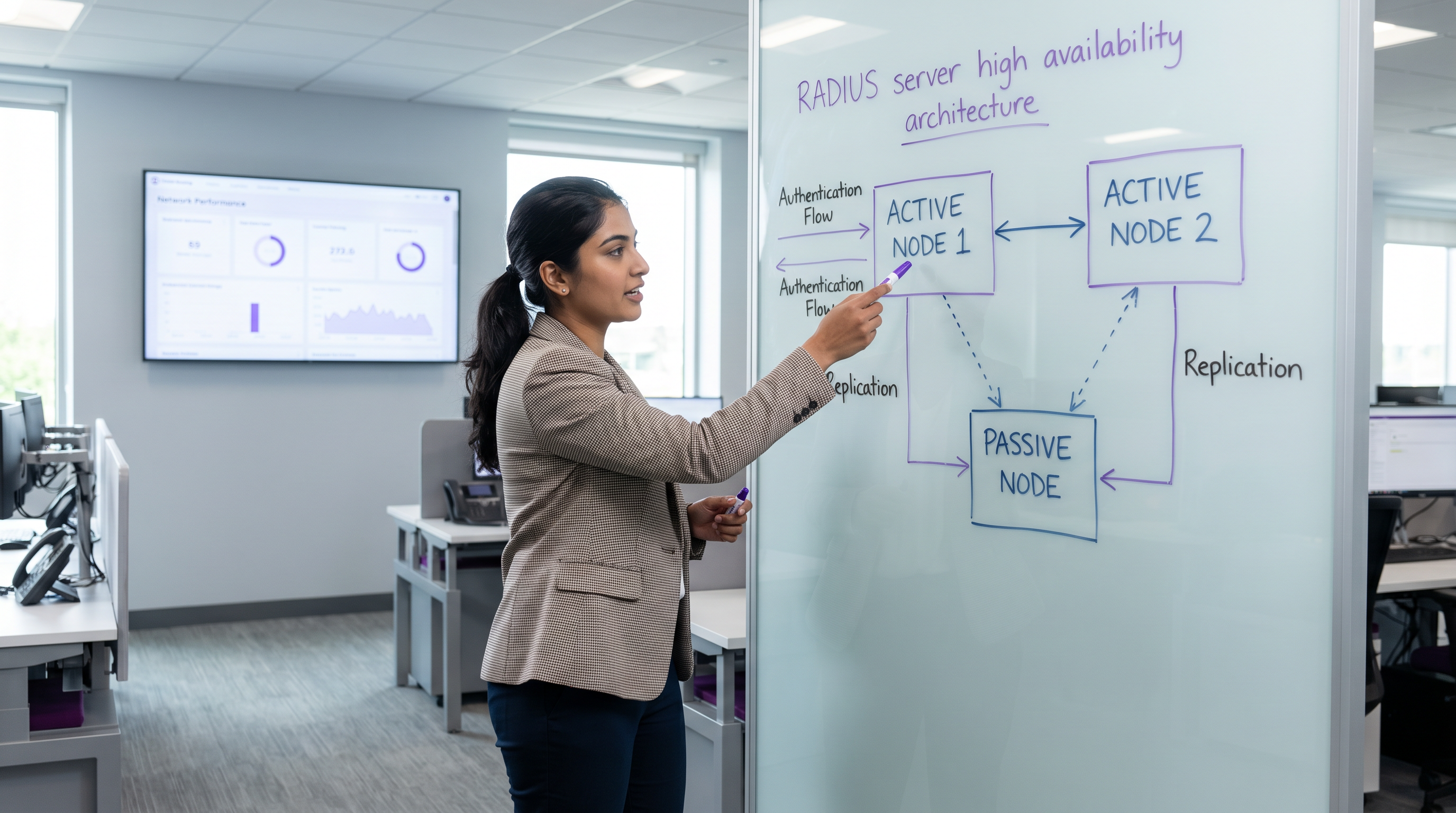
Aprofundamento Técnico: Entendendo a Arquitetura RADIUS
O RADIUS opera como um protocolo cliente-servidor sobre UDP, utilizando tipicamente a porta 1812 para autenticação e a porta 1813 para contabilização, conforme definido nas RFC 2865 e RFC 2866. A natureza stateless das solicitações de autenticação UDP é uma vantagem estrutural para o design de alta disponibilidade. Como cada pacote Access-Request contém todas as credenciais e parâmetros necessários, qualquer servidor RADIUS dentro de um cluster pode processar qualquer solicitação de forma independente, sem exigir sincronização de estado complexa para a fase de autenticação em si.
Arquitetura Ativo-Passivo
Em uma implantação Ativo-Passivo (ou primário-standby), um único servidor RADIUS processa todo o tráfego de autenticação e contabilização de entrada. Um servidor secundário permanece online, mas ocioso, recebendo atualizações de replicação de banco de dados, mas não respondendo ativamente aos Dispositivos de Acesso à Rede (NADs), como pontos de acesso, switches ou gateways de VPN.
Quando o servidor primário falha, o NAD detecta o timeout e redireciona as solicitações subsequentes para o servidor secundário. O tempo de detecção de failover depende inteiramente dos temporizadores de configuração do NAD. Um NAD típico envia uma solicitação RADIUS e aguarda um tempo de esgotamento de pacote padrão (geralmente dois segundos). Se nenhuma resposta for recebida, ele tenta novamente. Com uma configuração padrão de três tentativas por servidor, o NAD pode esperar até seis segundos antes de declarar o servidor primário como inativo e realizar o failover para o secundário. Em ambientes com três servidores configurados, essa janela de failover pode se estender para dezoito segundos. Para um local de Hospitalidade movimentado ou um ambiente de Varejo que processa transações, esse atraso representa uma interrupção perceptível no serviço.
Arquitetura Ativo-Ativo
Por outro lado, uma arquitetura Ativo-Ativo distribui a carga de autenticação entre vários servidores RADIUS operacionais simultaneamente. O tráfego é roteado para o cluster por meio de configuração round-robin nos NADs ou via um balanceador de carga dedicado.
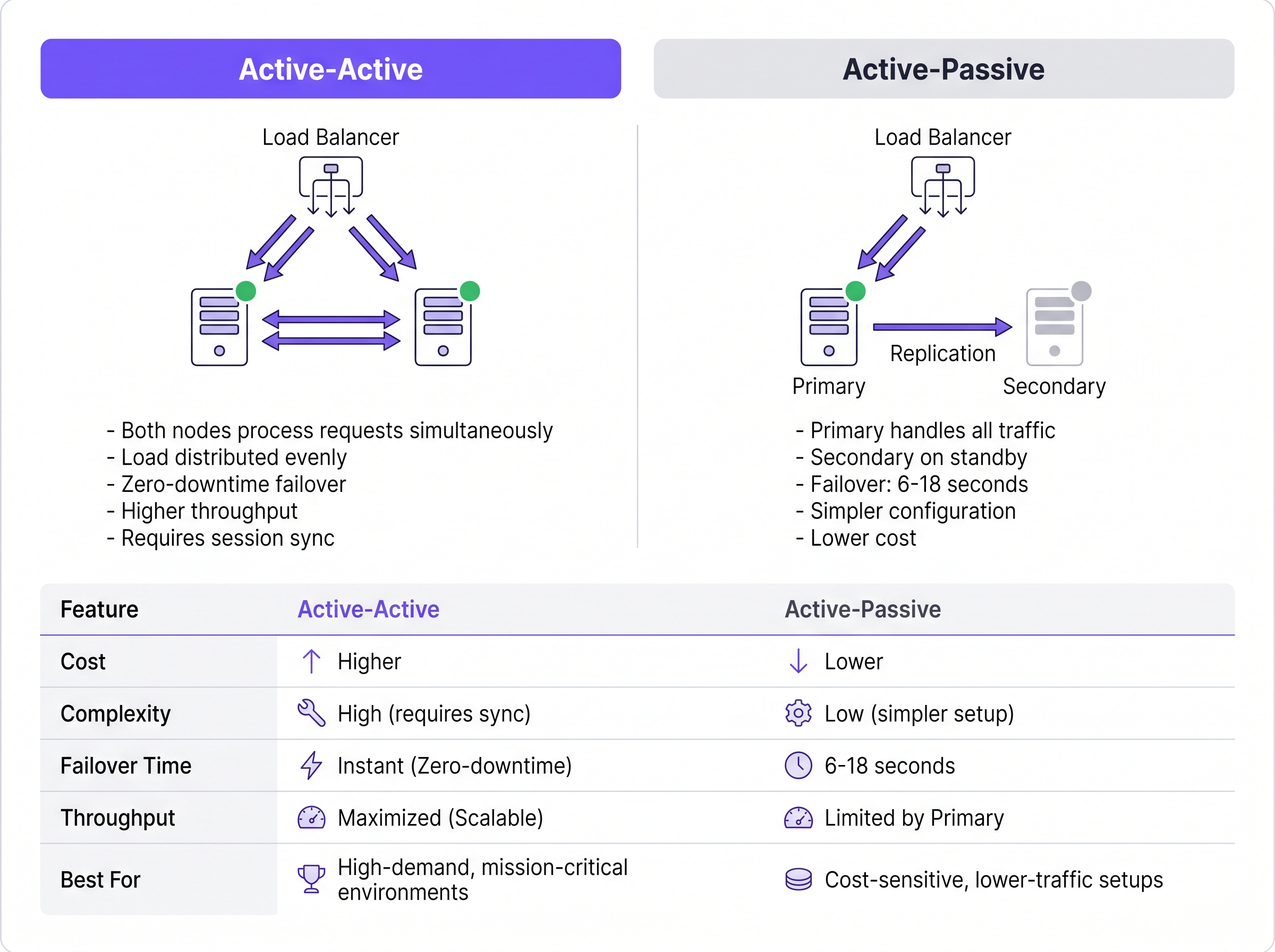
Este modelo elimina o atraso de detecção de failover inerente às configurações Ativo-Passivo. Se um nó falha, o balanceador de carga (ou os NADs usando round-robin) simplesmente deixa de rotear o tráfego para o servidor que não responde, normalmente dentro de um a dois segundos com base nos intervalos de verificação de integridade (health-check). Os nós ativos restantes absorvem instantaneamente o tráfego. Além disso, os clusters Ativo-Ativo escalam horizontalmente; adicionar capacidade para eventos de alta densidade requer apenas o provisionamento de nós adicionais ao cluster.
O Desafio da Replicação de Banco de Dados
Embora a autenticação RADIUS seja stateless, a contabilização RADIUS é inerentemente stateful. Ela rastreia o início da sessão (Start), o uso contínuo (Interim-Update) e o término (Stop). Para locais que utilizam WiFi Analytics ou sistemas de faturamento, esses dados de contabilização devem permanecer consistentes em todos os nós.
Dar suporte a um cluster RADIUS com um banco de dados replicado (como MySQL ou MariaDB integrado ao FreeRADIUS) é obrigatório para uma alta disponibilidade robusta. Para implantações Ativo-Ativo, a replicação multi-master síncrona — como Galera Cluster ou MySQL NDB Cluster — é necessária. A replicação síncrona garante que um registro de contabilização seja confirmado em todos os nós simultaneamente, evitando a perda de dados se um nó falhar. A replicação assíncrona tradicional, frequentemente usada em configurações Ativo-Passivo, introduz atraso de replicação. Se o nó primário falhar antes que o secundário receba a atualização, os dados da sessão ativa serão perdidos permanentemente, o que pode violar frameworks de conformidade como o PCI DSS.
Guia de Implementação: Nuvem vs On-Premise
A decisão arquitetônica vai além de como agrupar servidores em clusters; envolve onde esses servidores residem. Para operadores de vários sites, o backhaul do tráfego de autenticação para um data center on-premise centralizado introduz latência de WAN e cria um ponto único de falha no link de WAN.
Cloud RADIUS Platforms
Serviços de Cloud RADIUS resolvem desafios de distribuição geográfica ao hospedar a infraestrutura de autenticação em múltiplas zonas de disponibilidade globais. Quando um usuário se conecta em uma filial, a solicitação é roteada para o nó de borda na nuvem mais próximo, minimizando a latência.
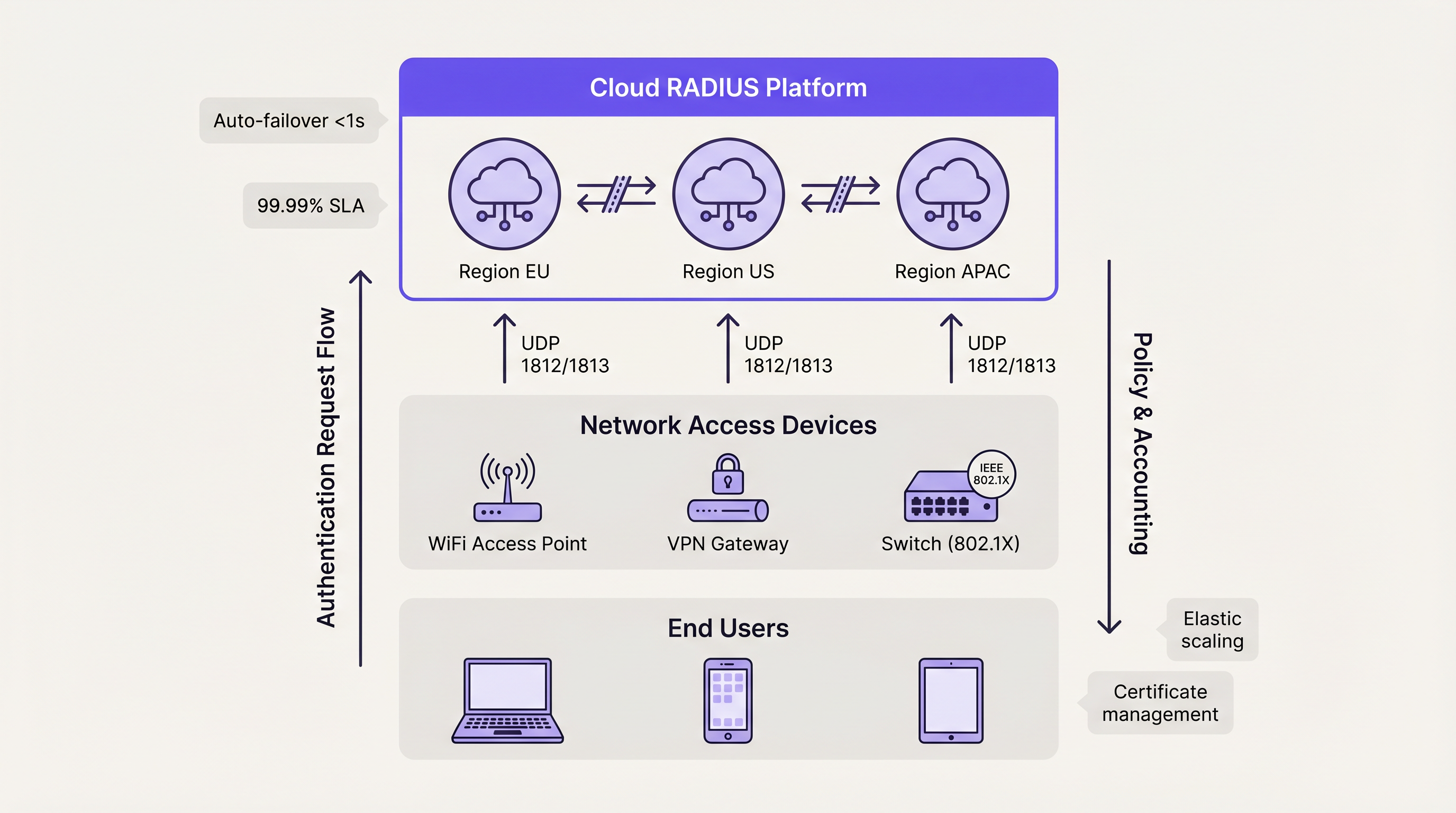
Plataformas de nuvem utilizam inerentemente arquiteturas Ativo-Ativo. O failover entre zonas de disponibilidade é gerenciado automaticamente pelo balanceamento de carga interno do provedor, abstraindo inteiramente a complexidade da equipe de engenharia do cliente. Este modelo normalmente oferece SLAs de 99,99% de uptime e elimina a necessidade de gerenciamento manual de certificados, correção de sistema operacional e ajuste de replicação de banco de dados. Para organizações que implantam Wayfinding ou Sensors em campi distribuídos, a autenticação hospedada na nuvem garante a aplicação consistente de políticas sem dependências de hardware localizadas.
Considerações de Implantação On-Premise
Organizações que operam em setores altamente regulamentados — como ambientes específicos de Saúde ou governamentais — podem exigir implantações on-premise devido a mandatos estritos de soberania de dados. Nesses cenários, a implantação de um cluster FreeRADIUS Ativo-Ativo com replicação síncrona Galera oferece o mais alto nível de resiliência.
No entanto, as equipes de engenharia devem considerar a sobrecarga operacional. O gerenciamento de certificados TLS em múltiplos nós, a garantia de consistência de configuração e o monitoramento ativo da integridade da replicação do banco de dados exigem recursos administrativos dedicados. Os balanceadores de carga de hardware devem ser configurados especificamente para suportar tráfego UDP com verificações de integridade RADIUS apropriadas, já que muitos balanceadores de carga padrão são otimizados apenas para tráfego TCP HTTP/HTTPS.
Melhores Práticas para Alta Disponibilidade RADIUS
- Distribuir em vez de Duplicar: Para implantações que excedem 500 usuários simultâneos, priorize arquiteturas Ativo-Ativo em vez de configurações Ativo-Passivo para maximizar o rendimento e minimizar a latência de failover.
- Implementar Replicação Síncrona: Proteja os dados de accounting com estado utilizando replicação de banco de dados multi-mestre síncrona (ex: Galera Cluster) em vez de modelos primário-réplica assíncronos.
- Padronizar a Confiança de Certificados: Em um cluster Ativo-Ativo, garanta que todos os nós apresentem o certificado de servidor idêntico ou certificados da mesma cadeia de Autoridade Certificadora (CA). Discrepâncias farão com que os handshakes EAP-TLS e PEAP falhem durante a rotação de nós.
- Ajustar Timers de NAD: Otimize os temporizadores de repetição e timeout de RADIUS em seus Dispositivos de Acesso à Rede (NAD). Um timeout de dois segundos com duas repetições oferece um equilíbrio entre a detecção rápida de failover e a prevenção de failover prematuro durante pequenos congestionamentos de rede.
- Testar Cenários de Falha: Trate os nós secundários como sistemas de produção. Simule regularmente falhas de nós, dessincronização de banco de dados e quedas de link WAN para validar se os mecanismos de failover automatizados funcionam conforme projetado.
Solução de Problemas e Mitigação de Riscos
O modo de falha mais prevalente na alta disponibilidade RADIUS é o desvio de configuração (configuration drift). Em configurações Ativo-Passivo, os administradores frequentemente atualizam políticas ou renovam certificados no nó primário, mas negligenciam o secundário. Quando ocorre um evento de failover, o nó secundário rejeita o tráfego legítimo devido a credenciais expiradas ou políticas desatualizadas.
Para mitigar esse risco, implemente ferramentas de gerenciamento de configuração (como Ansible ou Terraform) para implantar alterações simetricamente em todos os nós. Para o gerenciamento de certificados, utilize protocolos de renovação automatizados (como ACME) configurados para distribuir o certificado atualizado para todo o cluster simultaneamente.
Outro risco significativo é a configuração incorreta do balanceador de carga. Se um balanceador de carga não realizar verificações de integridade na camada de aplicação (especificamente verificando a capacidade de resposta da porta UDP 1812), ele pode continuar roteando o tráfego para um nó onde o sistema operacional está em execução, mas o daemon RADIUS travou. Certifique-se de que as verificações de integridade validem explicitamente a disponibilidade do serviço RADIUS.
ROI e Impacto nos Negócios
O retorno sobre o investimento para uma alta disponibilidade RADIUS robusta é medido principalmente através da mitigação de riscos e eficiência operacional. Interrupções de autenticação resultam em perdas imediatas de produtividade para os funcionários e graves danos à reputação de locais voltados ao público.
Ao transitar de implantações manuais de servidor único para arquiteturas Ativo-Ativo automatizadas (particularmente via Cloud RADIUS), as organizações recuperam horas significativas de engenharia anteriormente dedicadas à manutenção de rotina. Essa eficiência operacional permite que as equipes de rede se concentrem em iniciativas estratégicas, como a implantação de Os Principais Benefícios do SD WAN para Empresas Modernas ou a otimização da cobertura de alta densidade, em vez de apagar incêndios em falhas de autenticação. Fundamentalmente, a autenticação confiável é a camada base sobre a qual todos os serviços de rede subsequentes dependem.
Termos-Chave e Definições
Active-Active Architecture
A high availability design where multiple RADIUS servers process authentication requests simultaneously, distributing the load and providing instant failover without detection delays.
Essential for high-density venues (stadiums, large retail) where a single server cannot handle peak authentication surges.
Active-Passive Architecture
A redundancy model where a primary server handles all traffic, and a secondary server remains idle on standby until the primary fails.
Suitable for smaller, cost-sensitive deployments, but introduces a 6-18 second failover delay while the network access device detects the failure.
Synchronous Replication
A database replication method where data is written to all nodes in a cluster simultaneously before the transaction is considered complete.
Mandatory for Active-Active RADIUS accounting databases (like Galera Cluster) to prevent data loss and ensure compliance.
Asynchronous Replication
A database replication method where the primary node records the data and later copies it to secondary nodes, introducing a slight delay (lag).
Often used in Active-Passive setups but carries the risk of losing recent accounting records if the primary node fails abruptly.
Network Access Device (NAD)
The hardware component (such as a WiFi access point, switch, or VPN gateway) that requests authentication from the RADIUS server on behalf of the user.
The NAD's internal retry and timeout timers dictate how quickly an Active-Passive failover occurs.
Stateless Protocol
A communications protocol that treats each request as an independent transaction, unrelated to any previous request.
RADIUS authentication over UDP is stateless, allowing load balancers to route any request to any active server seamlessly.
Configuration Drift
The phenomenon where secondary or backup servers become out of sync with the primary server regarding policies, updates, or certificates over time.
The leading cause of failure in Active-Passive RADIUS deployments when the secondary node is forced to take over.
Cloud RADIUS
A managed authentication service hosted across globally distributed cloud infrastructure, providing built-in Active-Active redundancy and automatic scaling.
Replaces the need for IT teams to manually build, patch, and monitor redundant on-premise RADIUS servers.
Estudos de Caso
A European hotel group manages 45 properties across six countries. They currently run independent FreeRADIUS virtual machines at each property. A recent expired TLS certificate at one location caused a complete guest WiFi outage during a major conference. How should they redesign their authentication architecture to prevent localized outages and reduce maintenance overhead?
The hotel group should migrate from localized, single-node FreeRADIUS instances to a centralized Cloud RADIUS platform utilizing an Active-Active architecture. By leveraging a cloud provider with geographically distributed edge nodes, authentication requests from each property are routed to the nearest regional node, minimizing latency. Centralized policy management allows the IT team to define authentication rules once and apply them globally. The cloud provider automatically handles TLS certificate rotation, operating system patching, and database replication.
A national sports stadium is preparing for a 60,000-attendee event. Their current RADIUS setup is an Active-Passive configuration. During load testing, the primary server became saturated processing 8,000 authentication requests per minute when the gates opened, causing severe connection delays, while the secondary server remained completely idle. How can they optimize this deployment?
The network engineering team must convert the deployment from Active-Passive to Active-Active. First, they should reconfigure the stadium's Network Access Devices (NADs) to utilize round-robin load balancing across both RADIUS servers, instantly doubling their authentication throughput. Second, they should provision a third RADIUS node to provide necessary headroom for peak surges. Finally, to ensure accounting data remains consistent across all three active nodes, they must implement a synchronous multi-master database replication solution, such as Galera Cluster.
Análise de Cenário
Q1. Your enterprise retail client requires a highly available RADIUS solution for their point-of-sale terminals. They have strict PCI DSS compliance requirements dictating that absolutely no accounting session data can be lost during a server failover. Which database replication strategy must you implement for the RADIUS backend?
💡 Dica:Consider the difference between data being written simultaneously versus data being copied after the fact.
Mostrar Abordagem Recomendada
You must implement Synchronous Replication (such as a Galera Cluster or MySQL NDB Cluster). Synchronous replication ensures that the accounting record is committed to all nodes simultaneously before acknowledging the transaction. If you used Asynchronous replication, a node failure could result in the loss of recent transactions that had not yet been copied to the secondary database, violating the strict compliance requirement.
Q2. A university campus network uses an Active-Passive RADIUS setup. Students complain that when the primary server undergoes maintenance, it takes nearly 20 seconds for their laptops to connect to the WiFi. The access points are configured with a 3-second RADIUS timeout and 5 retries. How can you reduce the failover delay without changing the server architecture?
💡 Dica:Calculate the maximum wait time based on the NAD timers before it attempts the secondary server.
Mostrar Abordagem Recomendada
You should tune the timers on the Network Access Devices (access points). Currently, the AP waits 3 seconds and retries 5 times, resulting in an 18-second delay (3 seconds × 6 total attempts) before failing over to the passive server. By reducing the configuration to a 2-second timeout and 2 retries, the failover detection time drops to 6 seconds, significantly improving the user experience during maintenance windows.
Q3. You are migrating a multi-site corporate network from an Active-Passive on-premise RADIUS server to an Active-Active Cloud RADIUS platform. During the pilot phase, devices successfully authenticate against Cloud Node A, but when the load balancer routes them to Cloud Node B, the EAP-TLS handshakes fail. What is the most likely configuration error?
💡 Dica:Consider what the client device verifies when establishing a secure EAP tunnel with a new server.
Mostrar Abordagem Recomendada
The most likely issue is a Certificate Trust mismatch. In an Active-Active cluster, all RADIUS nodes must present the exact same server certificate (or certificates issued by the exact same trusted CA chain). If Cloud Node B is presenting a different certificate that the client devices do not trust, the EAP-TLS handshake will be rejected by the client, causing authentication to fail despite the server functioning correctly.
Principais Conclusões
- ✓RADIUS high availability is critical because authentication failures immediately block all network access for users and devices.
- ✓Active-Passive setups are simpler but introduce a 6-18 second failover delay dictated by the Network Access Device's retry timers.
- ✓Active-Active architectures process requests simultaneously, providing instant failover and horizontal scalability for high-density environments.
- ✓While RADIUS authentication is stateless, accounting is stateful and requires synchronous database replication (like Galera) to prevent data loss.
- ✓Cloud RADIUS platforms abstract HA complexity by providing globally distributed, automatically scaling Active-Active infrastructure.
- ✓Configuration drift and mismatched TLS certificates are the most common causes of failure during RADIUS failover events.



